| URL: | https://www.bing.com/ck/a?!&&p=19fa11608cfad754c940c5d248a9a4bc596a505d88cf477aa14b165ddd091b4dJmltdHM9MTY1MDg1NjkzMCZpZ3VpZD04ODM3OTkzMy1mZTQzLTQ1MWItYWJmMy0yNzdjYzM5YjY1MTAmaW5zaWQ9NTE3OQ&ptn=3&fclid=e435bbd6-c446-11ec-ad15-1dd86f9ce96d&u=a1aHR0cHM6Ly93d3cuYWxkZWlkLmNvbS93aWtpL1B5dGhvbi1vbGV0b29scy9vbGV2YmE_bXNjbGtpZD1lNDM1YmJkNmM0NDYxMWVjYWQxNTFkZDg2ZjljZTk2ZA&ntb=1 |
| Full analysis: | https://app.any.run/tasks/4bf83c49-f790-4cac-83b0-0a15d36c0a07 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2022, 03:22:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2B3A6BCA385324CC68790866975F7A21 |
| SHA1: | D2D5980A0A5CB77A405954470250D3E07288FC19 |
| SHA256: | E0DC47BE0D4F787E76EDD655CDB5DFA72B1C3C168ABA4E7221E2BE6BA49C9DFF |
| SSDEEP: | 6:2OLsR0ZPHpJ/9wBv0K/Ve4jShWp5hSxyvVNoeM/TIrfwT7cTC7eRUYhpmOm47:2QHQ0AmhaDCyvLAE7wT7c3XVmc |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 948)
INFO
Checks supported languages
- iexplore.exe (PID: 3040)
- iexplore.exe (PID: 948)
Reads the computer name
- iexplore.exe (PID: 3040)
- iexplore.exe (PID: 948)
Application launched itself
- iexplore.exe (PID: 3040)
Reads settings of System Certificates
- iexplore.exe (PID: 3040)
- iexplore.exe (PID: 948)
Checks Windows Trust Settings
- iexplore.exe (PID: 3040)
- iexplore.exe (PID: 948)
Reads internet explorer settings
- iexplore.exe (PID: 948)
Creates files in the user directory
- iexplore.exe (PID: 3040)
- iexplore.exe (PID: 948)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 948)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3040)
Changes settings of System certificates
- iexplore.exe (PID: 3040)
Changes internet zones settings
- iexplore.exe (PID: 3040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 948 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3040 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3040 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.bing.com/ck/a?!&&p=19fa11608cfad754c940c5d248a9a4bc596a505d88cf477aa14b165ddd091b4dJmltdHM9MTY1MDg1NjkzMCZpZ3VpZD04ODM3OTkzMy1mZTQzLTQ1MWItYWJmMy0yNzdjYzM5YjY1MTAmaW5zaWQ9NTE3OQ&ptn=3&fclid=e435bbd6-c446-11ec-ad15-1dd86f9ce96d&u=a1aHR0cHM6Ly93d3cuYWxkZWlkLmNvbS93aWtpL1B5dGhvbi1vbGV0b29scy9vbGV2YmE_bXNjbGtpZD1lNDM1YmJkNmM0NDYxMWVjYWQxNTFkZDg2ZjljZTk2ZA&ntb=1" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
16 037
Read events
15 891
Write events
144
Delete events
2
Modification events
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30955603 | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30955603 | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
15
Text files
39
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:201F5896490DD914600A243BF8F09864 | SHA256:6B38489663DD10F27DED7AF48C691CBAD4CA41FAFF7A01A346B34144477DD279 | |||
| 3040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:24B8937931252B8C5CBD574E86EFE1EE | SHA256:AC7BB612D4C7BC9D85E3288FD7BE1FBE09ABB5C6467D1B8FC7B10F5622A0ED5C | |||
| 3040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\favicon[3].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\imagestore\f7ruq93\imagestore.dat | binary | |
MD5:C594C601A465ED590712F76416121894 | SHA256:6DB02F43C84C514545DA846A04FB2025EC8E1A2EF274771C6972F2C36FFD2054 | |||
| 948 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\a[1].htm | html | |
MD5:7F290ED9770C14553D6089A6F266A6CC | SHA256:E2CA0F721A10FF14789F5FC533CEF557BCEF171D6A2047A59A2ABB558C59D3A5 | |||
| 948 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\load[1].css | text | |
MD5:AFF65788C5D0A45E3AD37E8E95A42D65 | SHA256:D43626DB3FF712B2D9011022F358F8980D1A85177470FA7CE667EC32DC17F3CF | |||
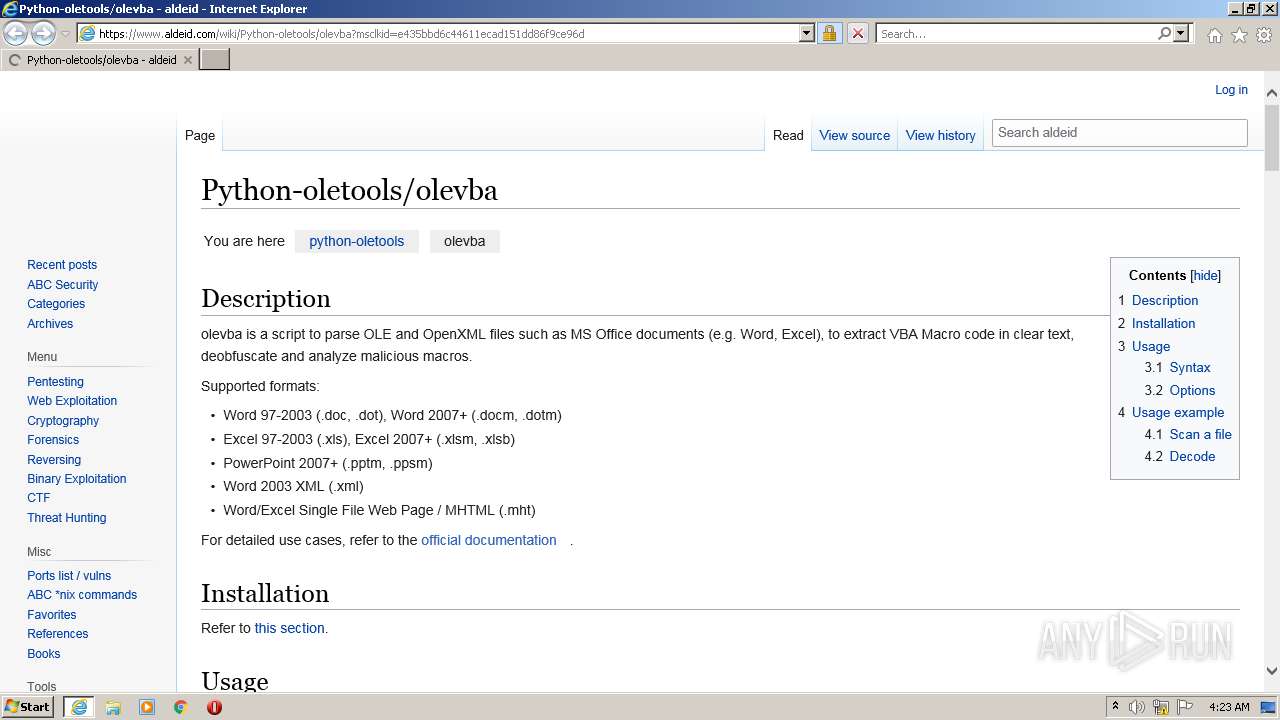
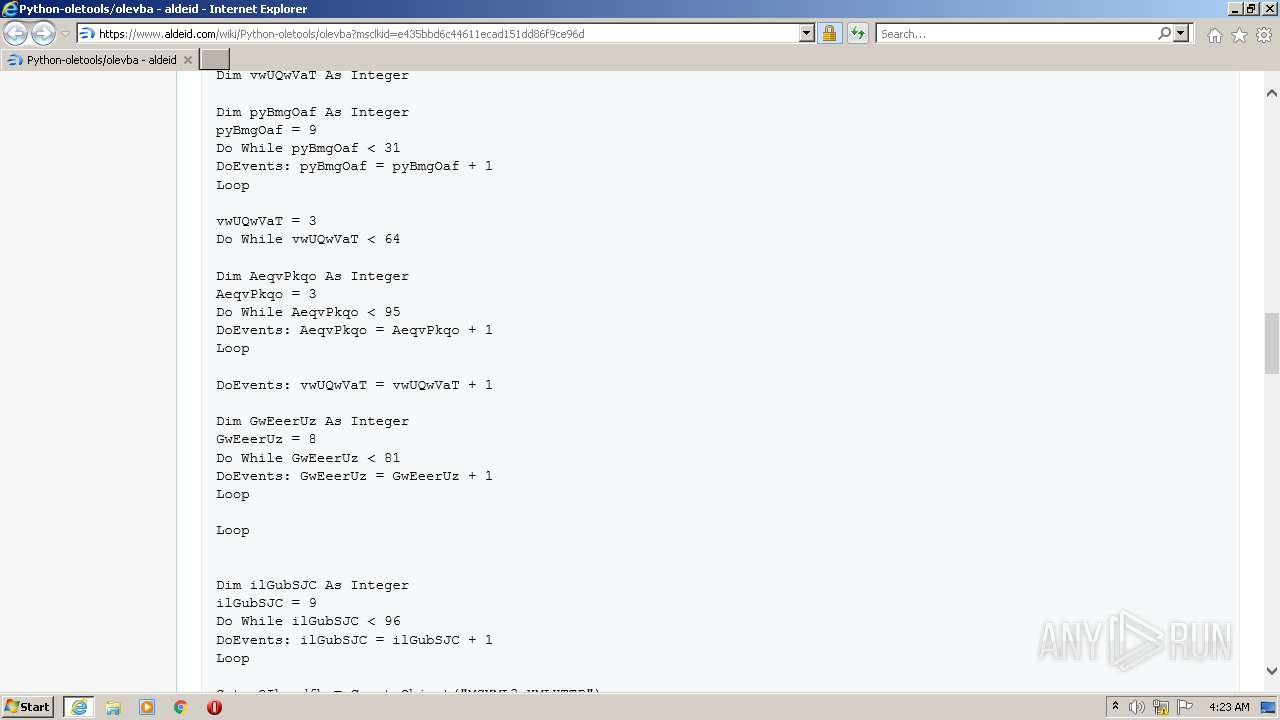
| 948 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\olevba[1].htm | html | |
MD5:03E90D834AA46FDE1875CC50BD14EACC | SHA256:BC2C7867CE046AFBC5A084CACAA41BC0D45EE98D289FF9606F3AFBFAE47479D4 | |||
| 948 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\load[1].js | text | |
MD5:83BEB952E382C897AF73BCA34DCB4D24 | SHA256:09EDC9128DD05A9B73A5EFD63158F500FECA5E323E03F26835C059DF566BEF1C | |||
| 948 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\aldeid[1].png | image | |
MD5:39062C43DCB1C0AE8E3937B964651048 | SHA256:50D5098195883E558340FE546D97CD867A7F4523C2D36A76C93095D970FBF222 | |||
| 3040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
68
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3040 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
948 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEA8SVMKPsnFcEm%2FVYIITs7I%3D | US | der | 471 b | whitelisted |
948 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3040 | iexplore.exe | GET | 200 | 95.140.236.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?39e194423c8fafb1 | GB | compressed | 4.70 Kb | whitelisted |
3040 | iexplore.exe | GET | 200 | 95.140.236.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e3cc3e82c4f7f198 | GB | compressed | 4.70 Kb | whitelisted |
948 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
948 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHr7M35ZTSPHb9t8TGKb2tY%3D | US | der | 1.40 Kb | whitelisted |
948 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHophRq39F1meVBmQbb%2F1x0%3D | US | der | 1.40 Kb | whitelisted |
948 | iexplore.exe | GET | 200 | 52.222.250.112:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
948 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
948 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3040 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3040 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
948 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
948 | iexplore.exe | 199.232.192.134:443 | aldeid.disqus.com | — | US | suspicious |
948 | iexplore.exe | 142.250.184.206:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
948 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | — | US | suspicious |
948 | iexplore.exe | 151.101.0.134:443 | disqus.com | Fastly | US | unknown |
948 | iexplore.exe | 172.217.18.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
948 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
www.aldeid.com |
| malicious |
aldeid.disqus.com |
| suspicious |
www.google-analytics.com |
| whitelisted |
disqus.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |