| File name: | Rolex_file.exe |
| Full analysis: | https://app.any.run/tasks/f61dcb5a-8b75-4c52-845e-b98f75c3f06f |
| Verdict: | Malicious activity |
| Analysis date: | January 20, 2026, 18:16:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | F313ADA70224987AEE015C52AB0308E1 |
| SHA1: | 912FAF38C4ABACAB99B7C217A3F608EE6385E161 |
| SHA256: | E091DD27AAC2F45C59FBB43177EFDECA98B6CC7F59194A6FE8D51286FF09A171 |
| SSDEEP: | 49152:tQ0nkT5Sv53vFeikd/Bq46TnUxldBjbtmw09Nj76m2C:t8TIBNeikXN6cdKVTd |
MALICIOUS
Executing a file with an untrusted certificate
- Rolex_file.exe (PID: 9028)
- Rolex_file.exe (PID: 7192)
SUSPICIOUS
Application launched itself
- Rolex_file.exe (PID: 9028)
Reads the date of Windows installation
- Rolex_file.exe (PID: 9028)
INFO
Checks supported languages
- Rolex_file.exe (PID: 9028)
- Rolex_file.exe (PID: 7192)
Create files in a temporary directory
- Rolex_file.exe (PID: 9028)
Reads security settings of Internet Explorer
- Rolex_file.exe (PID: 9028)
Process checks computer location settings
- Rolex_file.exe (PID: 9028)
Reads the computer name
- Rolex_file.exe (PID: 9028)
Reads Microsoft Office registry keys
- Rolex_file.exe (PID: 9028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Clipper DOS Executable (33.5) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (33.2) |
| .exe | | | DOS Executable Generic (33.2) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2023:06:28 16:28:27+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 95744 |
| InitializedDataSize: | 933888 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x114f0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 12.1.0.18912 |
| ProductVersionNumber: | 12.1.0.18912 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Zhuhai Kingsoft Office Software Co.,Ltd |
| FileDescription: | WPS Office |
| FileVersion: | 12,1,0,18912 |
| InternalName: | ksolaunch |
| LegalCopyright: | Copyright©2024 Kingsoft Corporation. All rights reserved. |
| OriginalFileName: | ksolaunch.exe |
| ProductName: | WPS Office |
| ProductVersion: | 12,1,0,18912 |
| MIMEType: | - |
Total processes
152
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2392 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" "C:\Users\admin\AppData\Local\Temp\Rolex_file.xlsx" | C:\Program Files\Microsoft Office\root\Office16\EXCEL.EXE | Rolex_file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 7192 | Rolex_file.exe | C:\Users\admin\AppData\Local\Temp\Rolex_file.exe | — | Rolex_file.exe | |||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Exit code: 0 Version: 12,1,0,18912 Modules
| |||||||||||||||
| 9028 | "C:\Users\admin\AppData\Local\Temp\Rolex_file.exe" | C:\Users\admin\AppData\Local\Temp\Rolex_file.exe | — | explorer.exe | |||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Exit code: 3221225477 Version: 12,1,0,18912 Modules
| |||||||||||||||
Total events
6 945
Read events
6 709
Write events
216
Delete events
20
Modification events
| (PID) Process: | (9028) Rolex_file.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.xlsx\OpenWithProgids |
| Operation: | write | Name: | Excel.Sheet.12 |
Value: | |||
| (PID) Process: | (9028) Rolex_file.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {33154C99-BF49-443D-A73C-303A23ABBE97} {886D8EEB-8CF2-4446-8D02-CDBA1DBDCF99} 0xFFFF |
Value: 0100000000000000D41FC7F5388ADC01 | |||
| (PID) Process: | (2392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 1 |
Value: 01D014000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (2392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\EXCEL\2392 |
| Operation: | write | Name: | 0 |
Value: 0B0E109812B7AA3002F644A2591925E67451CE230046EE9AC4C78FC7A2EE016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511D812D2120965007800630065006C002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (2392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (2392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (2392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (2392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (2392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (2392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
Executable files
0
Suspicious files
12
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2392 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\BF1FFK9MOXBPZQ3KD8K5.temp | binary | |
MD5:4FCB2A3EE025E4A10D21E1B154873FE2 | SHA256:90BF6BAA6F968A285F88620FBF91E1F5AA3E66E2BAD50FD16F37913280AD8228 | |||
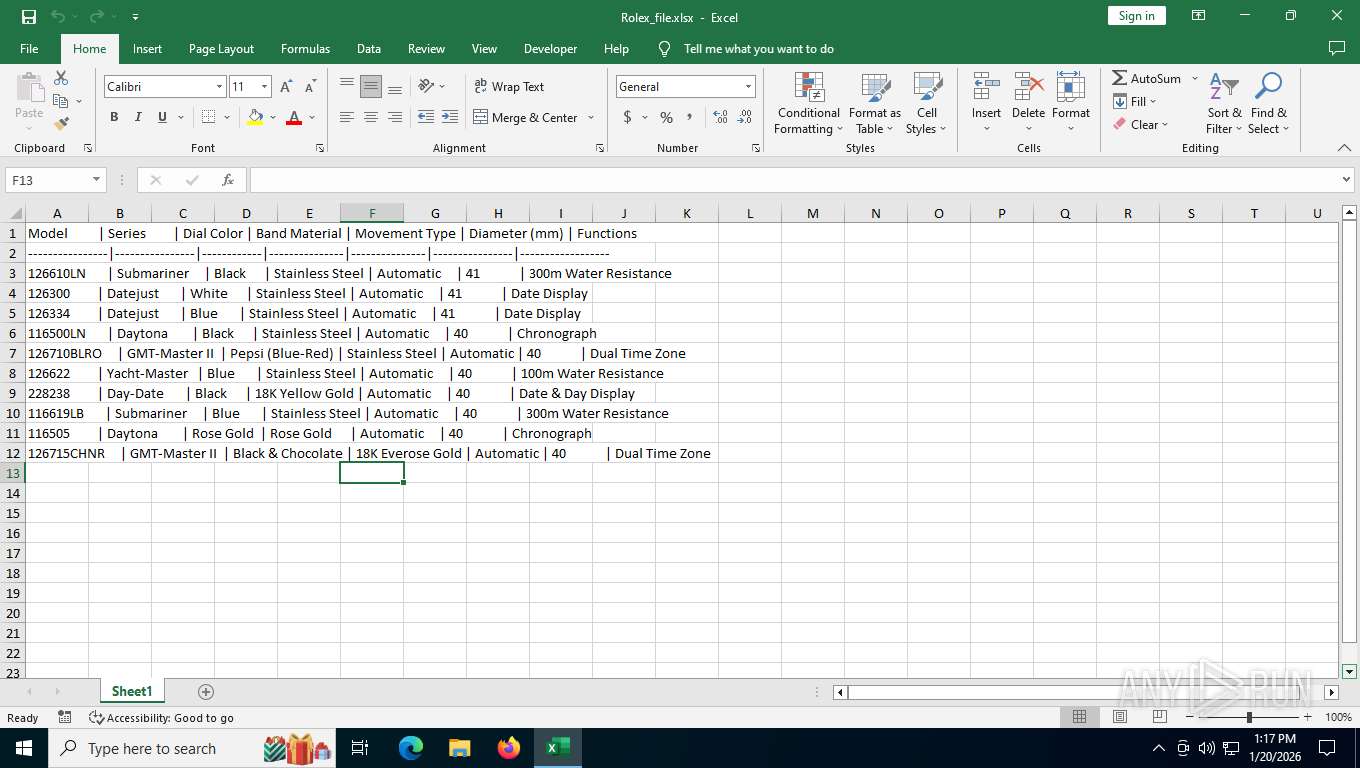
| 9028 | Rolex_file.exe | C:\Users\admin\AppData\Local\Temp\Rolex_file.xlsx | binary | |
MD5:6897FC52BEB35BC86AA5BBEBBBF9BEA1 | SHA256:CEC19B6766E15B21B3E9029168DE032B10FA89B2F0E3C0A9C2346D73DF35702F | |||
| 2392 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\b8ab77100df80ab2.customDestinations-ms | binary | |
MD5:4FCB2A3EE025E4A10D21E1B154873FE2 | SHA256:90BF6BAA6F968A285F88620FBF91E1F5AA3E66E2BAD50FD16F37913280AD8228 | |||
| 2392 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:3E1FE6EA1DA84C97E30AA9E756CE8744 | SHA256:B29D2166AE71AF42A8583F57499C081D4213D2E016FED2582F3B547B71041AEC | |||
| 2392 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Governance\Anonymous\floodgatecampaigns.json.tmp | text | |
MD5:E03336CE0C06FE6D7B10629AEA48EBA7 | SHA256:FB5F336659498A07AD7D9D4C331A5688DC1969EEF276AD12B6245B79F0A6E8AB | |||
| 2392 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Wef\CustomFunctions\v1.7\hostproperties.json | text | |
MD5:7A29F1E157244591277E3C25F29A8029 | SHA256:05EEBA4D6CA7148DCD0A6317A45241A49A4C8D88D628B27D8B19889EF6E70771 | |||
| 2392 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:C33EEE0B194491697B343E6B5E4B5F88 | SHA256:B94E8C7B6FC185751C7CAA22357B7AF8C3D99C37CB51CABB50055EAE836F88CC | |||
| 2392 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\excel.exe_Rules.xml | xml | |
MD5:FEC95A25C0A5F22A7E6718F6A496DCB8 | SHA256:B0C3BD18424C6C7E8CAEADB1DE3DF2D6F99C19D931ECE2EECD172C0985113428 | |||
| 2392 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\FontCache\4\Catalog\ListAll.Json | text | |
MD5:7C5578BC58BDE6DC855D5C929CF54232 | SHA256:A48ACBE81F33E5918B096A6B89687E505DA0E79196F74DC48B6E068708378A3F | |||
| 2392 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:88E3067115663B24AE18AC8697022F14 | SHA256:C36A3D09F90ACC03806EE3396BE3F7D9D495817DFBE74D34D95FC82529AE674F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
26
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/WaaS/FeatureManagement?IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&CurrentBranch=vb_release&AccountFirstChar=&ActivationChannel=Retail&OEMModel=DELL&FlightRing=Retail&AttrDataVer=186&InstallLanguage=en-US&OSUILocale=en-US&WebExperience=1&FlightingBranchName=&ChassisTypeId=1&OSSkuId=48&App=CDM&InstallDate=1661339444&AppVer=&OSArchitecture=AMD64&DefaultUserRegion=244&TelemetryLevel=1&OSVersion=10.0.19045.4046&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
1352 | SIHClient.exe | GET | 200 | 52.165.164.15:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
1352 | SIHClient.exe | GET | 200 | 135.232.92.137:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
2392 | EXCEL.EXE | GET | 200 | 52.109.76.240:443 | https://officeclient.microsoft.com/config16/?lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3 | unknown | xml | 128 Kb | whitelisted |
5044 | svchost.exe | POST | 200 | 20.190.159.75:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
5044 | svchost.exe | POST | 200 | 20.190.159.75:443 | https://login.live.com/RST2.srf | unknown | xml | 5.45 Kb | whitelisted |
2392 | EXCEL.EXE | POST | — | 20.50.201.203:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | — | — | whitelisted |
2392 | EXCEL.EXE | POST | 200 | 20.50.201.203:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | text | 10 b | whitelisted |
2392 | EXCEL.EXE | GET | 200 | 52.123.129.14:443 | https://ecs.office.com/config/v2/Office/excel/16.0.16026.20146/Production/CC?&Clientid=%7bD61AB268-C26A-439D-BB15-2A0DEDFCA6A3%7d&Application=excel&Platform=win32&Version=16.0.16026.20146&MsoVersion=16.0.16026.20002&SDX=fa000000002.2.0.1907.31003&SDX=fa000000005.1.0.1909.30011&SDX=fa000000006.1.0.1909.13002&SDX=fa000000008.1.0.1908.16006&SDX=fa000000009.1.0.1908.6002&SDX=fa000000016.1.0.1810.13001&SDX=fa000000029.1.0.1906.25001&SDX=fa000000033.1.0.1908.24001&SDX=wa104381125.1.0.1810.9001&ProcessName=excel.exe&Audience=Production&Build=ship&Architecture=x64&Language=en-US&SubscriptionLicense=false&PerpetualLicense=2019&LicenseCategory=6&LicenseSKU=Professional2019Retail&OsVersion=10.0&OsBuild=19045&Channel=CC&InstallType=C2R&SessionId=%7bAAB71298-0230-44F6-A259-1925E67451CE%7d&LabMachine=false | unknown | text | 128 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6720 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7964 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2392 | EXCEL.EXE | 52.109.76.240:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5044 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2392 | EXCEL.EXE | 52.109.89.19:443 | roaming.svc.cloud.microsoft | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2392 | EXCEL.EXE | 52.123.129.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
roaming.svc.cloud.microsoft |
| whitelisted |
ecs.office.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |