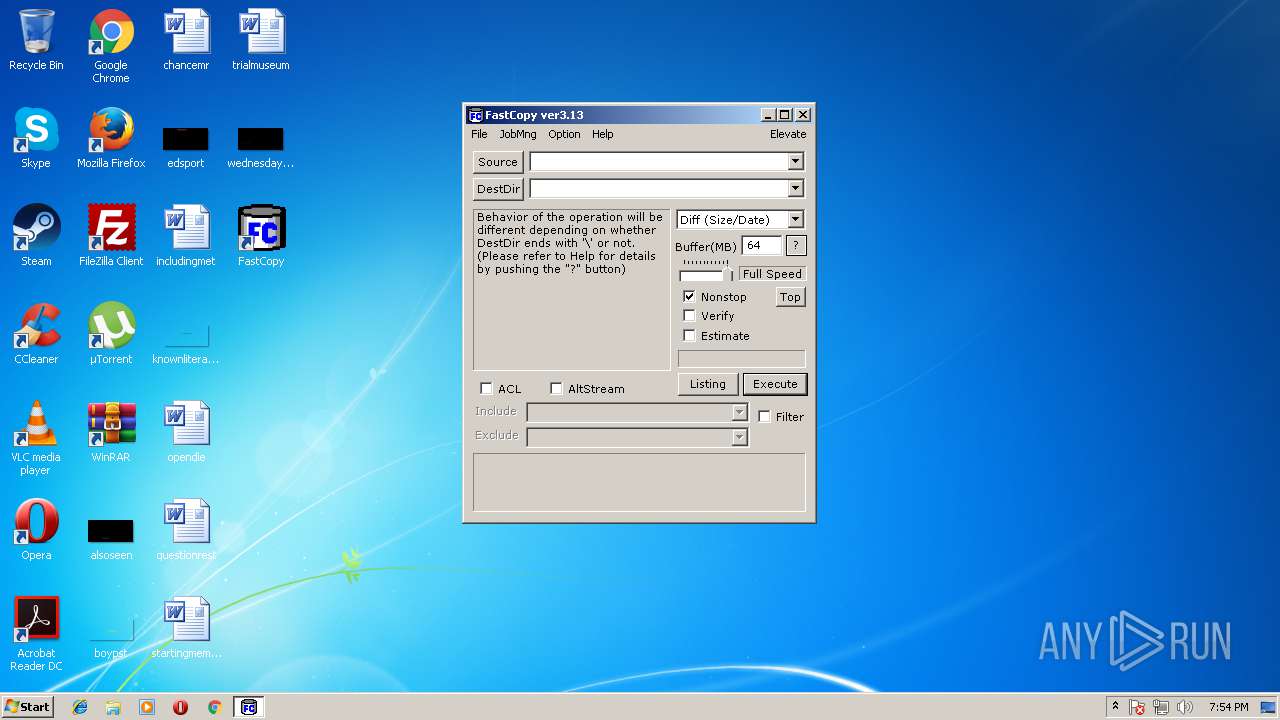
| File name: | FastCopy.exe |
| Full analysis: | https://app.any.run/tasks/9502be00-9688-46b3-a859-852b4900775c |
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2018, 18:52:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 50453A61DDAA245E3F92C91617738A6D |
| SHA1: | AFFCA2D17C3F4E8612CB99819B4CE4613AA47AC4 |
| SHA256: | E0DC39E8D05C8F0FB531842086C55FDBC5F4D8539C64B1740155FF73210FA248 |
| SSDEEP: | 12288:SC1DZ0DdOC2xjzm62X2+KXDAviPrAD/XtdTfOtHjW+f6bDIsUS6D11V7yykm7x:V904vjz0viPrAjXt5Lyx |
MALICIOUS
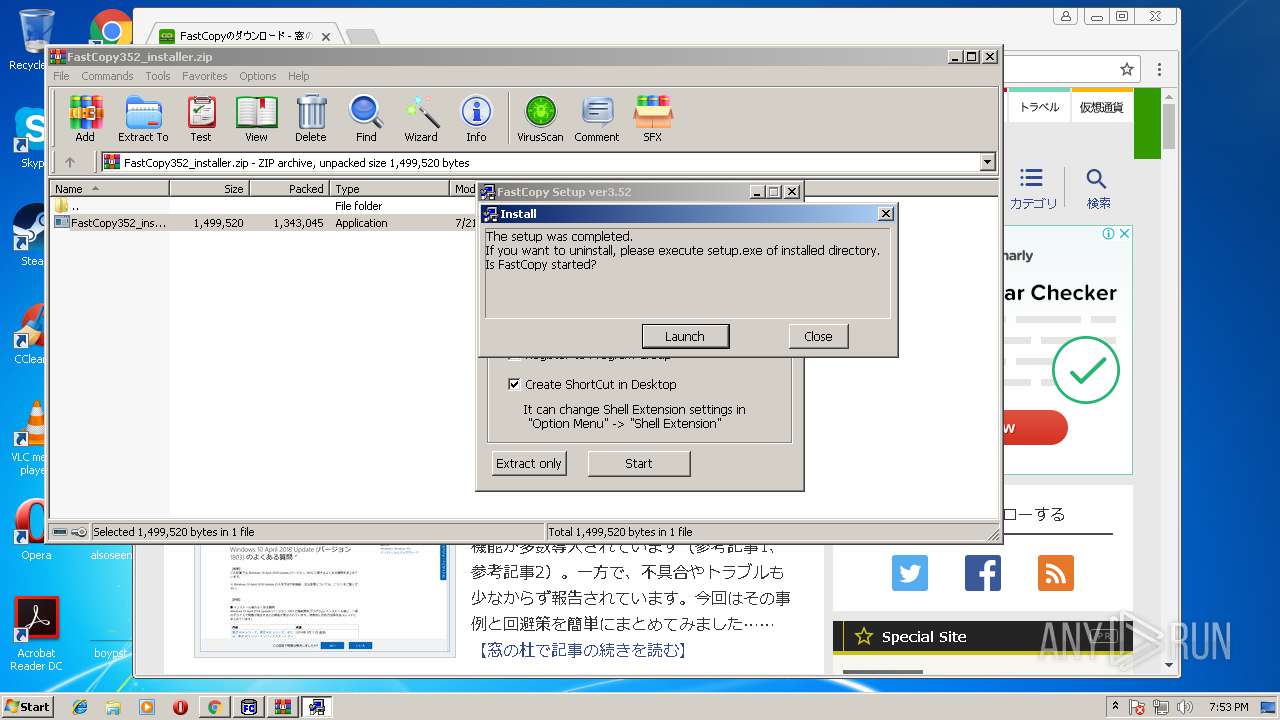
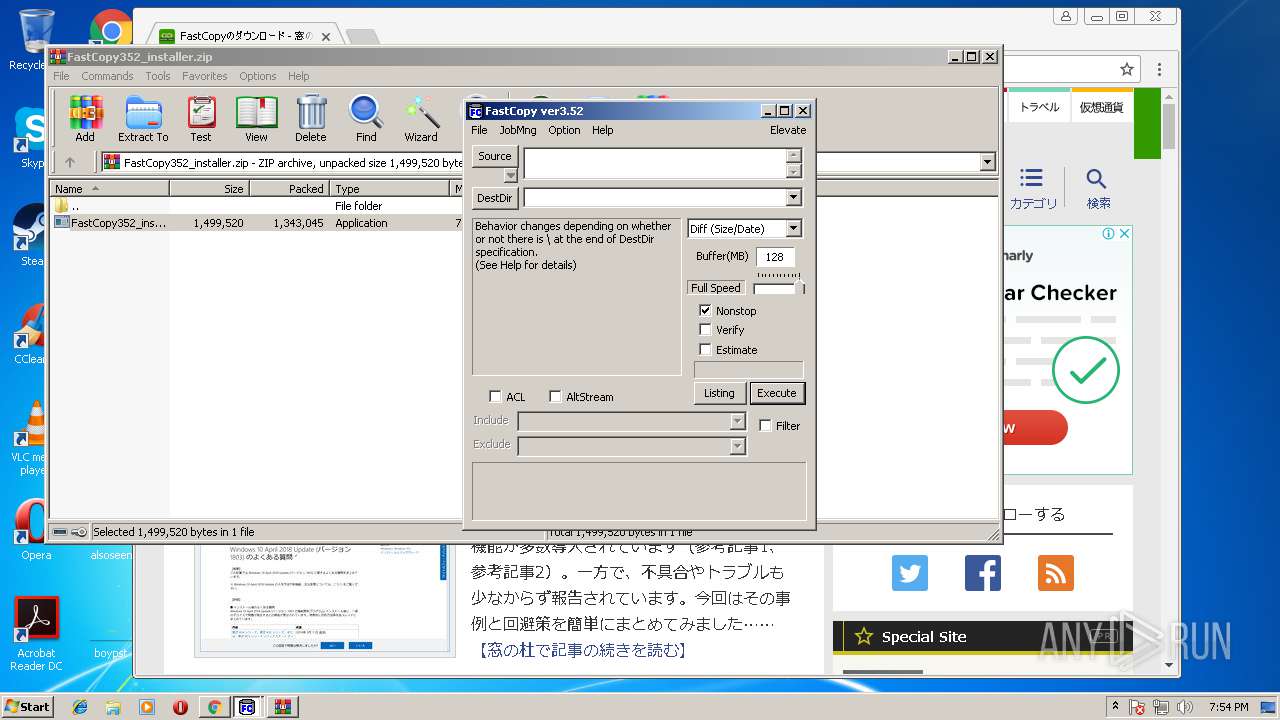
Application was dropped or rewritten from another process
- FastCopy352_installer.exe (PID: 384)
- FastCopy352_installer.exe (PID: 4080)
- FastCopy.exe (PID: 2780)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1376)
SUSPICIOUS
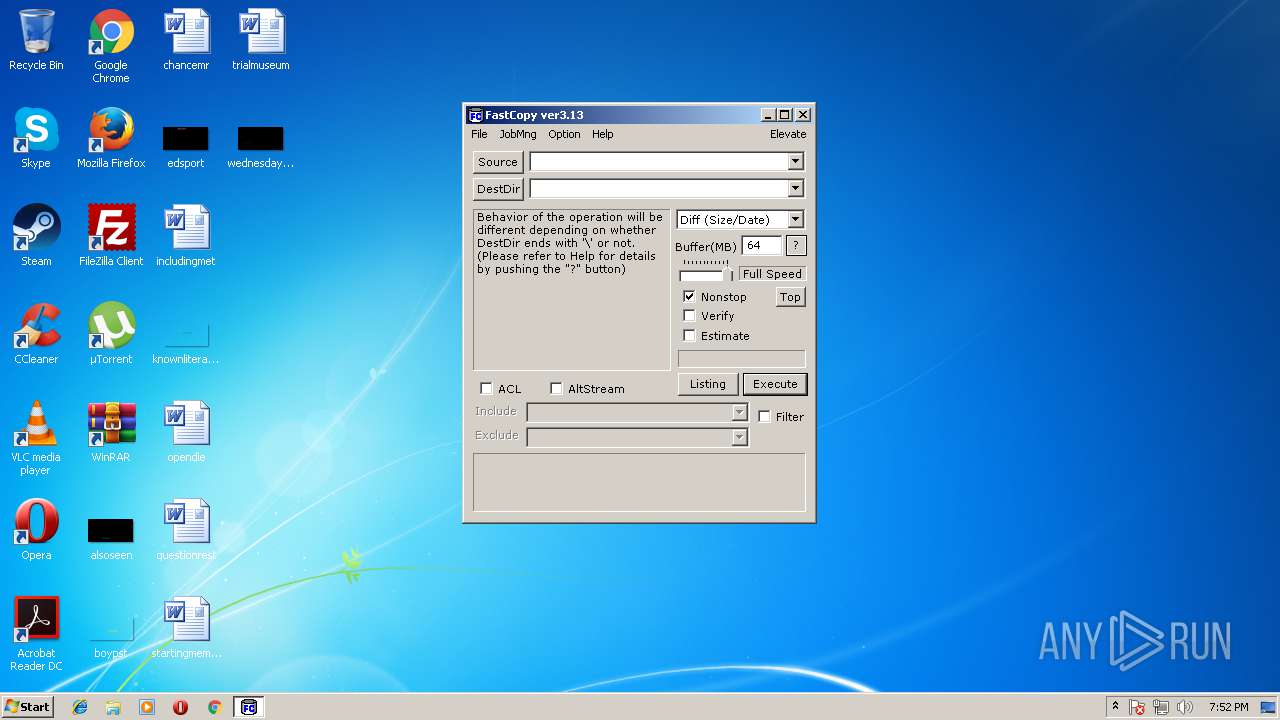
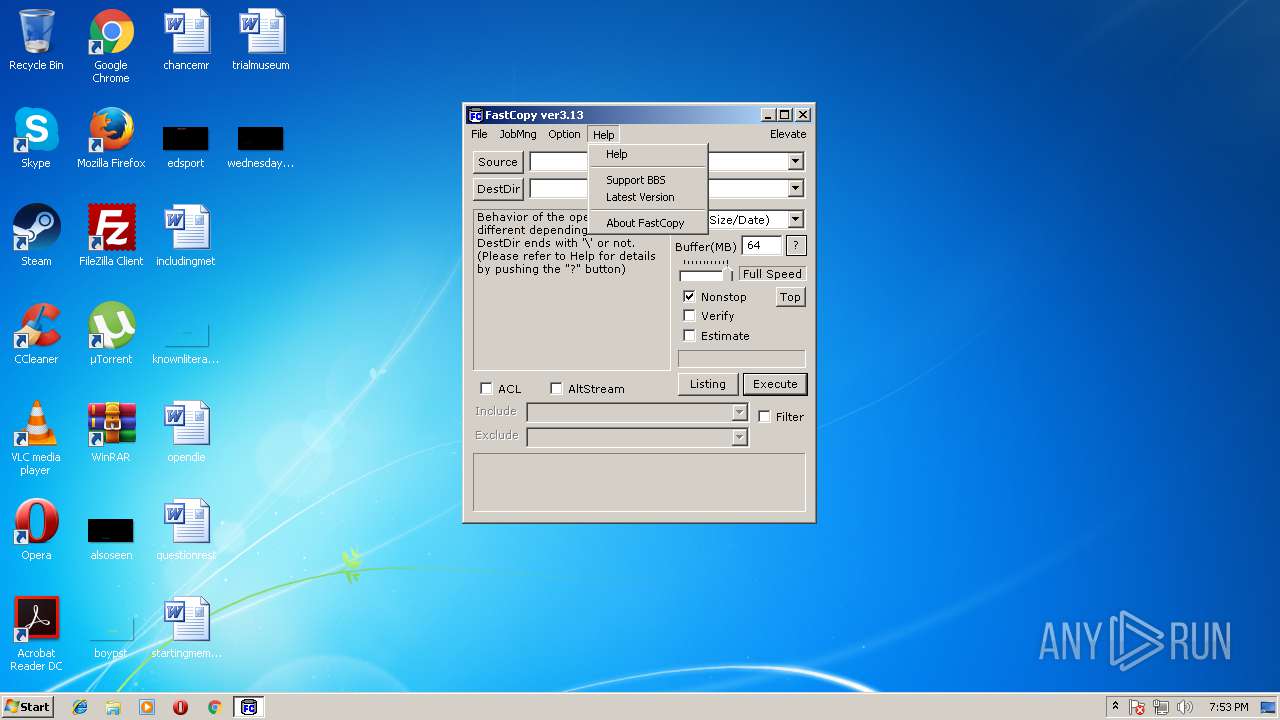
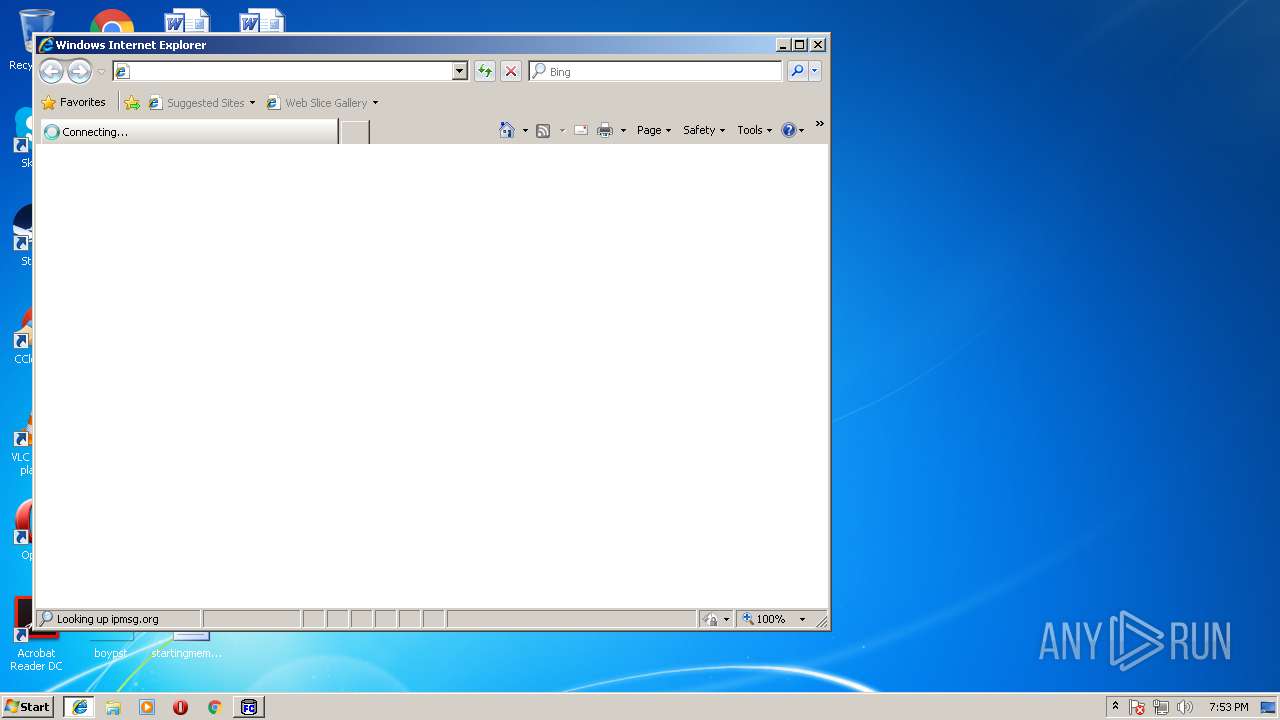
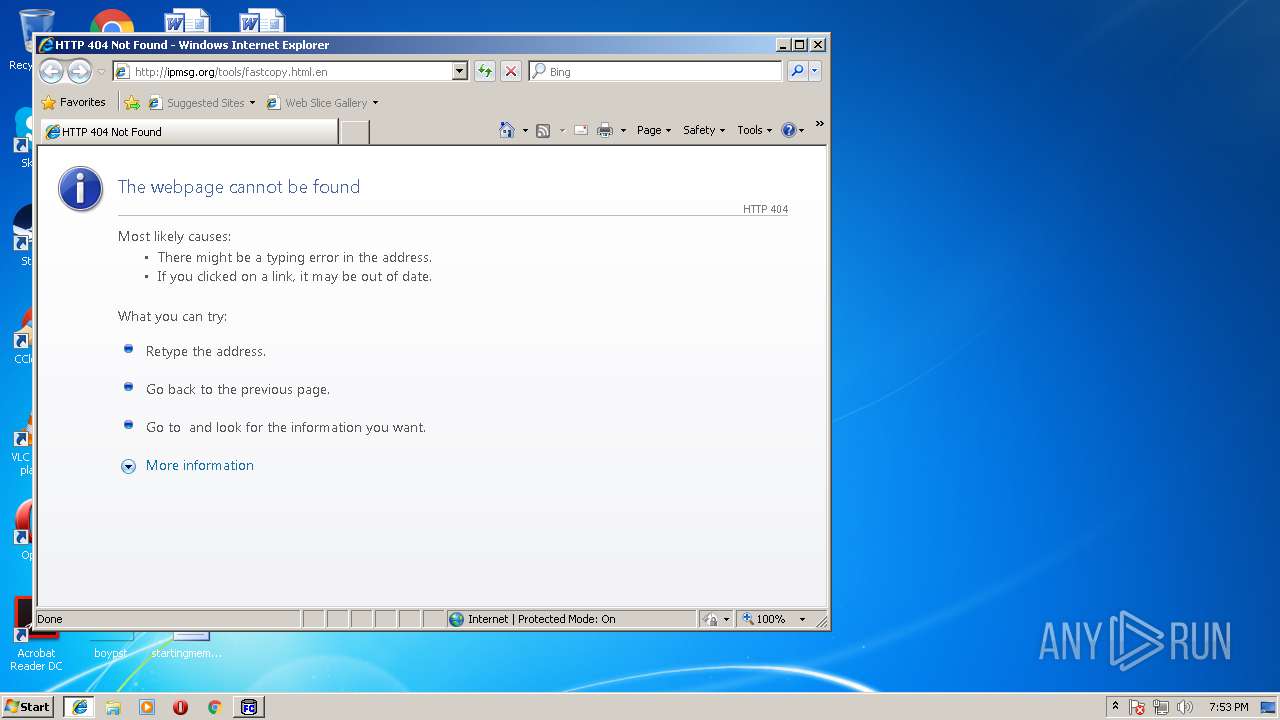
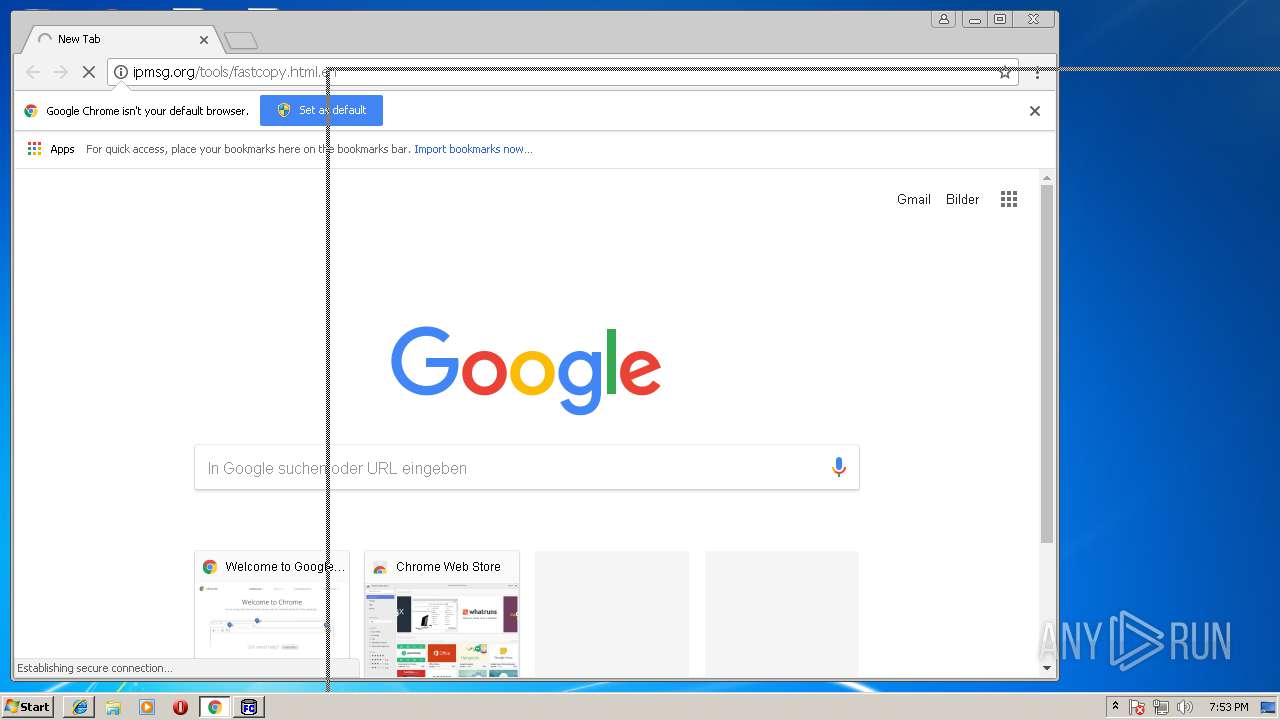
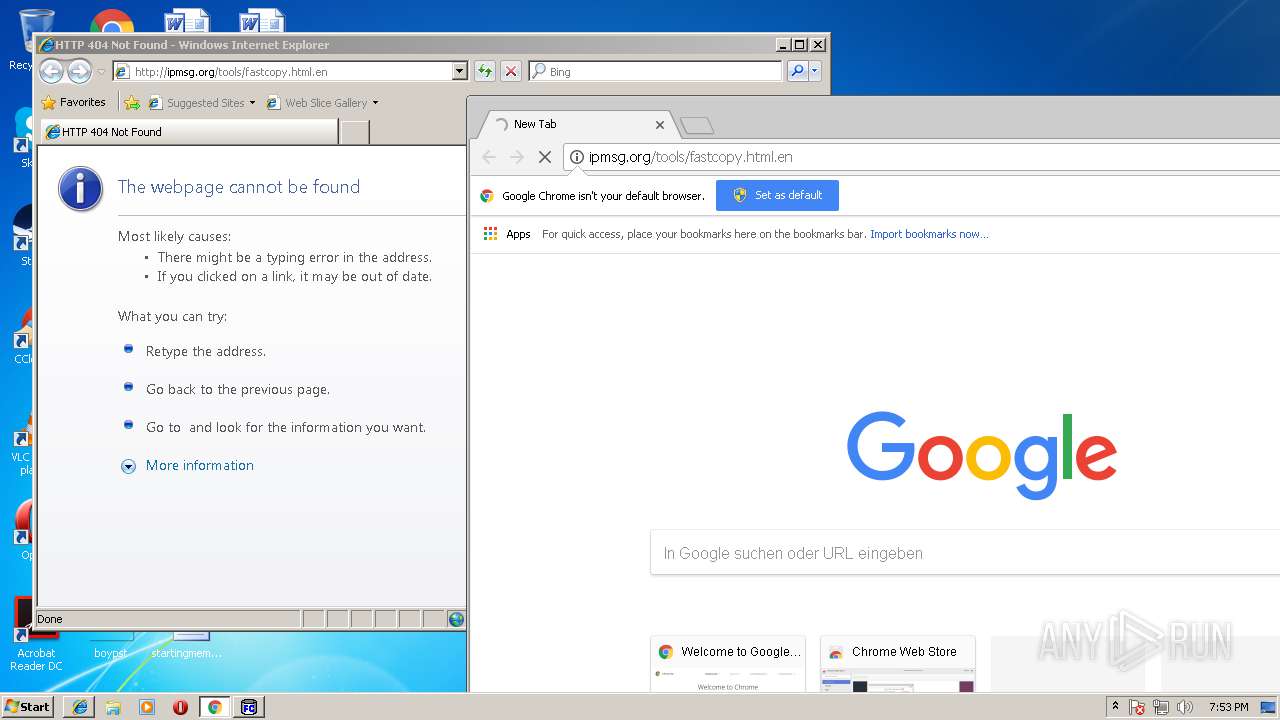
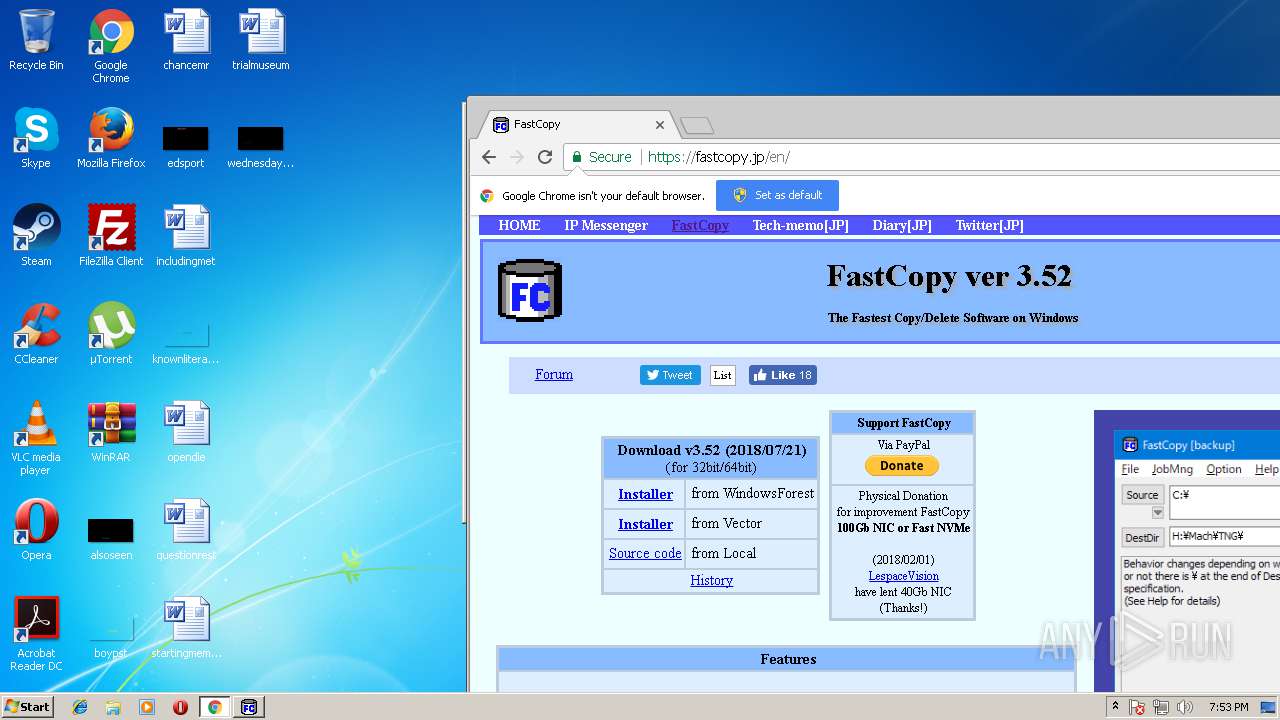
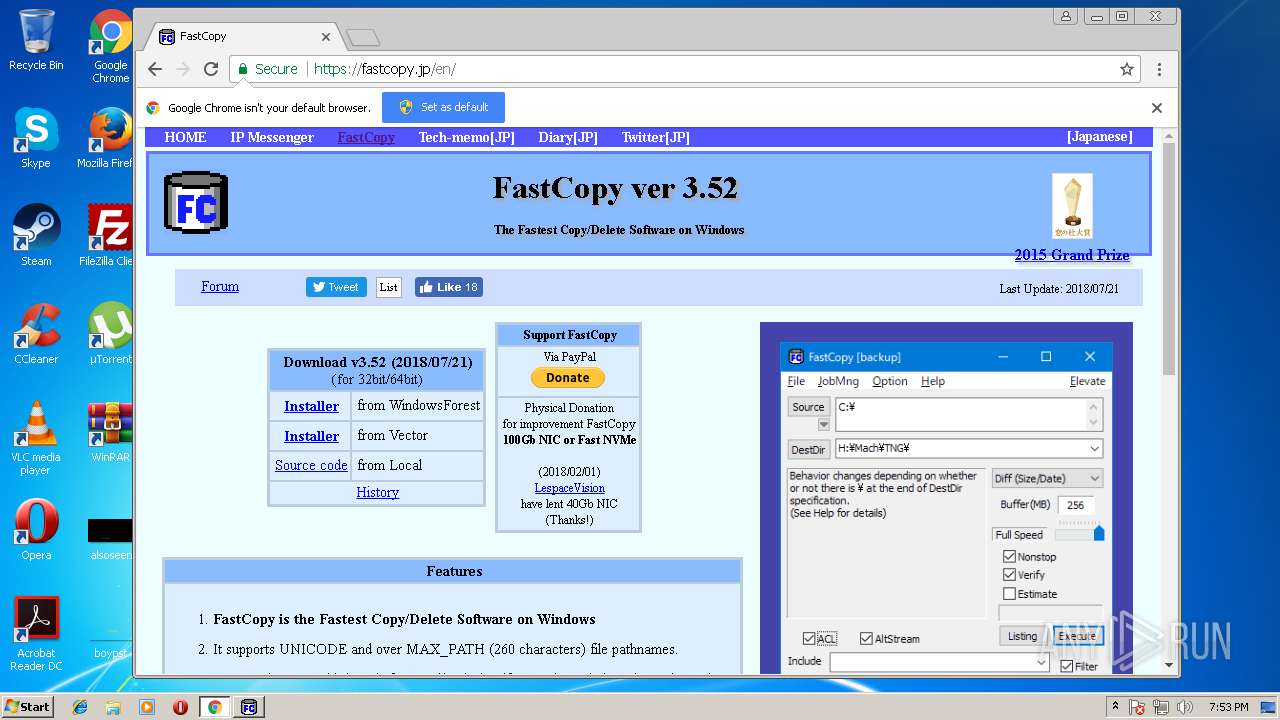
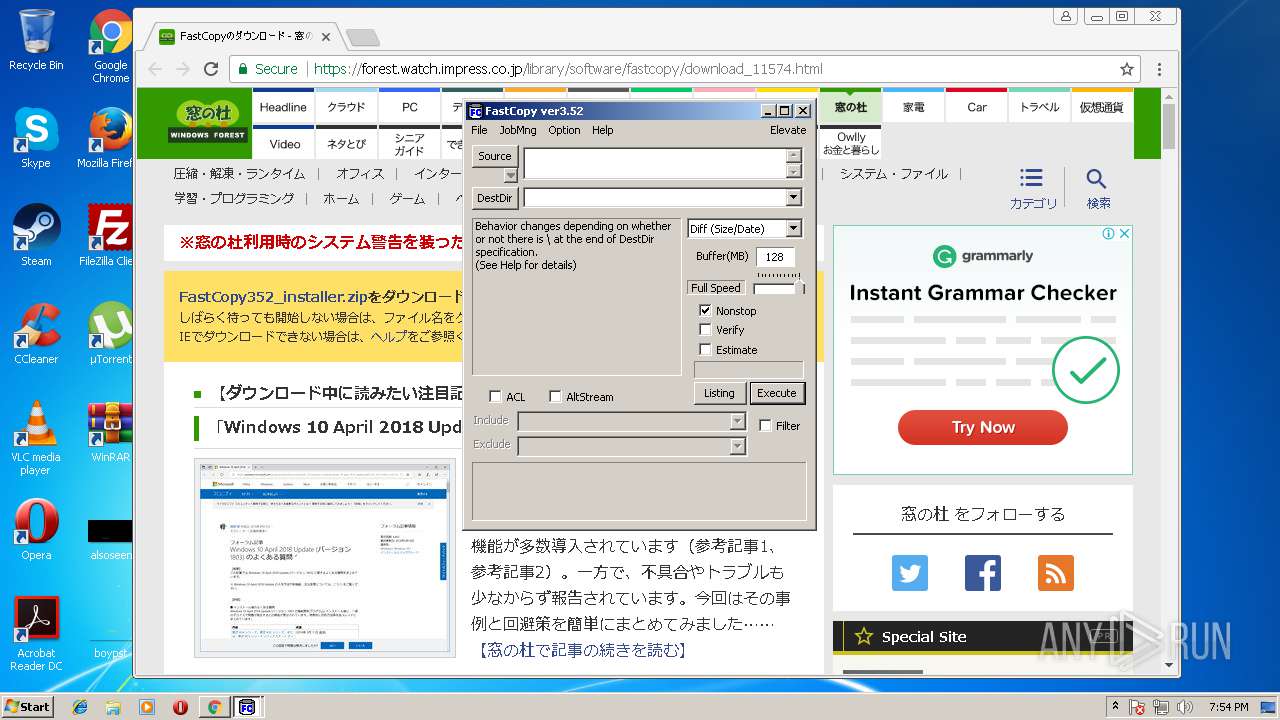
Starts Internet Explorer
- FastCopy.exe (PID: 1916)
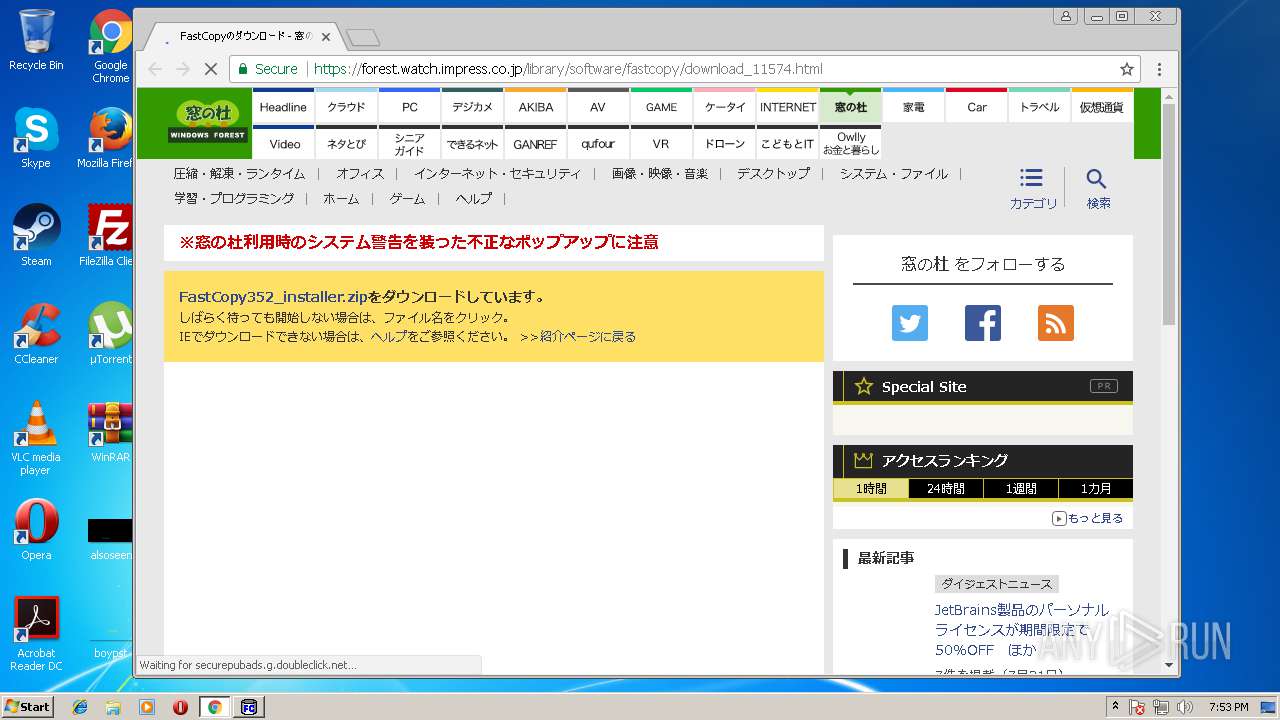
Executable content was dropped or overwritten
- FastCopy352_installer.exe (PID: 384)
- FastCopy352_installer.exe (PID: 4080)
- WinRAR.exe (PID: 2184)
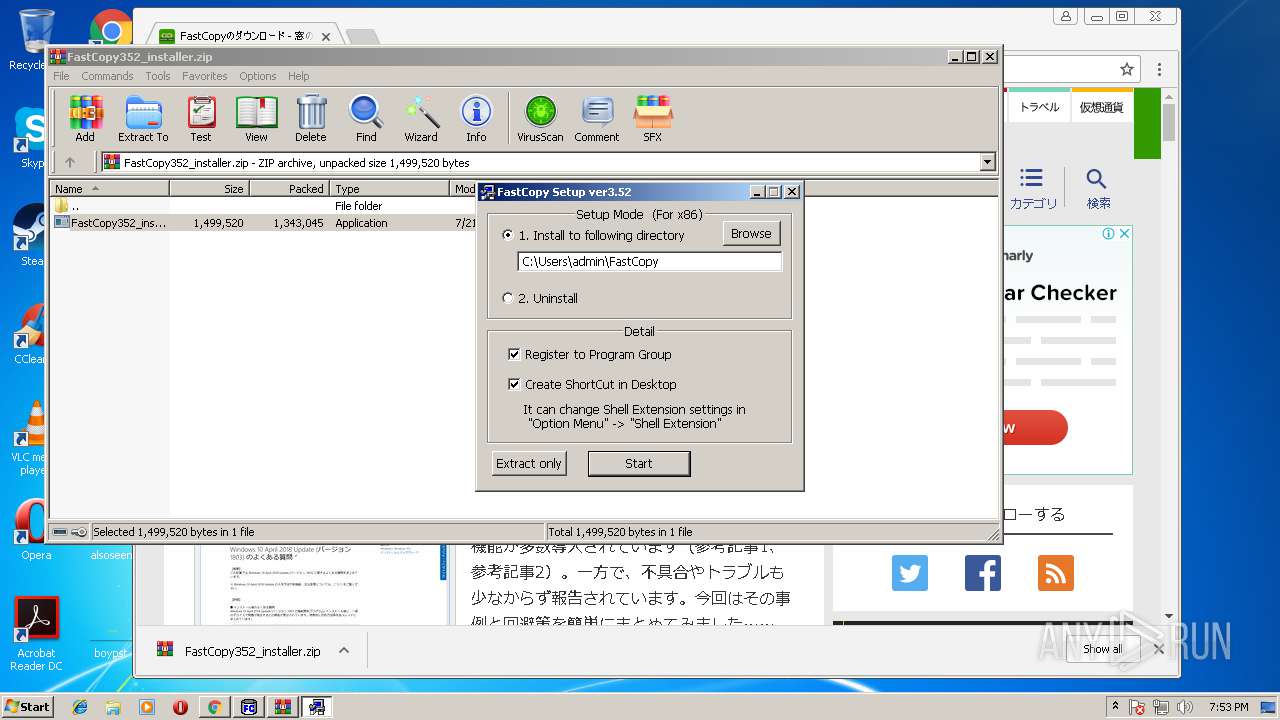
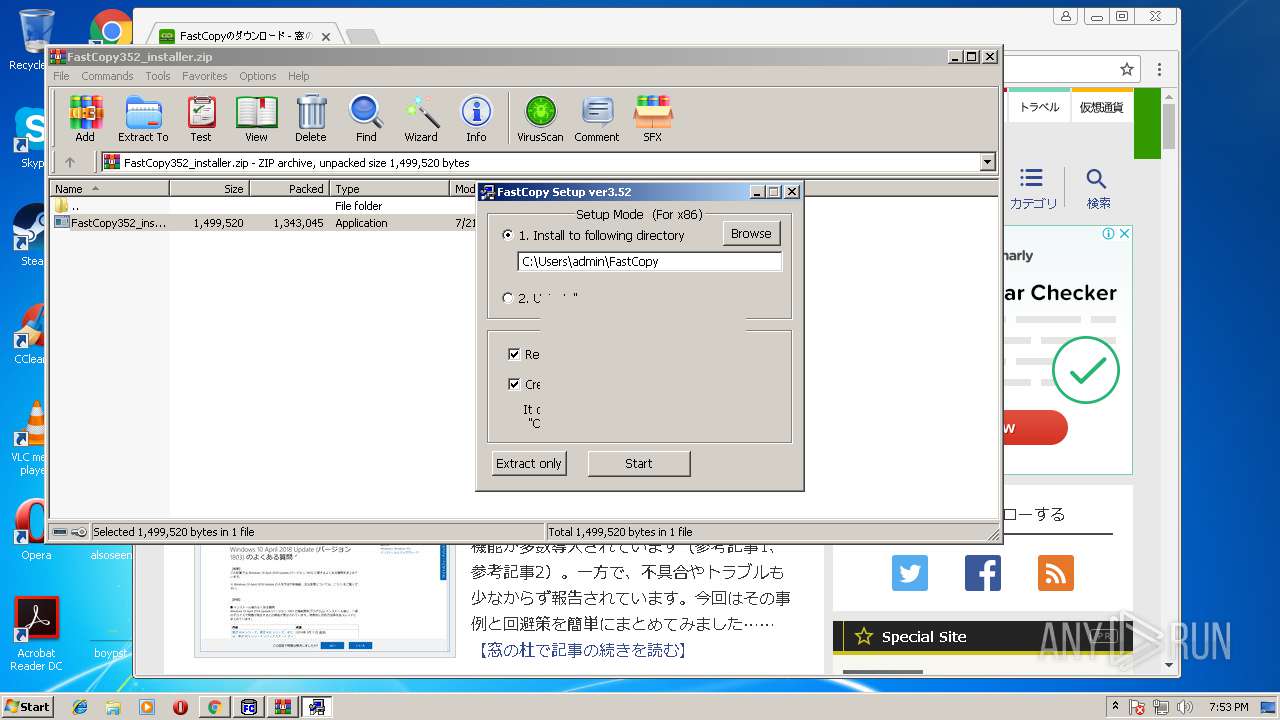
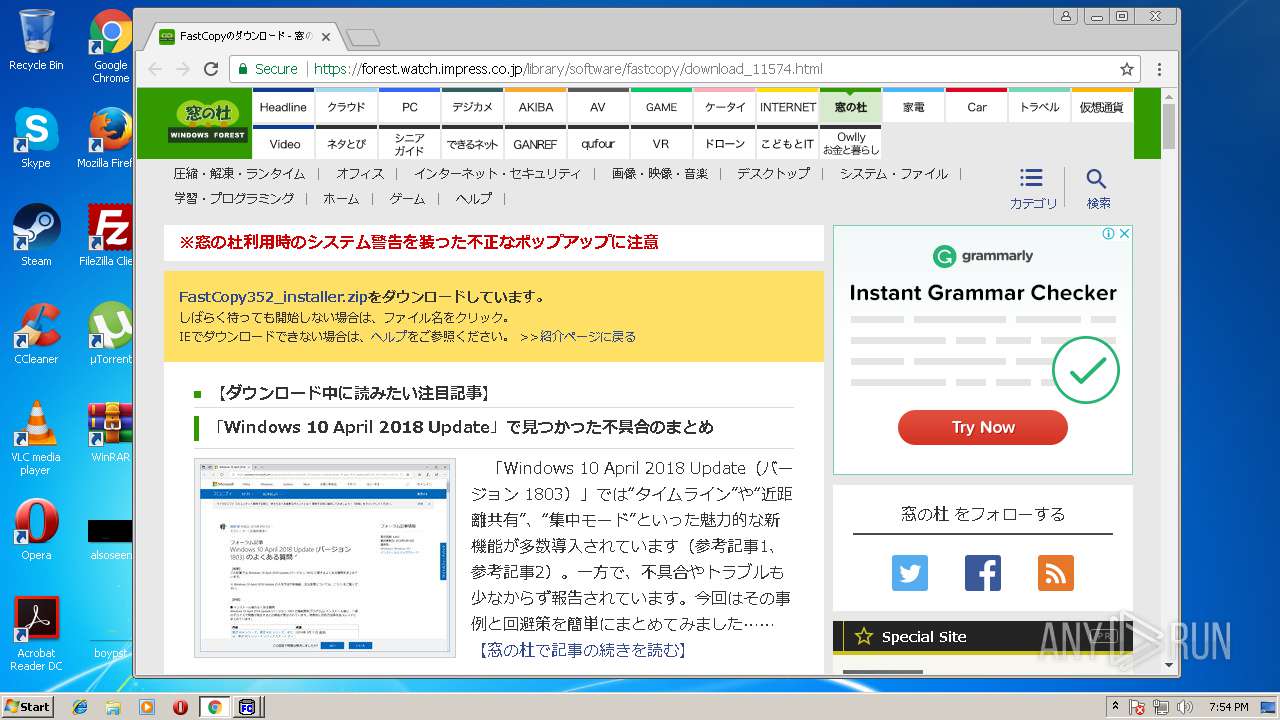
Creates files in the user directory
- FastCopy352_installer.exe (PID: 4080)
Creates a software uninstall entry
- FastCopy352_installer.exe (PID: 4080)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3448)
Reads Internet Cache Settings
- iexplore.exe (PID: 3168)
- chrome.exe (PID: 3188)
Reads internet explorer settings
- iexplore.exe (PID: 3168)
Dropped object may contain URL's
- iexplore.exe (PID: 3168)
- FastCopy352_installer.exe (PID: 4080)
- iexplore.exe (PID: 3448)
- chrome.exe (PID: 3188)
Application launched itself
- chrome.exe (PID: 3188)
Reads settings of System Certificates
- chrome.exe (PID: 3188)
Creates files in the user directory
- chrome.exe (PID: 3188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:03:14 16:02:31+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 457216 |
| InitializedDataSize: | 228352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31396 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.1.3.0 |
| ProductVersionNumber: | 3.1.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Japanese |
| CharacterSet: | Unicode |
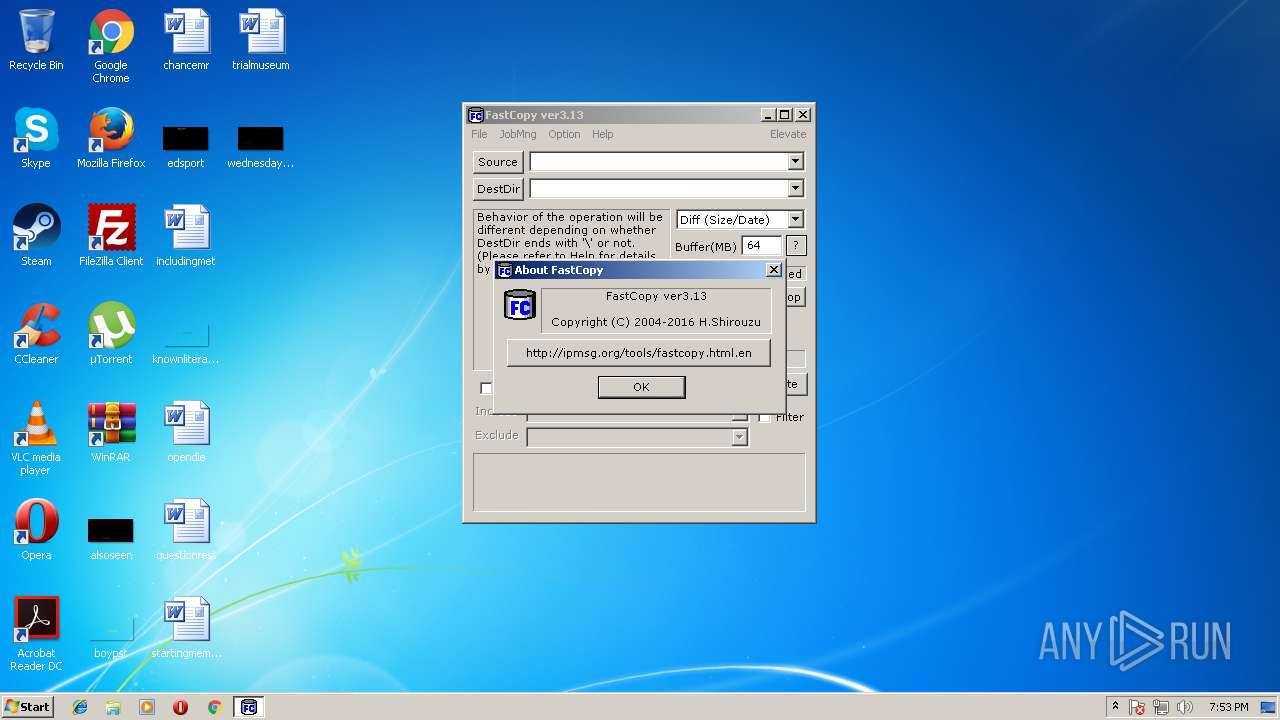
| Comments: | http://ipmsg.org/tools/fastcopy.html |
| CompanyName: | SHIROUZU Hiroaki |
| FileDescription: | FastCopy |
| FileVersion: | 3.1.3.0 |
| InternalName: | FastCopy |
