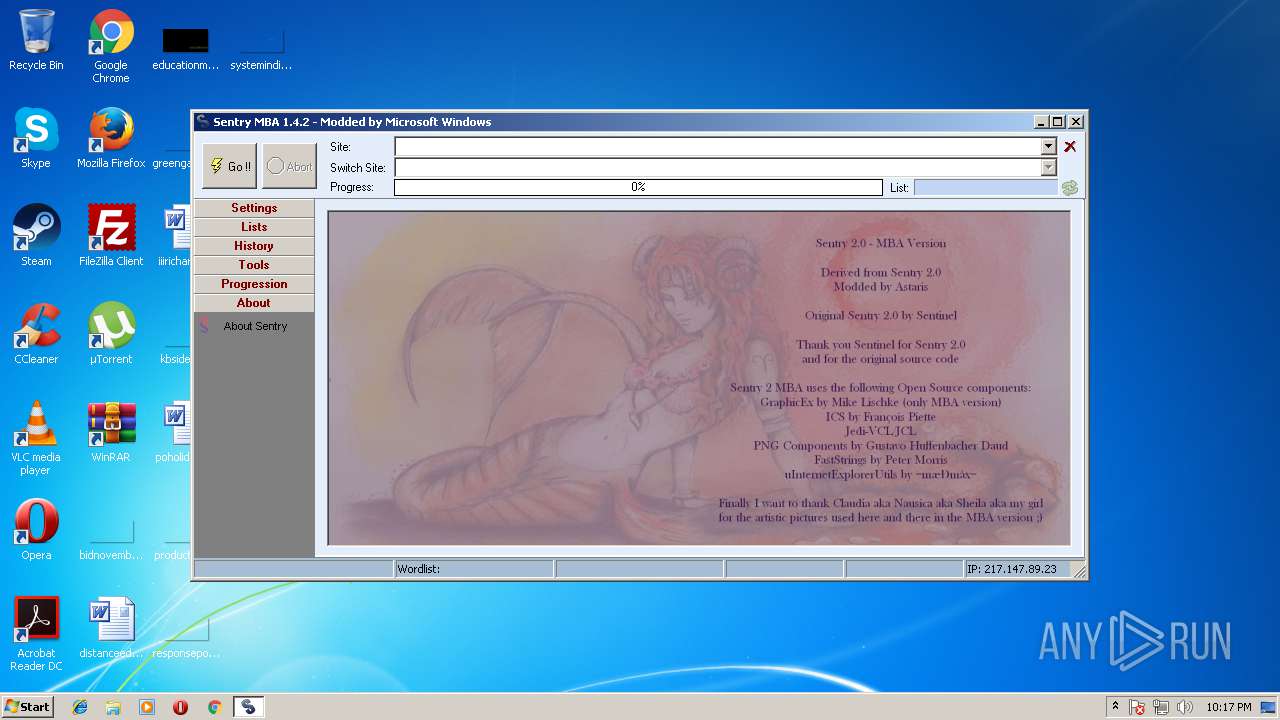
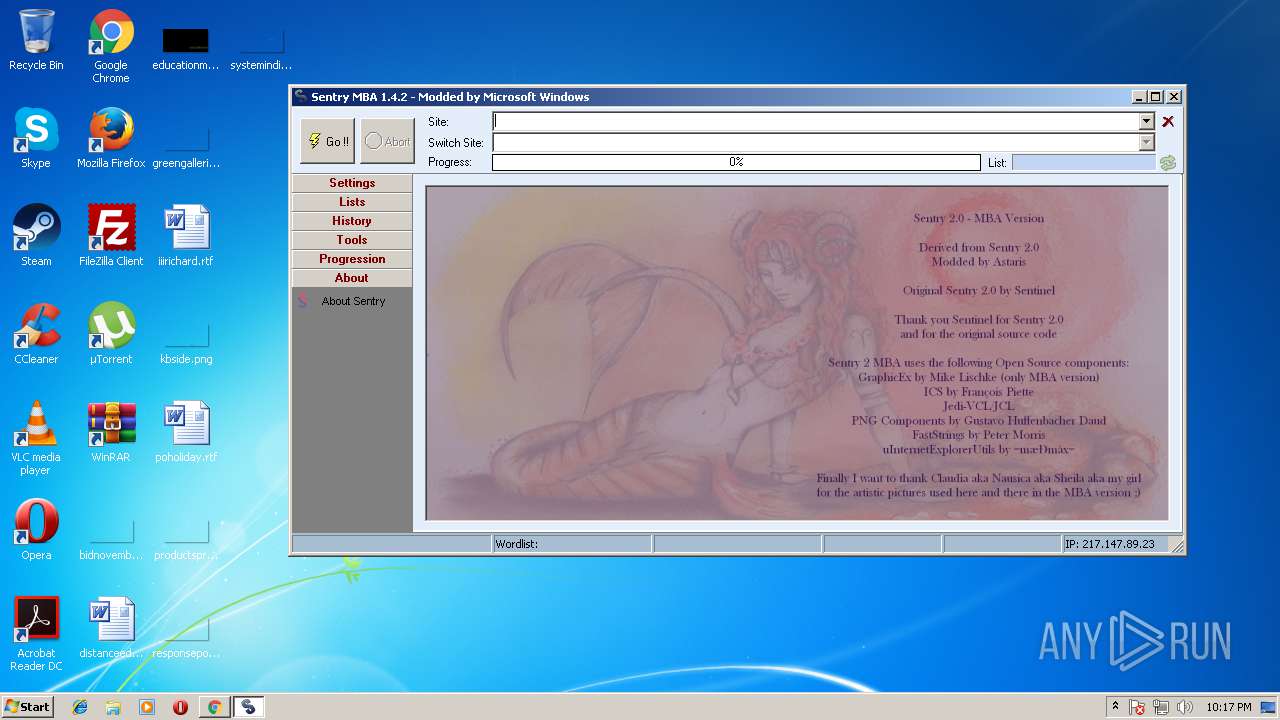
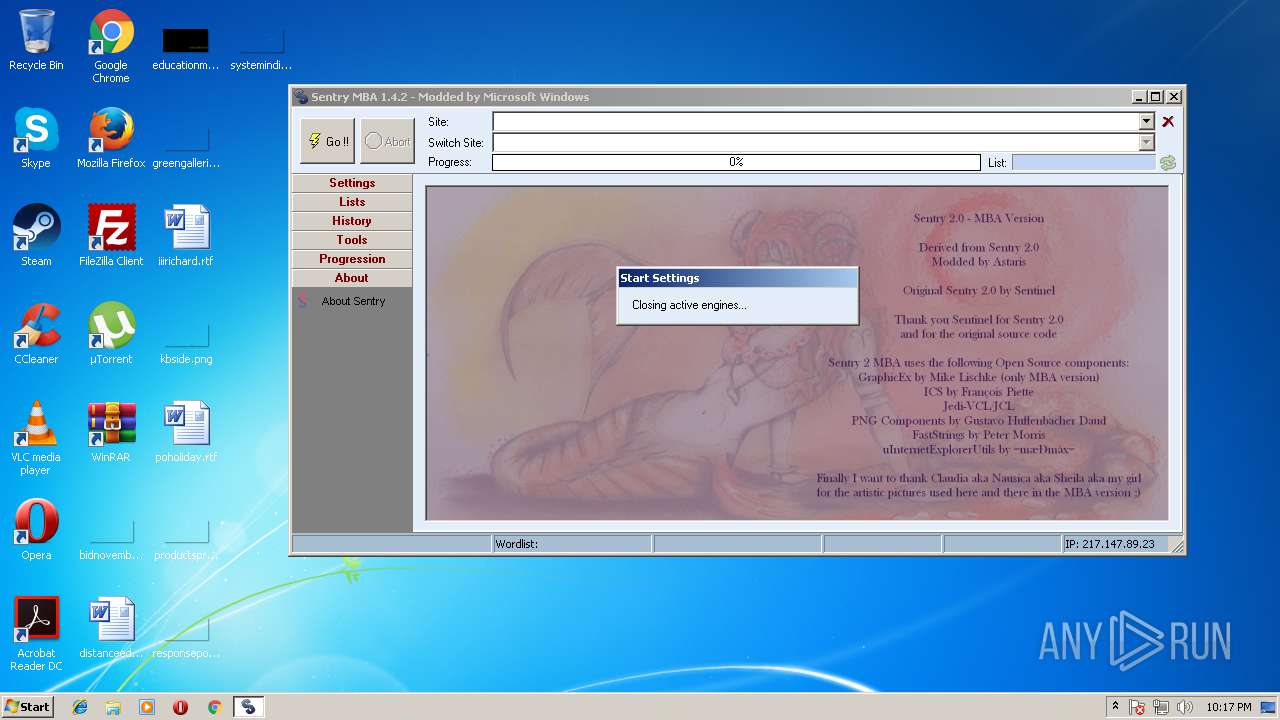
| File name: | Sentry_MBA.exe |
| Full analysis: | https://app.any.run/tasks/0cdcf6e9-5d6a-417a-94f7-3debd56de55c |
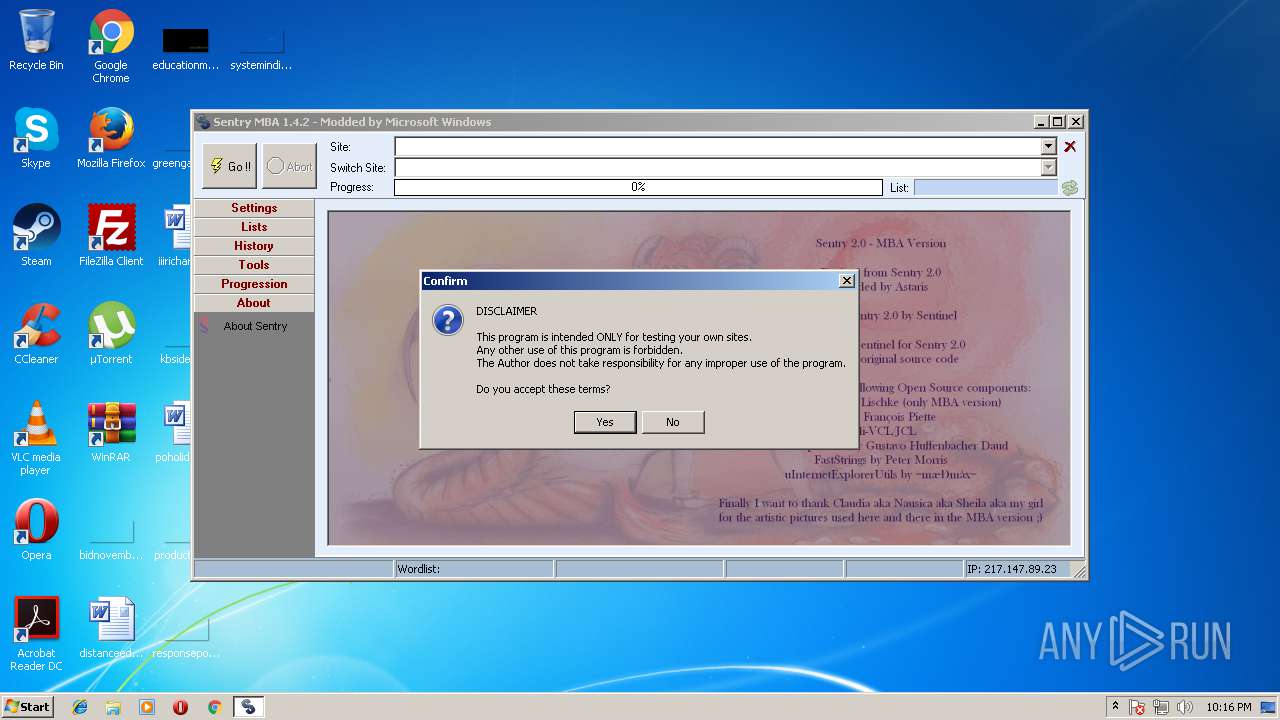
| Verdict: | Suspicious activity |
| Analysis date: | August 16, 2018, 21:16:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 93717BC3E83724F34667B7E0E296D3D0 |
| SHA1: | E8FAE634F0144ED47957EB6B66A6AE4F4D85AE8C |
| SHA256: | E0D9265D78BCB9F73A8744DA0F4DB60DB5FF67B3467890E0B02EEAD5C0A1335A |
| SSDEEP: | 98304:PD4ET113p6hnHcn84Ull604Qqdwl+C9d/F/Wwze48:PPzEhnHcn84Ull604QqdwlH9d/FeMe48 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks for external IP
- Sentry_MBA.exe (PID: 3292)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (39.3) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (38) |
| .exe | | | Win32 Executable Delphi generic (12.9) |
