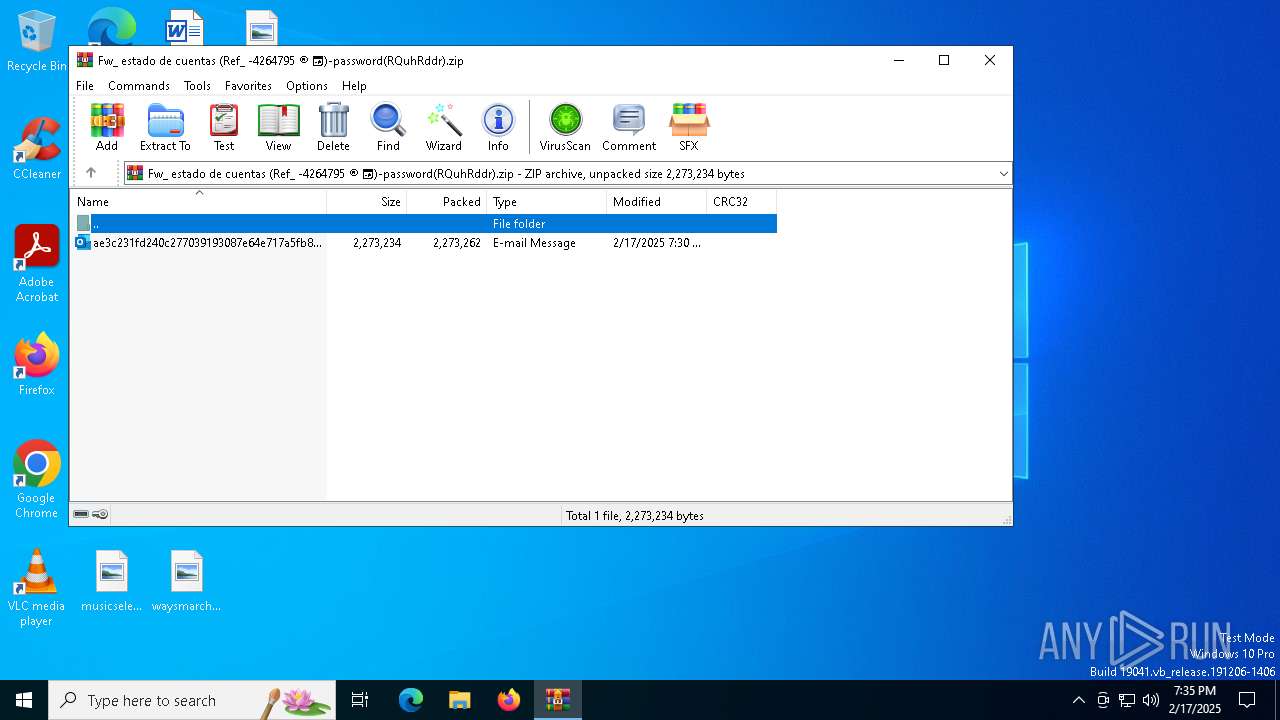
| File name: | Fw_ estado de cuentas (Ref_ -4264795 ® 📅)-password(RQuhRddr).zip |
| Full analysis: | https://app.any.run/tasks/e130a95a-0e29-4d9f-b7dd-f902480b0ff9 |
| Verdict: | Malicious activity |
| Analysis date: | February 17, 2025, 19:35:22 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
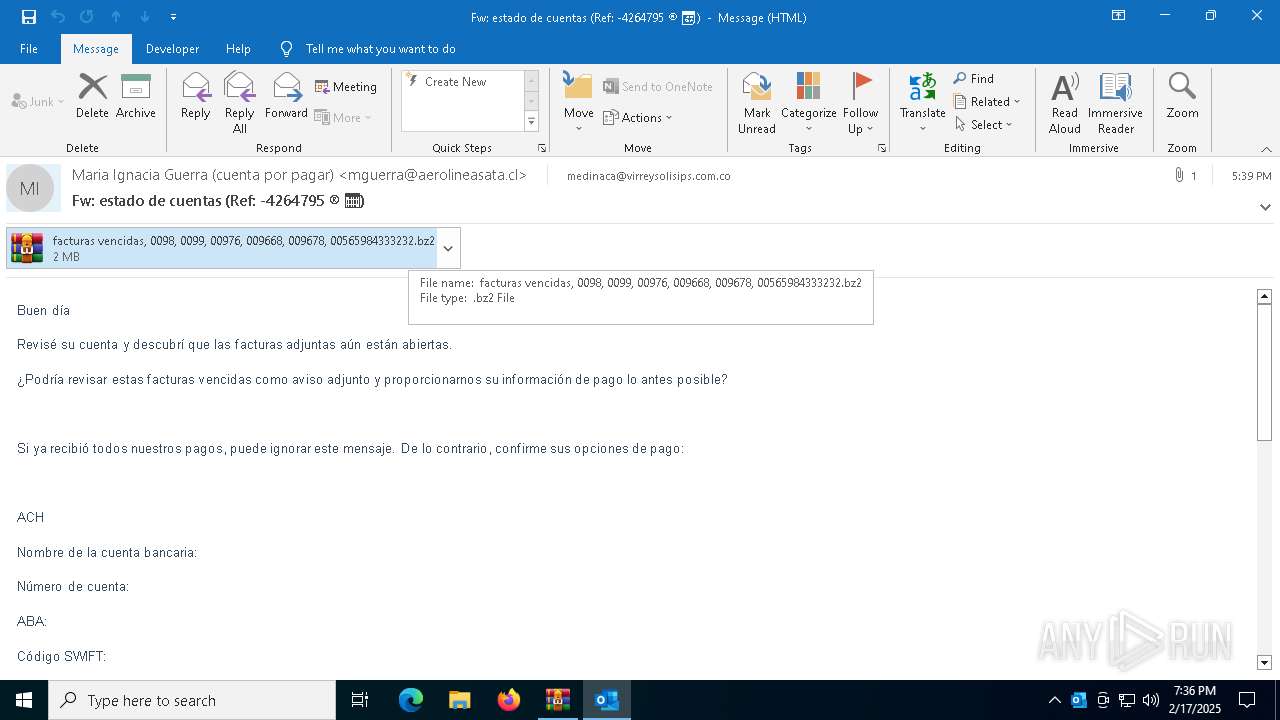
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 054DBB672BB8D2AD4B623D184D1B3C88 |
| SHA1: | F40A970B947586E5D8DB9C1436C071BB36E4BAA0 |
| SHA256: | E077FEC342FC701565440C194E5BAAD04694CD31DC128ACB86CF3B272CEC8E5C |
| SSDEEP: | 98304:rIM8ATOLc76U2j6AewRbM0n7p23opL8uspfOQOvoID8NBdHP999wz/CRcqtP7cU5:vkI |
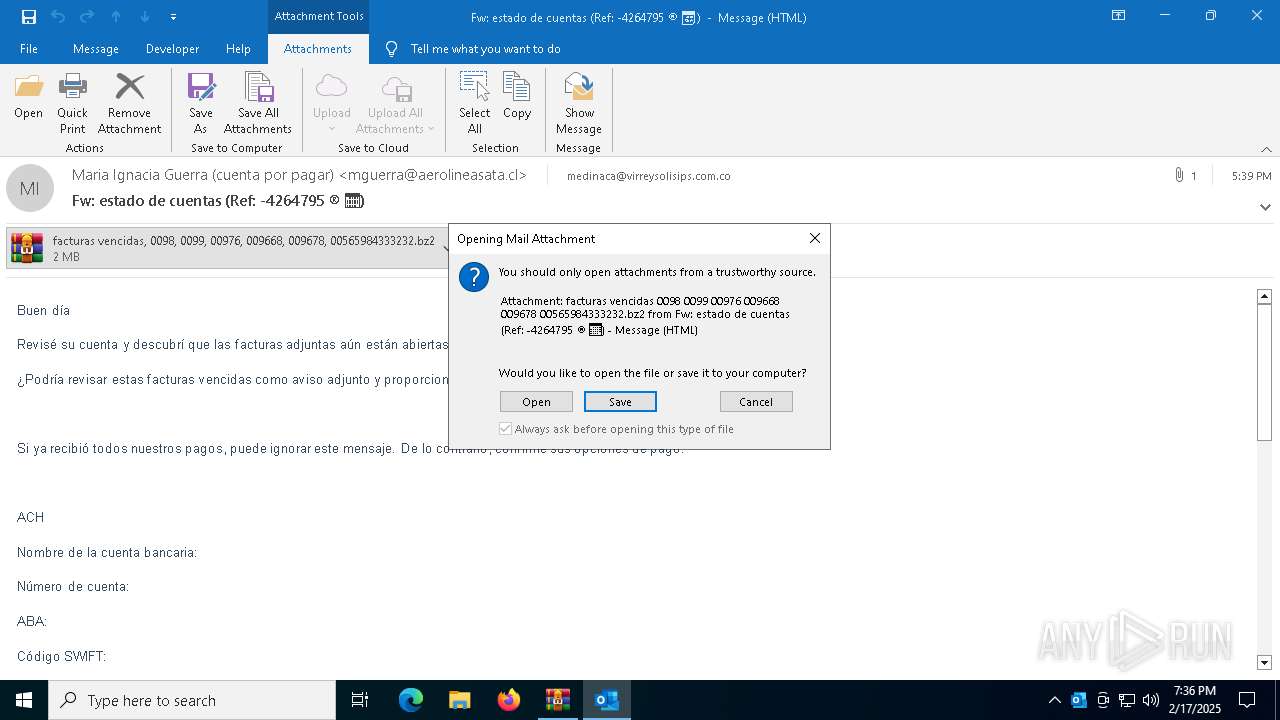
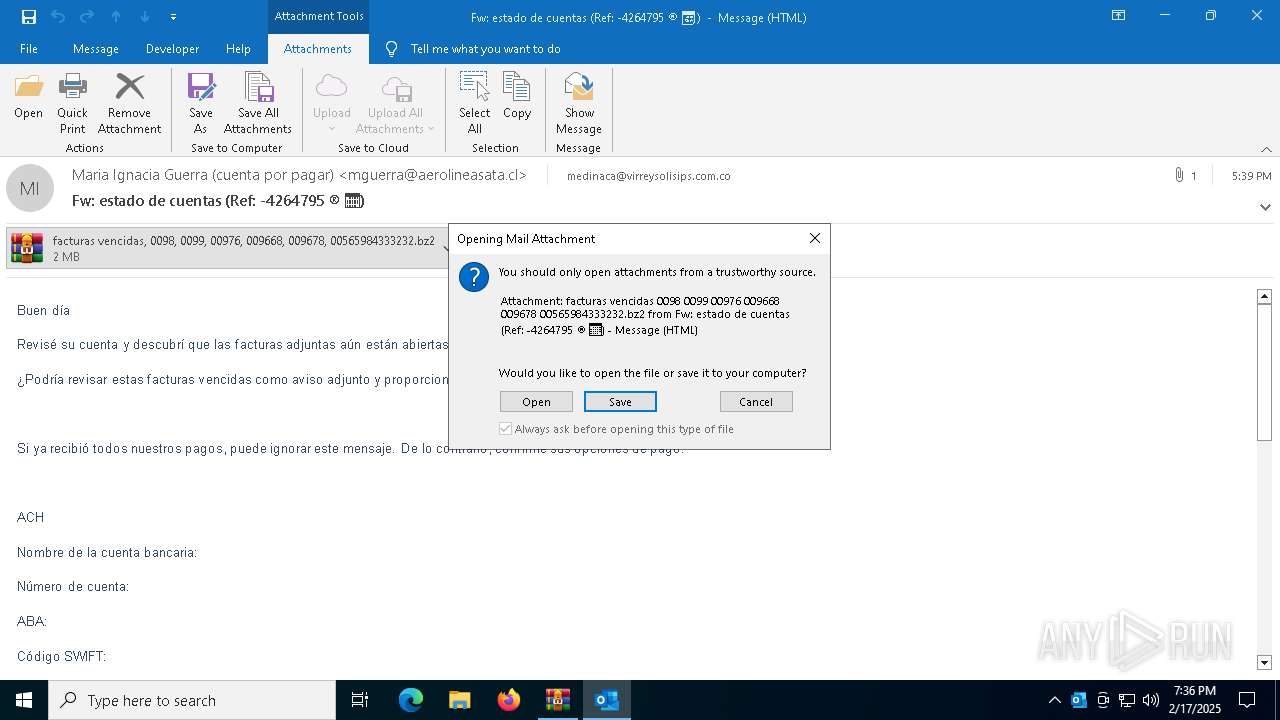
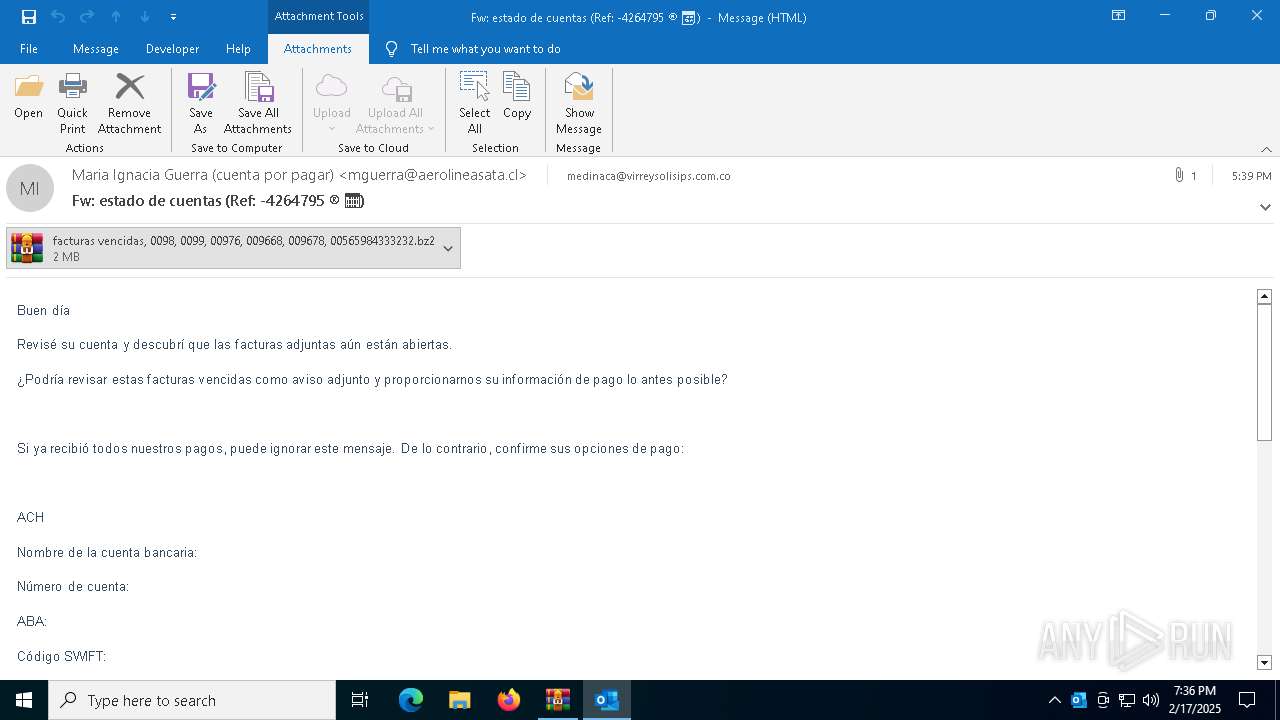
MALICIOUS
Executing a file with an untrusted certificate
- facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe (PID: 6900)
- facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe (PID: 6952)
- facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe (PID: 6724)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6412)
- WinRAR.exe (PID: 6296)
Reads Microsoft Outlook installation path
- WinRAR.exe (PID: 6412)
INFO
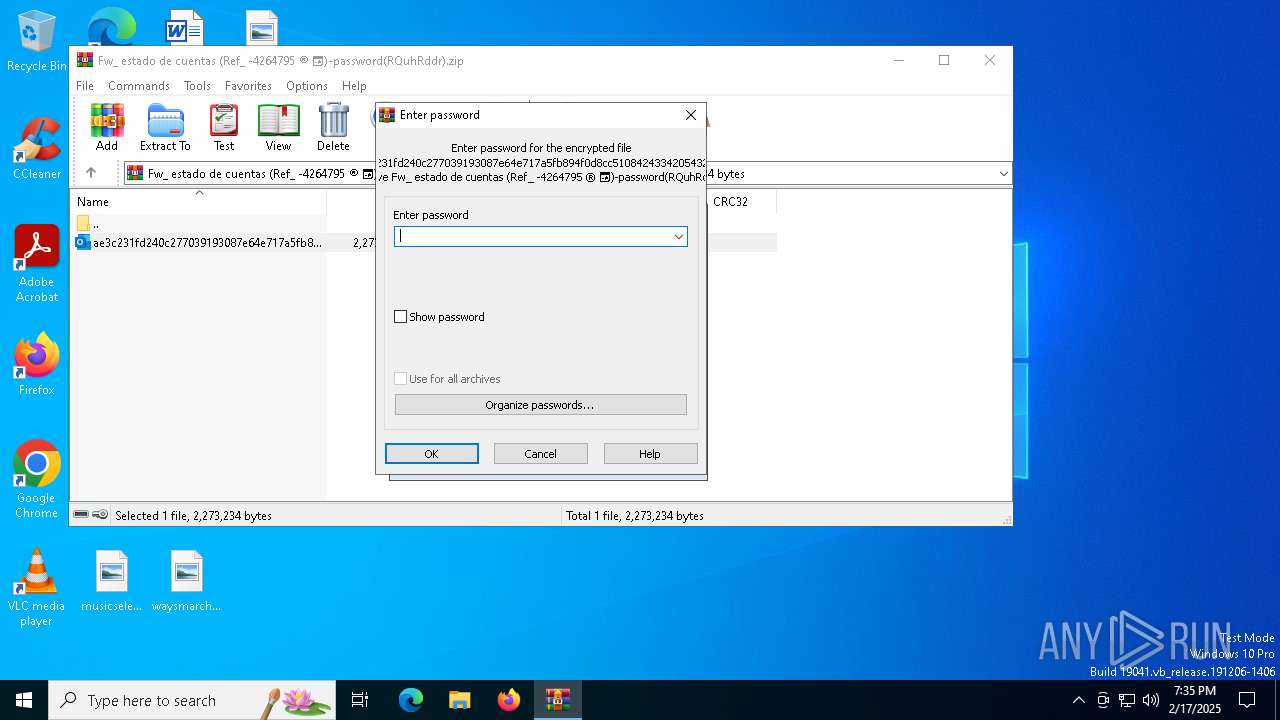
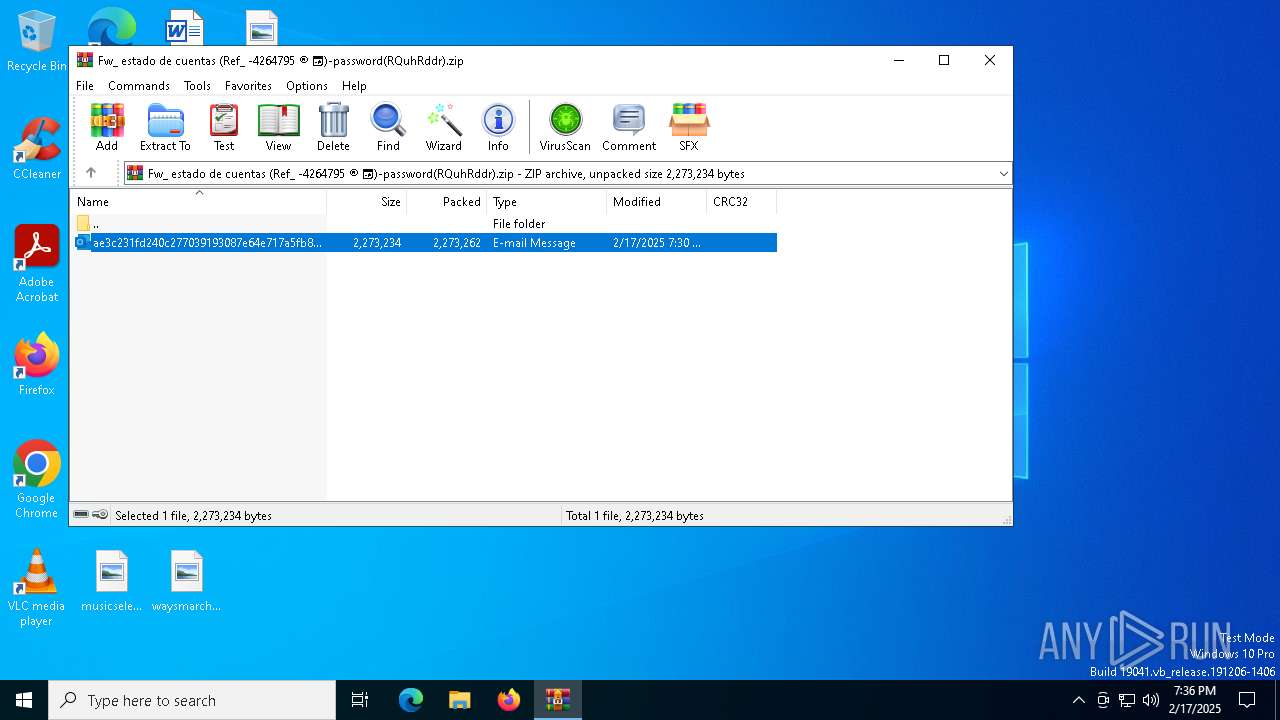
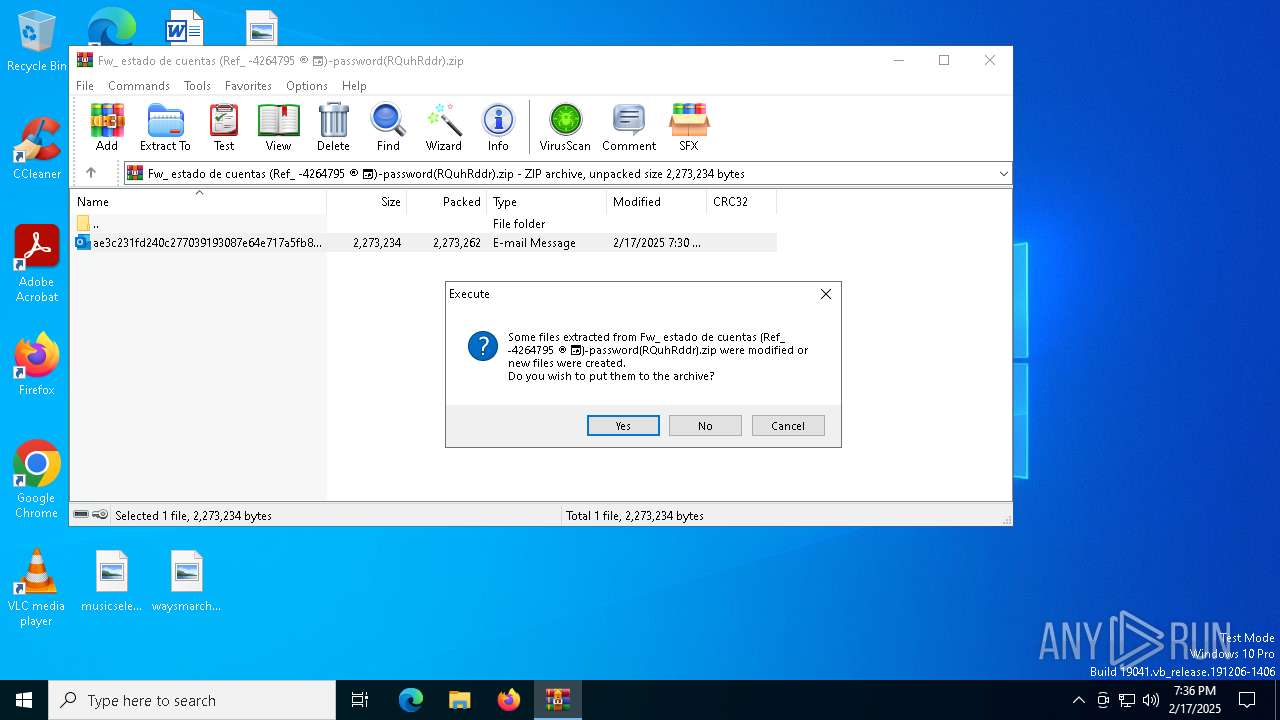
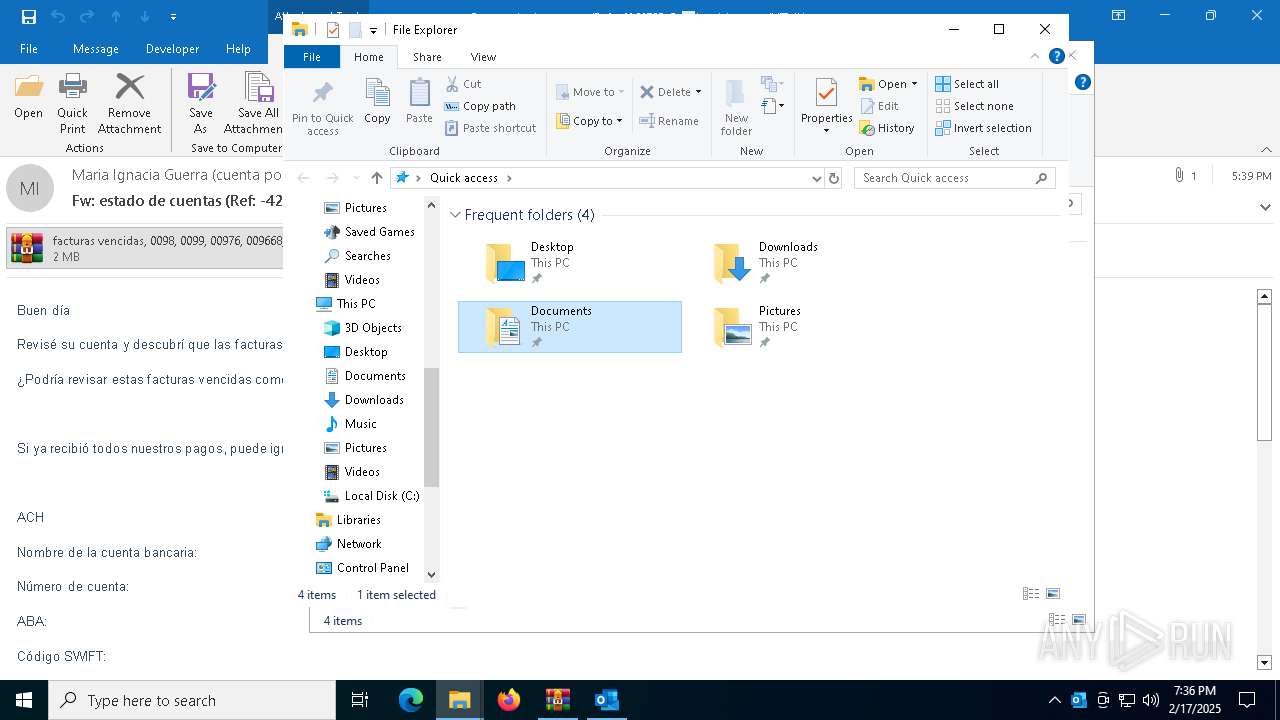
Manual execution by a user
- WinRAR.exe (PID: 6296)
- MSBuild.exe (PID: 2956)
- MSBuild.exe (PID: 1020)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 6412)
Reads the machine GUID from the registry
- facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe (PID: 6900)
- facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe (PID: 6724)
- MSBuild.exe (PID: 1020)
- MSBuild.exe (PID: 2956)
- facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe (PID: 6952)
Reads the computer name
- facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe (PID: 6724)
- facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe (PID: 6900)
- MSBuild.exe (PID: 1020)
- MSBuild.exe (PID: 2956)
- facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe (PID: 6952)
Checks supported languages
- MSBuild.exe (PID: 2956)
- facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe (PID: 6900)
- MSBuild.exe (PID: 1020)
- facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe (PID: 6952)
- facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe (PID: 6724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:02:17 19:30:56 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 2273262 |
| ZipUncompressedSize: | 2273234 |
| ZipFileName: | ae3c231fd240c277039193087e64e717a5fb894f0d8cc5108424334205432706.eml |
Total processes
140
Monitored processes
10
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2956 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 4132 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
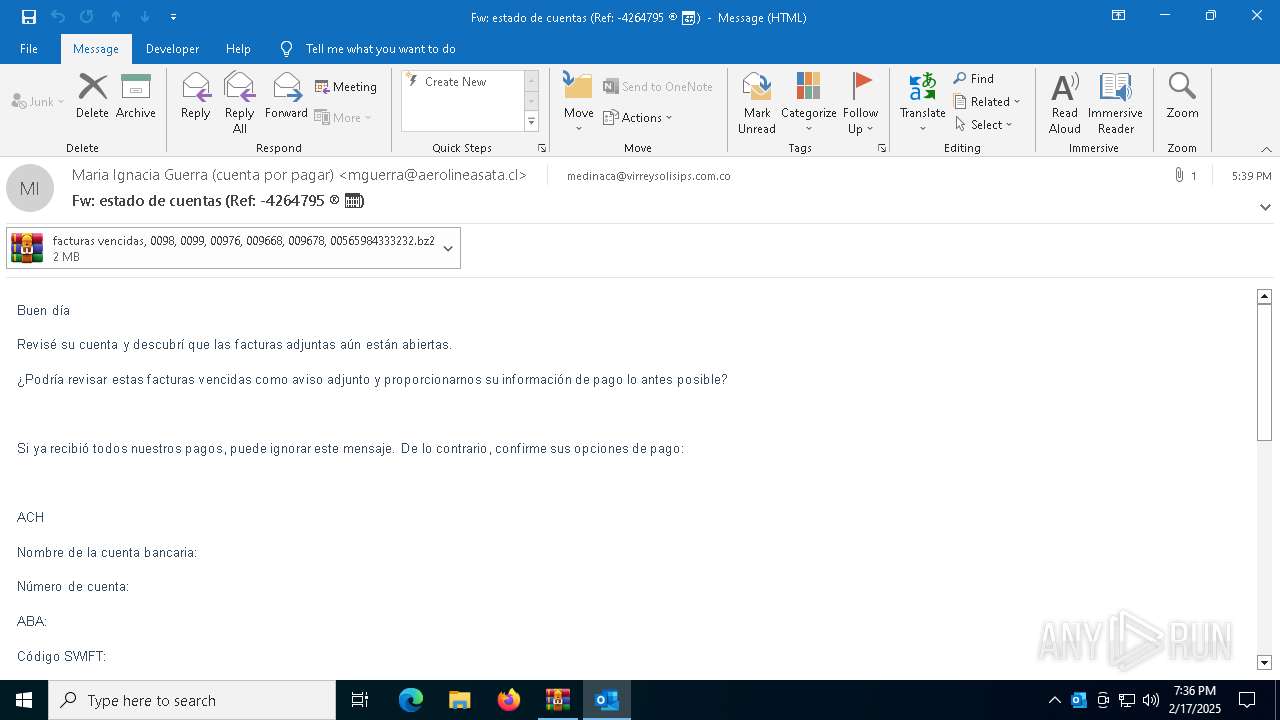
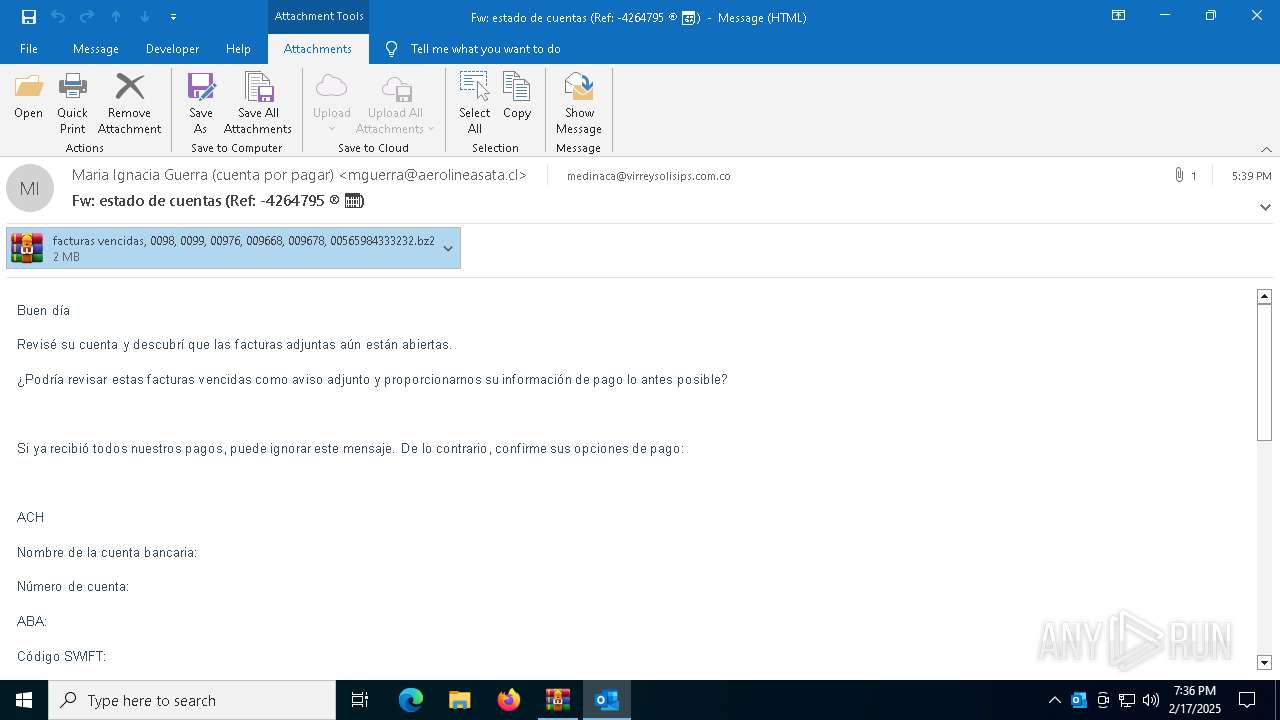
| 4872 | "C:\Program Files\Microsoft Office\Root\Office16\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Rar$DIb6412.24610\ae3c231fd240c277039193087e64e717a5fb894f0d8cc5108424334205432706.eml" | C:\Program Files\Microsoft Office\root\Office16\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 6148 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "E21C83F7-976C-46A4-BA11-DF9073645F73" "28E4CA9A-E378-4C91-B9F4-239A0C5893C2" "4872" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
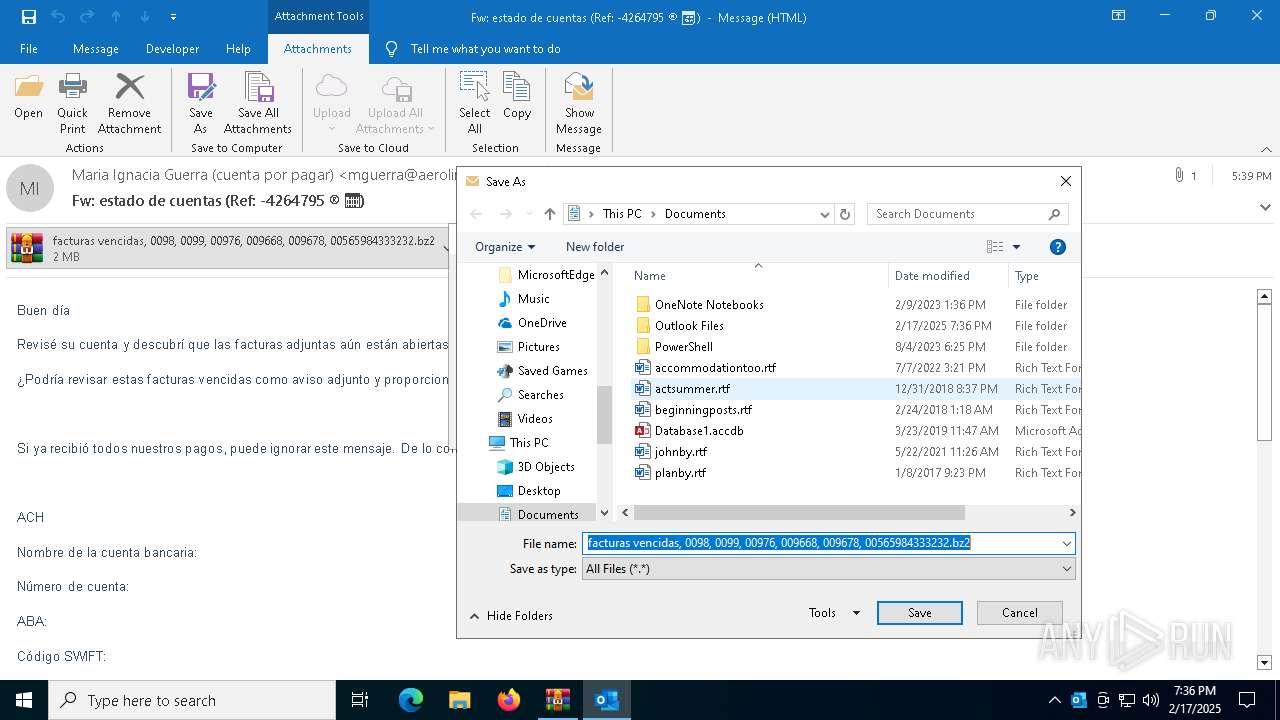
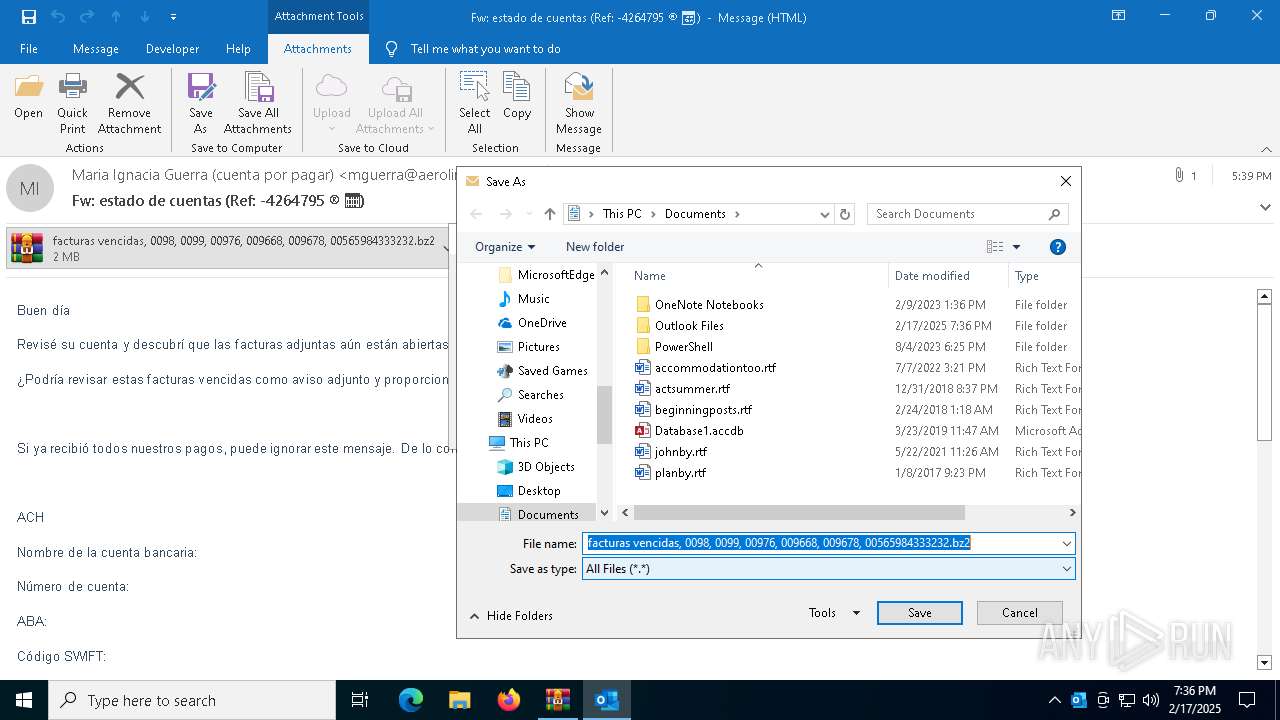
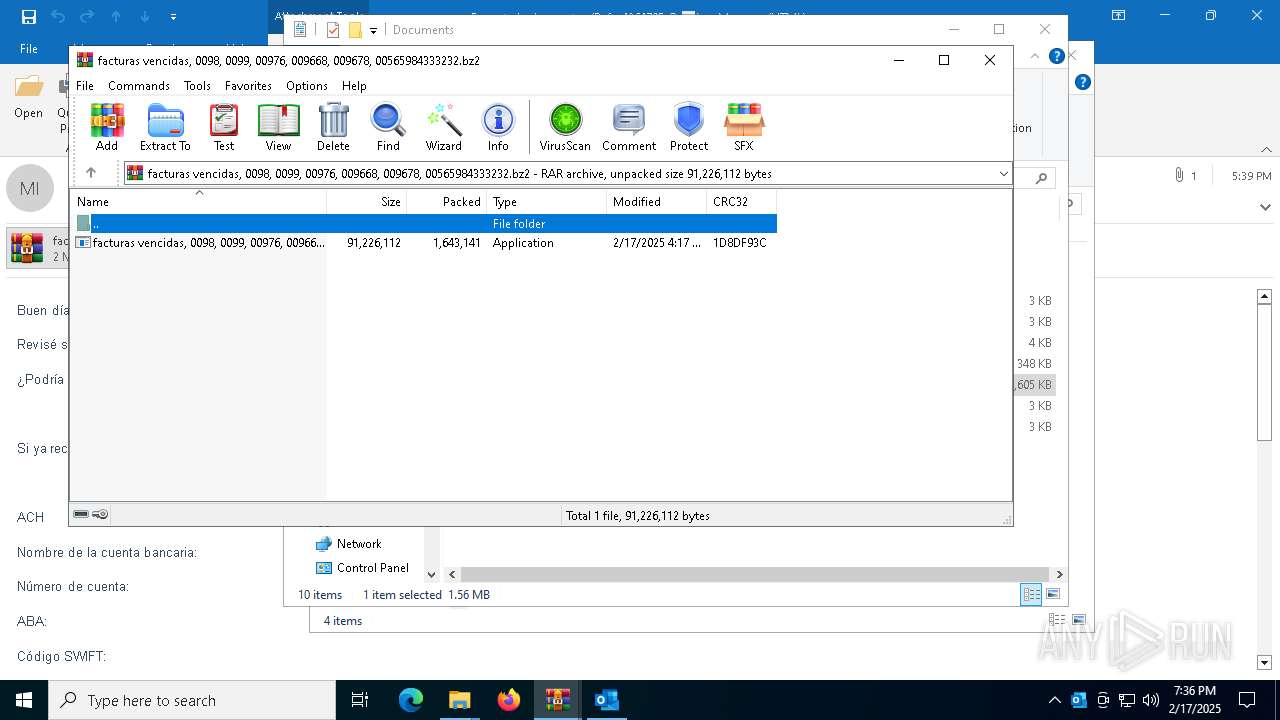
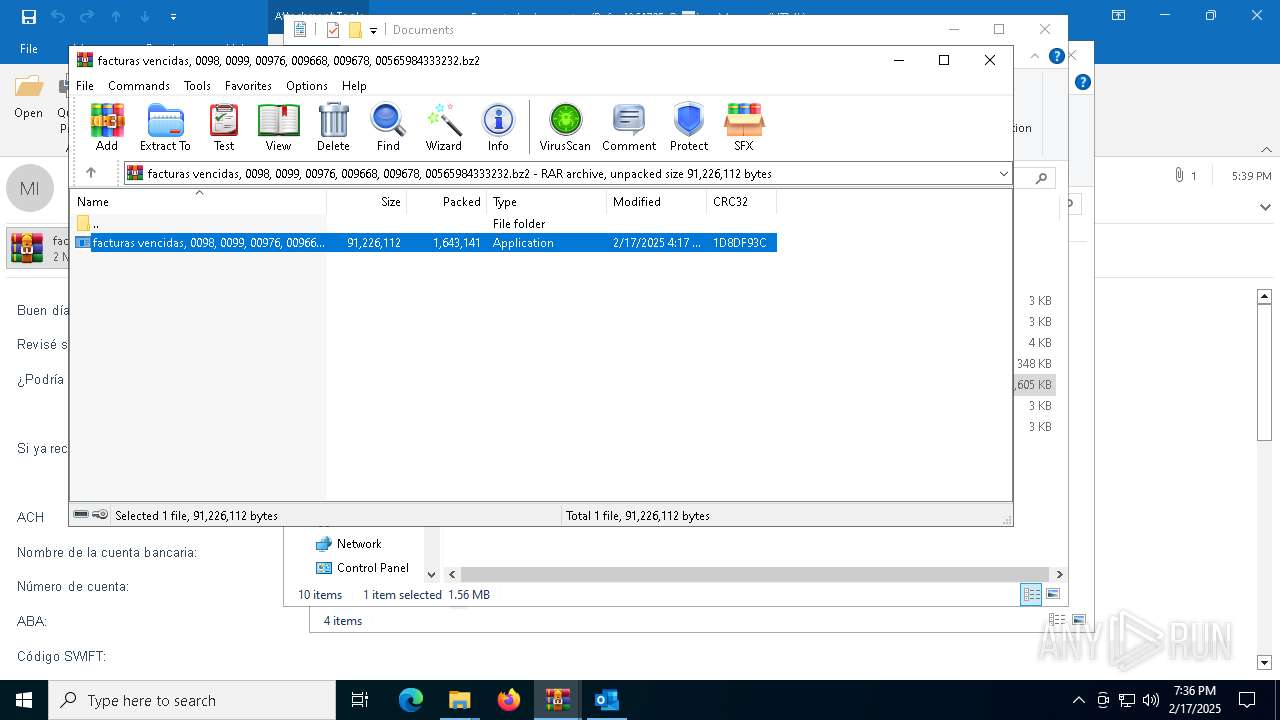
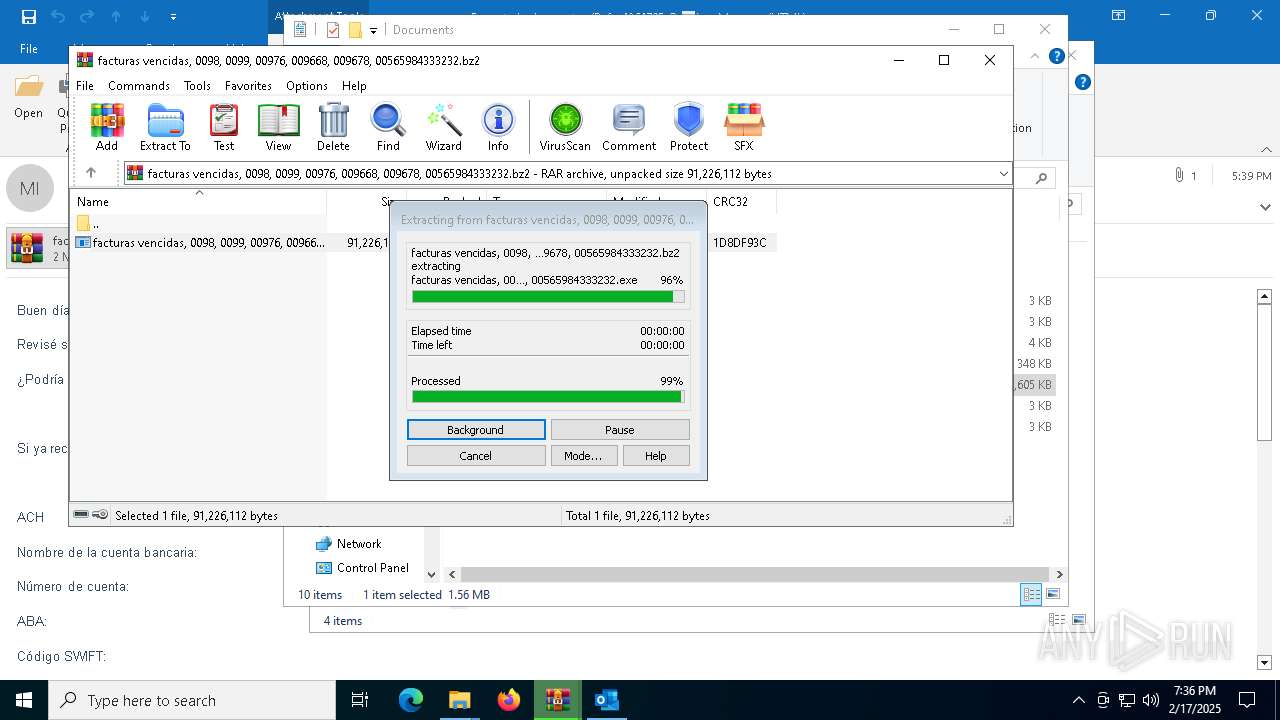
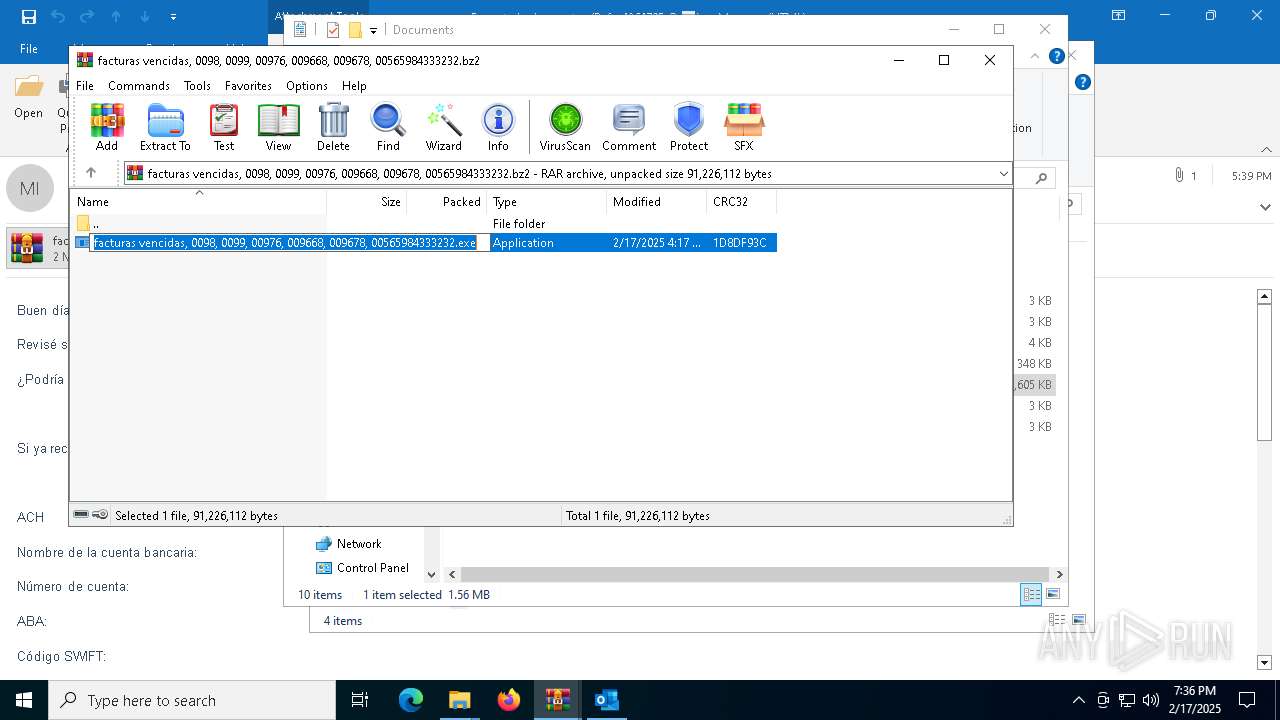
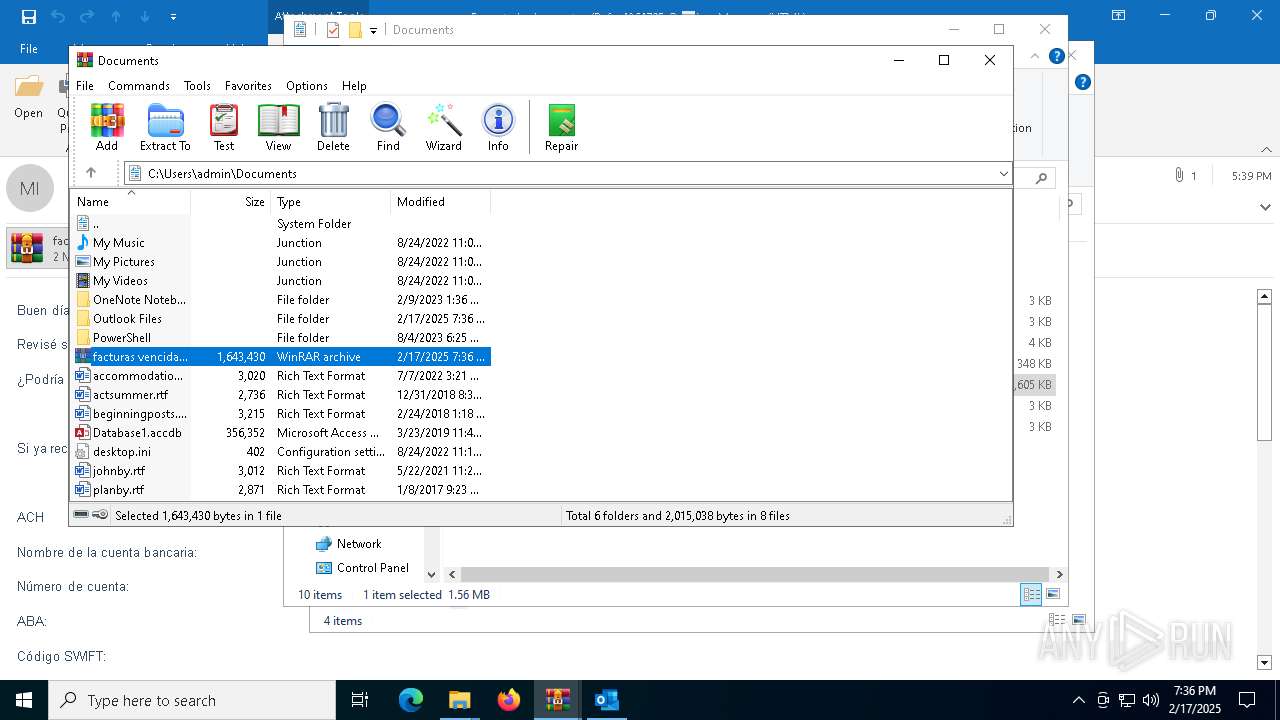
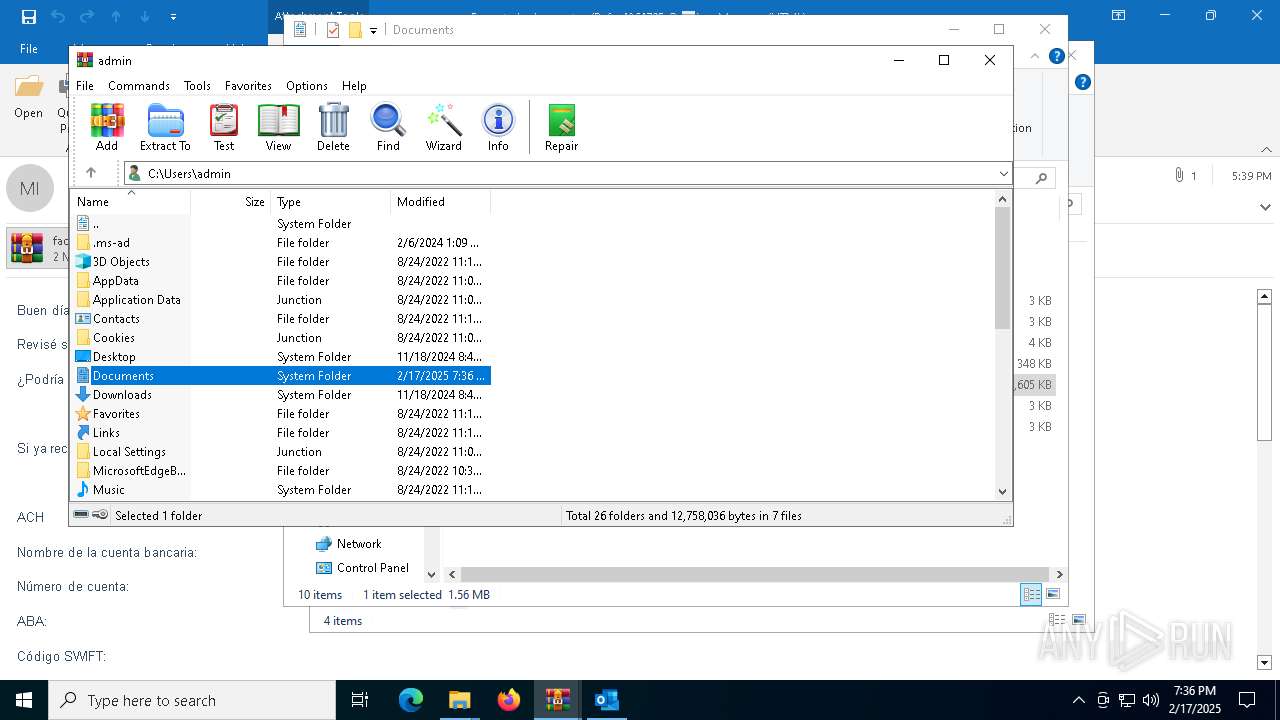
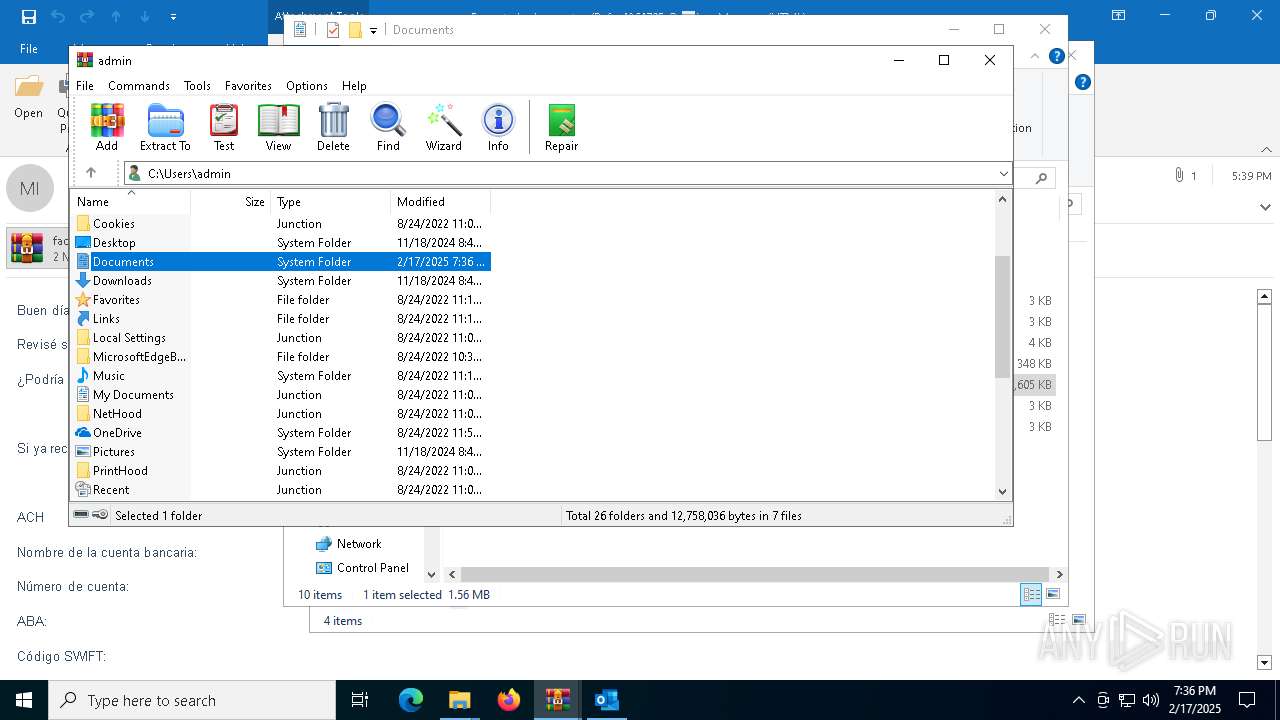
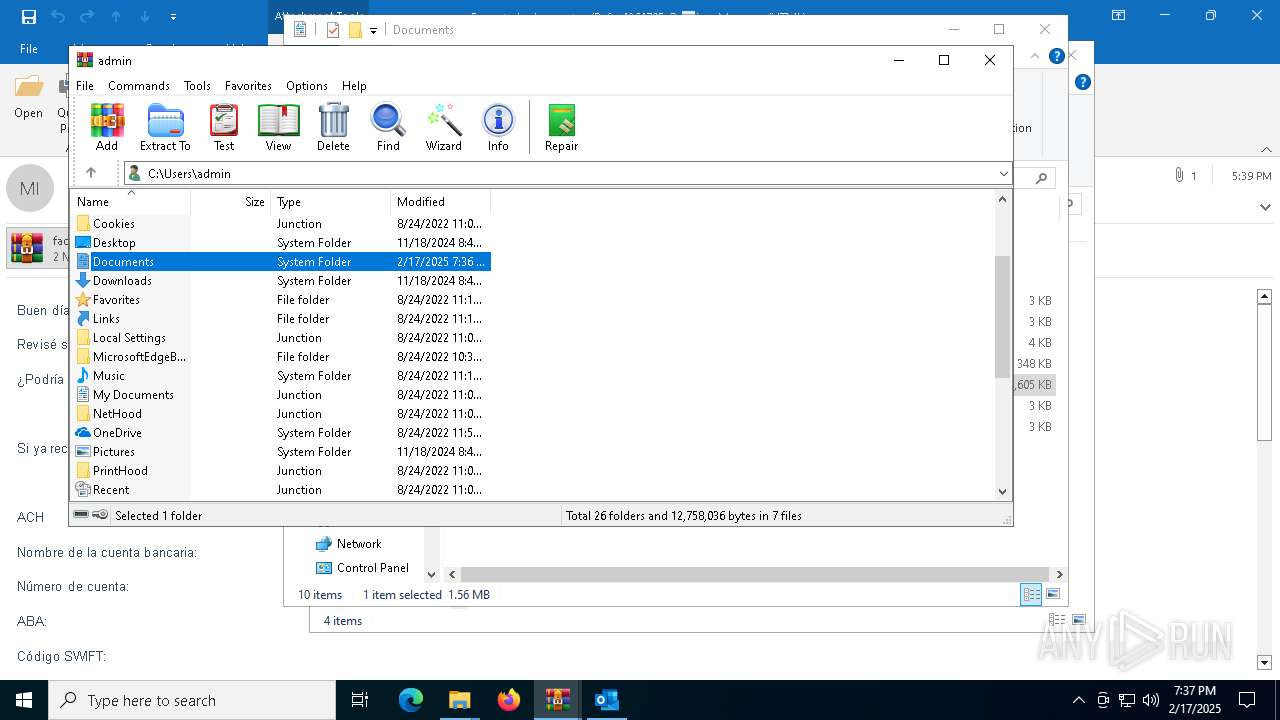
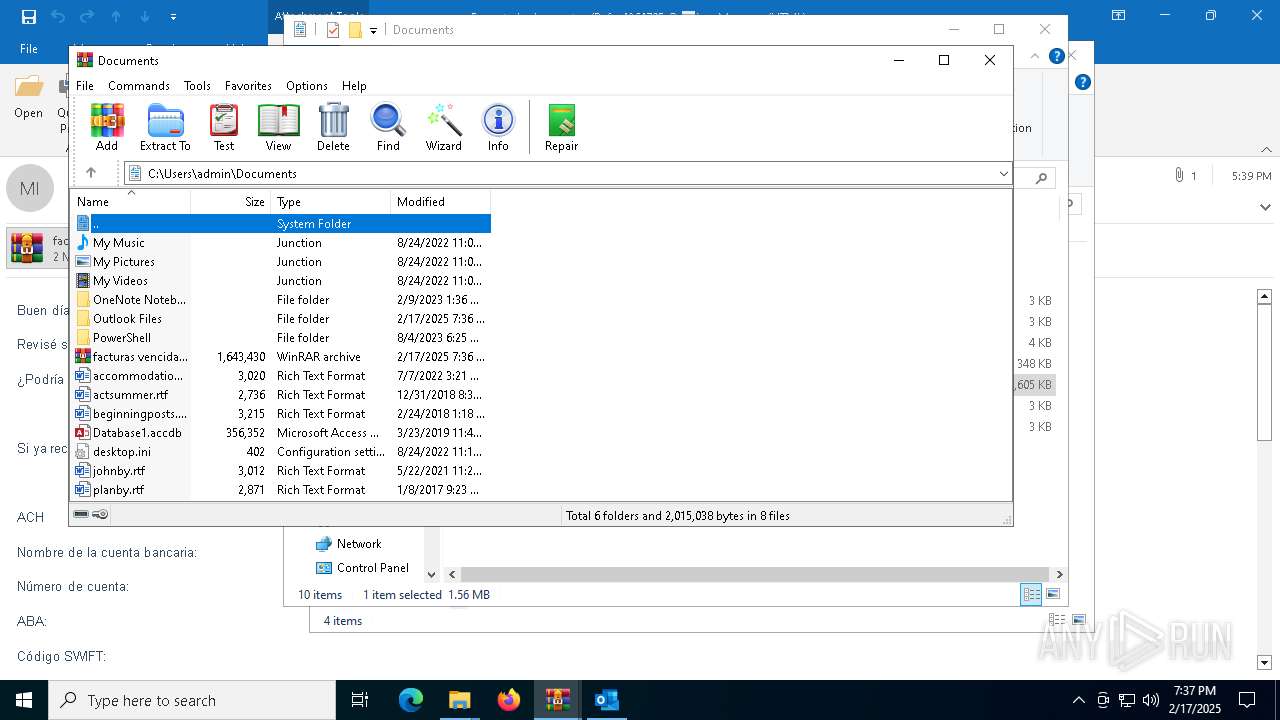
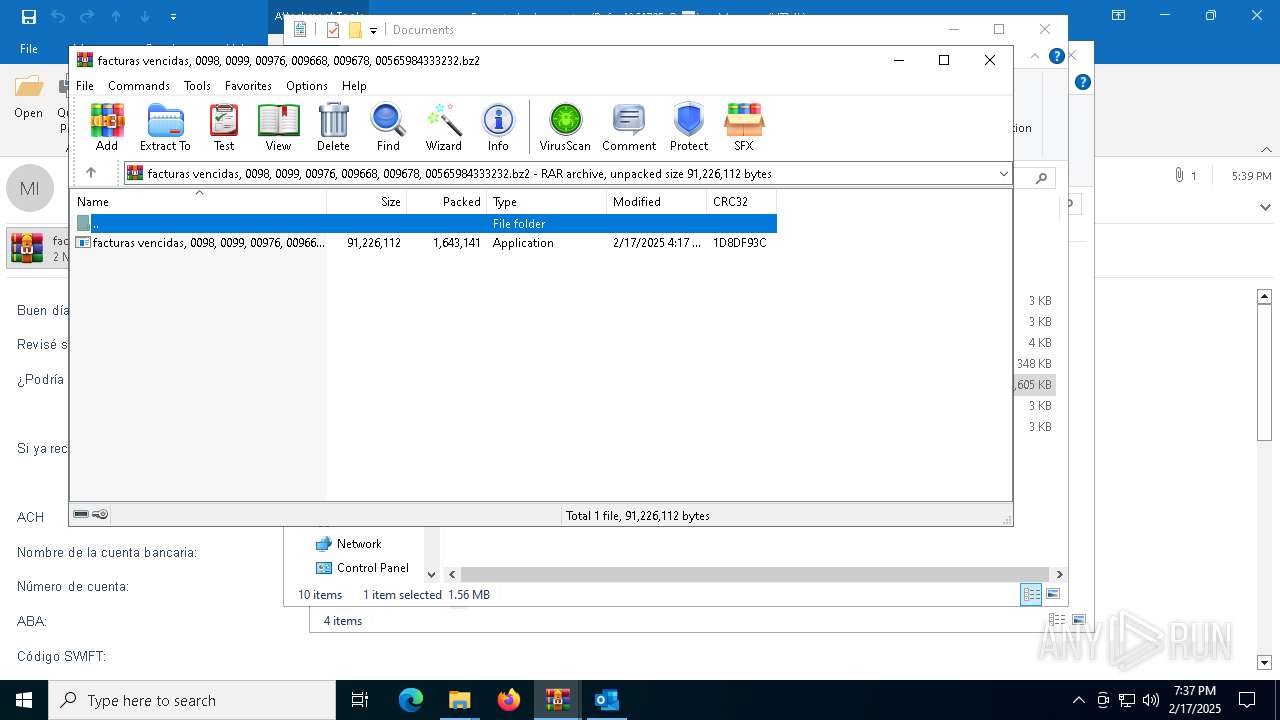
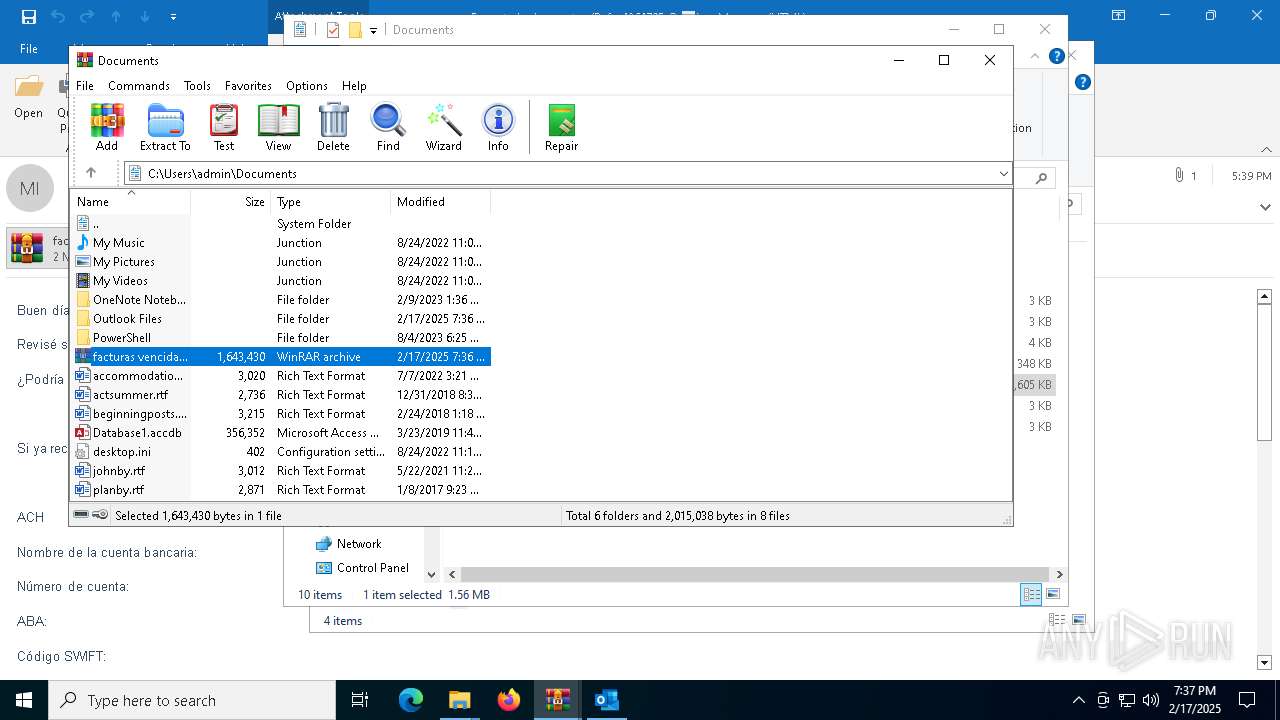
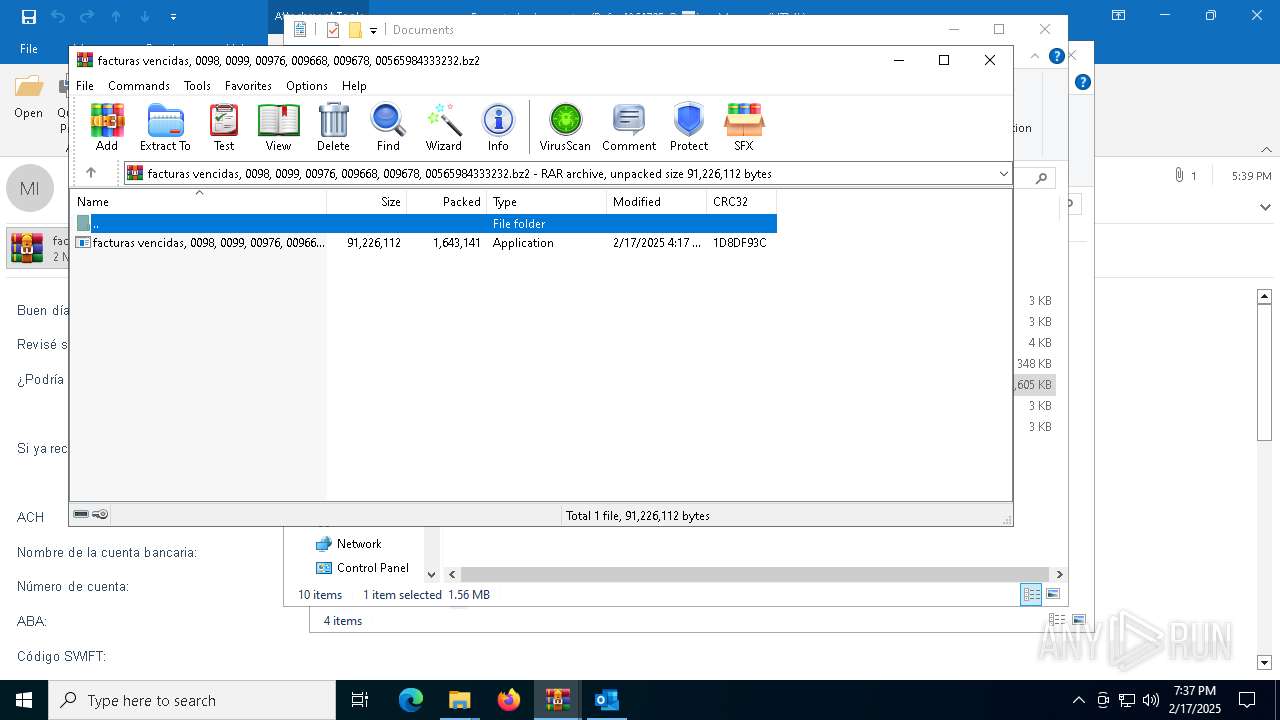
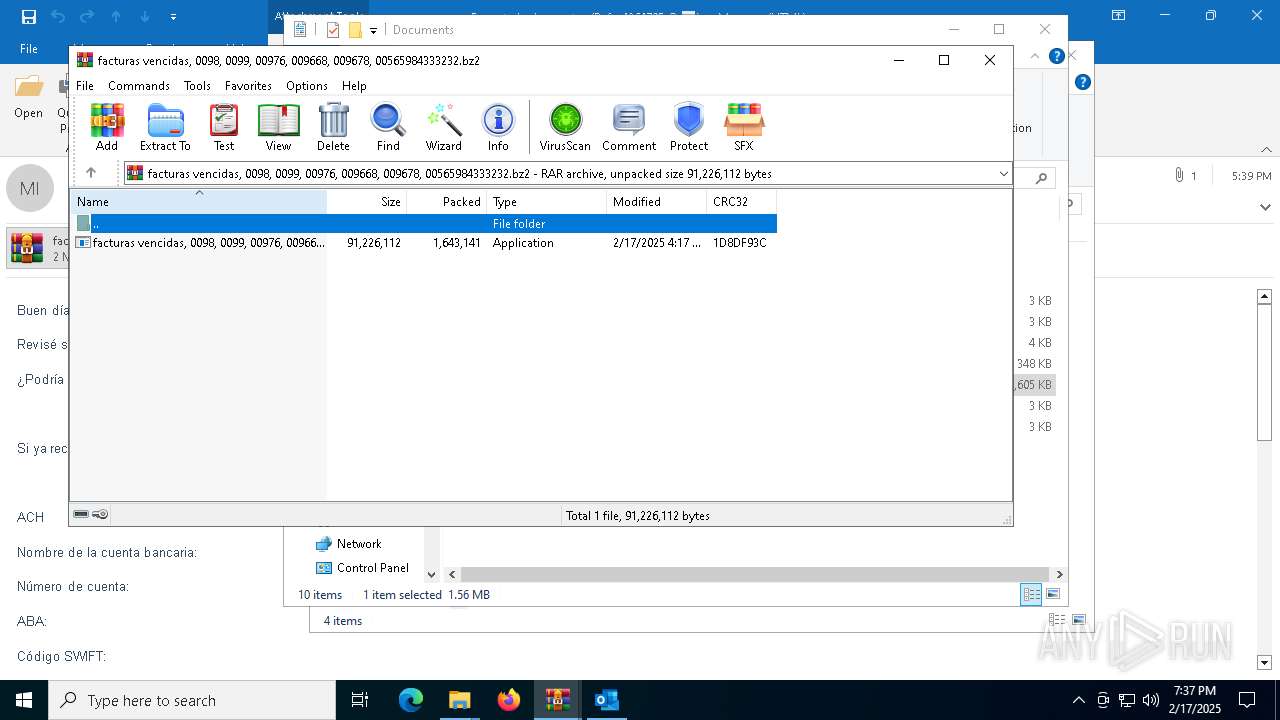
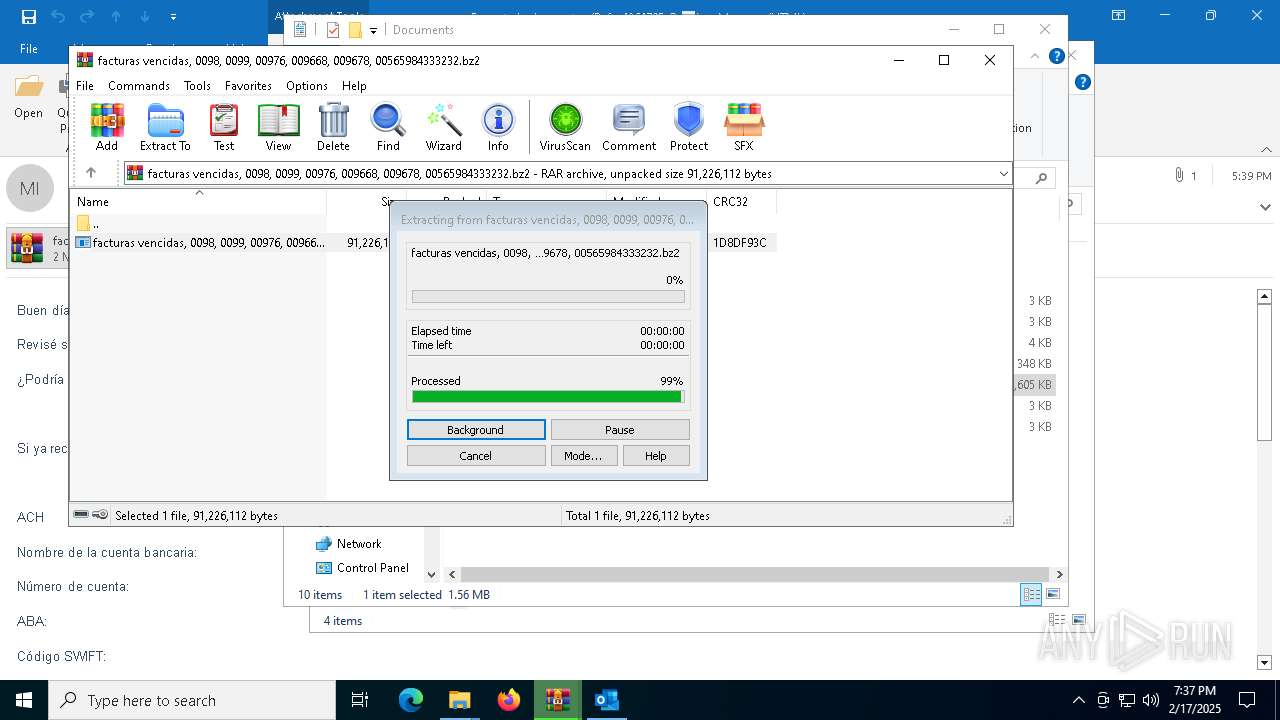
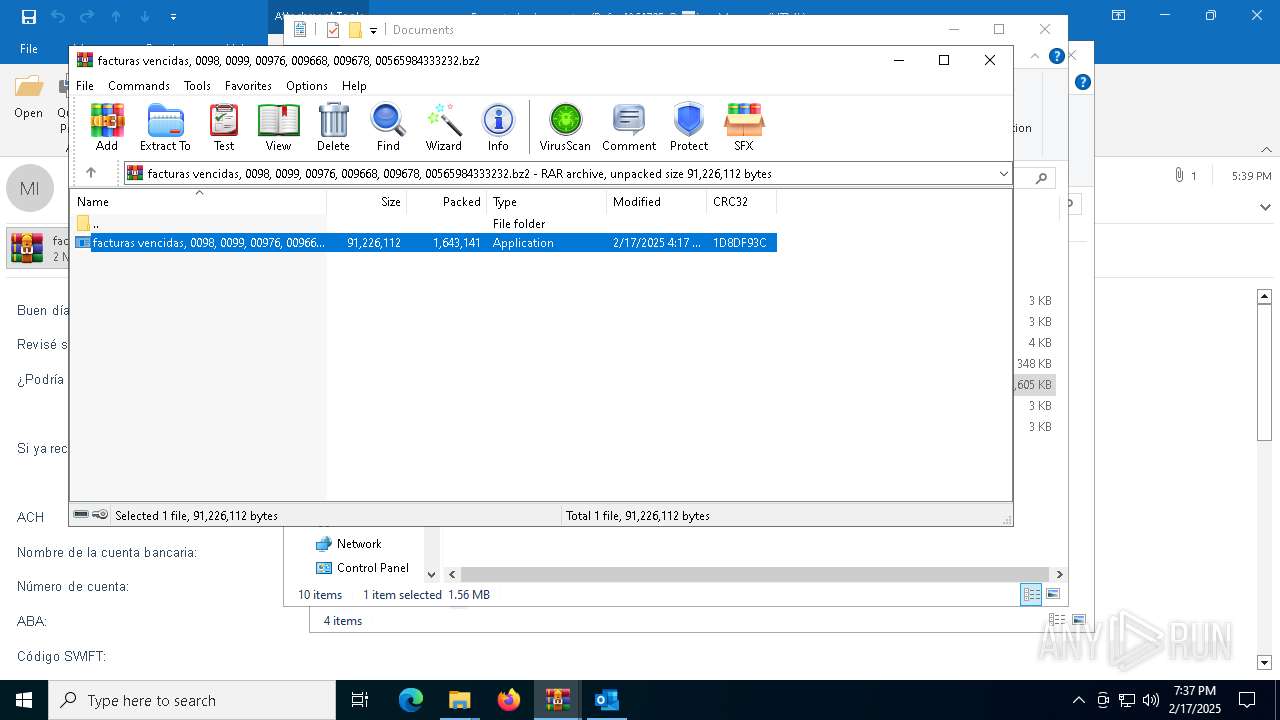
| 6296 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Documents\facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.bz2" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6412 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Fw_ estado de cuentas (Ref_ -4264795 ® 📅)-password(RQuhRddr).zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6724 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6296.34606\facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6296.34606\facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Foxmail安装程序 Version: 7.2.25.331 Modules
| |||||||||||||||
| 6900 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6296.31939\facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6296.31939\facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Foxmail安装程序 Exit code: 4294967295 Version: 7.2.25.331 Modules
| |||||||||||||||
| 6952 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6296.32375\facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6296.32375\facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Foxmail安装程序 Exit code: 4294967295 Version: 7.2.25.331 Modules
| |||||||||||||||
Total events
23 136
Read events
21 854
Write events
1 140
Delete events
142
Modification events
| (PID) Process: | (6412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Fw_ estado de cuentas (Ref_ -4264795 ® 📅)-password(RQuhRddr).zip | |||
| (PID) Process: | (6412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (6412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.eml\OpenWithProgids |
| Operation: | write | Name: | Outlook.File.eml.15 |
Value: | |||
Executable files
0
Suspicious files
12
Text files
9
Unknown types
0
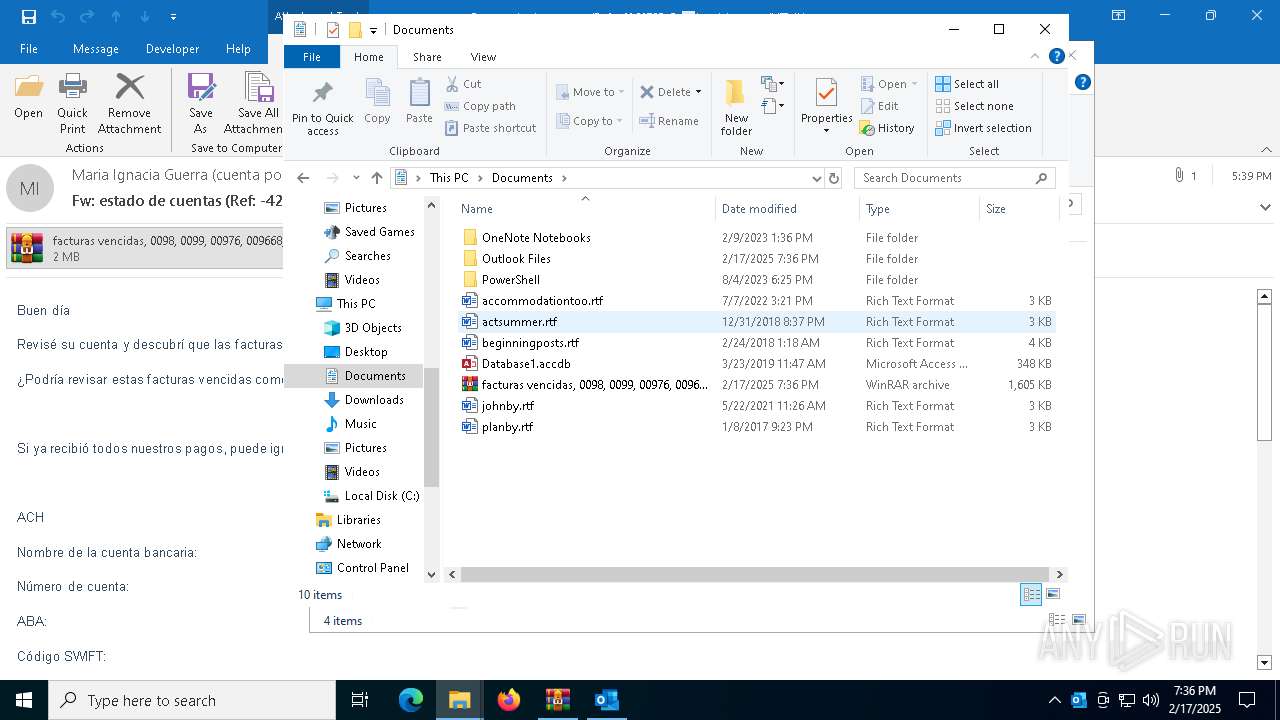
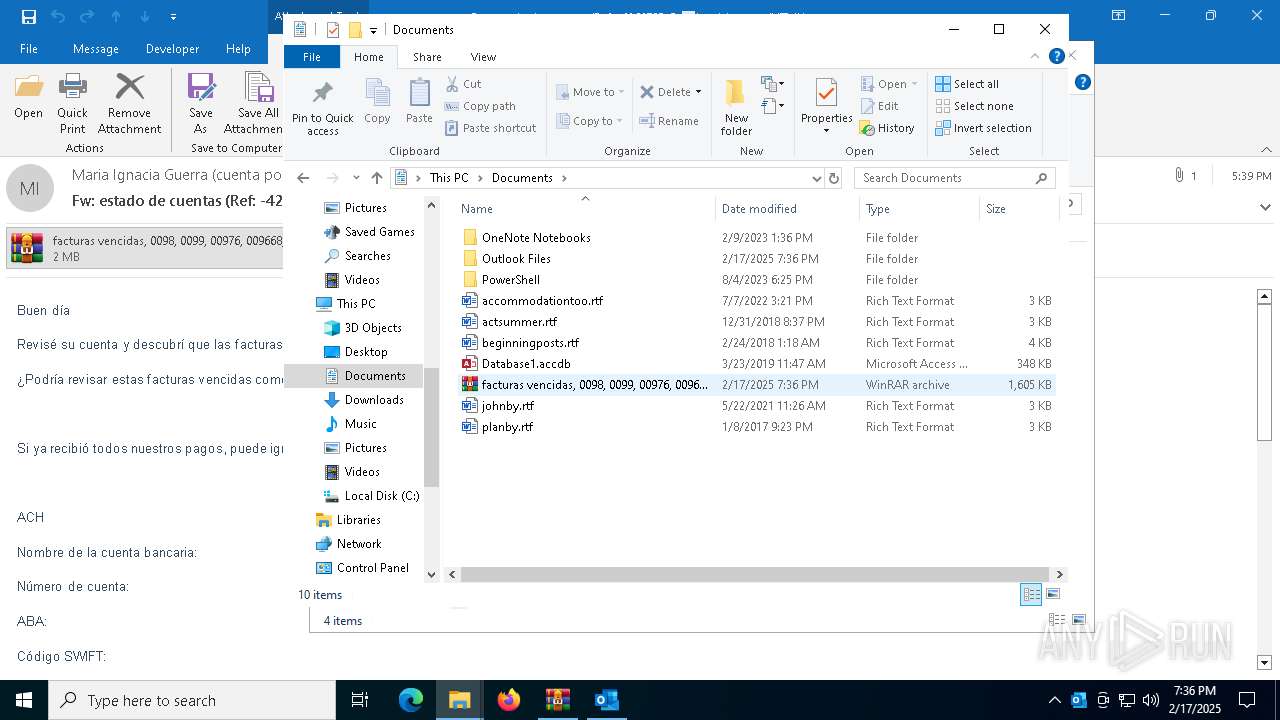
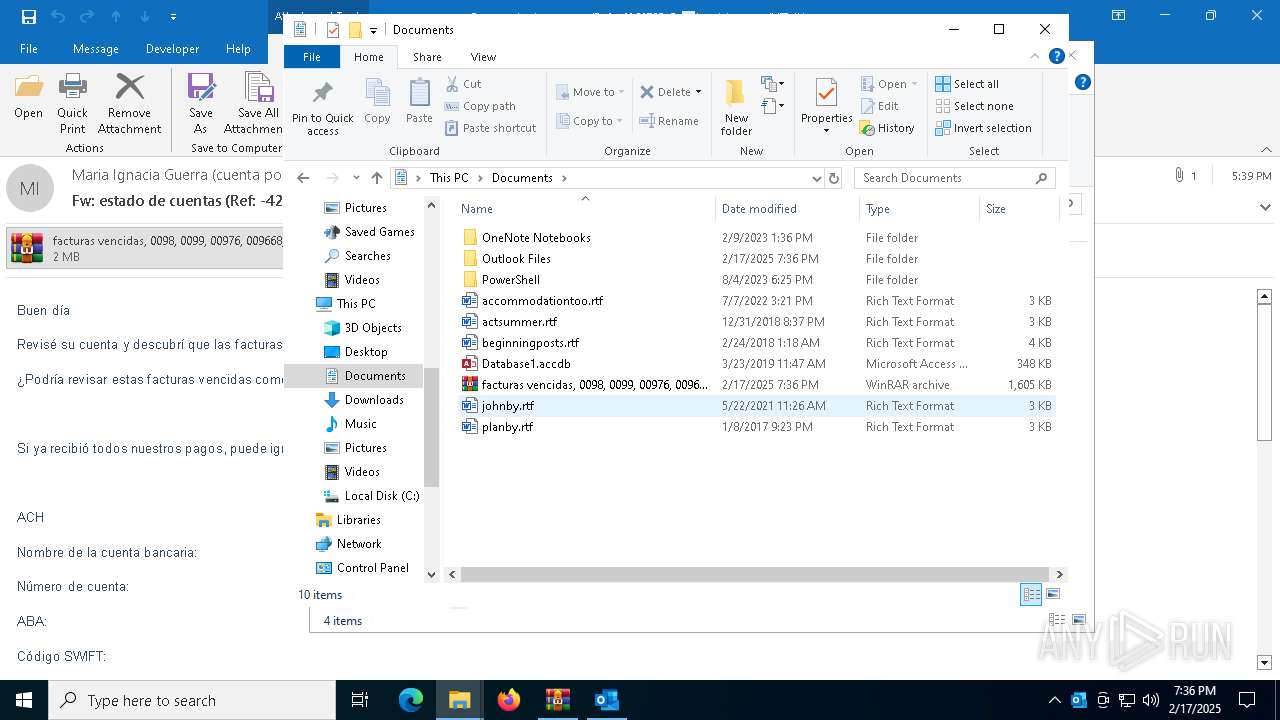
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4872 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 4872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:5798F9560CF805131118626D407C72A8 | SHA256:DA98238E16A962692B5AB6EA02722825DECB00C5B969A9FD8A26422417ADBB7F | |||
| 6296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6296.31939\facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe | — | |
MD5:— | SHA256:— | |||
| 6296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6296.32375\facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe | — | |
MD5:— | SHA256:— | |||
| 6412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb6412.24610\ae3c231fd240c277039193087e64e717a5fb894f0d8cc5108424334205432706.eml:OECustomProperty | binary | |
MD5:01545789031D5DCDDC1DF1791DDC3839 | SHA256:C7C634B658BD8EE0CC1FA4B3CA5B59724C8844E5C17E940F7E9DD3C36E9AC0C0 | |||
| 6296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6296.34606\facturas vencidas, 0098, 0099, 00976, 009668, 009678, 00565984333232.exe | — | |
MD5:— | SHA256:— | |||
| 4872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\8D25A55B-00EC-4C80-B6DC-1EB4B1CAD8B4 | xml | |
MD5:DD467C9DFD0442C2A2EB417B387AFC9B | SHA256:F13E195612B3F9D23A24FAAE137E38C5DFEC2826285539D8BEBA8BF62B5EEC2A | |||
| 4872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 4872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\6V51S18E\facturas vencidas 0098 0099 00976 009668 009678 00565984333232 (002).bz2 | compressed | |
MD5:0BDBE74B38EB6AED00AC0553AEC49D38 | SHA256:FC65828E720F89F2674E80A501303F987DA499E1CB663DF9033224CA46D8CF0A | |||
| 4872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TableViewPreviewPrefs_2_9AE679FE801B8743B419154E491D8C31.dat | xml | |
MD5:0E092DB99AEE99FDFF9B5B222C732CFD | SHA256:D1614AD99ADED9F6F5C1BE7FE7FFA5124BD04A526580DA3818EA8A954E852AA6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
42
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4872 | OUTLOOK.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5892 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6316 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7016 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4872 | OUTLOOK.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6316 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5892 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
936 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |