| URL: | https://eur01.safelinks.protection.outlook.com/?url=http%3A%2F%2Fwww.mediafire.com%2Ffile%2Fkj5t80vc5n90h9z%2FEngineering%25252C_CellFE%25252C_Inc..pdf%2Ffile&data=02%7C01%7C%7Ce892bcf6f31a49e7172c08d7d4f2bdd8%7C28042244bb514cd680347776fa3703e8%7C1%7C0%7C637212011341339412&sdata=Q4yr%2BYfwPi7jCTVF9%2F7NQ70bDDU9EEfQJn9umNWd4b4%3D&reserved=0 |
| Full analysis: | https://app.any.run/tasks/c3df4bfa-3f13-4685-900a-e39608c04d1f |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 21:56:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6A2DDF11F209E190060D68AF015F5ADE |
| SHA1: | 8B3406F148BF759B6B63FE5FD569A3A6C7C45F78 |
| SHA256: | E097002CBFDE2F383C9F902B0469AC6D4AB6AE56C78E6DB1864D5566701B4D14 |
| SSDEEP: | 6:2U9V9iRXPNHszh3eG/fsA9OYcR713D4TM3kDXKXQILgWES/yU0skD7bwsM:2U9qVsF3eefs4O73Ez4LZjyLskDfRM |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 628)
INFO
Reads the hosts file
- chrome.exe (PID: 2380)
- chrome.exe (PID: 628)
Reads Internet Cache Settings
- chrome.exe (PID: 628)
Application launched itself
- chrome.exe (PID: 628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
95
Monitored processes
60
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,12789185659100227985,15980958293931010377,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2607800566029092376 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://eur01.safelinks.protection.outlook.com/?url=http%3A%2F%2Fwww.mediafire.com%2Ffile%2Fkj5t80vc5n90h9z%2FEngineering%25252C_CellFE%25252C_Inc..pdf%2Ffile&data=02%7C01%7C%7Ce892bcf6f31a49e7172c08d7d4f2bdd8%7C28042244bb514cd680347776fa3703e8%7C1%7C0%7C637212011341339412&sdata=Q4yr%2BYfwPi7jCTVF9%2F7NQ70bDDU9EEfQJn9umNWd4b4%3D&reserved=0" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,12789185659100227985,15980958293931010377,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9371214312261246645 --renderer-client-id=56 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4608 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,12789185659100227985,15980958293931010377,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9838259024328668165 --renderer-client-id=50 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,12789185659100227985,15980958293931010377,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10153779059228876158 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2864 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,12789185659100227985,15980958293931010377,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9792217494192569880 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,12789185659100227985,15980958293931010377,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4810450613014877612 --renderer-client-id=54 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,12789185659100227985,15980958293931010377,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4482955423593635208 --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5640 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,12789185659100227985,15980958293931010377,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12372185153757260586 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3684 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,12789185659100227985,15980958293931010377,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17640241332792835434 --mojo-platform-channel-handle=4400 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 019
Read events
893
Write events
121
Delete events
5
Modification events
| (PID) Process: | (1920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 628-13230079007647875 |
Value: 259 | |||
| (PID) Process: | (628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (628) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
82
Text files
281
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E826B20-274.pma | — | |
MD5:— | SHA256:— | |||
| 628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b8cc2607-b422-4b02-ae08-c286cb2034f7.tmp | — | |
MD5:— | SHA256:— | |||
| 628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa67ce9.TMP | text | |
MD5:— | SHA256:— | |||
| 628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa67d08.TMP | text | |
MD5:— | SHA256:— | |||
| 628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa67f89.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
186
DNS requests
119
Threats
71
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
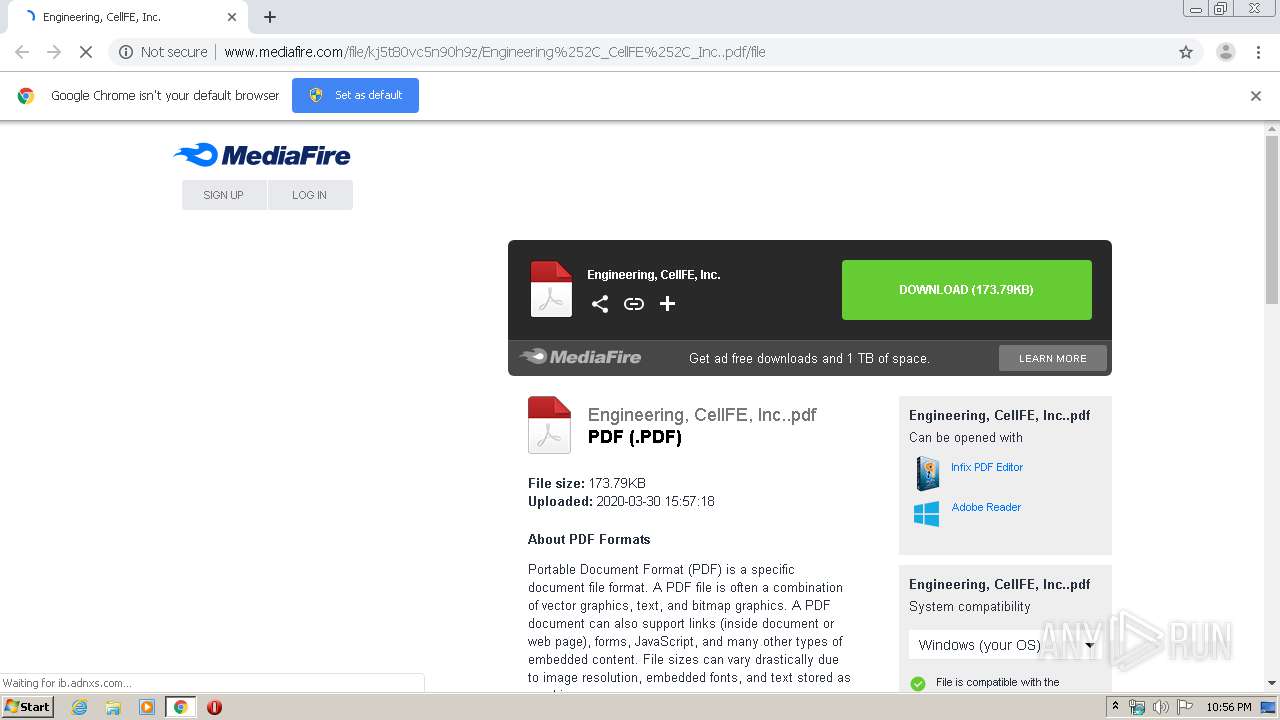
2380 | chrome.exe | GET | 200 | 104.17.166.186:80 | http://6.adsco.re/ | US | — | — | whitelisted |
2380 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/file/kj5t80vc5n90h9z/Engineering%252C_CellFE%252C_Inc..pdf/file | US | html | 82.2 Kb | shared |
2380 | chrome.exe | GET | 200 | 172.217.16.174:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | text | 798 b | whitelisted |
2380 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/js/prebid2.44.1.js | US | text | 52.9 Kb | shared |
2380 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/download/apps_list_sprite-v4.png | US | image | 6.78 Kb | shared |
2380 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/images/icons/svg_light/icons_sprite.svg | US | image | 8.47 Kb | shared |
2380 | chrome.exe | POST | 200 | 185.33.223.83:80 | http://ib.adnxs.com/ut/v3/prebid | unknown | text | 247 b | whitelisted |
2380 | chrome.exe | GET | 200 | 104.17.166.186:80 | http://c.adsco.re/ | US | html | 11.2 Kb | whitelisted |
2380 | chrome.exe | POST | 200 | 162.252.214.5:80 | http://adsco.re/p | US | text | 132 b | whitelisted |
2380 | chrome.exe | GET | 307 | 185.33.223.83:80 | http://ib.adnxs.com/async_usersync?cbfn=AN_async_load | unknown | compressed | 247 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2380 | chrome.exe | 34.95.120.147:443 | mediafire-d.openx.net | — | US | unknown |
2380 | chrome.exe | 216.58.206.10:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
2380 | chrome.exe | 185.33.223.83:80 | ib.adnxs.com | AppNexus, Inc | — | unknown |
2380 | chrome.exe | 23.66.18.151:443 | www.aaxdetect.com | Akamai Technologies, Inc. | NL | unknown |
2380 | chrome.exe | 172.217.22.65:443 | tpc.googlesyndication.com | Google Inc. | US | whitelisted |
2380 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2380 | chrome.exe | 104.47.2.28:443 | eur01.safelinks.protection.outlook.com | Microsoft Corporation | IE | whitelisted |
2380 | chrome.exe | 216.58.210.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2380 | chrome.exe | 104.16.202.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
2380 | chrome.exe | 216.58.210.2:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
eur01.safelinks.protection.outlook.com |
| whitelisted |
accounts.google.com |
| shared |
www.mediafire.com |
| shared |
www.googletagmanager.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
c.aaxads.com |
| whitelisted |
translate.google.com |
| whitelisted |
static.mediafire.com |
| shared |
download1376.mediafire.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2380 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2380 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2380 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |