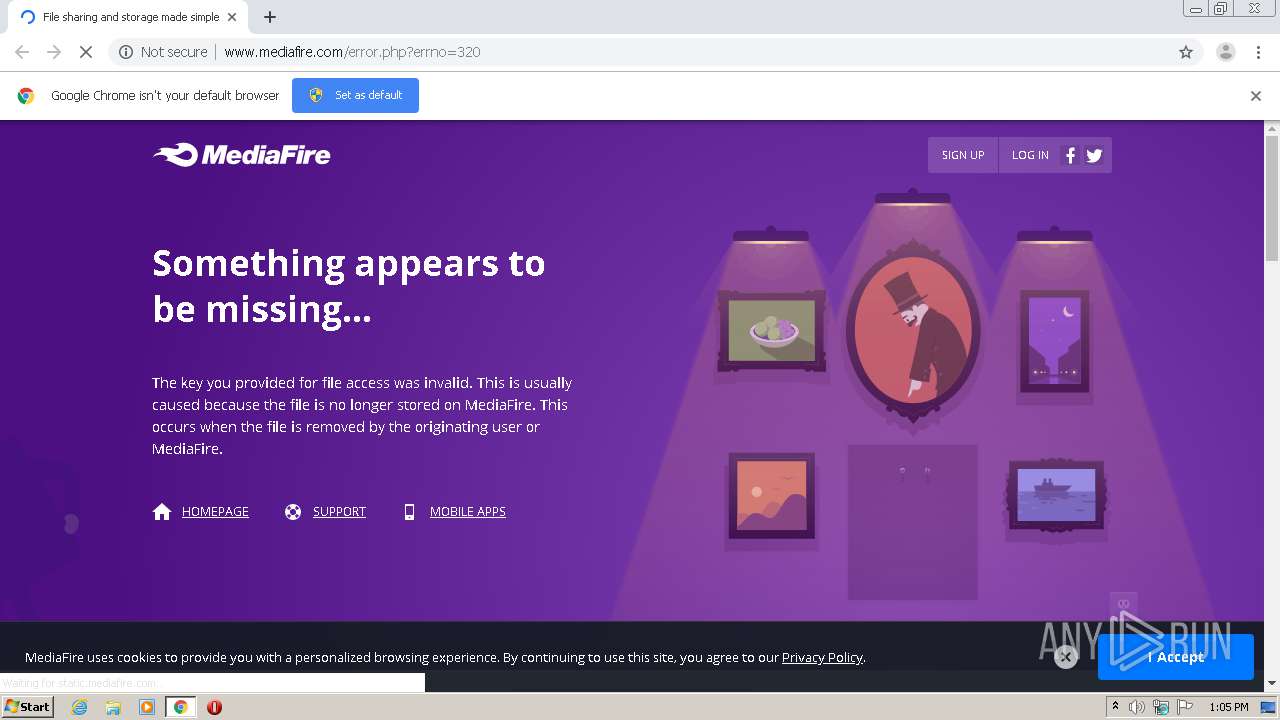
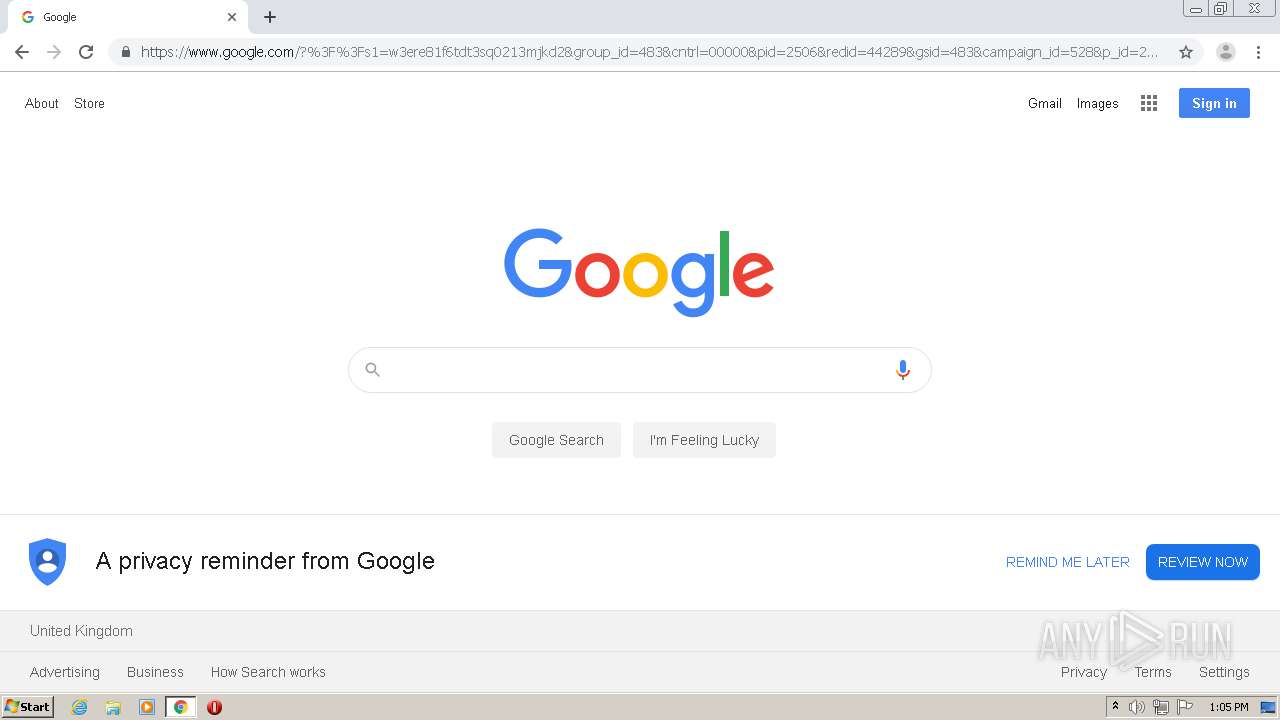
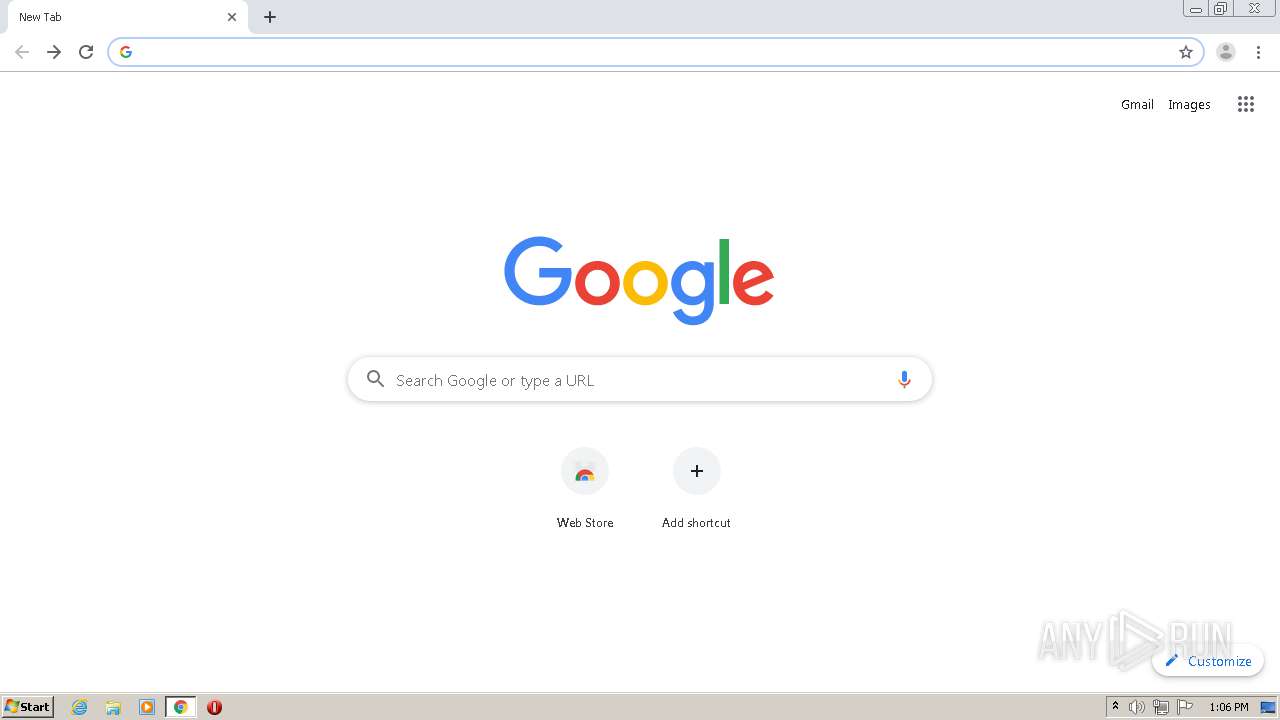
| URL: | http://www.mediafire.com/error.php?errno=320 |
| Full analysis: | https://app.any.run/tasks/085daa72-bf0d-433e-912a-e52f573777b9 |
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2020, 12:05:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A28E15E3CCFB0514BCECA85424987AC2 |
| SHA1: | 515BF829BB34C6EF5DC9CA49E217628C14A67B95 |
| SHA256: | E0E3B6EF7B0A21080BB6650E23F7E715F33059EE9F1FE7BC342979CB9E34E2FD |
| SSDEEP: | 3:N1KJS4w3eGXCcTVn:Cc4w3eGX9n |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
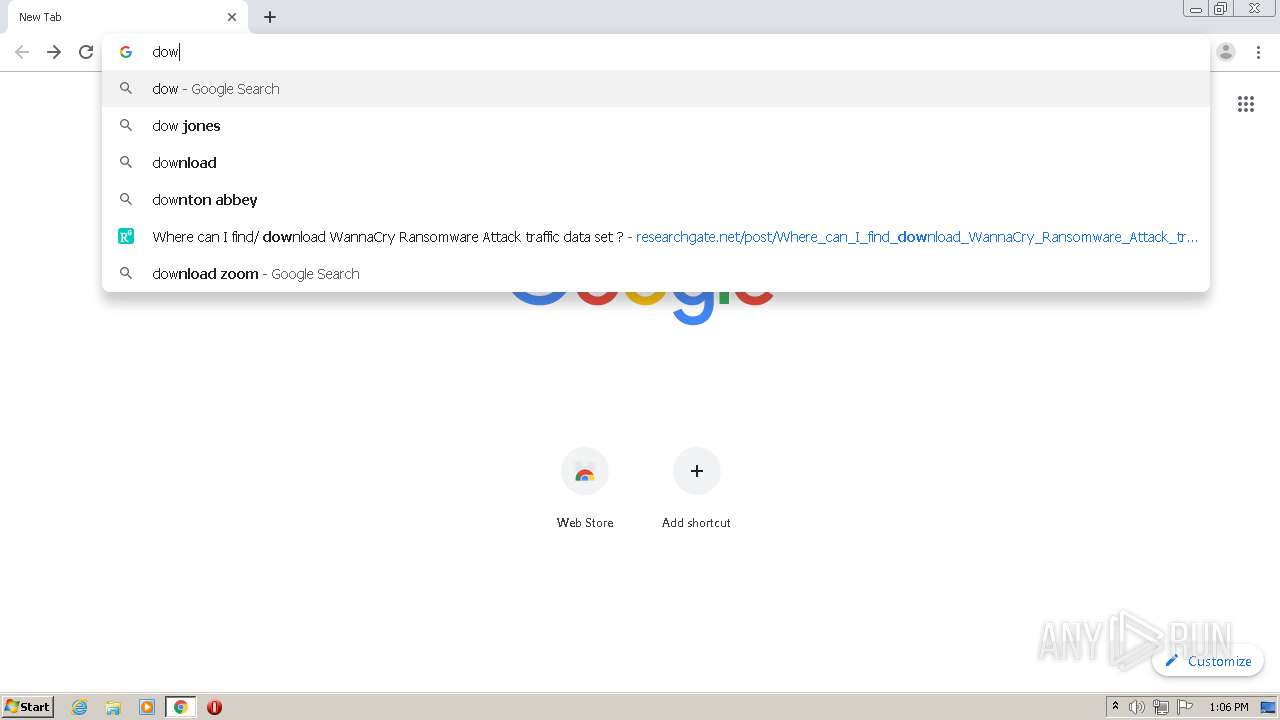
Reads the hosts file
- chrome.exe (PID: 2364)
- chrome.exe (PID: 3972)
Reads settings of System Certificates
