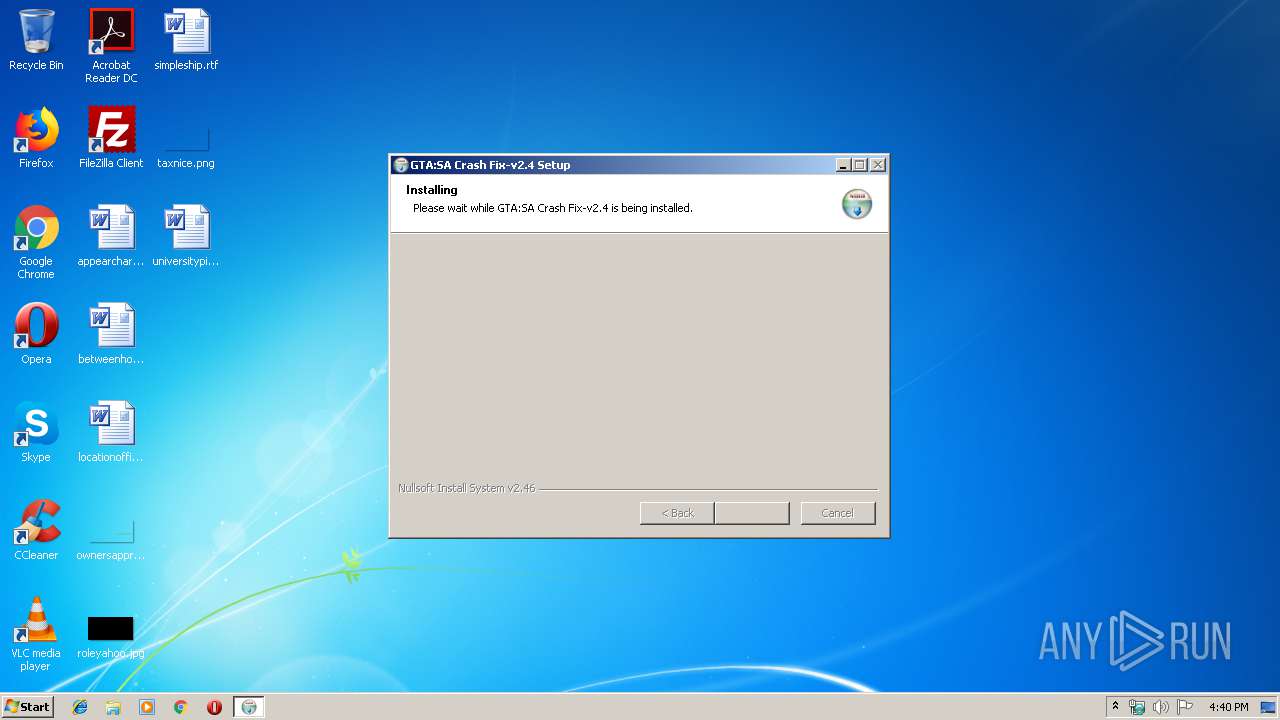
| File name: | crashes-v2.4.exe |
| Full analysis: | https://app.any.run/tasks/3c04d41a-a058-47fa-aff7-aa1efb7a1d8c |
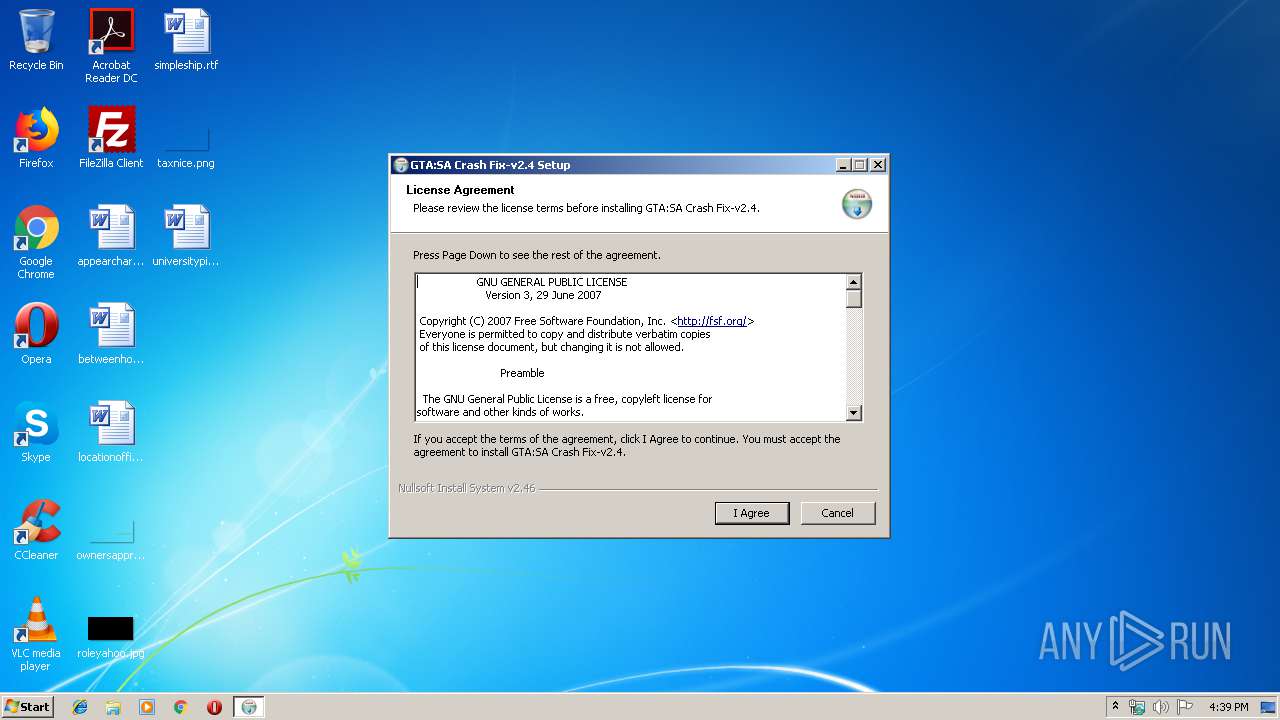
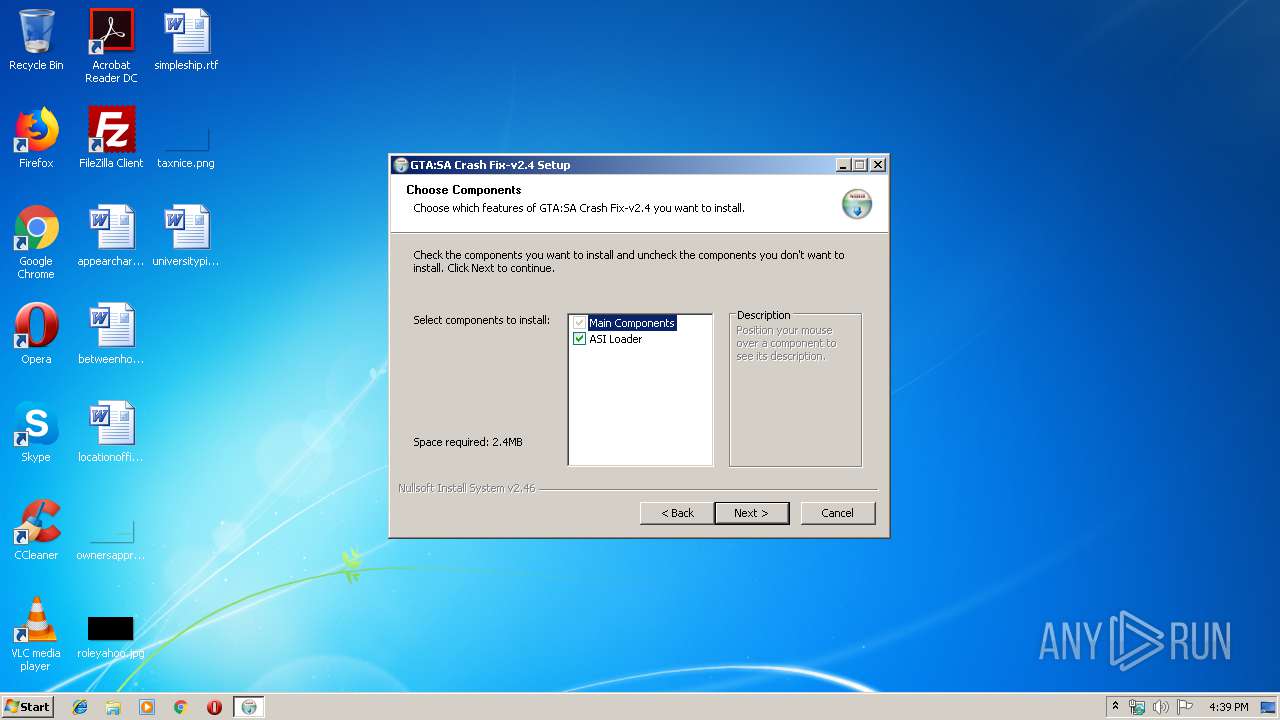
| Verdict: | Malicious activity |
| Analysis date: | November 17, 2019, 16:39:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C5DF14BDF69D52237ECE428C80A17C9E |
| SHA1: | 04F6EC9CB2EE08DDD3F477A93D55B538CE98BE0B |
| SHA256: | E0A8CDD3890C374CE93F01CE5A3D23FD66F3747EFD57AA37BF735CDE60EF4070 |
| SSDEEP: | 24576:W3qWlqZItc1WnlpmNC8O+JpuSCQDa3DQnfkPseWdwuyXGyMEY:hWlqZItRTmg+i3QDkOfkPmdXd1 |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3472)
Application was dropped or rewritten from another process
- crashes-v2.4.exe (PID: 2744)
- crashes-v2.4.exe (PID: 1324)
SUSPICIOUS
Executable content was dropped or overwritten
- crashes-v2.4.exe (PID: 2768)
- crashes-v2.4.exe (PID: 2744)
Creates a software uninstall entry
- crashes-v2.4.exe (PID: 2744)
Executed via COM
- DllHost.exe (PID: 1976)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 6 (93.8) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (2.3) |
| .exe | | | Win32 Executable (generic) (1.6) |
| .exe | | | Win16/32 Executable Delphi generic (0.7) |
| .exe | | | Generic Win/DOS Executable (0.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 29696 |
| InitializedDataSize: | 10752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x80e4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000722C | 0x00007400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51167 |
DATA | 0x00009000 | 0x00000218 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.1517 |
BSS | 0x0000A000 | 0x0000A899 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00015000 | 0x00000864 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.17386 |
.tls | 0x00016000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00017000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.20692 |
.reloc | 0x00018000 | 0x000005CC | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.44309 |
.rsrc | 0x00019000 | 0x00001400 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.34792 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 6.26582 | 4264 | UNKNOWN | Russian - Russia | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 6.90278 | 172 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 1.7815 | 20 | UNKNOWN | Russian - Russia | RT_GROUP_ICON |
Imports
advapi32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
41
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1324 | "C:\Users\admin\AppData\Local\Temp\3582-490\crashes-v2.4.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\crashes-v2.4.exe | — | crashes-v2.4.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1976 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2744 | "C:\Users\admin\AppData\Local\Temp\3582-490\crashes-v2.4.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\crashes-v2.4.exe | crashes-v2.4.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2768 | "C:\Users\admin\AppData\Local\Temp\crashes-v2.4.exe" | C:\Users\admin\AppData\Local\Temp\crashes-v2.4.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3472 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 145
Read events
1 127
Write events
18
Delete events
0
Modification events
| (PID) Process: | (2768) crashes-v2.4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2768) crashes-v2.4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2744) crashes-v2.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2744) crashes-v2.4.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-2 |
Value: Access the computers and devices that are on your network. | |||
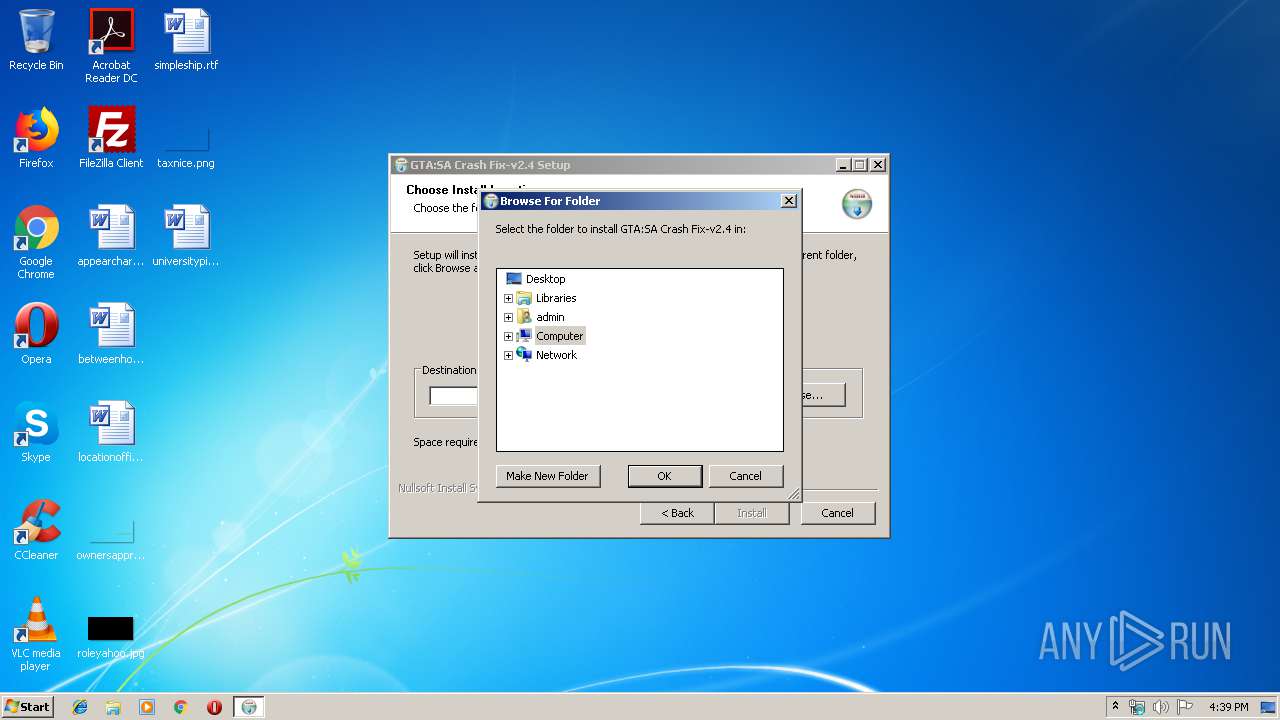
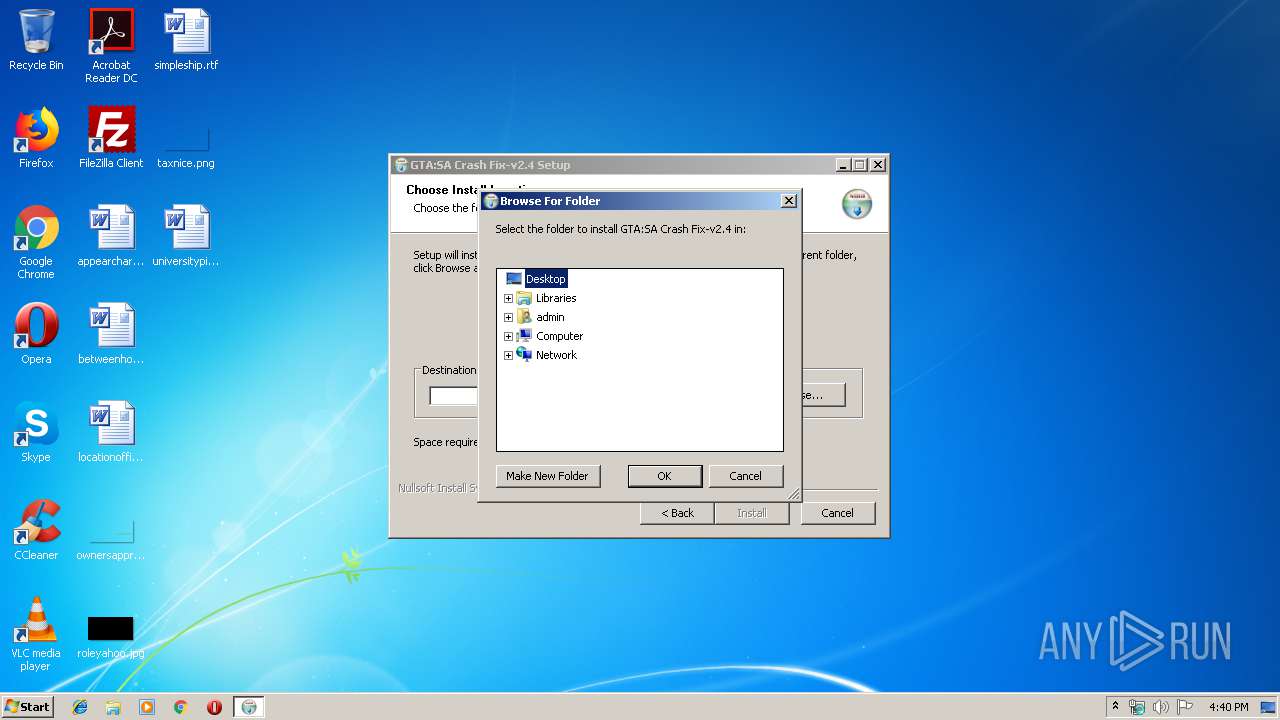
| (PID) Process: | (2744) crashes-v2.4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (2744) crashes-v2.4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
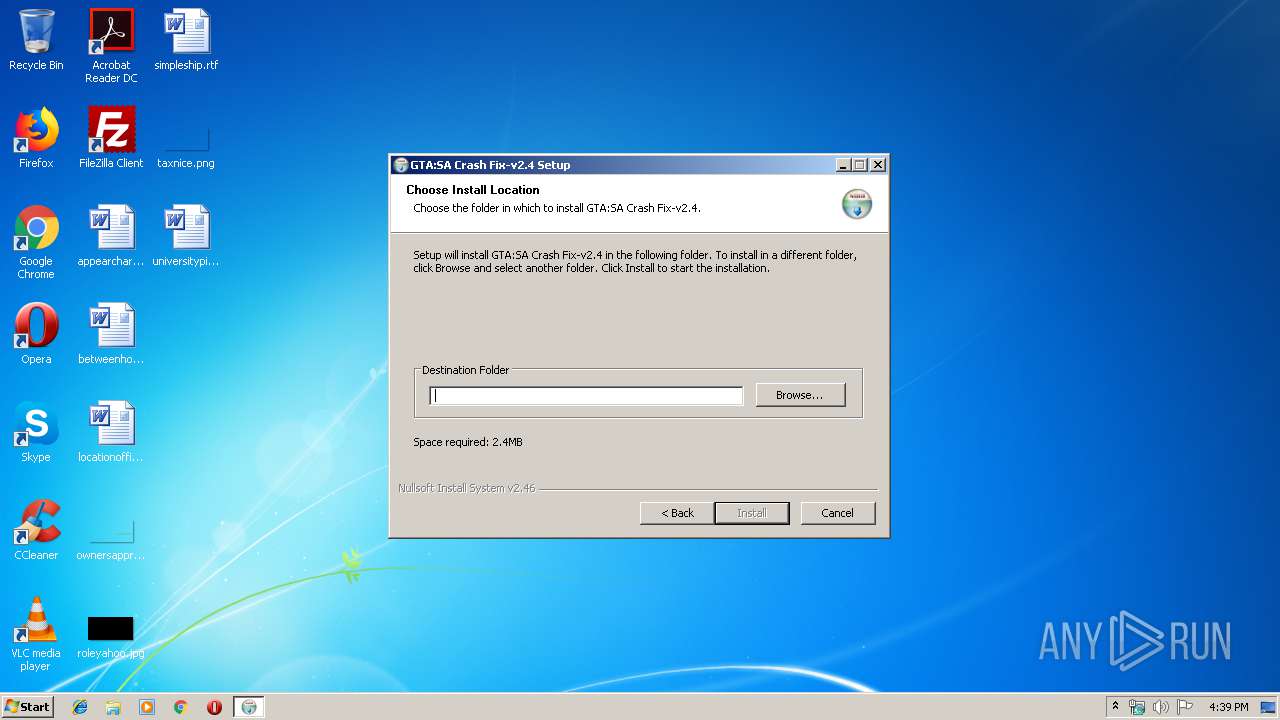
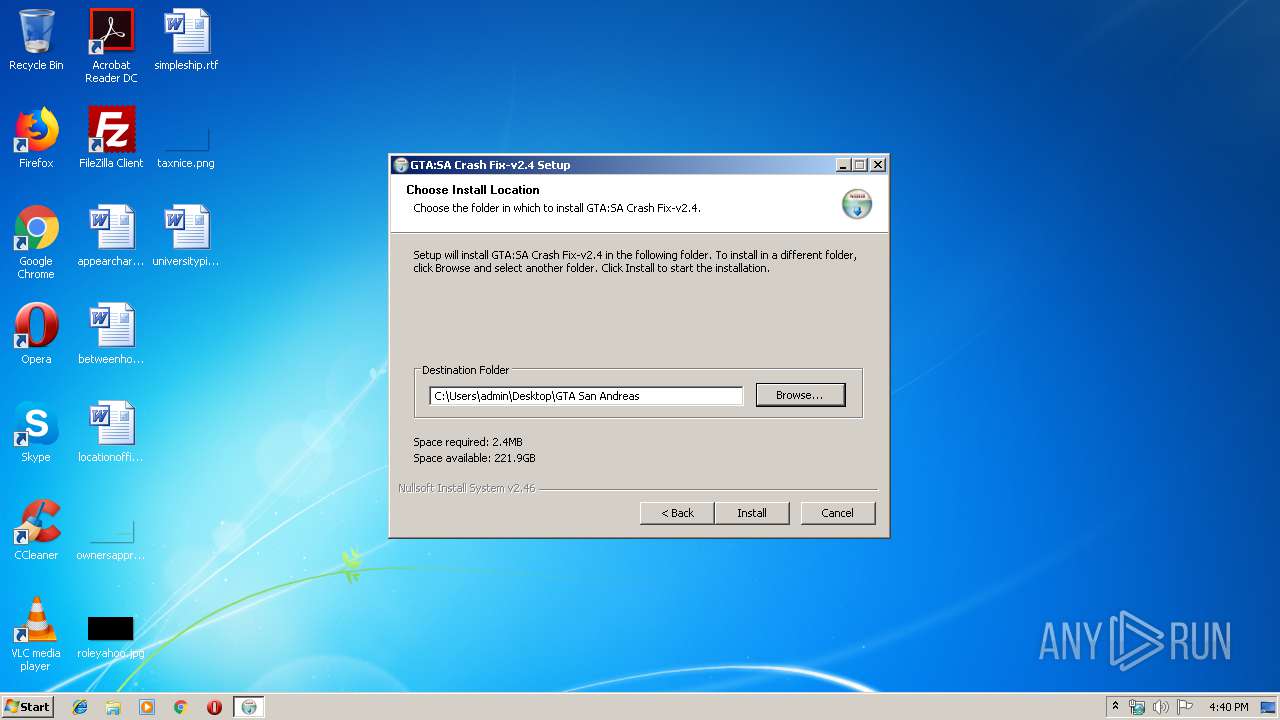
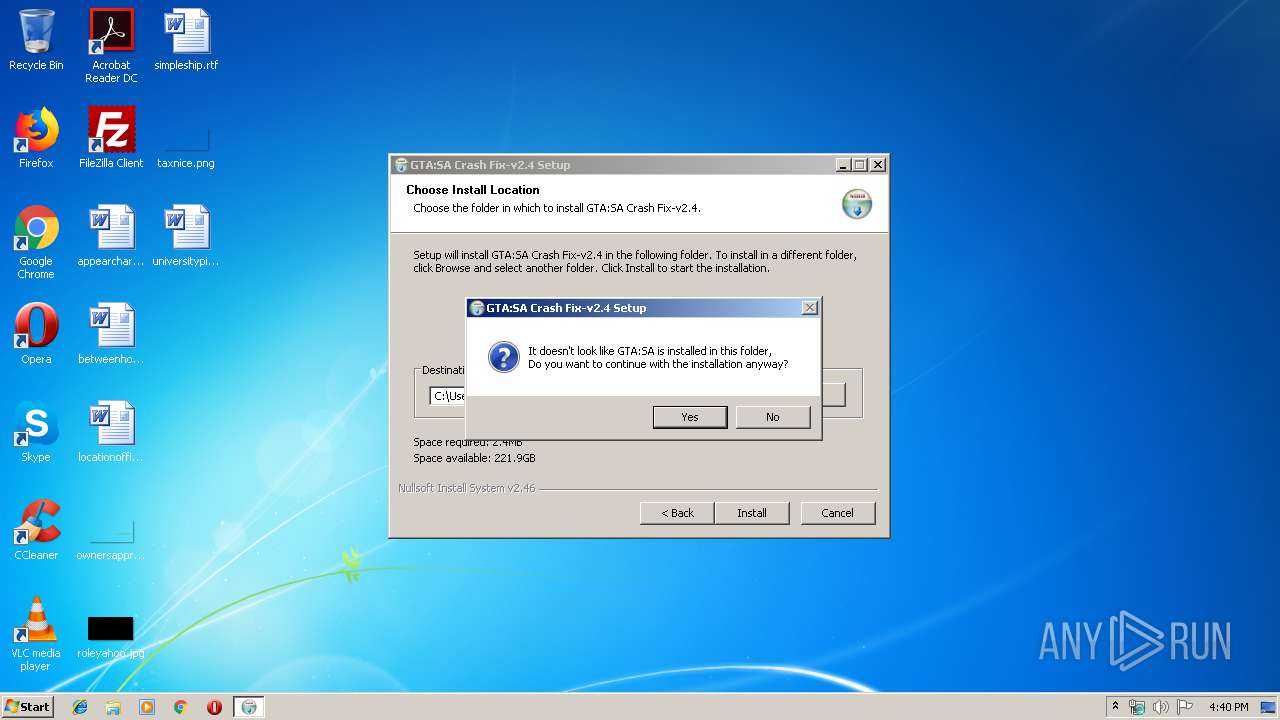
| (PID) Process: | (2744) crashes-v2.4.exe | Key: | HKEY_CURRENT_USER\Software\crashesasi |
| Operation: | write | Name: | |
Value: C:\Users\admin\Desktop\GTA San Andreas | |||
| (PID) Process: | (2744) crashes-v2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GTA:SA Crash Fix-v2.4 |
| Operation: | write | Name: | DisplayName |
Value: GTA:SA Crash Fix-v2.4 | |||
| (PID) Process: | (2744) crashes-v2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GTA:SA Crash Fix-v2.4 |
| Operation: | write | Name: | UninstallString |
Value: C:\Users\admin\Desktop\GTA San Andreas\uninstall_crashes.exe | |||
| (PID) Process: | (2744) crashes-v2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GTA:SA Crash Fix-v2.4 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\Desktop\GTA San Andreas\uninstall_crashes.exe | |||
Executable files
8
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2744 | crashes-v2.4.exe | C:\Users\admin\AppData\Local\Temp\nsqAF75.tmp | — | |
MD5:— | SHA256:— | |||
| 2744 | crashes-v2.4.exe | C:\Users\admin\Desktop\GTA San Andreas\uninstall_crashes.exe | executable | |
MD5:— | SHA256:— | |||
| 2744 | crashes-v2.4.exe | C:\Users\admin\Desktop\GTA San Andreas\CrashSender1402.exe | executable | |
MD5:870D76914C77619FD05F44BB732BA5F8 | SHA256:CA3CBD2F17F923961FFF0897D8095D4DA9435A2B70FC5C8788820034D618743A | |||
| 2744 | crashes-v2.4.exe | C:\Users\admin\Desktop\GTA San Andreas\vorbisFile.dll | executable | |
MD5:FBE34F162166FEA391A3F74FF4701A25 | SHA256:A31CBC43A80A6737137500516B6E1973F47E93C24C8599E007F5272747FF0548 | |||
| 2768 | crashes-v2.4.exe | C:\Users\admin\AppData\Local\Temp\tmp5023.tmp | binary | |
MD5:— | SHA256:— | |||
| 2744 | crashes-v2.4.exe | C:\Users\admin\Desktop\GTA San Andreas\crashrpt_lang.ini | text | |
MD5:5B3D69BAFF897B03FBDB3D5A119B3D57 | SHA256:0B27EE8347E0A2E47B89F03EA9439592980DC61FD0B6A69AFA007F7FEBBB8574 | |||
| 2744 | crashes-v2.4.exe | C:\Users\admin\Desktop\GTA San Andreas\CrashRpt1402.dll | executable | |
MD5:A30D8407AC1A2BCBA5361C946C9E5D8A | SHA256:B6739DF785B43BFE9504BF0C58E2CEF09519007F0AE1318FDEE103132540EE44 | |||
| 2768 | crashes-v2.4.exe | C:\Users\admin\AppData\Local\Temp\3582-490\crashes-v2.4.exe | executable | |
MD5:129C295F3D50001C000BD84127D18DF2 | SHA256:564CCE5E981F0FD113680440F44741B12CAEB2E9377FF3056DCFF43CB421774E | |||
| 2744 | crashes-v2.4.exe | C:\Users\admin\Desktop\GTA San Andreas\vorbishooked.dll | executable | |
MD5:2B7B803311D2B228F065C45D13E1AEB2 | SHA256:A08923479000CEC366967FB8259E0920B7AA18859722C7DDA1415726BED4774F | |||
| 2744 | crashes-v2.4.exe | C:\Users\admin\Desktop\GTA San Andreas\crashes.asi | executable | |
MD5:47FC1F23D62BE8573986AB200C178E3C | SHA256:2D60EAAB590A62220034AEAF5416B1028494958A97E7D06CA8B3A266CBB22337 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report