| File name: | aupcsetup.exe |
| Full analysis: | https://app.any.run/tasks/288206e1-afba-43ff-a939-b96f4436811a |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2019, 06:15:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 14AC36DE703127411D27DBF7B4DE5D2F |
| SHA1: | FED3DF6843ED1F189C8C789736BE0CC1A414DD07 |
| SHA256: | E0B157BF9CE29F6CFC26834C69814DB7A11FB1FA1B882C42FF70DB241A8509F5 |
| SSDEEP: | 196608:FA3058p032WZbzSbHft8WNc50F6tDdOt1uLTAtHRu5OuIdroeSJG:Fe0K0328zWHl8WNc500ct1gTAtIHGU |
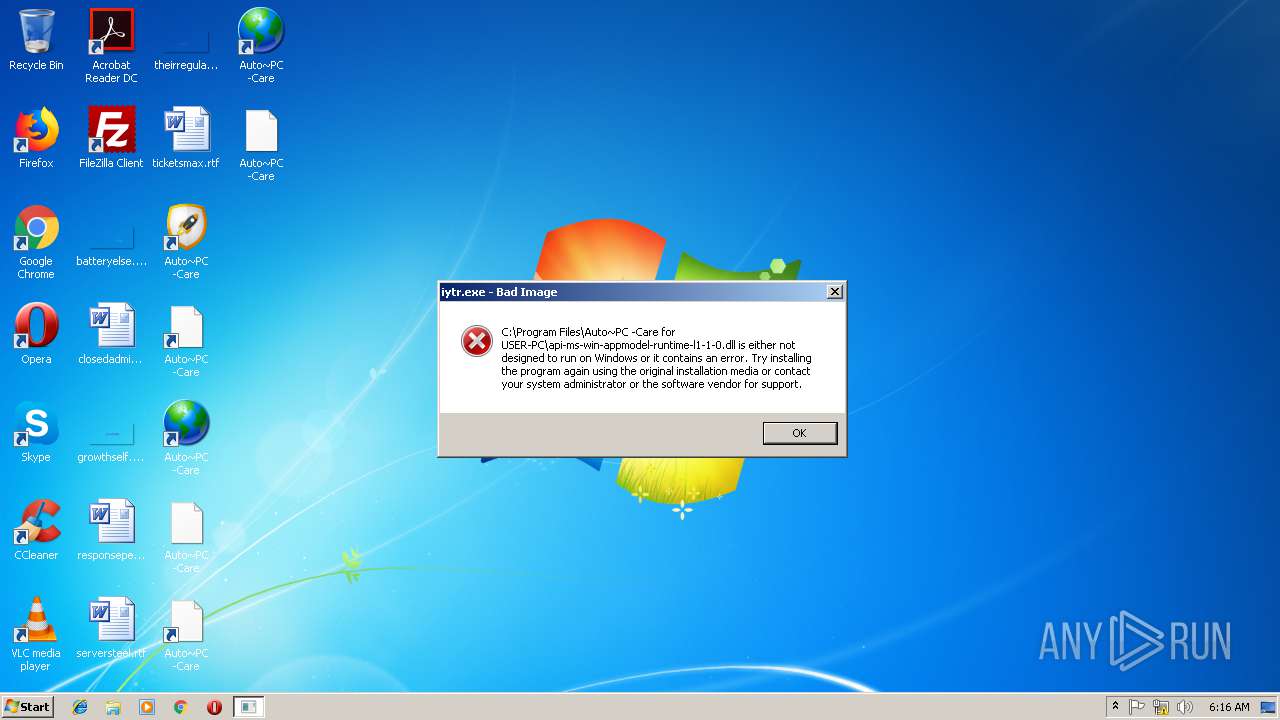
MALICIOUS
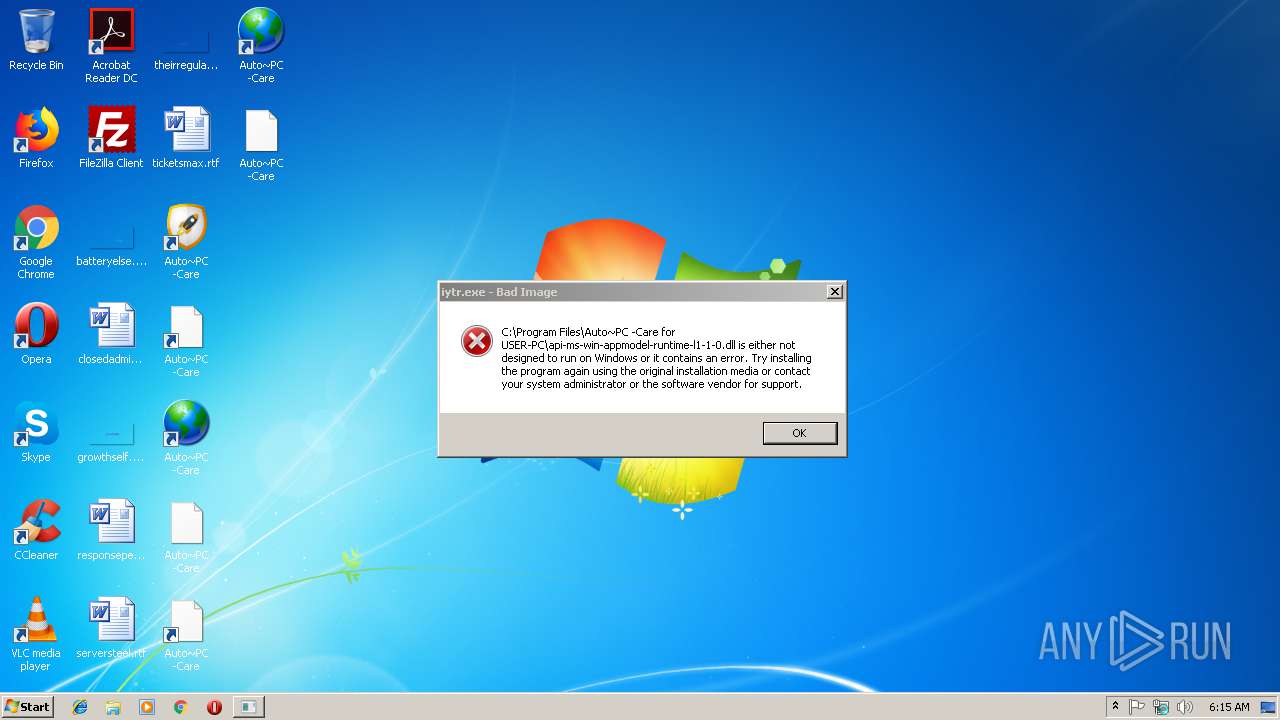
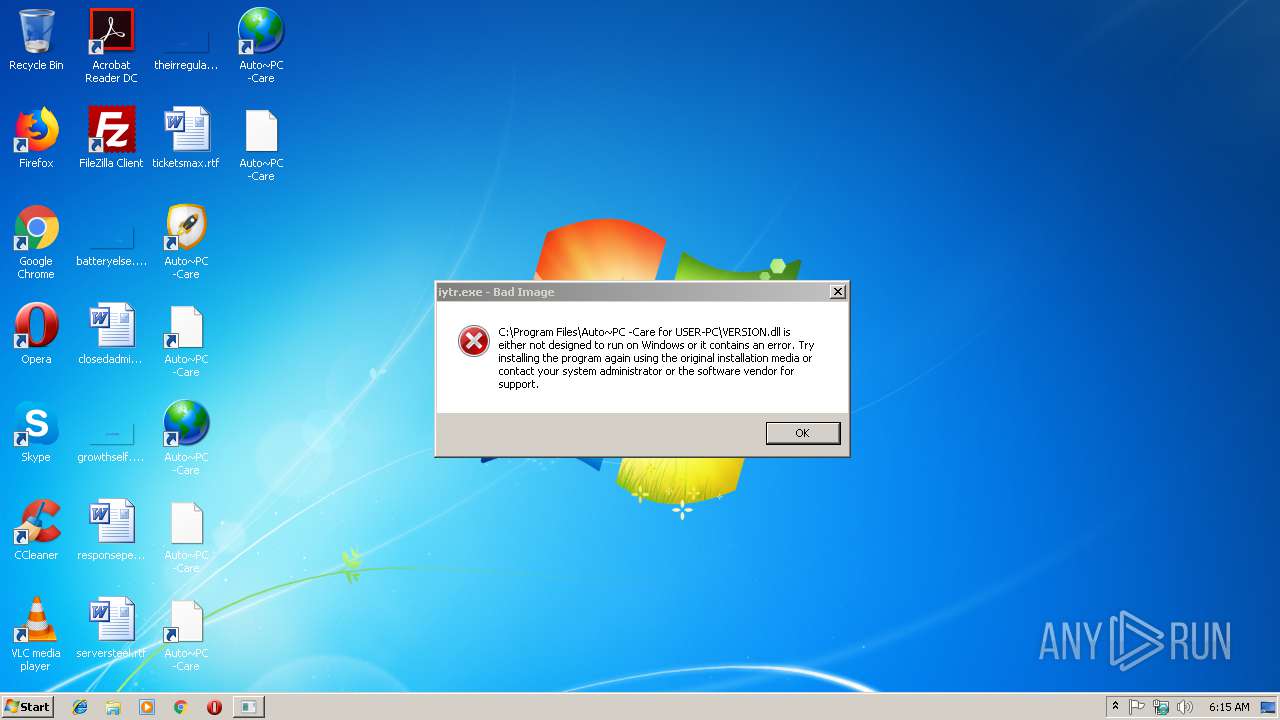
Application was dropped or rewritten from another process
- iytr.exe (PID: 3924)
- iytr.exe (PID: 2196)
- iytr.exe (PID: 3700)
Loads dropped or rewritten executable
- iytr.exe (PID: 3924)
Loads the Task Scheduler COM API
- iytr.exe (PID: 3924)
SUSPICIOUS
Reads Windows owner or organization settings
- aupcsetup.tmp (PID: 2432)
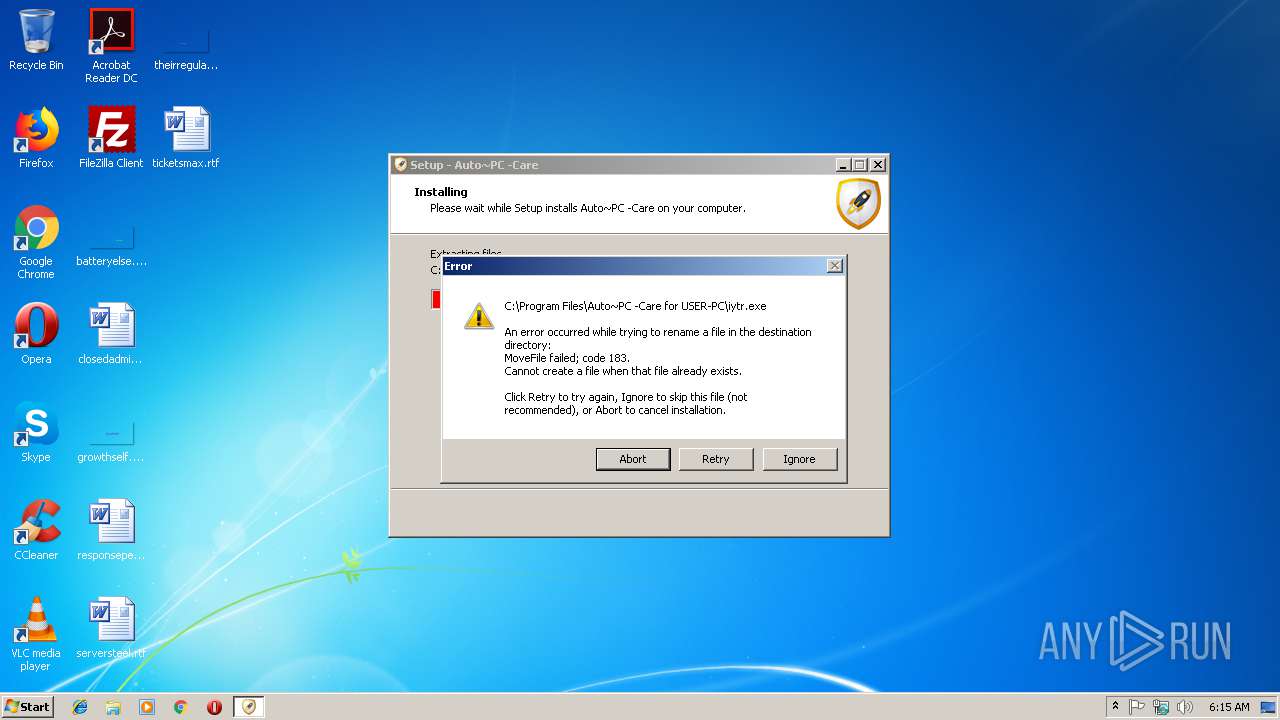
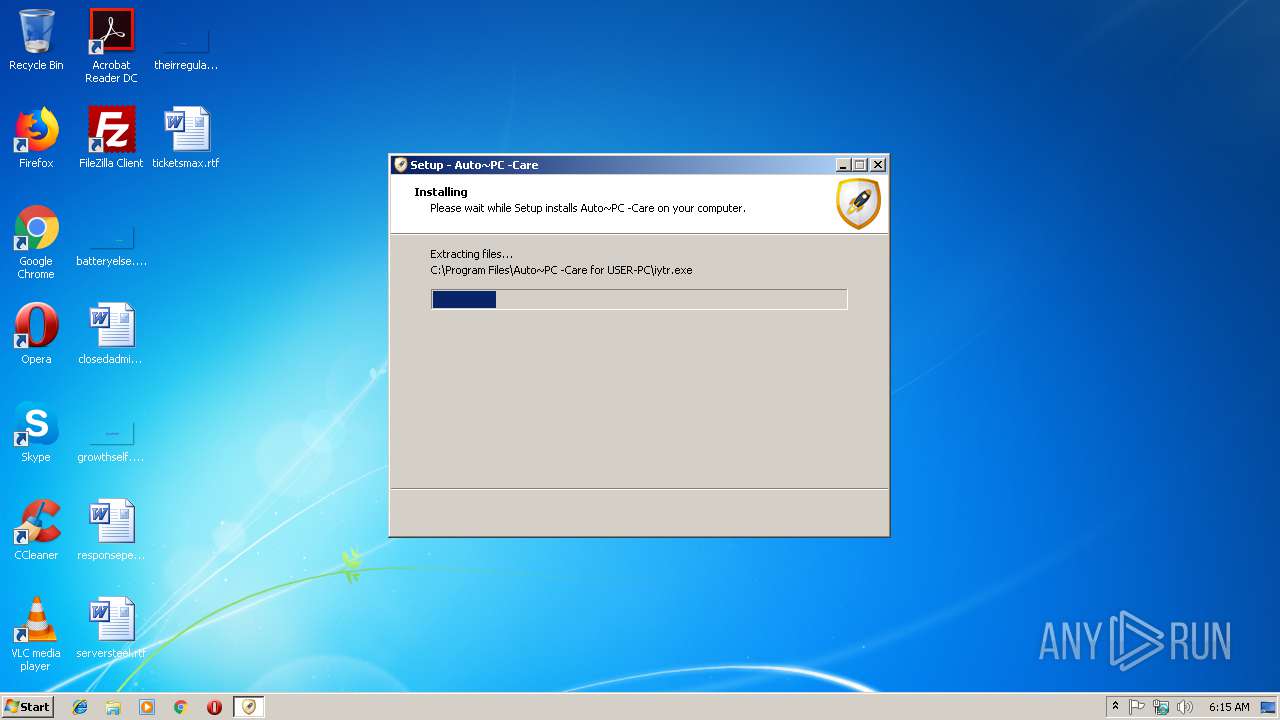
Executable content was dropped or overwritten
- aupcsetup.exe (PID: 3812)
- aupcsetup.exe (PID: 4076)
- aupcsetup.tmp (PID: 2432)
Reads the Windows organization settings
- aupcsetup.tmp (PID: 2432)
Uses TASKKILL.EXE to kill process
- aupcsetup.tmp (PID: 2432)
Creates files in the user directory
- iytr.exe (PID: 3924)
INFO
Application was dropped or rewritten from another process
- aupcsetup.tmp (PID: 2432)
- aupcsetup.tmp (PID: 2468)
Loads dropped or rewritten executable
- aupcsetup.tmp (PID: 2432)
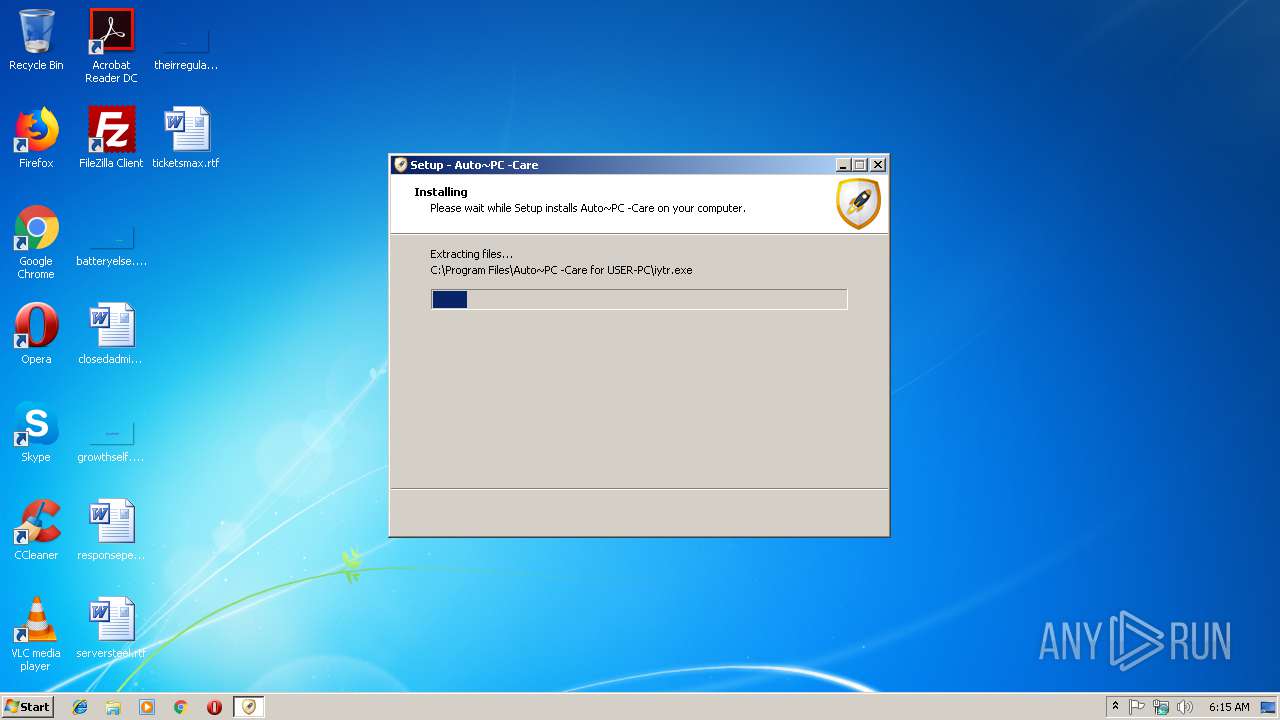
Creates files in the program directory
- aupcsetup.tmp (PID: 2432)
Creates a software uninstall entry
- aupcsetup.tmp (PID: 2432)
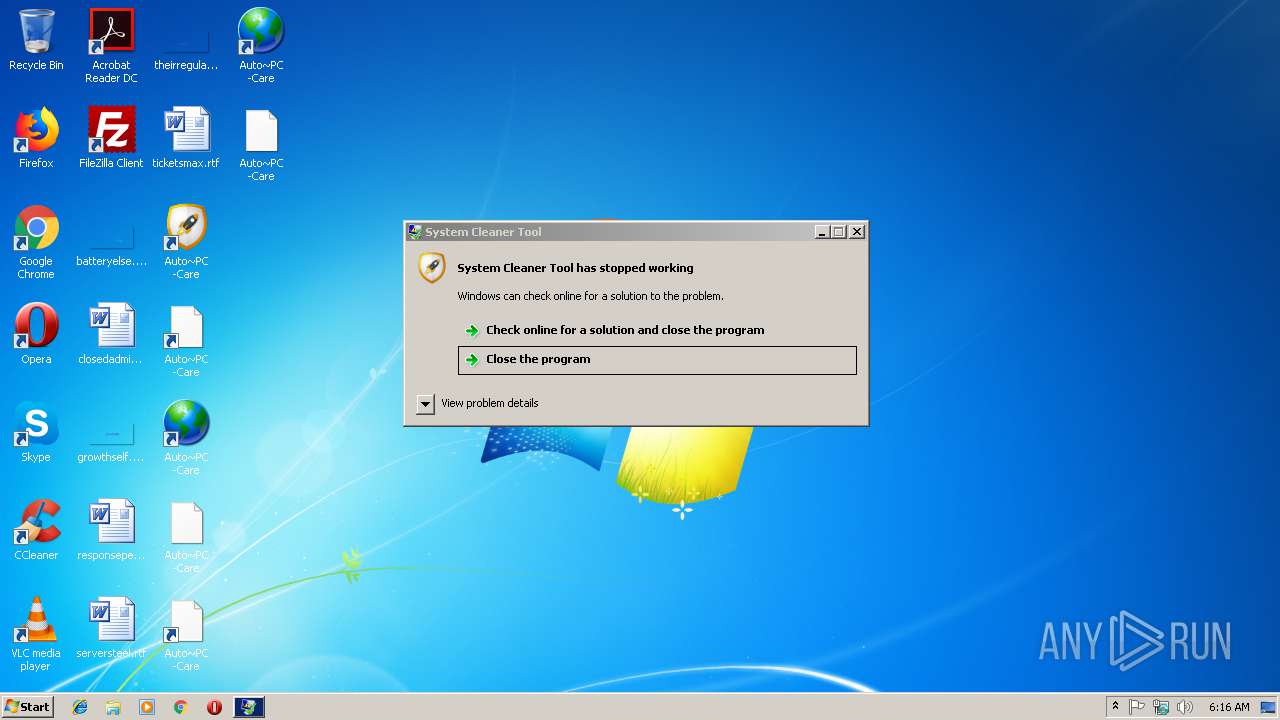
Application was crashed
- iytr.exe (PID: 2196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:01:15 09:22:50+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 65024 |
| InitializedDataSize: | 104448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x113bc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.0.94 |
| ProductVersionNumber: | 3.0.0.94 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
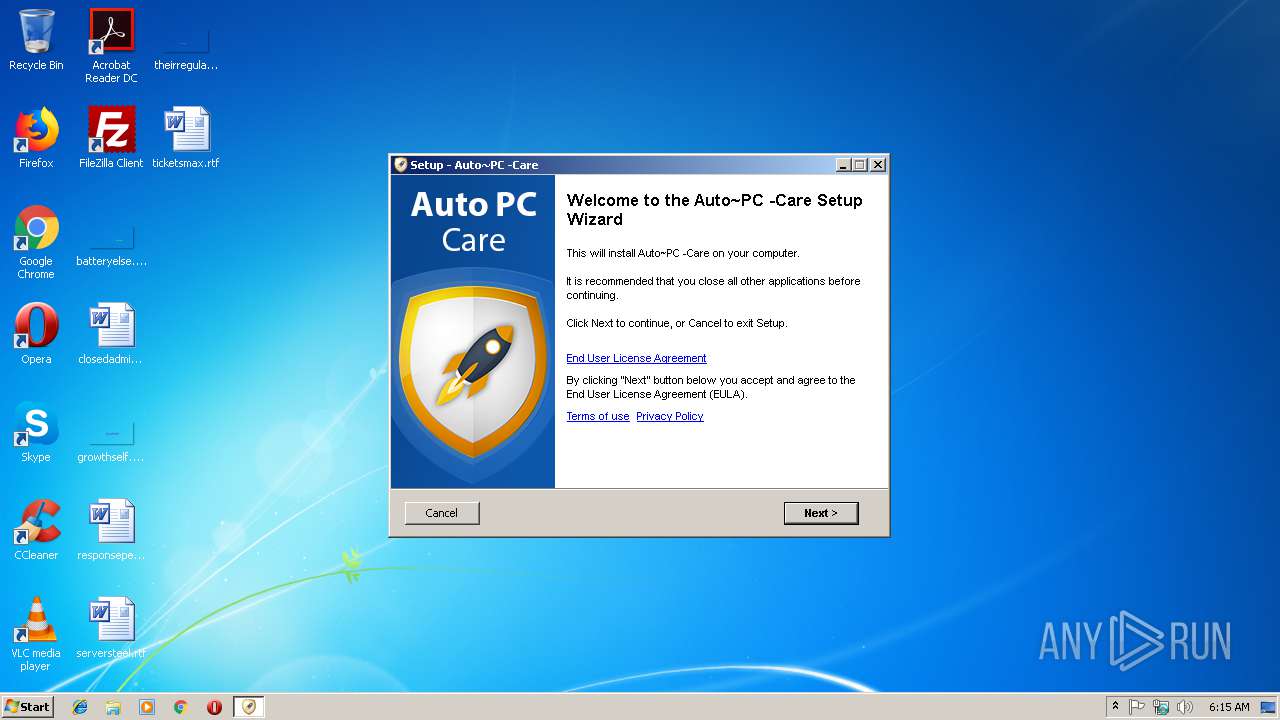
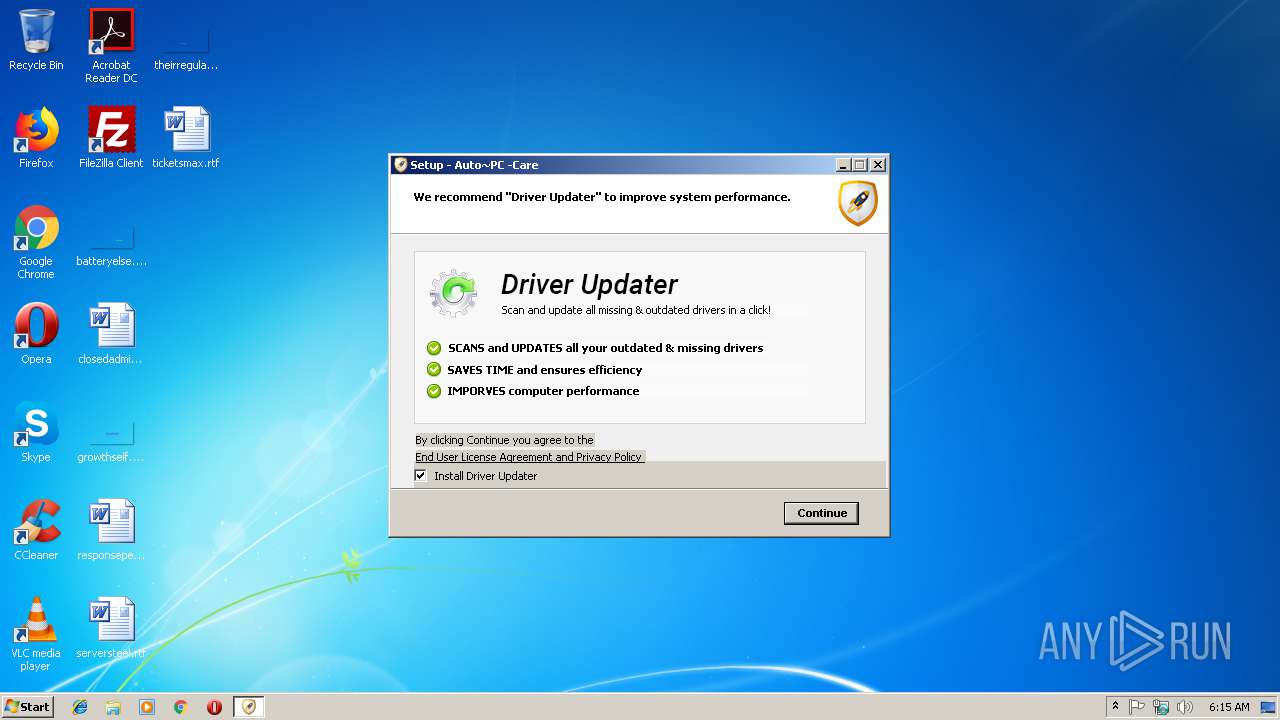
| FileDescription: | Auto~PC -Care Setup |
| FileVersion: | 3.0.0.94 |
| LegalCopyright: | |
| ProductName: | Auto~PC -Care |
| ProductVersion: | 3.0.0.94 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jan-2016 08:22:50 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Auto~PC -Care Setup |
| FileVersion: | 3.0.0.94 |
| LegalCopyright: | - |
| ProductName: | Auto~PC -Care |
| ProductVersion: | 3.0.0.94 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 15-Jan-2016 08:22:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F134 | 0x0000F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39169 |
.itext | 0x00011000 | 0x00000B44 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.74305 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.24753 |
.bss | 0x00013000 | 0x000056B8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000DD0 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97188 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x000179C8 | 0x00017A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.1072 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.01167 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.23539 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.36474 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.58309 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.64239 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
45
Monitored processes
8
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | "C:\Program Files\Auto~PC -Care for USER-PC\iytr.exe" firstshow | C:\Program Files\Auto~PC -Care for USER-PC\iytr.exe | aupcsetup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: System Cleaner Tool Exit code: 3228369022 Version: 3.0.0.94 Modules
| |||||||||||||||
| 2432 | "C:\Users\admin\AppData\Local\Temp\is-TTFJ0.tmp\aupcsetup.tmp" /SL5="$40192,7263879,170496,C:\Users\admin\AppData\Local\Temp\aupcsetup.exe" /SPAWNWND=$3019A /NOTIFYWND=$30190 | C:\Users\admin\AppData\Local\Temp\is-TTFJ0.tmp\aupcsetup.tmp | aupcsetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2468 | "C:\Users\admin\AppData\Local\Temp\is-7RFPL.tmp\aupcsetup.tmp" /SL5="$30190,7263879,170496,C:\Users\admin\AppData\Local\Temp\aupcsetup.exe" | C:\Users\admin\AppData\Local\Temp\is-7RFPL.tmp\aupcsetup.tmp | — | aupcsetup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3620 | "C:\Windows\System32\taskkill.exe" /f /im "iytr.exe" | C:\Windows\System32\taskkill.exe | — | aupcsetup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3700 | "C:\Program Files\Auto~PC -Care for USER-PC\iytr.exe" | C:\Program Files\Auto~PC -Care for USER-PC\iytr.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: System Cleaner Tool Exit code: 0 Version: 3.0.0.94 Modules
| |||||||||||||||
| 3812 | "C:\Users\admin\AppData\Local\Temp\aupcsetup.exe" | C:\Users\admin\AppData\Local\Temp\aupcsetup.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Auto~PC -Care Setup Exit code: 0 Version: 3.0.0.94 Modules
| |||||||||||||||
| 3924 | "C:\Program Files\Auto~PC -Care for USER-PC\iytr.exe" getwebparam | C:\Program Files\Auto~PC -Care for USER-PC\iytr.exe | aupcsetup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: System Cleaner Tool Exit code: 1 Version: 3.0.0.94 Modules
| |||||||||||||||
| 4076 | "C:\Users\admin\AppData\Local\Temp\aupcsetup.exe" /SPAWNWND=$3019A /NOTIFYWND=$30190 | C:\Users\admin\AppData\Local\Temp\aupcsetup.exe | aupcsetup.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Auto~PC -Care Setup Exit code: 0 Version: 3.0.0.94 Modules
| |||||||||||||||
Total events
757
Read events
610
Write events
141
Delete events
6
Modification events
| (PID) Process: | (2432) aupcsetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 800900002A063C0875A9D401 | |||
| (PID) Process: | (2432) aupcsetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 309617B4DFADD4337749E203A5C88D788747E893F190201C1FB338132DC35577 | |||
| (PID) Process: | (2432) aupcsetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2432) aupcsetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2432) aupcsetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2432) aupcsetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Auto~PC -Care for USER-PC\iytr.exe | |||
| (PID) Process: | (2432) aupcsetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 20D1D2CB8F3F87DB3236D1512918214549AF38D38C604AB7B8250EEA577F1E39 | |||
| (PID) Process: | (2432) aupcsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Auto~PC -Care For USER-PC |
| Operation: | write | Name: | TELNO |
Value: (855)-332-0124 | |||
| (PID) Process: | (2432) aupcsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Auto~PC -Care For USER-PC |
| Operation: | write | Name: | ISTELNO |
Value: 1 | |||
| (PID) Process: | (2432) aupcsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Auto~PC -Care For USER-PC |
| Operation: | write | Name: | apst |
Value: 0 | |||
Executable files
19
Suspicious files
2
Text files
24
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2432 | aupcsetup.tmp | C:\Program Files\Auto~PC -Care for USER-PC\is-OD3FB.tmp | — | |
MD5:— | SHA256:— | |||
| 2432 | aupcsetup.tmp | C:\Program Files\Auto~PC -Care for USER-PC\is-D92VF.tmp | — | |
MD5:— | SHA256:— | |||
| 2432 | aupcsetup.tmp | C:\Program Files\Auto~PC -Care for USER-PC\iytr.exe | — | |
MD5:— | SHA256:— | |||
| 2432 | aupcsetup.tmp | C:\Program Files\Auto~PC -Care for USER-PC\is-JU337.tmp | — | |
MD5:— | SHA256:— | |||
| 2432 | aupcsetup.tmp | C:\Program Files\Auto~PC -Care for USER-PC\is-MFOMB.tmp | — | |
MD5:— | SHA256:— | |||
| 2432 | aupcsetup.tmp | C:\Program Files\Auto~PC -Care for USER-PC\is-2RLN6.tmp | — | |
MD5:— | SHA256:— | |||
| 2432 | aupcsetup.tmp | C:\Program Files\Auto~PC -Care for USER-PC\is-5241L.tmp | — | |
MD5:— | SHA256:— | |||
| 2432 | aupcsetup.tmp | C:\Program Files\Auto~PC -Care for USER-PC\is-D75L7.tmp | — | |
MD5:— | SHA256:— | |||
| 2432 | aupcsetup.tmp | C:\Program Files\Auto~PC -Care for USER-PC\is-KVNJ7.tmp | — | |
MD5:— | SHA256:— | |||
| 2432 | aupcsetup.tmp | C:\Program Files\Auto~PC -Care for USER-PC\is-0RAMG.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3924 | iytr.exe | GET | 404 | 87.248.214.129:80 | http://trkr.trkinstl.com/ipfiles/85_203_20_17.txt | IT | — | — | malicious |
3924 | iytr.exe | GET | 200 | 63.143.46.130:80 | http://www.trkinstl.com/getip/ | US | text | 12 b | malicious |
3924 | iytr.exe | GET | 200 | 63.143.46.130:80 | http://cc.trkinstl.com/productprice.svc/getcountrycode | US | text | 4 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3924 | iytr.exe | 63.143.46.130:80 | cc.trkinstl.com | Limestone Networks, Inc. | US | malicious |
3924 | iytr.exe | 87.248.214.129:80 | trkr.trkinstl.com | Limelight Networks, Inc. | IT | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cc.trkinstl.com |
| malicious |
www.trkinstl.com |
| malicious |
trkr.trkinstl.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3924 | iytr.exe | A Network Trojan was detected | SC ADWARE AdWare PUA:Win32/SpeedChecker / MSIL/GT32SupportGeeks |
Process | Message |
|---|---|
iytr.exe | Native library pre-loader is trying to load native SQLite library "C:\Program Files\Auto~PC -Care for USER-PC\x86\SQLite.Interop.dll"...
|
iytr.exe | Native library pre-loader failed to get setting "SQLite_ForceLogPrepare" value: System.Xml.XmlException: Root element is missing.
at System.Xml.XmlTextReaderImpl.Throw(Exception e)
at System.Xml.XmlTextReaderImpl.ThrowWithoutLineInfo(String res)
at System.Xml.XmlTextReaderImpl.ParseDocumentContent()
at System.Xml.XmlTextReaderImpl.Read()
at System.Xml.XmlLoader.Load(XmlDocument doc, XmlReader reader, Boolean preserveWhitespace)
at System.Xml.XmlDocument.Load(XmlReader reader)
at System.Xml.XmlDocument.Load(String filename)
at System.Data.SQLite.UnsafeNativeMethods.GetSettingValue(String name, String default)
|