| .exe | | | Win32 Executable (generic) (4.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 3416576 |
| InitializedDataSize: | 2518528 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x342f90 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.2.0 |
| ProductVersionNumber: | 1.4.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | - |
| FileDescription: | Sentry MBA |
| FileVersion: | 1.4.2 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | 1.4.2 |
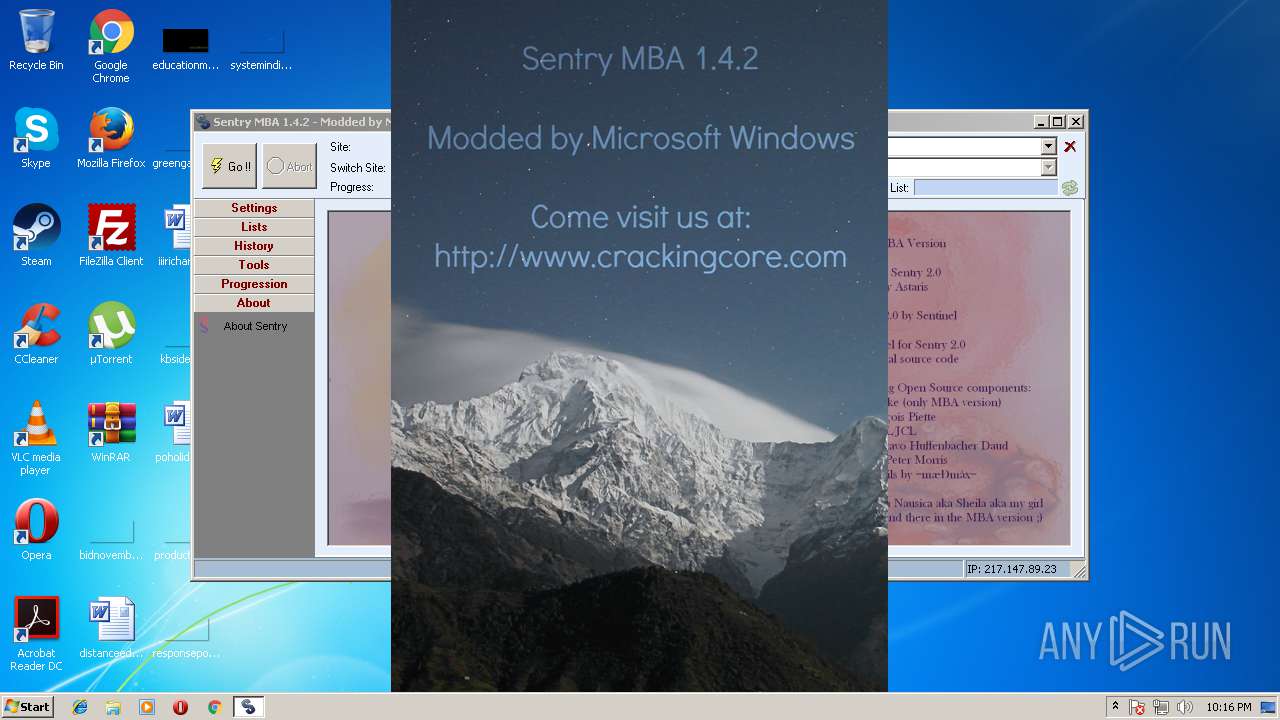
| Comments: | Sentry MBA 1.4.2 - Modded by Microsoft Windows |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | - |
| FileDescription: | Sentry MBA |
| FileVersion: | 1.4.2 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | 1.4.2 |
| Comments: | Sentry MBA 1.4.2 - Modded by Microsoft Windows |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0034200C | 0x00342200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59638 |
DATA | 0x00344000 | 0x0003D6FC | 0x0003D800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.08181 |
BSS | 0x00382000 | 0x00012BE5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00395000 | 0x0000340A | 0x00003600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.81997 |
.tls | 0x00399000 | 0x0000001C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0039A000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.210826 |
.reloc | 0x0039B000 | 0x00028DAC | 0x00028E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.7153 |
.rsrc | 0x003C4000 | 0x001FCEA9 | 0x001FD000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.63765 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.95218 | 581 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.55456 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 3.63604 | 38056 | UNKNOWN | English - United States | RT_ICON |
4 | 3.67148 | 21640 | UNKNOWN | English - United States | RT_ICON |
5 | 3.72219 | 16936 | UNKNOWN | English - United States | RT_ICON |
6 | 3.82507 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.9077 | 4264 | UNKNOWN | English - United States | RT_ICON |
8 | 3.96927 | 2440 | UNKNOWN | English - United States | RT_ICON |
9 | 4.41708 | 1128 | UNKNOWN | English - United States | RT_ICON |
10 | 2.57172 | 308 | UNKNOWN | Italian - Italy | RT_CURSOR |
Imports
MsVfW32.dll |
advapi32.dll |
avifil32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3292 | "C:\Users\admin\AppData\Local\Temp\Sentry_MBA.exe" | C:\Users\admin\AppData\Local\Temp\Sentry_MBA.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Sentry MBA Exit code: 0 Version: 1.4.2 Modules
| |||||||||||||||
Total events
3
Read events
3
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3292 | Sentry_MBA.exe | C:\Users\admin\AppData\Local\Temp\Settings.ini | text | |
MD5:3D67D78D1D95AA4269D3265993A86E92 | SHA256:0D5E59DFEDF3762891C60A13B5C3D8AAE9F2D889AEA3BC60A631B2339242D60D | |||
| 3292 | Sentry_MBA.exe | C:\Users\admin\AppData\Local\Temp\History.ini | text | |
MD5:D0DBB4B69023577481808EA914FDF880 | SHA256:3F3AE6F85D022C669F9977E4C7A5AB80A1AB61C4A3C782E96FB65B1BBAEF318A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3292 | Sentry_MBA.exe | GET | 200 | 162.88.96.194:80 | http://checkip.dyndns.org/ | PL | html | 105 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3292 | Sentry_MBA.exe | 162.88.96.194:80 | checkip.dyndns.org | Dynamic Network Services, Inc. | PL | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkip.dyndns.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1092 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.dyndns. Domain |
3292 | Sentry_MBA.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup - checkip.dyndns.org |
3292 | Sentry_MBA.exe | Potentially Bad Traffic | ET POLICY DynDNS CheckIp External IP Address Server Response |