| URL: | https://cn.bing.com/images/search?view=detailV2&id=55B6ADD5C3A08DC7D2131F399EC2965B038C2B27&thid=OIP.2zCBvgk06rIqjIoXuFpAjQHaIM&exph=990&expw=895&q=Medical+Science+Liaison+&selectedindex=216&ajaxhist=0&vt=0&ccid=2zCBvgk0&simid=608019750690491995&mediaurl=http://blog.rpharms.com/wp-content/uploads/2019/05/Sinead.jpg&sim=11 |
| Full analysis: | https://app.any.run/tasks/397f1127-89e9-40da-aa22-e2e2a5f9e91e |
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2020, 12:08:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EF1C58D774CE6DE1FA8E610BBE36F2F9 |
| SHA1: | C190538FBBFA141C2E95B1B5E4288E36DD7CC1A0 |
| SHA256: | E0D4F517F94F7F23917F12E76824C76394F8D83DF9A6A211F27997F41A9727C2 |
| SSDEEP: | 6:2W8W1MjHAfvBvMWMrkvvNg9YiyF+k4N6ywQeny2IfuHYNfrDWLdiVOlAZGFe:2/MGHAfJkHEy98F94wyCxIeurDWLdgEE |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 348)
Changes internet zones settings
- iexplore.exe (PID: 348)
Creates files in the user directory
- iexplore.exe (PID: 2864)
- iexplore.exe (PID: 348)
Reads settings of System Certificates
- iexplore.exe (PID: 2864)
- iexplore.exe (PID: 348)
Reads Internet Cache Settings
- iexplore.exe (PID: 2864)
- iexplore.exe (PID: 348)
Reads internet explorer settings
- iexplore.exe (PID: 2864)
Changes settings of System certificates
- iexplore.exe (PID: 348)
Adds / modifies Windows certificates
- iexplore.exe (PID: 348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://cn.bing.com/images/search?view=detailV2&id=55B6ADD5C3A08DC7D2131F399EC2965B038C2B27&thid=OIP.2zCBvgk06rIqjIoXuFpAjQHaIM&exph=990&expw=895&q=Medical+Science+Liaison+&selectedindex=216&ajaxhist=0&vt=0&ccid=2zCBvgk0&simid=608019750690491995&mediaurl=http://blog.rpharms.com/wp-content/uploads/2019/05/Sinead.jpg&sim=11" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:348 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
5 795
Read events
609
Write events
3 470
Delete events
1 716
Modification events
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 815343316 | |||
| (PID) Process: | (348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30805004 | |||
| (PID) Process: | (348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
53
Text files
174
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabE0A4.tmp | — | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE0A5.tmp | — | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BDN4UM0F.txt | — | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\R5B4JG02.txt | — | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\XHNRCTNH.txt | — | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\W62U69ZT.txt | — | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\05FB85Y2.txt | — | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\Z1JMUHZU.txt | — | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\zFu6kibiZnkuaiI4GHP_YKwOYDQ[1].css | text | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\search[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
89
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2864 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2864 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
2864 | iexplore.exe | GET | 200 | 2.21.242.197:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
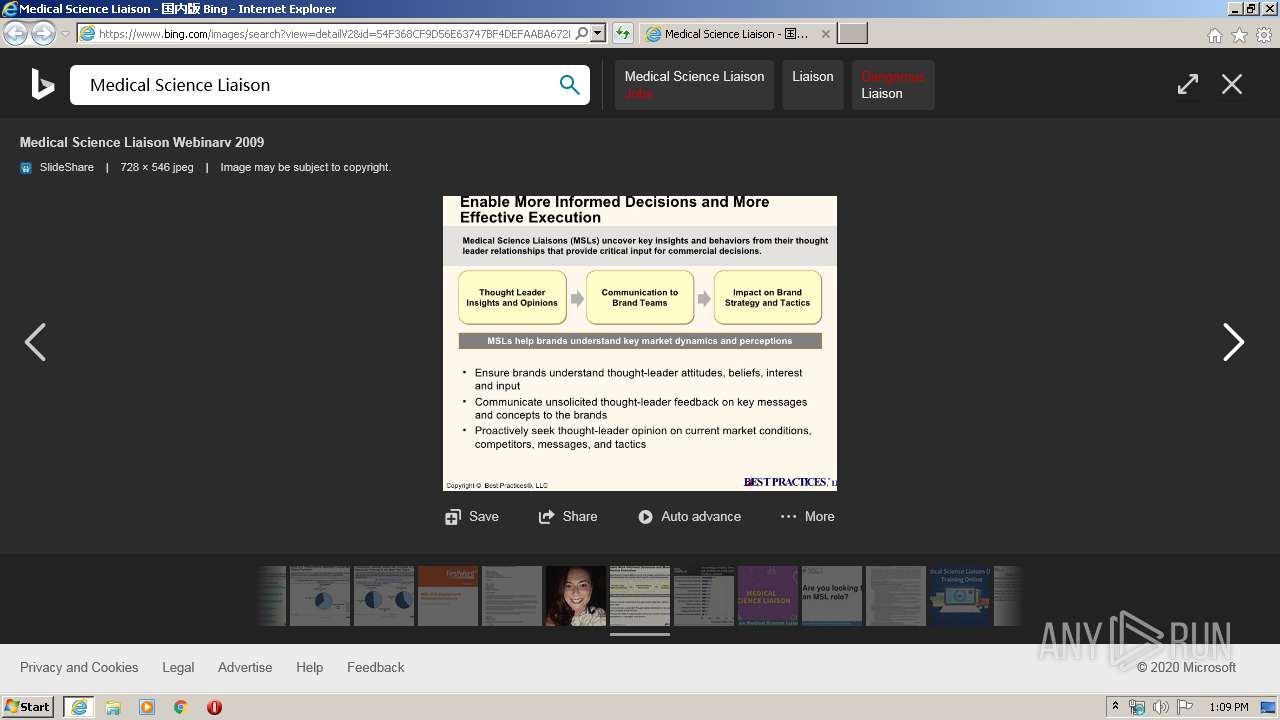
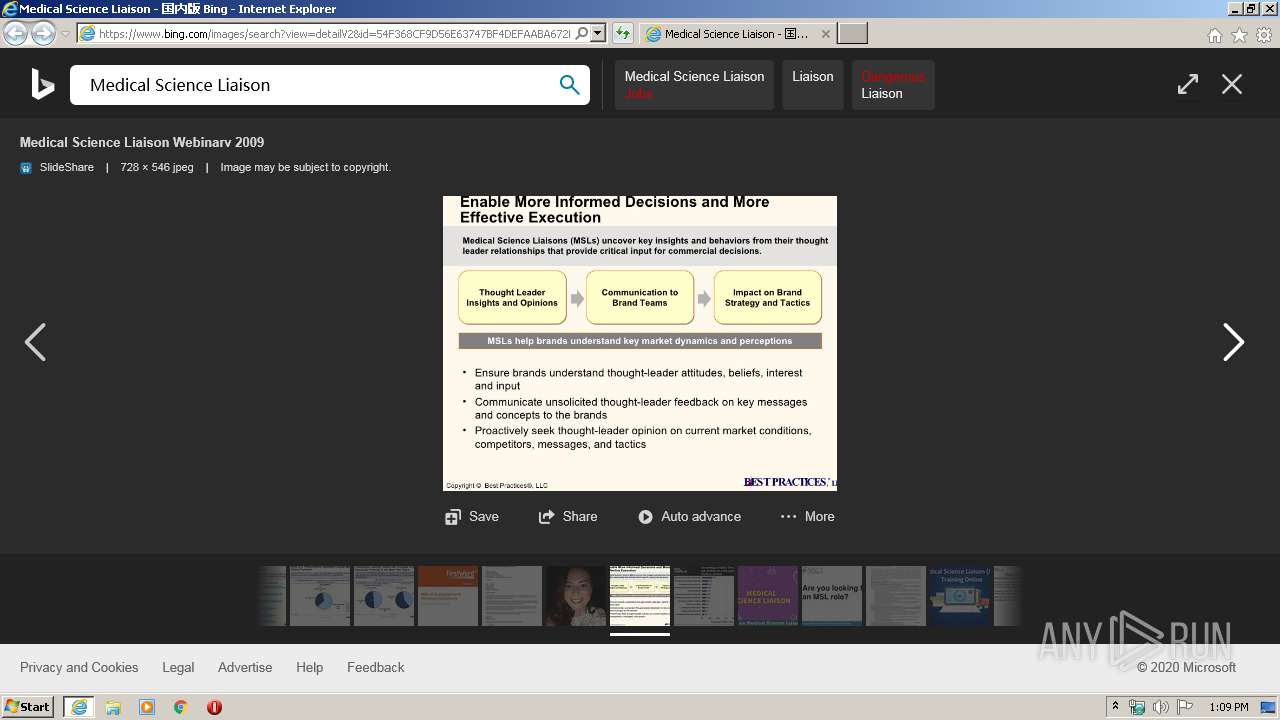
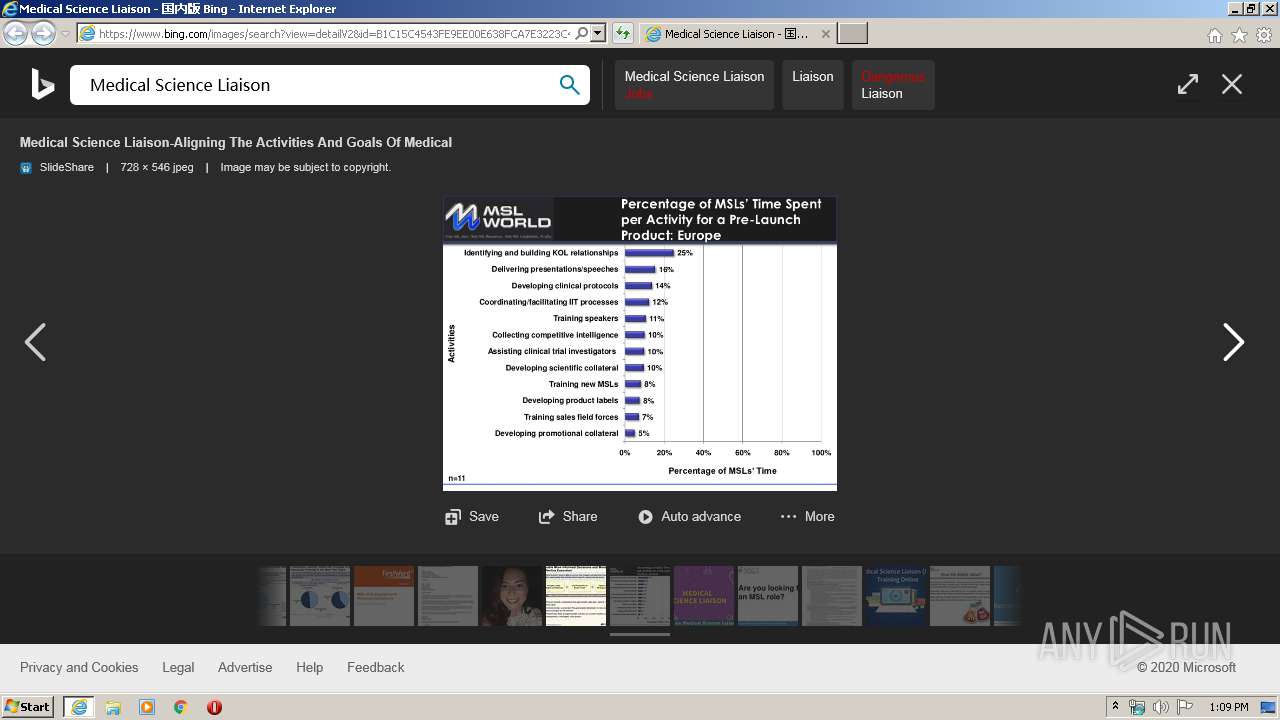
2864 | iexplore.exe | GET | 200 | 92.122.254.166:80 | http://image.slidesharecdn.com/mslwebinarv22009-124899576844-phpapp02/95/medical-science-liaison-webinarv-2009-7-728.jpg?cb=1248977911 | unknown | image | 109 Kb | suspicious |
2864 | iexplore.exe | GET | 200 | 13.225.87.155:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2864 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2864 | iexplore.exe | GET | 200 | 13.225.87.98:80 | http://crl.rootca1.amazontrust.com/rootca1.crl | US | der | 439 b | whitelisted |
2864 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEQDwHUvue3yjezwFZqwFlyRY | US | der | 728 b | whitelisted |
2864 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAzrHNjfpYB7QzlaS35YKq8%3D | US | der | 471 b | whitelisted |
2864 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2864 | iexplore.exe | 104.18.14.176:443 | i.pinimg.com | Cloudflare Inc | US | shared |
2864 | iexplore.exe | 35.197.245.96:80 | blog.rpharms.com | Google Inc. | US | unknown |
2864 | iexplore.exe | 54.165.64.41:443 | www.filepicker.io | Amazon.com, Inc. | US | unknown |
2864 | iexplore.exe | 2.21.242.197:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | whitelisted |
2864 | iexplore.exe | 13.225.87.155:80 | o.ss2.us | — | US | unknown |
348 | iexplore.exe | 204.79.197.200:443 | cn.bing.com | Microsoft Corporation | US | whitelisted |
2864 | iexplore.exe | 204.79.197.200:443 | cn.bing.com | Microsoft Corporation | US | whitelisted |
2864 | iexplore.exe | 92.122.254.166:443 | image.slidesharecdn.com | GTT Communications Inc. | — | unknown |
2864 | iexplore.exe | 92.122.254.166:80 | image.slidesharecdn.com | GTT Communications Inc. | — | unknown |
2864 | iexplore.exe | 13.225.87.98:80 | crl.rootca1.amazontrust.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cn.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
tse4.mm.bing.net |
| whitelisted |
tse2.mm.bing.net |
| whitelisted |
tse1.mm.bing.net |
| whitelisted |
tse3.mm.bing.net |
| whitelisted |
image.slidesharecdn.com |
| suspicious |
i.pinimg.com |
| whitelisted |
blog.rpharms.com |
| unknown |