| LegalCopyright: | Copyright (C) 2004-2016 SHIROUZU Hiroaki All rights reserved. |
| OriginalFileName: | FastCopy.exe |
| ProductName: | FastCopy |
| ProductVersion: | 3.1.3.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Mar-2016 15:02:31 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | http://ipmsg.org/tools/fastcopy.html |
| CompanyName: | SHIROUZU Hiroaki |
| FileDescription: | FastCopy |
| FileVersion: | 3.1.3.0 |
| InternalName: | FastCopy |
| LegalCopyright: | Copyright (C) 2004-2016 SHIROUZU Hiroaki All rights reserved. |
| OriginalFilename: | FastCopy.exe |
| ProductName: | FastCopy |
| ProductVersion: | 3.1.3.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 14-Mar-2016 15:02:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0006F8EE | 0x0006FA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54427 |
.rdata | 0x00071000 | 0x000207B6 | 0x00020800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.25956 |
.data | 0x00092000 | 0x0000A5A8 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.72561 |
.tls | 0x0009D000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x0009E000 | 0x0000CA80 | 0x0000CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.37741 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00081 | 1609 | UNKNOWN | Japanese - Japan | RT_MANIFEST |
2 | 5.35458 | 318 | UNKNOWN | Japanese - Japan | RT_STRING |
3 | 5.34288 | 460 | UNKNOWN | Japanese - Japan | RT_STRING |
4 | 5.00208 | 500 | UNKNOWN | Japanese - Japan | RT_STRING |
5 | 5.57005 | 368 | UNKNOWN | Japanese - Japan | RT_STRING |
6 | 5.16556 | 618 | UNKNOWN | Japanese - Japan | RT_STRING |
7 | 5.11551 | 324 | UNKNOWN | Japanese - Japan | RT_STRING |
8 | 3.88468 | 74 | UNKNOWN | Japanese - Japan | RT_STRING |
9 | 2.37767 | 78 | UNKNOWN | Japanese - Japan | RT_STRING |
10 | 5.0299 | 336 | UNKNOWN | Japanese - Japan | RT_STRING |
Imports
ACTIVEDS.dll |
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
SHELL32.dll |
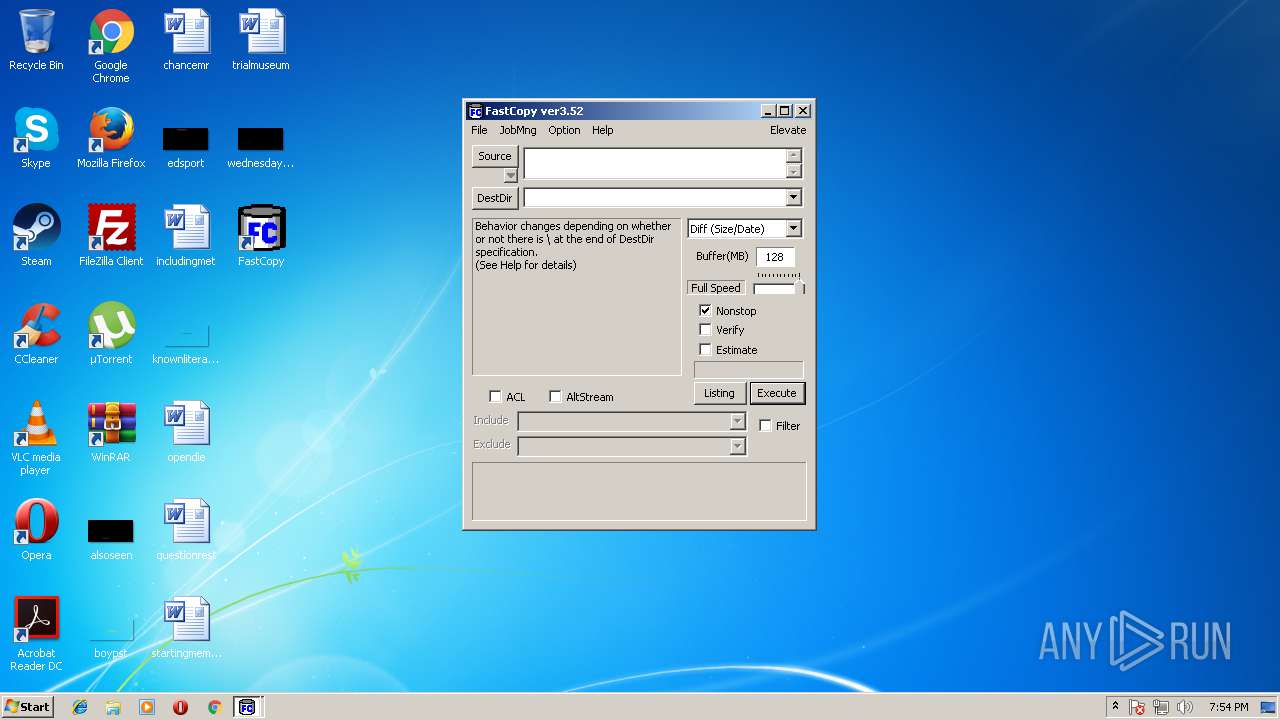
Total processes
52
Monitored processes
17
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 384 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2184.40785\FastCopy352_installer.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2184.40785\FastCopy352_installer.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1784,746082472993292051,15883956378959507672,131072 --service-pipe-token=43F1D728B4D41D1FF88CBBB04785956E --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=43F1D728B4D41D1FF88CBBB04785956E --renderer-client-id=2 --mojo-platform-channel-handle=1288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 1376 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe9_ Global\UsGthrCtrlFltPipeMssGthrPipe9 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1916 | "C:\Users\admin\AppData\Local\Temp\FastCopy.exe" | C:\Users\admin\AppData\Local\Temp\FastCopy.exe | — | explorer.exe | |||||||||||
User: admin Company: SHIROUZU Hiroaki Integrity Level: MEDIUM Description: FastCopy Exit code: 0 Version: 3.1.3.0 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1784,746082472993292051,15883956378959507672,131072 --lang=en-US --no-sandbox --service-request-channel-token=377EB5FF116870BDCB8A9421713287D5 --mojo-platform-channel-handle=4576 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
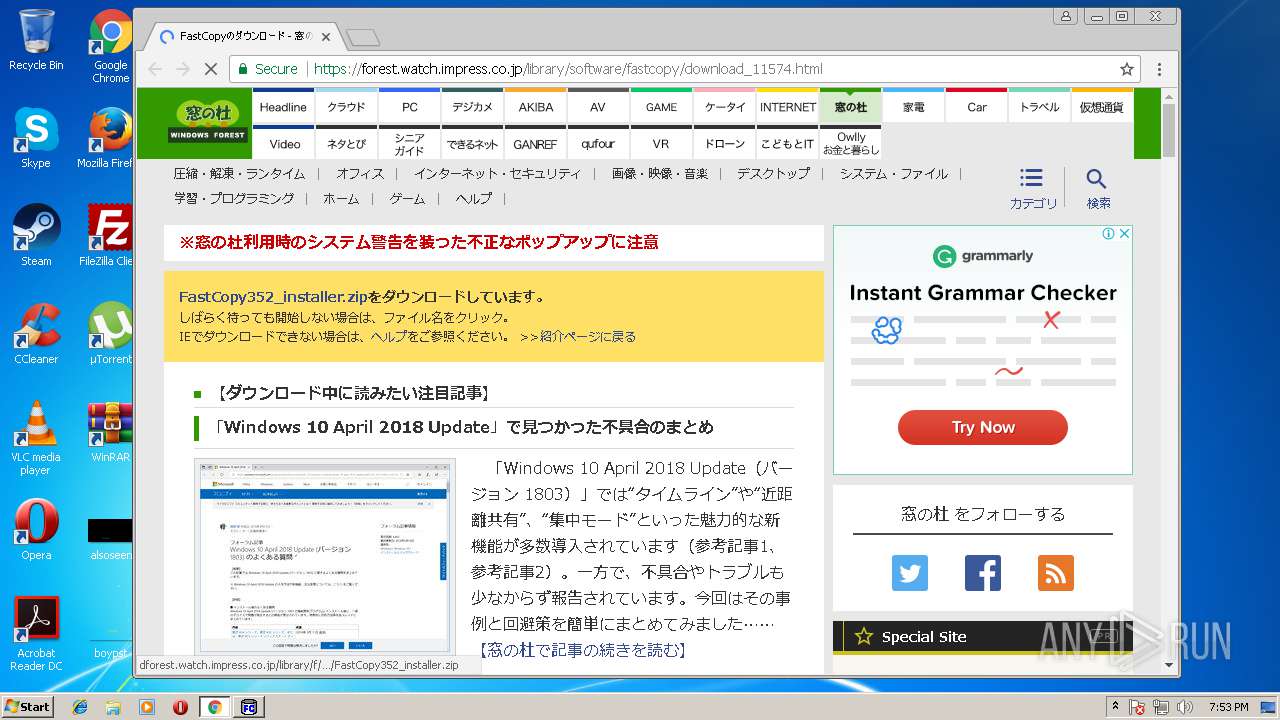
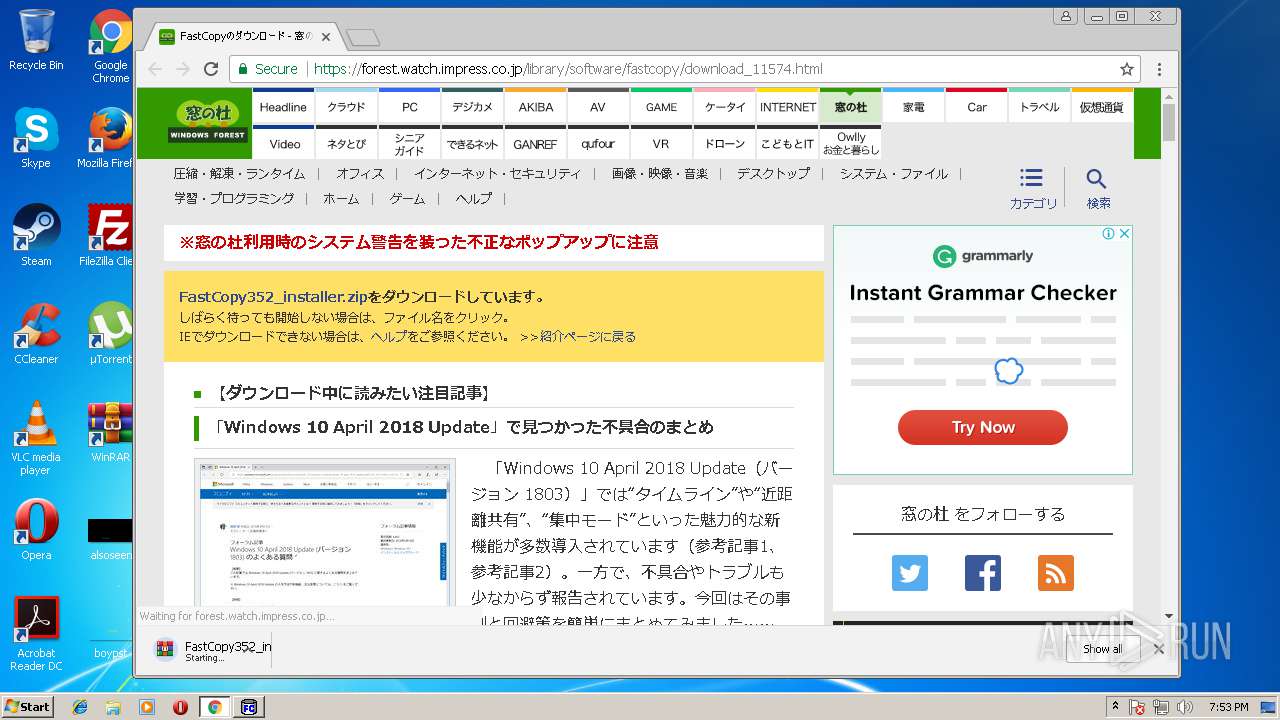
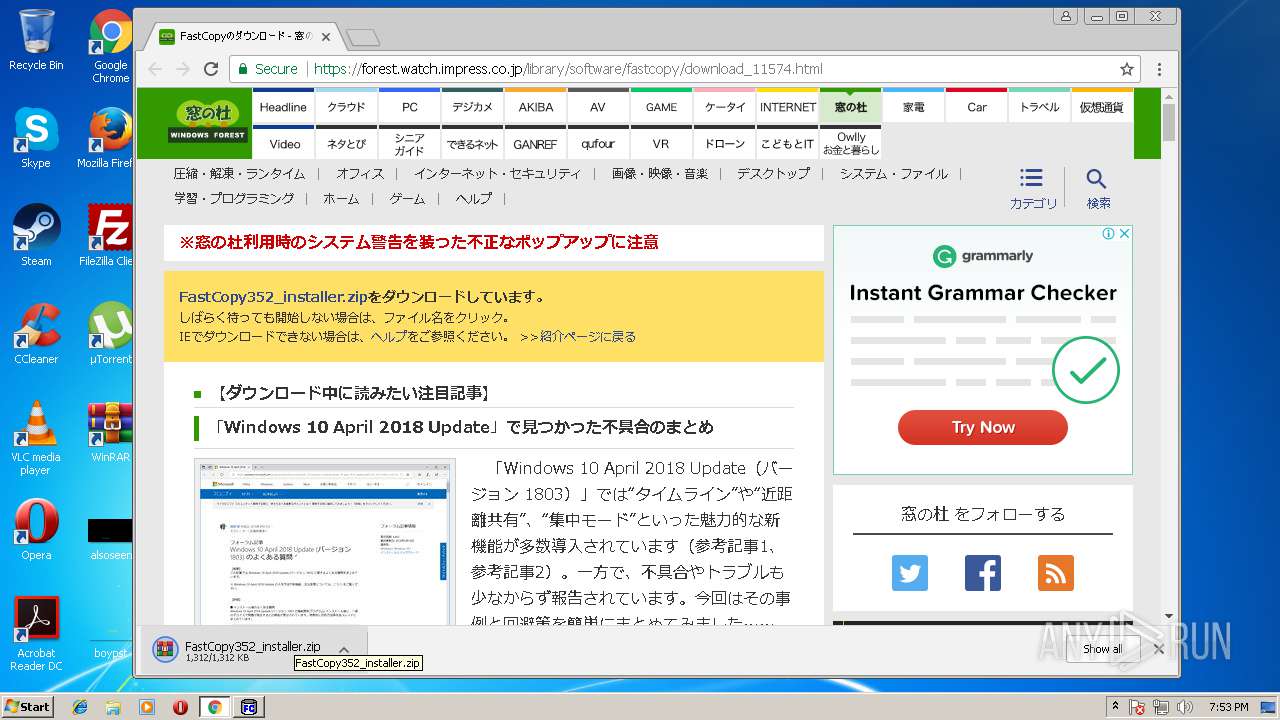
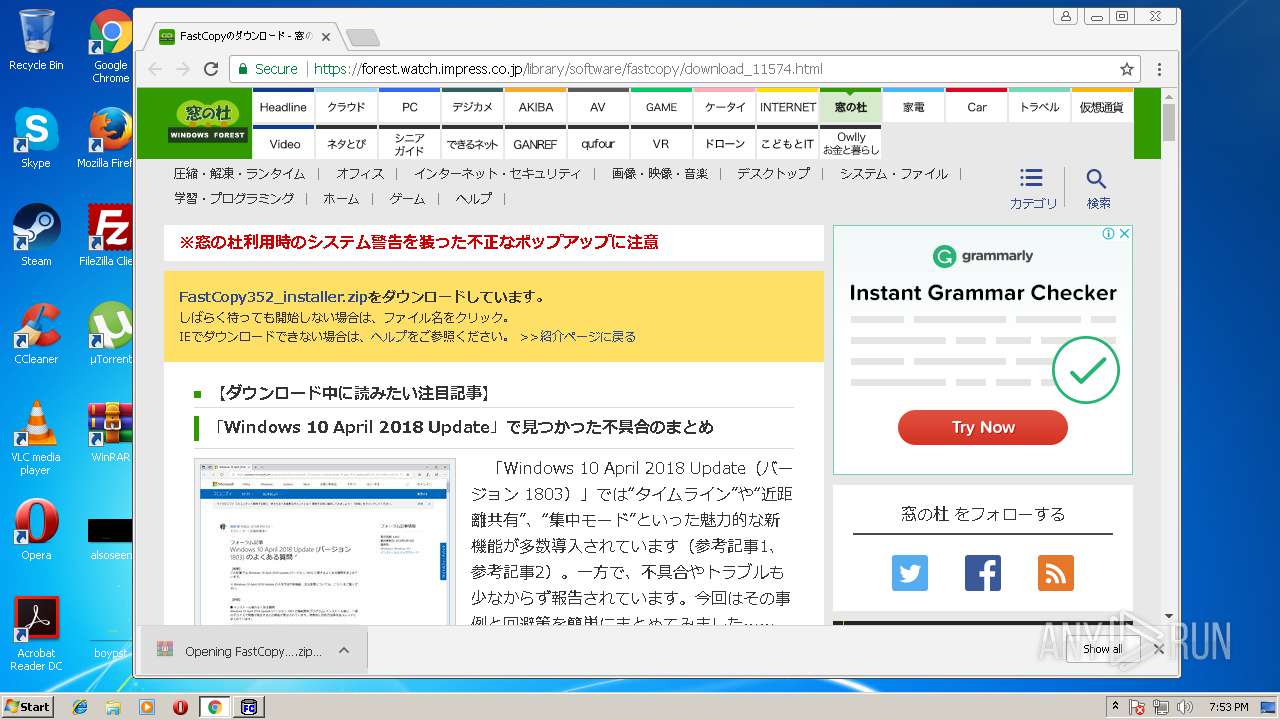
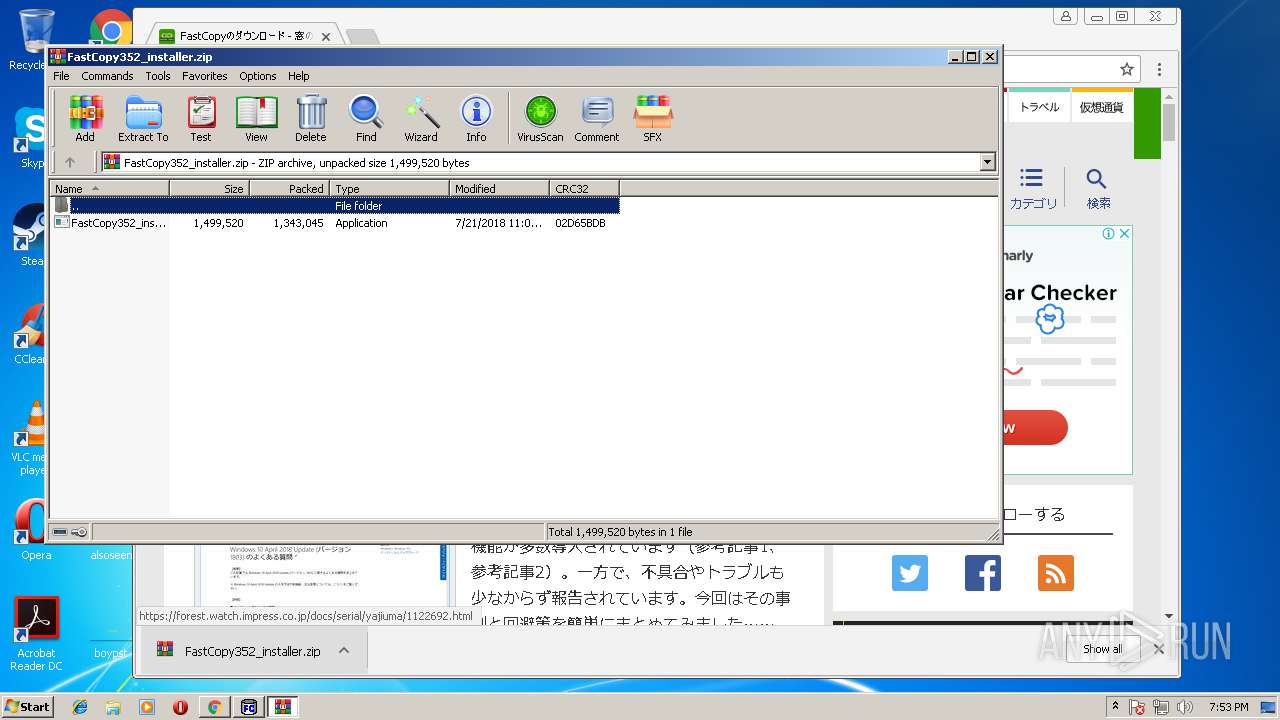
| 2184 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\FastCopy352_installer.zip" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=61.0.3163.91 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x68ab7d7c,0x68ab7da4,0x68ab7d8c | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1784,746082472993292051,15883956378959507672,131072 --service-pipe-token=847096C33BE9A03B035393B25CB62B8D --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=847096C33BE9A03B035393B25CB62B8D --renderer-client-id=5 --mojo-platform-channel-handle=3500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2780 | "C:\Users\admin\FastCopy\FastCopy.exe" | C:\Users\admin\FastCopy\FastCopy.exe | FastCopy352_installer.exe | ||||||||||||
User: admin Company: SHIROUZU Hiroaki Integrity Level: MEDIUM Description: FastCopy Exit code: 0 Version: 3.5.2.0 Modules
| |||||||||||||||
| 3168 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3448 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 571
Read events
2 354
Write events
212
Delete events
5
Modification events
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000048000000010000000000000000000000000000000000000000000000B096B68868EBD301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000D8BFD602040000000000000000000000000000000000000000000000F4BFD602040000000000000000000000000000000000000000000000D8372A0000000000FFFFFFFF000000000000000000000000010000002E00000000000000000000000000000002000000C0A801640000000000000000D84ED505AC02000005000000010000000000000000000000010000000000000000000000BF060000000000000000000000000000000000001000000088C0D60204000000000000000000000000000000000000000000000000000000C8E40C00000000000C0000000000000000000000 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {F473E999-94F2-11E8-ACE5-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 10 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E207070002001F00120035000500A900 | |||
Executable files
6
Suspicious files
144
Text files
85
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3448 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3448 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000008.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1916 | FastCopy.exe | C:\Users\admin\AppData\Local\Temp\FastCopy2.ini | text | |
MD5:— | SHA256:— | |||
| 3188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4bf7e31b-e90e-46b5-8b25-37a040ccdfac.tmp | — | |
MD5:— | SHA256:— | |||
| 3168 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 3188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:— | SHA256:— | |||
| 3188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF44a9c2.TMP | text | |
MD5:— | SHA256:— | |||
| 3188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\0b424357-803d-4002-a471-5e43f4cbfdf1\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
76
DNS requests
47
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3188 | chrome.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
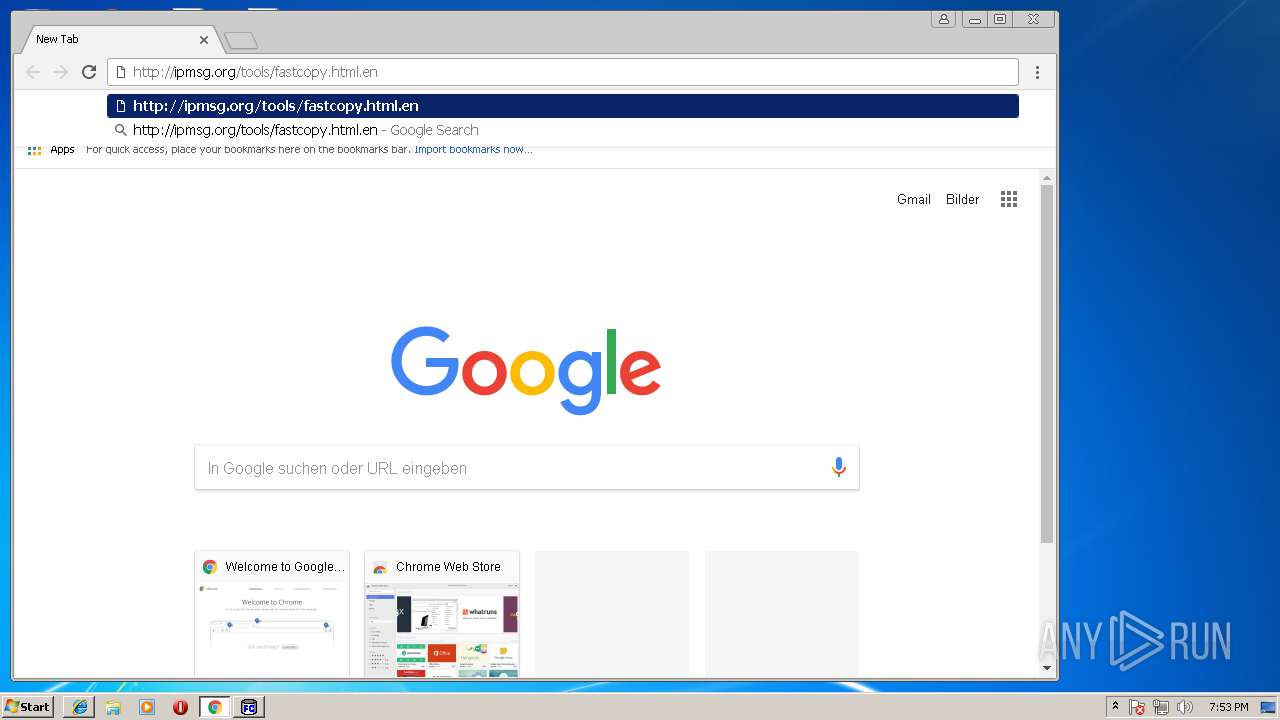
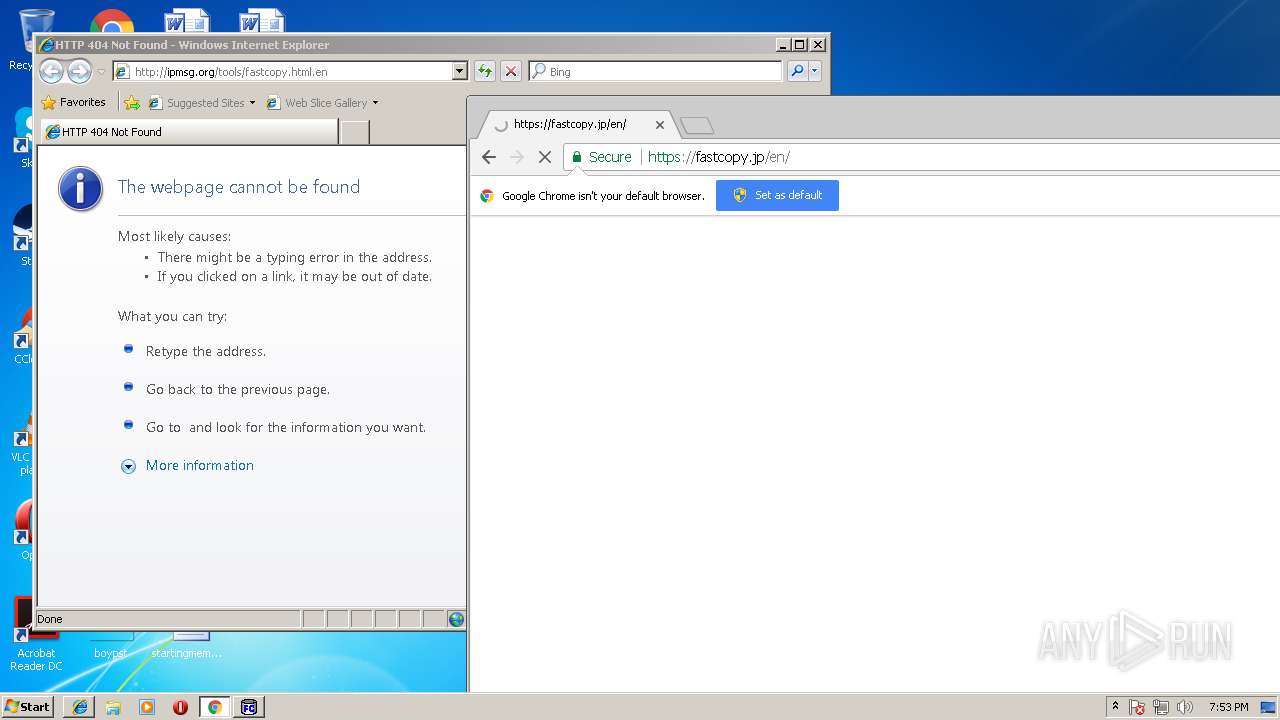
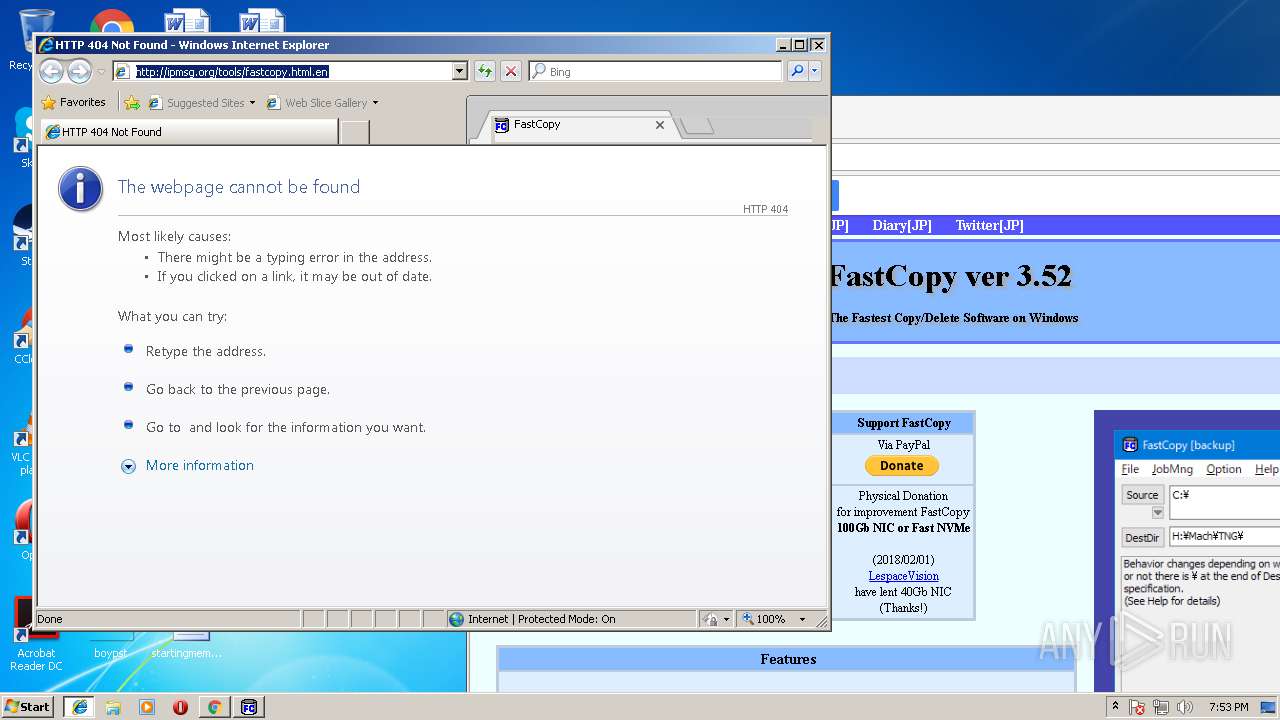
3188 | chrome.exe | GET | 301 | 49.212.200.23:80 | http://ipmsg.org/tools/fastcopy.html.en | JP | html | 307 b | whitelisted |
3168 | iexplore.exe | GET | 404 | 49.212.200.23:80 | http://ipmsg.org/tools/fastcopy.html.en | JP | html | 206 b | whitelisted |
3188 | chrome.exe | GET | 200 | 23.37.43.27:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEH7hSm9v7%2FLTfz%2BtZU062rQ%3D | NL | der | 1.71 Kb | whitelisted |
3188 | chrome.exe | GET | 200 | 192.35.177.64:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | US | cat | 893 b | shared |
3188 | chrome.exe | GET | 200 | 13.32.99.250:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3448 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3448 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3188 | chrome.exe | 172.217.168.3:443 | www.google.de | Google Inc. | US | whitelisted |
3188 | chrome.exe | 172.217.23.174:443 | apis.google.com | Google Inc. | US | whitelisted |
3188 | chrome.exe | 49.212.200.23:80 | ipmsg.org | SAKURA Internet Inc. | JP | unknown |
3188 | chrome.exe | 172.217.168.10:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3188 | chrome.exe | 49.212.200.23:443 | ipmsg.org | SAKURA Internet Inc. | JP | unknown |
3188 | chrome.exe | 216.58.215.228:443 | www.google.com | Google Inc. | US | whitelisted |
3188 | chrome.exe | 192.35.177.64:80 | apps.identrust.com | IdenTrust | US | malicious |
3188 | chrome.exe | 216.58.215.232:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3168 | iexplore.exe | 49.212.200.23:80 | ipmsg.org | SAKURA Internet Inc. | JP | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ipmsg.org |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
apps.identrust.com |
| shared |
Threats
Process | Message |
|---|---|
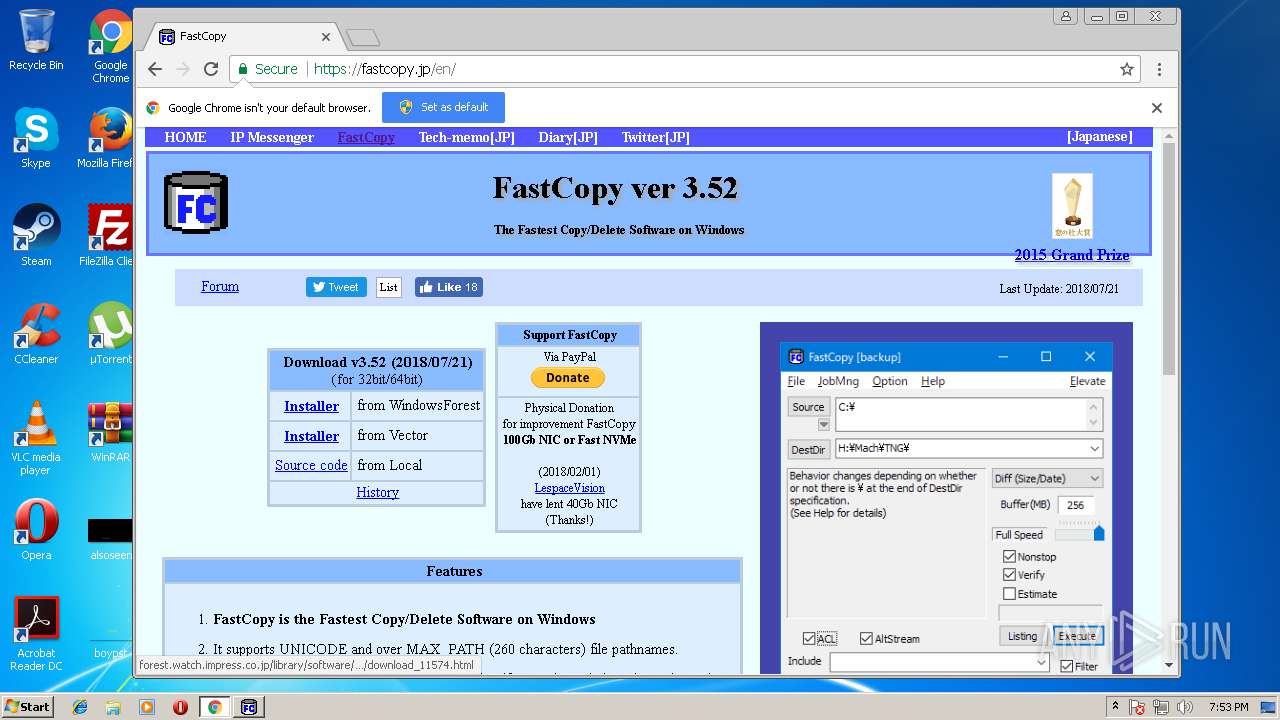
FastCopy.exe | 0000.18: host=fastcopy.jp path=fastcopy-update.dat data_len=0
|
FastCopy.exe | 0002.40: status=200
|
FastCopy.exe | 0002.40: payload(0/200) = err=
|
FastCopy.exe | 0002.42: time=20180721230941
|
FastCopy.exe | 0002.42: ver=3.52 path=/archive/FastCopy352_installer.exe hash=32 size=1499520 ver=3.52010000/3.52010000
|