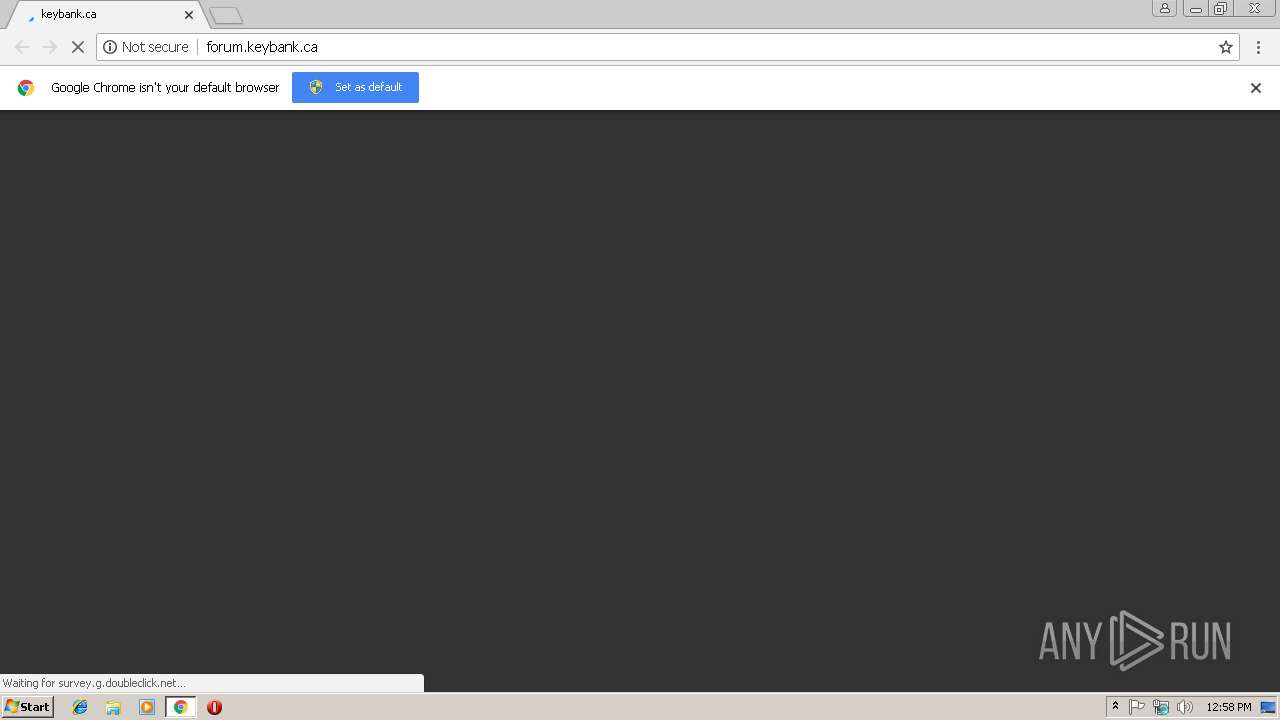
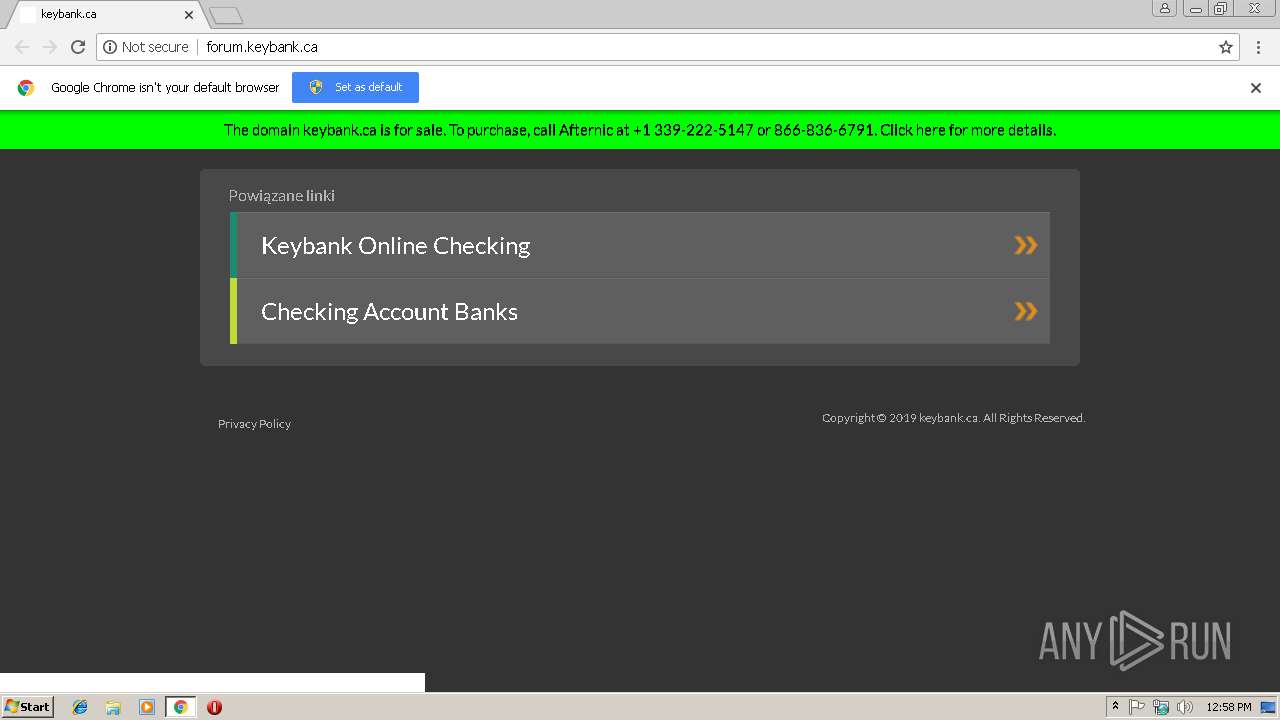
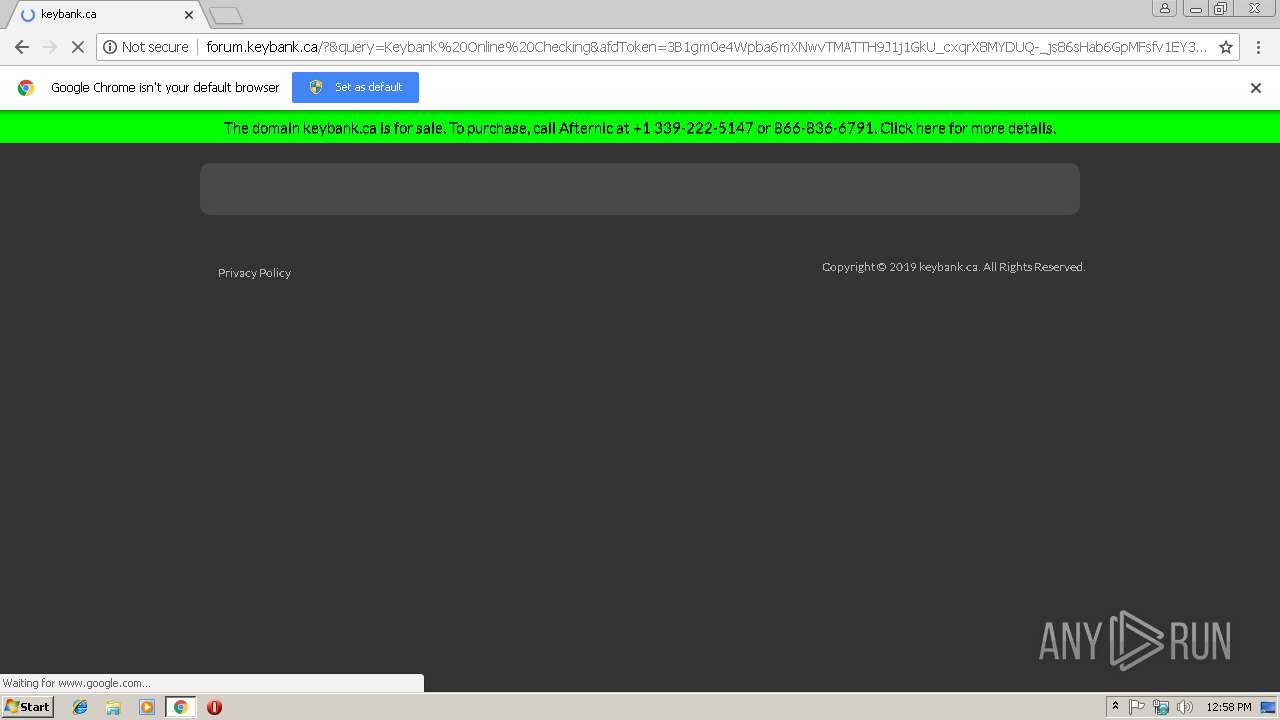
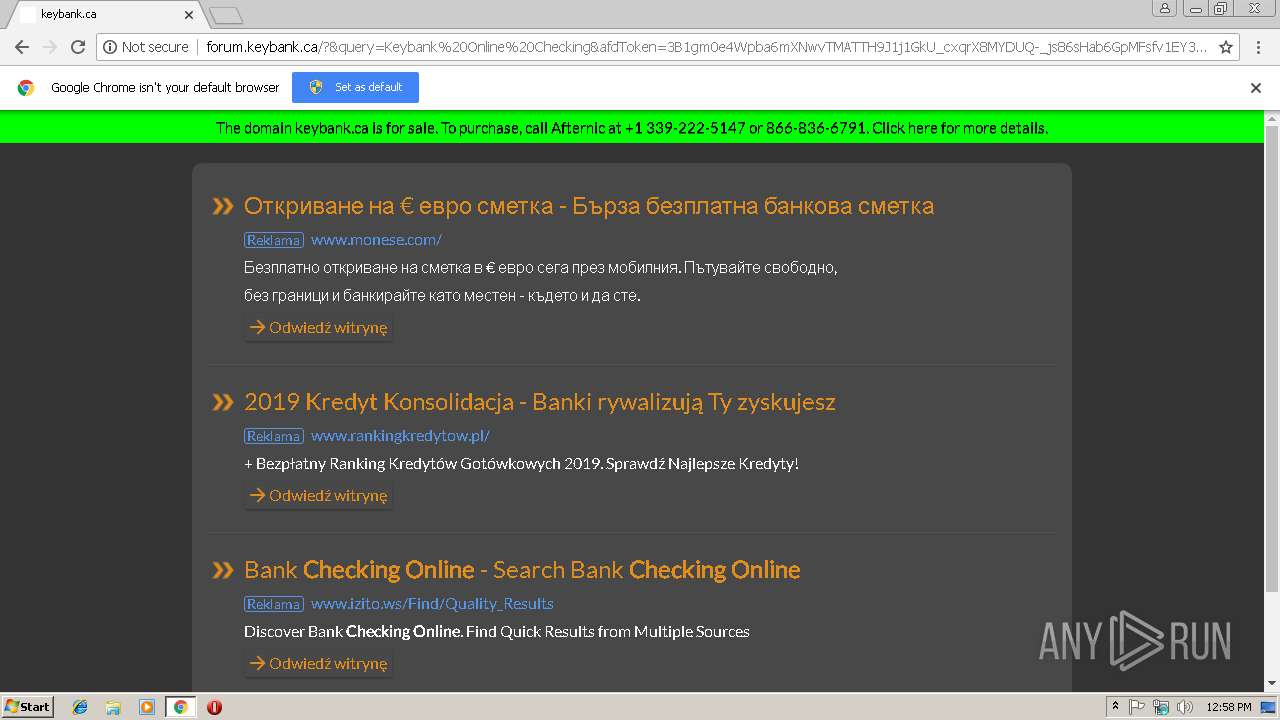
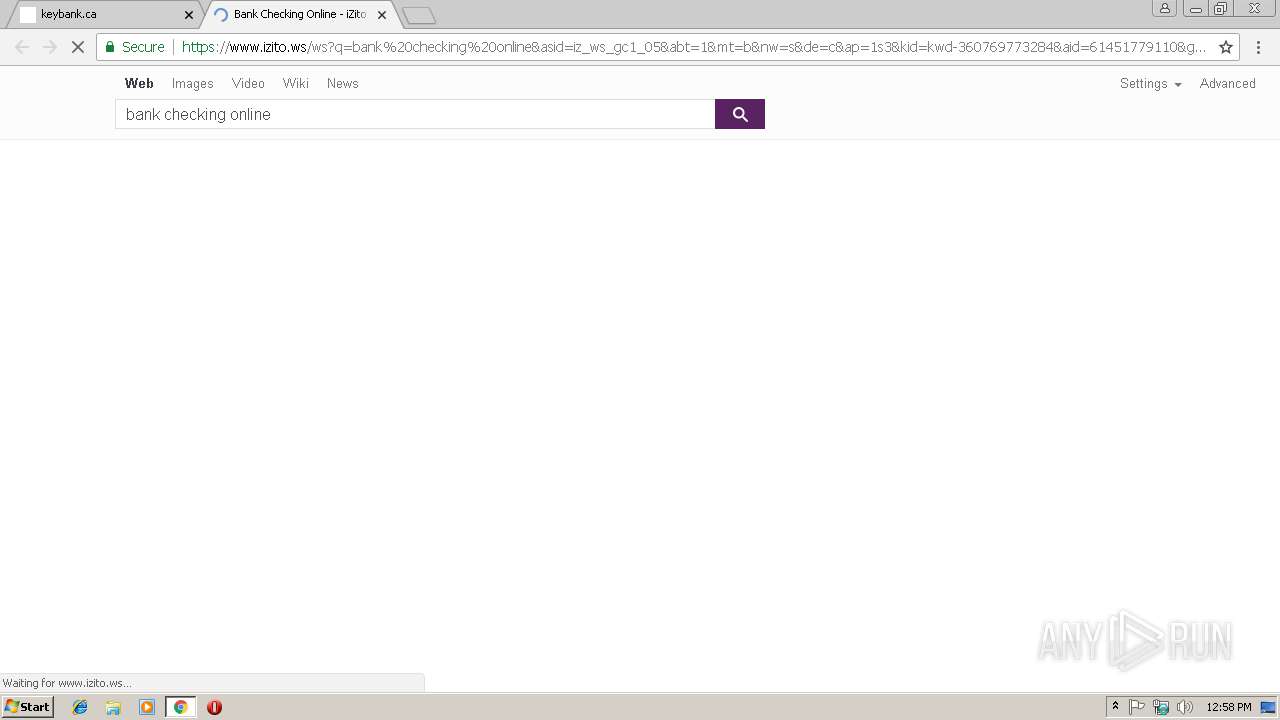
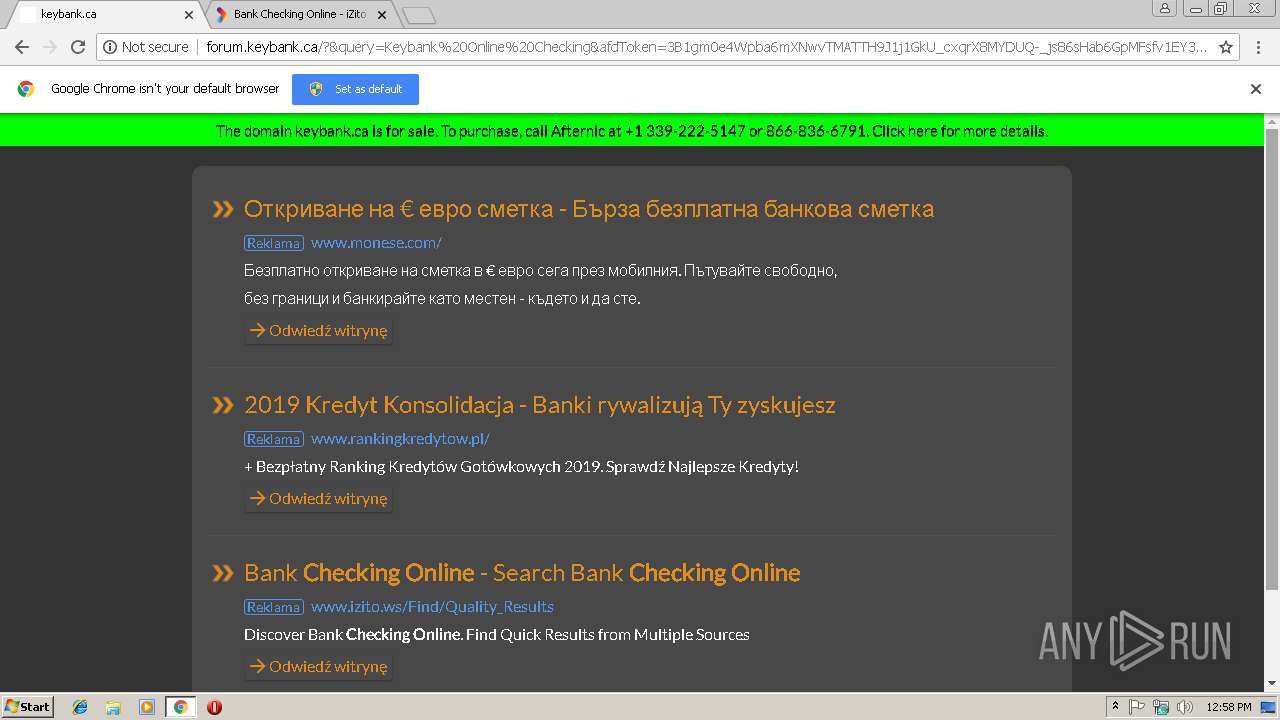
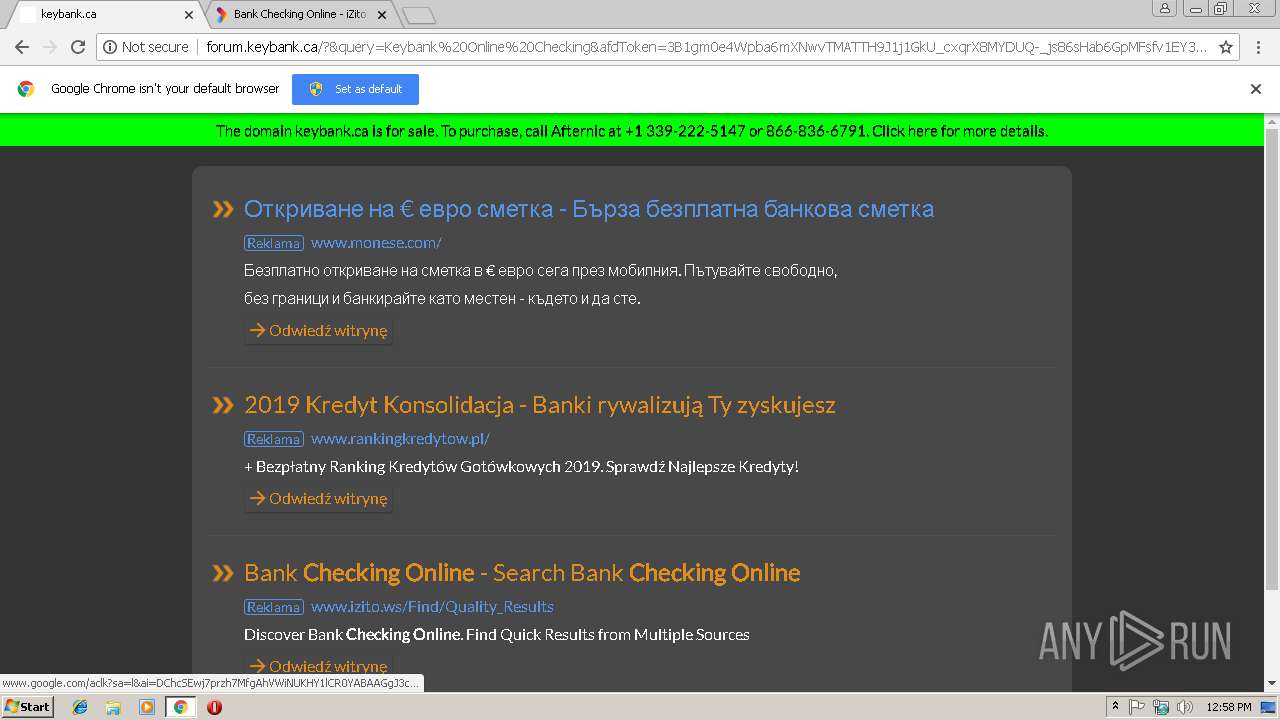
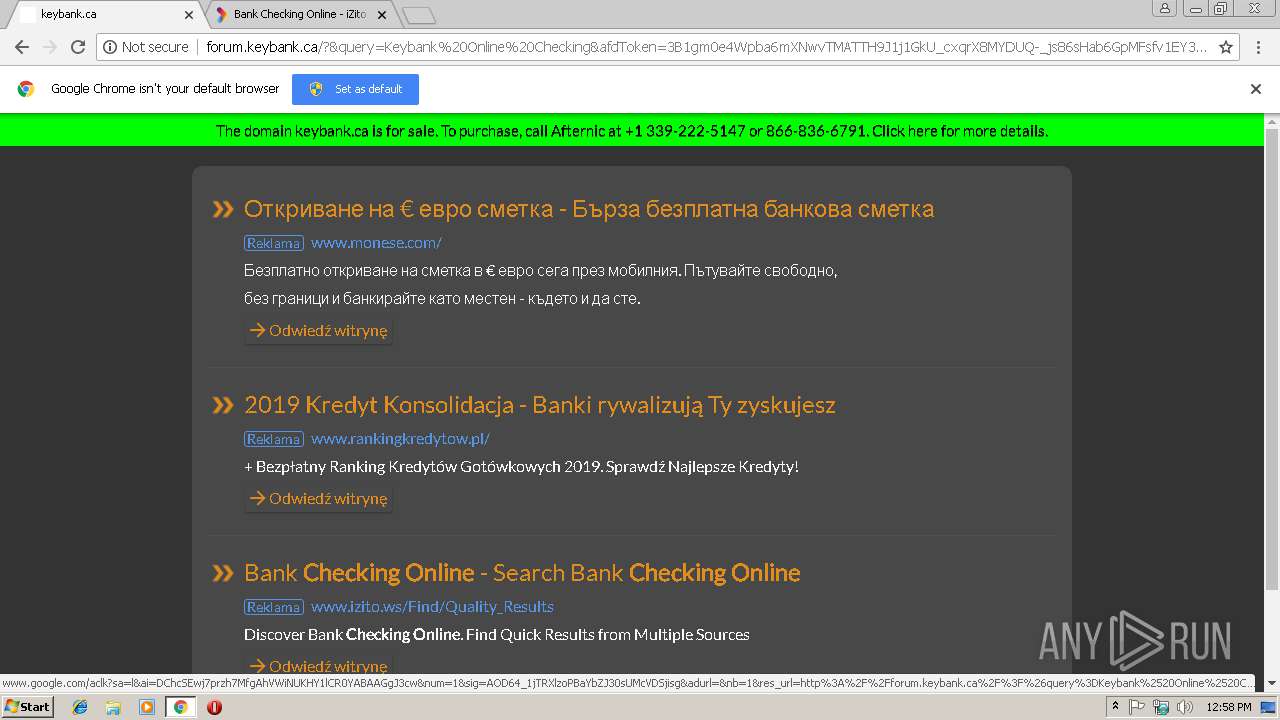
| URL: | http://forum.keybank.ca |
| Full analysis: | https://app.any.run/tasks/422bad97-615d-40a5-9b14-3b74b7828ae2 |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2019, 12:57:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4756A775D99FAE9D42396396451C316B |
| SHA1: | 5A0B94DFA28B5276DA2E64F07AF72284179993BD |
| SHA256: | E0DD7EF35C446CA7D5CA85E3A34A55E4C0C60B36A90A47BDC9B892EE01411BAC |
| SSDEEP: | 3:N1KYnA2p:CYnA2p |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2968)
Reads settings of System Certificates
