| File name: | 51【云票】.exe |
| Full analysis: | https://app.any.run/tasks/b3072bca-1418-4eb0-8ad2-e5aa705d048a |
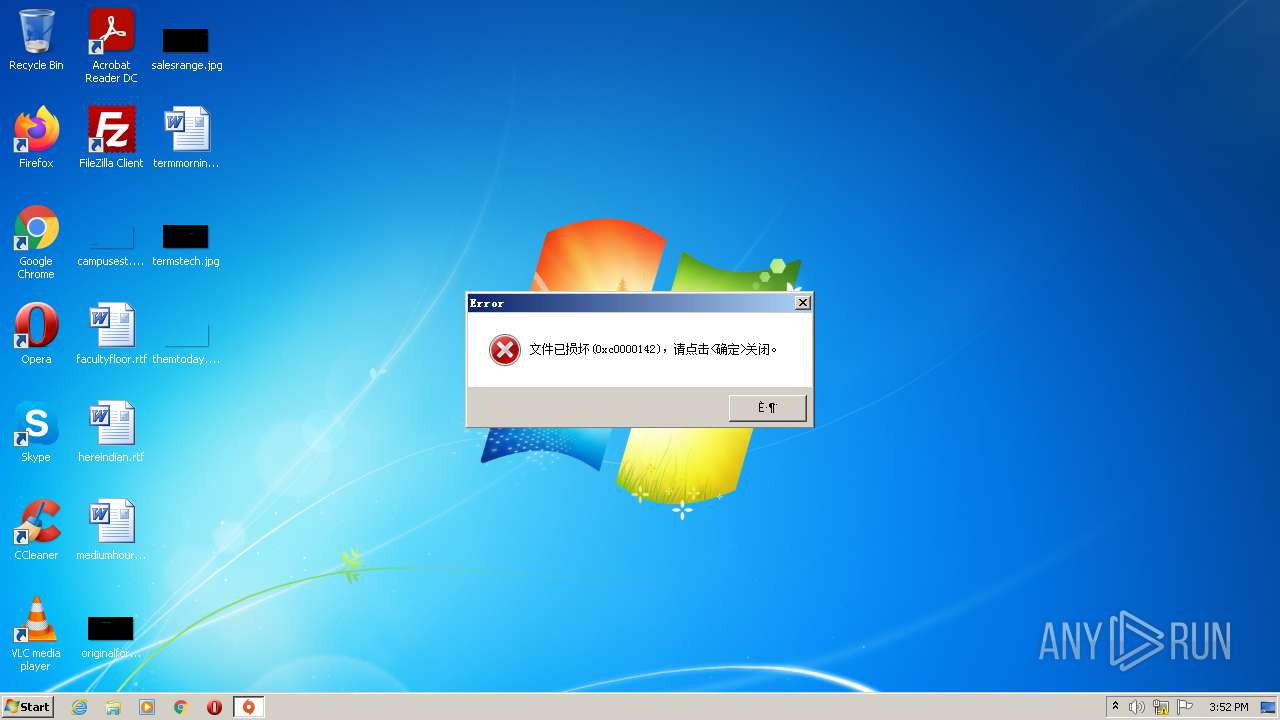
| Verdict: | Malicious activity |
| Analysis date: | November 20, 2021, 15:52:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6733AF0EF7AD1E145115A92688E41454 |
| SHA1: | 77DBDA5BC5A7B5B7DCA48E49392593E49E1183AD |
| SHA256: | E0DFF28F0E921B10DA00F57AB534839EB0E6B27917B7D80D2CFD8197F75F0595 |
| SSDEEP: | 24576:2JgZOLjU/OtYBfTO882FC5/YHJ9nTOVySKRk3Aj/8:lZOLGYIC5K9nT7N/8 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the computer name
- 51????.exe (PID: 2900)
Checks supported languages
- 51????.exe (PID: 2900)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (25.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (22.8) |
| .exe | | | UPX compressed Win32 Executable (22.3) |
| .exe | | | Win32 EXE Yoda's Crypter (21.9) |
| .exe | | | Win32 Executable (generic) (3.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:11:13 10:25:27+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 4222976 |
| InitializedDataSize: | 4222976 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3a6000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 32.43.223.1 |
| ProductVersionNumber: | 32.43.223.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 32.43.223.1 |
| FileDescription: | Gert-Jan Weerheime |
| ProductName: | SyncFoldersh |
| ProductVersion: | 32.43.223.1 |
| CompanyName: | gg |
| LegalCopyright: | ee |
| Comments: | SyncFoldersh |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Nov-2021 09:25:27 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 13-Nov-2021 09:25:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000991FA | 0x00052000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.96014 |
.rdata | 0x0009B000 | 0x00026036 | 0x00027000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.16661 |
.data | 0x000C2000 | 0x00021B28 | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.59635 |
.rsrc | 0x000E4000 | 0x002C2000 | 0x0008D000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.94903 |
.perplex5\x12\x06 | 0x003A6000 | 0x00061235 | 0x00061235 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97895 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 7.96803 | 158989 | UNKNOWN | UNKNOWN | RAR |
1 | 0 | 1758 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.35307 | 744 | UNKNOWN | English - Canada | RT_ICON |
3 | 2.72043 | 488 | UNKNOWN | English - Canada | RT_ICON |
4 | 2.94751 | 296 | UNKNOWN | English - Canada | RT_ICON |
5 | 3.1366 | 3752 | UNKNOWN | English - Canada | RT_ICON |
6 | 2.87529 | 2216 | UNKNOWN | English - Canada | RT_ICON |
7 | 2.58876 | 1736 | UNKNOWN | English - Canada | RT_ICON |
8 | 1.93048 | 1384 | UNKNOWN | English - Canada | RT_ICON |
9 | 3.27466 | 270376 | UNKNOWN | English - Canada | RT_ICON |
Imports
KERNEL32.DLL |
USER32.DLL |
Total processes
35
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2900 | "C:\Users\admin\AppData\Local\Temp\51????.exe" | C:\Users\admin\AppData\Local\Temp\51????.exe | Explorer.EXE | ||||||||||||
User: admin Company: gg Integrity Level: MEDIUM Description: Gert-Jan Weerheime Exit code: 0 Version: 32.43.223.1 Modules
| |||||||||||||||
Total events
334
Read events
314
Write events
20
Delete events
0
Modification events
| (PID) Process: | (2900) 51????.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2900) 51????.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2900) 51????.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2900) 51????.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2900) 51????.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2900) 51????.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2900) 51????.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2900) 51????.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2900) 51????.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2900) 51????.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2900 | 51????.exe | GET | — | 212.95.139.72:80 | http://sdghdcvgsqrd.vip/facai13/ | IR | — | — | unknown |
2900 | 51????.exe | POST | — | 212.95.139.72:80 | http://sdghdcvgsqrd.vip/facai13/index.php?c=post | IR | — | — | unknown |
2900 | 51????.exe | GET | 200 | 162.14.132.226:80 | http://pv.sohu.com/cityjson?ie=gb2312 | US | text | 76 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2900 | 51????.exe | 212.95.139.72:80 | sdghdcvgsqrd.vip | Hesabgar Pardaz Gharb Company (Private Joint Stock) | IR | unknown |
2900 | 51????.exe | 162.14.132.226:80 | pv.sohu.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pv.sohu.com |
| malicious |
sdghdcvgsqrd.vip |
| unknown |
Threats
2 ETPRO signatures available at the full report