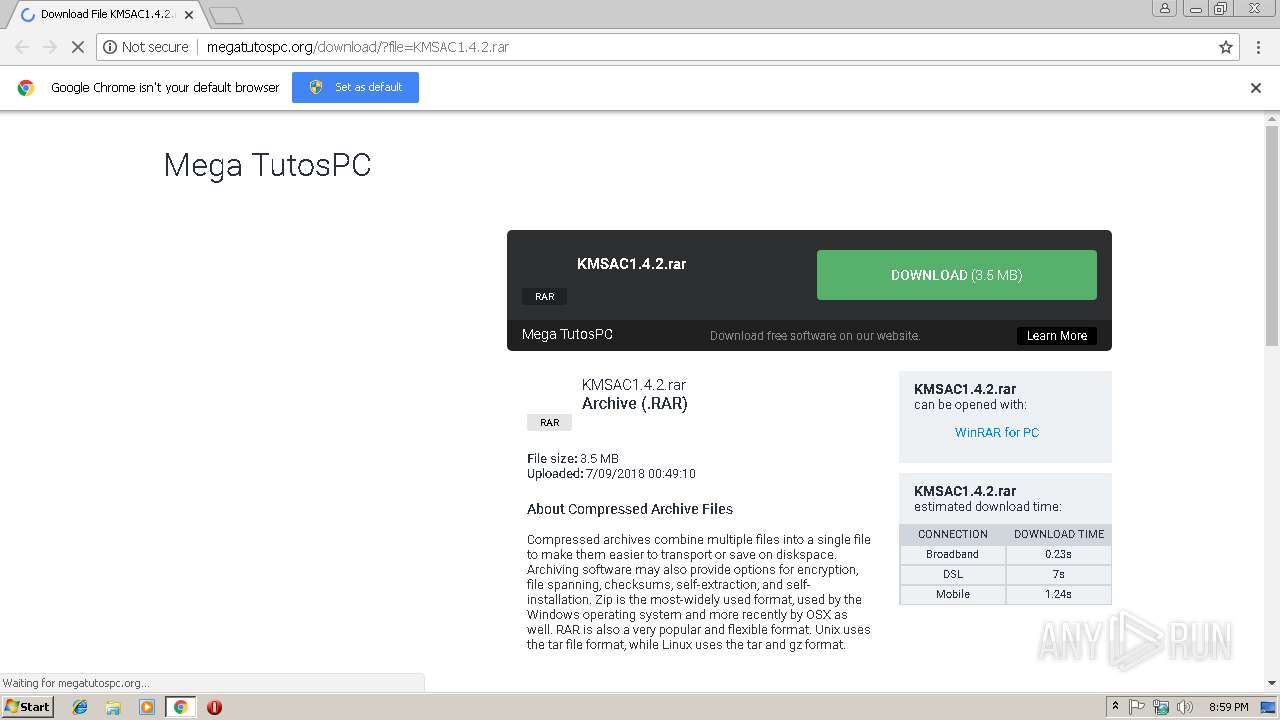
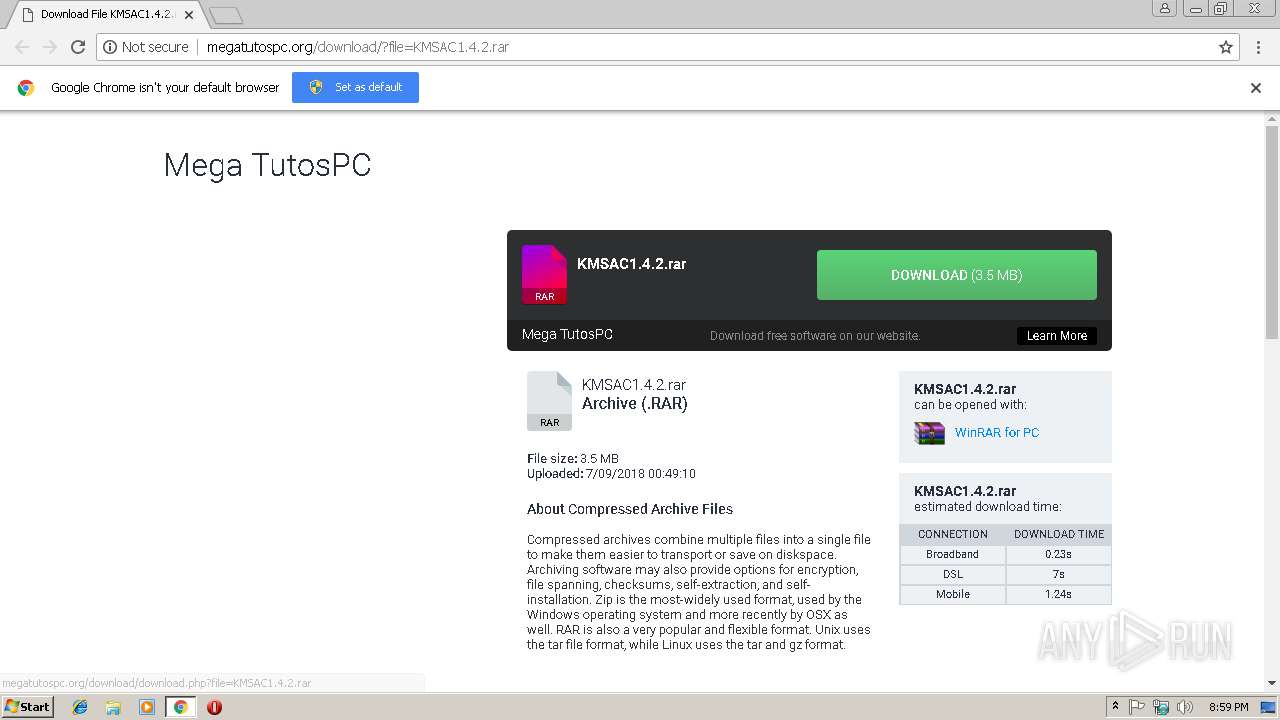
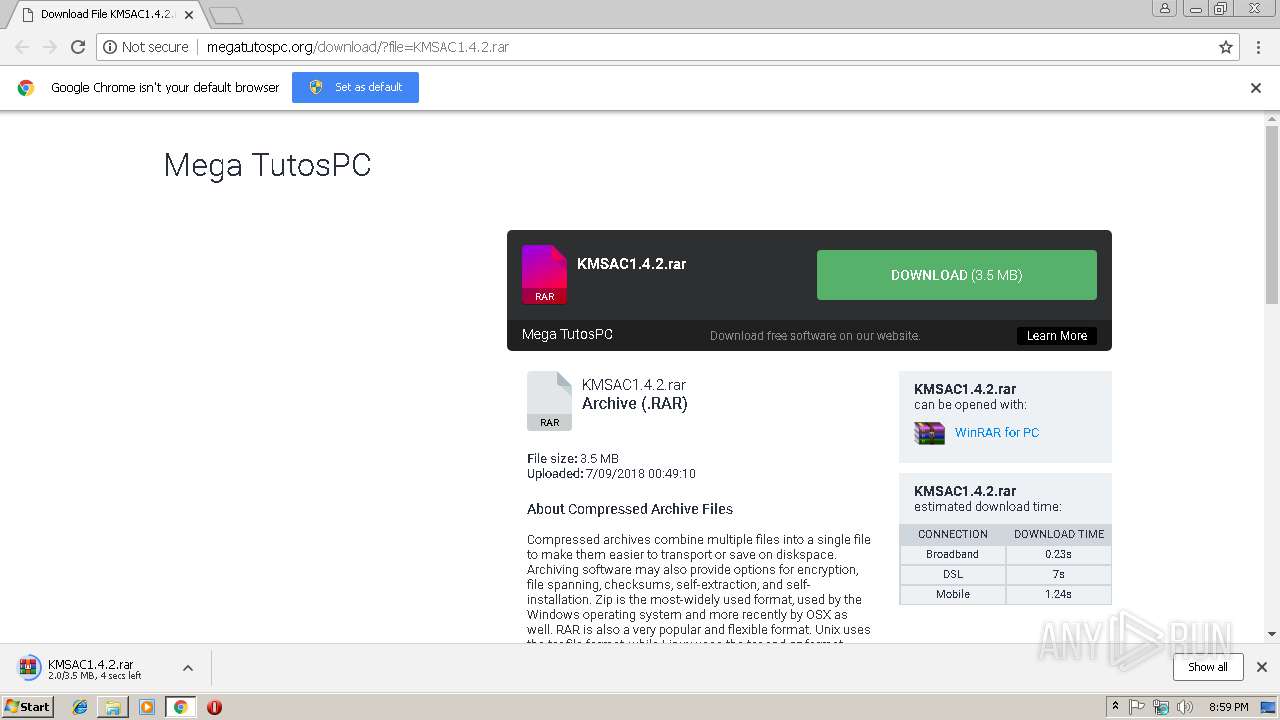
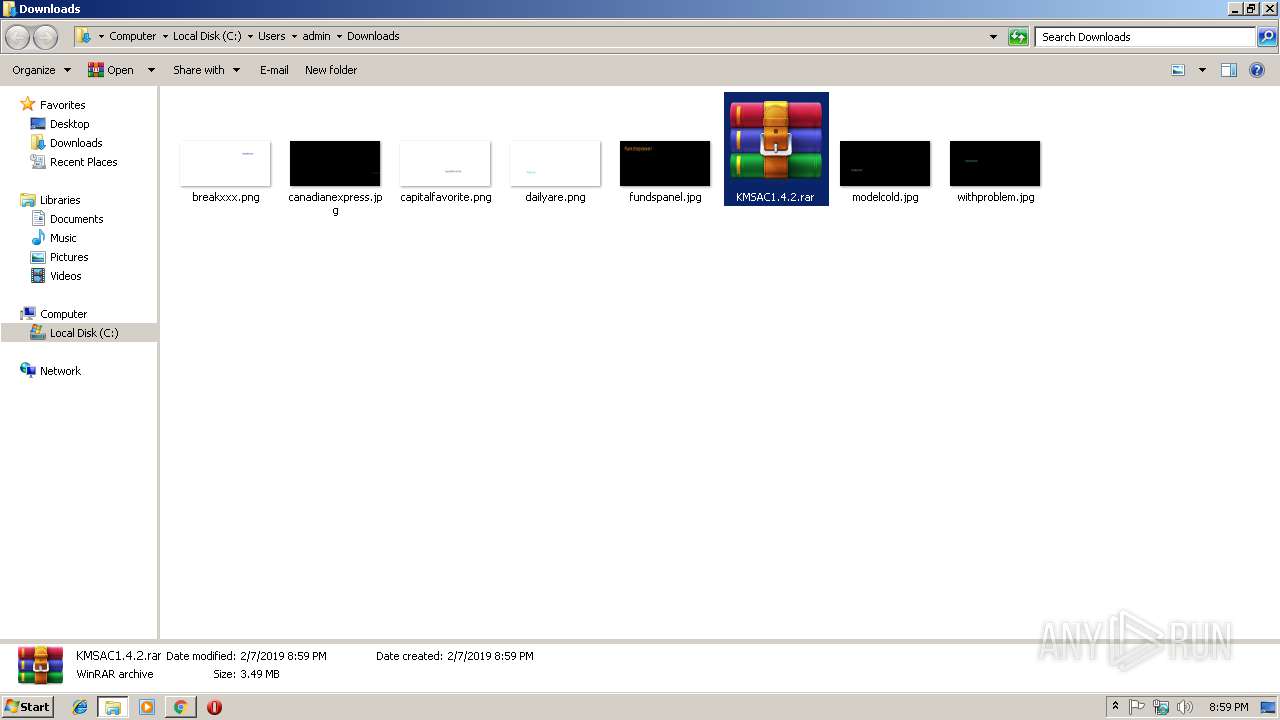
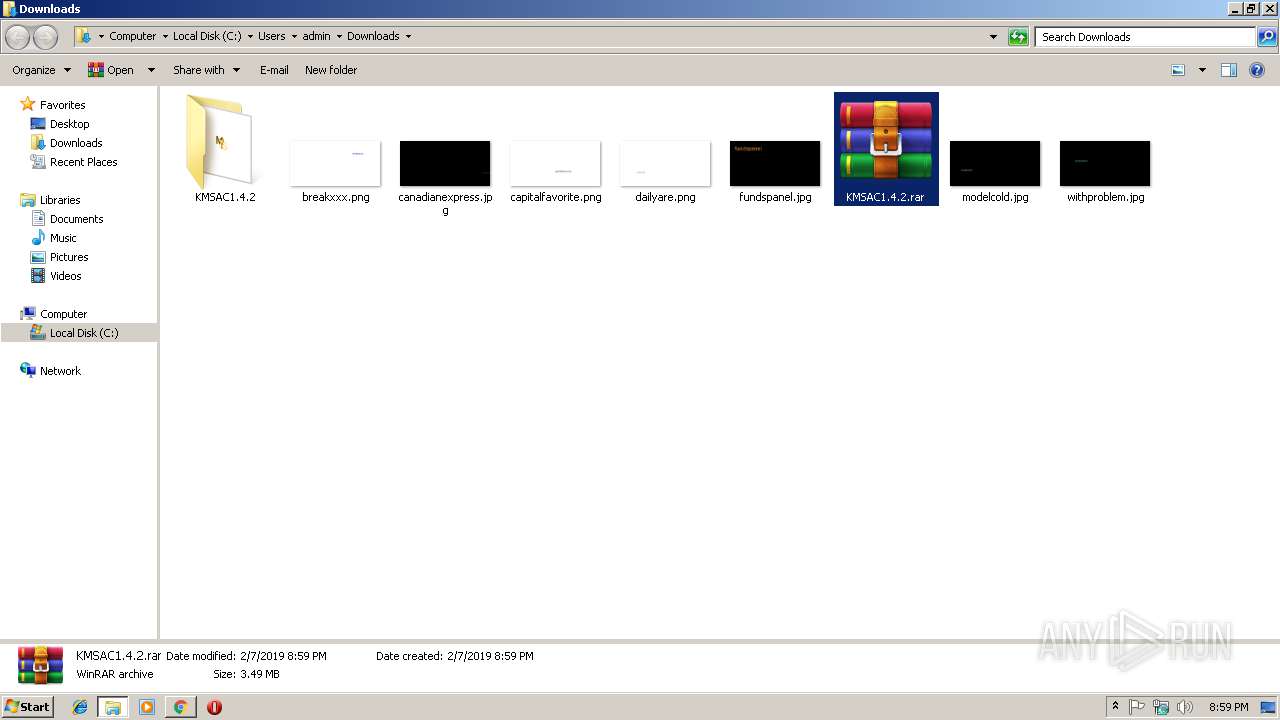
| URL: | http://megatutospc.org/download/download.php?file=KMSAC1.4.2.rar |
| Full analysis: | https://app.any.run/tasks/da6e9423-2a72-4d9d-a07a-23e91aed6b9a |
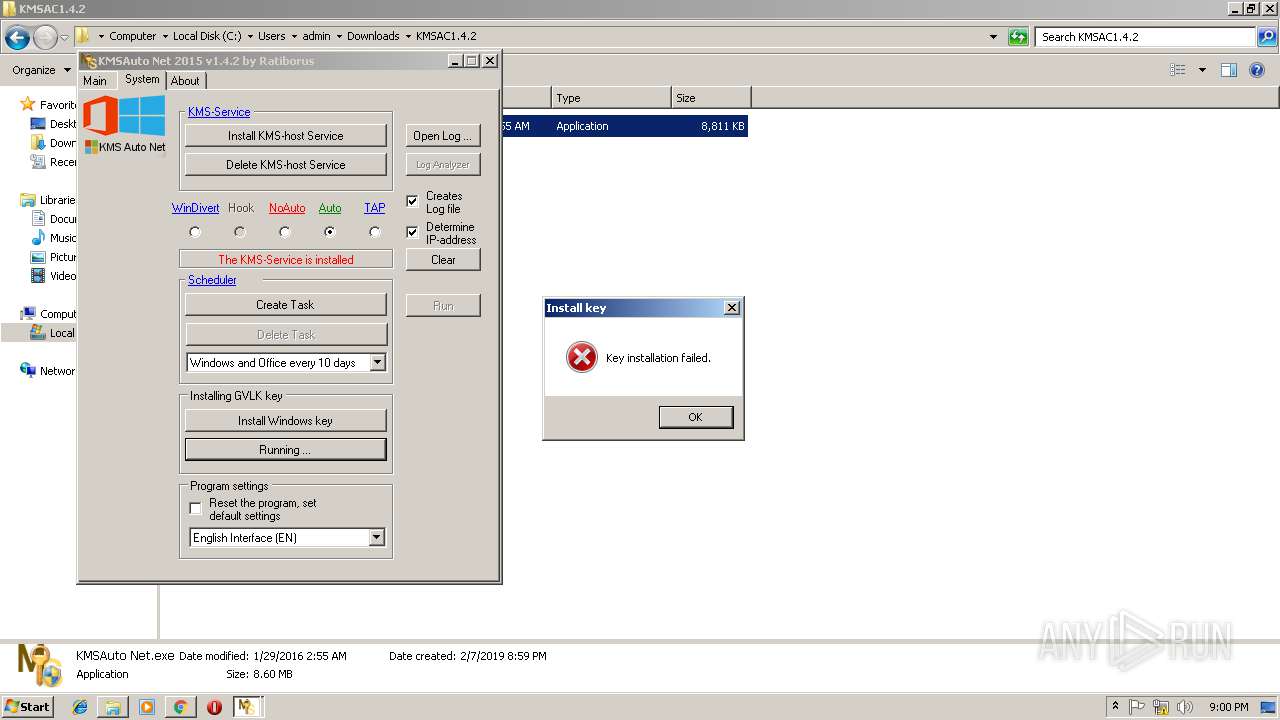
| Verdict: | Malicious activity |
| Analysis date: | February 07, 2019, 20:58:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9DA93D3A61E30FD6C6DB13B164BA7F5F |
| SHA1: | C8AACAD2EEF85756DC5304EB6448C3E1A7FF5010 |
| SHA256: | E0730E4A0372097CA3A78B6DF33082C83A47B1B451BCA9F795AD397353313364 |
| SSDEEP: | 3:N1KTEtWVGfpXJlrOYu8XLUXn:CHGfdnrO6LUXn |
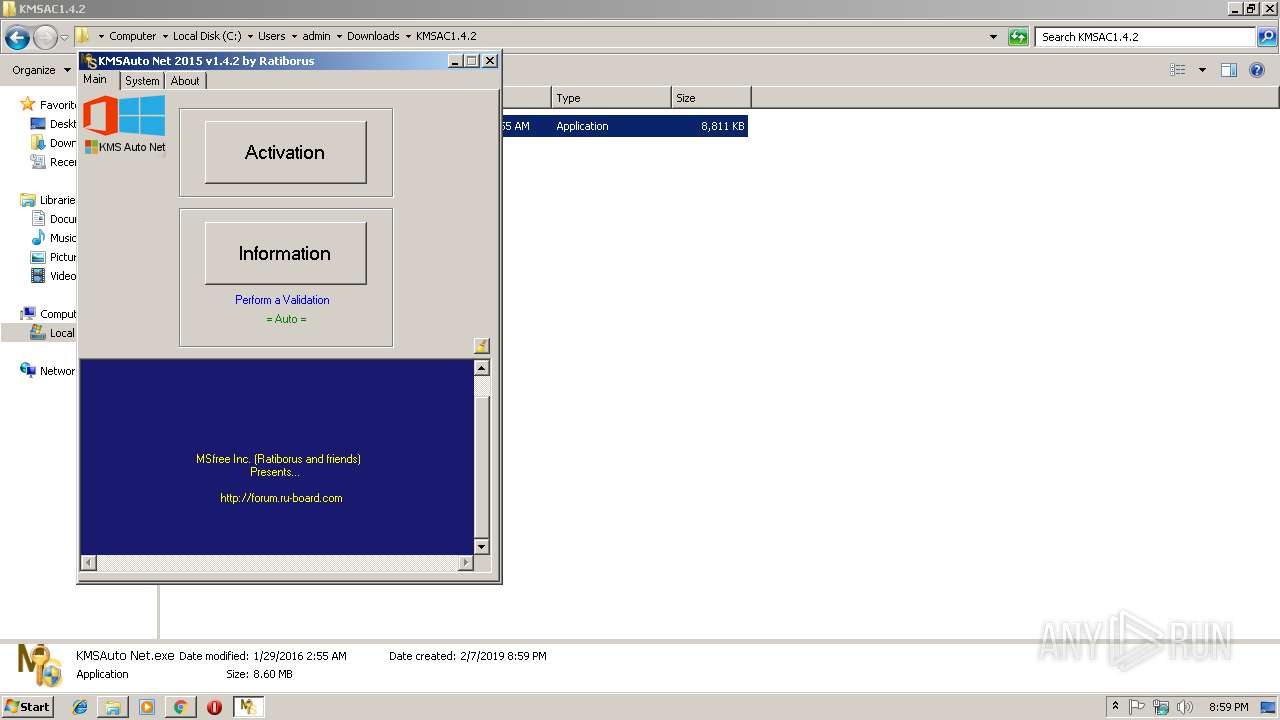
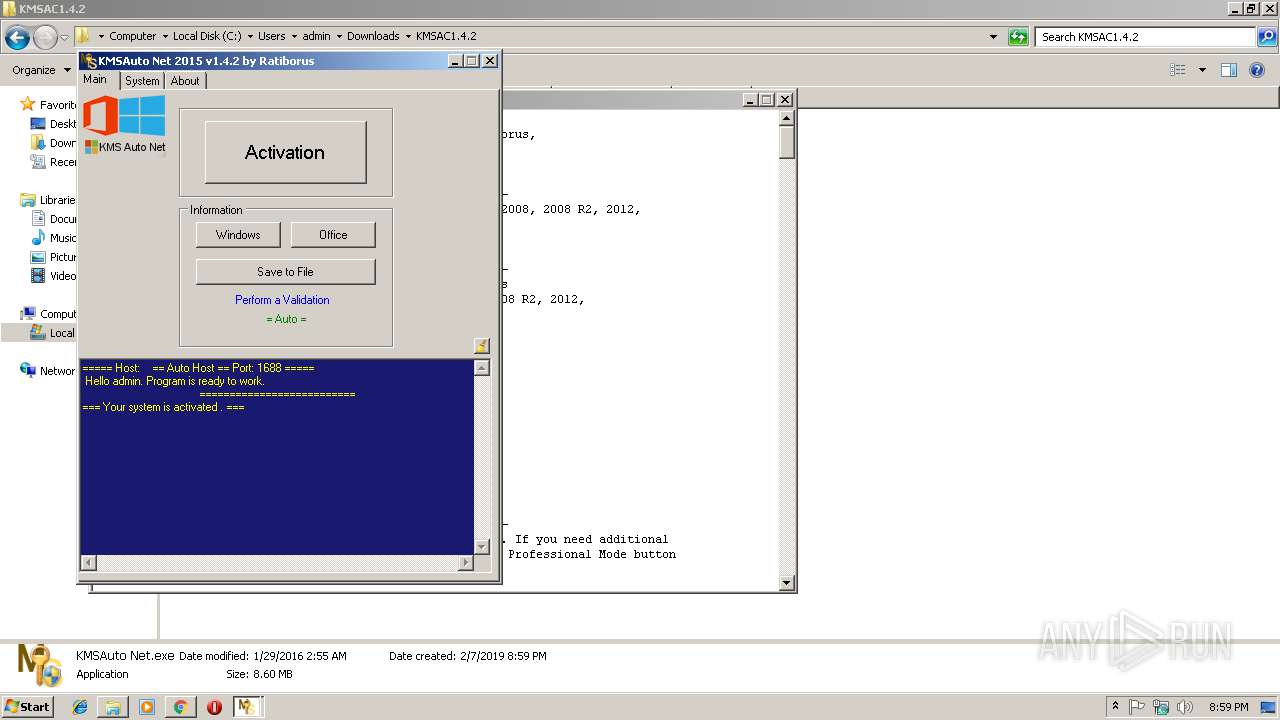
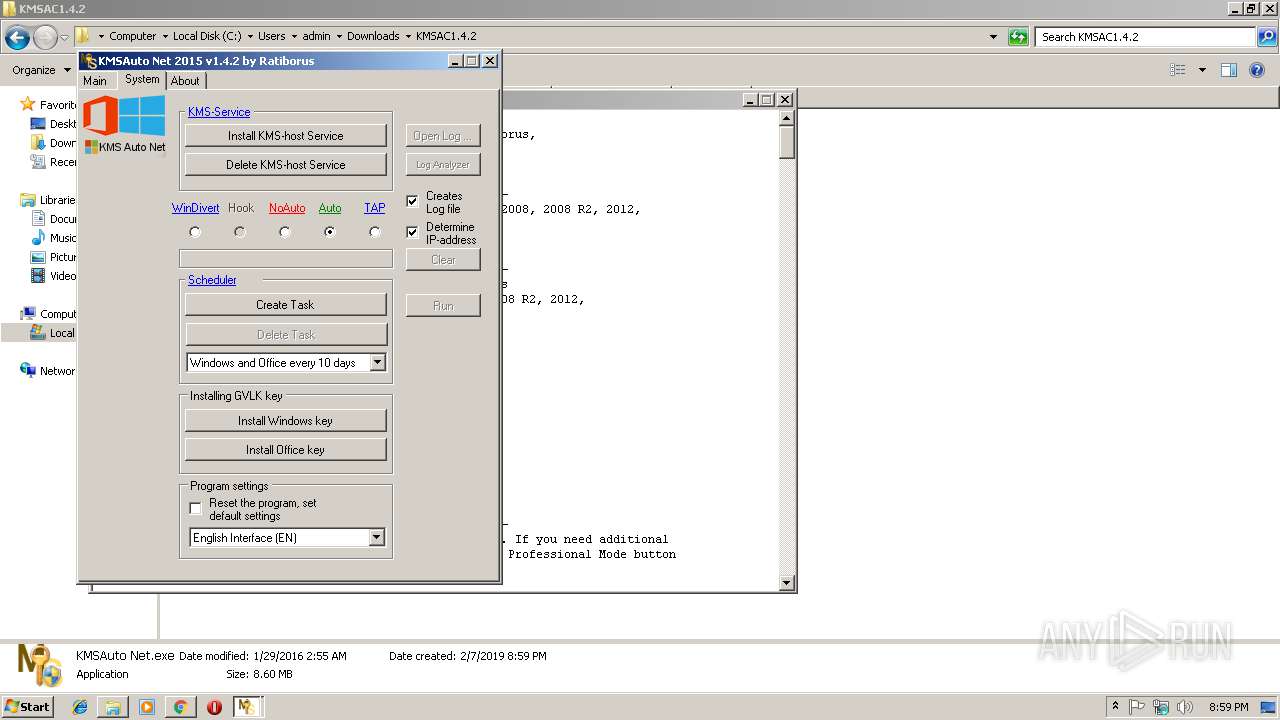
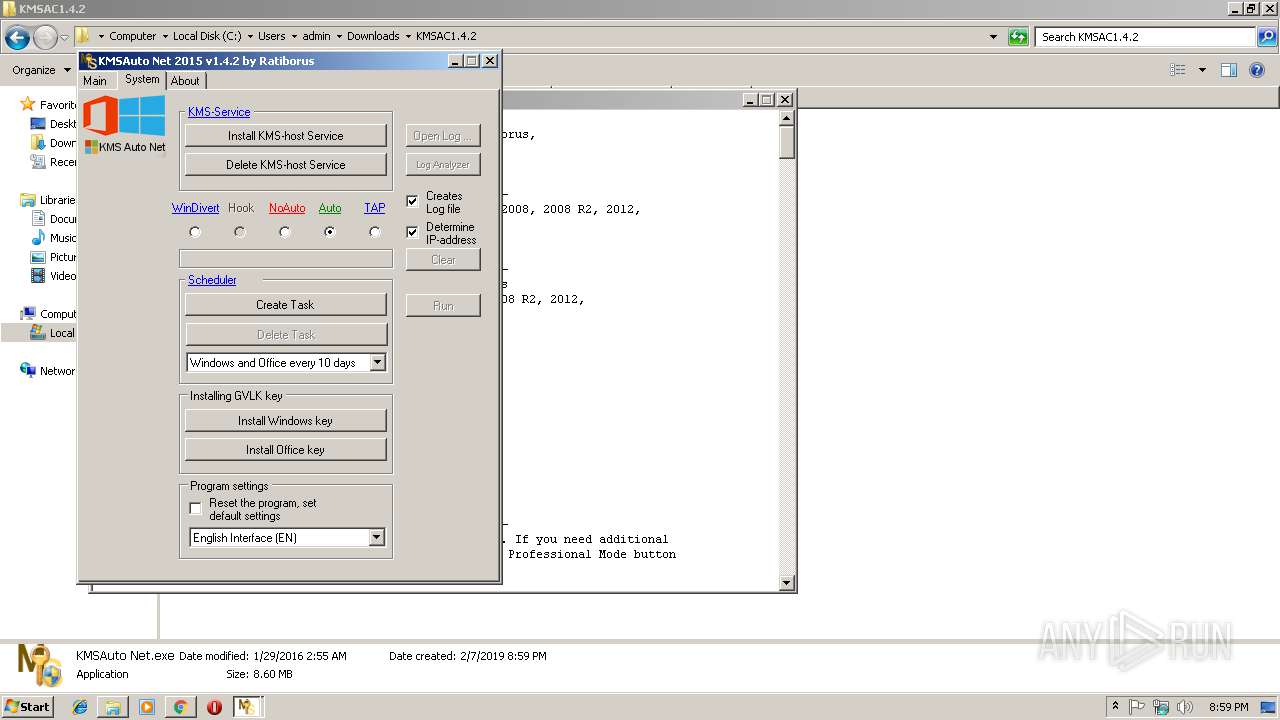
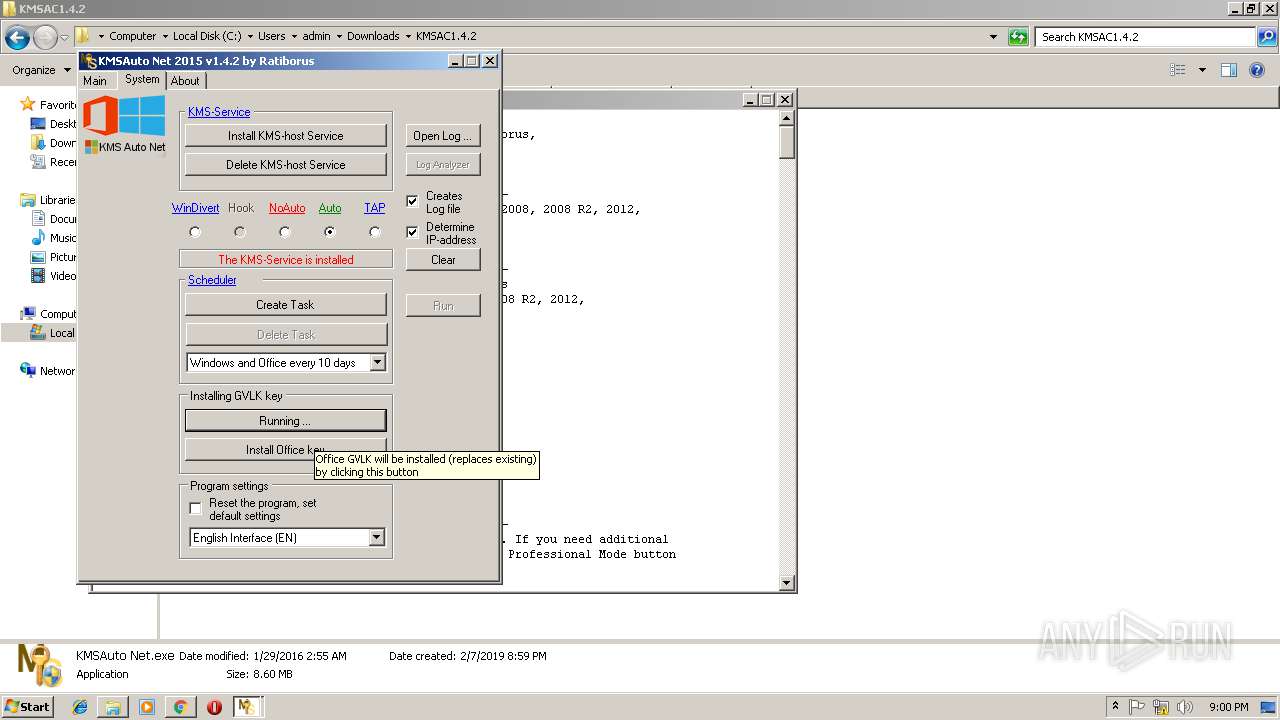
