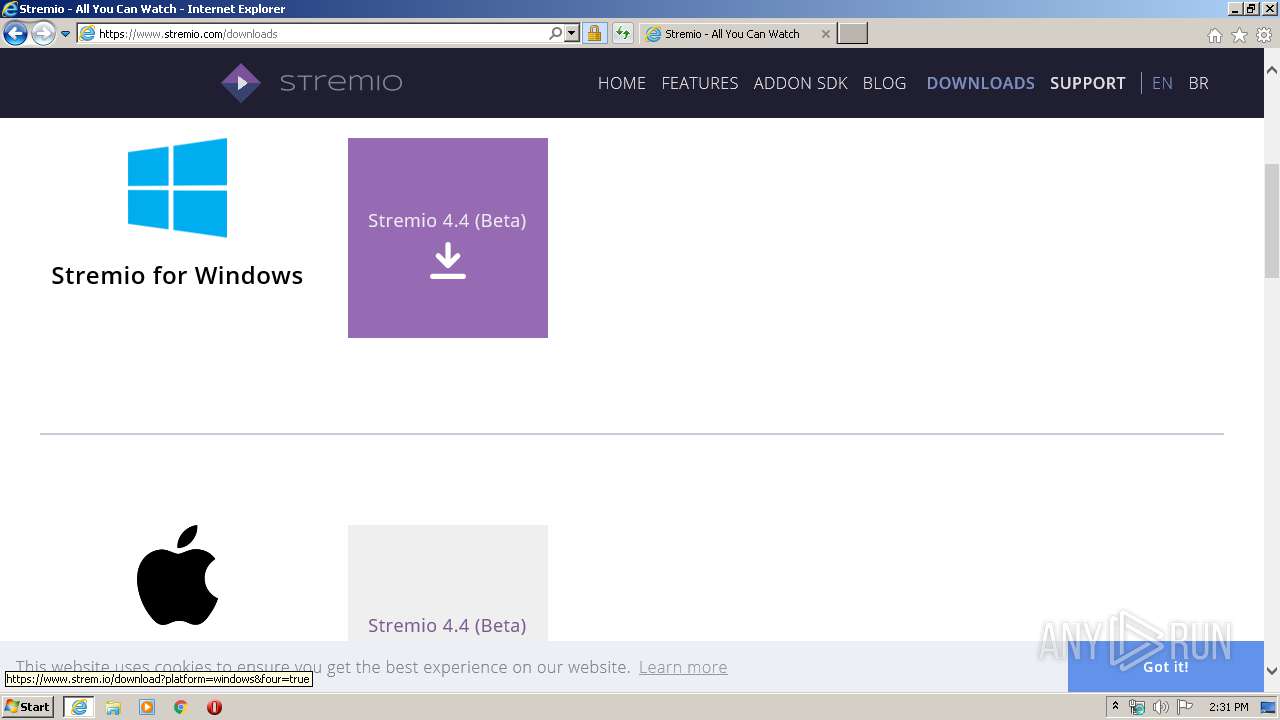
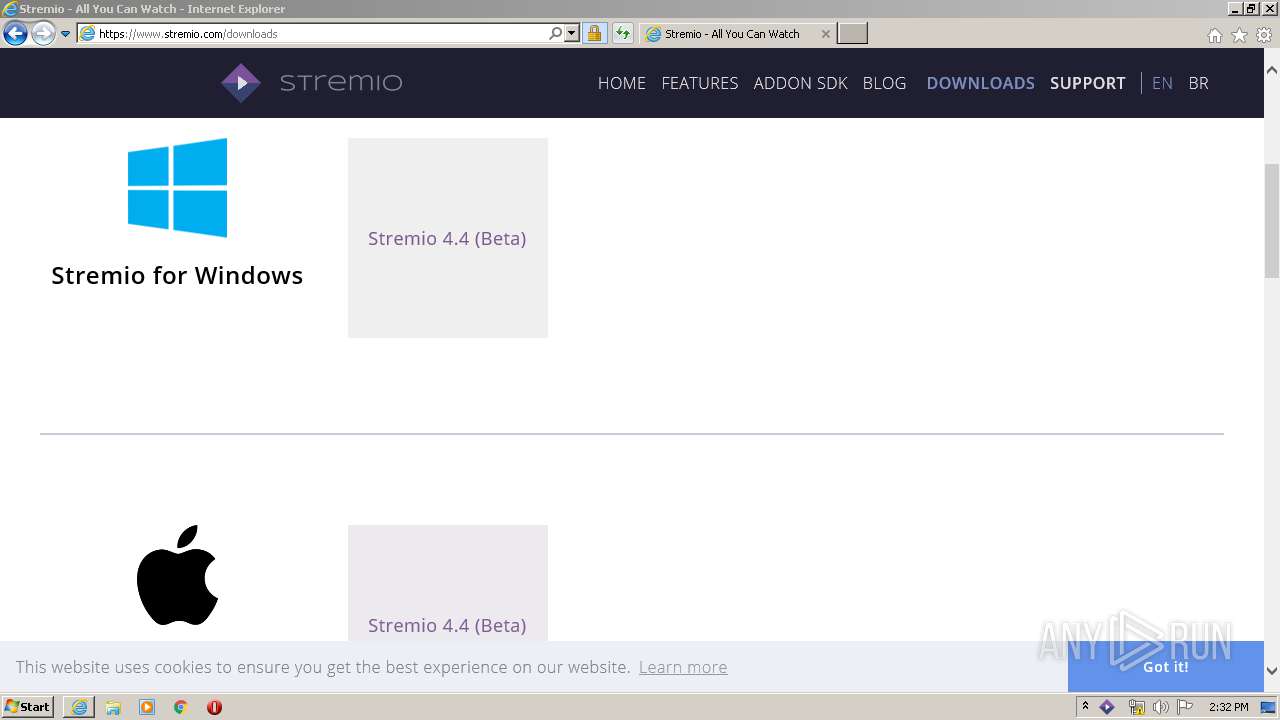
| URL: | https://stremio.com |
| Full analysis: | https://app.any.run/tasks/af3343b2-a20f-4a64-85cf-2493e80e94c0 |
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2020, 13:30:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 02F948CBE492D8E65A98425593D90943 |
| SHA1: | 708D81FA033470C4851B76E3DC440C46730BE3A3 |
| SHA256: | E0C22A532B5DED5D3E19376B379747445FF90BD96BE4AFDF2EE4CA011E1C624F |
| SSDEEP: | 3:N8cdOT:2cdOT |
MALICIOUS
Application was dropped or rewritten from another process
- QtWebEngineProcess.exe (PID: 2340)
- stremio.exe (PID: 2536)
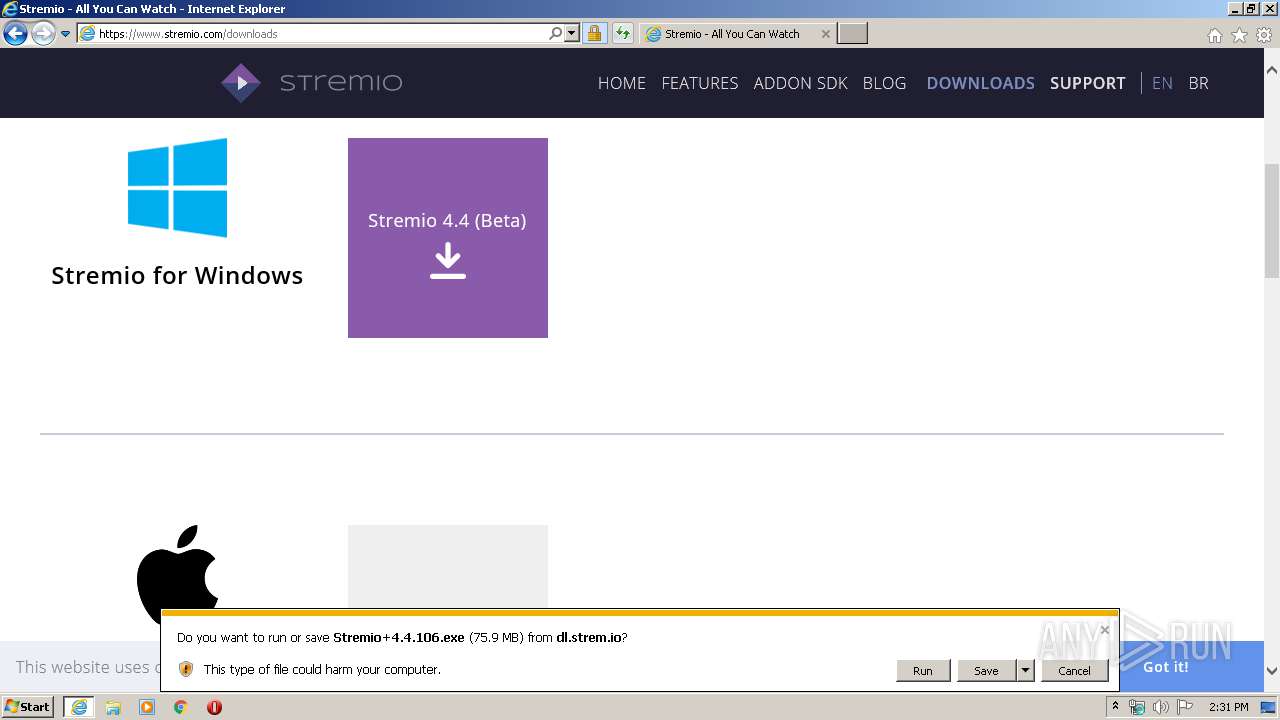
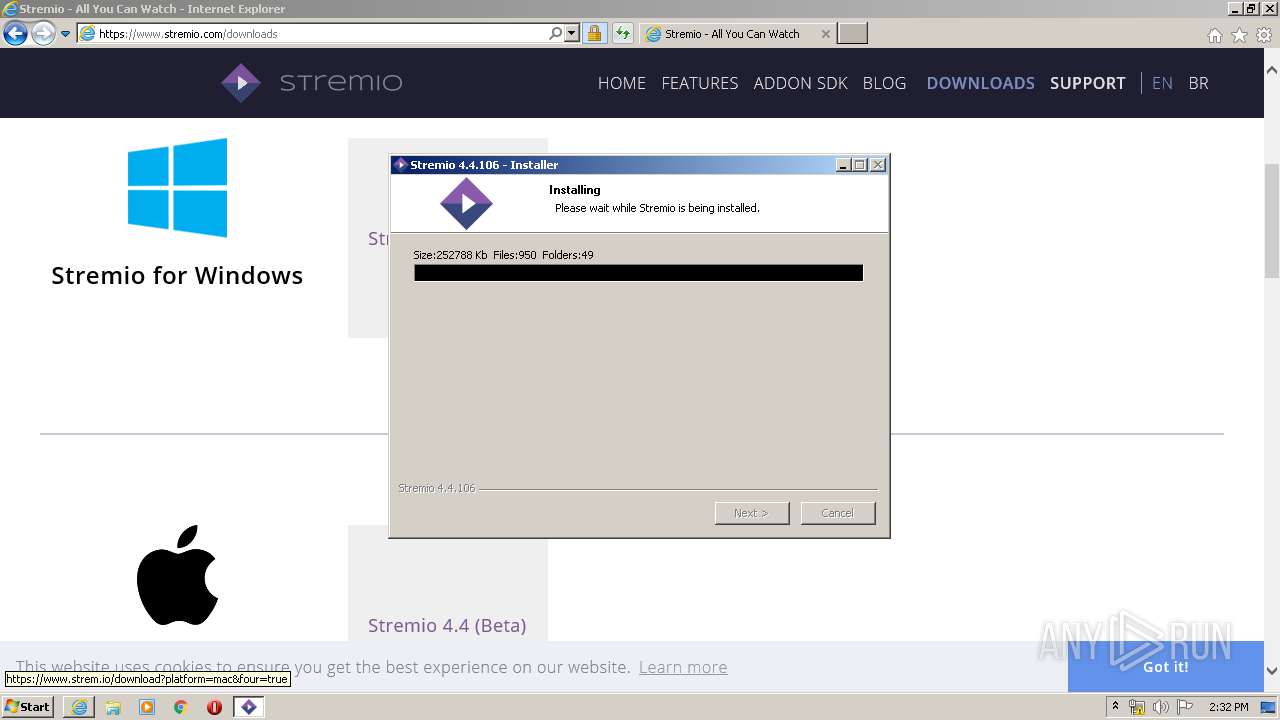
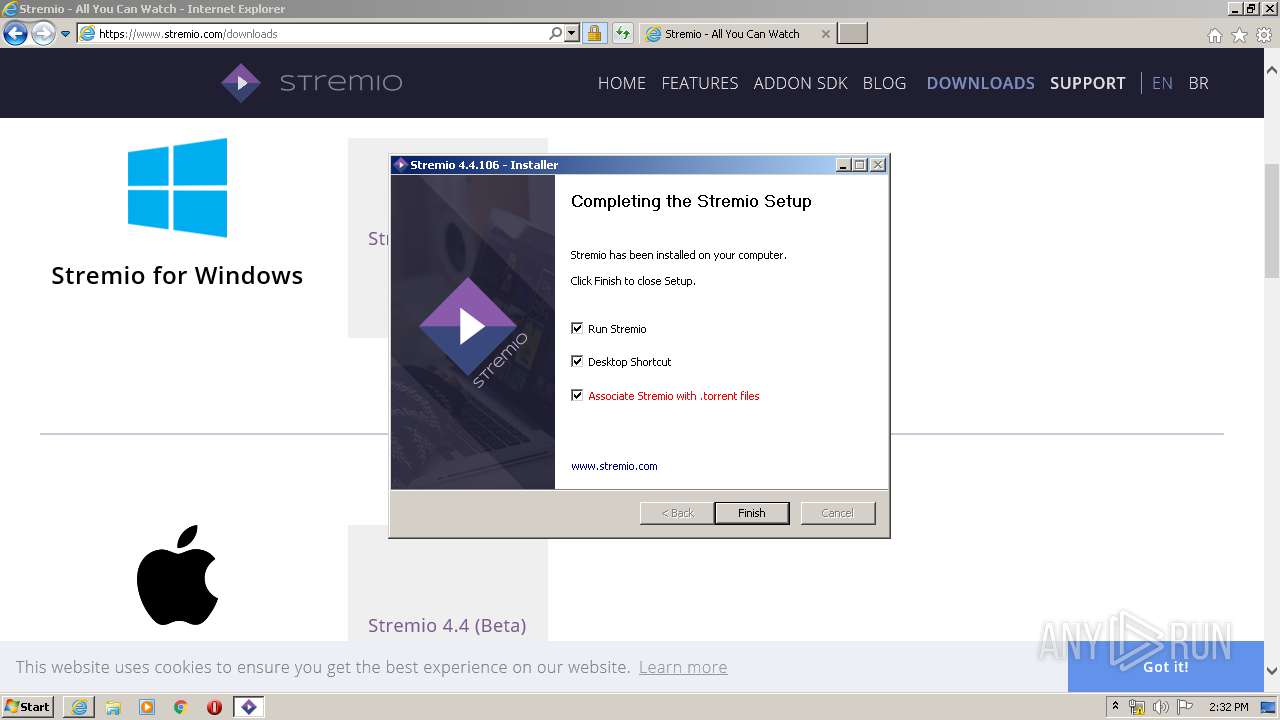
- Stremio+4.4.106.exe (PID: 3860)
Loads dropped or rewritten executable
- Stremio+4.4.106.exe (PID: 3860)
- stremio.exe (PID: 2536)
- WerFault.exe (PID: 1640)
- QtWebEngineProcess.exe (PID: 2340)
SUSPICIOUS
Executable content was dropped or overwritten
- Stremio+4.4.106.exe (PID: 3860)
Creates files in the user directory
- Stremio+4.4.106.exe (PID: 3860)
Modifies the open verb of a shell class
- Stremio+4.4.106.exe (PID: 3860)
Creates a software uninstall entry
- Stremio+4.4.106.exe (PID: 3860)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1084)
Application launched itself
- iexplore.exe (PID: 1084)
Creates files in the user directory
- iexplore.exe (PID: 3360)
- iexplore.exe (PID: 1084)
Reads internet explorer settings
- iexplore.exe (PID: 3360)
Reads Internet Cache Settings
- iexplore.exe (PID: 1084)
- iexplore.exe (PID: 3360)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1084)
Dropped object may contain Bitcoin addresses
- Stremio+4.4.106.exe (PID: 3860)
Reads the hosts file
- stremio.exe (PID: 2536)
Reads settings of System Certificates
- stremio.exe (PID: 2536)
- iexplore.exe (PID: 1084)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1084)
Changes settings of System certificates
- iexplore.exe (PID: 1084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1084 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://stremio.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1640 | C:\Windows\system32\WerFault.exe -u -p 2536 -s 2476 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\AppData\Local\Programs\LNV\Stremio-4\QtWebEngineProcess.exe" --type=renderer --disable-accelerated-video-decode --disable-gpu-memory-buffer-video-frames --disable-shared-workers --enable-threaded-compositing --no-sandbox --disable-webrtc-hw-encoding --primordial-pipe-token=E1D270038330D6FF65484649AB0DA1CC --lang=en-US --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553 --disable-gpu-compositing --service-request-channel-token=E1D270038330D6FF65484649AB0DA1CC --renderer-client-id=2 --mojo-platform-channel-handle=1580 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\LNV\Stremio-4\QtWebEngineProcess.exe | — | stremio.exe | |||||||||||
User: admin Company: The Qt Company Ltd. Integrity Level: MEDIUM Description: Qt Qtwebengineprocess Exit code: 0 Version: 5.9.9.0 Modules
| |||||||||||||||
| 2536 | "C:\Users\admin\AppData\Local\Programs\LNV\Stremio-4\stremio.exe" | C:\Users\admin\AppData\Local\Programs\LNV\Stremio-4\stremio.exe | Stremio+4.4.106.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3 Version: 4.4.106.0 Modules
| |||||||||||||||
| 3360 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1084 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
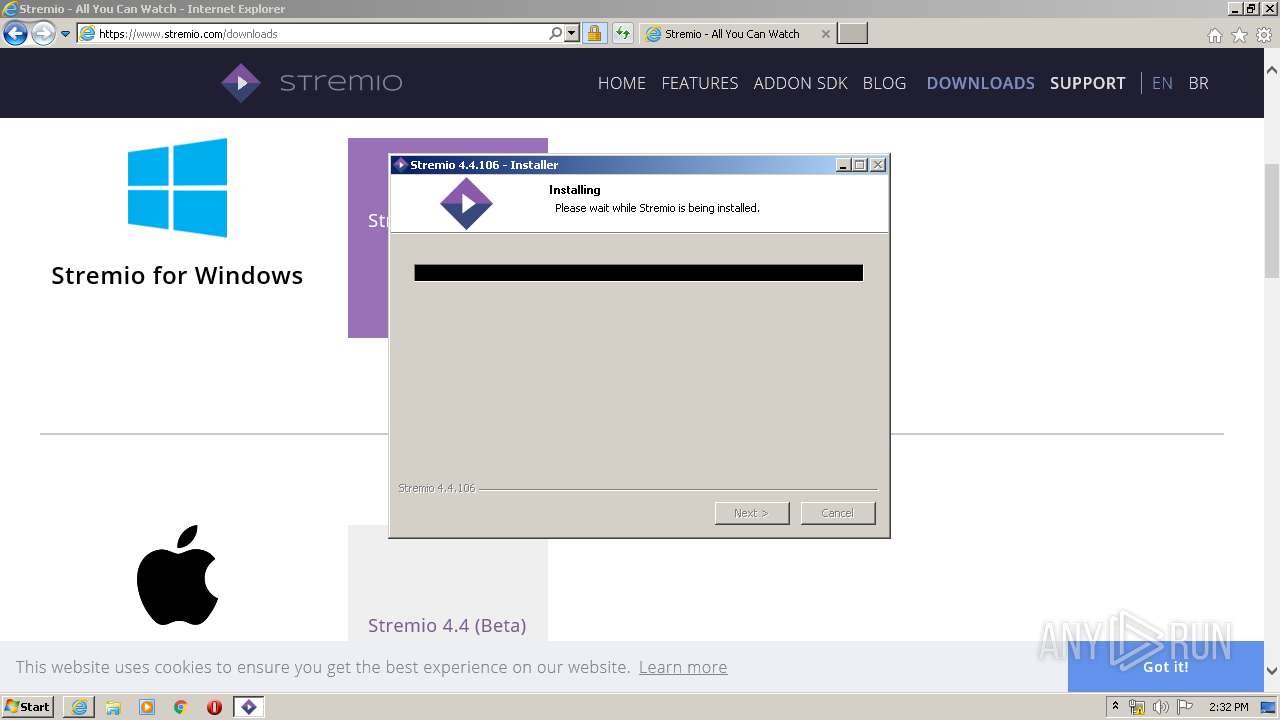
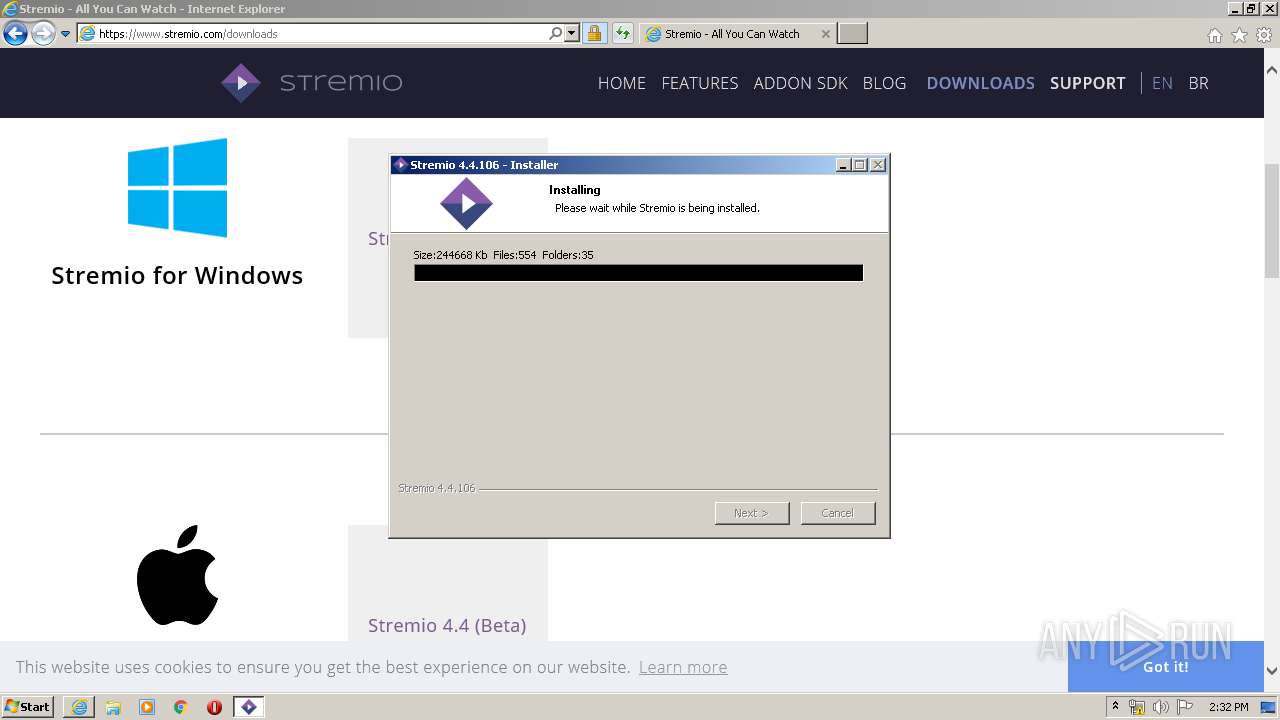
| 3860 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\Stremio+4.4.106.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\Stremio+4.4.106.exe | iexplore.exe | ||||||||||||
User: admin Company: Smart Code Ltd. Integrity Level: MEDIUM Description: Stremio 4.4.106 Installer Exit code: 0 Version: 4.4.106 Modules
| |||||||||||||||
Total events
6 905
Read events
1 659
Write events
3 523
Delete events
1 723
Modification events
| (PID) Process: | (1084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2787784310 | |||
| (PID) Process: | (1084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30805015 | |||
| (PID) Process: | (1084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
86
Suspicious files
484
Text files
509
Unknown types
59
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3360 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabEECD.tmp | — | |
MD5:— | SHA256:— | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarEECE.tmp | — | |
MD5:— | SHA256:— | |||
| 1084 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\64DCC9872C5635B1B7891B30665E0558_5552C20A2631357820903FD38A8C0F9F | binary | |
MD5:— | SHA256:— | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\stremio-txt-logo-small[1].png | image | |
MD5:— | SHA256:— | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\3PLWVN89.txt | text | |
MD5:— | SHA256:— | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\64DCC9872C5635B1B7891B30665E0558_5552C20A2631357820903FD38A8C0F9F | der | |
MD5:— | SHA256:— | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9EC3B71635F8BA3FC68DE181A104A0EF_F6C39EF89D8A3A72327D8412589658B2 | der | |
MD5:— | SHA256:— | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\icons[1].css | text | |
MD5:— | SHA256:— | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\main[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
67
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3360 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEENSAj%2F6qJAfE5%2Fj9OXBRE4%3D | US | der | 471 b | whitelisted |
3360 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | US | der | 312 b | whitelisted |
3360 | iexplore.exe | GET | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3360 | iexplore.exe | GET | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDy4NKedukSQwgAAAAAMgpY | US | der | 472 b | whitelisted |
3360 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTOpjOEf6LG1z52jqAxwDlTxoaOCgQUQAlhZ%2FC8g3FP3hIILG%2FU1Ct2PZYCEQCNmx6n%2FS%2FCc0UBRhCdwaxd | US | der | 279 b | whitelisted |
3360 | iexplore.exe | GET | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDtTANYN6TEwggAAAAAMgvv | US | der | 472 b | whitelisted |
3360 | iexplore.exe | GET | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3360 | iexplore.exe | GET | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQC71JgJax1YIwIAAAAAXGhg | US | der | 472 b | whitelisted |
3360 | iexplore.exe | GET | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDtTANYN6TEwggAAAAAMgvv | US | der | 472 b | whitelisted |
3360 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3360 | iexplore.exe | 104.16.136.12:443 | stremio.com | Cloudflare Inc | US | unknown |
1084 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3360 | iexplore.exe | 216.58.206.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3360 | iexplore.exe | 151.139.128.14:80 | ocsp.trust-provider.com | Highwinds Network Group, Inc. | US | suspicious |
3360 | iexplore.exe | 172.217.22.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3360 | iexplore.exe | 104.17.64.4:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
3360 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3360 | iexplore.exe | 172.217.23.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3360 | iexplore.exe | 172.217.16.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3360 | iexplore.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
stremio.com |
| whitelisted |
ocsp.trust-provider.com |
| whitelisted |
ocsp.comodoca4.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.stremio.com |
| unknown |
cdnjs.cloudflare.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
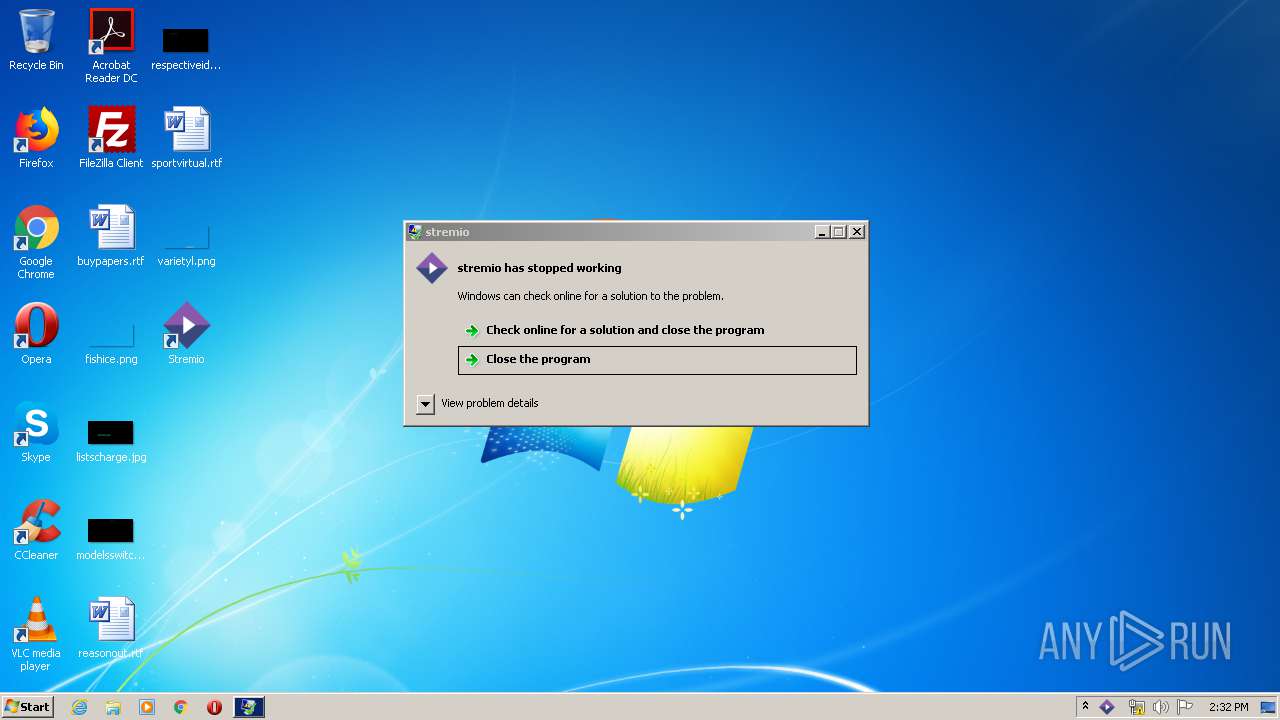
Threats
Process | Message |
|---|---|
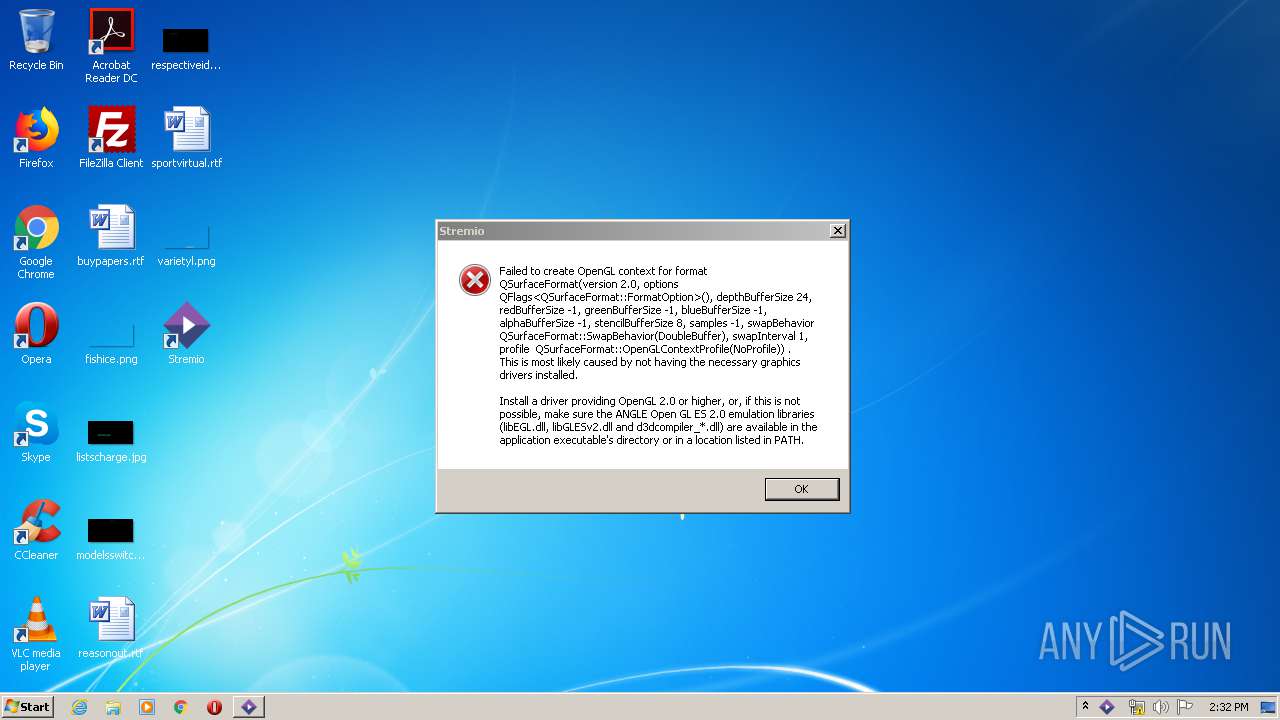
stremio.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
stremio.exe | QWindowsEGLStaticContext::create: Could not initialize EGL display: error 0x3001
|
stremio.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll isÐ |
stremio.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
stremio.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
stremio.exe | QWindowsEGLStaticContext::create: Could not initialize EGL display: error 0x3001
|
stremio.exe | ScreenSaver::retrieveState
|
stremio.exe | QWindowsEGLStaticContext::create: Could not initialize EGL display: error 0x3001
|
stremio.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
stremio.exe | WebEngineContext used before QtWebEngine::initialize() or OpenGL context creation failed.
|