- chrome.exe (PID: 2968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,6446415706175171745,7615301987602728214,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=9BE182491F94DB8DE1B2BE36D5A59A8A --mojo-platform-channel-handle=3720 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,6446415706175171745,7615301987602728214,131072 --enable-features=PasswordImport --service-pipe-token=51ED6FA61BDC52E740339FBF3FD5FF58 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=51ED6FA61BDC52E740339FBF3FD5FF58 --renderer-client-id=4 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2972 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://forum.keybank.ca | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,6446415706175171745,7615301987602728214,131072 --enable-features=PasswordImport --service-pipe-token=5D826C859948FCEEE2E98292722194D3 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5D826C859948FCEEE2E98292722194D3 --renderer-client-id=3 --mojo-platform-channel-handle=2076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f6000b0,0x6f6000c0,0x6f6000cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,6446415706175171745,7615301987602728214,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=D2D089AB33EEFB2B5442DED154E35414 --mojo-platform-channel-handle=2388 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 4036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,6446415706175171745,7615301987602728214,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=8A06F70D374E981BF1B0C8A1342079BF --mojo-platform-channel-handle=964 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
504
Read events
460
Write events
41
Delete events
3
Modification events
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2968-13195054702488625 |
Value: 259 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2968-13195054702488625 |
Value: 259 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
37
Text files
66
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0f2c684b-8e34-432f-9077-1e78f9277841.tmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\757d8765-3c04-4143-83a2-383c43e4204d.tmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF19990a.TMP | text | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
88
DNS requests
51
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
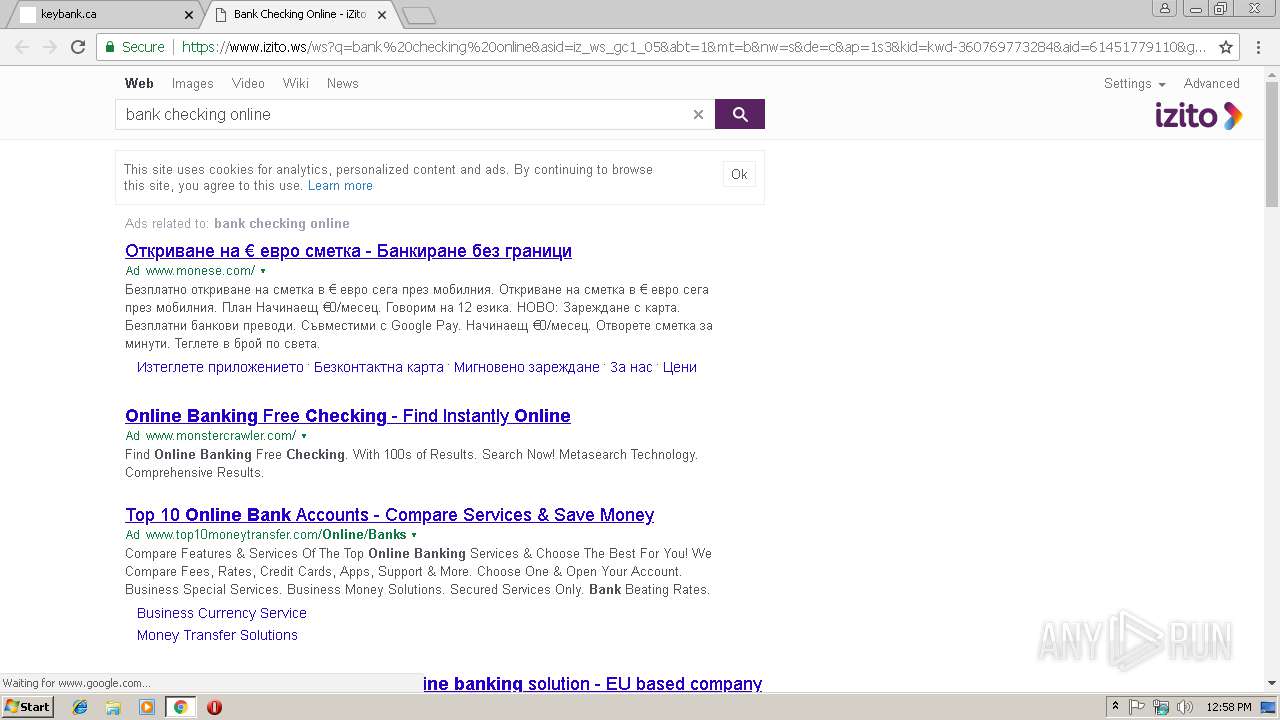
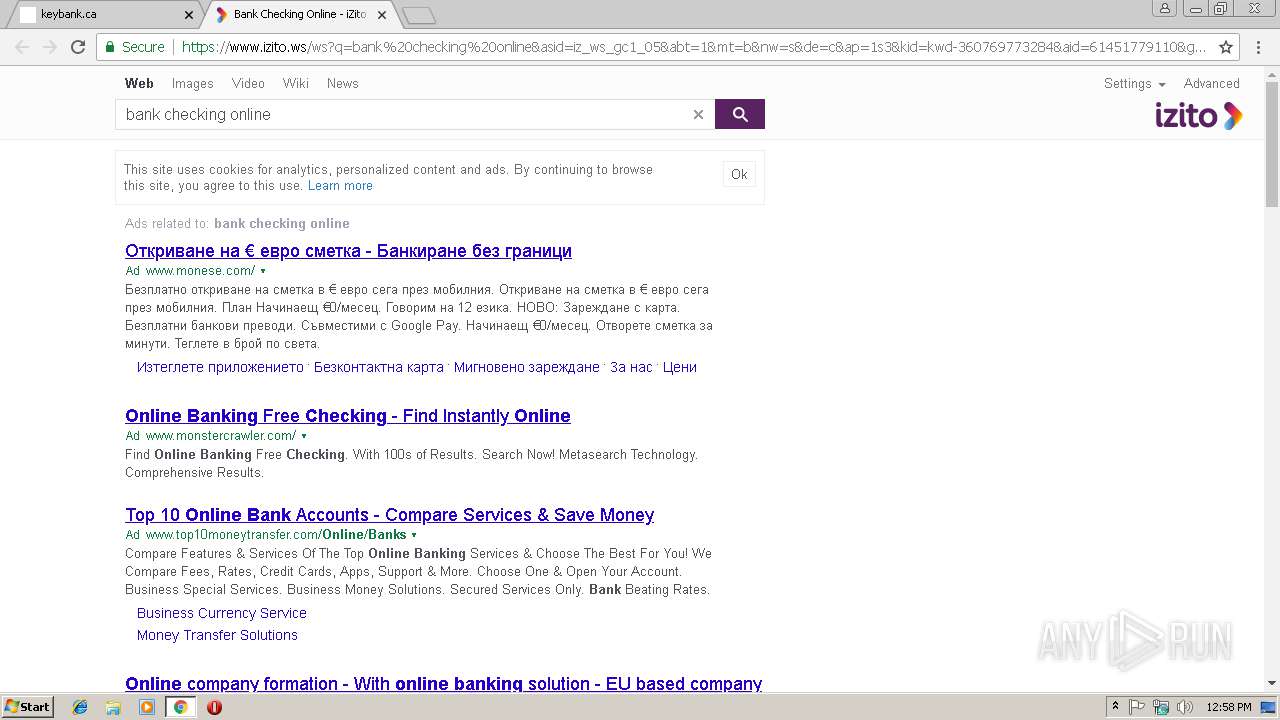
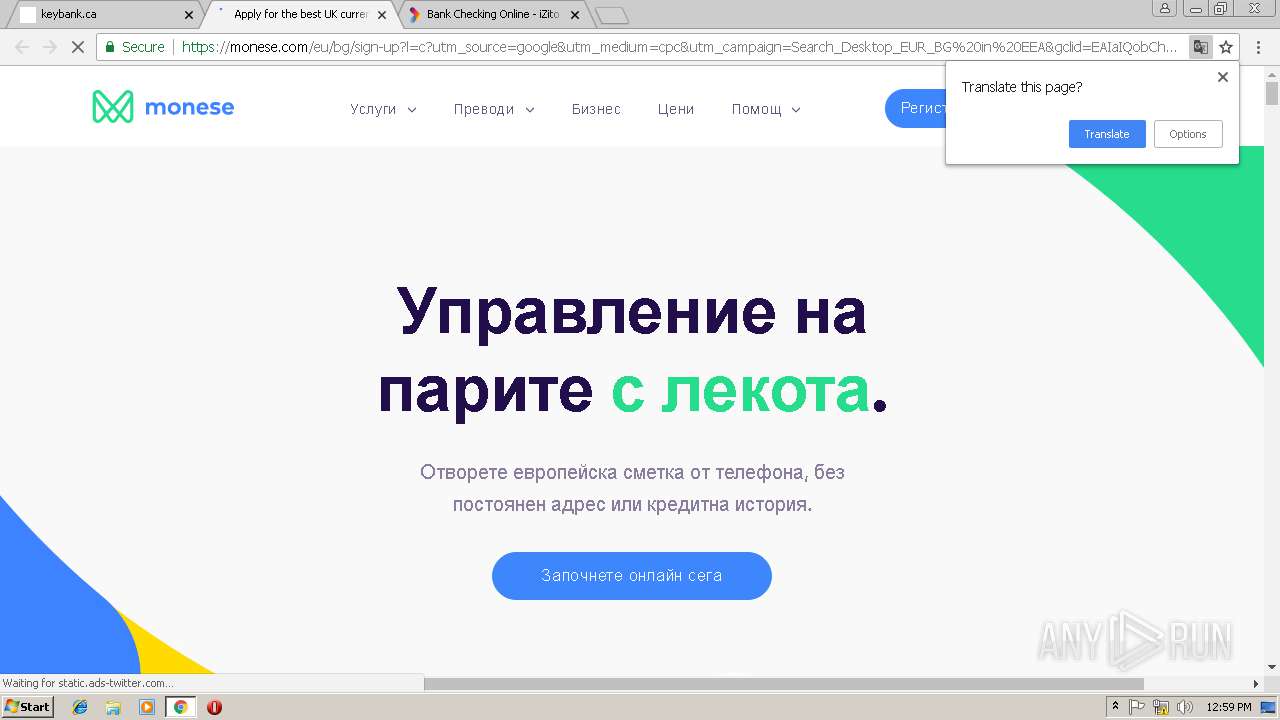
2968 | chrome.exe | GET | 200 | 172.217.23.164:80 | http://www.google.com/adsense/domains/caf.js | US | text | 55.4 Kb | malicious |
2968 | chrome.exe | GET | 200 | 184.168.221.104:80 | http://forum.keybank.ca/ | US | html | 5.67 Kb | malicious |
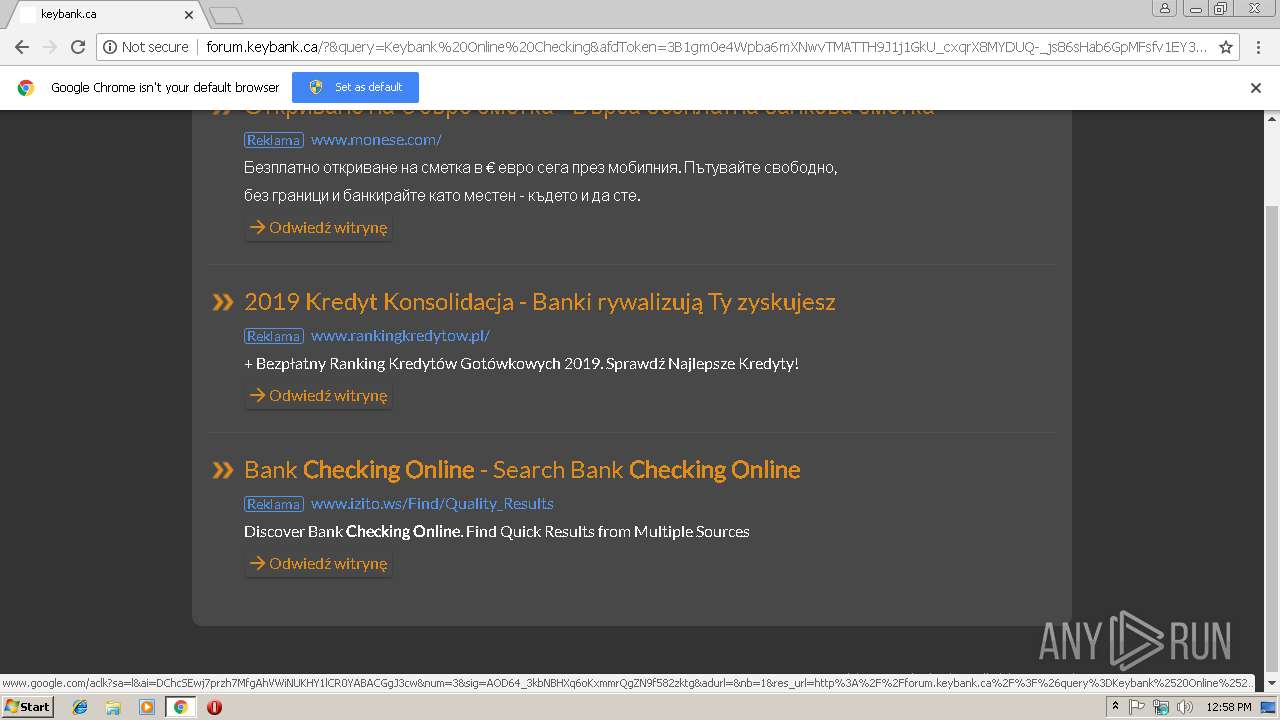
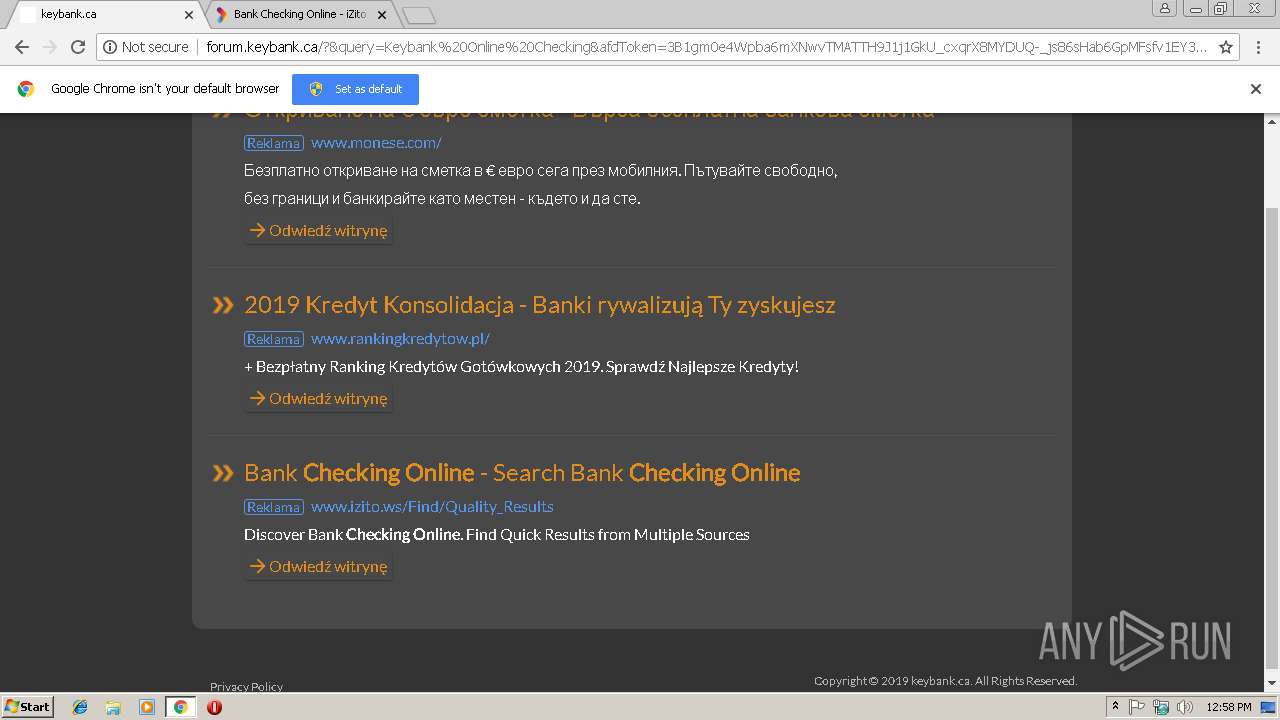
2968 | chrome.exe | GET | 200 | 184.168.221.104:80 | http://forum.keybank.ca/?&query=Keybank%20Online%20Checking&afdToken=3B1gm0e4Wpba6mXNwvTMATTH9J1j1GkU_cxqrX8MYDUQ-_js86sHab6GpMFsfv1EY3KsiVAgXjLlx8ECxs9eIwqCwHIYFfyVffp4-I6EUGw&pcsa=false | US | html | 6.51 Kb | malicious |
2968 | chrome.exe | GET | 200 | 172.217.16.145:80 | http://survey.g.doubleclick.net/insights/consumersurveys/static/416122968644848560/prompt_embed_static.js | US | text | 131 Kb | whitelisted |
2968 | chrome.exe | GET | 200 | 172.217.16.145:80 | http://survey.g.doubleclick.net/async_survey?site=kv4ic6olrzkr6 | US | text | 17.6 Kb | whitelisted |
2968 | chrome.exe | GET | 200 | 216.58.205.225:80 | http://afs.googleusercontent.com/dp-namemedia/bullet-arrows-orange.png | US | image | 564 b | whitelisted |
2968 | chrome.exe | GET | 200 | 172.217.23.164:80 | http://www.google.com/afs/ads/i/iframe.html | US | html | 601 b | malicious |
2968 | chrome.exe | GET | 200 | 172.217.23.164:80 | http://www.google.com/dp/ads?r=m&domain_name=keybank.ca&client=dp-namemedia01&channel=undefined&adtest=off&adsafe=low&type=3&pcsa=false&swp=as-drid-2490750057351877&oe=UTF-8&ie=UTF-8&fexp=21404%2C17300002&format=r6&num=0&output=afd_ads&v=3&adext=as1%2Csr1&bsl=8&u_his=1&u_tz=0&dt=1550581105445&u_w=1280&u_h=720&biw=1280&bih=582&psw=-1&psh=-1&frm=0&uio=st24sa11lt40sl1sr1-&jsv=80731&rurl=http%3A%2F%2Fforum.keybank.ca%2F | US | html | 6.10 Kb | malicious |
2968 | chrome.exe | GET | 200 | 172.217.23.164:80 | http://www.google.com/dp/ads?r=m&domain_name=keybank.ca&client=dp-namemedia01&channel=undefined&adtest=off&adsafe=low&type=0&pcsa=false&swp=as-drid-2490750057351877&q=Keybank%20Online%20Checking&afdt=3B1gm0e4Wpba6mXNwvTMATTH9J1j1GkU_cxqrX8MYDUQ-_js86sHab6GpMFsfv1EY3KsiVAgXjLlx8ECxs9eIwqCwHIYFfyVffp4-I6EUGw&oe=UTF-8&ie=UTF-8&fexp=21404%2C17300002&format=n3%7Cr0&ad=n3&num=0&output=afd_ads&v=3&adext=as1%2Csr1&bsl=8&u_his=2&u_tz=0&dt=1550581108465&u_w=1280&u_h=720&biw=1280&bih=582&psw=-1&psh=-1&frm=0&uio=sl1sr1-af3st24sd16sv16sa10lt40ld28lv28-st13sa11lt15&jsv=80731&rurl=http%3A%2F%2Fforum.keybank.ca%2F%3F%26query%3DKeybank%2520Online%2520Checking%26afdToken%3D3B1gm0e4Wpba6mXNwvTMATTH9J1j1GkU_cxqrX8MYDUQ-_js86sHab6GpMFsfv1EY3KsiVAgXjLlx8ECxs9eIwqCwHIYFfyVffp4-I6EUGw%26pcsa%3Dfalse&referer=http%3A%2F%2Fwww.google.com%2F | US | html | 6.98 Kb | malicious |
2968 | chrome.exe | GET | 200 | 216.58.205.238:80 | http://www.google-analytics.com/__utm.gif?utmwv=5.7.2&utms=2&utmn=739421248&utmhn=forum.keybank.ca&utmt=event&utme=5(lander_page*page_visit*Simple2C)&utmcs=UTF-8&utmsr=1280x720&utmvp=1280x582&utmsc=24-bit&utmul=en-us&utmje=0&utmfl=-&utmdt=keybank.ca&utmhid=1412269996&utmr=-&utmp=%2F&utmht=1550581105843&utmac=UA-2201473-4&utmcc=__utma%3D92487434.1779871999.1550581106.1550581106.1550581106.1%3B%2B__utmz%3D92487434.1550581106.1.1.utmcsr%3D(direct)%7Cutmccn%3D(direct)%7Cutmcmd%3D(none)%3B&utmjid=&utmu=6AAAAAAAAAAAAAAAAAAAAAAE~ | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2968 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 172.217.18.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 184.168.221.104:80 | forum.keybank.ca | GoDaddy.com, LLC | US | malicious |
2968 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2968 | chrome.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 172.217.23.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 172.217.18.163:80 | www.gstatic.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 172.217.16.145:80 | survey.g.doubleclick.net | Google Inc. | US | unknown |
2968 | chrome.exe | 172.217.21.226:443 | adservice.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
forum.keybank.ca |
| malicious |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
d24cze5sab2jwg.cloudfront.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
survey.g.doubleclick.net |
| whitelisted |