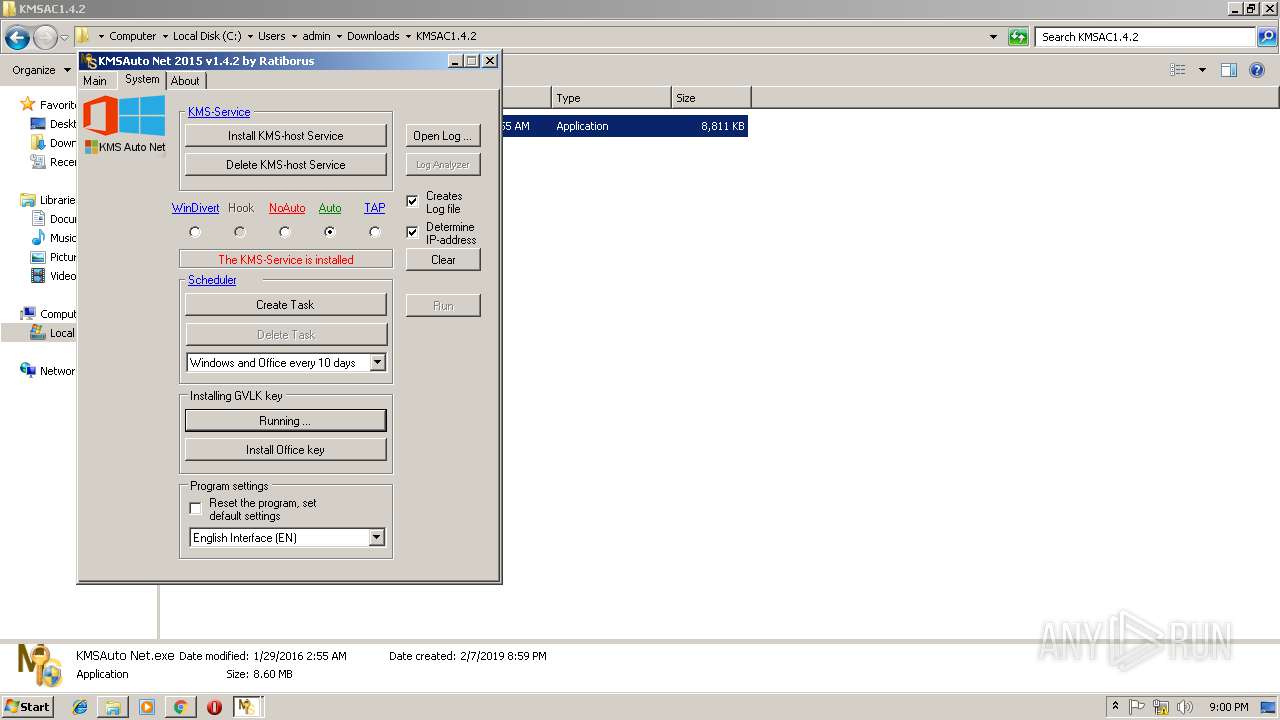
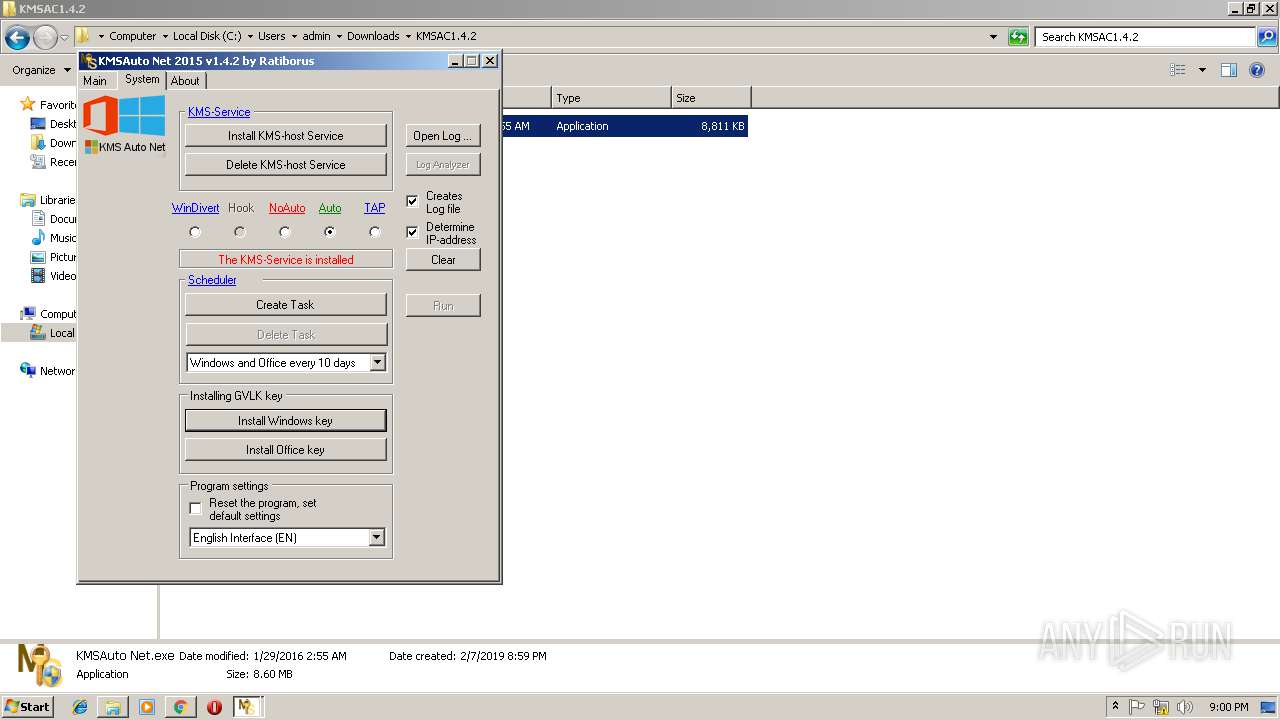
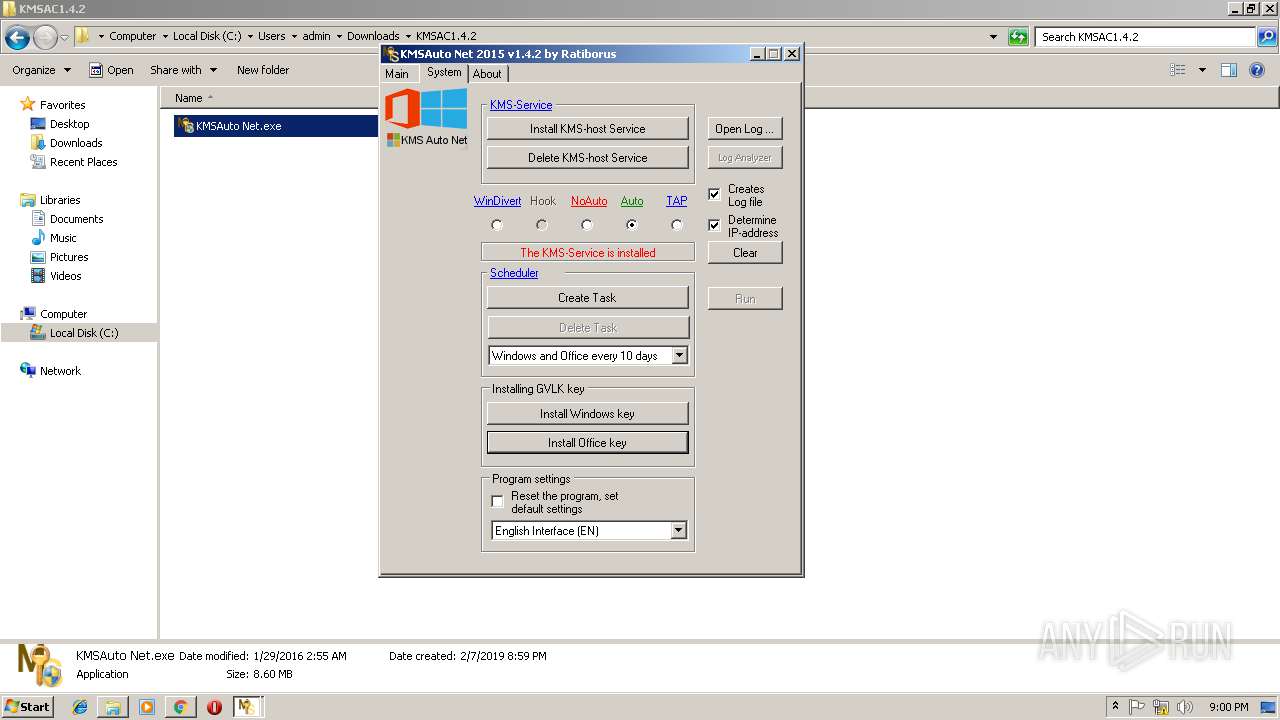
MALICIOUS
Application was dropped or rewritten from another process
- KMSAuto Net.exe (PID: 2732)
- certmgr.exe (PID: 3208)
- certmgr.exe (PID: 3160)
- KMSAuto Net.exe (PID: 3236)
- AESDecoder.exe (PID: 2588)
- bin_x86.dat (PID: 2464)
- KMSSS.exe (PID: 2156)
Changes settings of System certificates
- certmgr.exe (PID: 3160)
- certmgr.exe (PID: 3208)
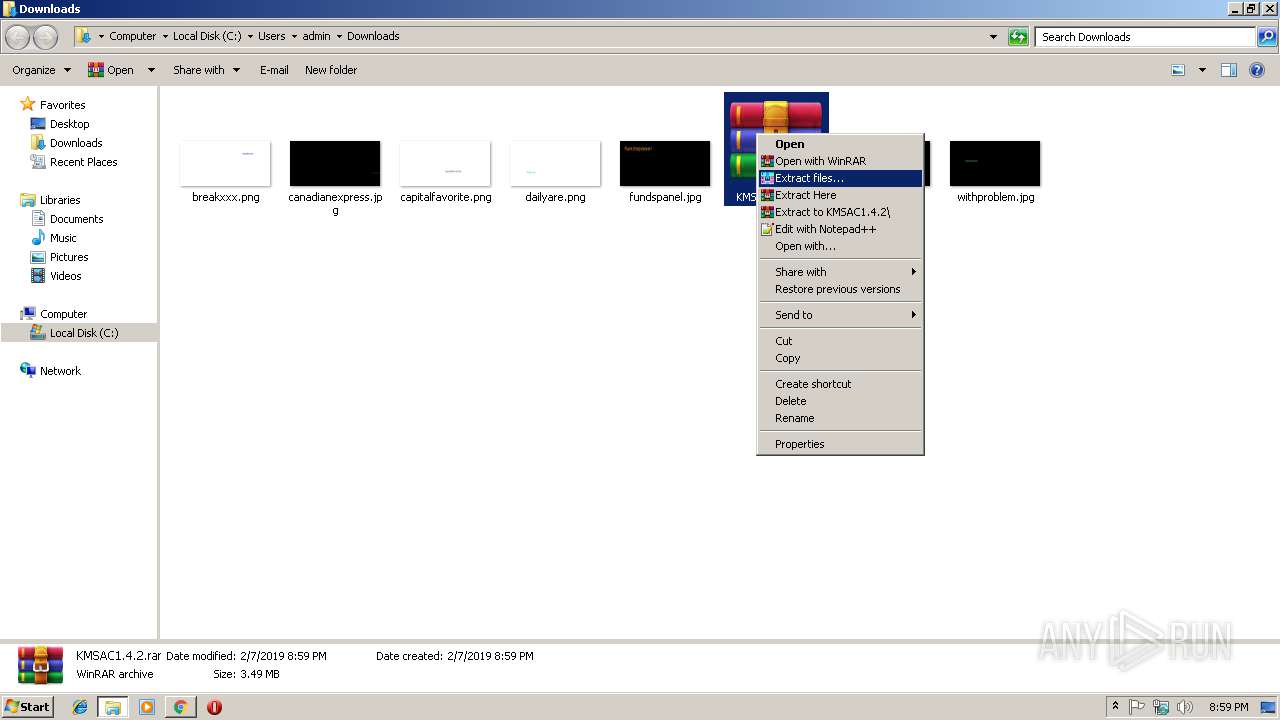
SUSPICIOUS
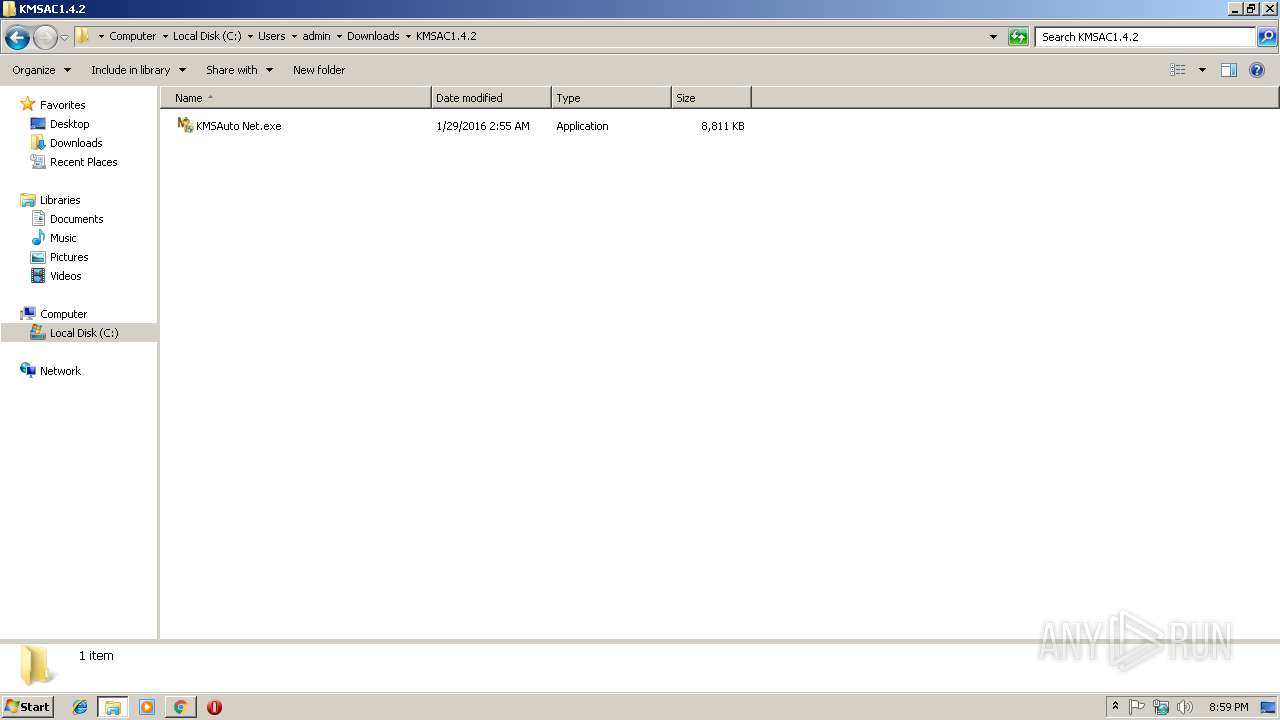
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1260)
- wzt.dat (PID: 3196)
- bin.dat (PID: 3244)
- AESDecoder.exe (PID: 2588)
- KMSAuto Net.exe (PID: 2732)
- bin_x86.dat (PID: 2464)
Creates files in the program directory
- KMSAuto Net.exe (PID: 2732)
- wzt.dat (PID: 3196)
- bin.dat (PID: 3244)
- bin_x86.dat (PID: 2464)
- AESDecoder.exe (PID: 2588)
- KMSSS.exe (PID: 2156)
Starts application with an unusual extension
- cmd.exe (PID: 2524)
- cmd.exe (PID: 2556)
- cmd.exe (PID: 3104)
Reads internet explorer settings
- KMSAuto Net.exe (PID: 2732)
Reads Environment values
- KMSAuto Net.exe (PID: 2732)
Starts CMD.EXE for commands execution
- KMSAuto Net.exe (PID: 2732)
- cmd.exe (PID: 2400)
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 2268)
Uses NETSH.EXE for network configuration
- KMSAuto Net.exe (PID: 2732)
Creates or modifies windows services
- KMSAuto Net.exe (PID: 2732)
Starts SC.EXE for service management
- KMSAuto Net.exe (PID: 2732)
Executes scripts
- KMSAuto Net.exe (PID: 2732)
INFO
Application launched itself
- chrome.exe (PID: 2852)
Reads settings of System Certificates
- chrome.exe (PID: 2852)
Reads Internet Cache Settings
- chrome.exe (PID: 2852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
105
Monitored processes
44
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | C:\Windows\System32\cmd.exe /D /c del /F /Q "AESDecoder.exe" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
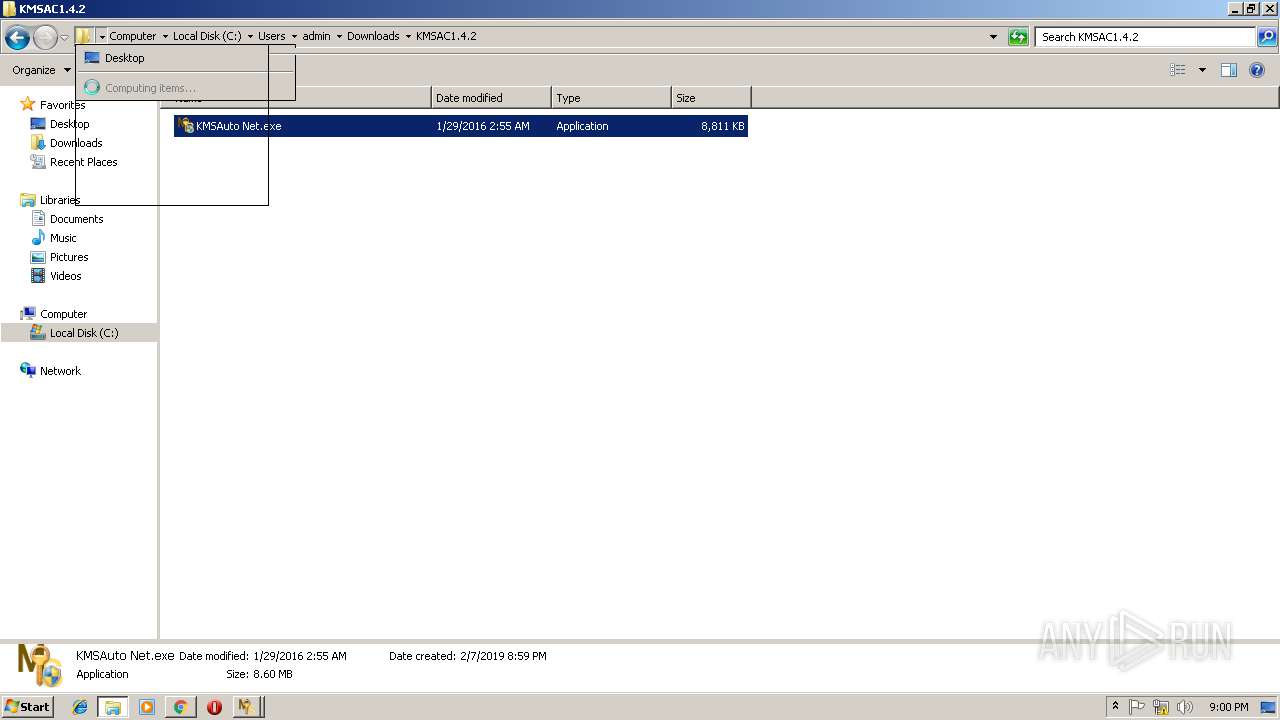
| 1260 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\KMSAC1.4.2.rar" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1E5ABBD55162287DE4A35D9E59AB85BD --mojo-platform-channel-handle=2312 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2156 | "C:\ProgramData\KMSAuto\bin\KMSSS.exe" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -AI 43200 -RI 43200 KillProcessOnPort -Log -IP | C:\ProgramData\KMSAuto\bin\KMSSS.exe | — | services.exe | |||||||||||
User: SYSTEM Company: MDL Forum, mod by Ratiborus Integrity Level: SYSTEM Description: KMS Server Emulator Service (XP) Exit code: 0 Version: 1.2.1.0 Modules
| |||||||||||||||
| 2188 | "sc.exe" start KMSEmulator | C:\Windows\system32\sc.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2192 | cmd /c echo test>>"C:\Users\admin\Downloads\KMSAC1.4.2\test.test" | C:\Windows\system32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2232 | C:\Windows\System32\Netsh Advfirewall Firewall delete rule name="0pen Port KMS" protocol=TCP | C:\Windows\System32\Netsh.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2268 | C:\Windows\system32\cmd.exe /c netstat -ano | find ":1688 " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --service-pipe-token=6594FA022F0CF9BA49D6BA57F21202F0 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6594FA022F0CF9BA49D6BA57F21202F0 --renderer-client-id=4 --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2400 | C:\Windows\System32\cmd.exe /D /c for /f "tokens=5 delims=, " %i in ('netstat -ano ^| find ":1688 "') do taskkill /pid %i /f | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
885
Read events
718
Write events
164
Delete events
3
Modification events
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2852-13194046743293250 |
Value: 259 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2852-13194046743293250 |
Value: 259 | |||
Executable files
16
Suspicious files
22
Text files
68
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\457d2044-762c-4a72-aa94-bb3520782cc4.tmp | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8af63905-3ee7-4449-811b-5dbf3055d9c2.tmp | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF246be9.TMP | text | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF246c38.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
27
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2852 | chrome.exe | GET | — | 67.23.239.31:80 | http://megatutospc.org/favicon.ico | US | — | — | whitelisted |
2852 | chrome.exe | GET | 200 | 67.23.239.31:80 | http://megatutospc.org/download/?file=KMSAC1.4.2.rar | US | html | 2.63 Kb | whitelisted |
2852 | chrome.exe | GET | 200 | 67.23.239.31:80 | http://megatutospc.org/download/css/style.css | US | text | 2.99 Kb | whitelisted |
2852 | chrome.exe | GET | 200 | 67.23.239.31:80 | http://megatutospc.org/download/download.php?file=KMSAC1.4.2.rar | US | text | 116 b | whitelisted |
2852 | chrome.exe | GET | 200 | 67.23.239.31:80 | http://megatutospc.org/download/img/region.png | US | image | 22.4 Kb | whitelisted |
2852 | chrome.exe | GET | 200 | 67.23.239.31:80 | http://megatutospc.org/download/img/winrar.png | US | image | 1.23 Mb | whitelisted |
2852 | chrome.exe | GET | 200 | 67.23.239.31:80 | http://megatutospc.org/download/img/seguro.png | US | image | 9.62 Kb | whitelisted |
2852 | chrome.exe | GET | 200 | 67.23.239.31:80 | http://megatutospc.org/download/img/logo.png | US | image | 4.58 Kb | whitelisted |
2852 | chrome.exe | GET | 200 | 216.58.207.66:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 29.4 Kb | whitelisted |
2852 | chrome.exe | GET | 200 | 67.23.239.31:80 | http://megatutospc.org/download/img/file.png | US | image | 4.45 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2852 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2852 | chrome.exe | 67.23.239.31:80 | megatutospc.org | HostDime.com, Inc. | US | unknown |
2852 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2852 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2852 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2852 | chrome.exe | 216.58.207.66:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2852 | chrome.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2852 | chrome.exe | 216.58.207.66:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2852 | chrome.exe | 216.58.210.2:443 | adservice.google.com | Google Inc. | US | whitelisted |
2852 | chrome.exe | 172.217.22.66:443 | adservice.google.ae | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
megatutospc.org |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
bit.ly |
| shared |
cookieinfoscript.com |
| whitelisted |
instagram.com |
| whitelisted |