- chrome.exe (PID: 3972)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2364)
Application launched itself
- chrome.exe (PID: 2364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
97
Monitored processes
61
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6317358534194004313,2046350406299153199,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4203984193118489446 --renderer-client-id=54 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5772 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6317358534194004313,2046350406299153199,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15899969164115127458 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6317358534194004313,2046350406299153199,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8027981329403338563 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6317358534194004313,2046350406299153199,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10272198290074383882 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6317358534194004313,2046350406299153199,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9117429075315114312 --mojo-platform-channel-handle=2968 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6317358534194004313,2046350406299153199,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6623085772556717722 --renderer-client-id=42 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6317358534194004313,2046350406299153199,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9847251924740096032 --mojo-platform-channel-handle=5784 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6317358534194004313,2046350406299153199,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2808220005869618173 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3632 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6317358534194004313,2046350406299153199,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17239669668296797661 --mojo-platform-channel-handle=4708 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6317358534194004313,2046350406299153199,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9544905187859049449 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2316 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
653
Read events
540
Write events
108
Delete events
5
Modification events
| (PID) Process: | (2364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2364) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2364-13240497927640125 |
Value: 259 | |||
Executable files
0
Suspicious files
157
Text files
130
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\16f08fd7-ea6c-47f1-9e89-dd1950d54205.tmp | — | |
MD5:— | SHA256:— | |||
| 2364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFd69d6.TMP | text | |
MD5:— | SHA256:— | |||
| 2364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFd69e6.TMP | text | |
MD5:— | SHA256:— | |||
| 2364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFd6a34.TMP | text | |
MD5:— | SHA256:— | |||
| 2364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFd69d6.TMP | text | |
MD5:— | SHA256:— | |||
| 2364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
220
DNS requests
152
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3972 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/icons/svg_light/icons_sprite.svg | US | image | 8.11 Kb | shared |
3972 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/css/mfv3_121575.php?ver=nonssl | US | text | 62.5 Kb | shared |
3972 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/css/mfv4_121575.php?ver=nonssl&date=2020-07-29 | US | text | 66.3 Kb | shared |
3972 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/icons/dropdown-arrow-left-white.png | US | image | 123 b | shared |
3972 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/error/feature2.svg | US | image | 1.75 Kb | shared |
3972 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/error/arrows.svg | US | image | 281 b | shared |
3972 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/home_unicorn/gizmodo.svg | US | image | 955 b | shared |
3972 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/error/feature3.svg | US | image | 2.55 Kb | shared |
3972 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/home_unicorn/lifehacker.svg | US | image | 1015 b | shared |
3972 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/home_unicorn/cnet.svg | US | image | 804 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3972 | chrome.exe | 157.240.20.35:443 | www.facebook.com | Facebook, Inc. | US | whitelisted |
3972 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
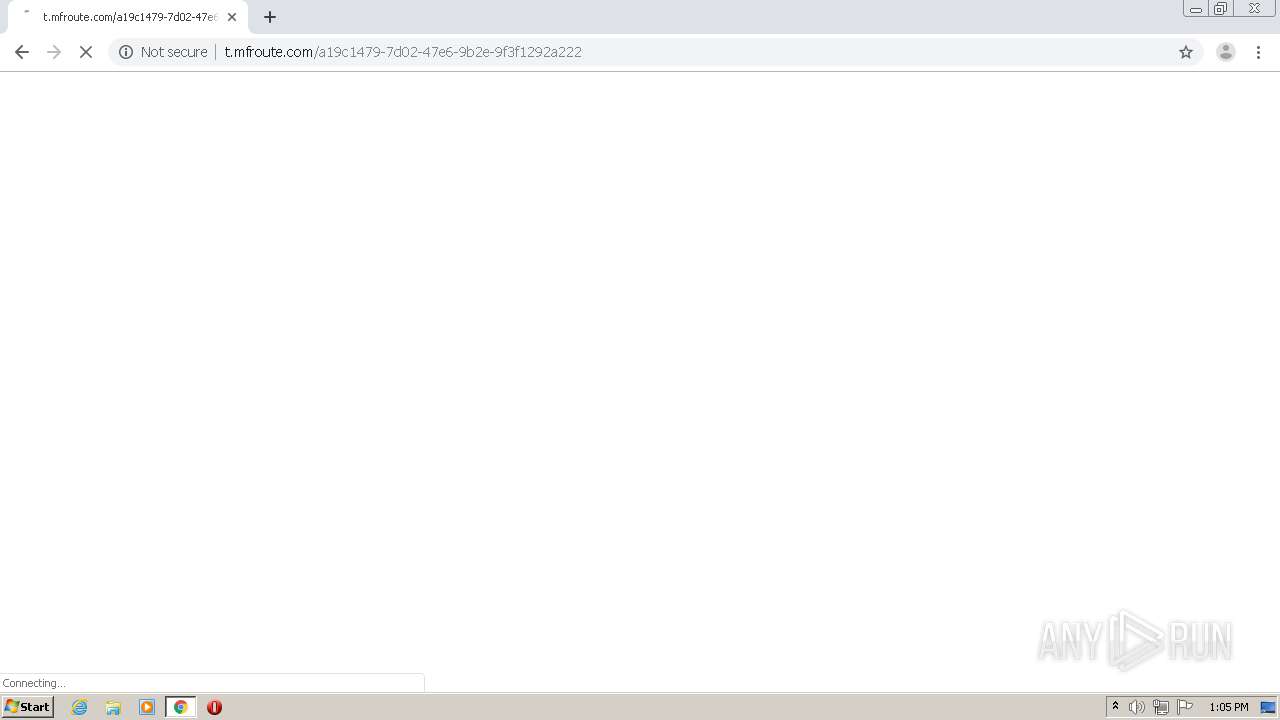
3972 | chrome.exe | 104.16.202.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
3972 | chrome.exe | 104.16.203.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
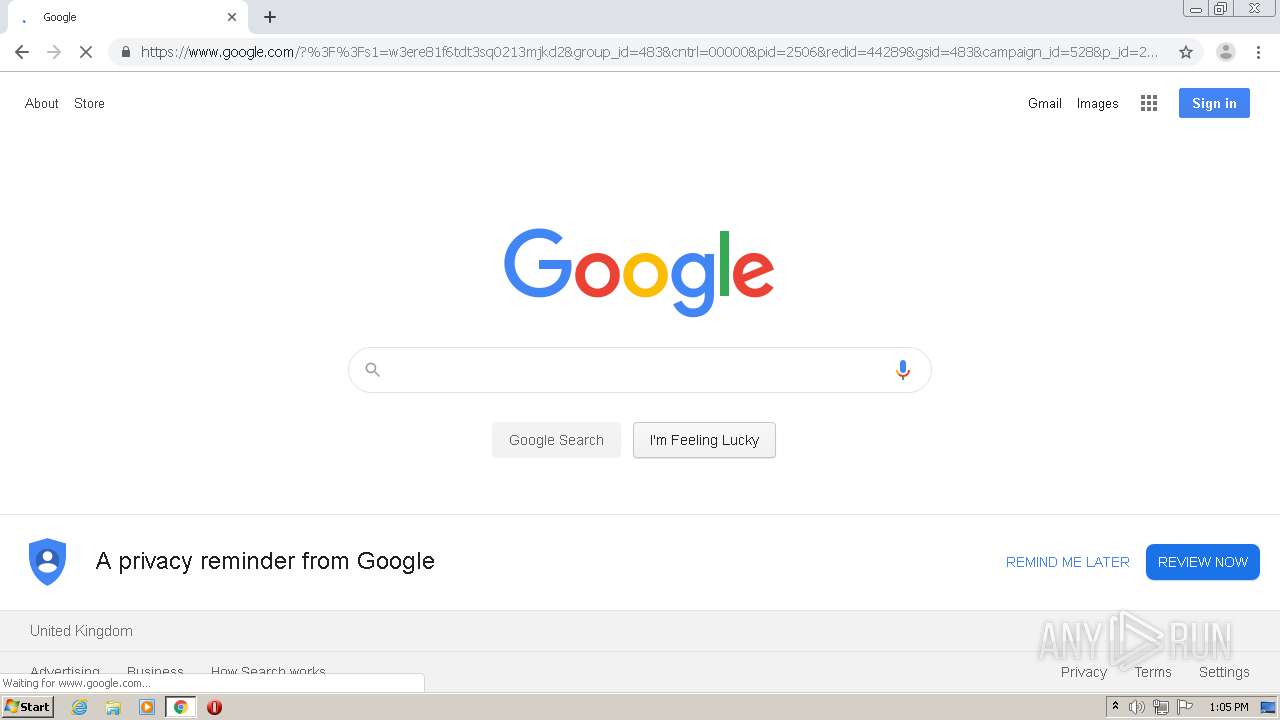
3972 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 172.217.21.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 172.217.23.170:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 172.217.18.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
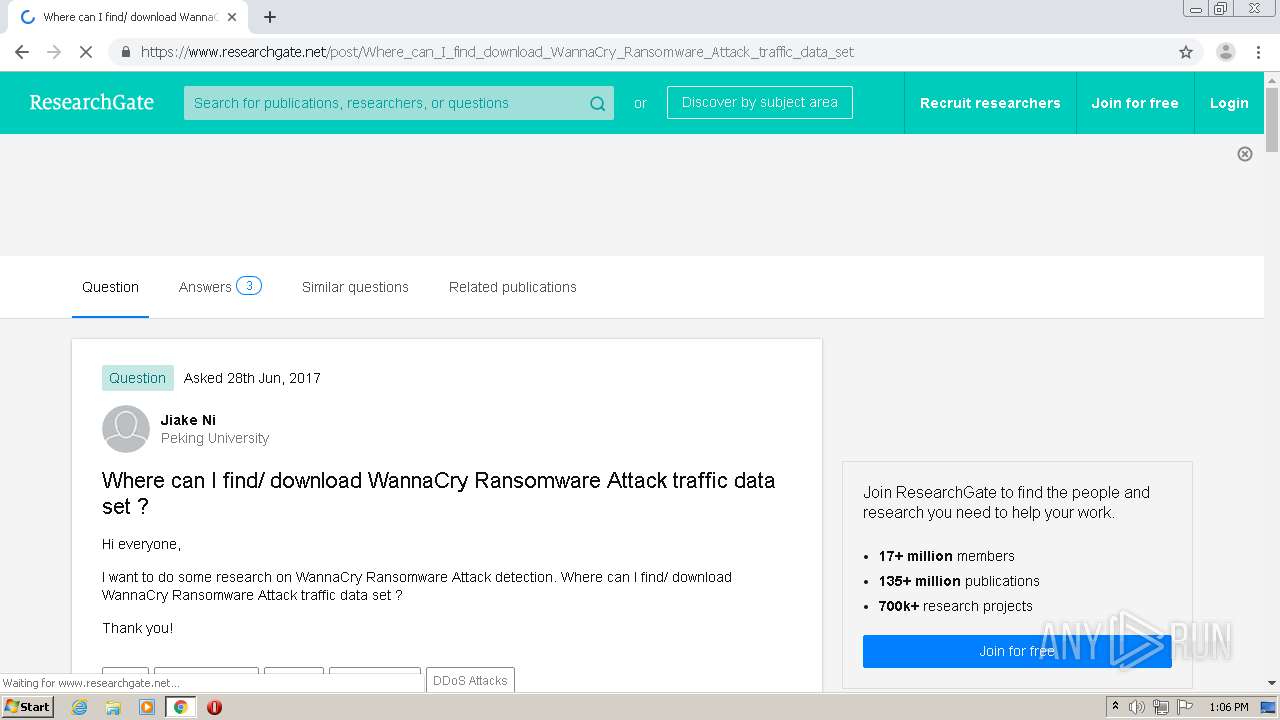
www.mediafire.com |
| shared |
accounts.google.com |
| shared |
static.mediafire.com |
| shared |
fonts.googleapis.com |
| whitelisted |
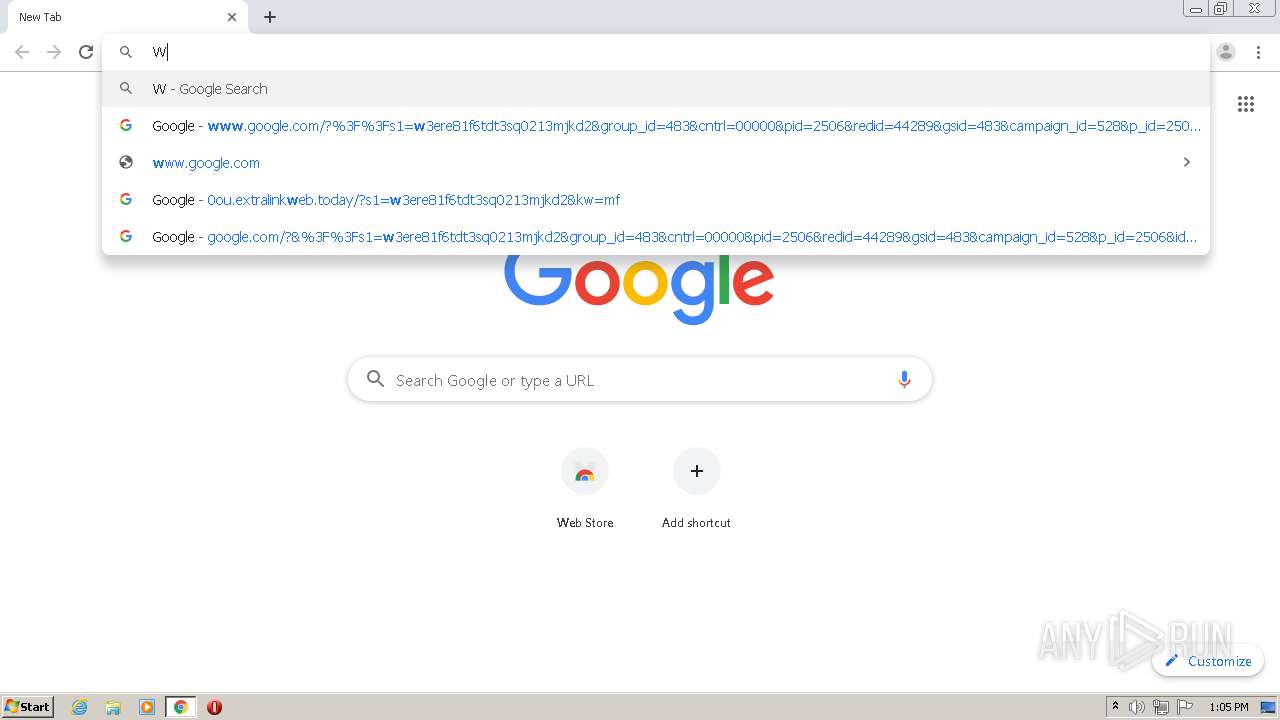
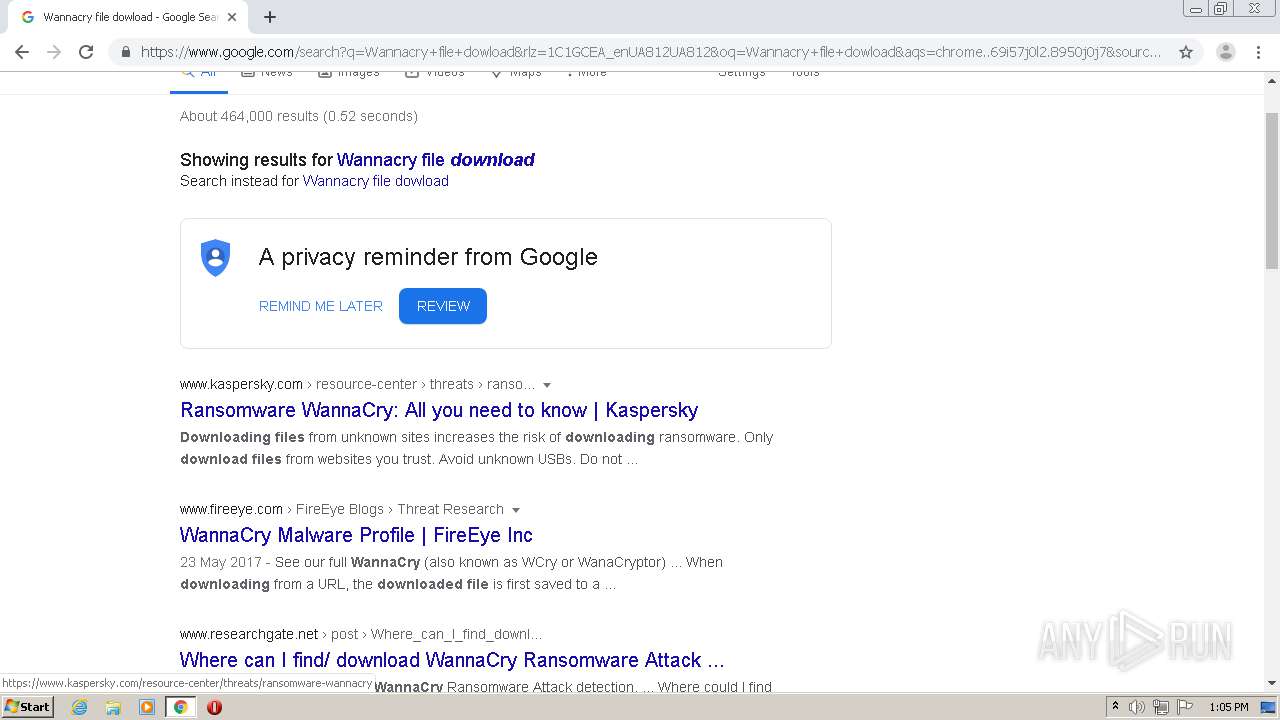
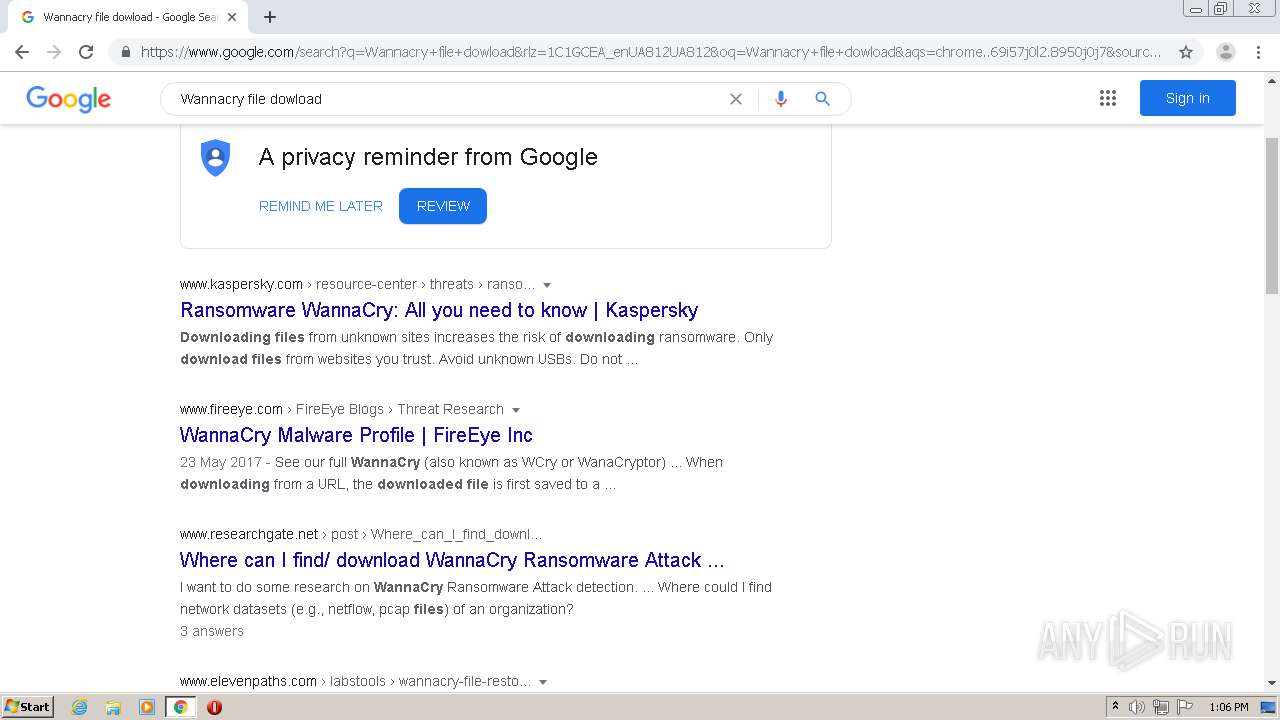
www.google.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3972 | chrome.exe | Misc Attack | ET DROP Dshield Block Listed Source group 1 |
3972 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3972 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |