| File name: | e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92 |
| Full analysis: | https://app.any.run/tasks/62cb9bd6-c4f5-4516-9c9b-a6718ab60bf5 |
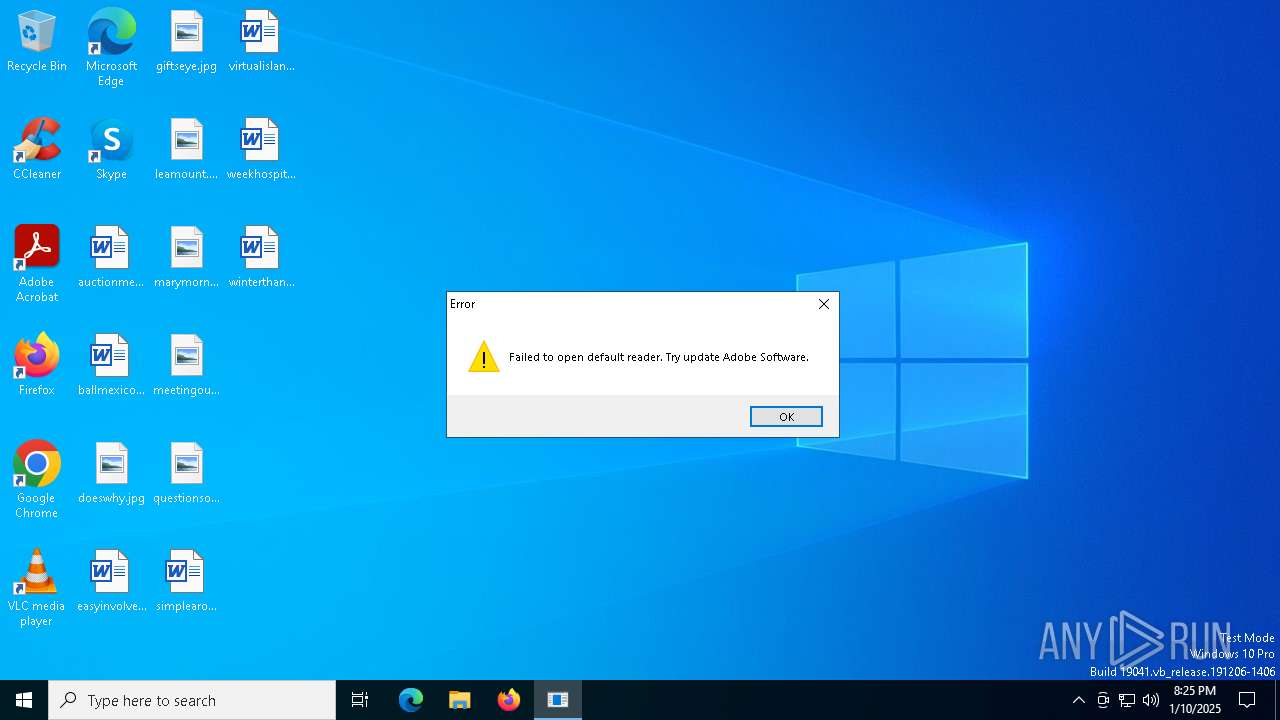
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2025, 20:24:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 2AB30945A2F43A06FFFD092AB599561A |
| SHA1: | 65075FCFD1B0318500471F078DFD4F1195FCE81B |
| SHA256: | E0E53651961939AF9EA23E40529BEC8418F5915D4A7FAA23184ADC4FEBB81B92 |
| SSDEEP: | 24576:TAGJftHMFSCVdhbgHN7GKKVjiv+xODiI6Tfk0zaERmVsx02BpoRLlJtDQsCJc3gS:TAGJftHMFSCVdhbgt7GKOjiv+xODiI60 |
MALICIOUS
Executing a file with an untrusted certificate
- e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe (PID: 2072)
- e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe (PID: 4308)
- e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe (PID: 5780)
SUSPICIOUS
Application launched itself
- e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe (PID: 2072)
Executes application which crashes
- e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe (PID: 5780)
INFO
Reads the computer name
- e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe (PID: 2072)
Reads the machine GUID from the registry
- e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe (PID: 2072)
Checks supported languages
- e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe (PID: 2072)
Checks proxy server information
- WerFault.exe (PID: 3692)
Reads the software policy settings
- WerFault.exe (PID: 3692)
Creates files or folders in the user directory
- WerFault.exe (PID: 3692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (49.4) |
|---|---|---|
| .scr | | | Windows screen saver (23.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.7) |
| .exe | | | Win32 Executable (generic) (8) |
| .exe | | | Generic Win/DOS Executable (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2046:02:07 06:51:50+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 874496 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd7636 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Search Protocol Host |
| FileVersion: | 1.0.0.0 |
| InternalName: | AHSf.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | AHSf.exe |
| ProductName: | Search Protocol Host |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
134
Monitored processes
4
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2072 | "C:\Users\admin\AppData\Local\Temp\e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe" | C:\Users\admin\AppData\Local\Temp\e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Search Protocol Host Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3692 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5780 -s 228 | C:\Windows\SysWOW64\WerFault.exe | e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4308 | "C:\Users\admin\AppData\Local\Temp\e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe" | C:\Users\admin\AppData\Local\Temp\e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe | — | e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Search Protocol Host Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5780 | "C:\Users\admin\AppData\Local\Temp\e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe" | C:\Users\admin\AppData\Local\Temp\e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe | e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Search Protocol Host Exit code: 3221225477 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
3 197
Read events
3 197
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
6
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3692 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_e0e53651961939af_2336d0fe78e0adee2df4abc129a378047f49ee2_9fcc216e_54f42a5b-adb3-4fcf-ab3c-d1288e84bdba\Report.wer | — | |
MD5:— | SHA256:— | |||
| 3692 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER680F.tmp.dmp | binary | |
MD5:D60952AC5C87F6CEF3BEE20ABA4252F8 | SHA256:F46F18456AAE22F52816AD91531D1D39E80E4B3ABC761907C6C801972357D765 | |||
| 3692 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER688E.tmp.xml | xml | |
MD5:1CD36413079B48FE42B6C2FAC55FEC90 | SHA256:EE79ECDEA6929173BF6E5ABB27238AD32C3D605ADA2331AD9B9A42281E43BA32 | |||
| 3692 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:FA84E4BCC92AA5DB735AB50711040CDE | SHA256:6D7205E794FDE4219A62D9692ECDDF612663A5CF20399E79BE87B851FCA4CA33 | |||
| 3692 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:F6F53CD09A41E968C363419B279D3112 | SHA256:6D2BB01CC7A9BADE2113B219CAC1BDA86B2733196B7E1BD0C807CE1E396B1892 | |||
| 3692 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\e0e53651961939af9ea23e40529bec8418f5915d4a7faa23184adc4febb81b92.exe.5780.dmp | binary | |
MD5:2FB3DA7E97B3E84485C098E224CB7A00 | SHA256:0FDAEBC1ACADFF0113E08CA76BDB5BA9001B95BE9BE7BC6A8D714A69E50A144B | |||
| 3692 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER685E.tmp.WERInternalMetadata.xml | xml | |
MD5:0B357067A06EE519461AC52FB3F1DC20 | SHA256:9B65DA51B9BE21F02EDEB21382B2BD8CB631DAFCA4719CA8821906DE811FBD36 | |||
| 3692 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:9D261428590030CCD92EB9009128F973 | SHA256:B1DCA9DE843C937118F93C3E0A5243AF7E7241DA09ED1739E705C3ACCEB3A112 | |||
| 3692 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:BDE4316FA023E8101237FA20BFD0FB14 | SHA256:434BC41126E54AC0C587E3CA61C2D0CF655109FA9BAB034315495B44E5ED5319 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
34
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6348 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7012 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7012 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3692 | WerFault.exe | GET | 200 | 23.32.238.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3692 | WerFault.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.172:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.172:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 104.126.37.137:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1076 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |