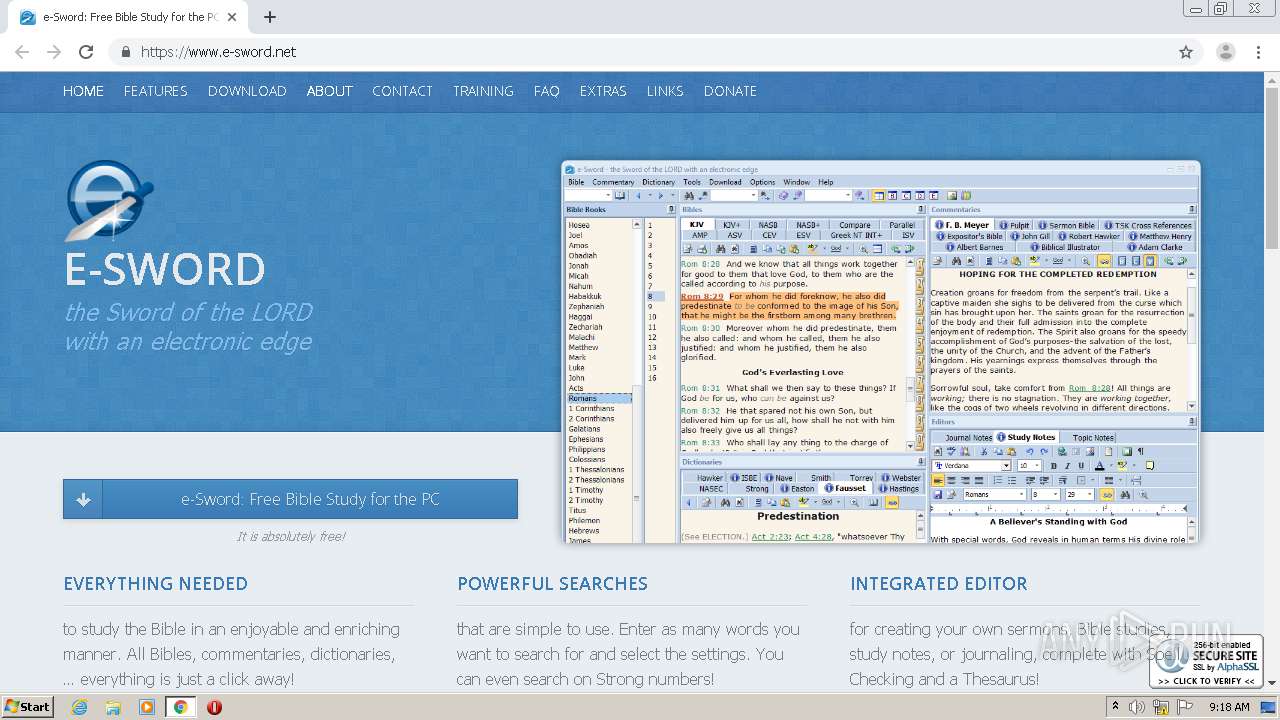
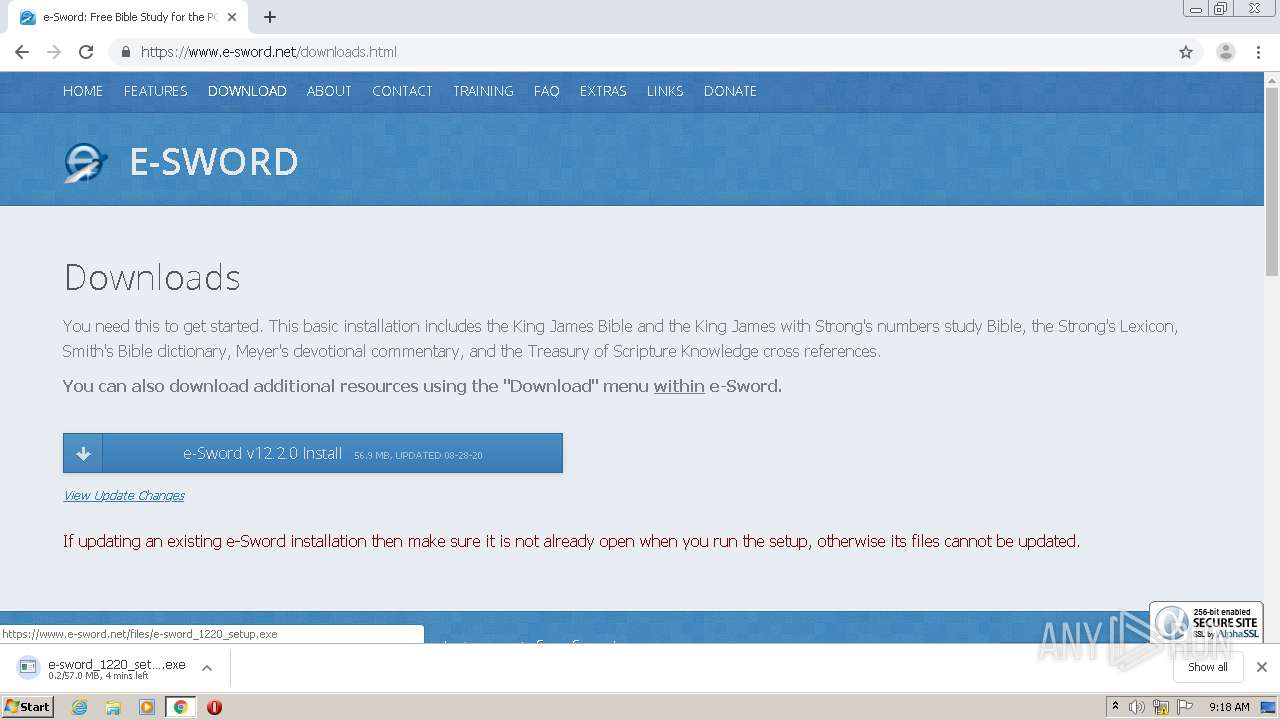
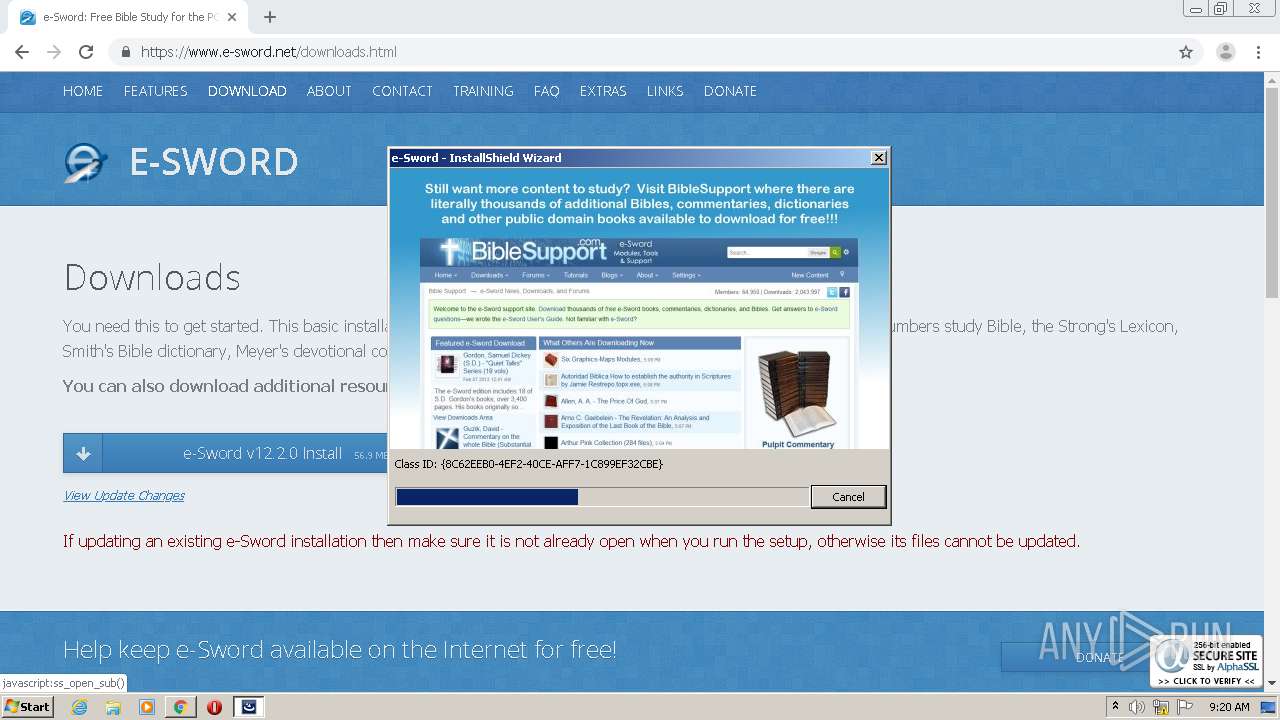
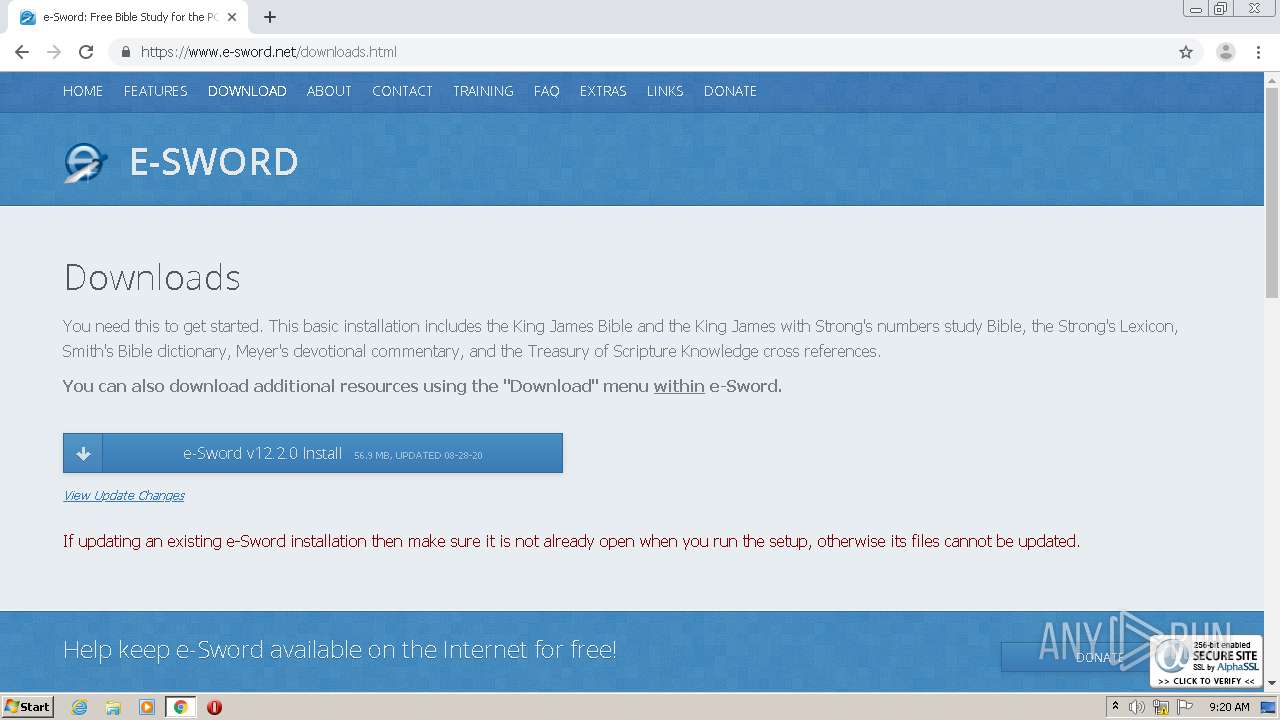
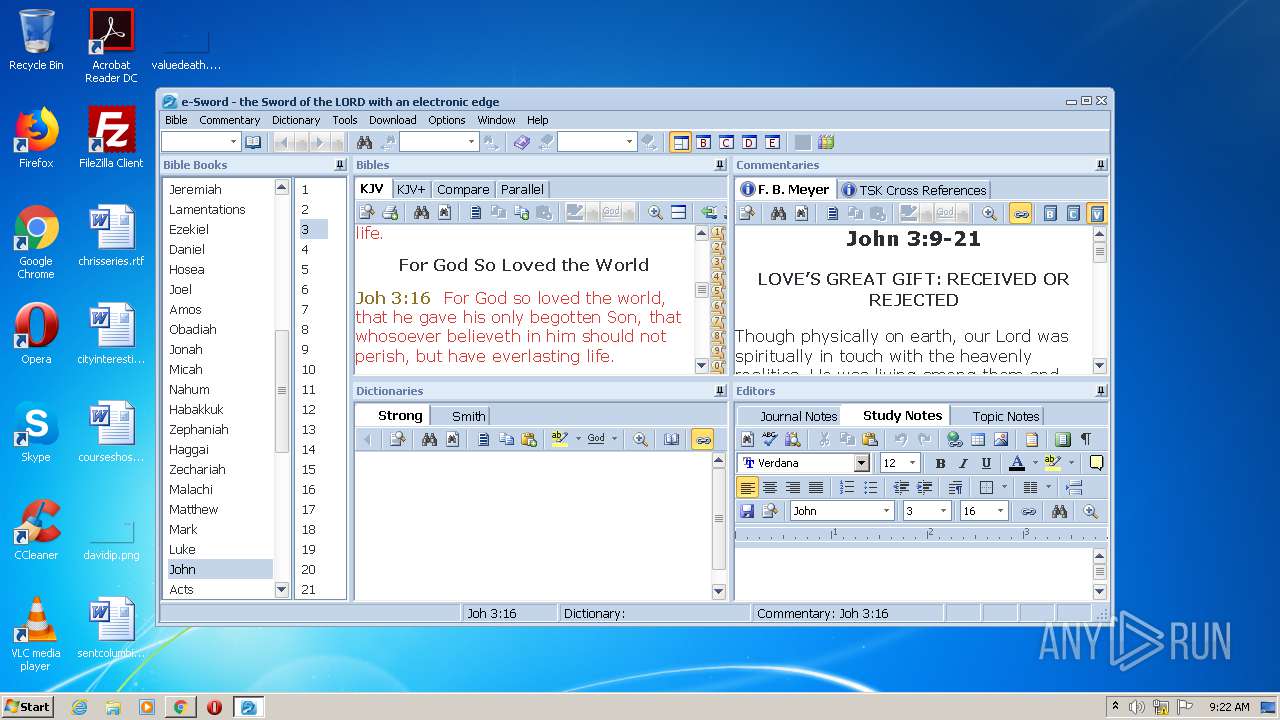
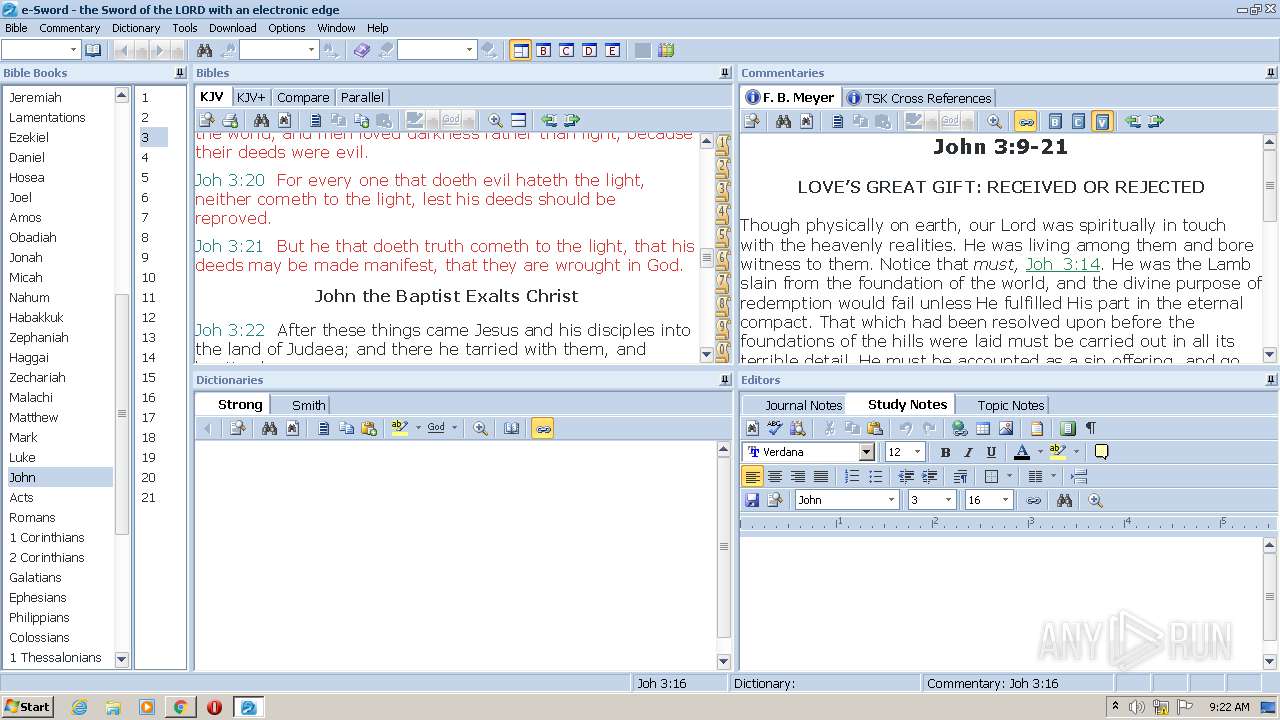
| URL: | https://www.e-sword.net/ |
| Full analysis: | https://app.any.run/tasks/8ee72b6d-395d-4d3a-9ef8-5aa7d4ddb5bd |
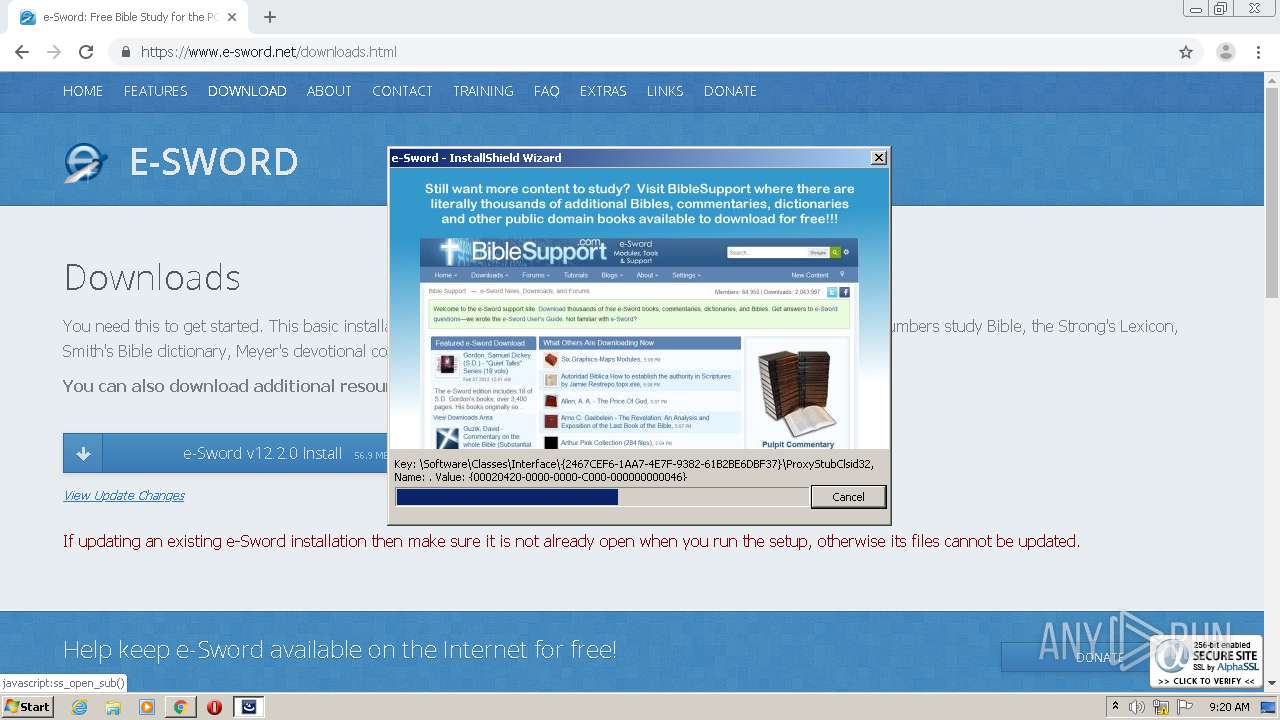
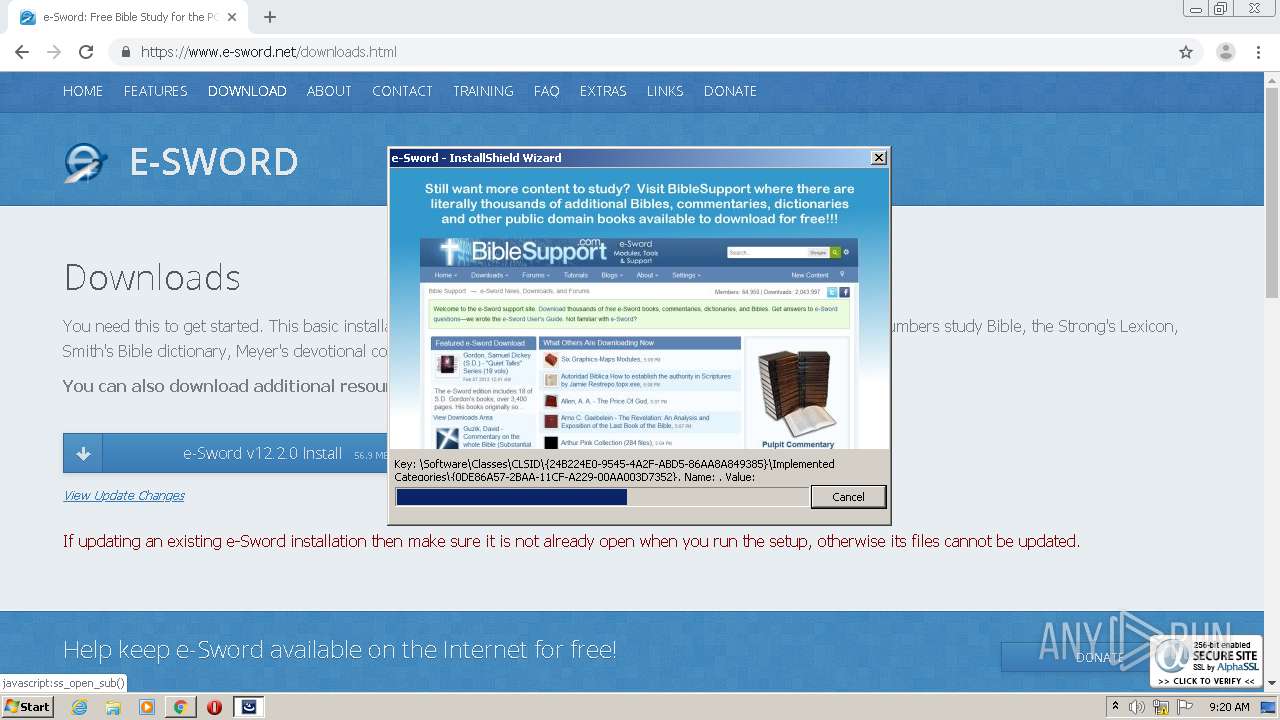
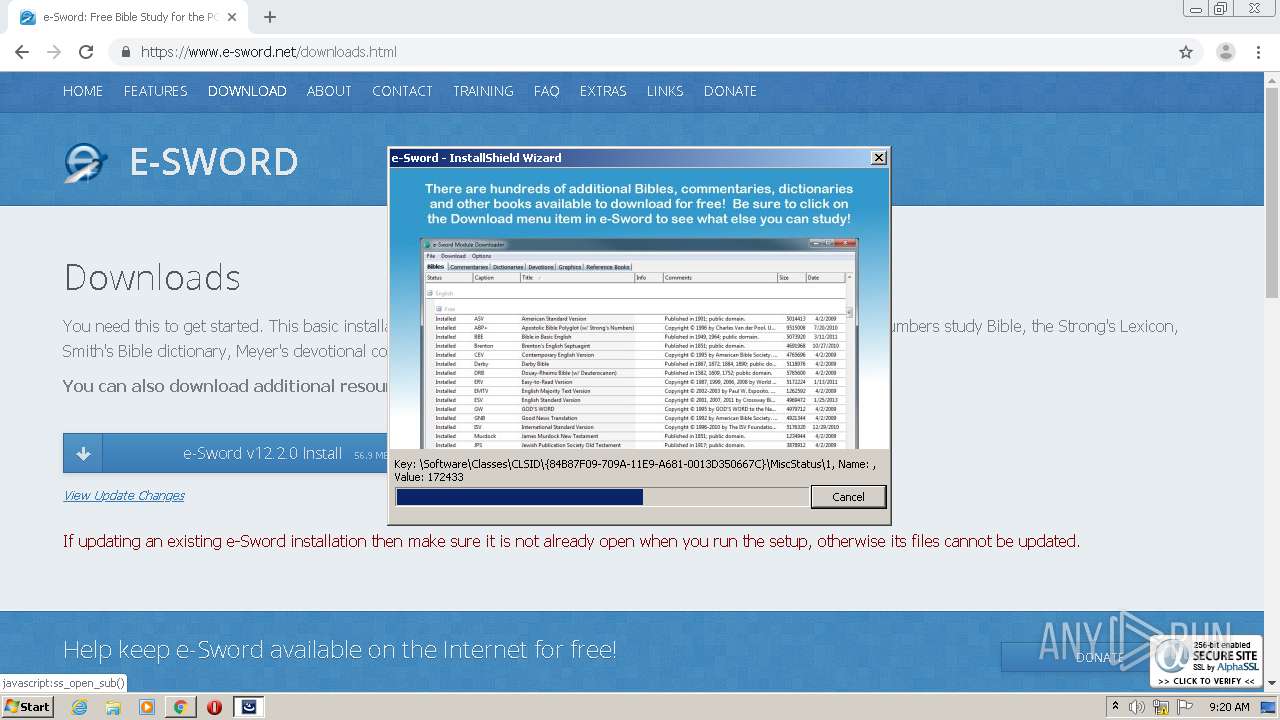
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 08:17:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 66766E7BABA792665BDB3FB6D15966F7 |
| SHA1: | 7169C78A92D2DBBE517A79C8893421E9EF6F4170 |
| SHA256: | E0C59590CE54F39D3B88D0D544895F717831521CD104966B9C7113235A8422CE |
| SSDEEP: | 3:N8DSLkARK:2OLk0K |
MALICIOUS
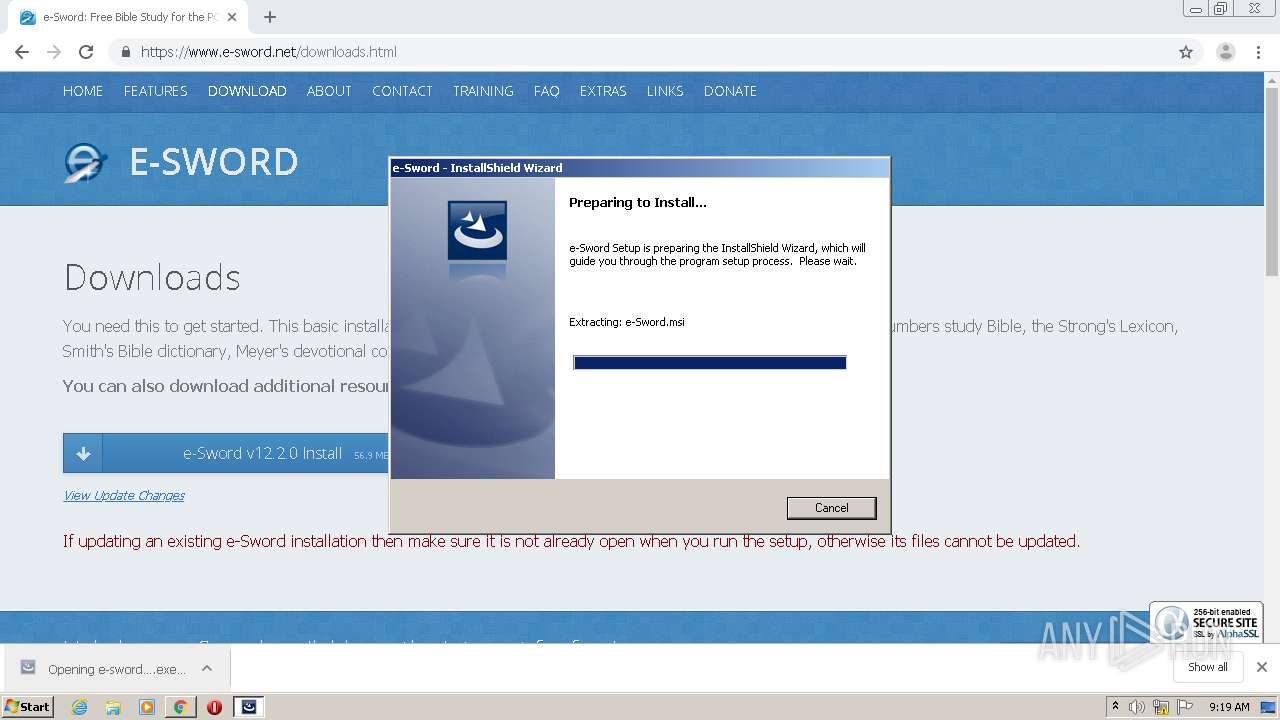
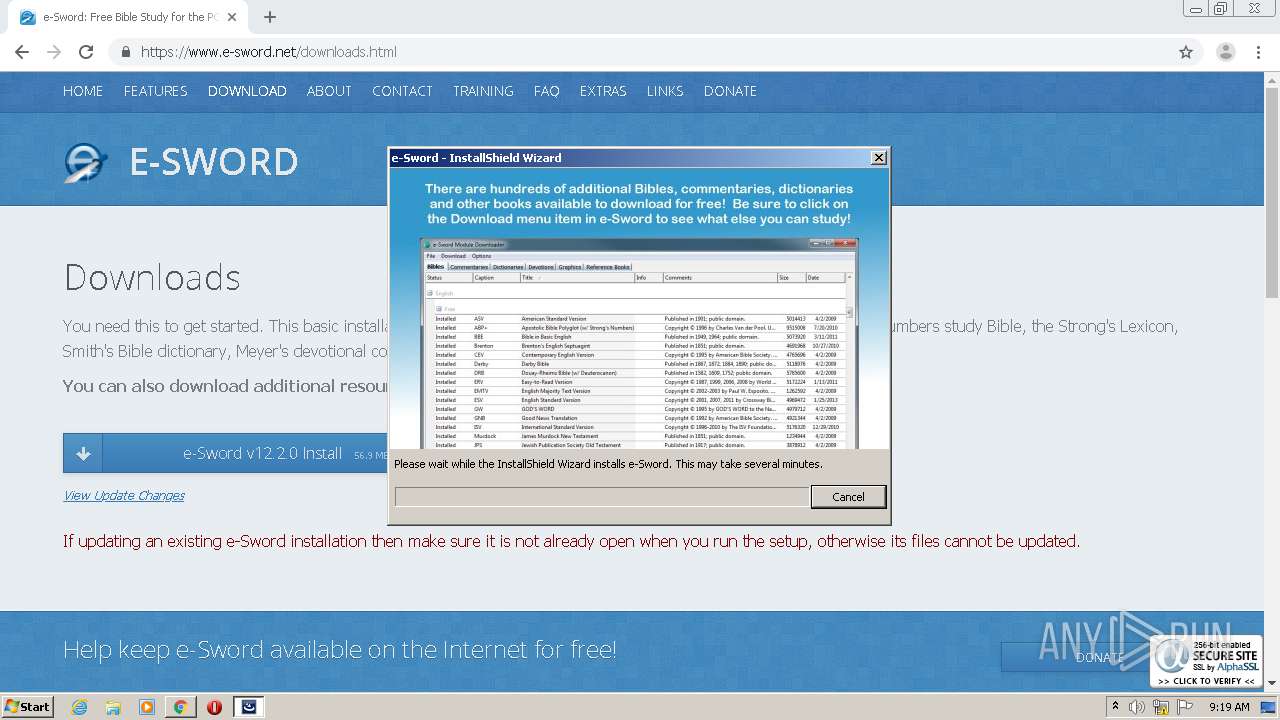
Application was dropped or rewritten from another process
- e-sword_1220_setup.exe (PID: 928)
- e-sword_1220_setup.exe (PID: 2848)
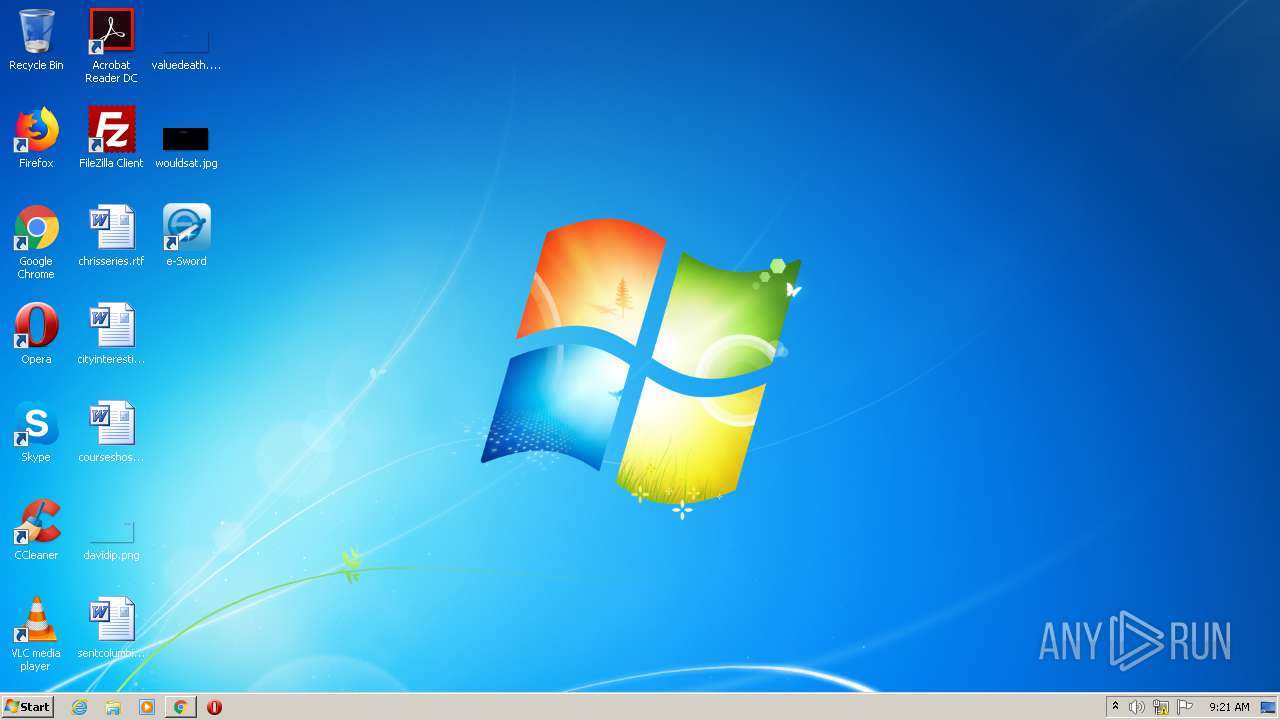
- e-Sword.exe (PID: 2756)
Loads dropped or rewritten executable
- e-Sword.exe (PID: 2756)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2544)
- e-sword_1220_setup.exe (PID: 928)
- msiexec.exe (PID: 2988)
Executed as Windows Service
- vssvc.exe (PID: 2624)
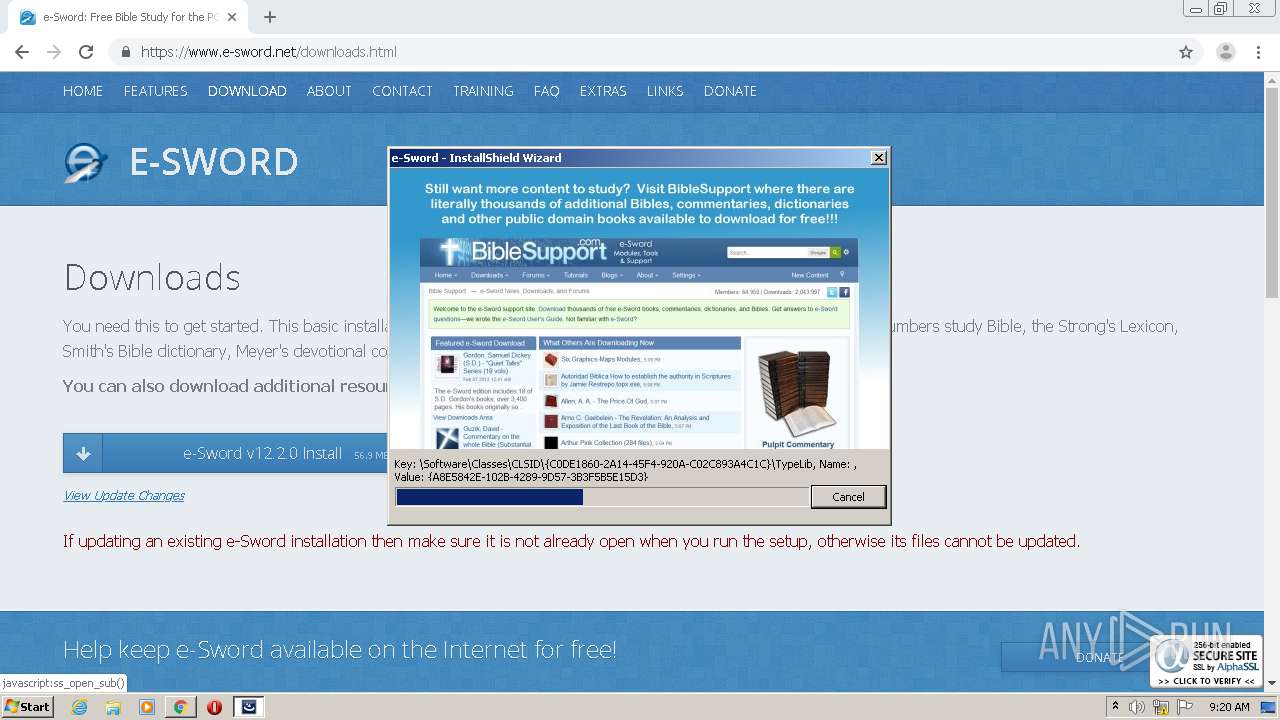
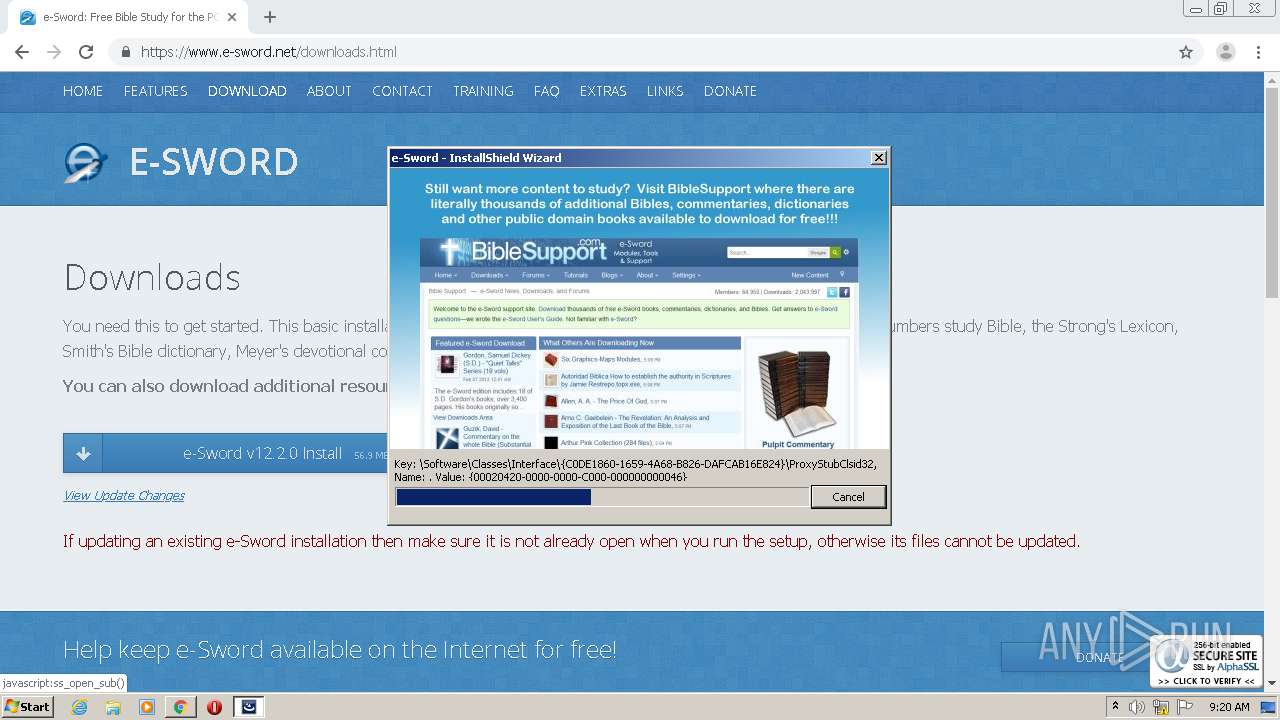
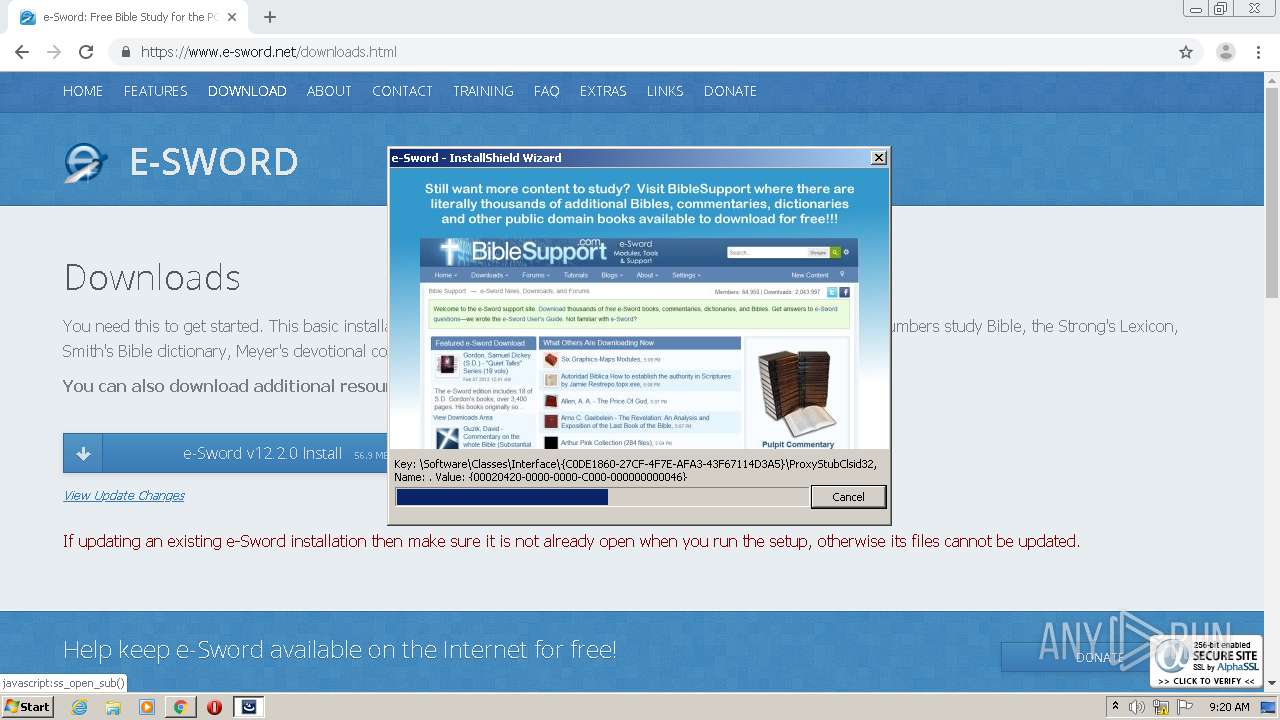
Creates COM task schedule object
- msiexec.exe (PID: 2988)
Creates files in the Windows directory
- msiexec.exe (PID: 2988)
Uses RUNDLL32.EXE to load library
- e-sword_1220_setup.exe (PID: 928)
Reads Internet Cache Settings
- e-Sword.exe (PID: 2756)
INFO
Application launched itself
- chrome.exe (PID: 2544)
- msiexec.exe (PID: 2988)
- chrome.exe (PID: 1772)
Reads the hosts file
- chrome.exe (PID: 2544)
- chrome.exe (PID: 3012)
Modifies the open verb of a shell class
- chrome.exe (PID: 2544)
Searches for installed software
- msiexec.exe (PID: 2988)
Reads Internet Cache Settings
- chrome.exe (PID: 2544)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2624)
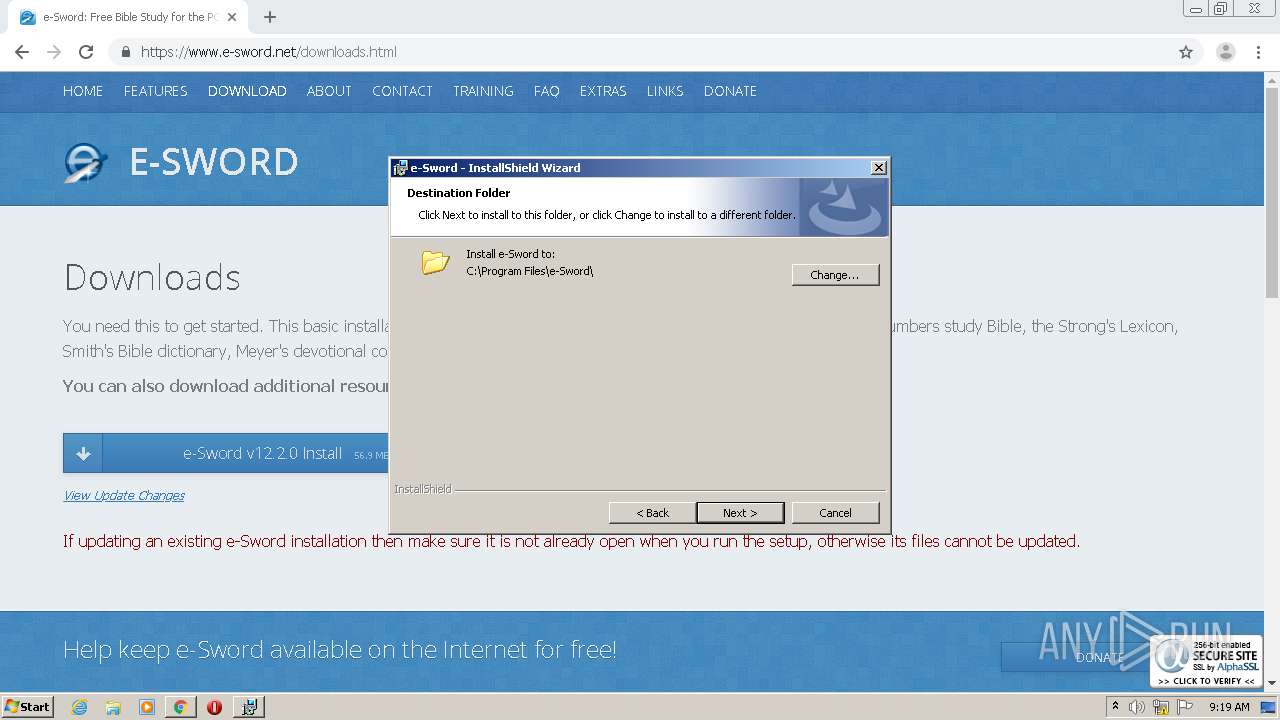
Creates files in the program directory
- msiexec.exe (PID: 2988)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2988)
Creates a software uninstall entry
- msiexec.exe (PID: 2988)
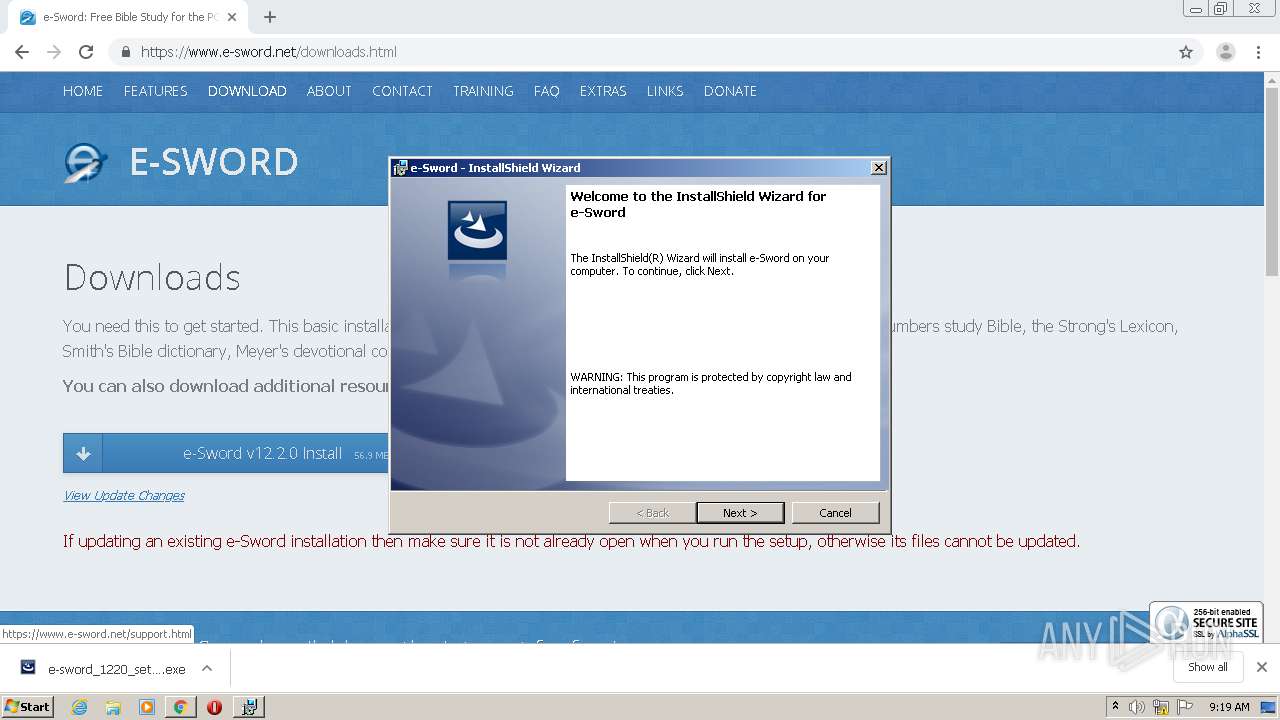
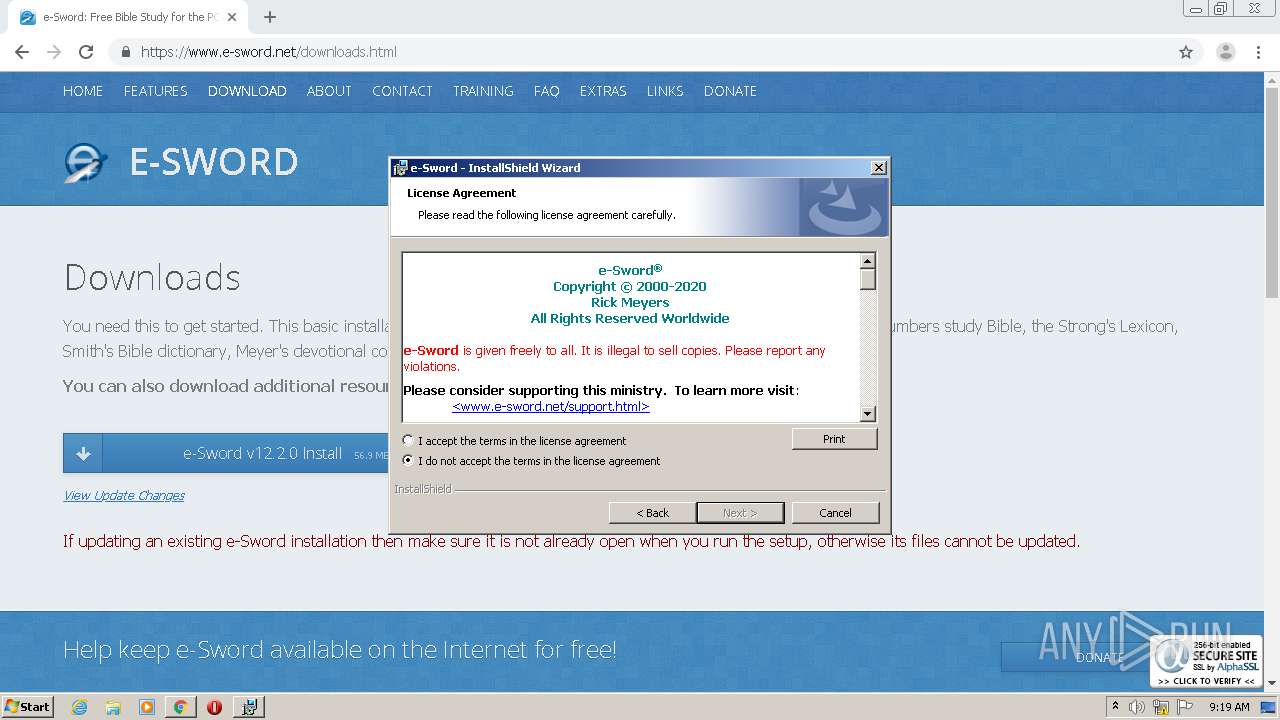
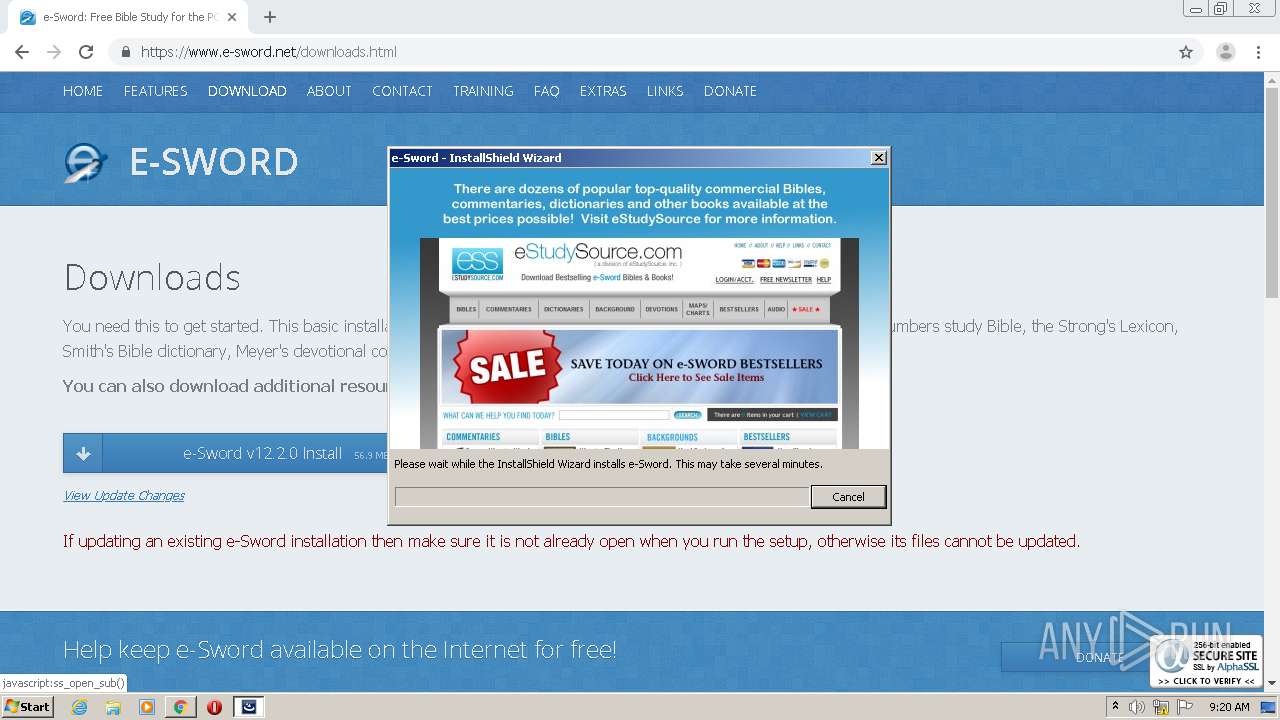
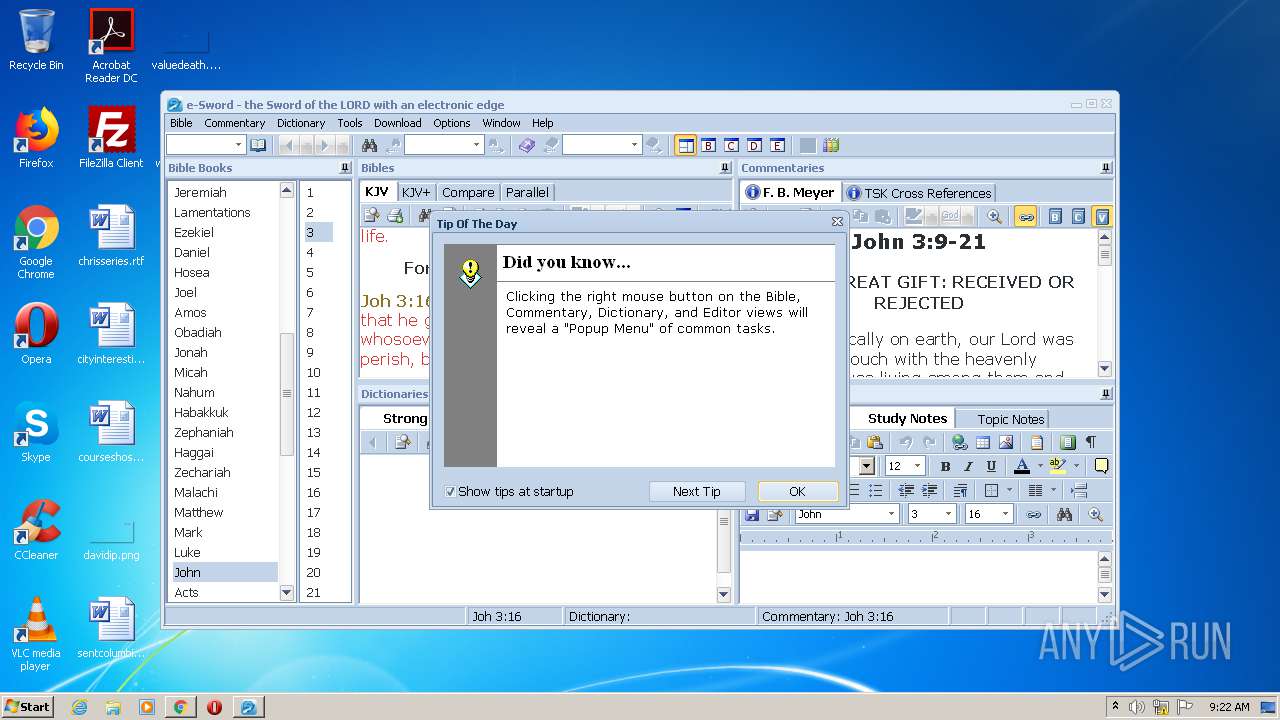
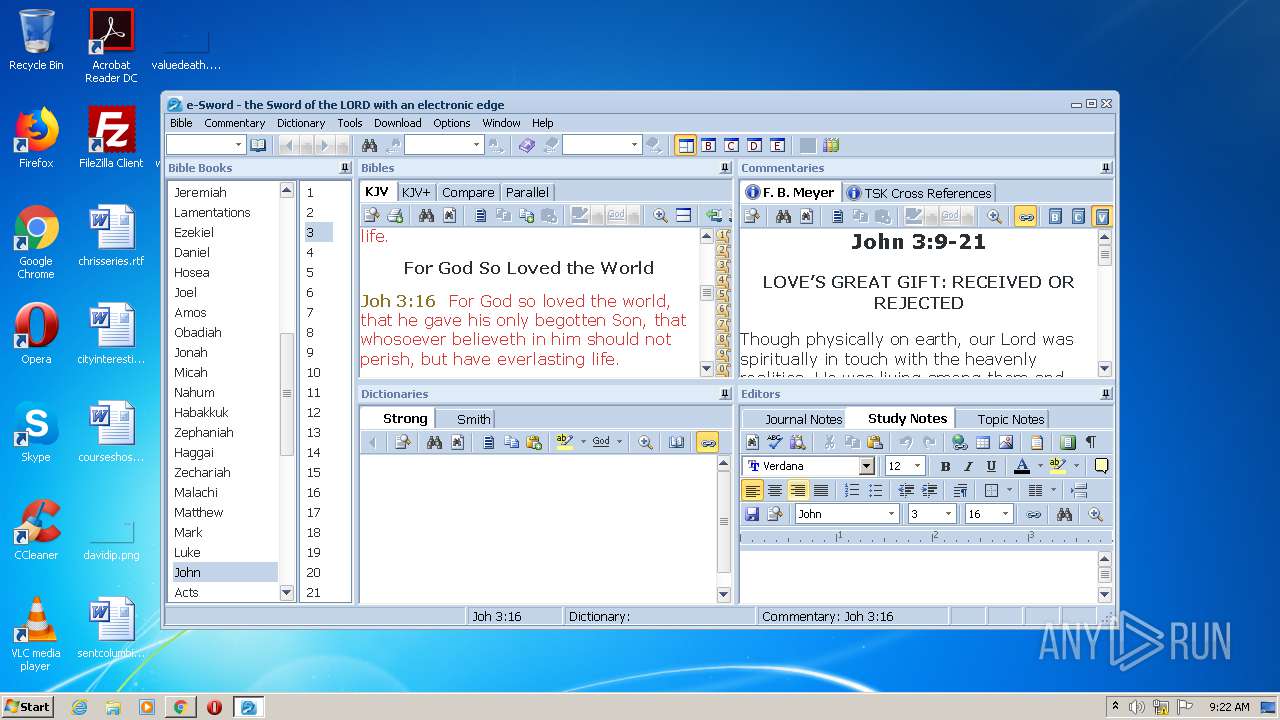
Manual execution by user
- e-Sword.exe (PID: 2756)
Reads settings of System Certificates
- chrome.exe (PID: 3012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
73
Monitored processes
31
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,6649174726863200444,12566431043744733620,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13888226089689537760 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1716 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,6649174726863200444,12566431043744733620,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17747080440795543504 --mojo-platform-channel-handle=3472 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
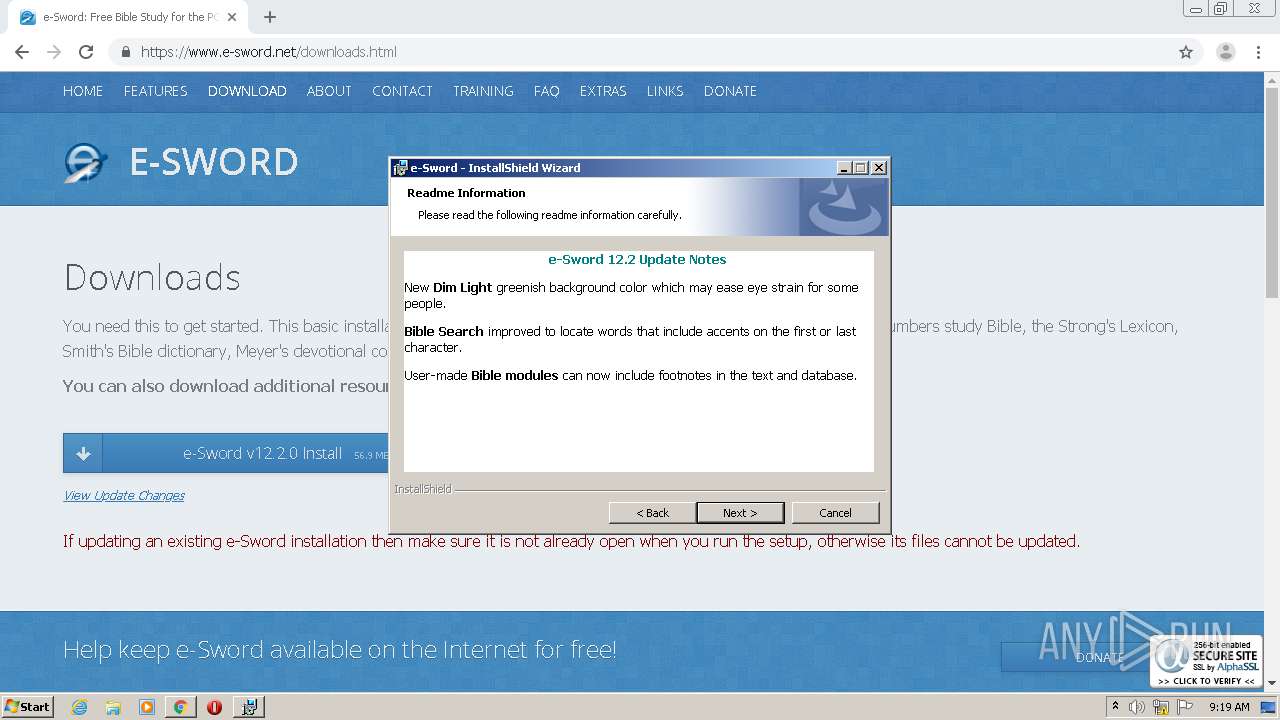
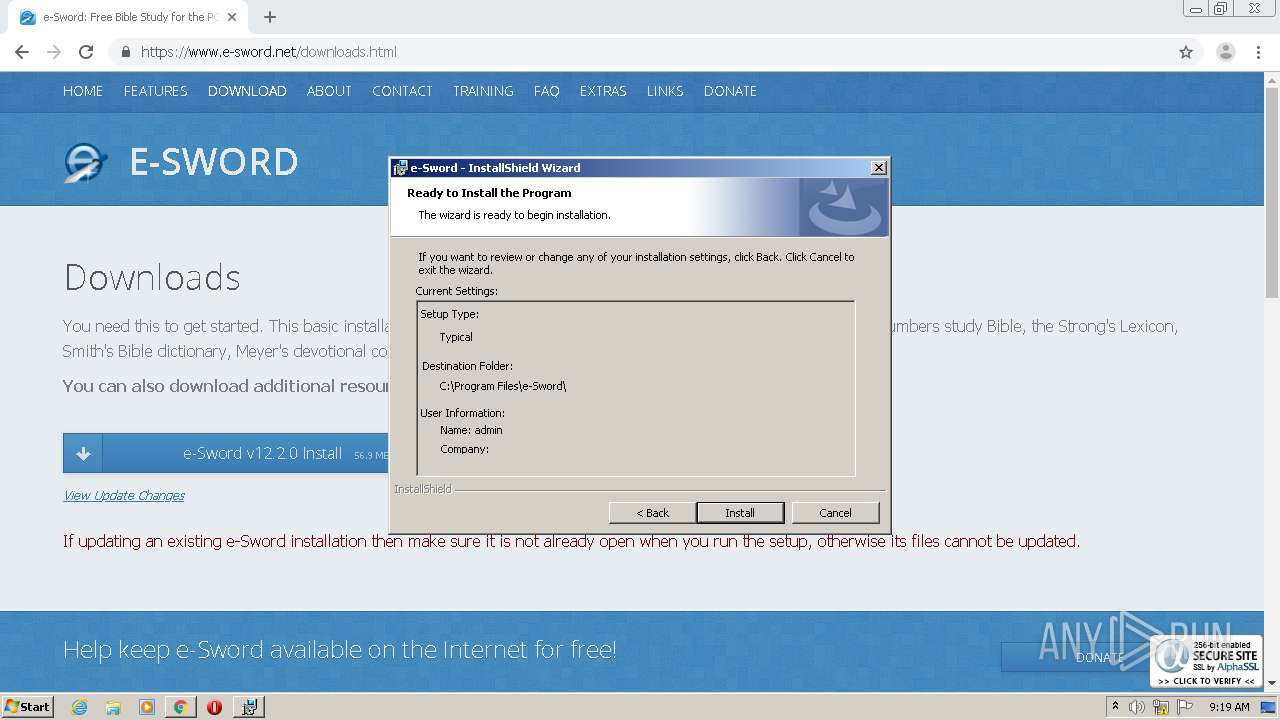
| 928 | "C:\Users\admin\Downloads\e-sword_1220_setup.exe" | C:\Users\admin\Downloads\e-sword_1220_setup.exe | chrome.exe | ||||||||||||
User: admin Company: Rick Meyers Integrity Level: HIGH Description: e-Sword Setup Exit code: 0 Version: 12.02.0000 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" -- "https://www.e-sword.net/support.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | rundll32.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,6649174726863200444,12566431043744733620,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4098584785164763084 --mojo-platform-channel-handle=1100 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,6649174726863200444,12566431043744733620,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11454690586355393883 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://www.e-sword.net/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2576 | C:\Windows\system32\MsiExec.exe -Embedding C95C42969959CFDE7D99380EBB2FA489 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,6649174726863200444,12566431043744733620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8727523139206133388 --mojo-platform-channel-handle=3496 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2624 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 799
Read events
3 893
Write events
3 885
Delete events
21
Modification events
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2544-13247569078760625 |
Value: 259 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2544-13247569078760625 |
Value: 259 | |||
Executable files
44
Suspicious files
48
Text files
142
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8D4BB7-9F0.pma | — | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bde3a722-2cd9-45ca-80d9-e17d53ff73aa.tmp | — | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:FB5B20517A0D1F7DAD485989565BEE5E | SHA256:99405F66EDBEB2306F4D0B4469DCADFF5293B5E1549C588CCFACEA439BB3B101 | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2d40c7.TMP | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:67F45CAA18C889645F50CD6216C81E65 | SHA256:33ED82CDDDFFD55A5059C147C6CD20F66C6712314F890A39576D3C10914D0029 | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 2544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:9543068B6751E1F3E11F91D72EE78D95 | SHA256:D060AD21AE6E04CB58668CAA52ADFCA573E018102CC07554D2ED3EAE11AB7785 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
32
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3012 | chrome.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/gsextendvalsha2g3r3/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBScTHEVwwIZyjbcuYshMwBMpKeO0wQU3bPnbagu6MVObs905nU8lBXO6B0CDG0wY02WiJQu7%2BtrNg%3D%3D | US | der | 1.53 Kb | whitelisted |
3012 | chrome.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDkikAt0nkg2iCDSd0Zl7 | US | der | 1.48 Kb | whitelisted |
3012 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
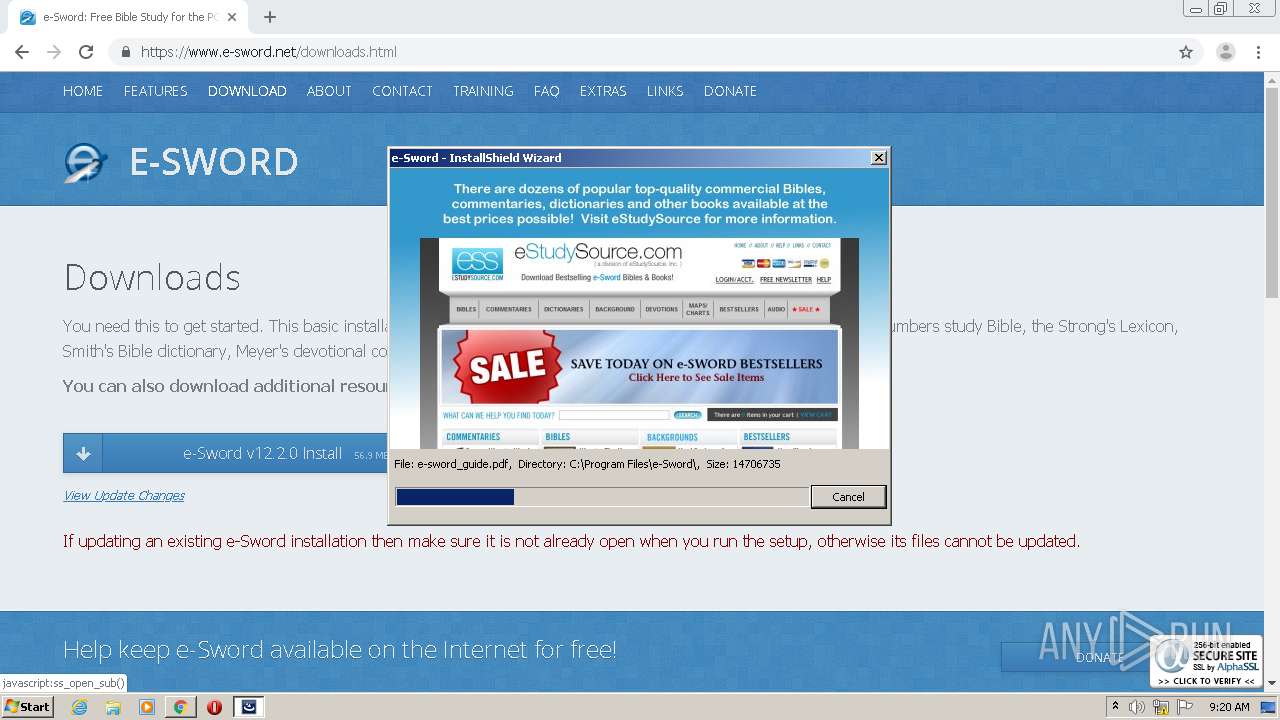
2756 | e-Sword.exe | GET | 301 | 69.39.239.211:80 | http://www.e-sword.net/blacklist.xml | US | html | 326 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3012 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 216.58.212.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 104.111.228.123:443 | www.paypalobjects.com | Akamai International B.V. | NL | unknown |
3012 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3012 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 69.39.239.211:443 | www.e-sword.net | GigeNET | US | unknown |
3012 | chrome.exe | 104.18.20.226:443 | seal.alphassl.com | Cloudflare Inc | US | shared |
3012 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 104.18.20.226:80 | seal.alphassl.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.e-sword.net |
| unknown |
accounts.google.com |
| shared |
seal.alphassl.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
clients1.google.com |
| whitelisted |