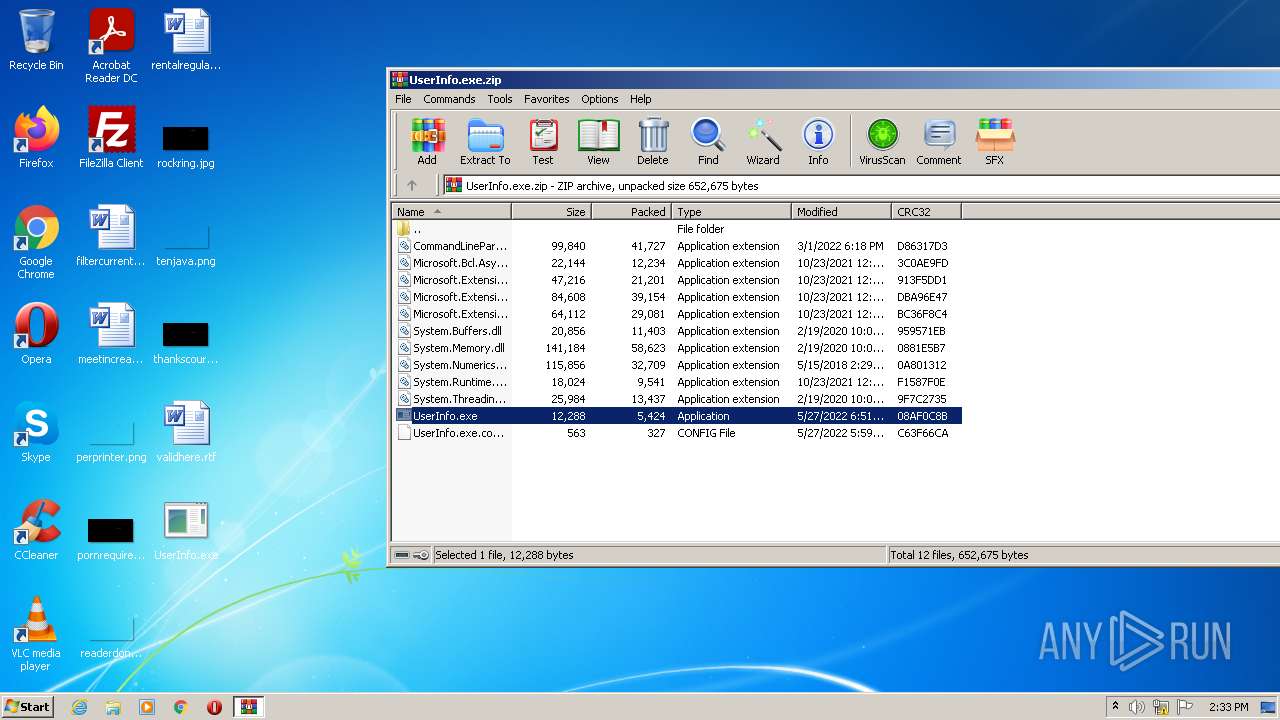
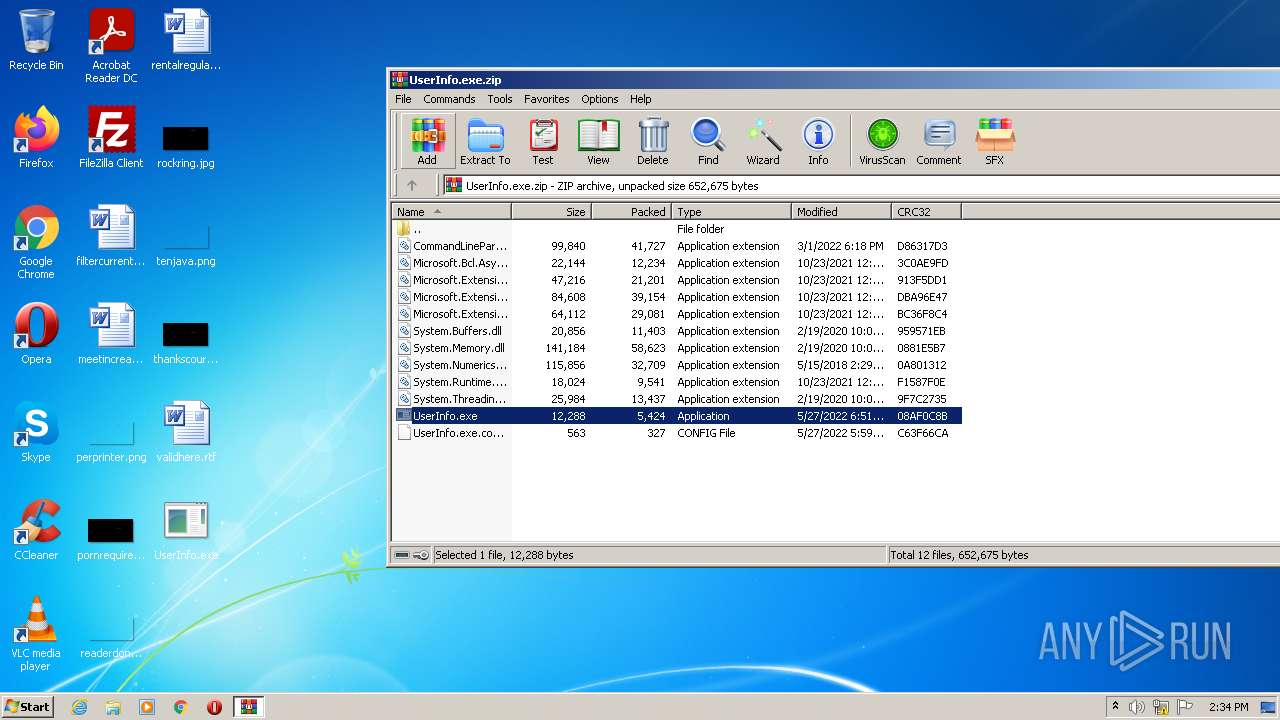
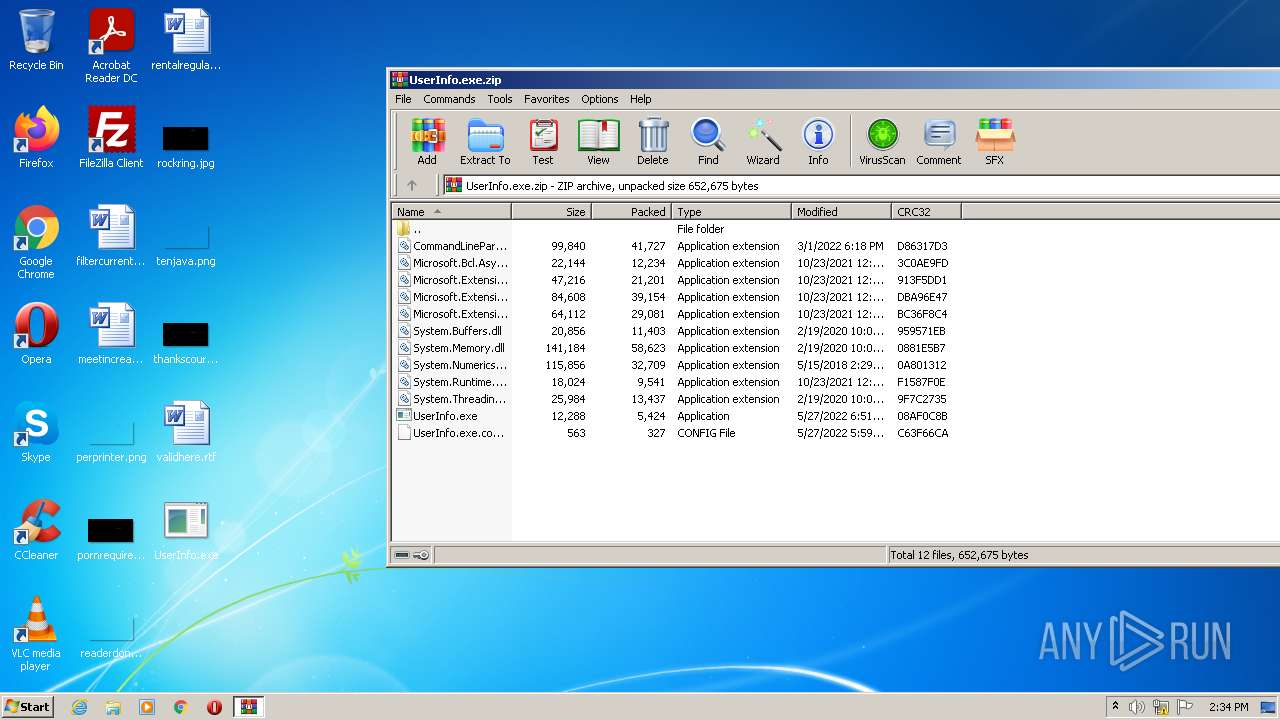
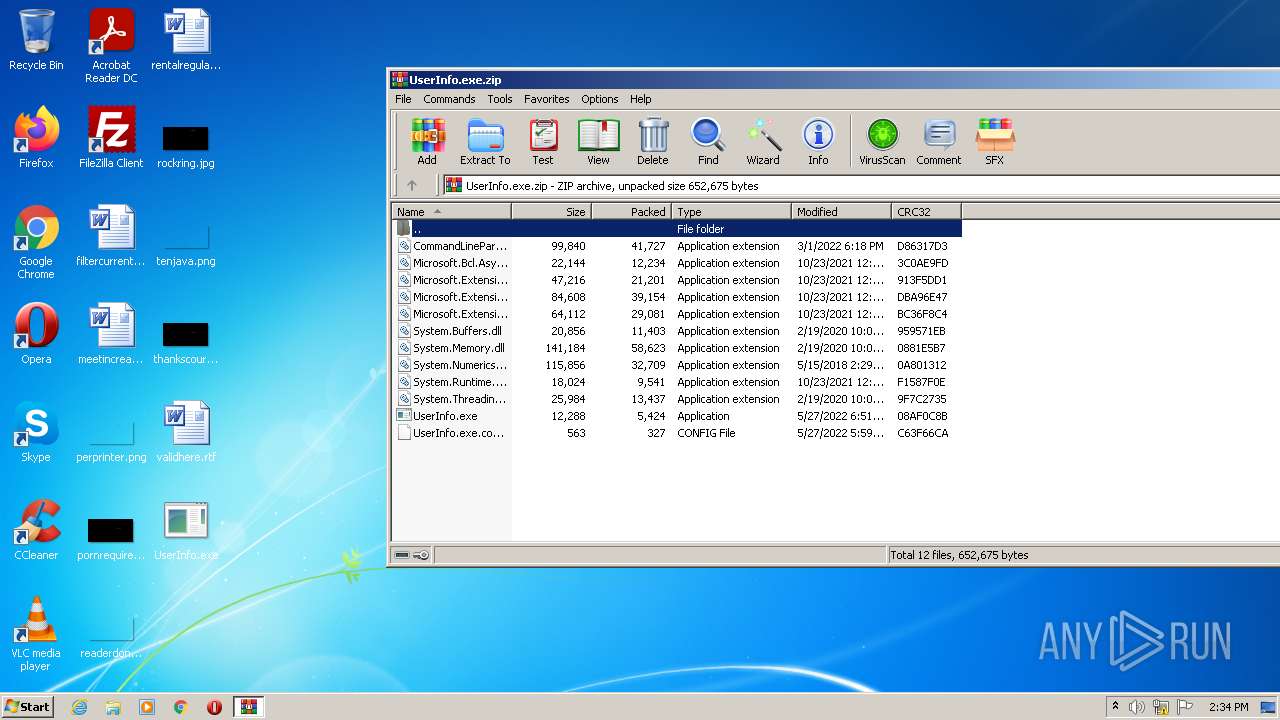
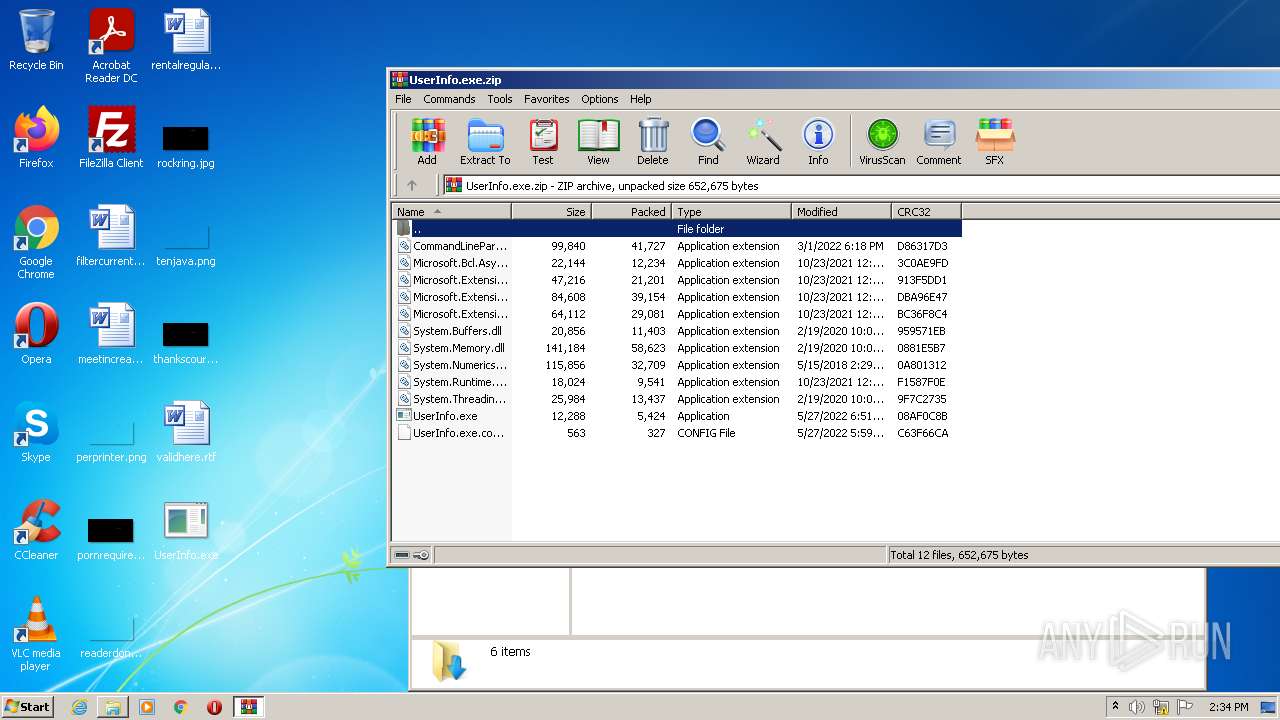
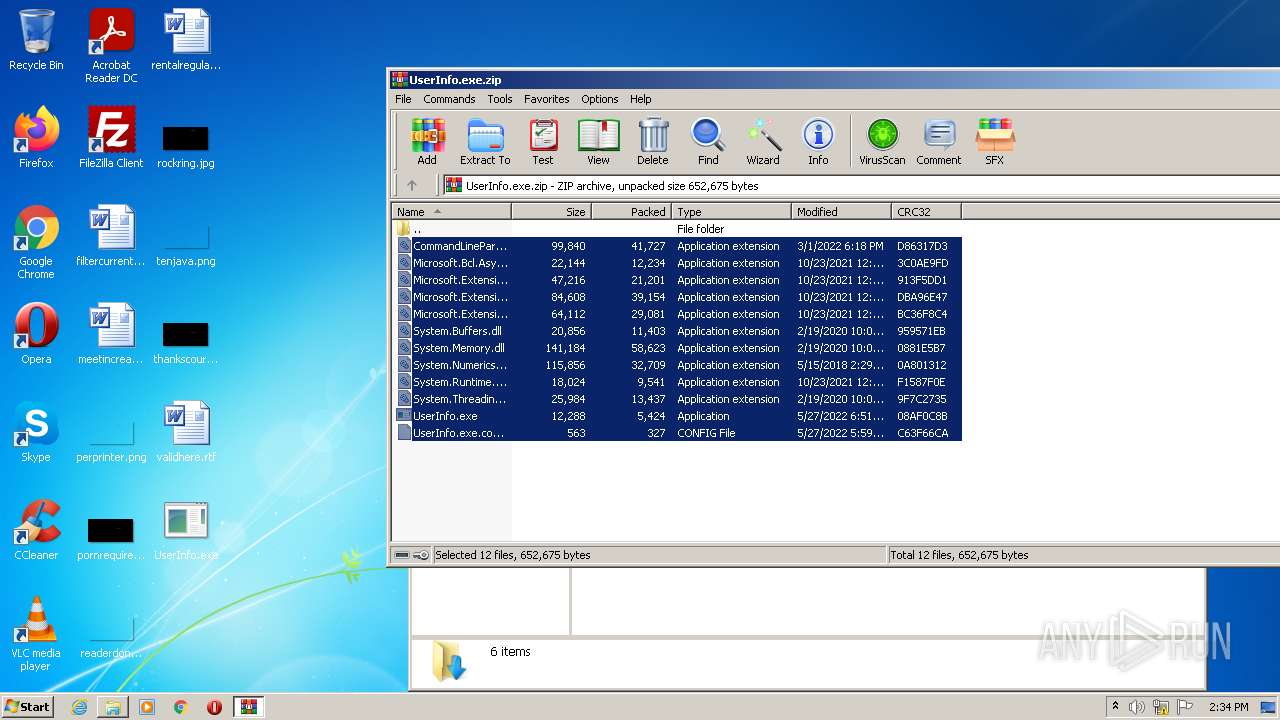
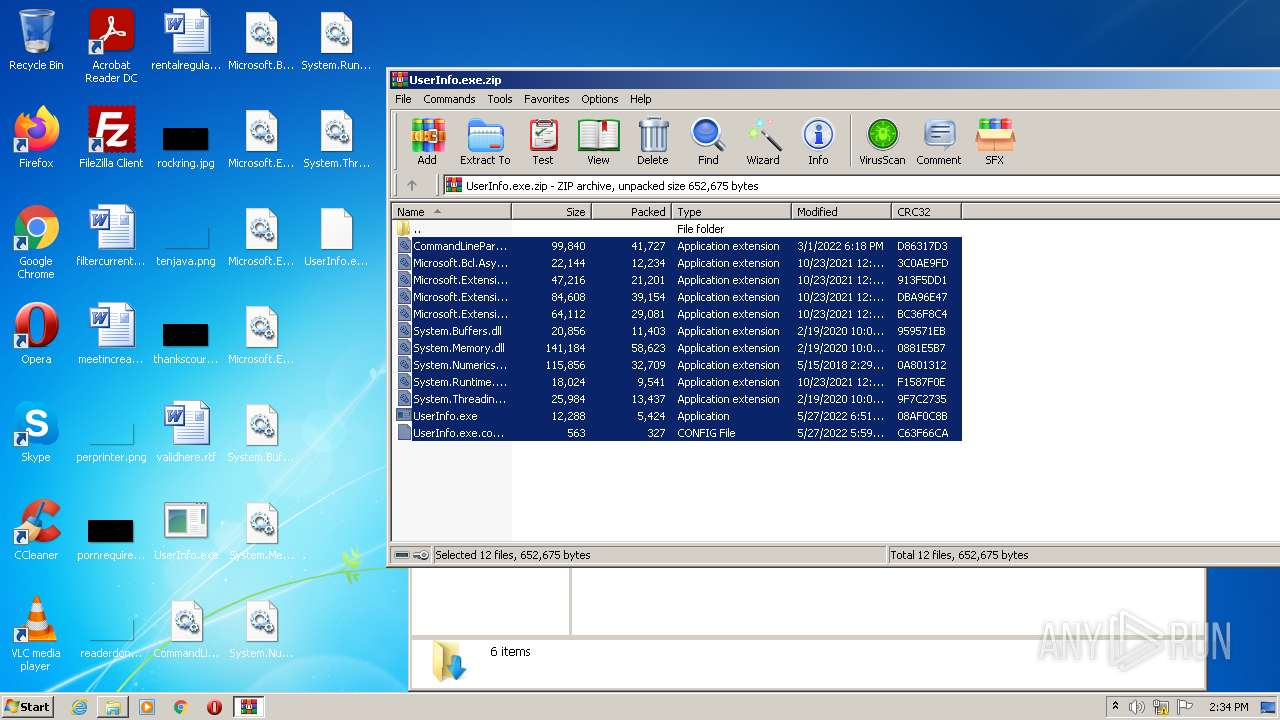
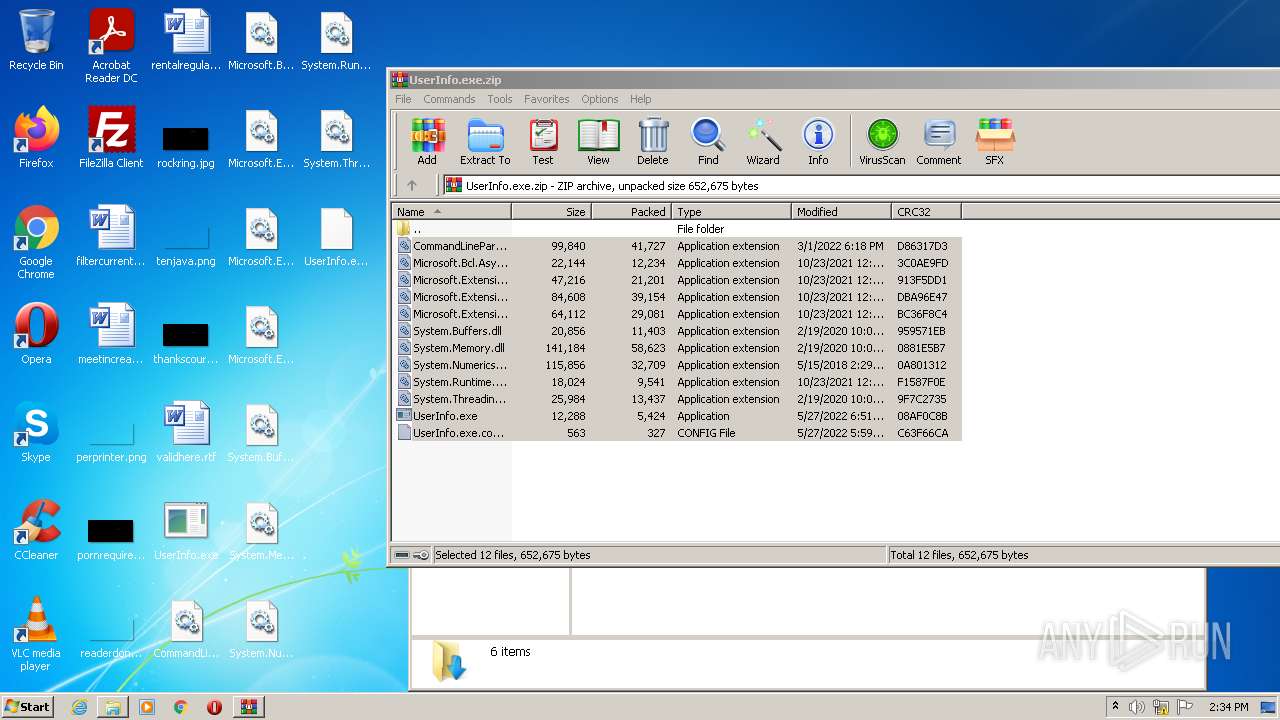
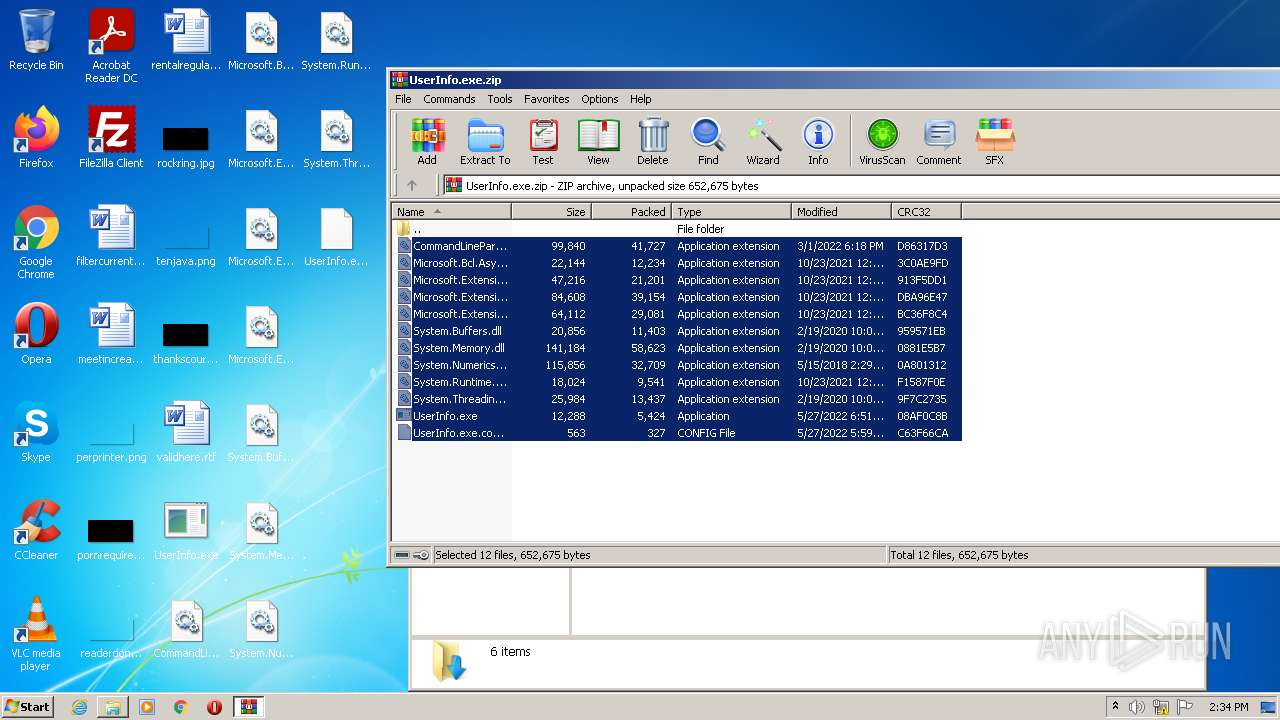
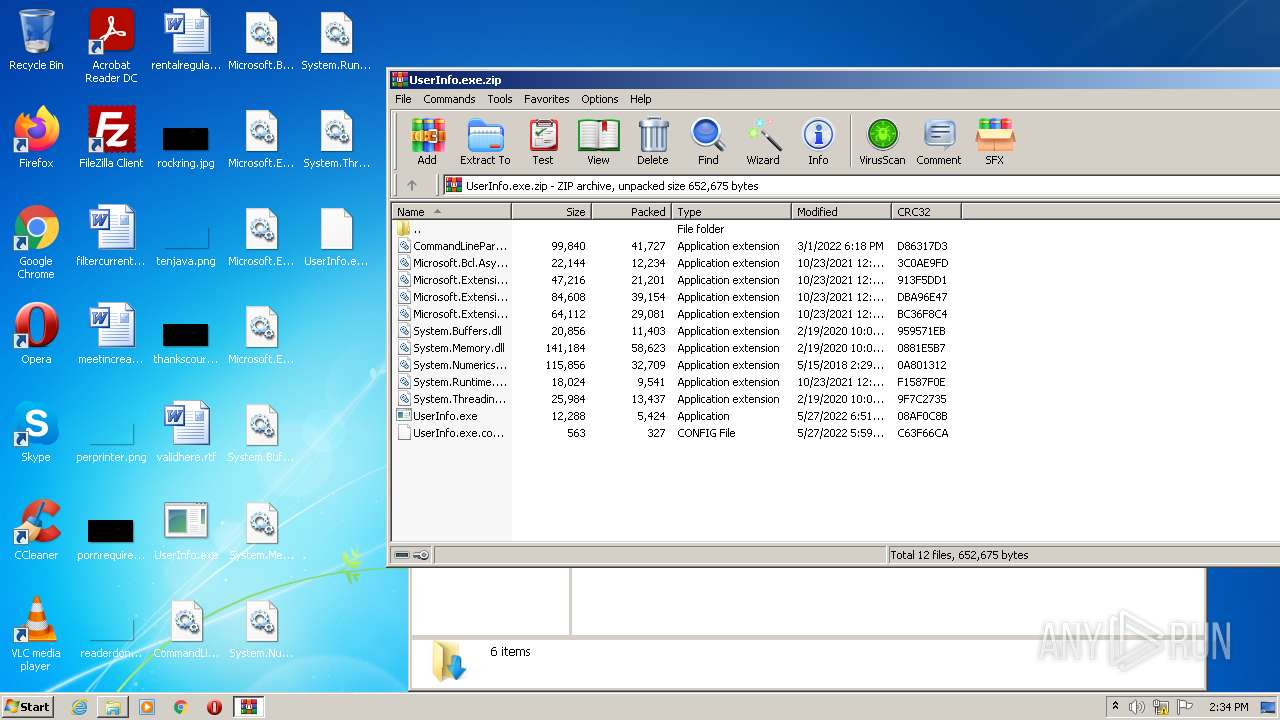
| File name: | UserInfo.exe.zip |
| Full analysis: | https://app.any.run/tasks/17d76e22-631e-453e-9bda-94692ef0bf8b |
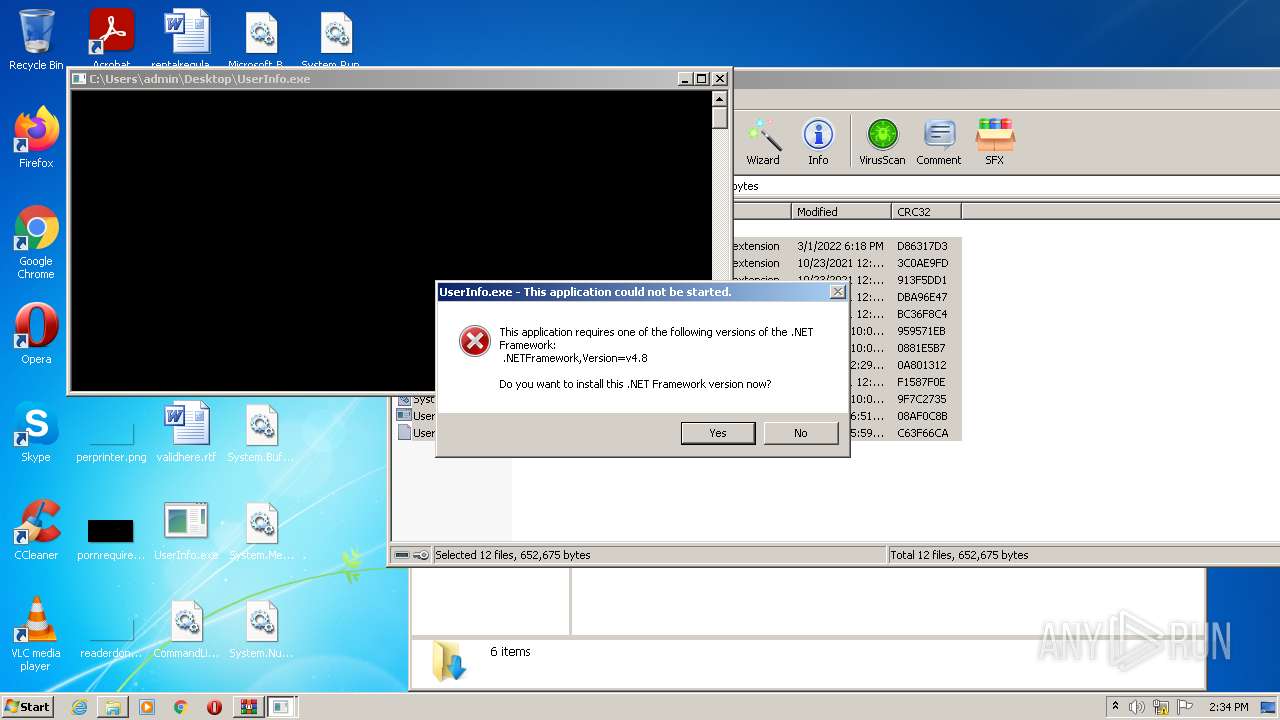
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2022, 13:32:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 6176C56FAC09669B6ACA6959DD05C4D9 |
| SHA1: | E57F5678FA75BD752608F157658CEE622006A0E6 |
| SHA256: | E070CE95A8B30E126D7AE1803EA15C5A8E7D27B13FC670B3AAA69D7026C2BC97 |
| SSDEEP: | 6144:a0aDcfilxI/pvZbMonMJd67PIQGFhIo0UeOUkMPEiWNuGMl25SIiyI+qm0Sb+TL:mhl2/pvRtMJkFGFaouOSREMl25Vb/FZo |
MALICIOUS
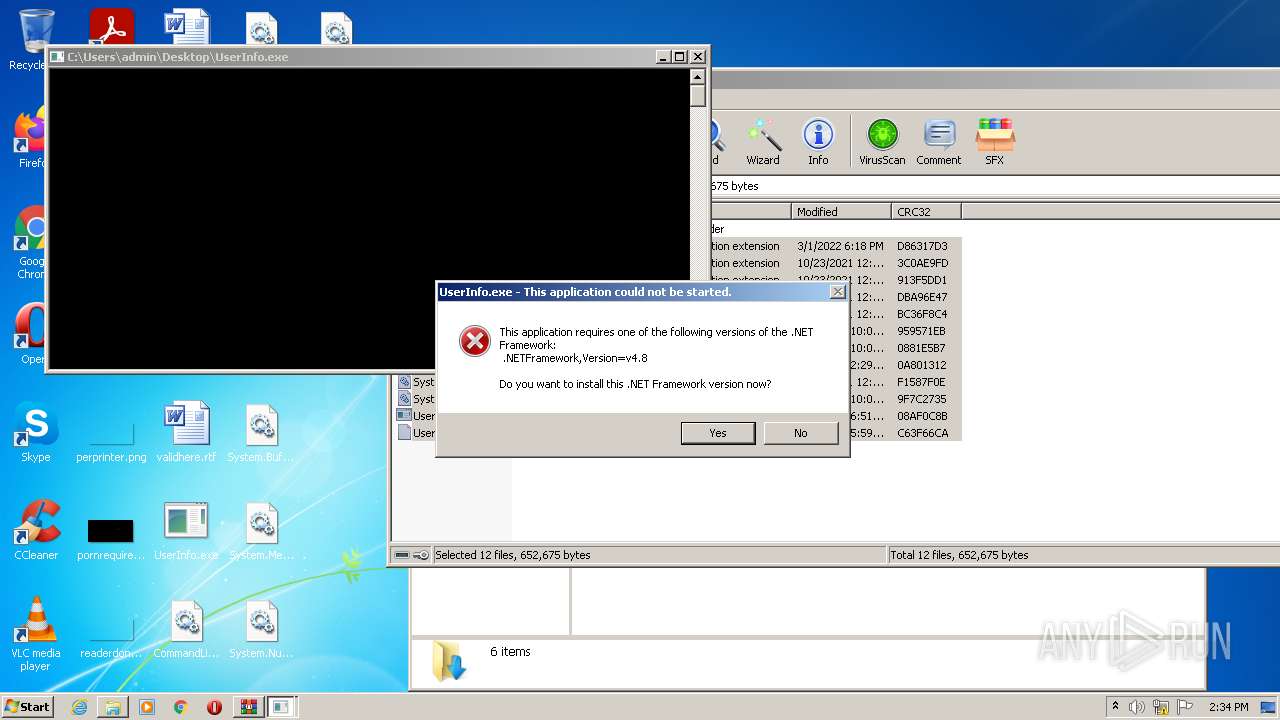
Application was dropped or rewritten from another process
- UserInfo.exe (PID: 1744)
- UserInfo.exe (PID: 1496)
- UserInfo.exe (PID: 2432)
- UserInfo.exe (PID: 3004)
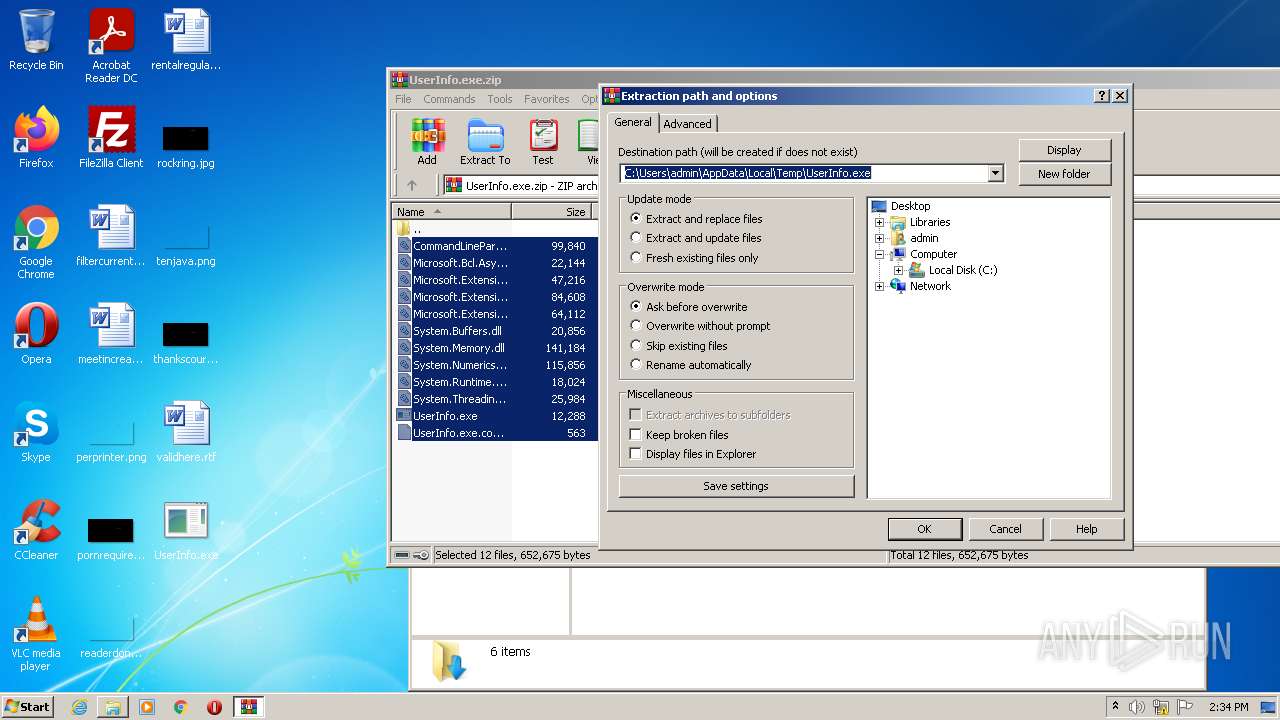
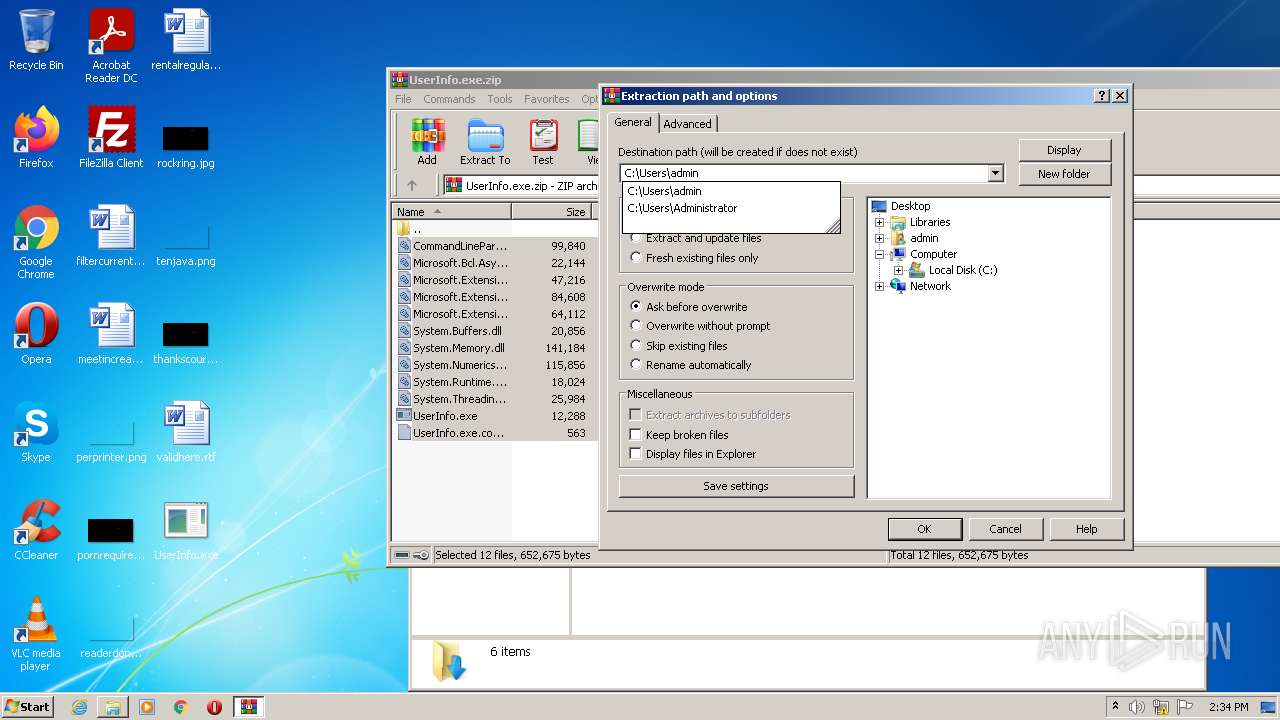
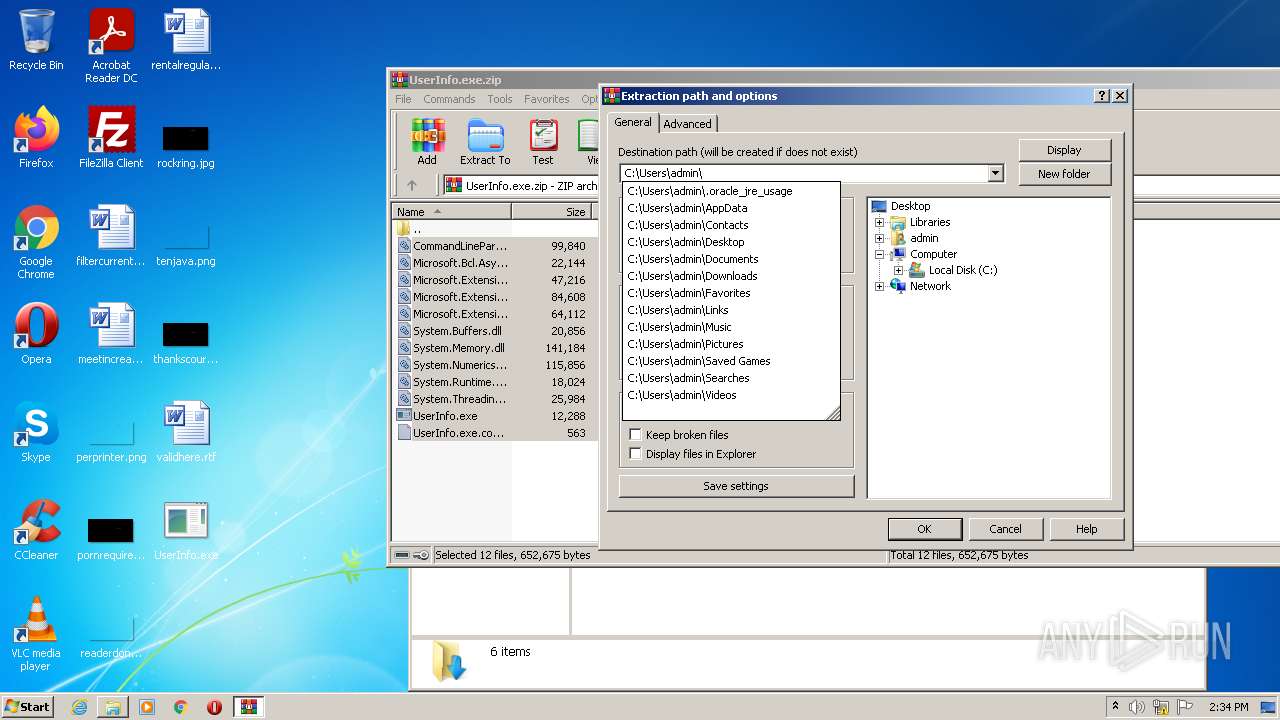
Drops executable file immediately after starts
- WinRAR.exe (PID: 2600)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2972)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2600)
- UserInfo.exe (PID: 1744)
- UserInfo.exe (PID: 1496)
- UserInfo.exe (PID: 2432)
- UserInfo.exe (PID: 3004)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2600)
Reads the computer name
- UserInfo.exe (PID: 1744)
- UserInfo.exe (PID: 1496)
- WinRAR.exe (PID: 2600)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1596)
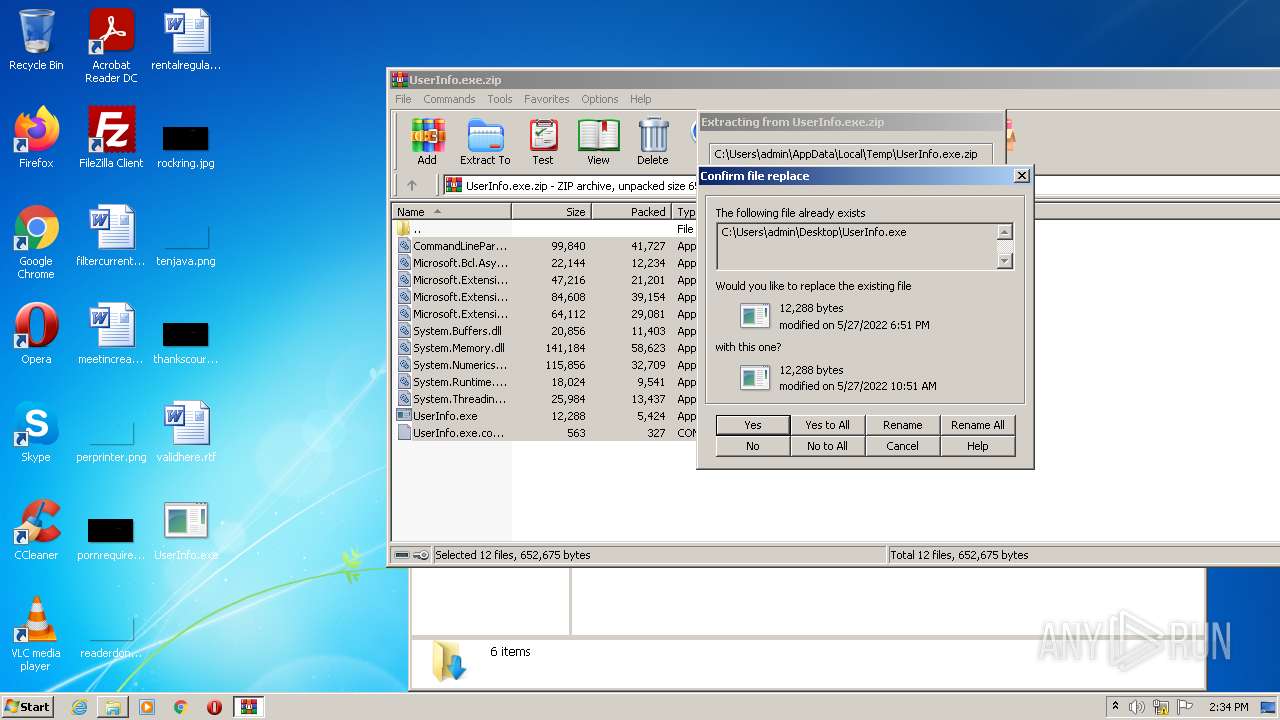
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2600)
INFO
Reads the computer name
- iexplore.exe (PID: 2124)
- iexplore.exe (PID: 1596)
- explorer.exe (PID: 2140)
Checks Windows Trust Settings
- iexplore.exe (PID: 1596)
- iexplore.exe (PID: 2124)
Checks supported languages
- iexplore.exe (PID: 2124)
- iexplore.exe (PID: 1596)
- explorer.exe (PID: 2140)
Application launched itself
- iexplore.exe (PID: 2124)
Reads settings of System Certificates
- iexplore.exe (PID: 2124)
- iexplore.exe (PID: 1596)
Changes internet zones settings
- iexplore.exe (PID: 2124)
Reads internet explorer settings
- iexplore.exe (PID: 1596)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2124)
Changes settings of System certificates
- iexplore.exe (PID: 2124)
Reads the date of Windows installation
- iexplore.exe (PID: 2124)
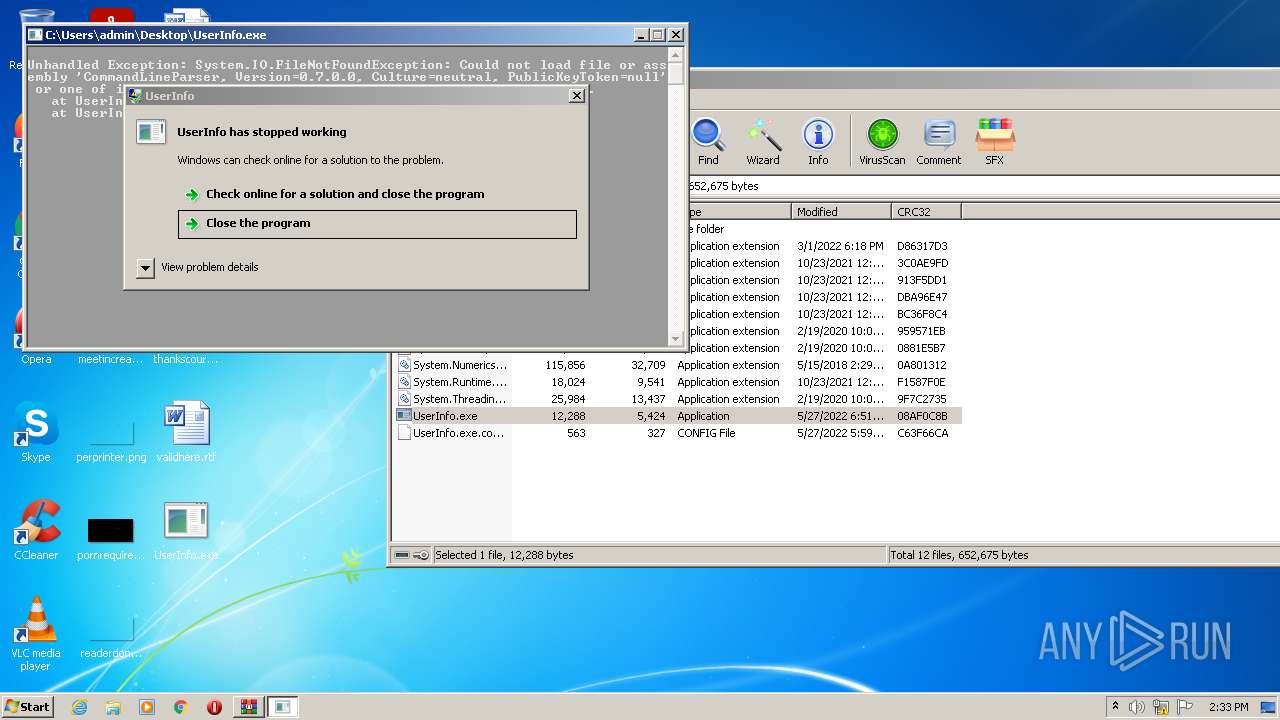
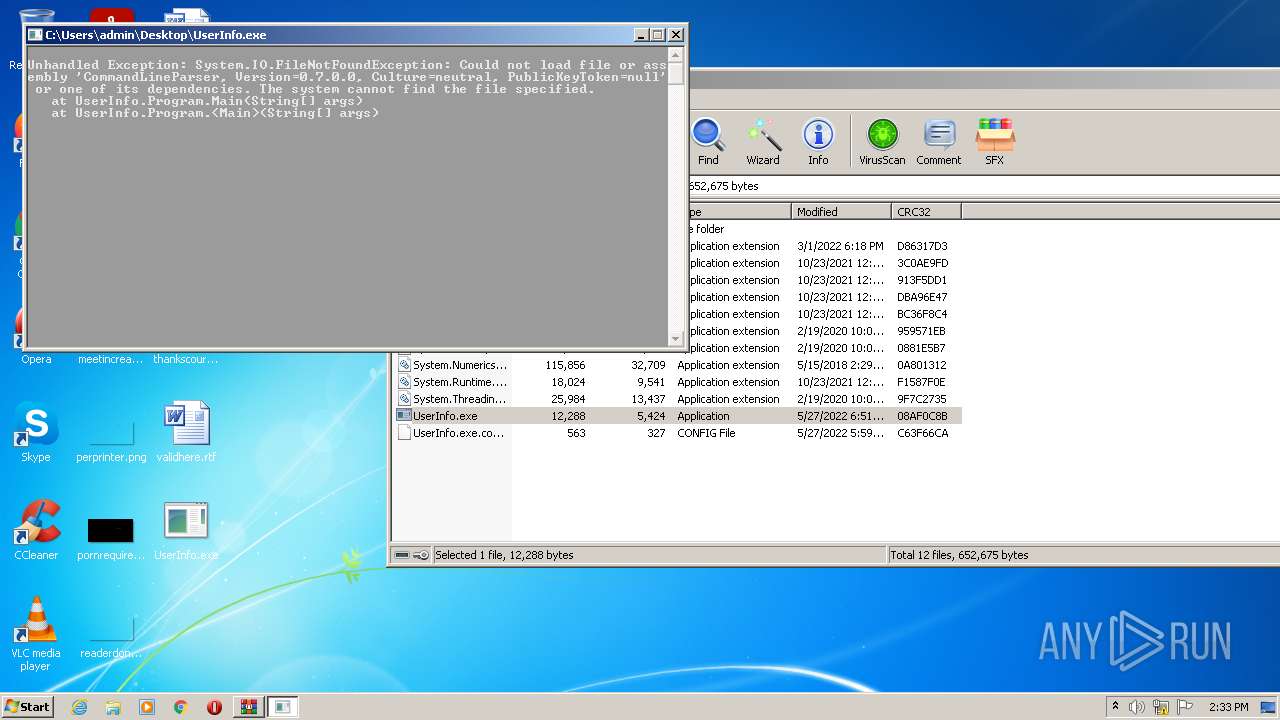
Manual execution by user
- UserInfo.exe (PID: 1496)
- explorer.exe (PID: 2140)
- UserInfo.exe (PID: 2432)
- UserInfo.exe (PID: 3004)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
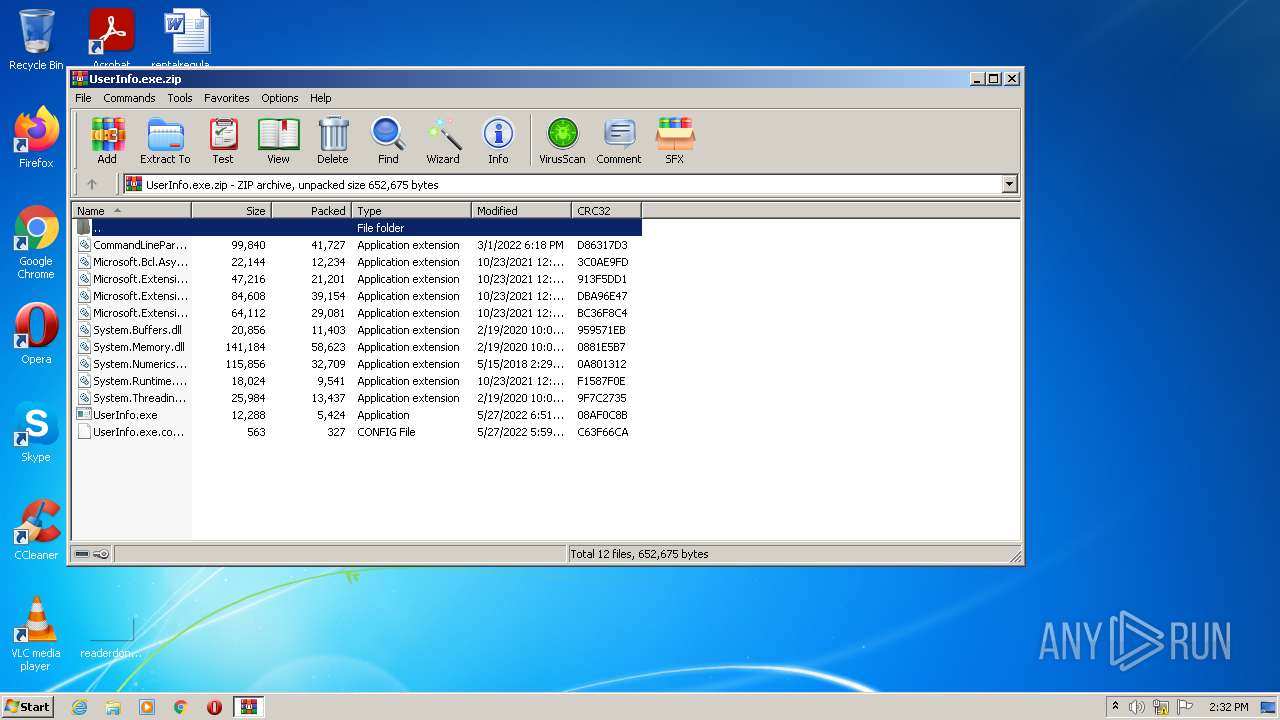
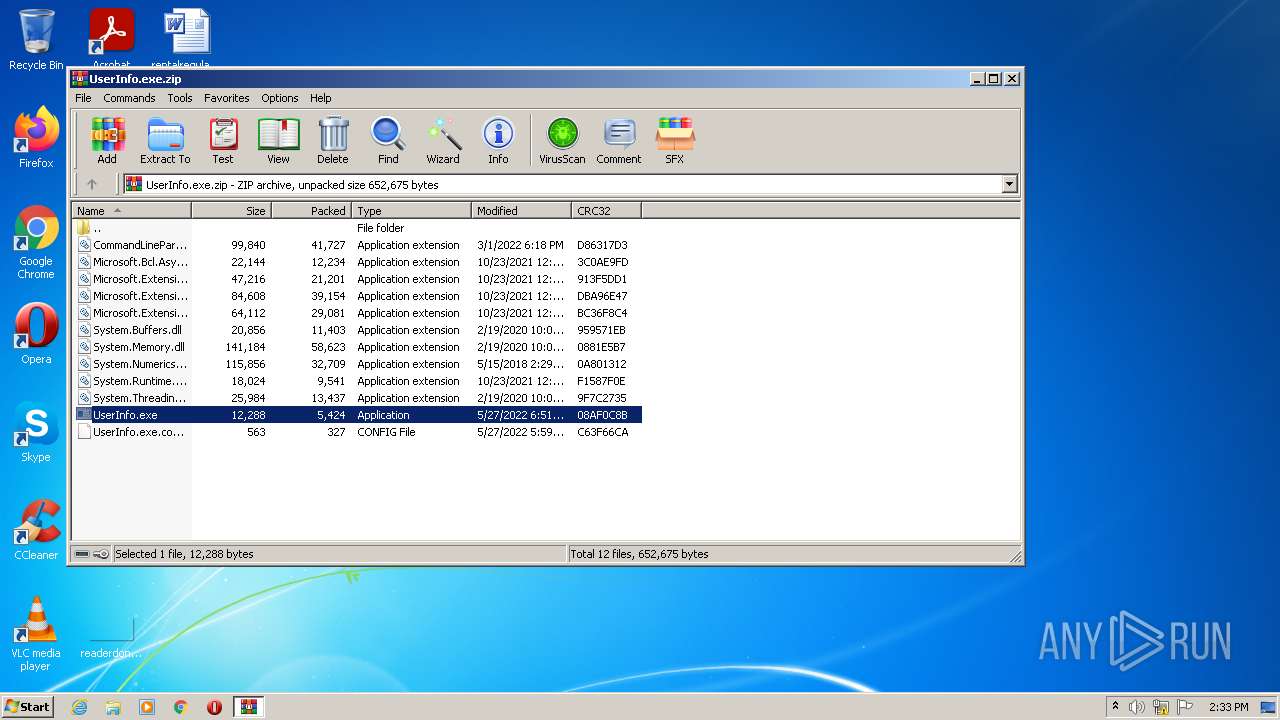
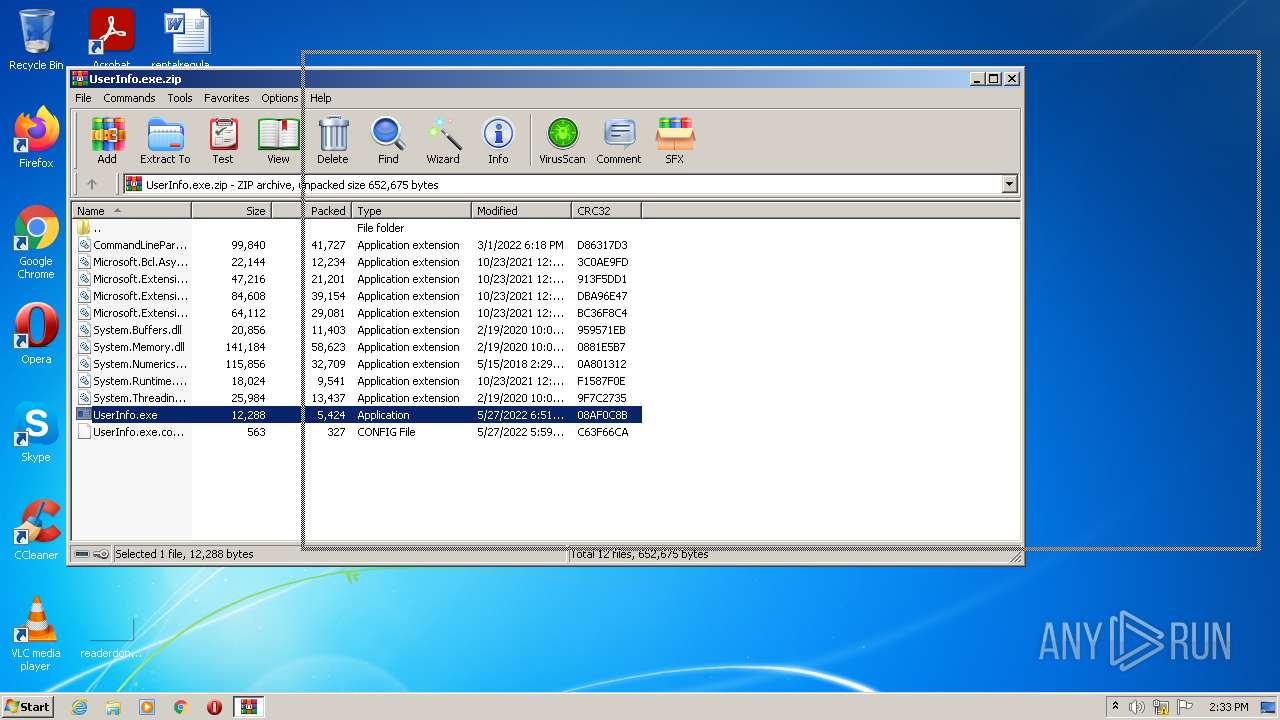
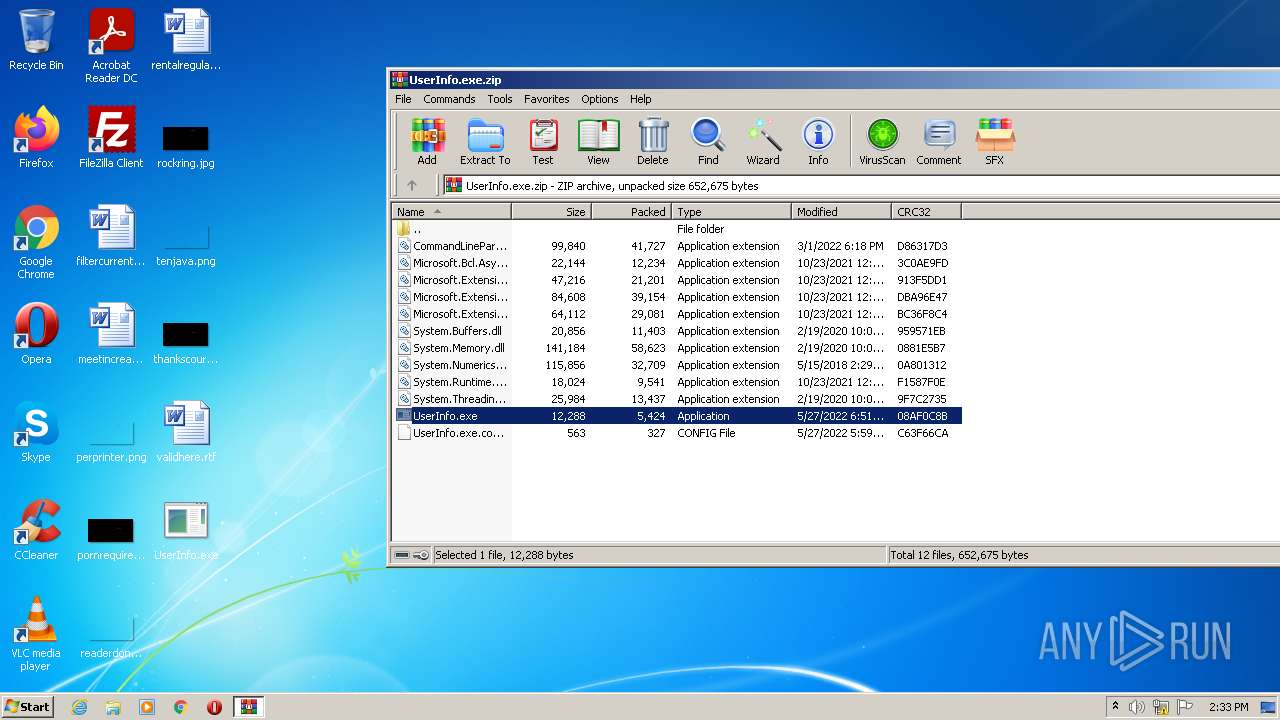
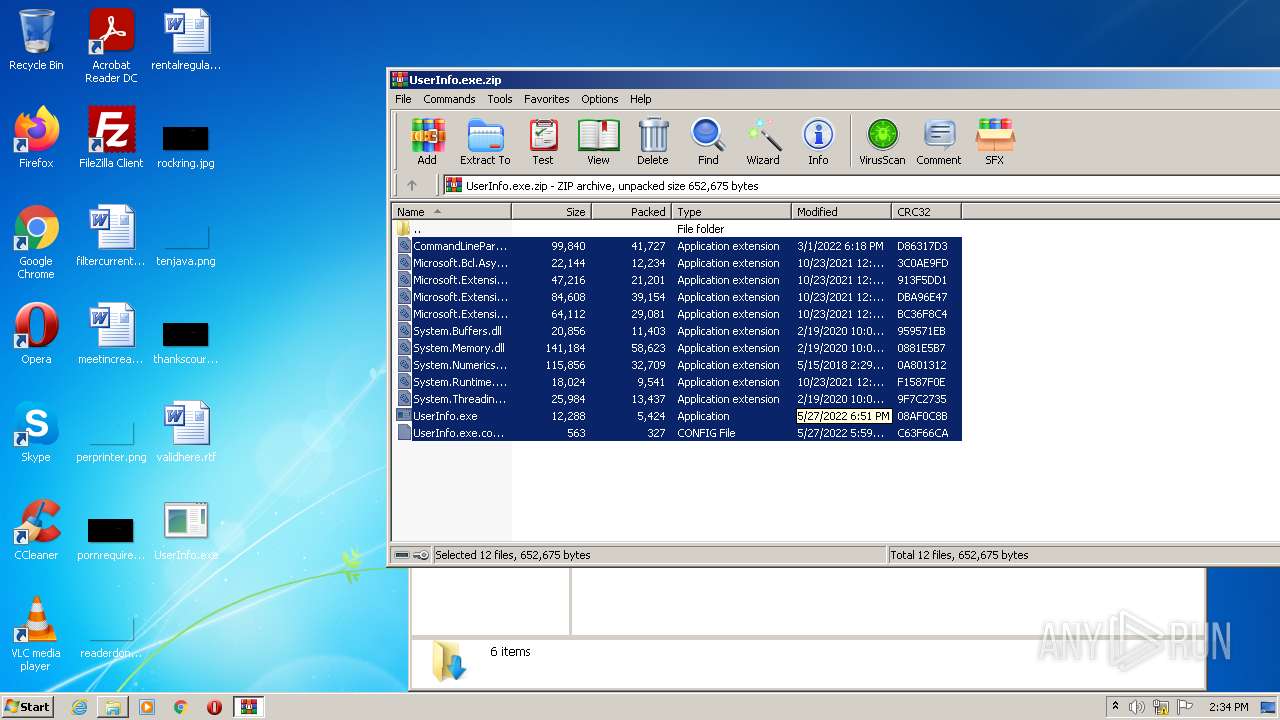
| ZipFileName: | UserInfo.exe |
|---|---|
| ZipUncompressedSize: | 12288 |
| ZipCompressedSize: | 5424 |
| ZipCRC: | 0x08af0c8b |
| ZipModifyDate: | 2022:05:27 10:51:02 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0008 |
| ZipRequiredVersion: | 20 |
Total processes
52
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
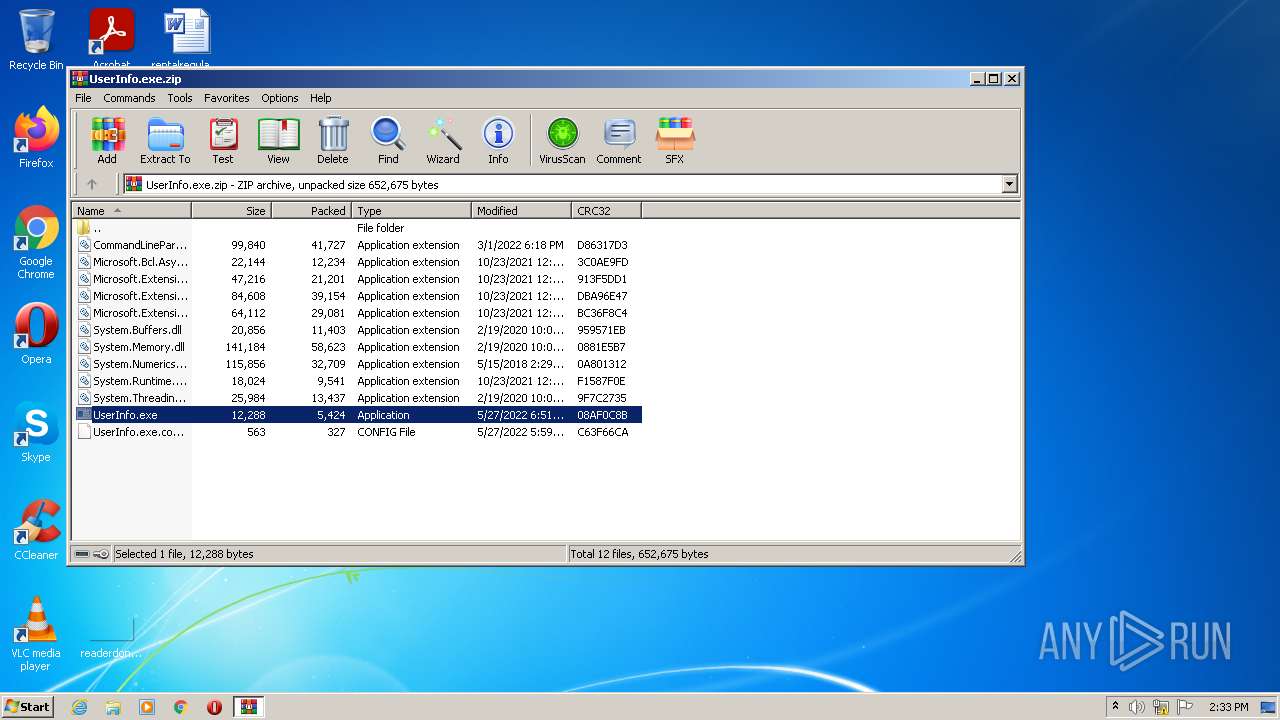
| 1496 | "C:\Users\admin\Desktop\UserInfo.exe" | C:\Users\admin\Desktop\UserInfo.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: UserInfo Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2124 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
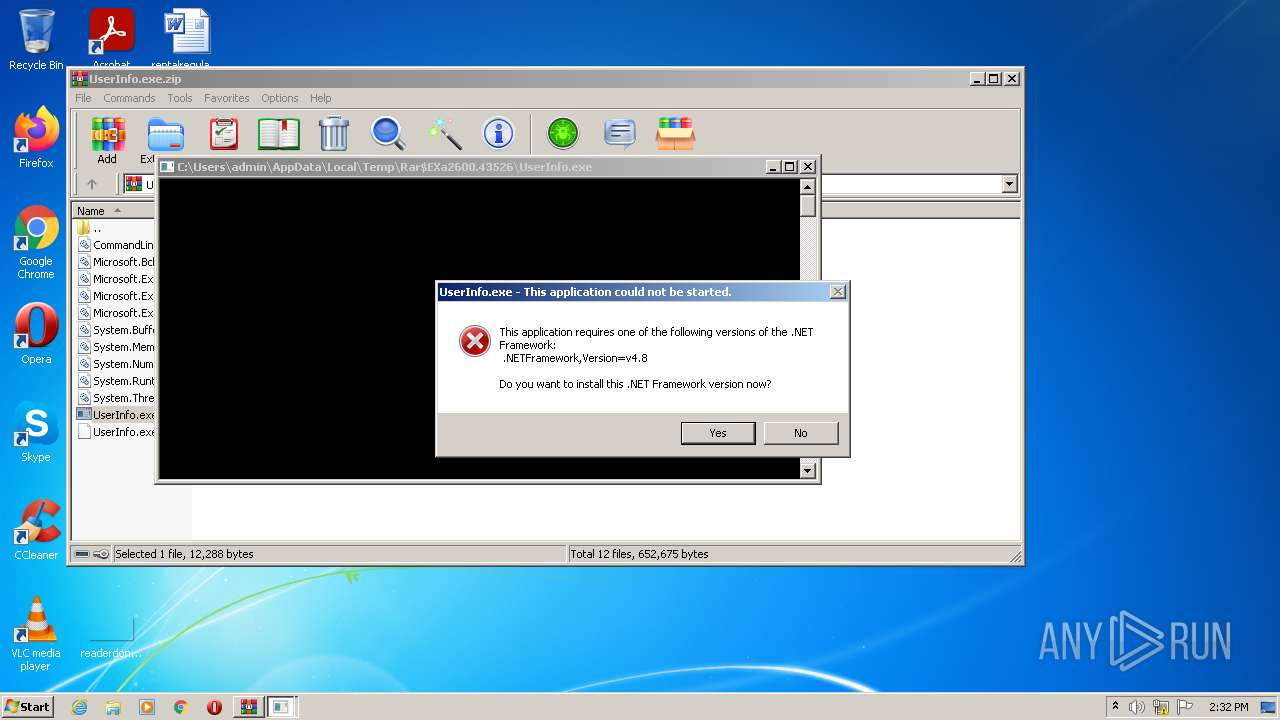
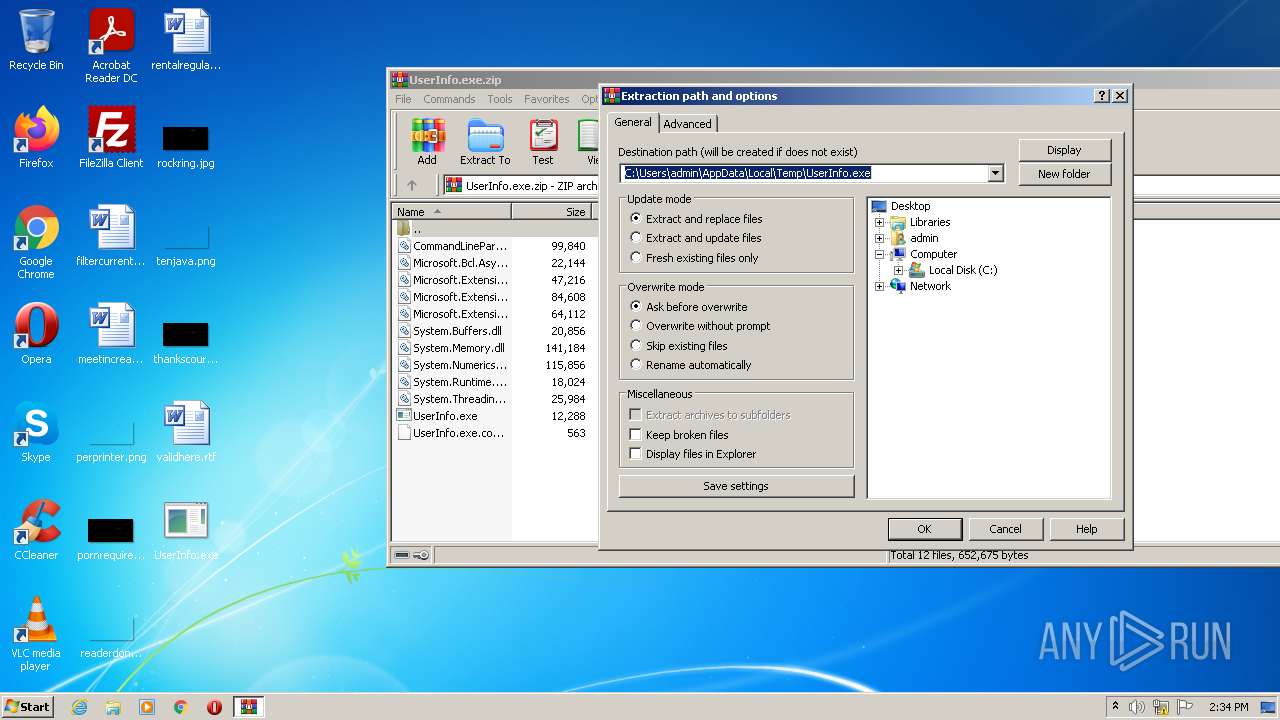
| 1744 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2600.43526\UserInfo.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2600.43526\UserInfo.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: UserInfo Exit code: 3221225547 Version: 1.0.0.0 Modules
| |||||||||||||||
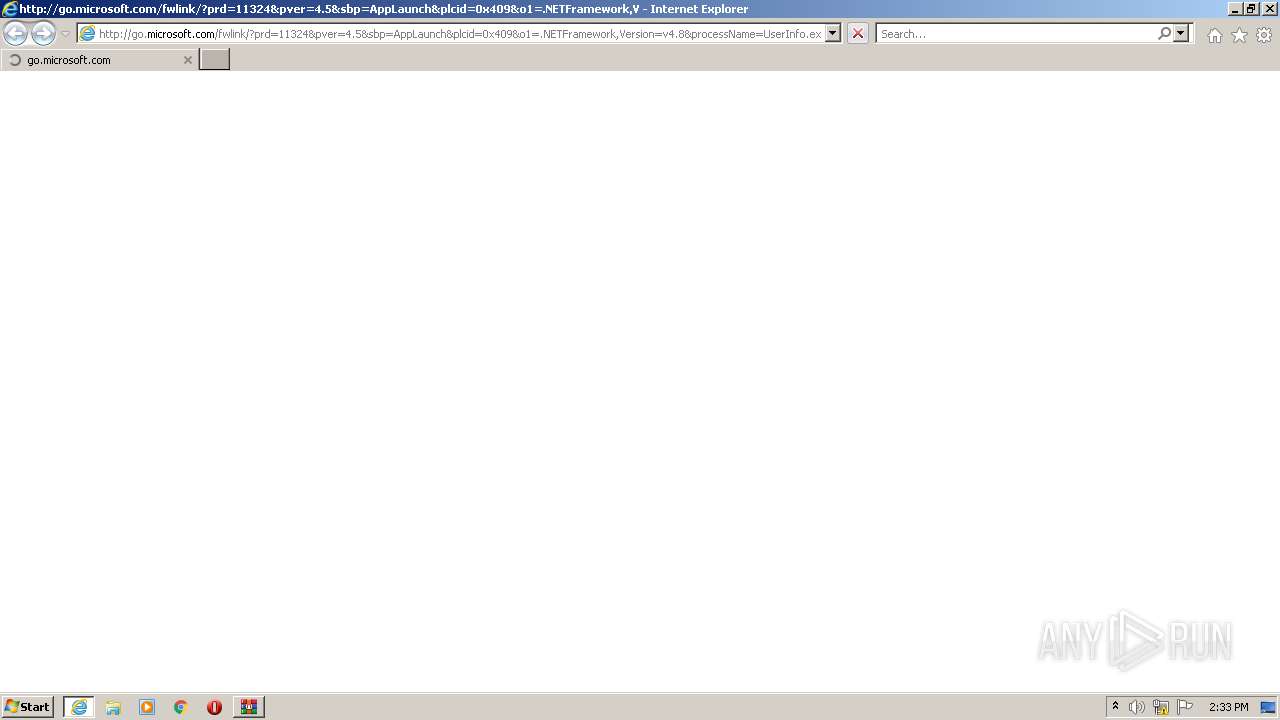
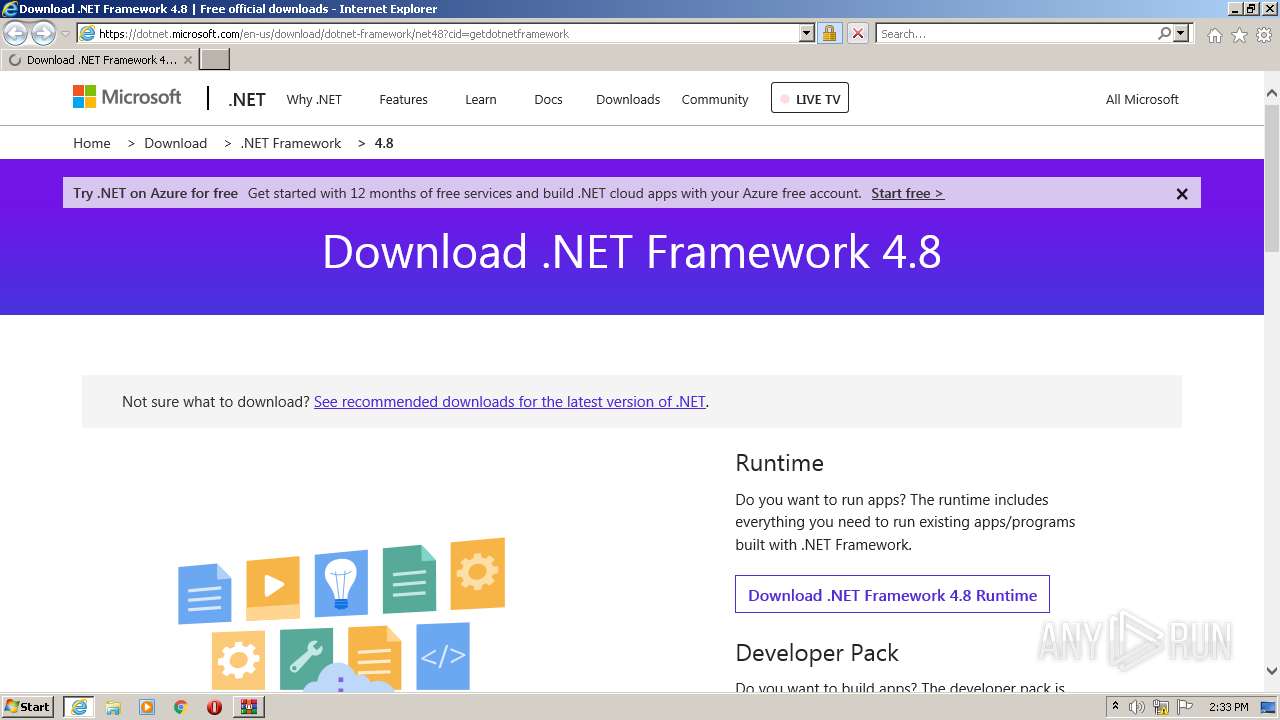
| 2124 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?prd=11324&pver=4.5&sbp=AppLaunch&plcid=0x409&o1=.NETFramework,Version=v4.8&processName=UserInfo.exe&platform=0000&osver=5&isServer=0&shimver=4.0.30319.34209 | C:\Program Files\Internet Explorer\iexplore.exe | UserInfo.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2140 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2432 | "C:\Users\admin\Desktop\UserInfo.exe" | C:\Users\admin\Desktop\UserInfo.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: UserInfo Exit code: 2148734720 Version: 1.0.0.0 Modules
| |||||||||||||||
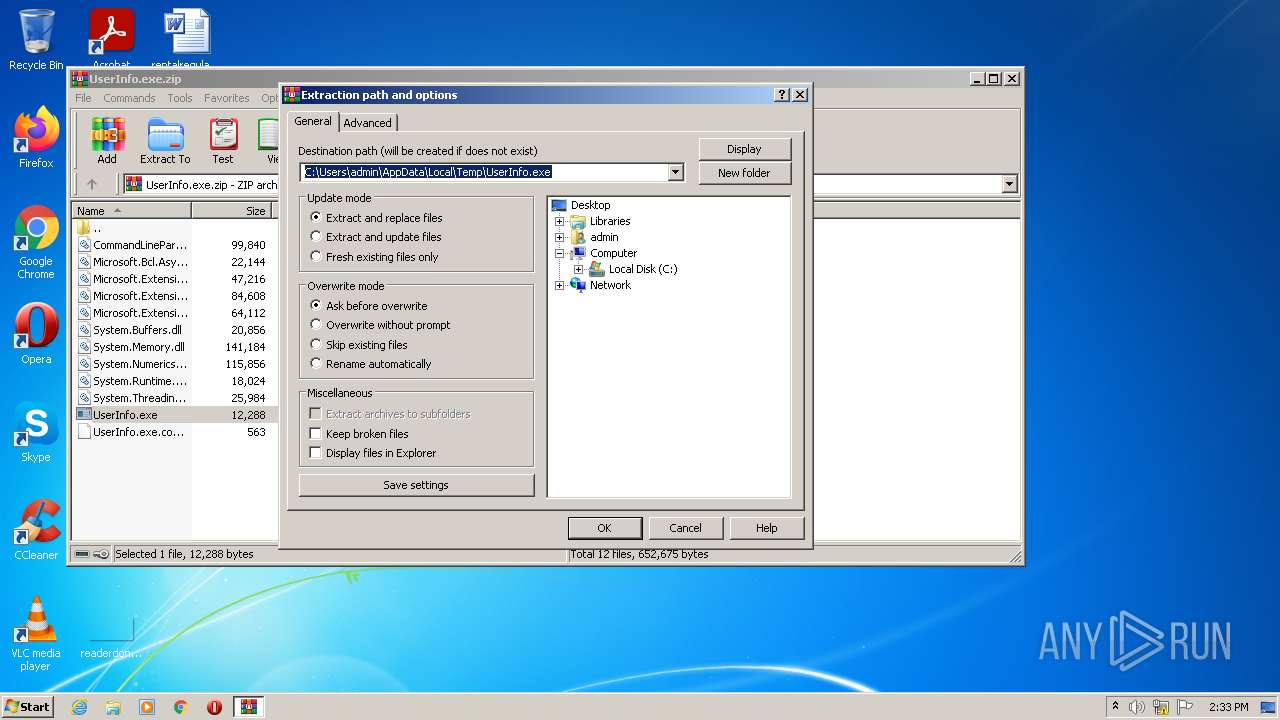
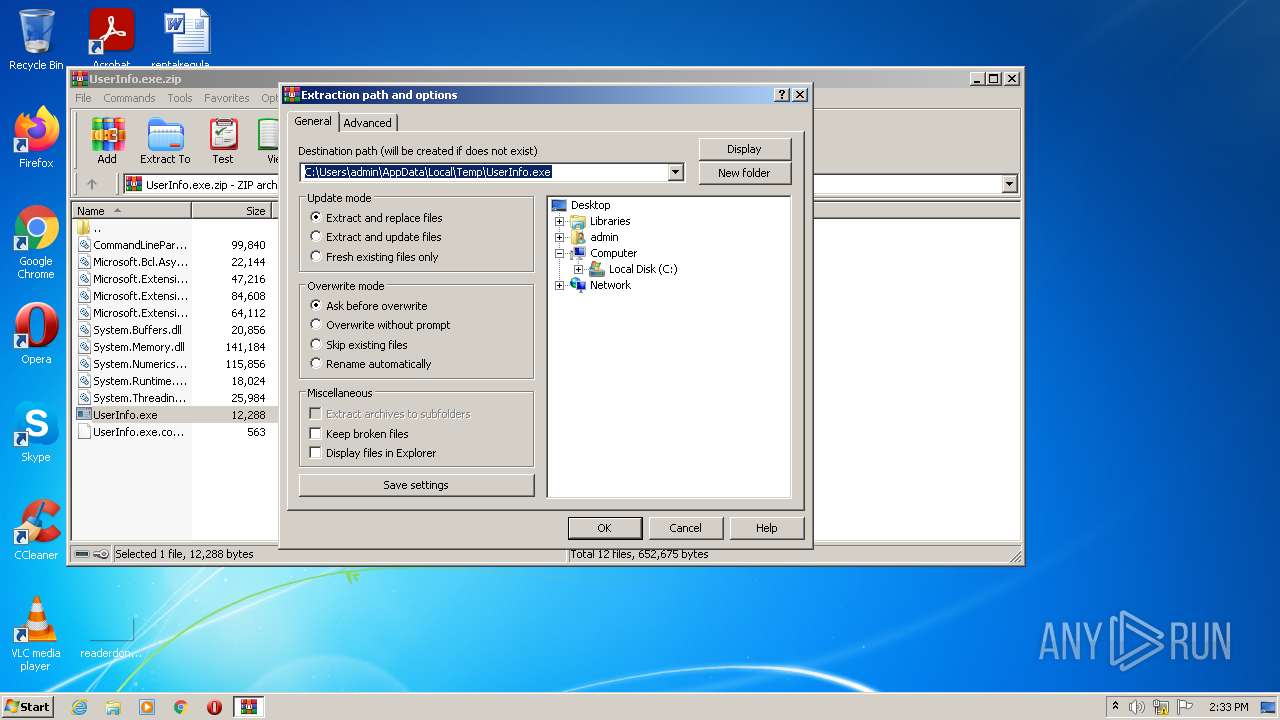
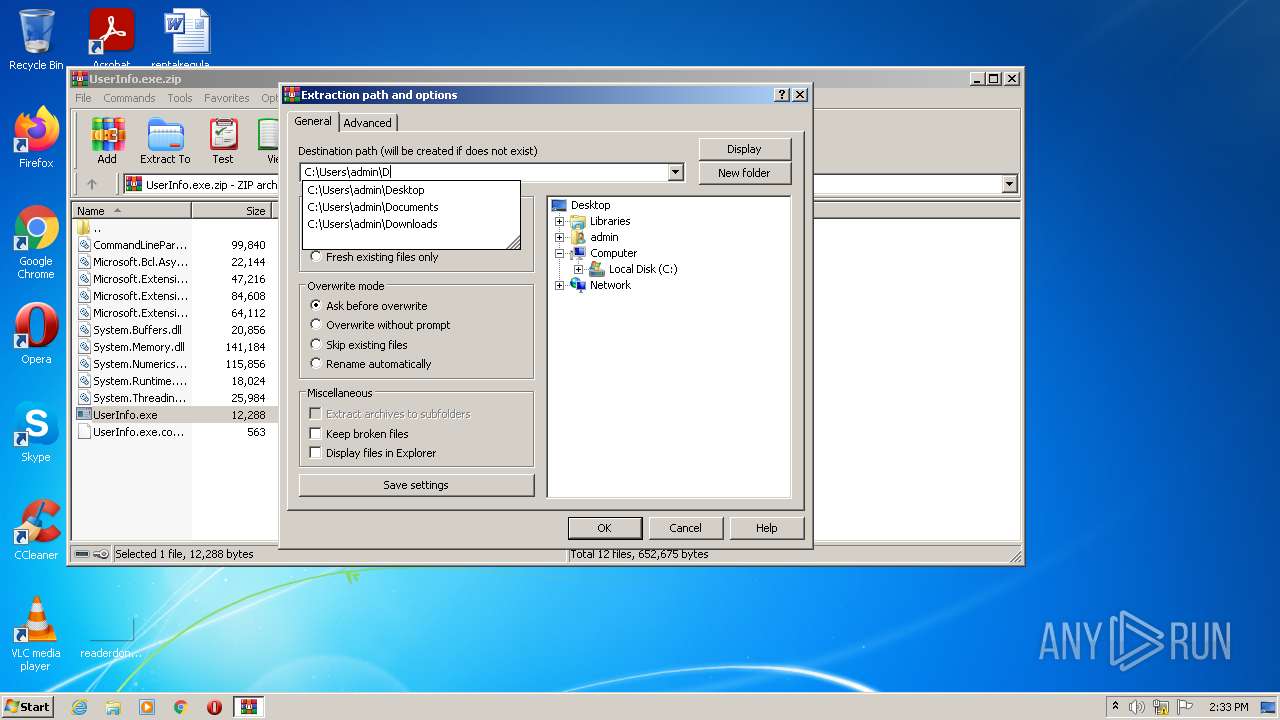
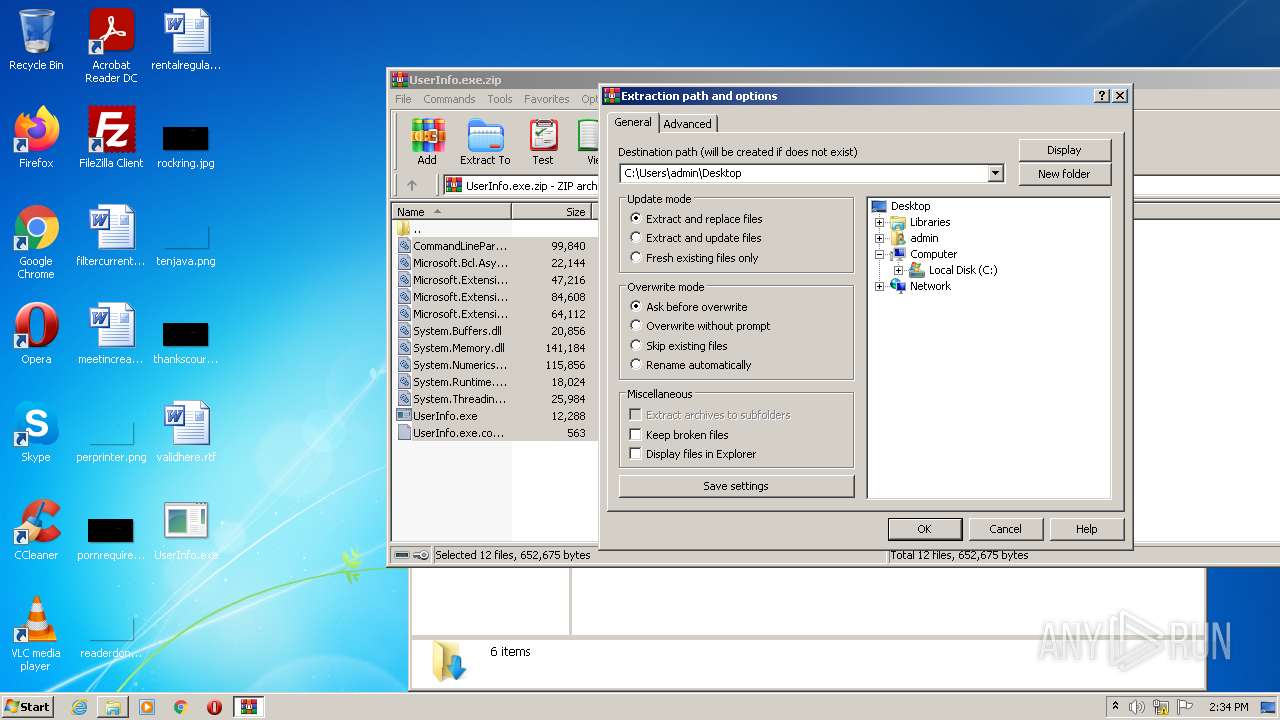
| 2600 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\UserInfo.exe.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2972 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 3004 | "C:\Users\admin\Desktop\UserInfo.exe" | C:\Users\admin\Desktop\UserInfo.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: UserInfo Exit code: 2148734720 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
12 728
Read events
12 561
Write events
164
Delete events
3
Modification events
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\UserInfo.exe.zip | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
22
Suspicious files
14
Text files
34
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1596 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_E503B048B745DFA14B81FCFC68D6DECE | binary | |
MD5:— | SHA256:— | |||
| 1596 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2600.43526\System.Numerics.Vectors.dll | executable | |
MD5:AAA2CBF14E06E9D3586D8A4ED455DB33 | SHA256:1D3EF8698281E7CF7371D1554AFEF5872B39F96C26DA772210A33DA041BA1183 | |||
| 1596 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1596 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2600.43526\System.Memory.dll | executable | |
MD5:6FB95A357A3F7E88ADE5C1629E2801F8 | SHA256:8E76318E8B06692ABF7DAB1169D27D15557F7F0A34D36AF6463EFF0FE21213C7 | |||
| 2600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2600.43526\CommandLineParser.dll | executable | |
MD5:AC23A1E64AE93D7875CF9F81CB015771 | SHA256:8CF072211733DEF35D47624E4AFD72F7FC96DDDE2393D4615712CD483DAD8FC7 | |||
| 2600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2600.43526\System.Buffers.dll | executable | |
MD5:ECDFE8EDE869D2CCC6BF99981EA96400 | SHA256:ACCCCFBE45D9F08FFEED9916E37B33E98C65BE012CFFF6E7FA7B67210CE1FEFB | |||
| 2600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2600.43526\UserInfo.exe.config | xml | |
MD5:467C9988E896A5596D1C64968CDCFF73 | SHA256:DD2A10593CCCB1D99DF5D76E63CD5081BA7E3387AED34DED0EF9588AACD4D3A1 | |||
| 1596 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
43
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2124 | iexplore.exe | GET | — | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | — | — | whitelisted |
1596 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1596 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
1596 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA9bw6F2y3ieICDHiTyBZ7Q%3D | US | der | 1.47 Kb | whitelisted |
1596 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | US | der | 471 b | whitelisted |
1596 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
2124 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 631 b | whitelisted |
1596 | iexplore.exe | GET | 200 | 8.253.204.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2d515f12aa11a923 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1596 | iexplore.exe | 8.253.204.120:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
1596 | iexplore.exe | 96.16.143.41:443 | go.microsoft.com | Akamai International B.V. | US | whitelisted |
1596 | iexplore.exe | 13.107.219.45:443 | dotnet.microsoft.com | Microsoft Corporation | US | suspicious |
2124 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1596 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1596 | iexplore.exe | 23.35.229.160:443 | www.microsoft.com | Zayo Bandwidth Inc | US | whitelisted |
1596 | iexplore.exe | 2.21.20.153:443 | statics-marketingsites-wcus-ms-com.akamaized.net | NTT America, Inc. | DE | suspicious |
1596 | iexplore.exe | 2.21.20.144:443 | img-prod-cms-rt-microsoft-com.akamaized.net | NTT America, Inc. | DE | suspicious |
2124 | iexplore.exe | 13.107.219.45:443 | dotnet.microsoft.com | Microsoft Corporation | US | suspicious |
1596 | iexplore.exe | 13.107.246.45:443 | wcpstatic.microsoft.com | Microsoft Corporation | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
dotnet.microsoft.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
statics-marketingsites-wcus-ms-com.akamaized.net |
| whitelisted |
js.monitor.azure.com |
| whitelisted |
img-prod-cms-rt-microsoft-com.akamaized.net |
| whitelisted |