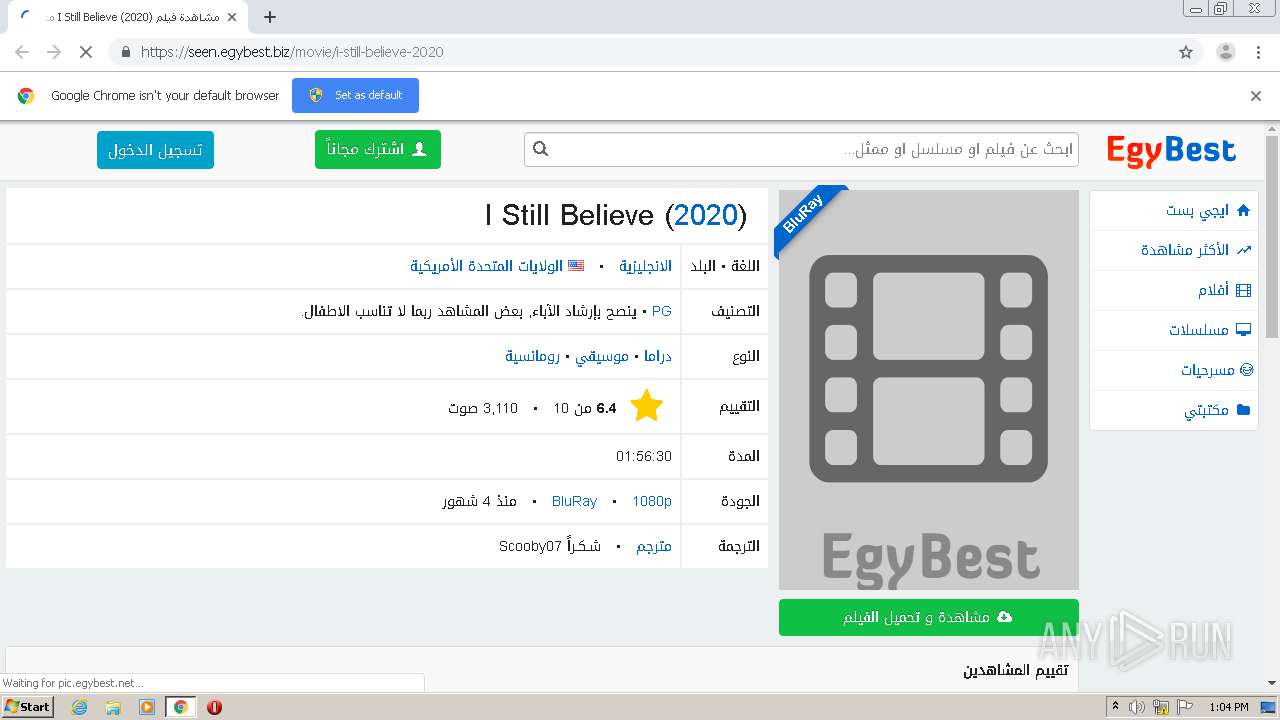
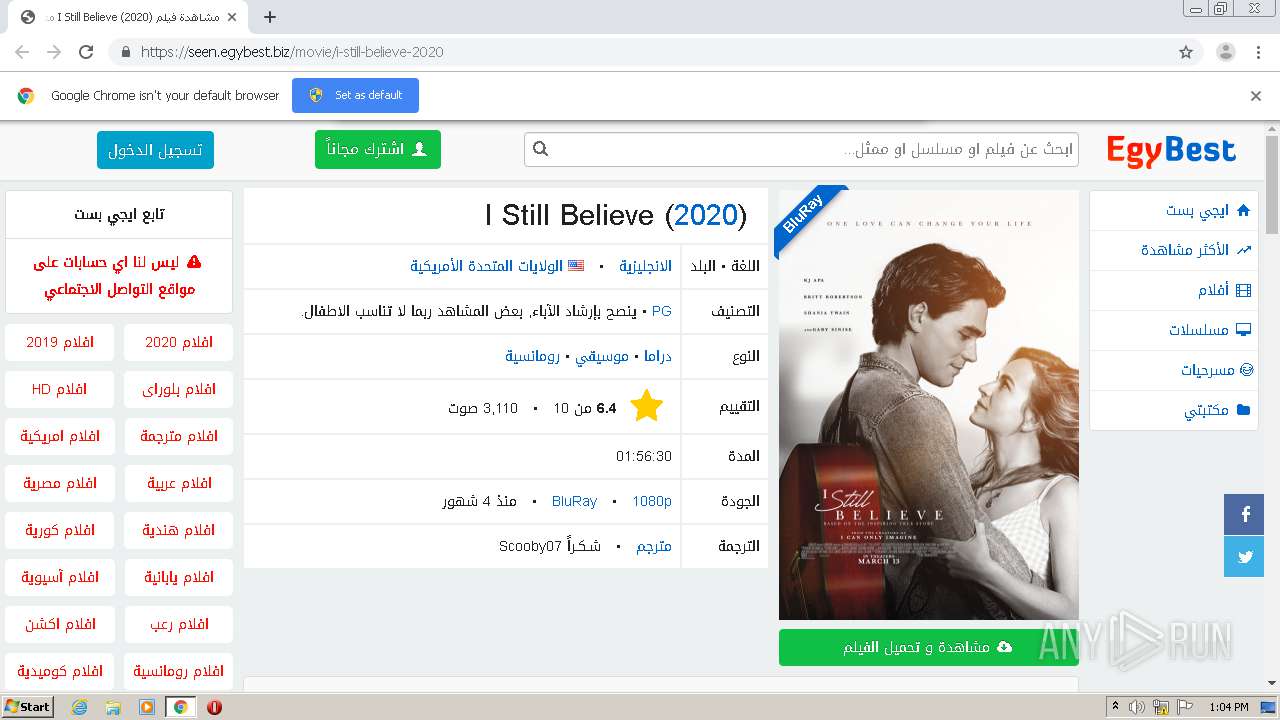
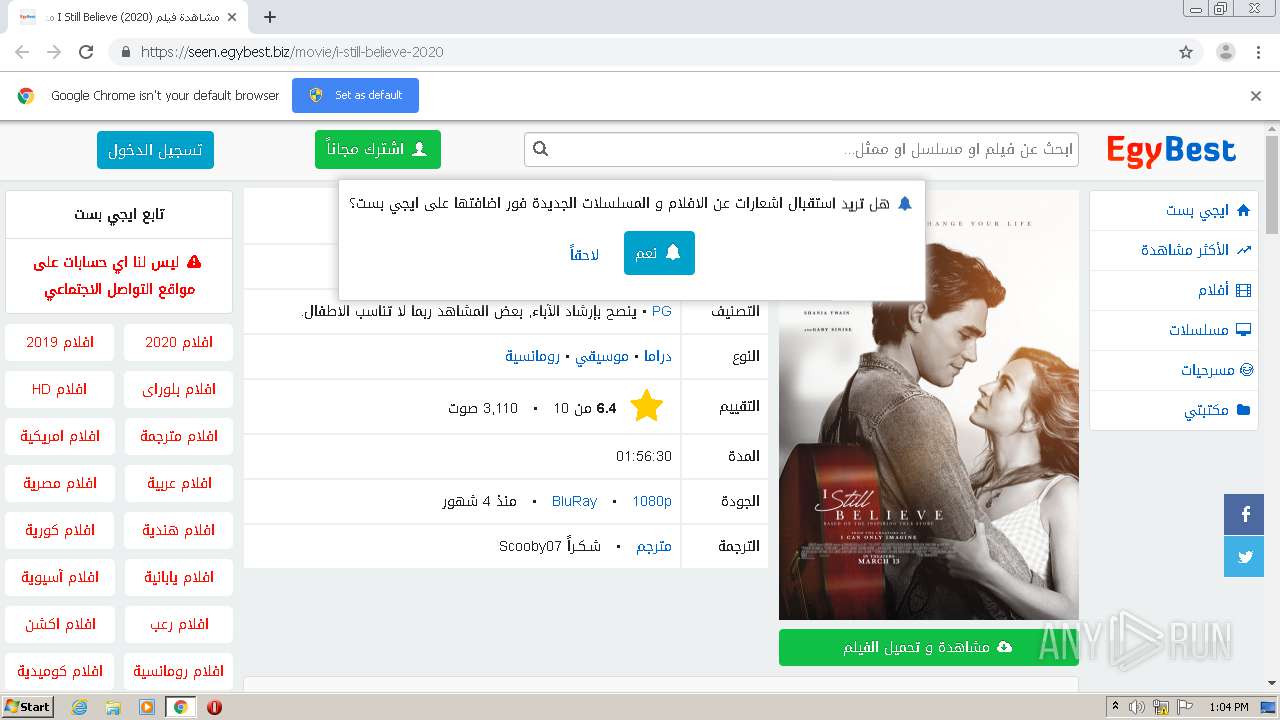
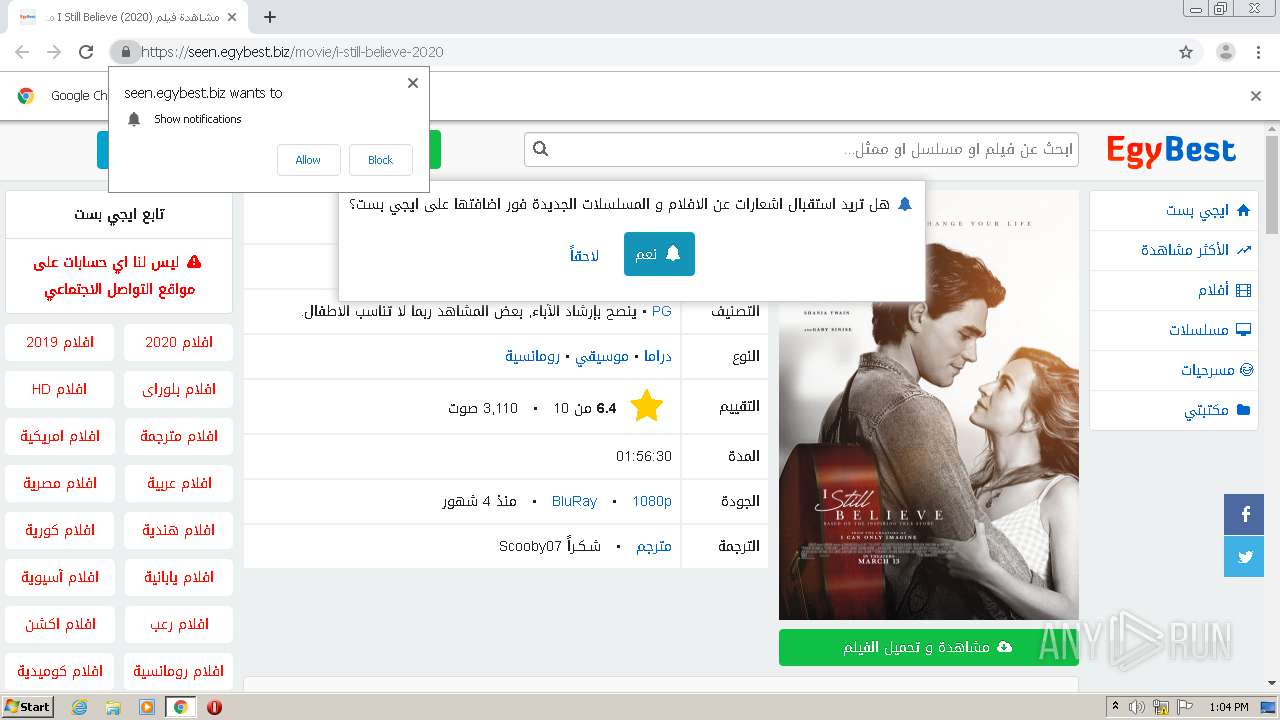
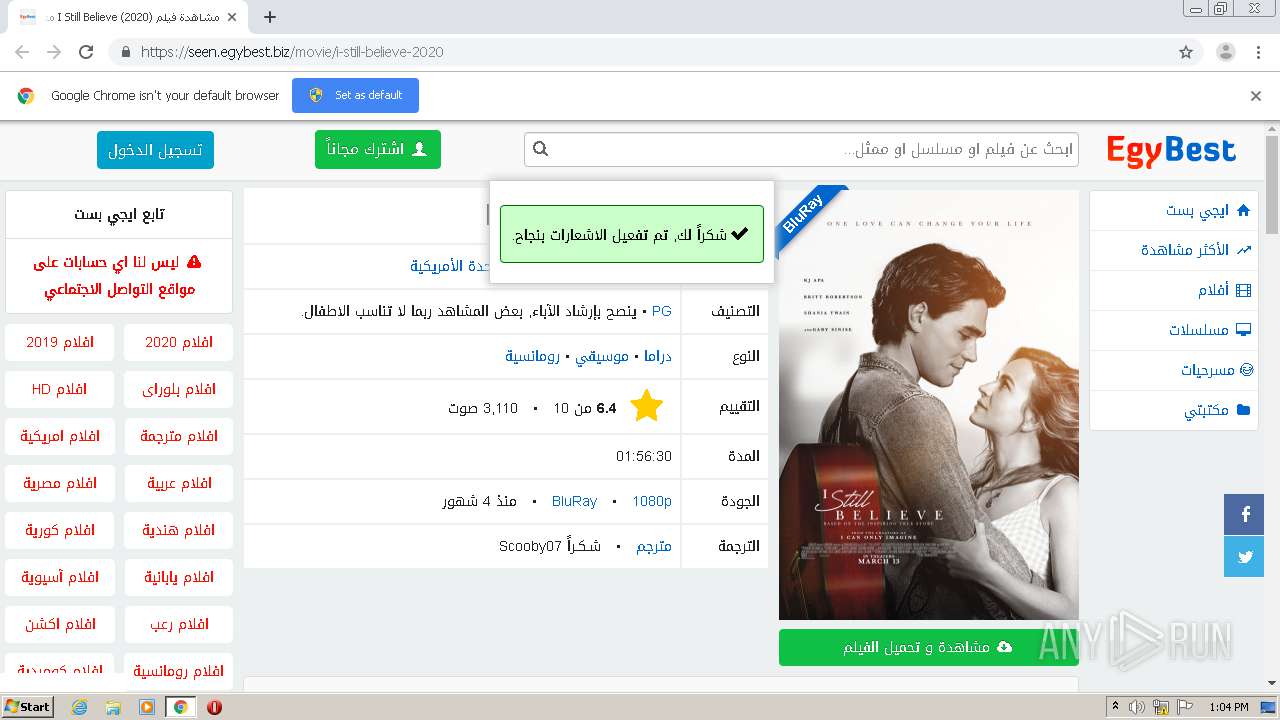
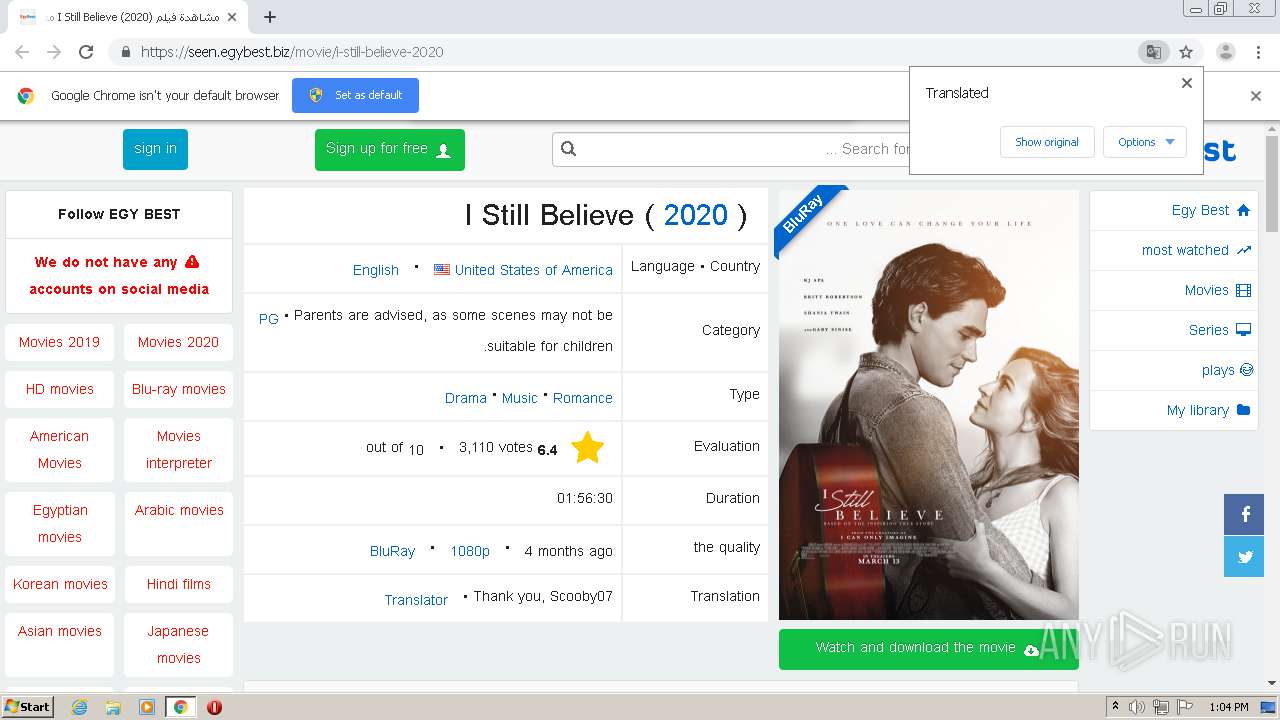
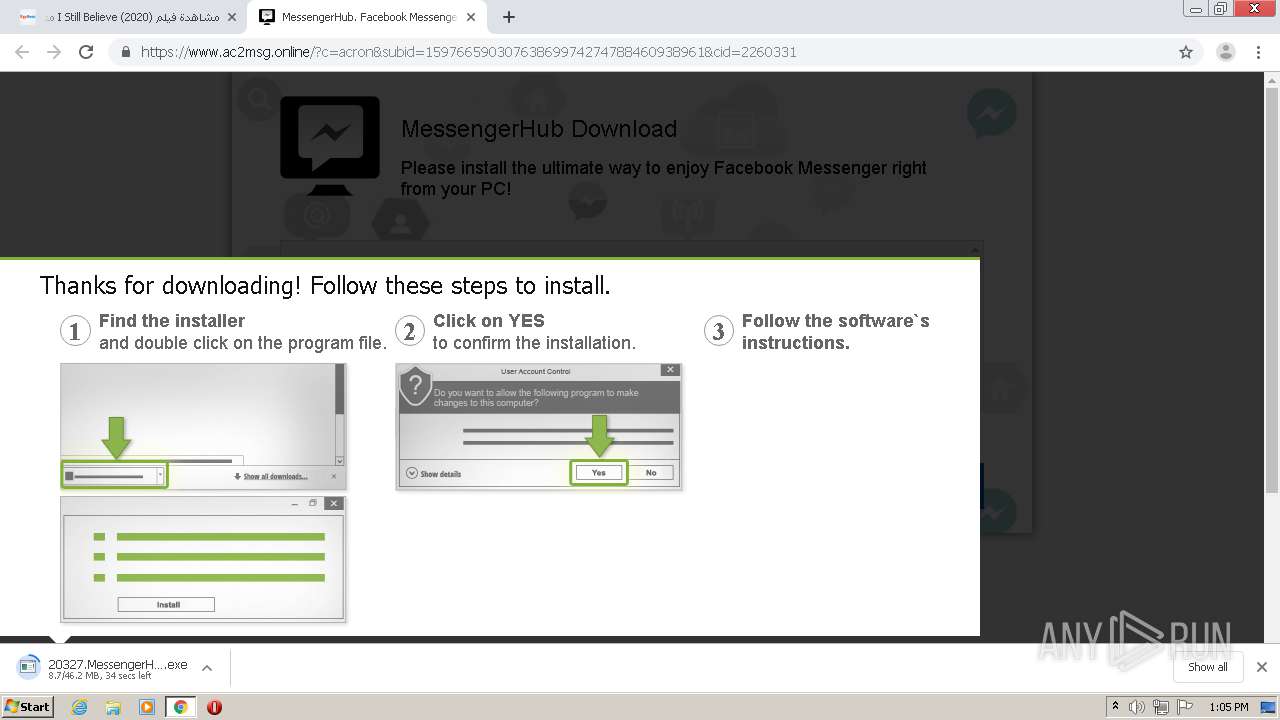
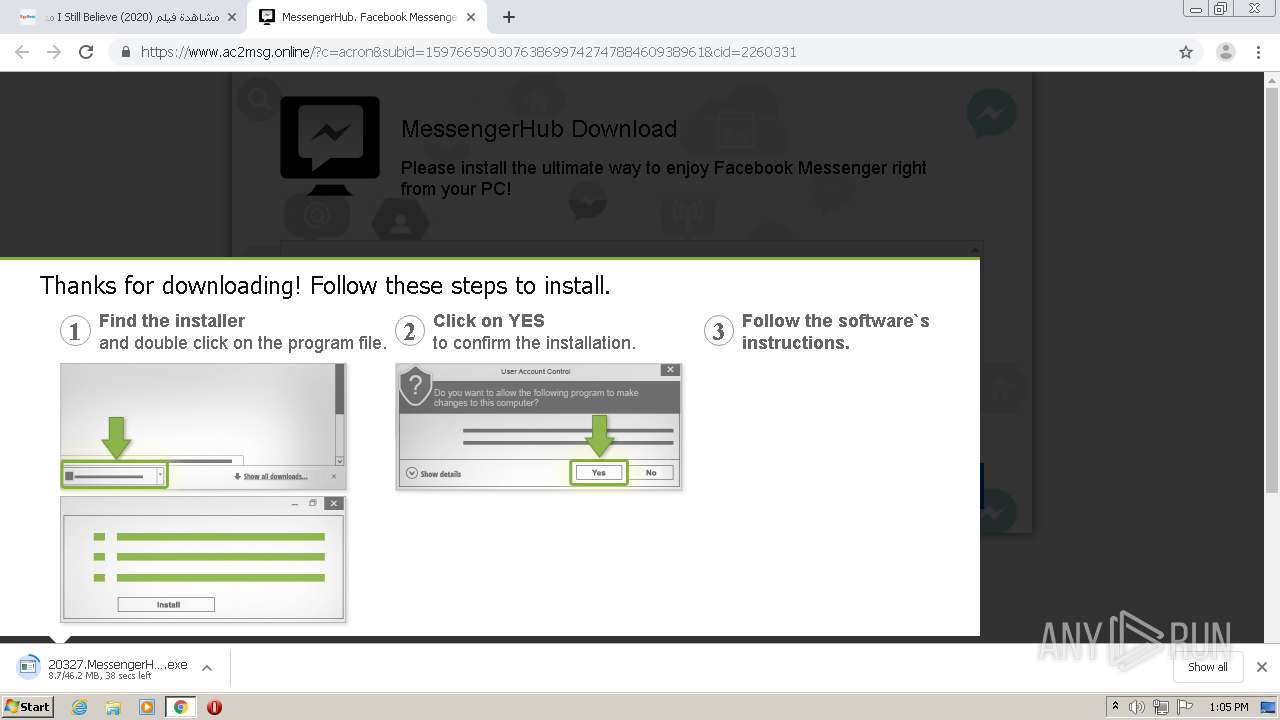
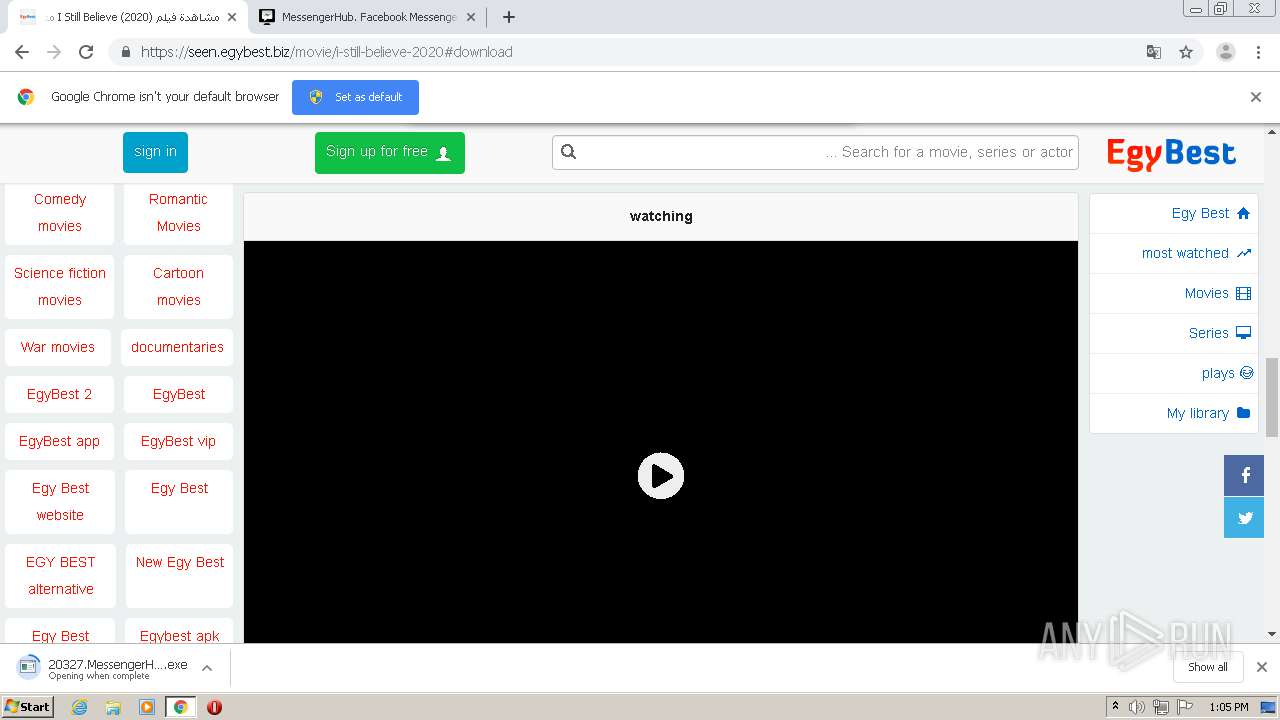
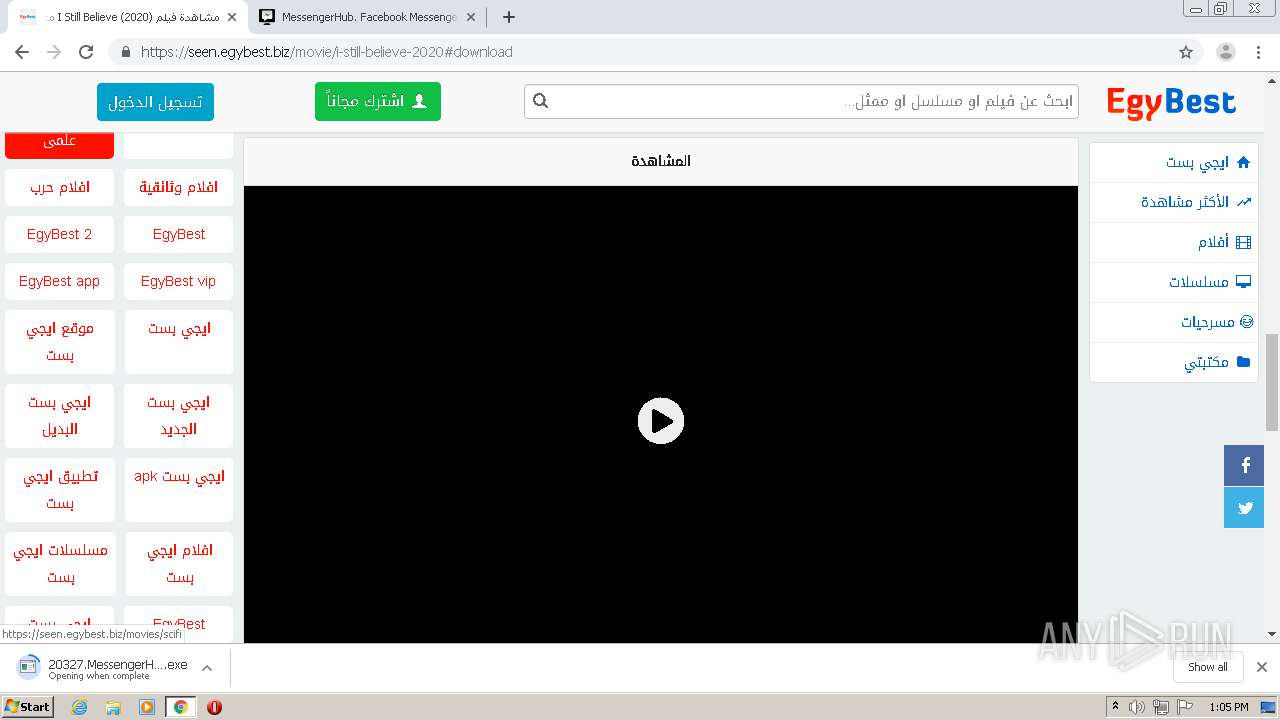
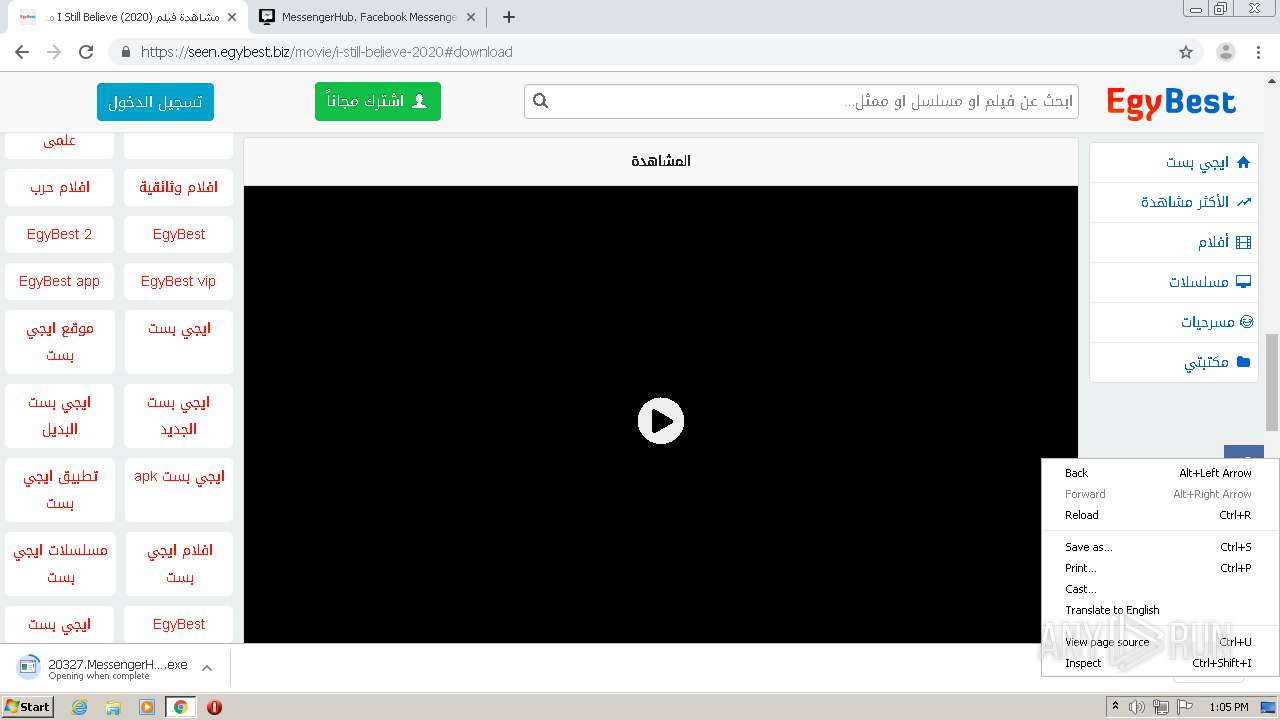
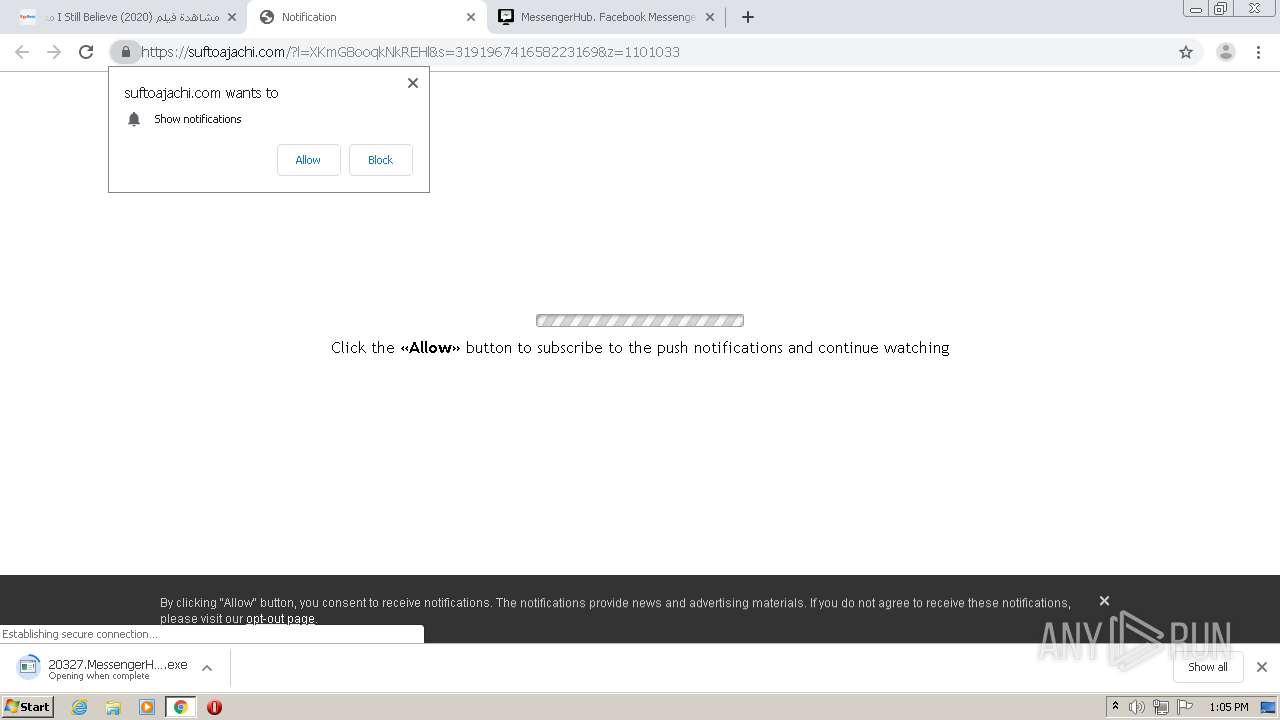
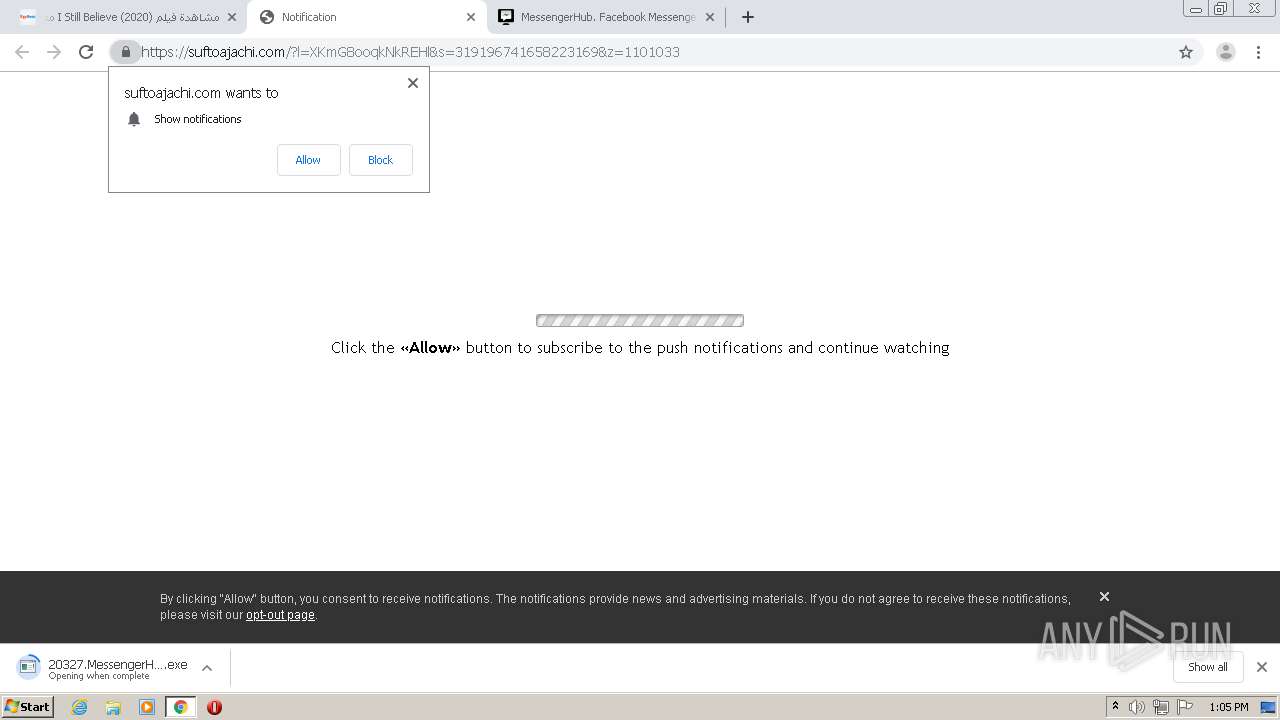
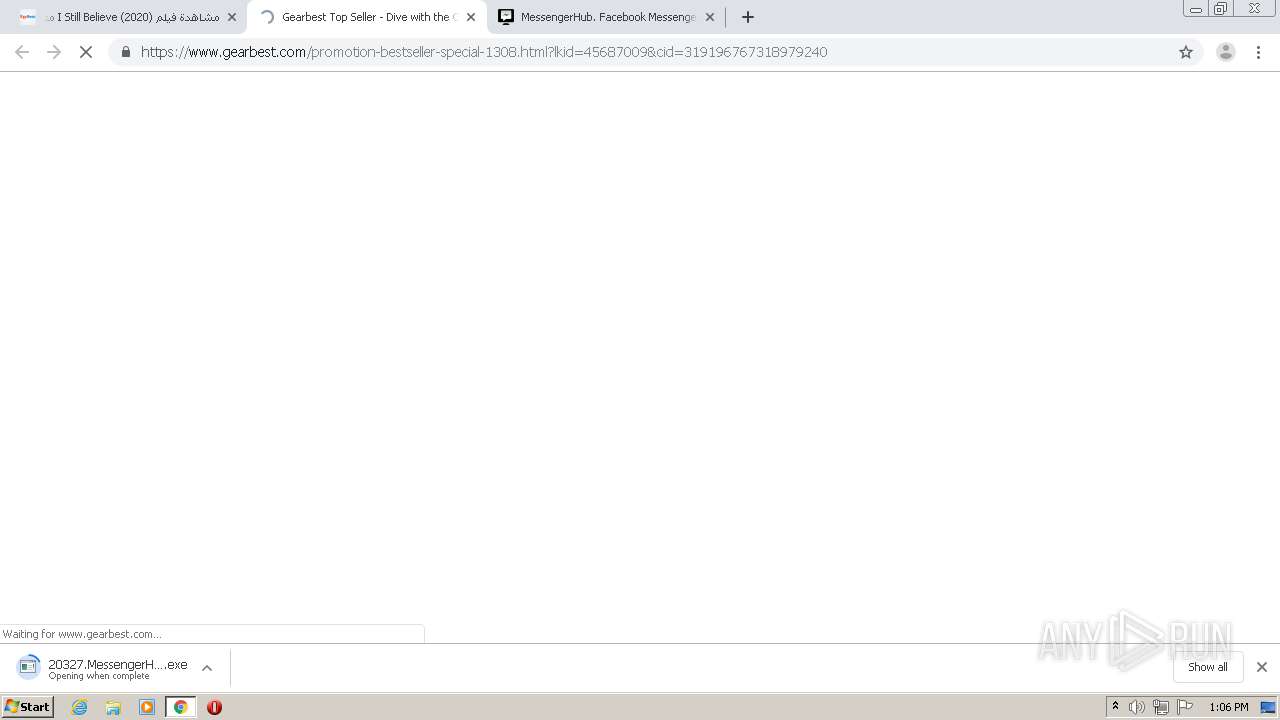
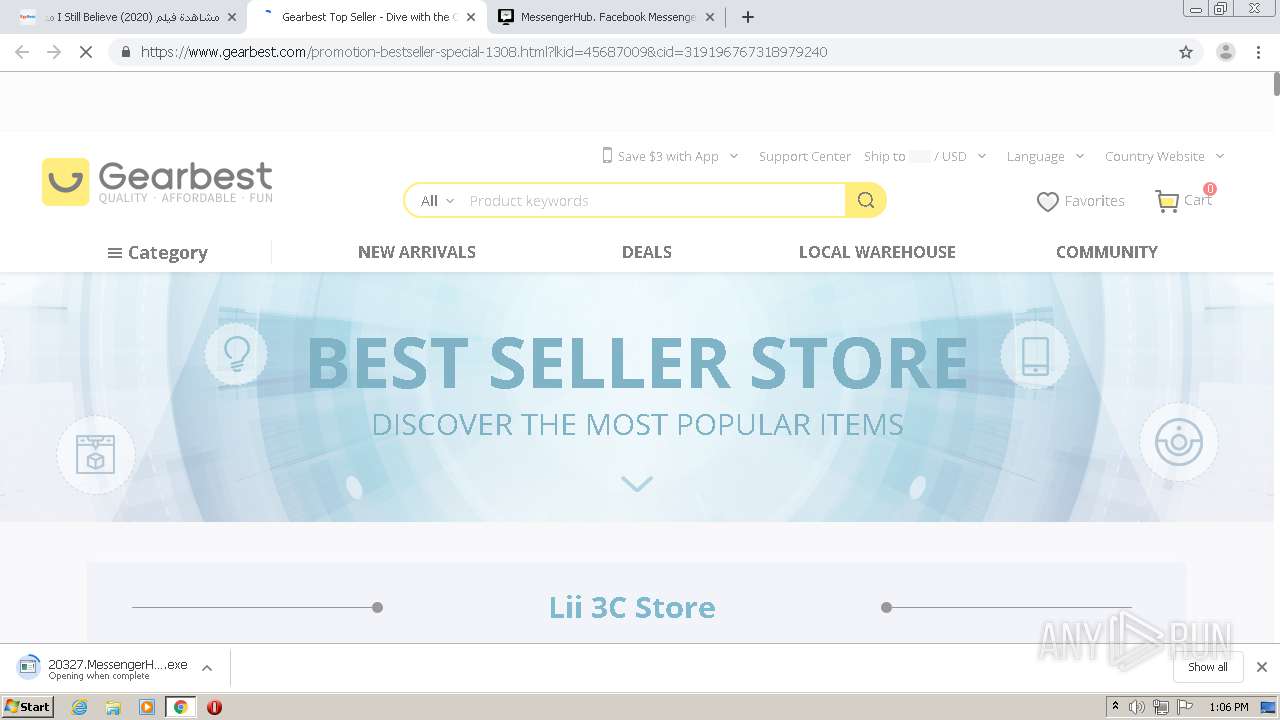
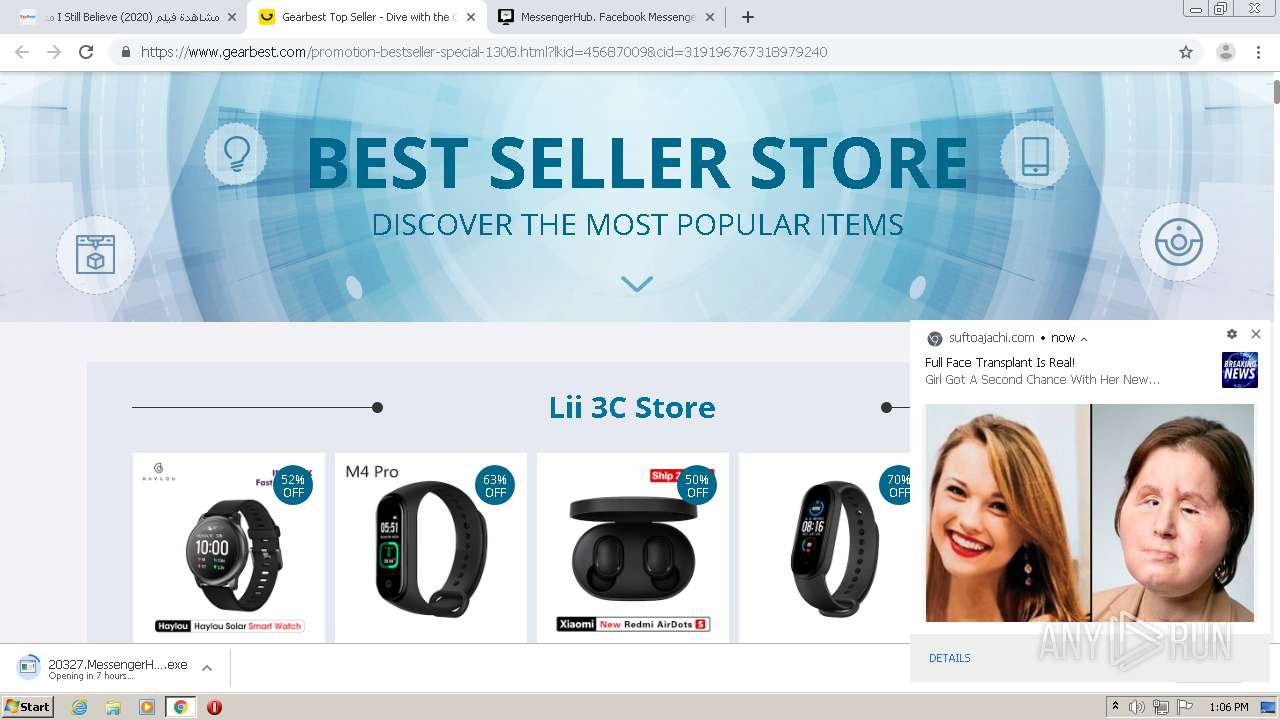
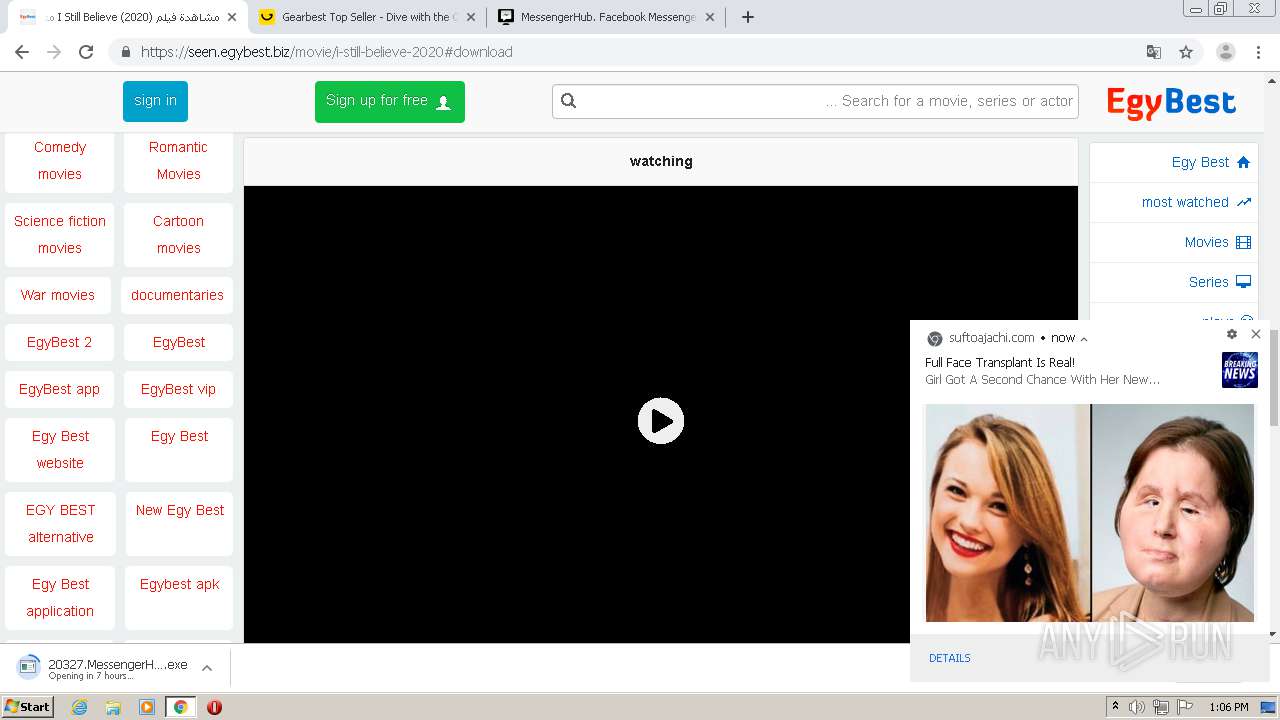
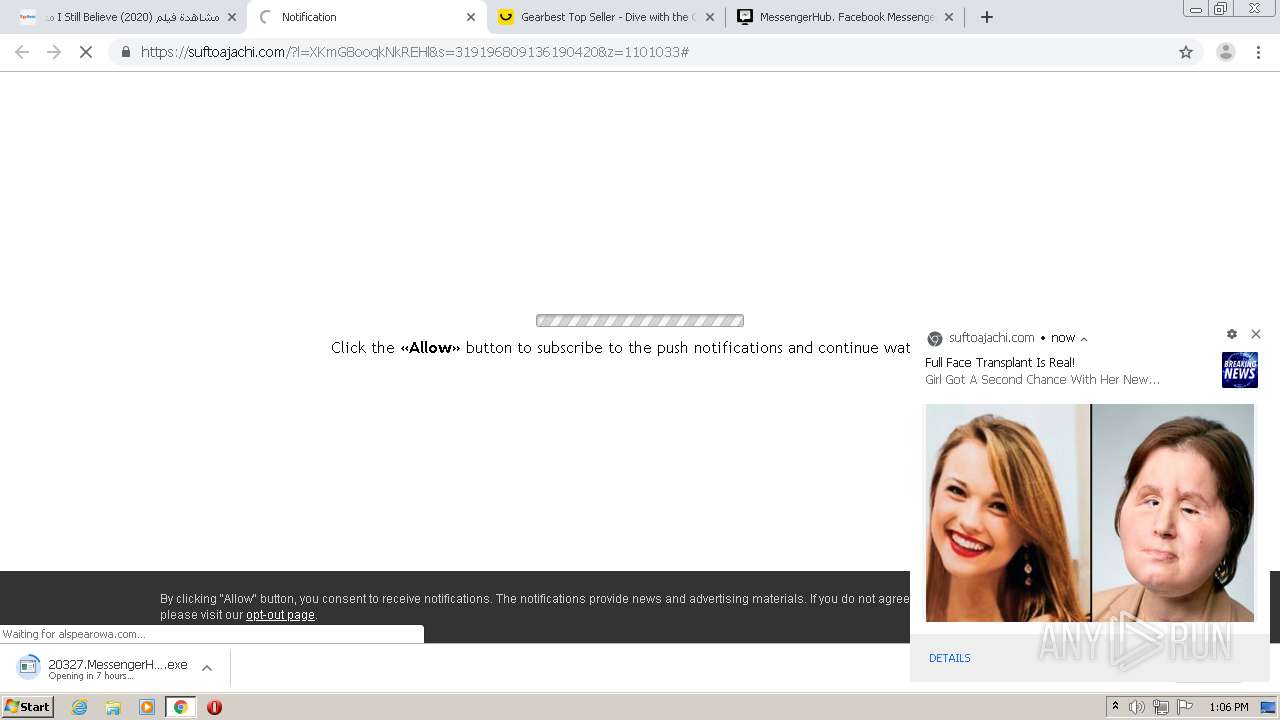
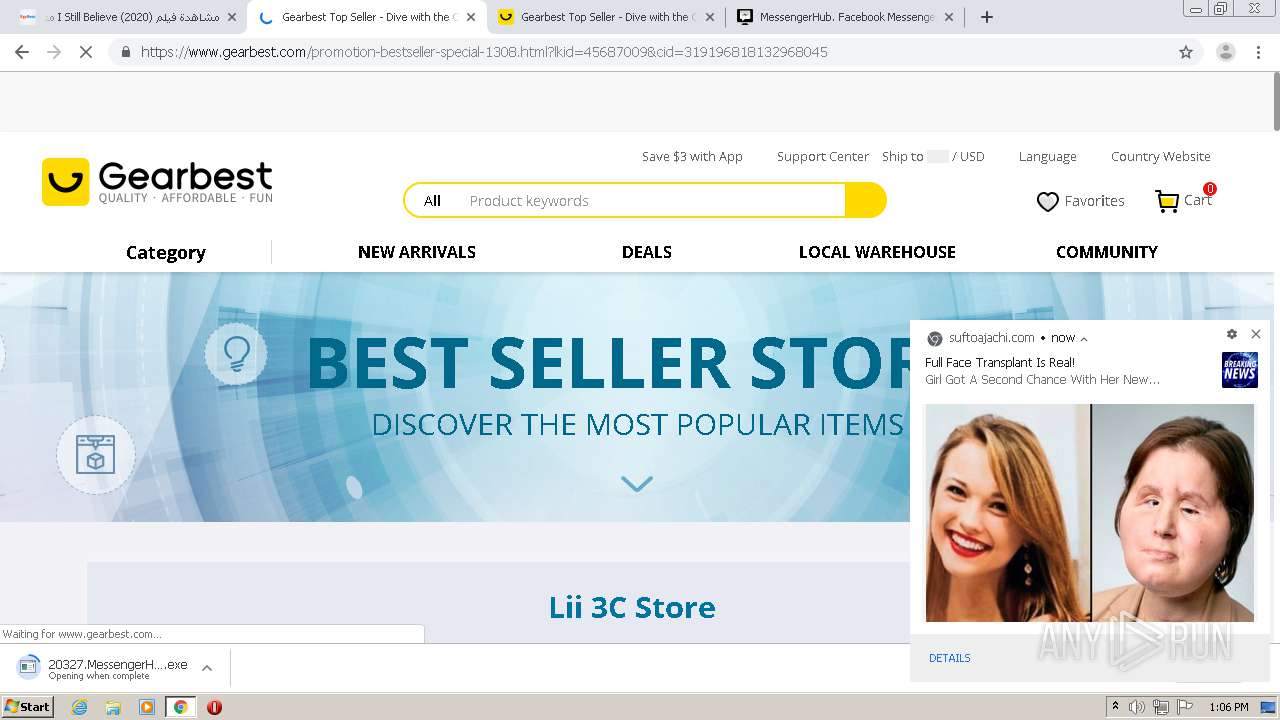
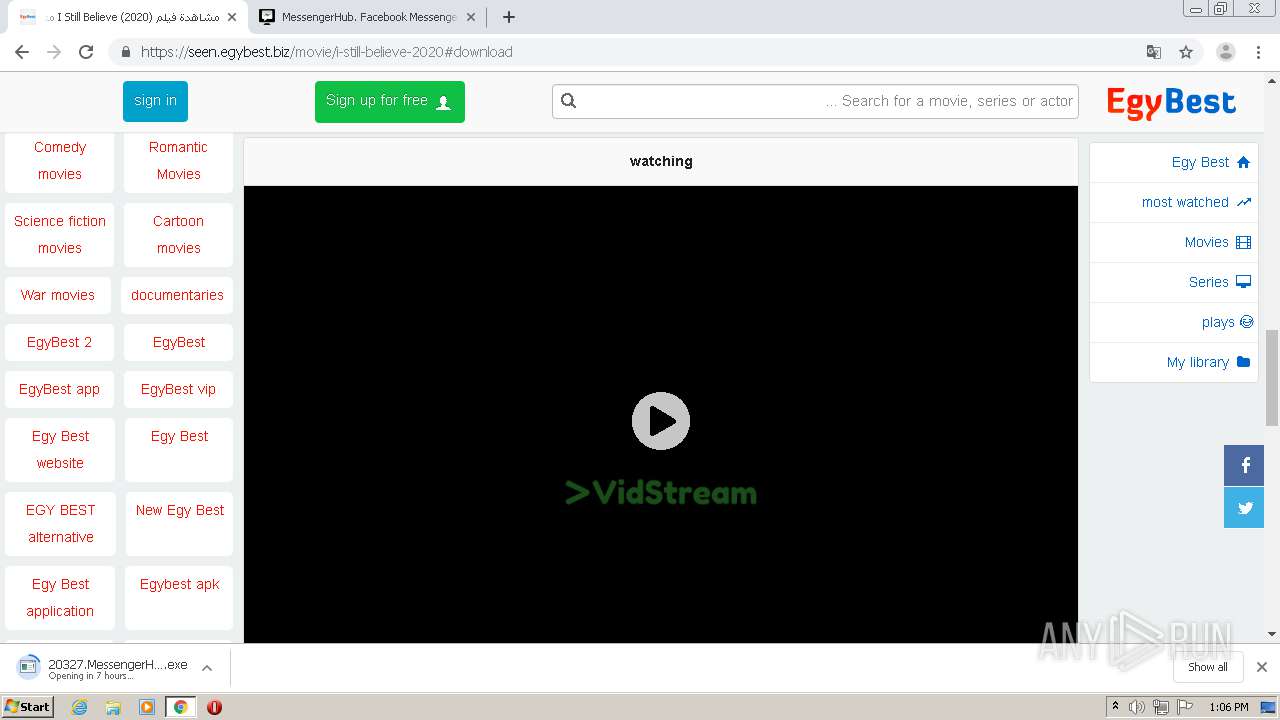
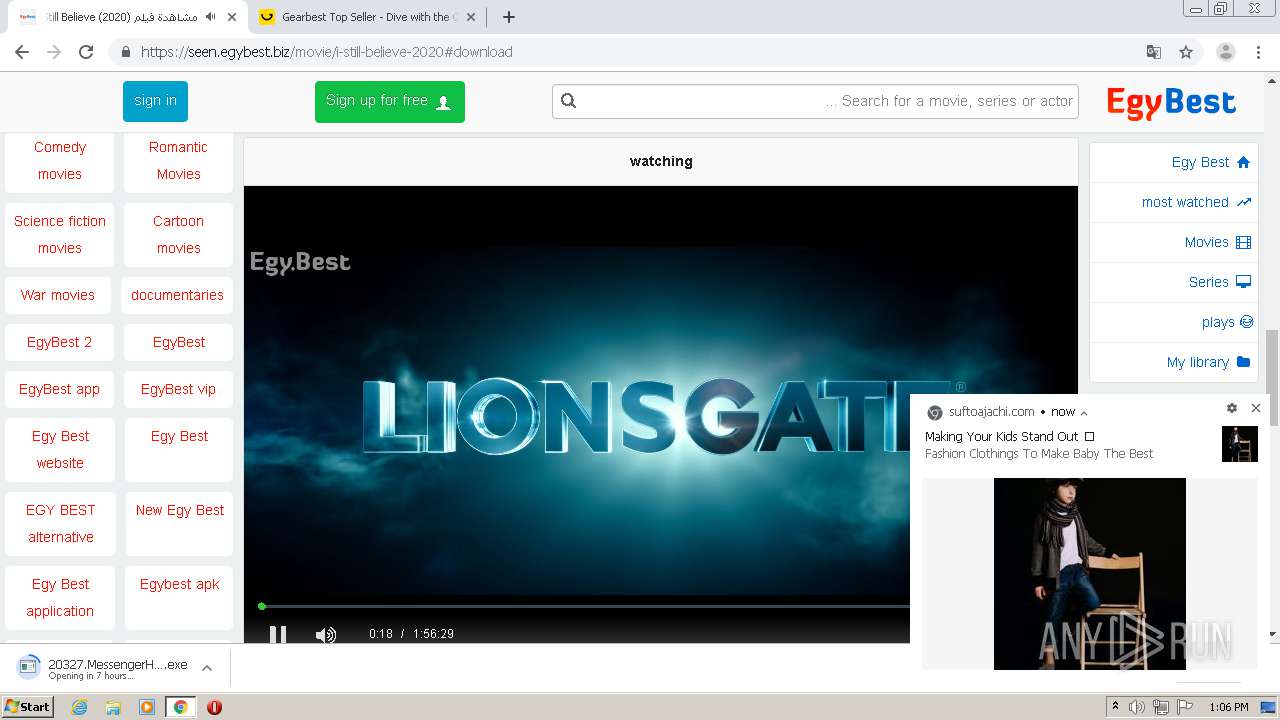
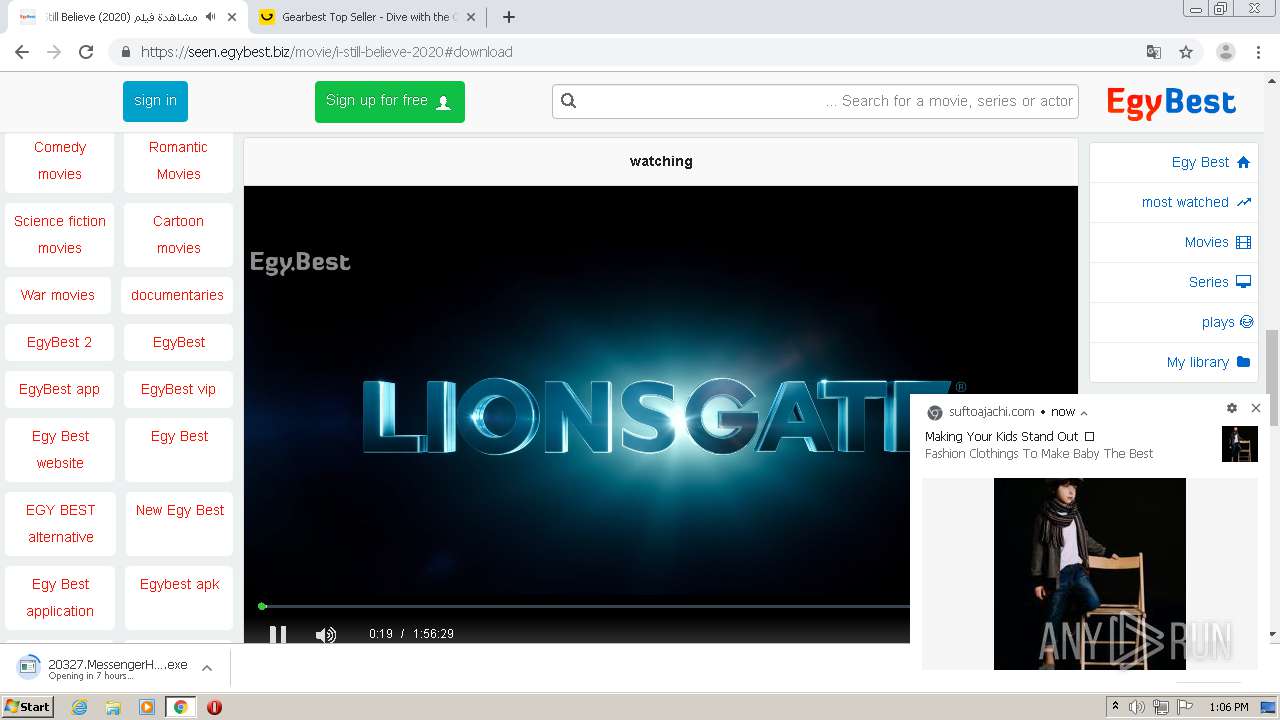
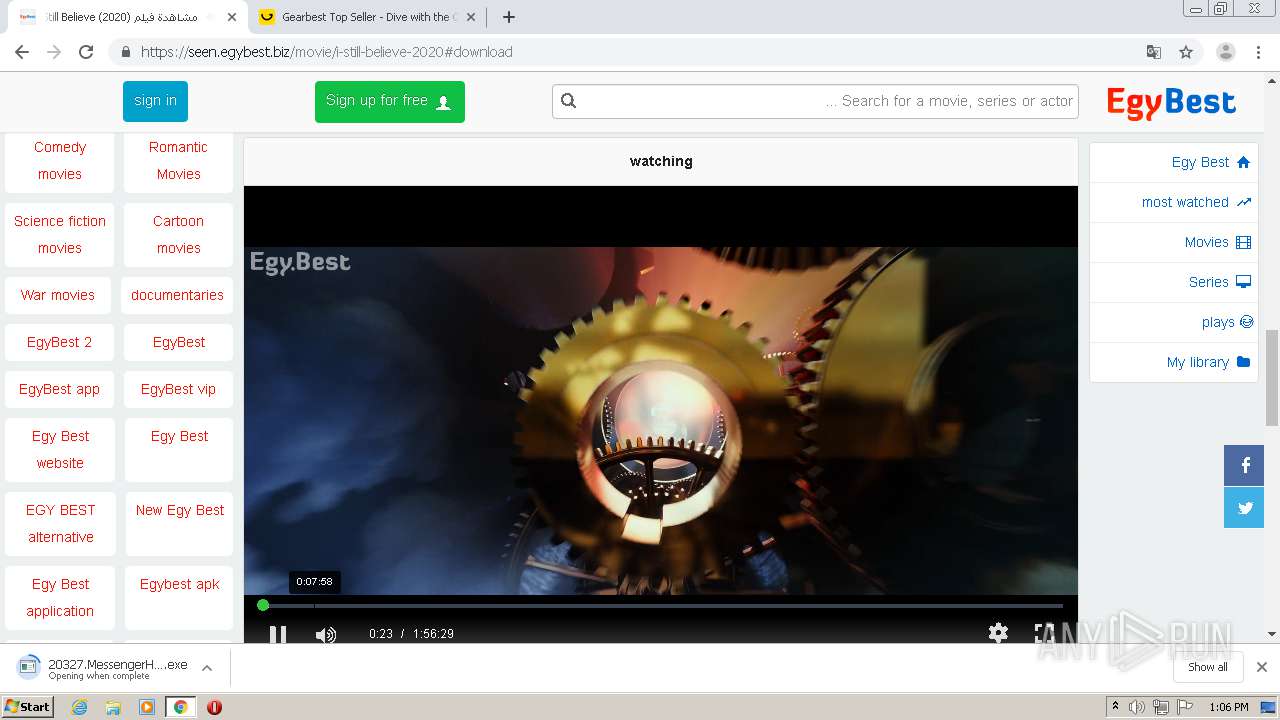
| URL: | https://seen.egybest.biz/movie/i-still-believe-2020 |
| Full analysis: | https://app.any.run/tasks/853550f7-c96b-4ac5-b97c-f1c3ec98ad3b |
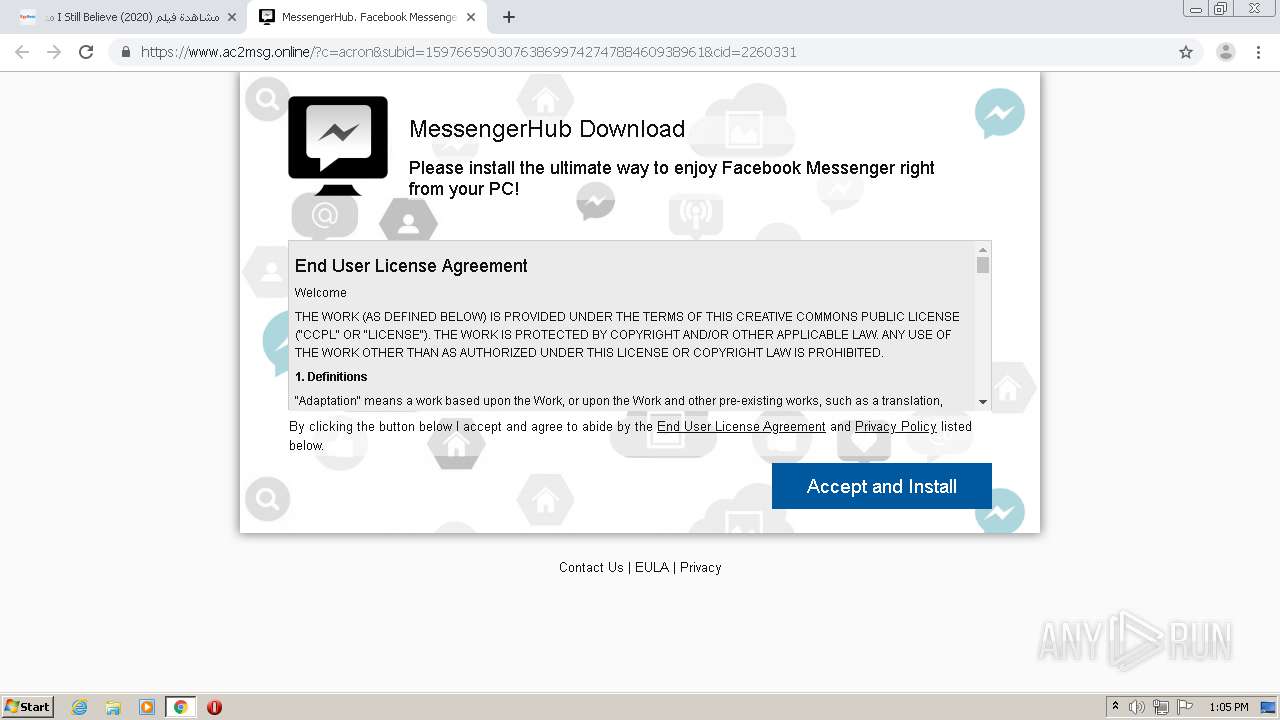
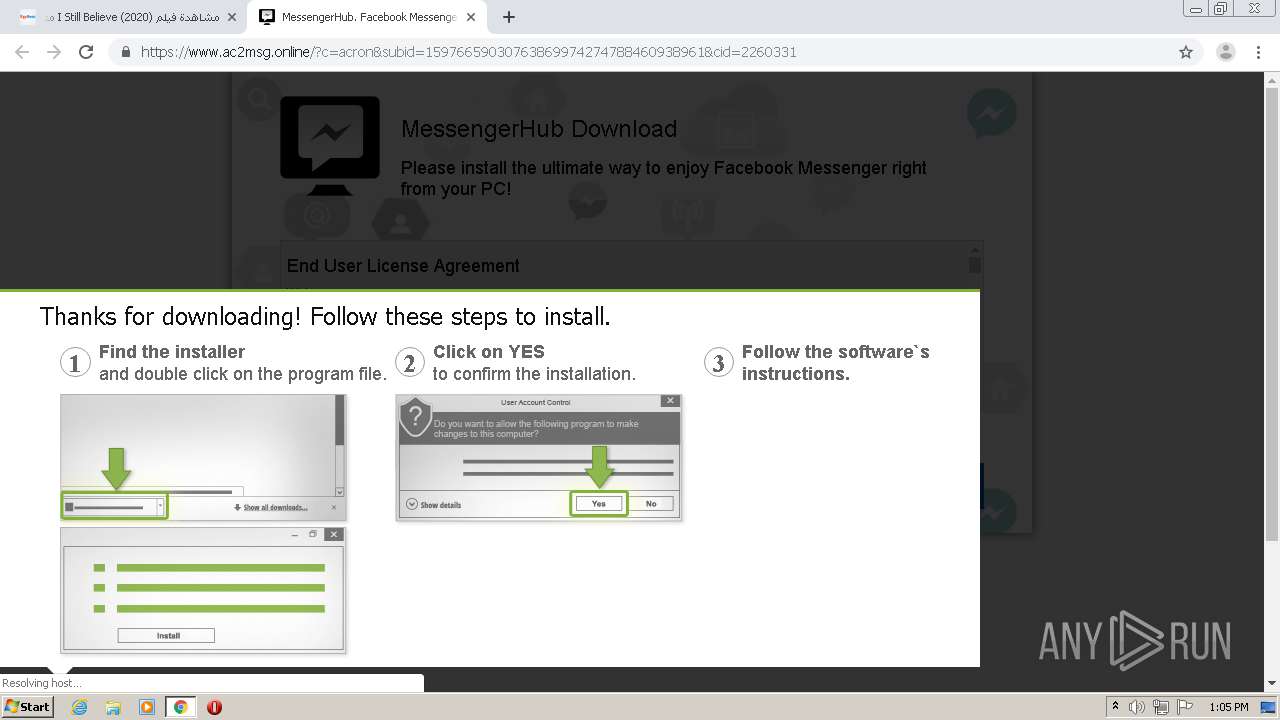
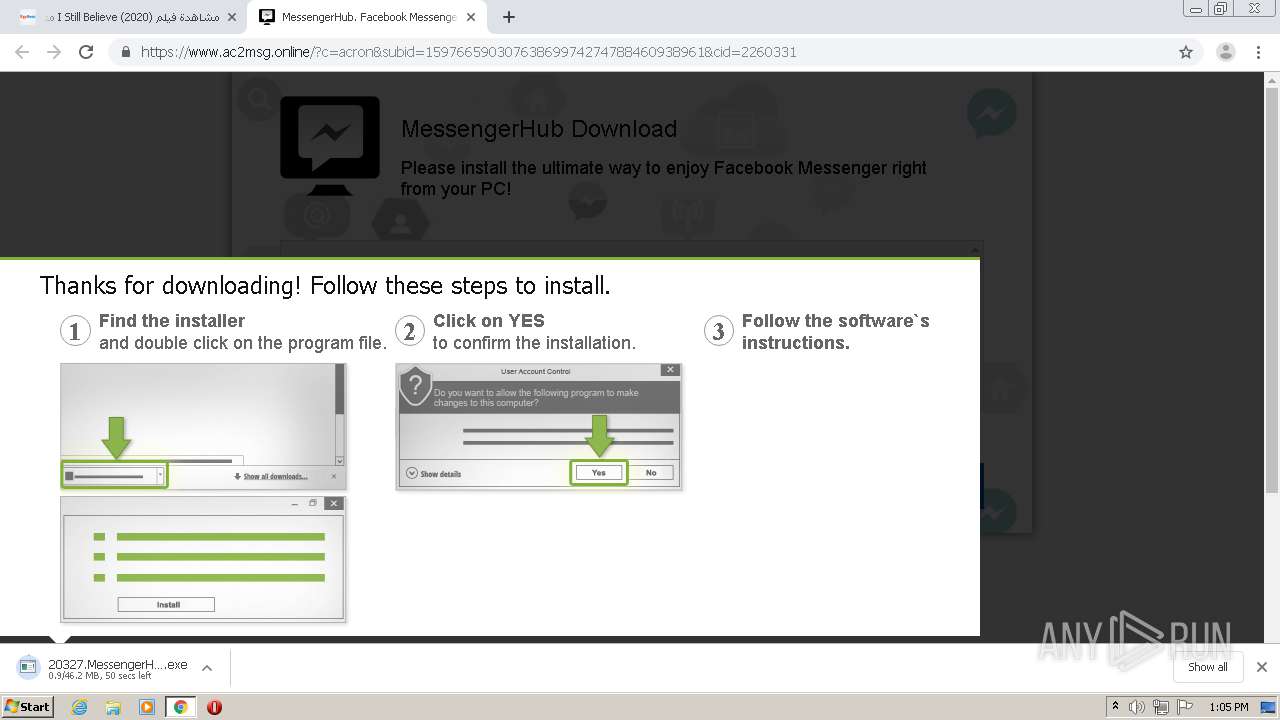
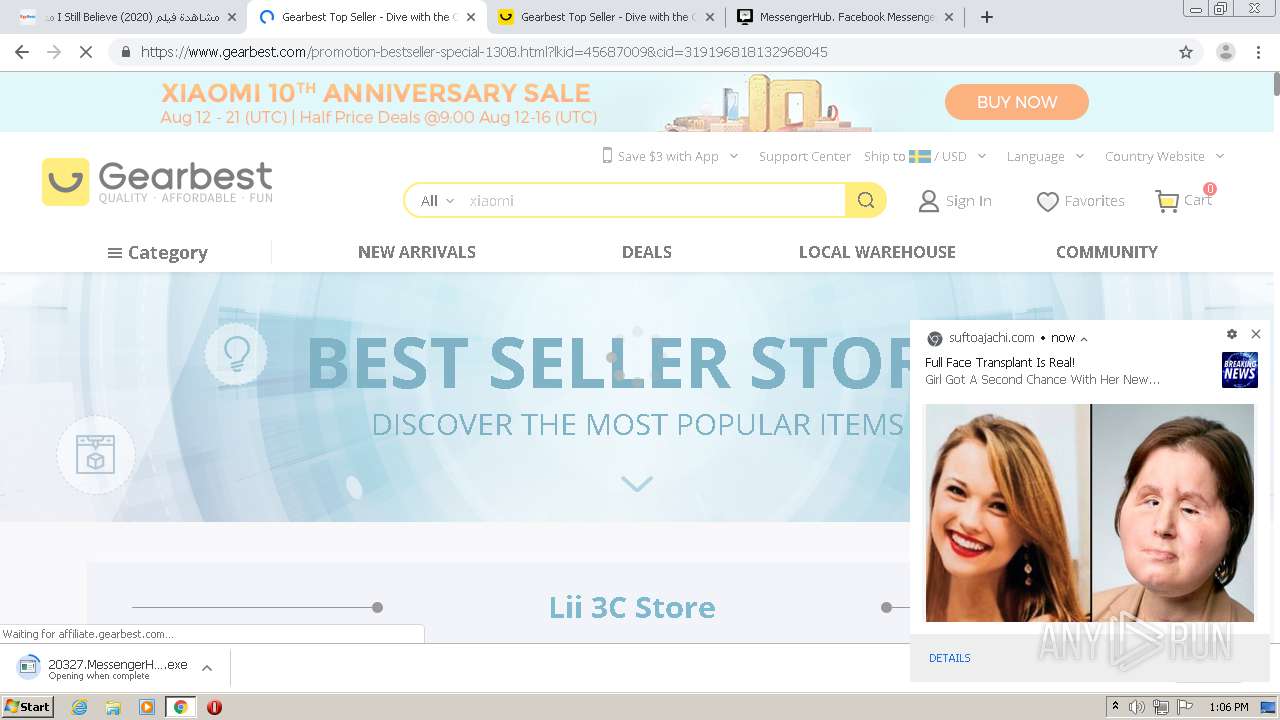
| Verdict: | Malicious activity |
| Analysis date: | August 17, 2020, 12:03:59 |
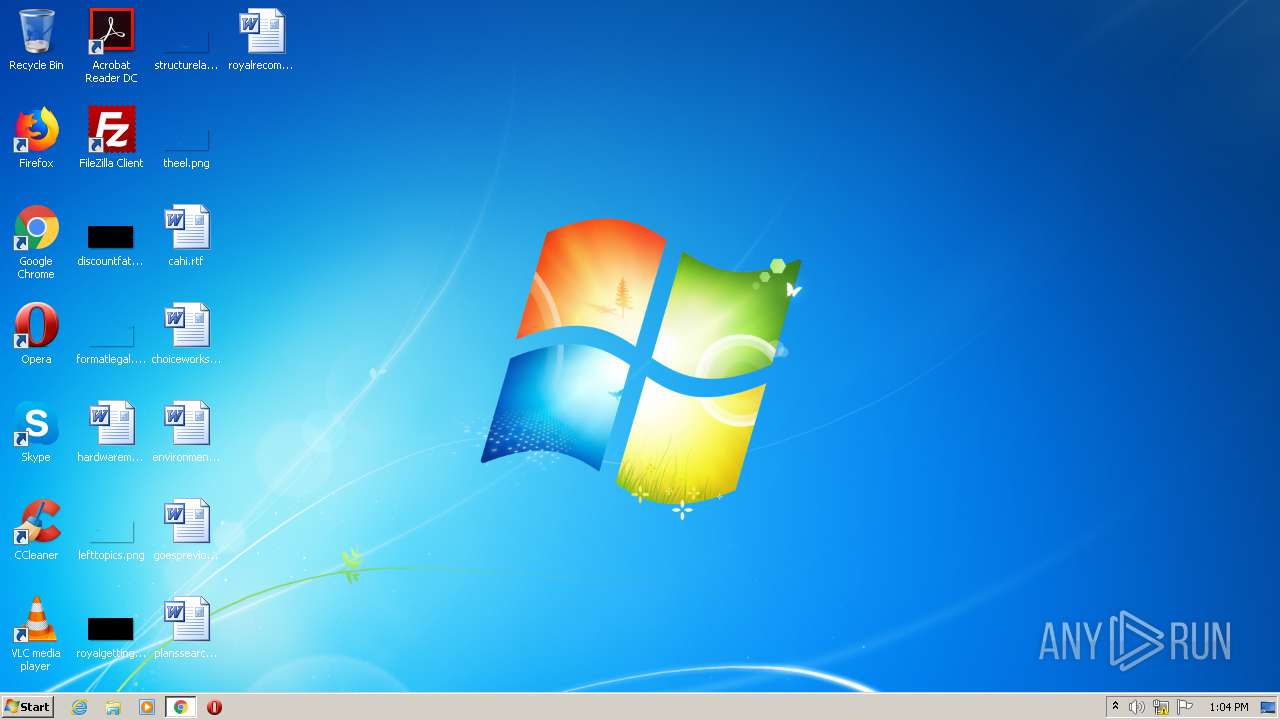
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 79AB333ED3778F90EDD90E6113ABBCE1 |
| SHA1: | 93841192304CC56C5563DAD0BC7401971A083FD8 |
| SHA256: | E0B7C4C7C01F671F2FE26AC6D05696B0AF102E380946AE28479522FB0ADD3454 |
| SSDEEP: | 3:N8Nu7WRL+KIxFLDMqVF:247OILU4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
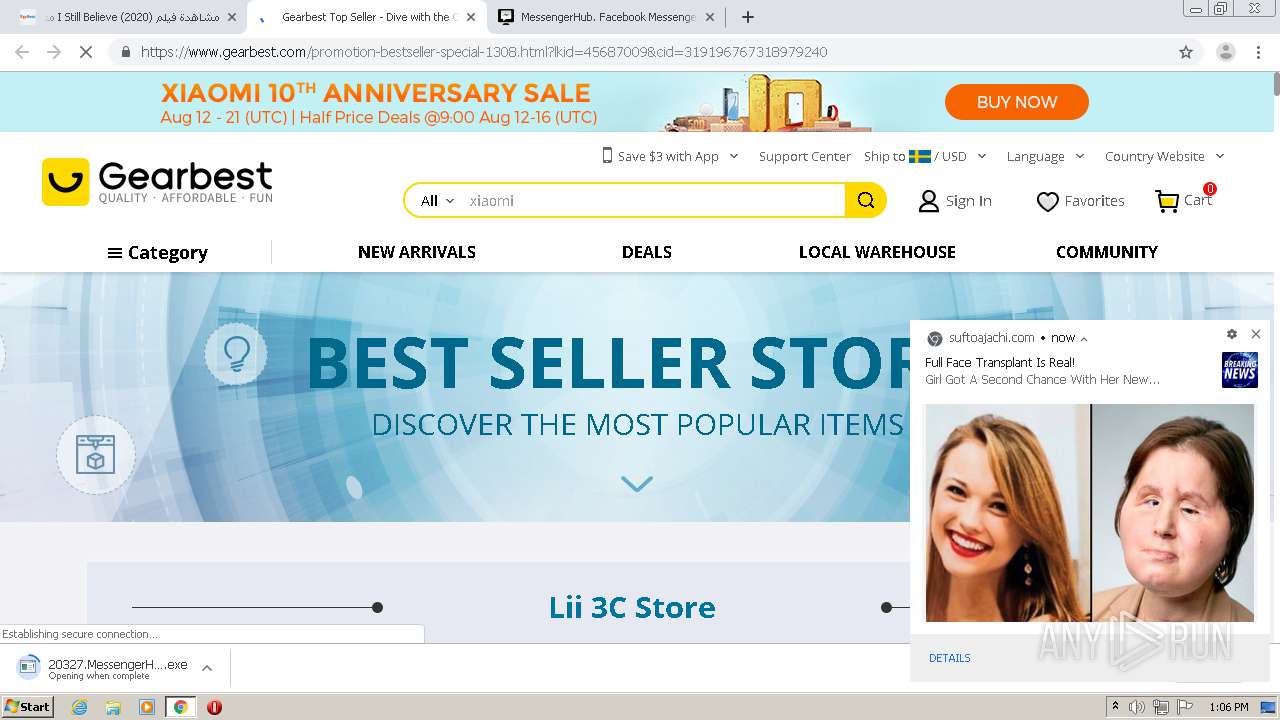
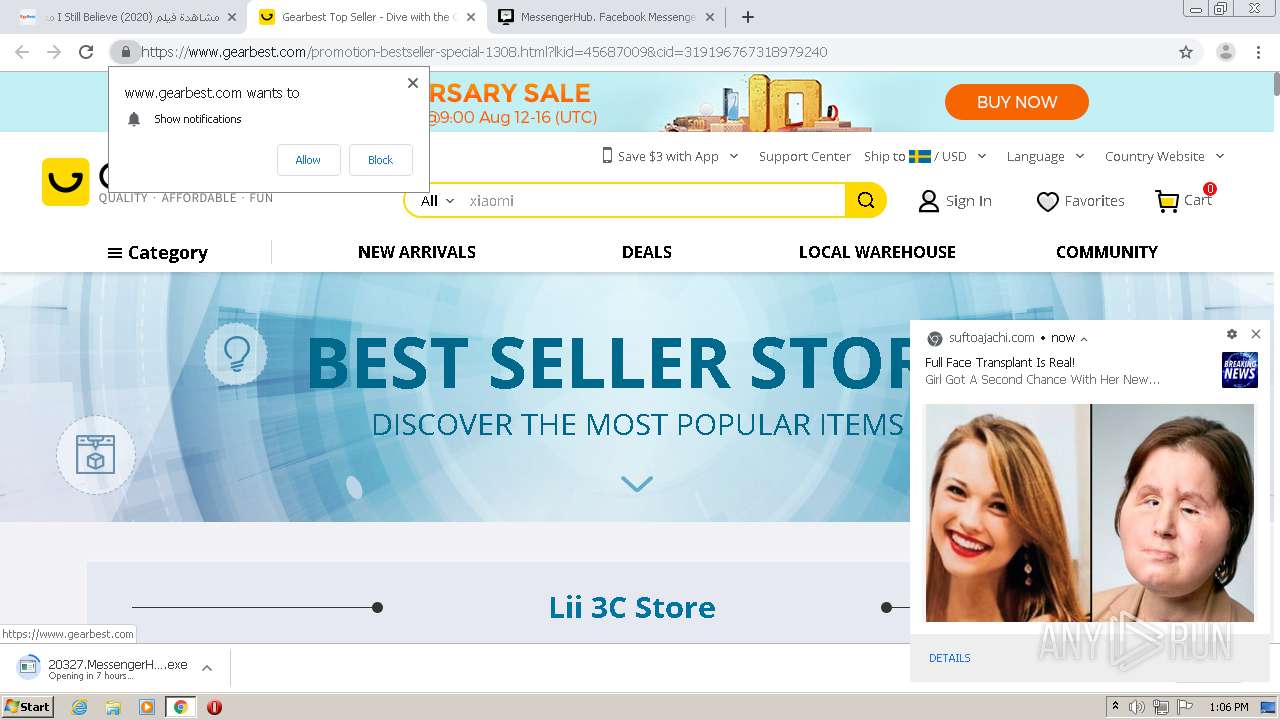
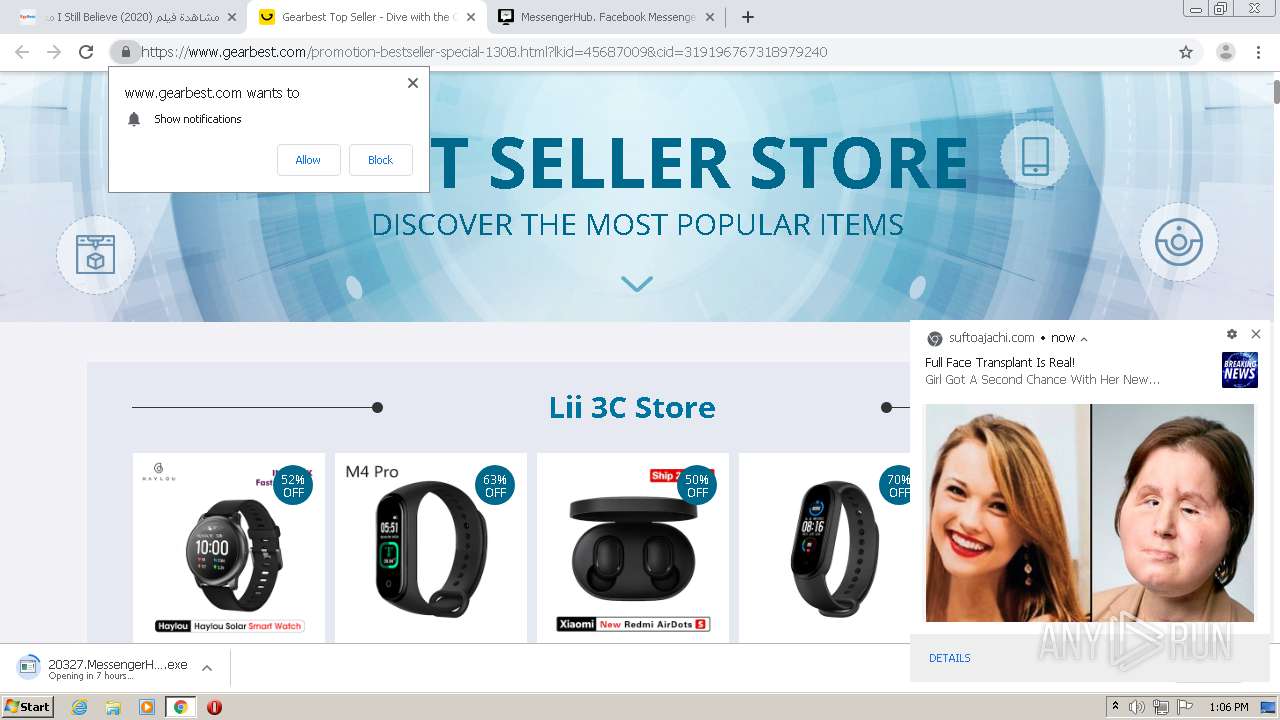
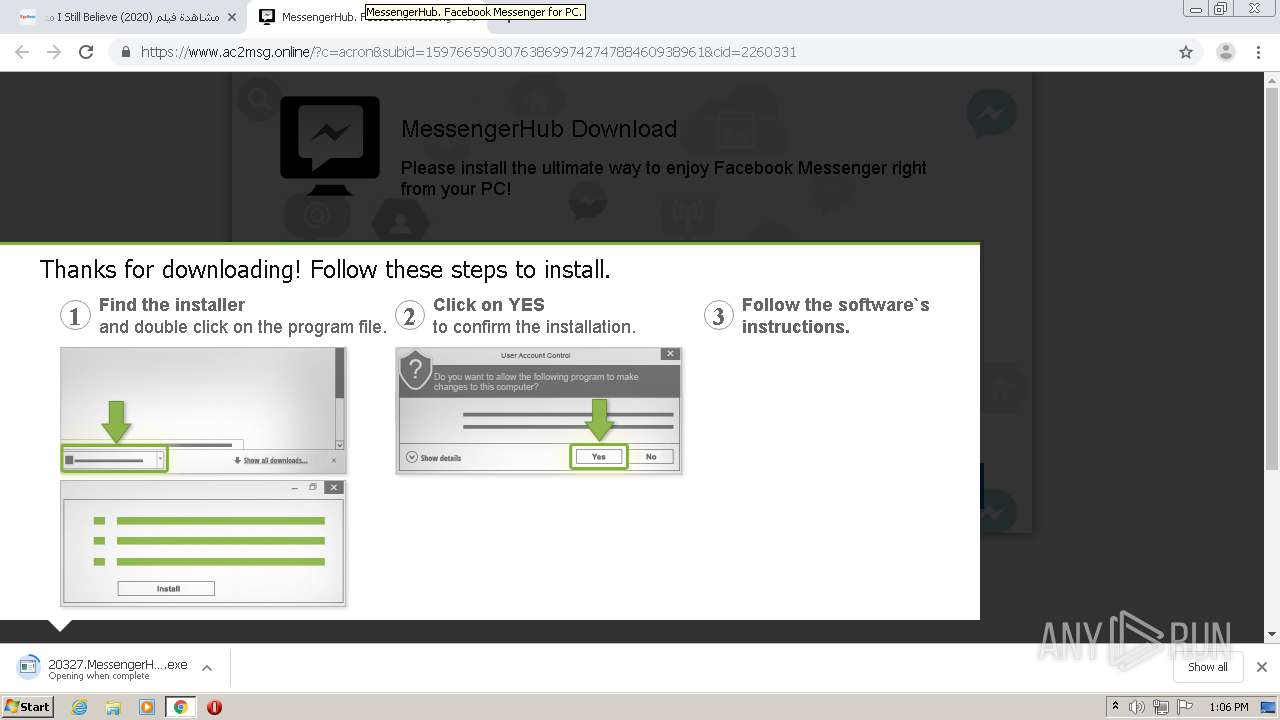
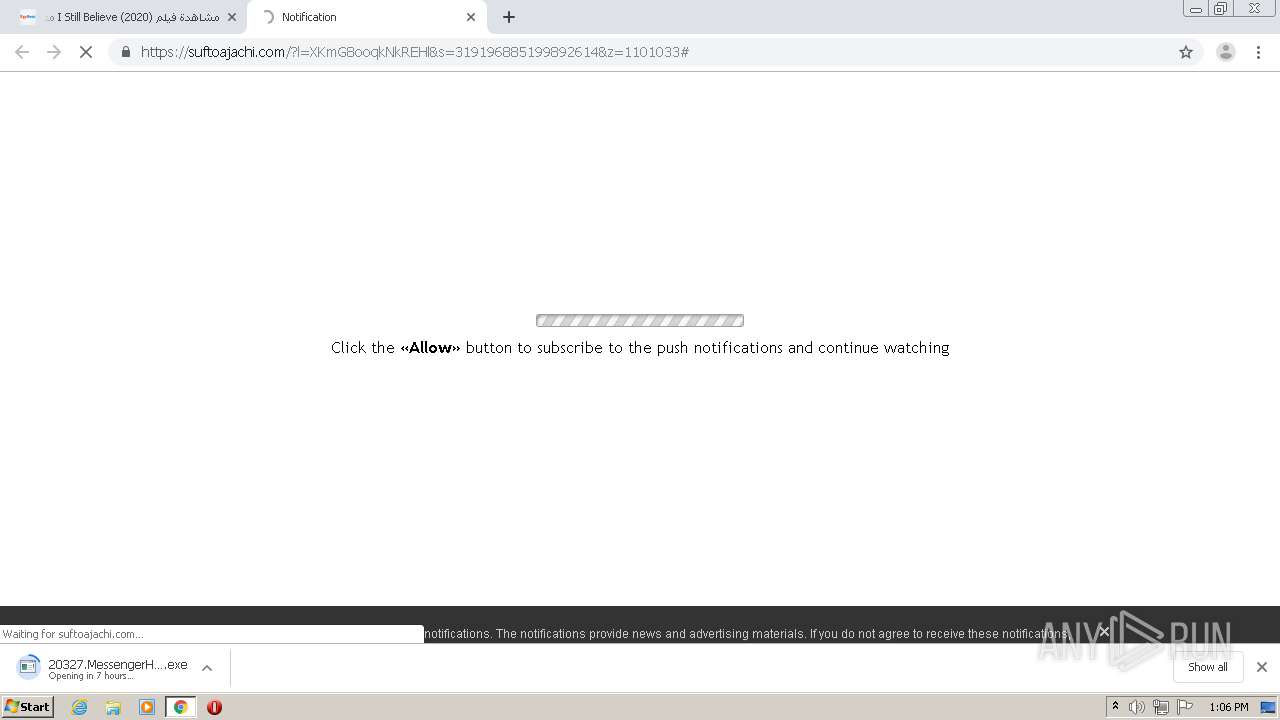
Executable content was dropped or overwritten
- chrome.exe (PID: 2816)
INFO
Reads the hosts file
- chrome.exe (PID: 2816)
- chrome.exe (PID: 2420)
Reads settings of System Certificates
- chrome.exe (PID: 2420)
Changes settings of System certificates
- chrome.exe (PID: 2420)
Creates files in the user directory
- chrome.exe (PID: 2816)
Application launched itself
- chrome.exe (PID: 2816)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
27
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,18283951428063352702,4890264000723468632,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6351652989418956440 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4344 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,18283951428063352702,4890264000723468632,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16200927088085127279 --mojo-platform-channel-handle=2452 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2880 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,18283951428063352702,4890264000723468632,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2486221994227174275 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,18283951428063352702,4890264000723468632,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17131222482823986099 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,18283951428063352702,4890264000723468632,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16997130958328346288 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,18283951428063352702,4890264000723468632,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16638505072234996093 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=696 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,18283951428063352702,4890264000723468632,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9055364703381964129 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2684 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,18283951428063352702,4890264000723468632,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14210033086137316139 --mojo-platform-channel-handle=3652 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,18283951428063352702,4890264000723468632,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12494328572800832393 --mojo-platform-channel-handle=1596 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 004
Read events
911
Write events
89
Delete events
4
Modification events
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2816-13242139453452375 |
Value: 259 | |||
Executable files
2
Suspicious files
281
Text files
163
Unknown types
50
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\faa41b45-79f6-4f27-8ee8-65af2105f4f4.tmp | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF14e6c4.TMP | text | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF14e722.TMP | text | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF14e8f7.TMP | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF14e703.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
143
DNS requests
84
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
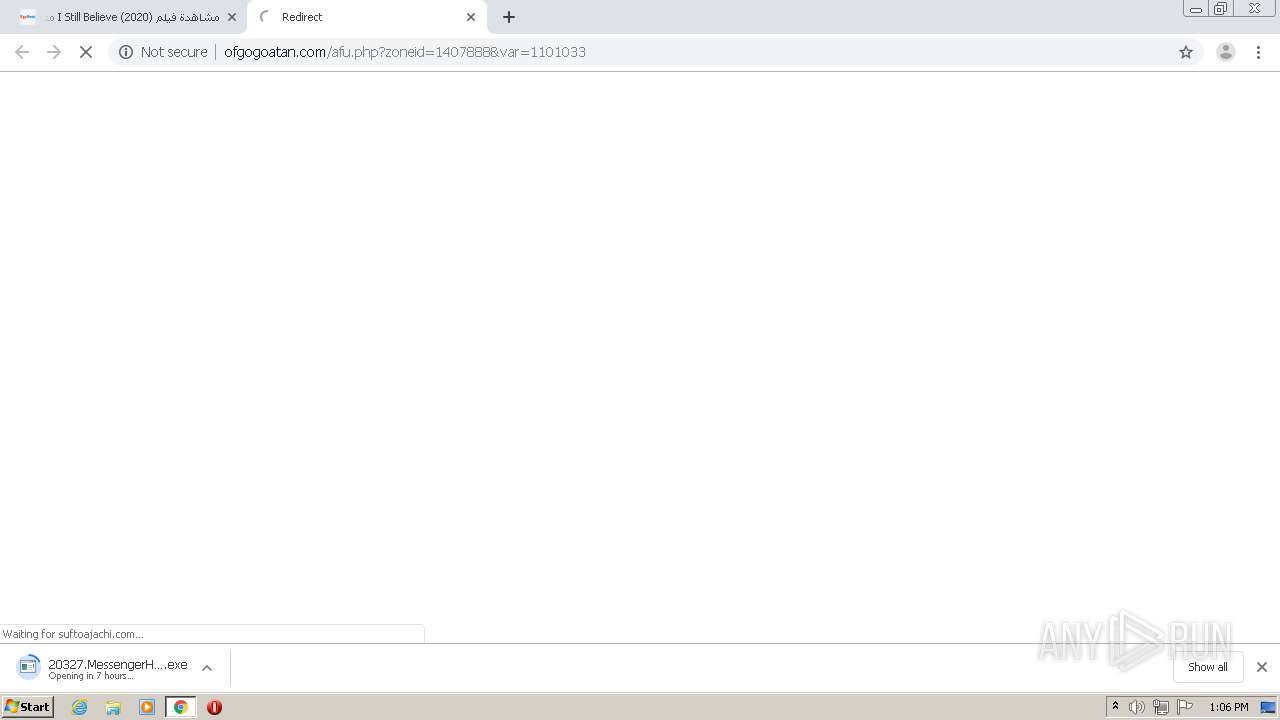
2420 | chrome.exe | GET | 200 | 139.45.195.49:80 | http://ofgogoatan.com/afu.php?zoneid=1101033 | US | html | 712 b | whitelisted |
2420 | chrome.exe | GET | 200 | 139.45.195.49:80 | http://ofgogoatan.com/afu.php?zoneid=1101033 | US | html | 712 b | whitelisted |
2420 | chrome.exe | GET | 200 | 139.45.195.49:80 | http://ofgogoatan.com/afu.php?zoneid=1101033 | US | html | 713 b | whitelisted |
2420 | chrome.exe | GET | 200 | 104.18.11.39:80 | http://cacerts.rapidssl.com/RapidSSLRSACA2018.crt | US | der | 1.18 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2420 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
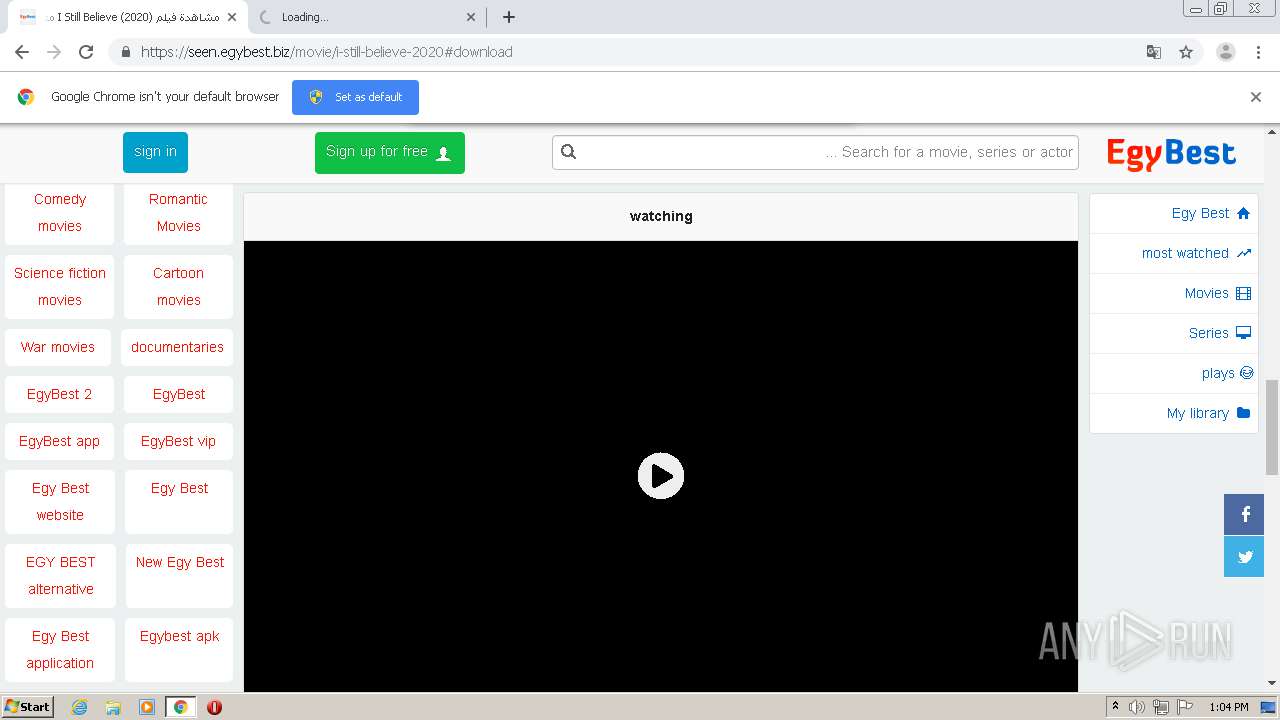
2420 | chrome.exe | 104.24.96.254:443 | seen.egybest.biz | Cloudflare Inc | US | unknown |
2420 | chrome.exe | 104.27.135.29:443 | cdn-static.egybest.net | Cloudflare Inc | US | unknown |
2420 | chrome.exe | 51.68.186.43:443 | capsfogpeck.com | — | GB | unknown |
2420 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2420 | chrome.exe | 172.217.16.182:443 | i.ytimg.com | Google Inc. | US | whitelisted |
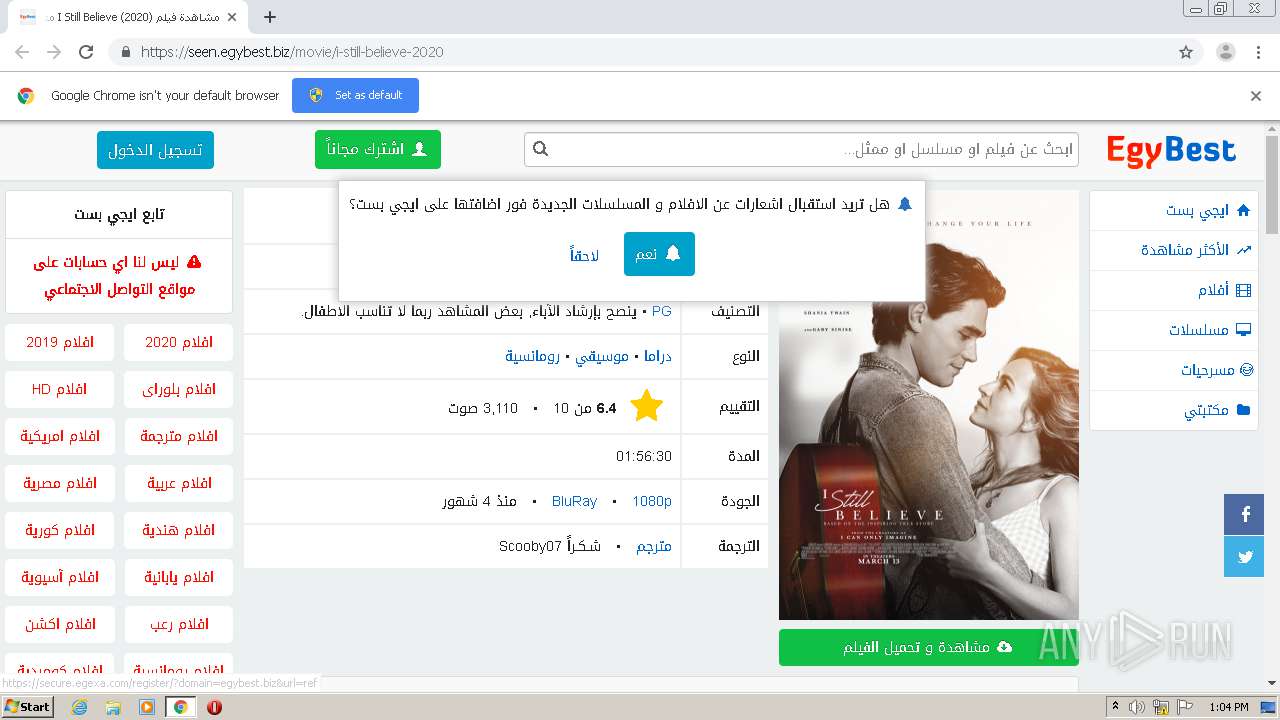
2420 | chrome.exe | 104.27.144.225:443 | secure.egexa.com | Cloudflare Inc | US | unknown |
2420 | chrome.exe | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2420 | chrome.exe | 172.217.22.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
2420 | chrome.exe | 74.125.140.188:5228 | mtalk.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
seen.egybest.biz |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
cdn-static.egybest.net |
| suspicious |
capsfogpeck.com |
| unknown |
pic.egybest.net |
| suspicious |
i.ytimg.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
secure.egexa.com |
| malicious |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |