| File name: | Rolex_file.exe |
| Full analysis: | https://app.any.run/tasks/9216cd10-ddae-49fb-a60f-64decd636522 |
| Verdict: | Malicious activity |
| Analysis date: | October 07, 2025, 12:01:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | F313ADA70224987AEE015C52AB0308E1 |
| SHA1: | 912FAF38C4ABACAB99B7C217A3F608EE6385E161 |
| SHA256: | E091DD27AAC2F45C59FBB43177EFDECA98B6CC7F59194A6FE8D51286FF09A171 |
| SSDEEP: | 49152:tQ0nkT5Sv53vFeikd/Bq46TnUxldBjbtmw09Nj76m2C:t8TIBNeikXN6cdKVTd |
MALICIOUS
Executing a file with an untrusted certificate
- Rolex_file.exe (PID: 2328)
- Rolex_file.exe (PID: 8116)
SUSPICIOUS
Application launched itself
- Rolex_file.exe (PID: 2328)
Reads security settings of Internet Explorer
- Rolex_file.exe (PID: 2328)
Reads the date of Windows installation
- Rolex_file.exe (PID: 2328)
INFO
Checks supported languages
- Rolex_file.exe (PID: 8116)
- Rolex_file.exe (PID: 2328)
Reads the computer name
- Rolex_file.exe (PID: 2328)
Process checks computer location settings
- Rolex_file.exe (PID: 2328)
Reads Microsoft Office registry keys
- Rolex_file.exe (PID: 2328)
Create files in a temporary directory
- Rolex_file.exe (PID: 2328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Clipper DOS Executable (33.5) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (33.2) |
| .exe | | | DOS Executable Generic (33.2) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2023:06:28 16:28:27+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 95744 |
| InitializedDataSize: | 933888 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x114f0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 12.1.0.18912 |
| ProductVersionNumber: | 12.1.0.18912 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Zhuhai Kingsoft Office Software Co.,Ltd |
| FileDescription: | WPS Office |
| FileVersion: | 12,1,0,18912 |
| InternalName: | ksolaunch |
| LegalCopyright: | Copyright©2024 Kingsoft Corporation. All rights reserved. |
| OriginalFileName: | ksolaunch.exe |
| ProductName: | WPS Office |
| ProductVersion: | 12,1,0,18912 |
| MIMEType: | - |
Total processes
175
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2328 | "C:\Users\admin\AppData\Local\Temp\Rolex_file.exe" | C:\Users\admin\AppData\Local\Temp\Rolex_file.exe | — | explorer.exe | |||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Exit code: 3221225477 Version: 12,1,0,18912 Modules
| |||||||||||||||
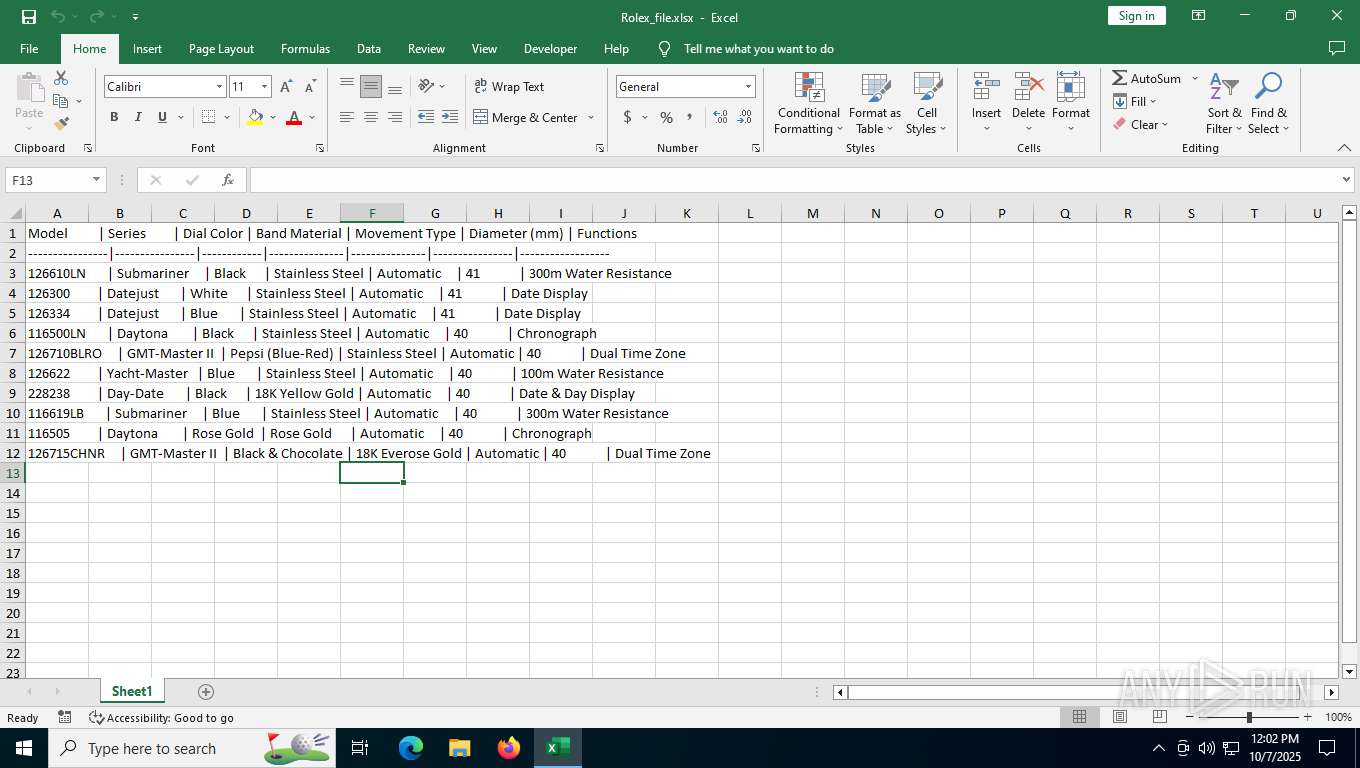
| 2756 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" "C:\Users\admin\AppData\Local\Temp\Rolex_file.xlsx" | C:\Program Files\Microsoft Office\root\Office16\EXCEL.EXE | Rolex_file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 8116 | Rolex_file.exe | C:\Users\admin\AppData\Local\Temp\Rolex_file.exe | — | Rolex_file.exe | |||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Exit code: 0 Version: 12,1,0,18912 Modules
| |||||||||||||||
| 8864 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 351
Read events
10 107
Write events
230
Delete events
14
Modification events
| (PID) Process: | (2328) Rolex_file.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.xlsx\OpenWithProgids |
| Operation: | write | Name: | Excel.Sheet.12 |
Value: | |||
| (PID) Process: | (2328) Rolex_file.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2328) Rolex_file.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2328) Rolex_file.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2328) Rolex_file.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2328) Rolex_file.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {33154C99-BF49-443D-A73C-303A23ABBE97} {886D8EEB-8CF2-4446-8D02-CDBA1DBDCF99} 0xFFFF |
Value: 010000000000000005B8A02D8237DC01 | |||
| (PID) Process: | (2328) Rolex_file.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\Office16\oregres.dll,-206 |
Value: Excel | |||
| (PID) Process: | (2756) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 1 |
Value: 01D014000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (2756) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\EXCEL\2756 |
| Operation: | write | Name: | 0 |
Value: 0B0E105AE448A3D273EA449F83CF8EFE6BEEE7230046B6A19C85A3F08DEE016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511C415D2120965007800630065006C002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (2756) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
Executable files
0
Suspicious files
10
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2756 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:B00961D90B6C89B0A161F620E2CF8983 | SHA256:7DF36122046C7A41C1A2E66C7284E0A5AB40926CF50A6B0A0F3A6F522D146201 | |||
| 2328 | Rolex_file.exe | C:\Users\admin\AppData\Local\Temp\Rolex_file.xlsx | document | |
MD5:6897FC52BEB35BC86AA5BBEBBBF9BEA1 | SHA256:CEC19B6766E15B21B3E9029168DE032B10FA89B2F0E3C0A9C2346D73DF35702F | |||
| 2756 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\C88F9511-F307-459B-9AD7-1E7A64910EFE | xml | |
MD5:D93CBAE03B06AB2A6914EA6DF026862A | SHA256:D554AA8087D6723AA1F899DBF4476DACA67759AB7B2965466D0D608247DCE520 | |||
| 2756 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\5475cb191e478c39370a215b2da98a37e9dc813d.tbres | binary | |
MD5:174FF7654F06BBE8B6CA2620F73E1A90 | SHA256:45953A1E04602EDCA64C3FED200D676844B5CBB036750D54355CCAFA10AF5361 | |||
| 2756 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Wef\CustomFunctions\v1.7\hostproperties.json | binary | |
MD5:7A29F1E157244591277E3C25F29A8029 | SHA256:05EEBA4D6CA7148DCD0A6317A45241A49A4C8D88D628B27D8B19889EF6E70771 | |||
| 2756 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\UsageMetricsStore\FileActivityStoreV3\Excel\ASkwMDAwMDAwMC0wMDAwLTAwMDAtMDAwMC0wMDAwMDAwMDAwMDBfTnVsbAA.S | binary | |
MD5:9822432696251882AB2F2F2FE35D7F02 | SHA256:FC0B55245AFD5502CCCA47956ECE0BB38EDC56C0C1903D7C9F43D951E4BBD345 | |||
| 2756 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\N97MW97D50X0GTCC442C.temp | binary | |
MD5:4FCB2A3EE025E4A10D21E1B154873FE2 | SHA256:90BF6BAA6F968A285F88620FBF91E1F5AA3E66E2BAD50FD16F37913280AD8228 | |||
| 2756 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:C7D4480A89E4284D133B39659E058692 | SHA256:DAEF871E533920F08FD060395CE1A8E1DC832BE9EB93B04AFE35515E274849E5 | |||
| 2756 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:FCFCDD1D94037FE9822C5A07A9A68DED | SHA256:E7638B06462B66BB114F627FD38911DA7DD76A7D54AD4BFC0DE0D0B9D71FA521 | |||
| 2756 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\b8ab77100df80ab2.customDestinations-ms | binary | |
MD5:4FCB2A3EE025E4A10D21E1B154873FE2 | SHA256:90BF6BAA6F968A285F88620FBF91E1F5AA3E66E2BAD50FD16F37913280AD8228 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
39
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6940 | svchost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6940 | svchost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2756 | EXCEL.EXE | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6972 | backgroundTaskHost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5480 | backgroundTaskHost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1560 | backgroundTaskHost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6080 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6016 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2756 | EXCEL.EXE | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
2756 | EXCEL.EXE | 52.123.129.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2756 | EXCEL.EXE | 52.111.243.12:443 | messaging.lifecycle.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5224 | SearchApp.exe | 184.86.251.28:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
6940 | svchost.exe | 40.126.31.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6940 | svchost.exe | 172.66.2.5:80 | ocsp.digicert.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |