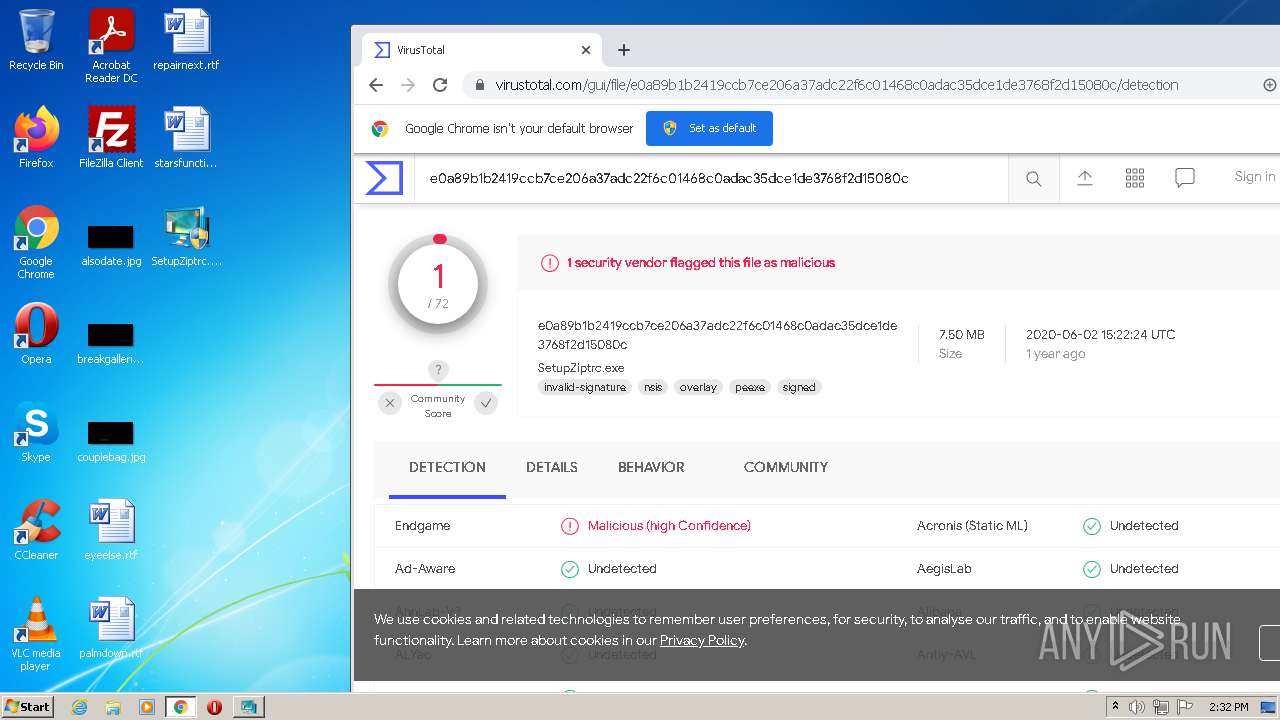
| File name: | SetupZiptrc.exe |
| Full analysis: | https://app.any.run/tasks/107fcafc-ddca-40a0-885b-17783ef7deb0 |
| Verdict: | Malicious activity |
| Analysis date: | September 03, 2021, 13:30:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 143B5C8CE91E02E83968A10125021108 |
| SHA1: | CA985FD4E54AC6D85EE1782A2B5F3405FE53A287 |
| SHA256: | E0A89B1B2419CCB7CE206A37ADC22F6C01468C0ADAC35DCE1DE3768F2D15080C |
| SSDEEP: | 196608:pb2wymqpAU3l0Okg7picA7hOjvXb8lbEfTq14h+/AZ:g5pAU3lSFhqb807hOAZ |
MALICIOUS
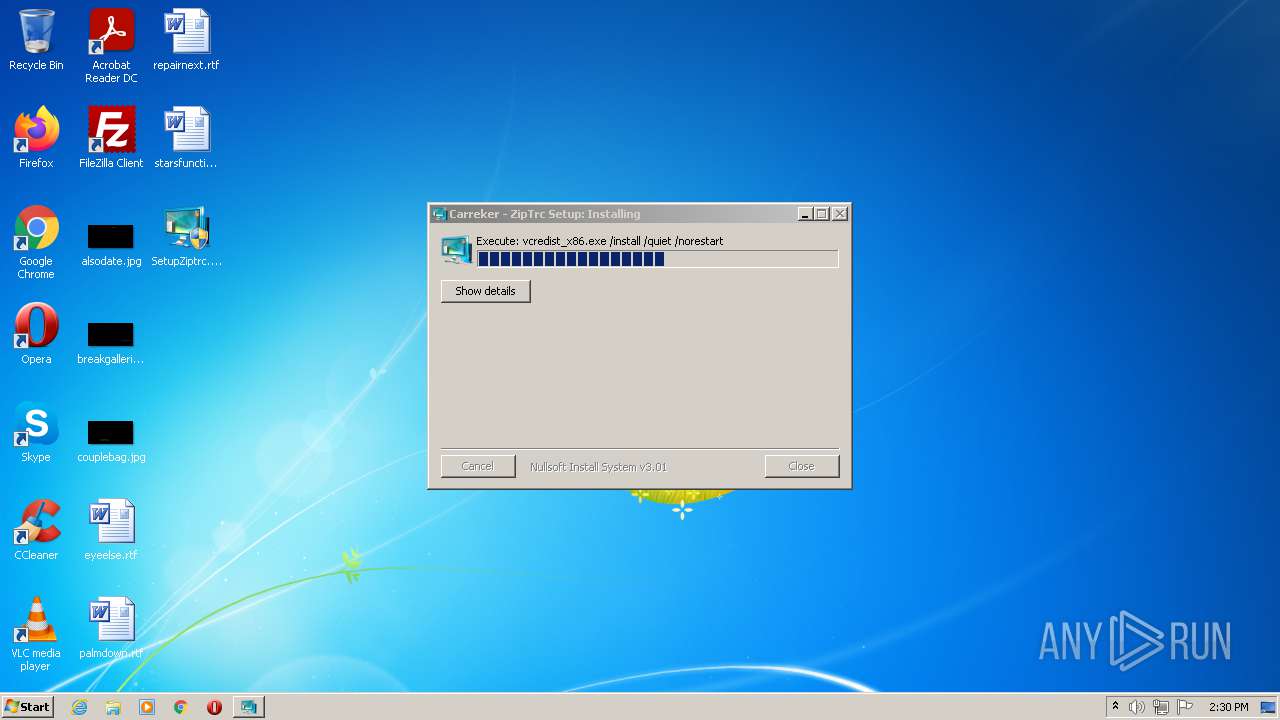
Drops executable file immediately after starts
- SetupZiptrc.exe (PID: 912)
- vcredist_x86.exe (PID: 3828)
Loads dropped or rewritten executable
- vcredist_x86.exe (PID: 3828)
- SetupZiptrc.exe (PID: 912)
- regsvr32.exe (PID: 660)
- regsvr32.exe (PID: 2192)
Changes the autorun value in the registry
- vcredist_x86.exe (PID: 3192)
Application was dropped or rewritten from another process
- vcredist_x86.exe (PID: 3192)
- vcredist_x86.exe (PID: 3828)
Registers / Runs the DLL via REGSVR32.EXE
- SetupZiptrc.exe (PID: 912)
SUSPICIOUS
Reads the computer name
- SetupZiptrc.exe (PID: 912)
- vcredist_x86.exe (PID: 3828)
- vcredist_x86.exe (PID: 3192)
Executable content was dropped or overwritten
- SetupZiptrc.exe (PID: 912)
- vcredist_x86.exe (PID: 3828)
- vcredist_x86.exe (PID: 3192)
- msiexec.exe (PID: 272)
Drops a file with too old compile date
- SetupZiptrc.exe (PID: 912)
Checks supported languages
- SetupZiptrc.exe (PID: 912)
- vcredist_x86.exe (PID: 3192)
- vcredist_x86.exe (PID: 3828)
- cmd.exe (PID: 904)
Creates files in the program directory
- SetupZiptrc.exe (PID: 912)
- vcredist_x86.exe (PID: 3192)
Drops a file that was compiled in debug mode
- SetupZiptrc.exe (PID: 912)
- vcredist_x86.exe (PID: 3828)
- vcredist_x86.exe (PID: 3192)
- msiexec.exe (PID: 272)
Creates a directory in Program Files
- SetupZiptrc.exe (PID: 912)
Reads Environment values
- SetupZiptrc.exe (PID: 912)
- vssvc.exe (PID: 1472)
Application launched itself
- vcredist_x86.exe (PID: 3192)
Searches for installed software
- vcredist_x86.exe (PID: 3828)
- vcredist_x86.exe (PID: 3192)
- msiexec.exe (PID: 272)
Creates files in the Windows directory
- vcredist_x86.exe (PID: 3192)
- msiexec.exe (PID: 272)
Executed as Windows Service
- vssvc.exe (PID: 1472)
- msiexec.exe (PID: 272)
Creates a software uninstall entry
- vcredist_x86.exe (PID: 3192)
- msiexec.exe (PID: 272)
- SetupZiptrc.exe (PID: 912)
Reads Windows owner or organization settings
- msiexec.exe (PID: 272)
Reads the Windows organization settings
- msiexec.exe (PID: 272)
Removes files from Windows directory
- msiexec.exe (PID: 272)
Starts CMD.EXE for commands execution
- SetupZiptrc.exe (PID: 912)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3556)
INFO
Checks supported languages
- vssvc.exe (PID: 1472)
- msiexec.exe (PID: 272)
- regsvr32.exe (PID: 2192)
- regsvr32.exe (PID: 660)
- chrome.exe (PID: 3556)
- chrome.exe (PID: 1420)
- chrome.exe (PID: 3244)
- chrome.exe (PID: 1848)
- chrome.exe (PID: 3296)
- chrome.exe (PID: 2100)
- chrome.exe (PID: 2436)
- chrome.exe (PID: 3912)
- chrome.exe (PID: 2860)
- chrome.exe (PID: 2144)
- chrome.exe (PID: 2004)
- chrome.exe (PID: 3760)
- chrome.exe (PID: 3148)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 2280)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 824)
Reads the computer name
- vssvc.exe (PID: 1472)
- msiexec.exe (PID: 272)
- regsvr32.exe (PID: 660)
- regsvr32.exe (PID: 2192)
- chrome.exe (PID: 3556)
- chrome.exe (PID: 1848)
- chrome.exe (PID: 2100)
- chrome.exe (PID: 3912)
- chrome.exe (PID: 2200)
Checks Windows Trust Settings
- msiexec.exe (PID: 272)
- vcredist_x86.exe (PID: 3192)
Reads settings of System Certificates
- vcredist_x86.exe (PID: 3192)
- msiexec.exe (PID: 272)
- chrome.exe (PID: 2100)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 272)
- chrome.exe (PID: 3556)
Manual execution by user
- chrome.exe (PID: 3556)
Application launched itself
- chrome.exe (PID: 3556)
Reads the hosts file
- chrome.exe (PID: 3556)
- chrome.exe (PID: 2100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x31a3 |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 162816 |
| CodeSize: | 25088 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2016:12:11 22:50:52+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2016 21:50:52 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2016 21:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006071 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43434 |
.rdata | 0x00008000 | 0x00001352 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.2373 |
.data | 0x0000A000 | 0x000254F8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03725 |
.ndata | 0x00030000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00038000 | 0x0003A040 | 0x0003A200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.68685 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28747 | 841 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.57677 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 5.87105 | 38056 | UNKNOWN | English - United States | RT_ICON |
4 | 5.91745 | 21640 | UNKNOWN | English - United States | RT_ICON |
5 | 5.85274 | 16936 | UNKNOWN | English - United States | RT_ICON |
6 | 6.10624 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 6.22365 | 4264 | UNKNOWN | English - United States | RT_ICON |
8 | 6.44439 | 2440 | UNKNOWN | English - United States | RT_ICON |
9 | 6.34991 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 3.05309 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
68
Monitored processes
26
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 660 | "C:\Windows\system32\regsvr32.exe" /s SetupLog4x.ocx | C:\Windows\system32\regsvr32.exe | — | SetupZiptrc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 688 | "C:\Users\admin\Desktop\SetupZiptrc.exe" | C:\Users\admin\Desktop\SetupZiptrc.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1008,15062848072102944877,10489682471127247449,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1984 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 904 | C:\Windows\system32\cmd.exe /c ""C:\Program Files\Carreker\ZipTrc\mktemp.cmd" " | C:\Windows\system32\cmd.exe | — | SetupZiptrc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 912 | "C:\Users\admin\Desktop\SetupZiptrc.exe" | C:\Users\admin\Desktop\SetupZiptrc.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1008,15062848072102944877,10489682471127247449,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2900 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1472 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,15062848072102944877,10489682471127247449,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1056 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,15062848072102944877,10489682471127247449,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3404 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
25 731
Read events
24 548
Write events
948
Delete events
235
Modification events
| (PID) Process: | (912) SetupZiptrc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager\Environment |
| Operation: | write | Name: | CAPTUREAPI_LOG4PROP |
Value: C:\Program Files\Carreker\ZipTrc\log4cplus.properties | |||
| (PID) Process: | (3192) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000E9E800F2C7A0D701780C0000700A0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3192) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000E9E800F2C7A0D701780C0000700A0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3192) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 68 | |||
| (PID) Process: | (3192) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000001B0D46F2C7A0D701780C0000700A0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3192) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000756F48F2C7A0D701780C0000D00A0000E80300000100000000000000000000001FF00DA863252E43BEBAF3AF205C3D1A0000000000000000 | |||
| (PID) Process: | (1472) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000029344DF2C7A0D701C0050000FC070000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1472) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000029344DF2C7A0D701C00500009C0B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1472) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000029344DF2C7A0D701C0050000E00D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1472) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000029344DF2C7A0D701C00500004C060000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
103
Suspicious files
77
Text files
178
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 912 | SetupZiptrc.exe | C:\Program Files\Carreker\ZipTrc\zip.exe | executable | |
MD5:— | SHA256:— | |||
| 912 | SetupZiptrc.exe | C:\Program Files\Carreker\ZipTrc\BugslayerUtil.dll | executable | |
MD5:— | SHA256:— | |||
| 912 | SetupZiptrc.exe | C:\Program Files\Carreker\ZipTrc\dumpel.exe | executable | |
MD5:— | SHA256:— | |||
| 912 | SetupZiptrc.exe | C:\Program Files\Carreker\ZipTrc\msvcr71.dll | executable | |
MD5:— | SHA256:— | |||
| 912 | SetupZiptrc.exe | C:\Program Files\Carreker\ZipTrc\msvcp71.dll | executable | |
MD5:— | SHA256:— | |||
| 912 | SetupZiptrc.exe | C:\Program Files\Carreker\ZipTrc\rangerlogdump.exe | executable | |
MD5:— | SHA256:— | |||
| 912 | SetupZiptrc.exe | C:\Program Files\Carreker\ZipTrc\DOZE.EXE | executable | |
MD5:— | SHA256:— | |||
| 912 | SetupZiptrc.exe | C:\Program Files\Carreker\ZipTrc\sem.dll | executable | |
MD5:— | SHA256:— | |||
| 912 | SetupZiptrc.exe | C:\Program Files\Carreker\ZipTrc\Log4X.ocx | executable | |
MD5:— | SHA256:— | |||
| 912 | SetupZiptrc.exe | C:\Program Files\Carreker\ZipTrc\SetupLog4x.ocx | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
25
DNS requests
19
Threats
0
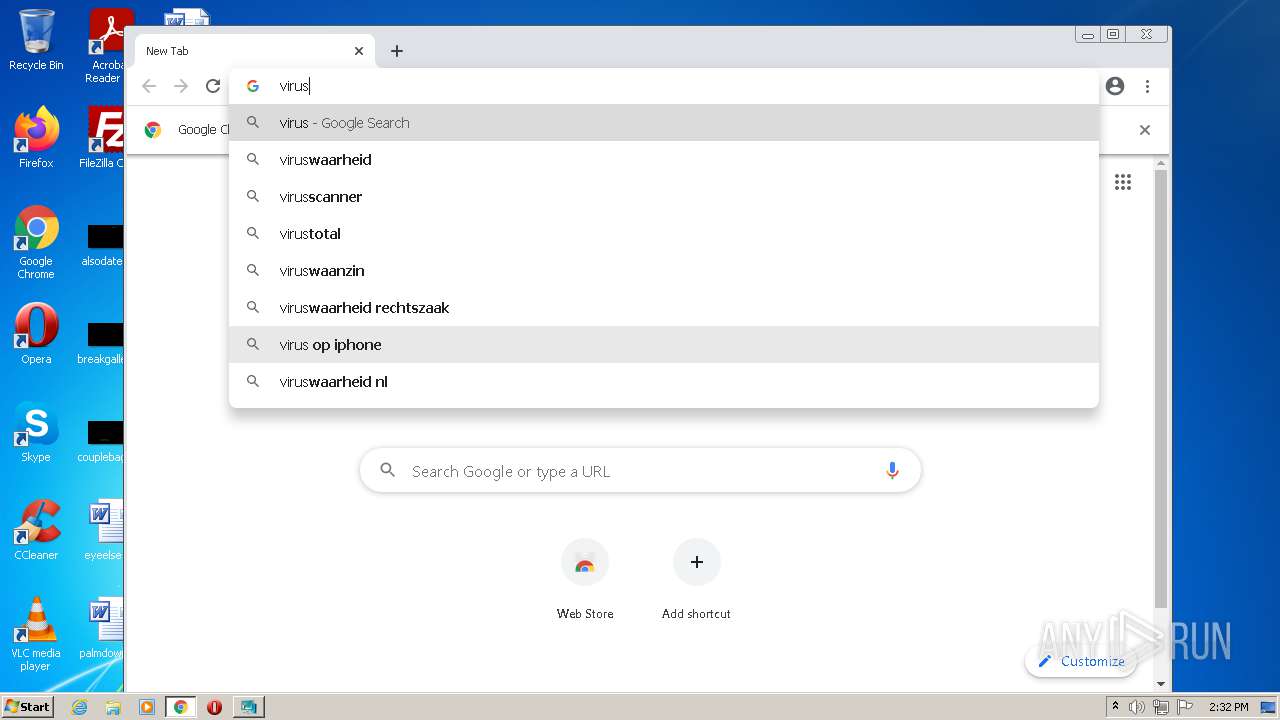
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
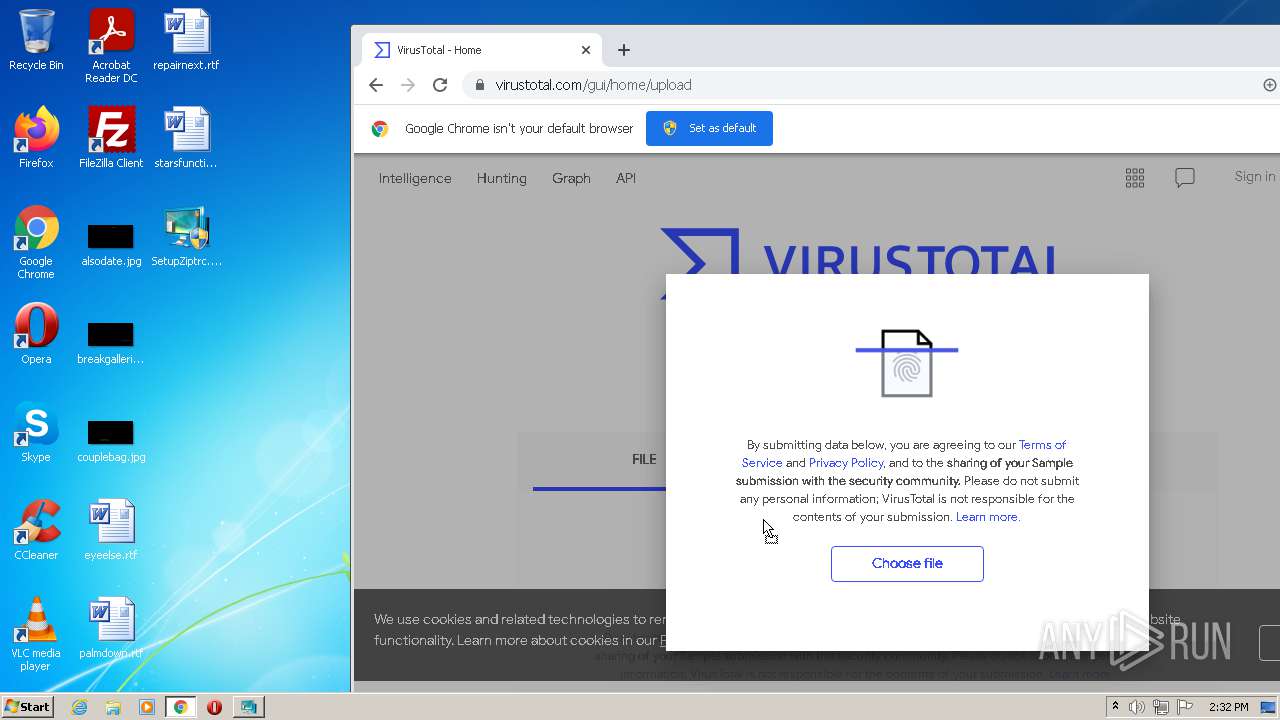
2100 | chrome.exe | GET | 302 | 216.239.38.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
3192 | vcredist_x86.exe | GET | 200 | 2.21.143.74:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | der | 1.05 Kb | whitelisted |
3192 | vcredist_x86.exe | GET | 200 | 92.123.194.162:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 767 b | whitelisted |
2100 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
3192 | vcredist_x86.exe | GET | 200 | 92.123.194.162:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 519 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3192 | vcredist_x86.exe | 2.16.186.81:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3192 | vcredist_x86.exe | 2.21.143.74:80 | www.microsoft.com | Telia Company AB | — | malicious |
2100 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1672 | svchost.exe | 8.253.204.249:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
2100 | chrome.exe | 142.250.184.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
2100 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
2100 | chrome.exe | 142.250.186.100:443 | www.google.com | Google Inc. | US | whitelisted |
2100 | chrome.exe | 216.58.212.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2100 | chrome.exe | 172.217.23.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2100 | chrome.exe | 142.250.184.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |