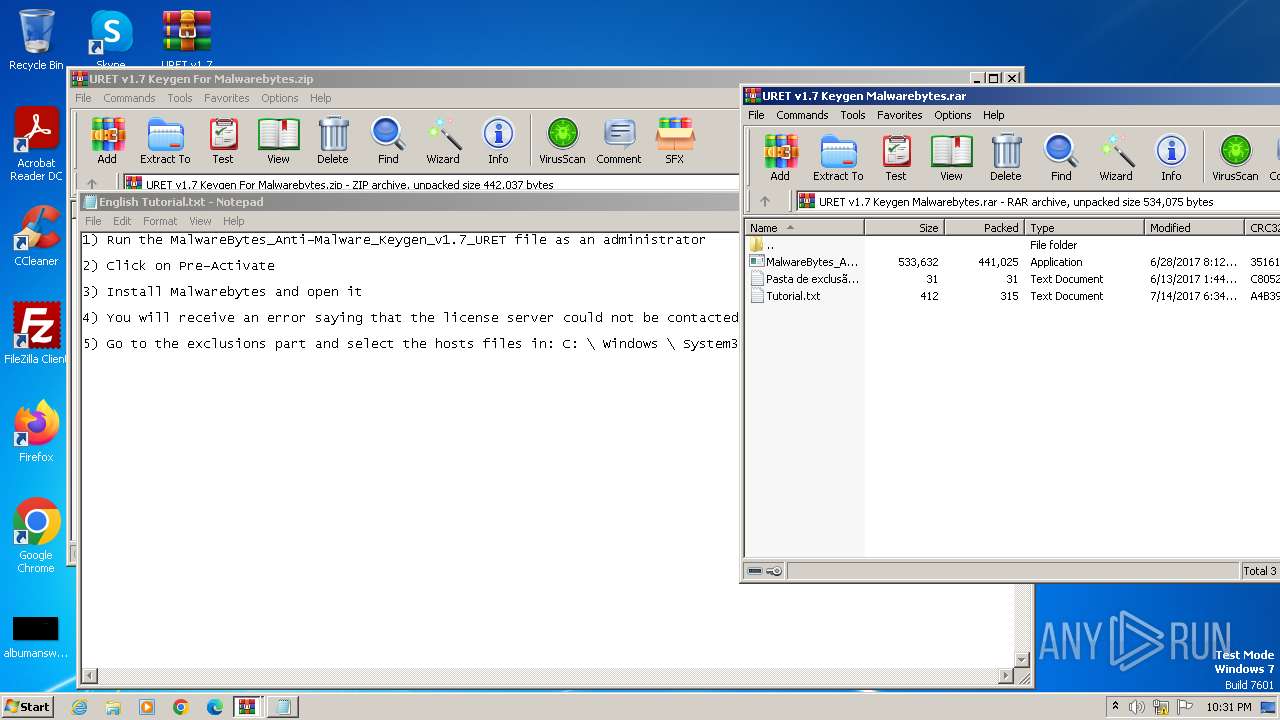
| File name: | URET v1.7 Keygen For Malwarebytes.zip |
| Full analysis: | https://app.any.run/tasks/4e79af96-0480-4196-8df7-ff5b4636d5e7 |
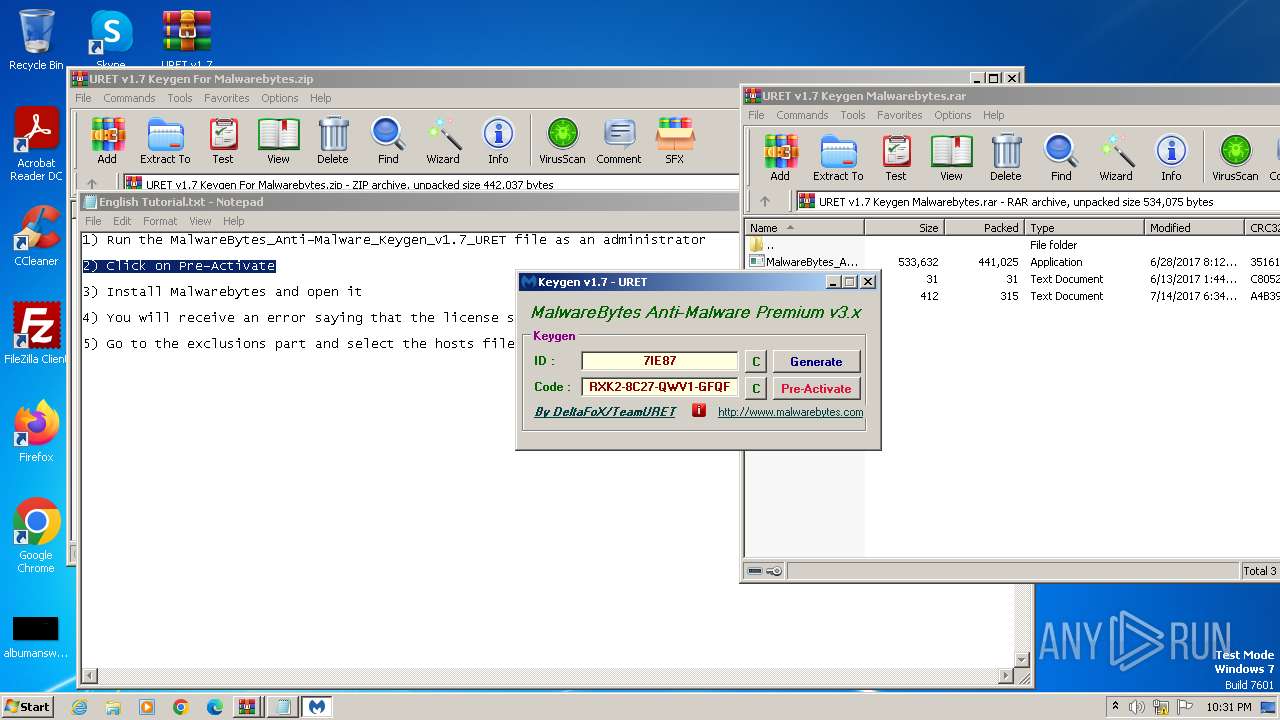
| Verdict: | Malicious activity |
| Analysis date: | February 23, 2025, 22:30:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 735F77B30670F266B0F7433CCE61E6C2 |
| SHA1: | 8E8D2A36F27CE3D102FE2756621768FB743B3DAA |
| SHA256: | E06C77B1CF1440E494009A769A3A837D3B1E14E736466B746771604CCDE817B9 |
| SSDEEP: | 12288:Z3x0LZjzhuQD15/TMUwKssdNwCHXcjvb58b9:Z3x0dRJp5/T3BsOwCMj98h |
MALICIOUS
No malicious indicators.SUSPICIOUS
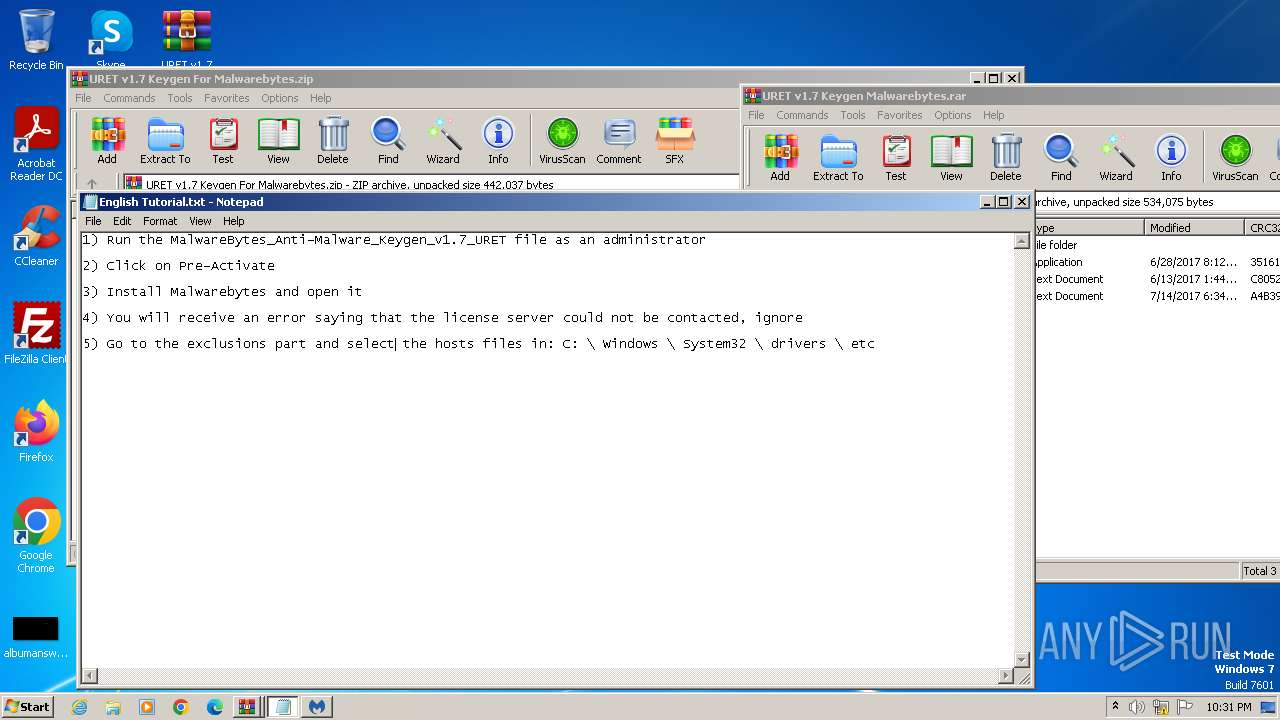
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 2292)
- WinRAR.exe (PID: 1620)
Application launched itself
- WinRAR.exe (PID: 1620)
Generic archive extractor
- WinRAR.exe (PID: 1620)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1620)
- WinRAR.exe (PID: 2292)
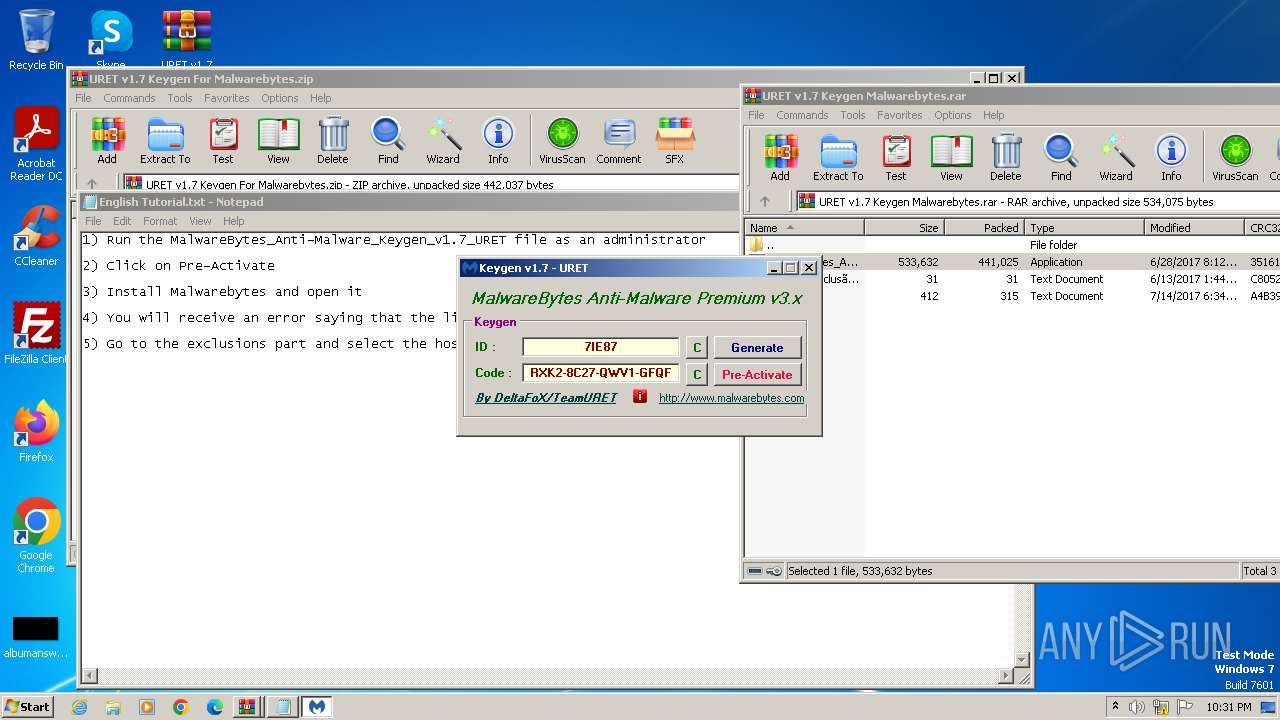
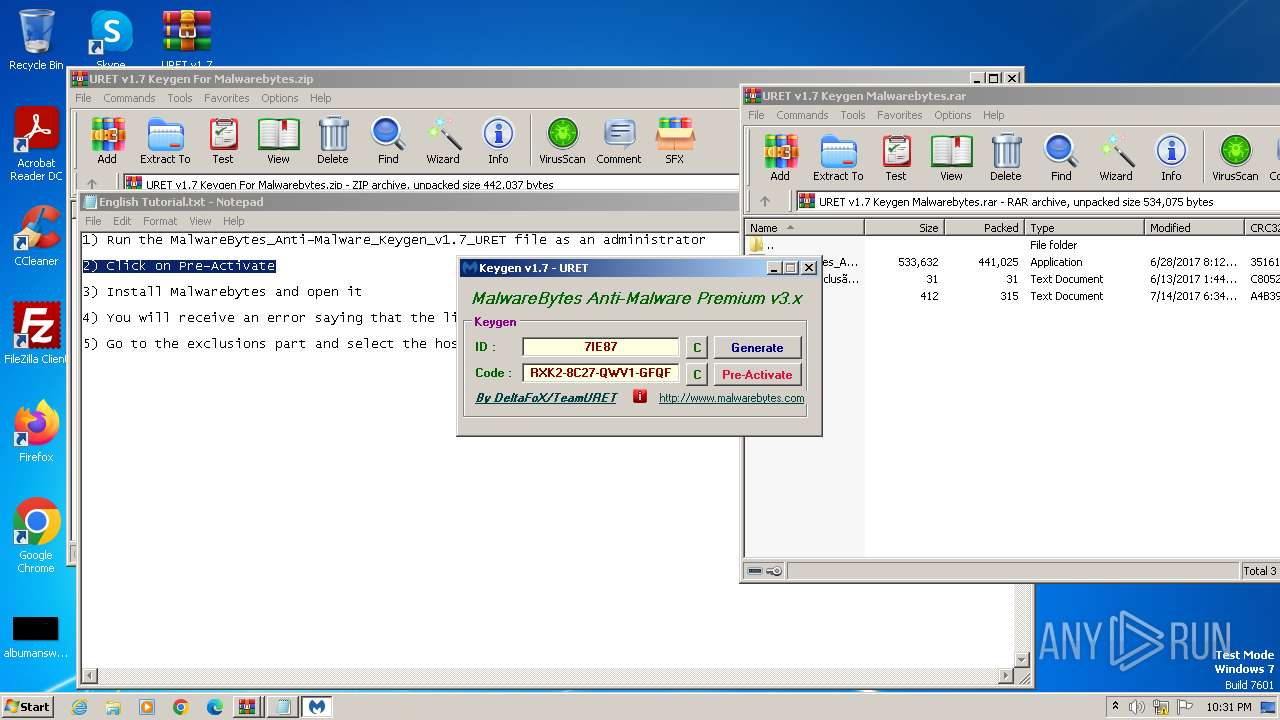
Searches for installed software
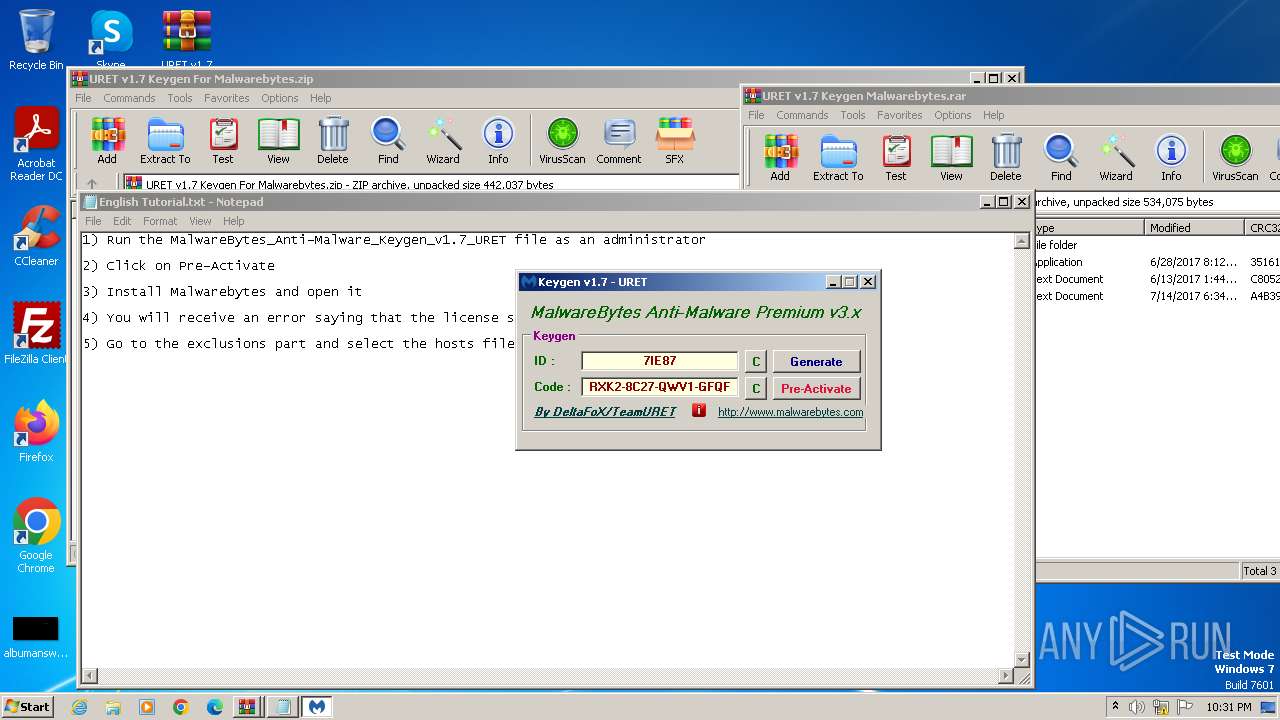
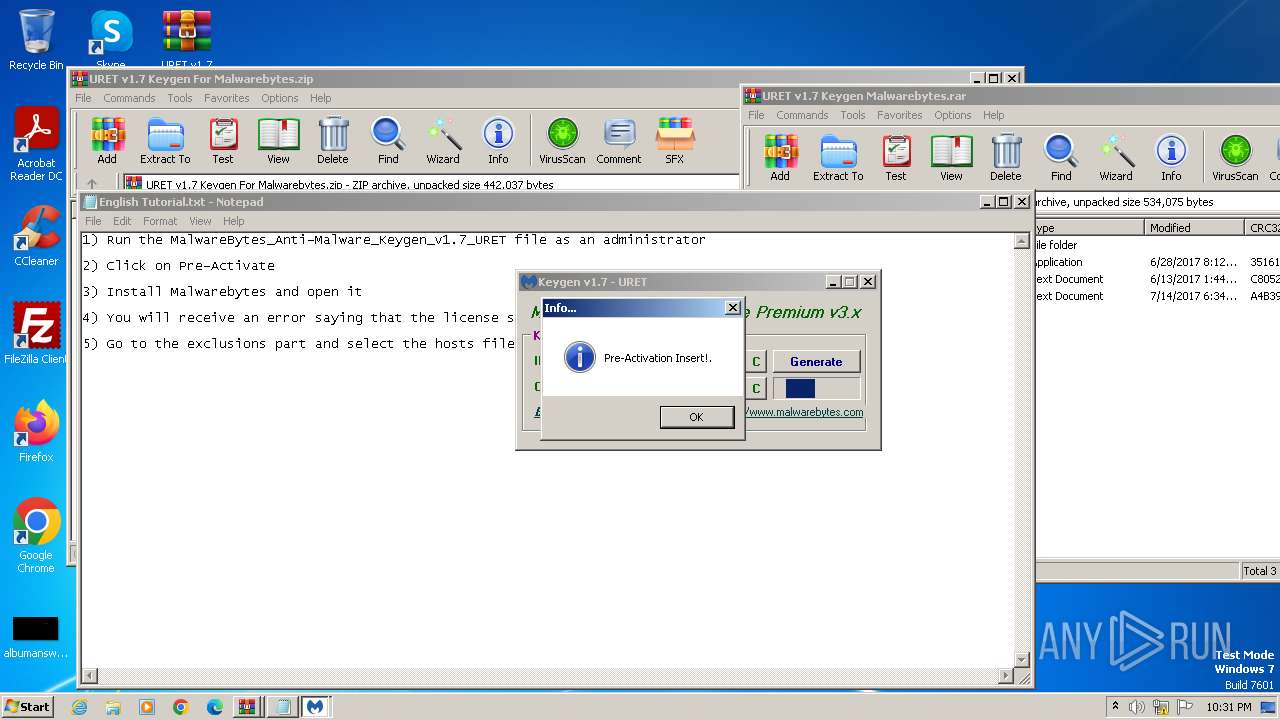
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3116)
Reads the Windows owner or organization settings
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3116)
Creates a software uninstall entry
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3116)
INFO
Creates files or folders in the user directory
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3116)
Reads the computer name
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3116)
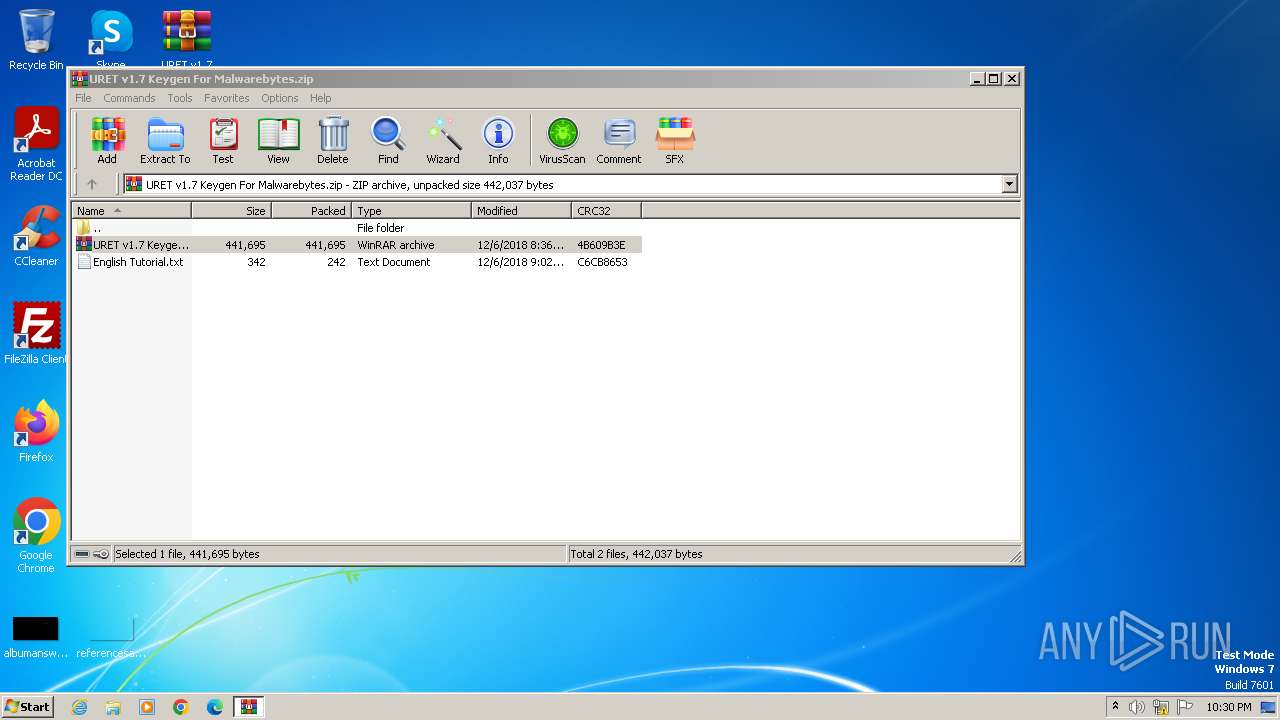
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2292)
Creates files in the program directory
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3116)
Checks supported languages
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3116)
Reads the machine GUID from the registry
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
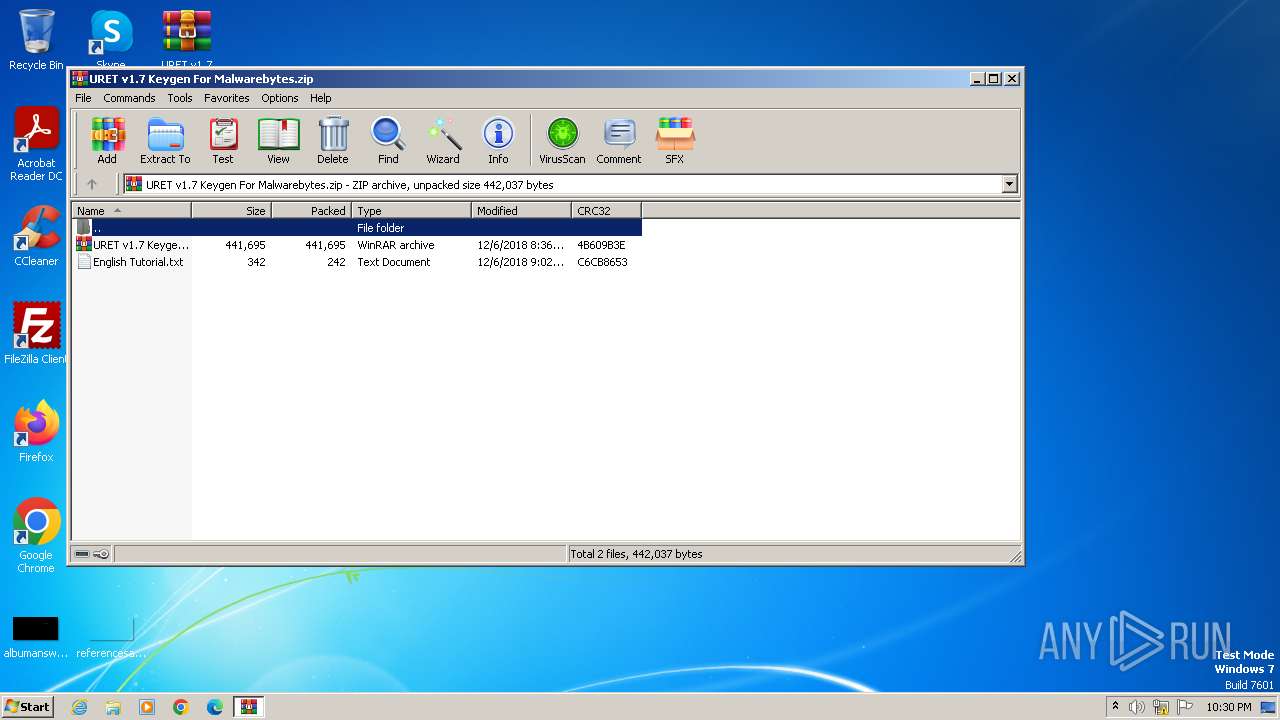
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:12:06 01:02:32 |
| ZipCRC: | 0xc6cb8653 |
| ZipCompressedSize: | 242 |
| ZipUncompressedSize: | 342 |
| ZipFileName: | English Tutorial.txt |
Total processes
42
Monitored processes
6
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
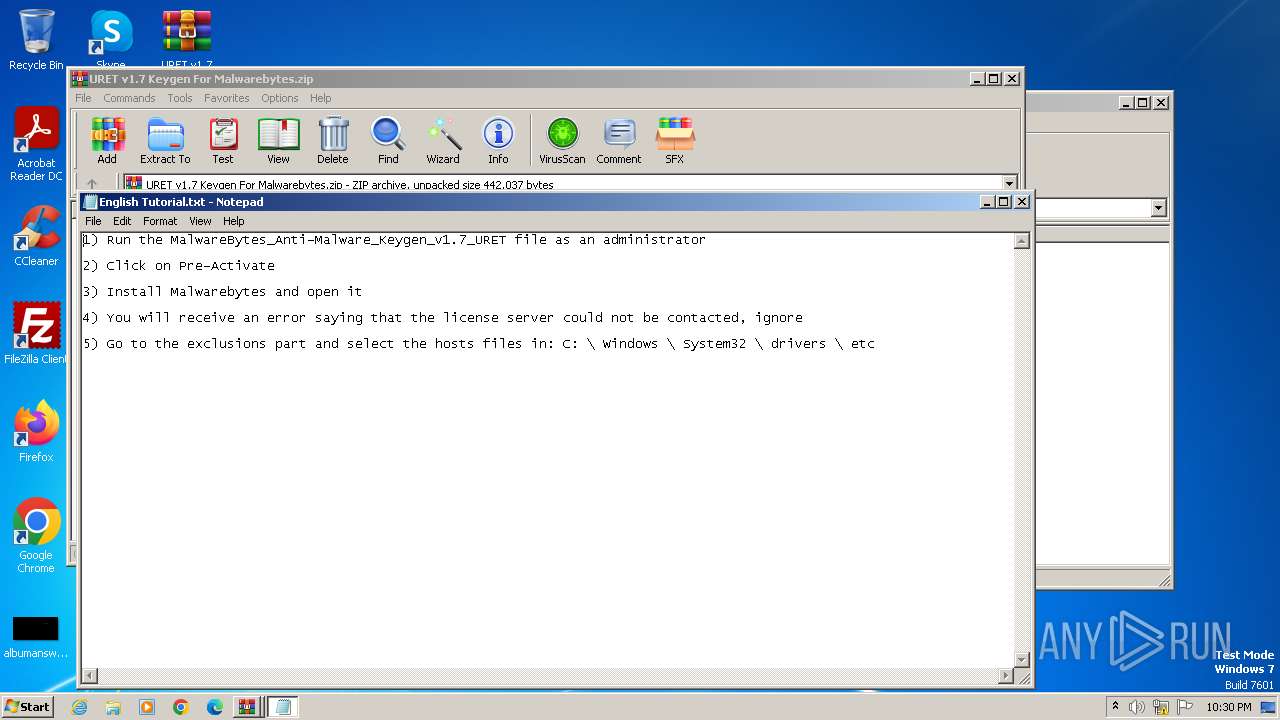
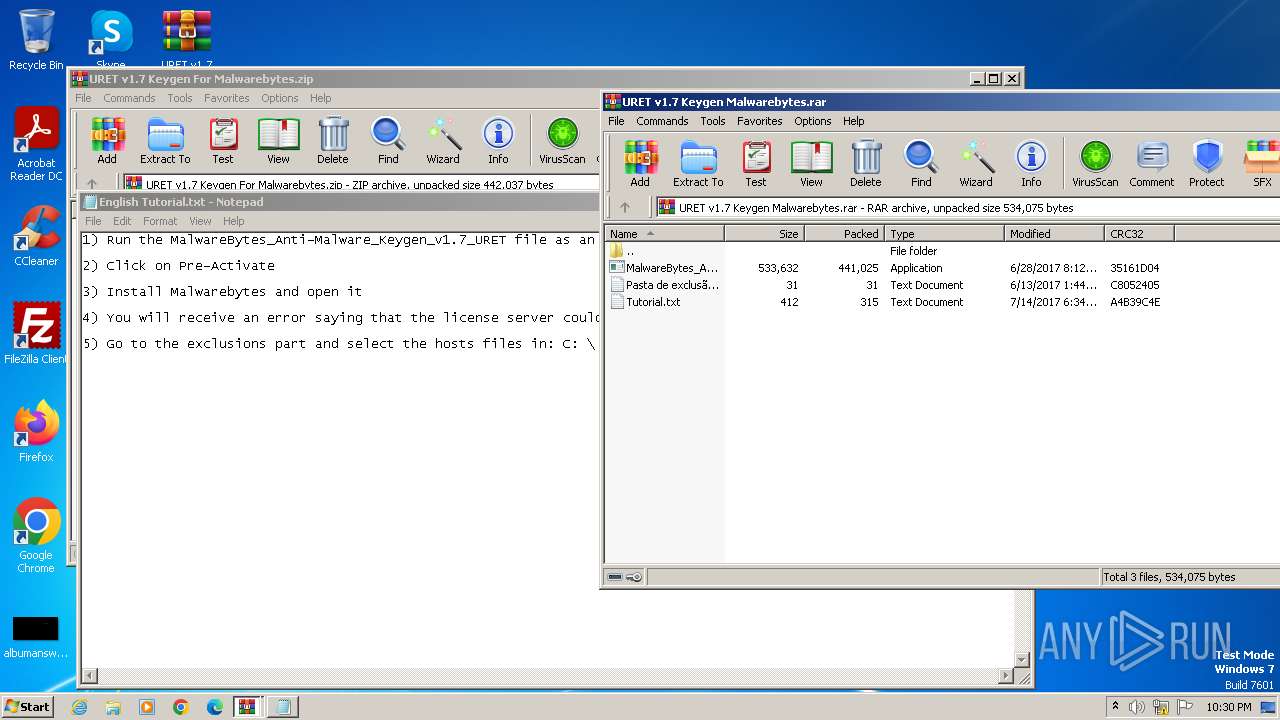
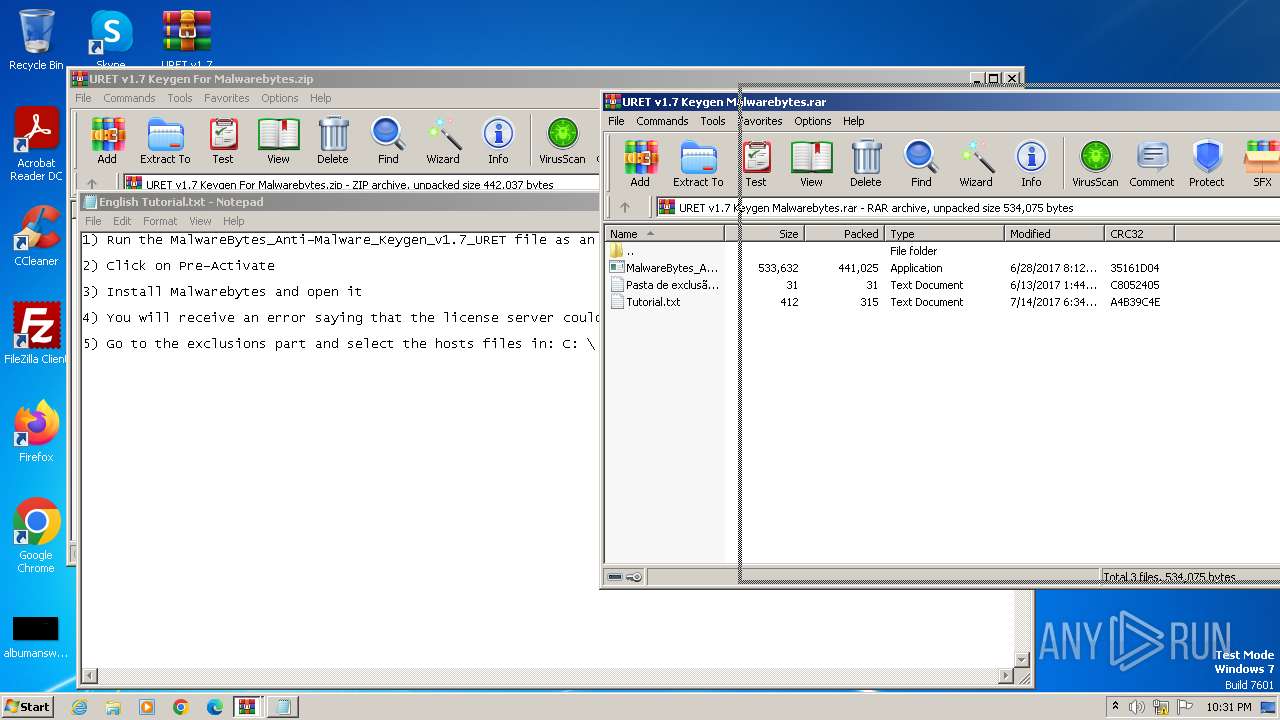
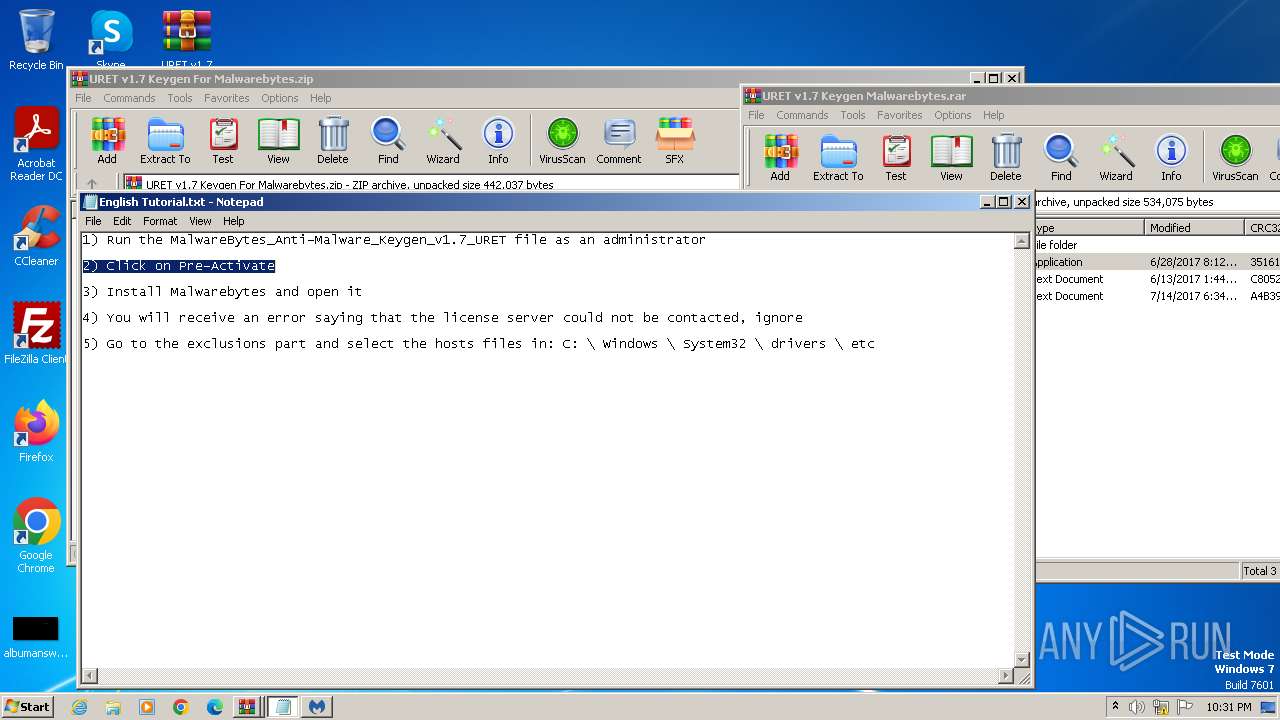
| 920 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa1620.16557\English Tutorial.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
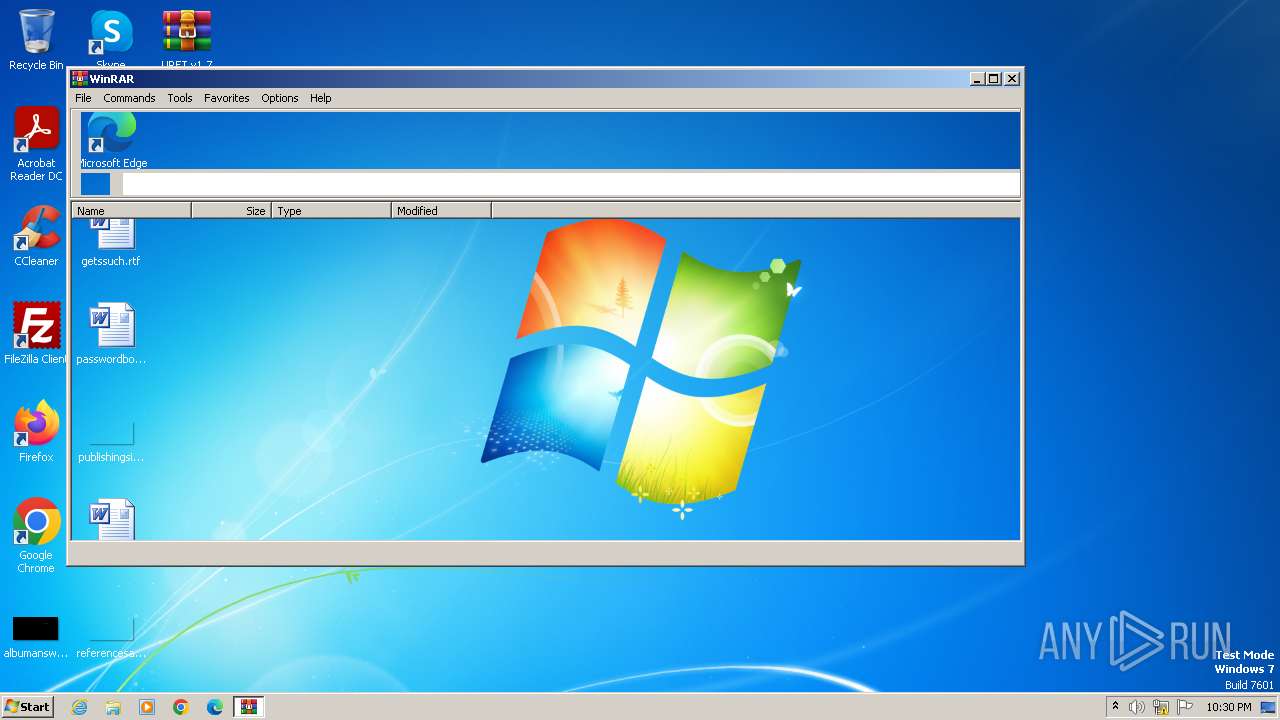
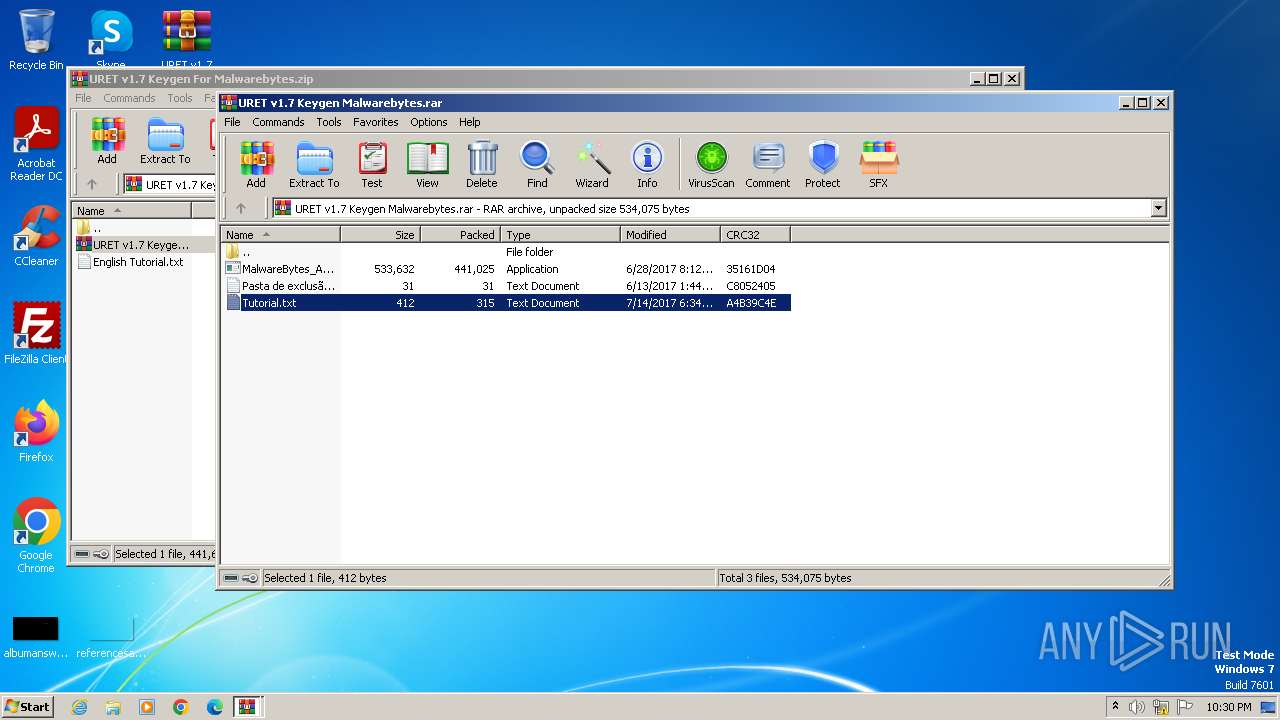
| 1620 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\URET v1.7 Keygen For Malwarebytes.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
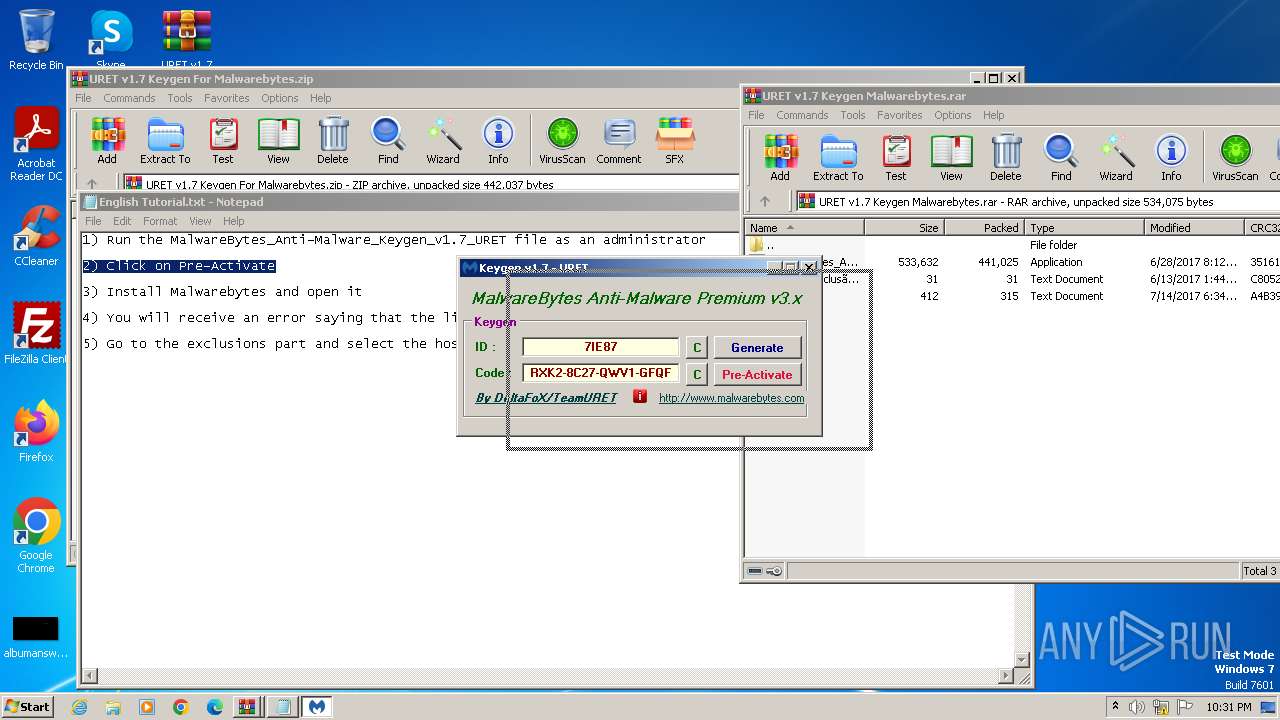
| 1780 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2292.17575\MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2292.17575\MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe | — | WinRAR.exe | |||||||||||
User: admin Company: URET Integrity Level: MEDIUM Description: MalwareBytes_Anti-Malware_DFoX Exit code: 3221226540 Version: 1.7.0.0 Modules
| |||||||||||||||
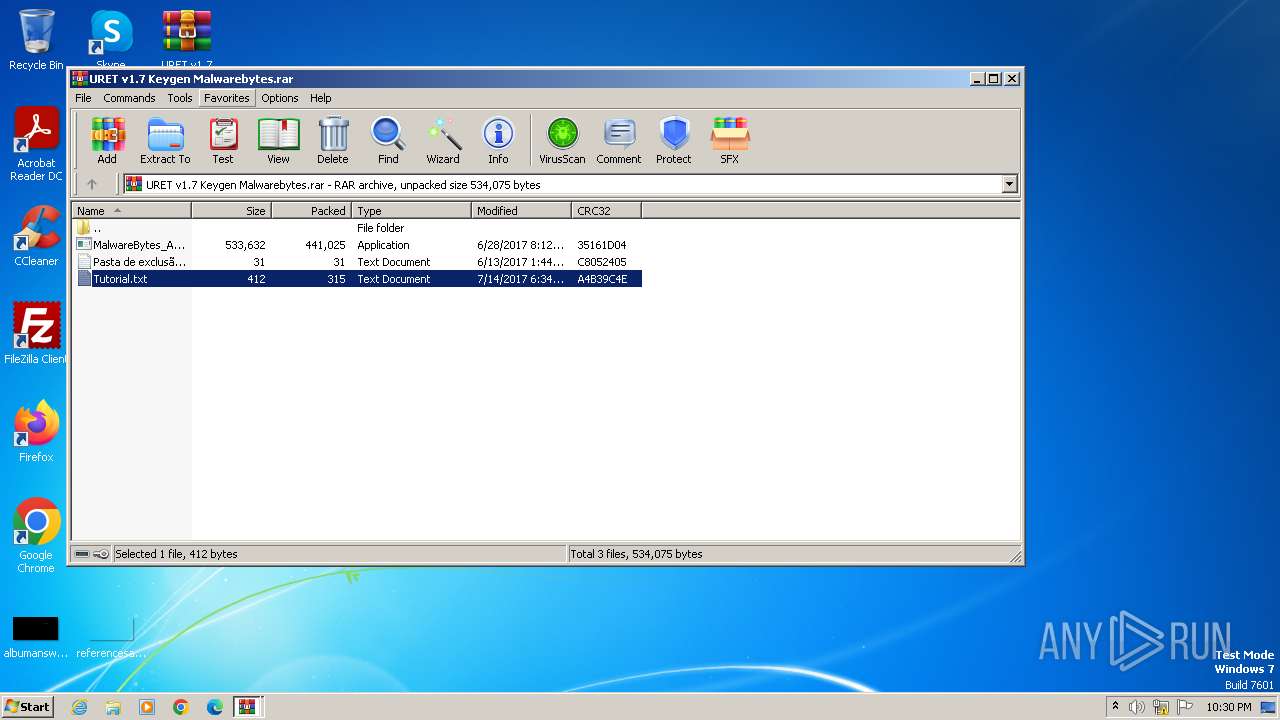
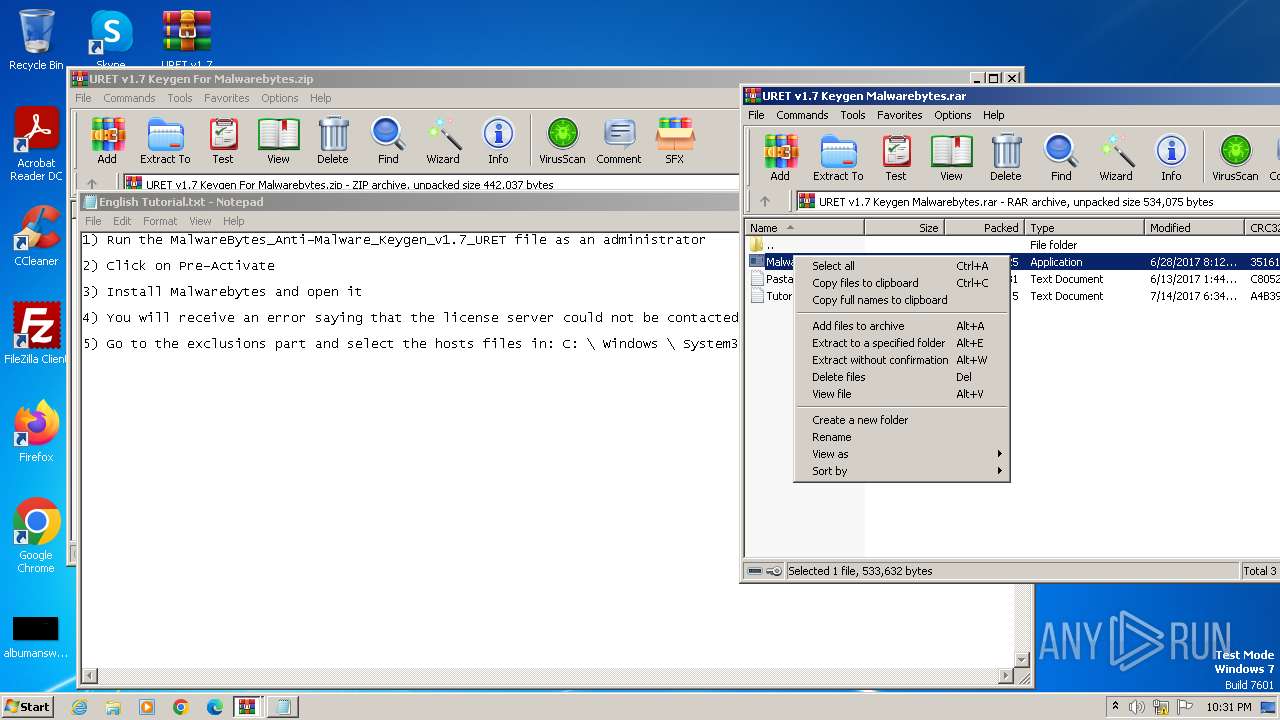
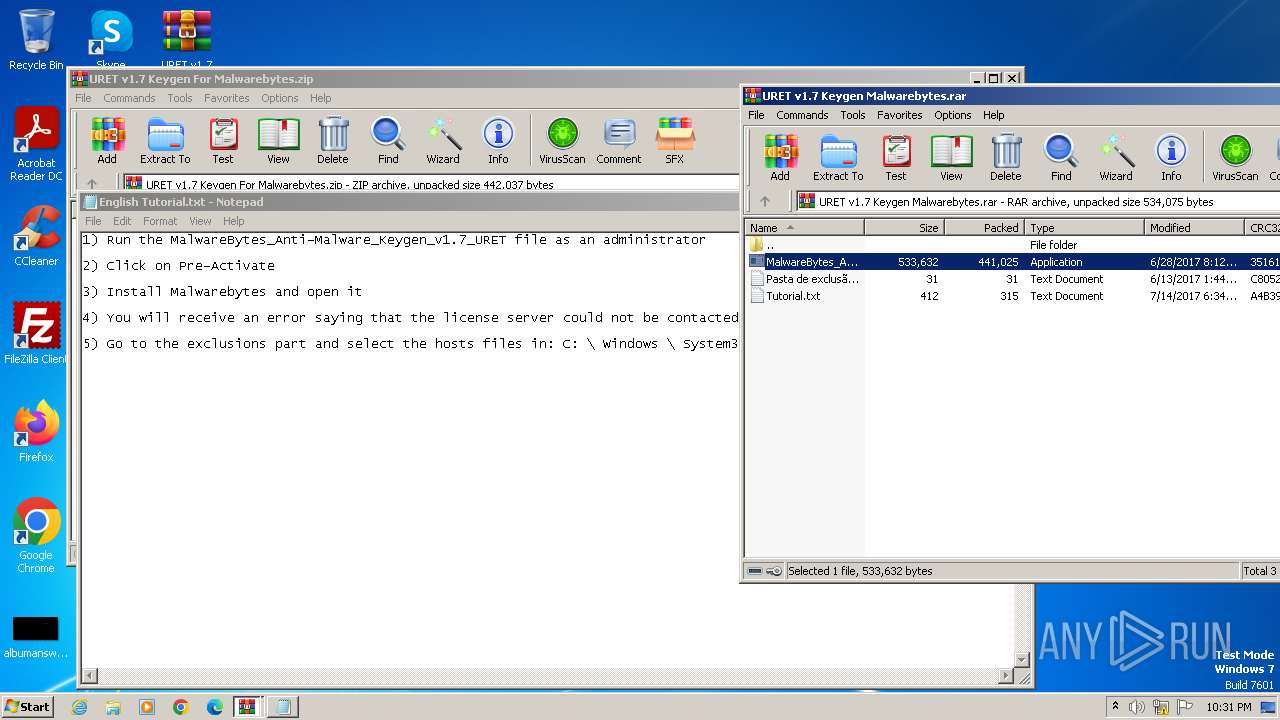
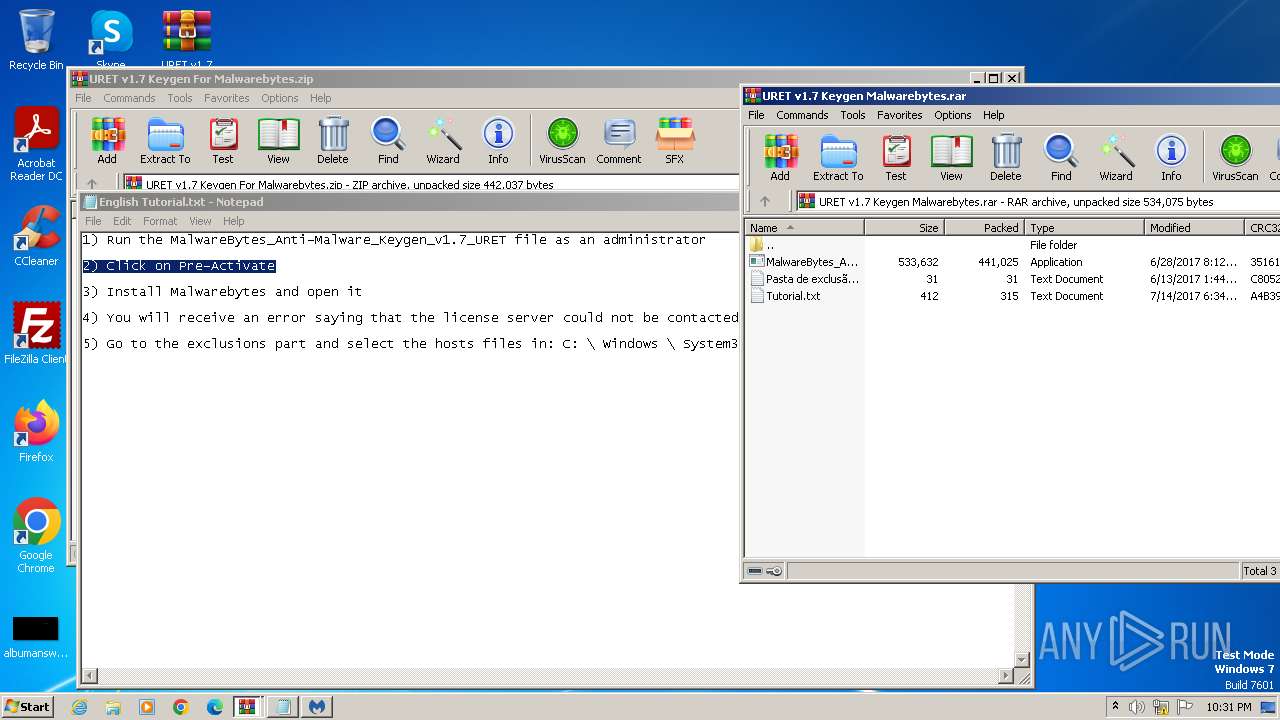
| 2292 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa1620.15454\URET v1.7 Keygen Malwarebytes.rar" | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
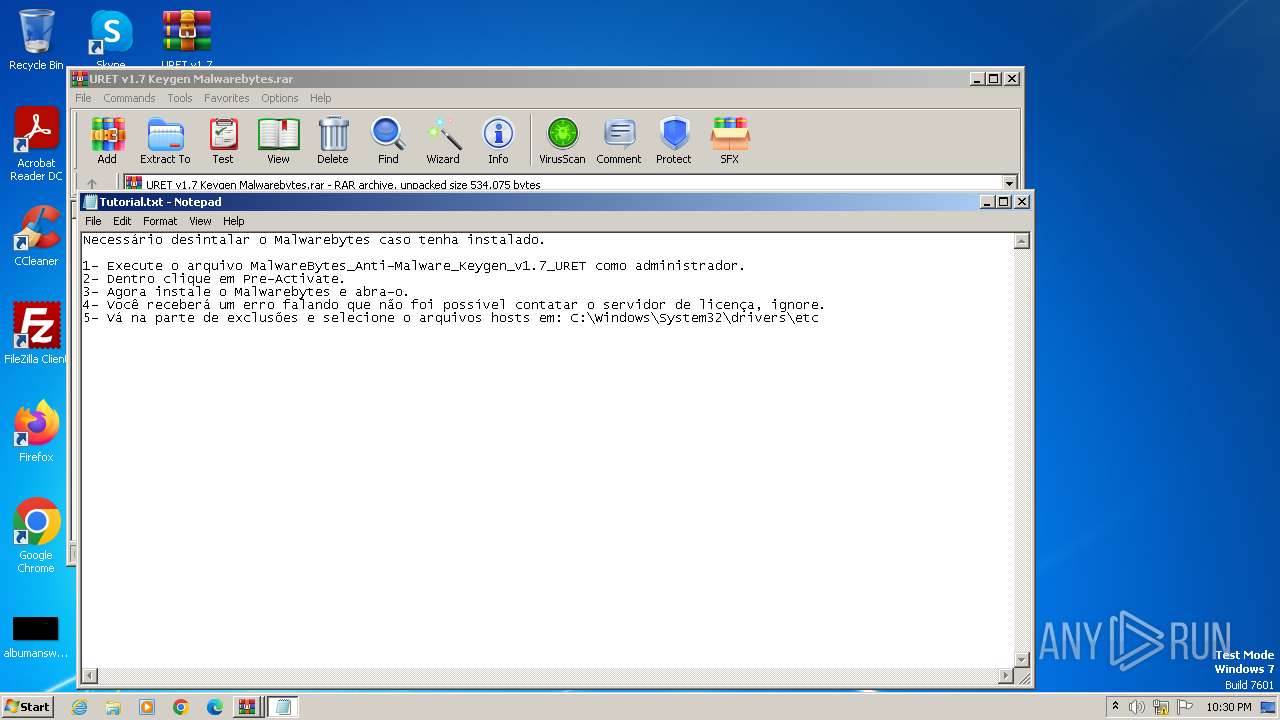
| 2900 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa2292.15715\Tutorial.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3116 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2292.17575\MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2292.17575\MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe | WinRAR.exe | ||||||||||||
User: admin Company: URET Integrity Level: HIGH Description: MalwareBytes_Anti-Malware_DFoX Version: 1.7.0.0 Modules
| |||||||||||||||
Total events
2 793
Read events
2 734
Write events
59
Delete events
0
Modification events
| (PID) Process: | (1620) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\URET v1.7 Keygen For Malwarebytes.zip | |||
| (PID) Process: | (1620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
Executable files
1
Suspicious files
2
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2292 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2292.15715\Tutorial.txt | text | |
MD5:819F090666638D7AADA0A5F448FAB510 | SHA256:3933A2F4F693A38DF61D80221A09089AB031B62F8260A9DF4D525386640EB342 | |||
| 3116 | MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe | C:\Windows\System32\drivers\etc\hosts | text | |
MD5:5A0236338F3A342F99894C1C2392CC4B | SHA256:4418E91234485F9A0E9AF6580761B072B6E5631CF05D02361D49AEF85950DD59 | |||
| 2292 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2292.17575\Pasta de exclusão.txt | text | |
MD5:65A0201F8283C2F3C1960146EF063A83 | SHA256:73A27AF4300C85E32A5060BBCE2F6B9B41240FEE05D4FA8D331B5F7B21AC7132 | |||
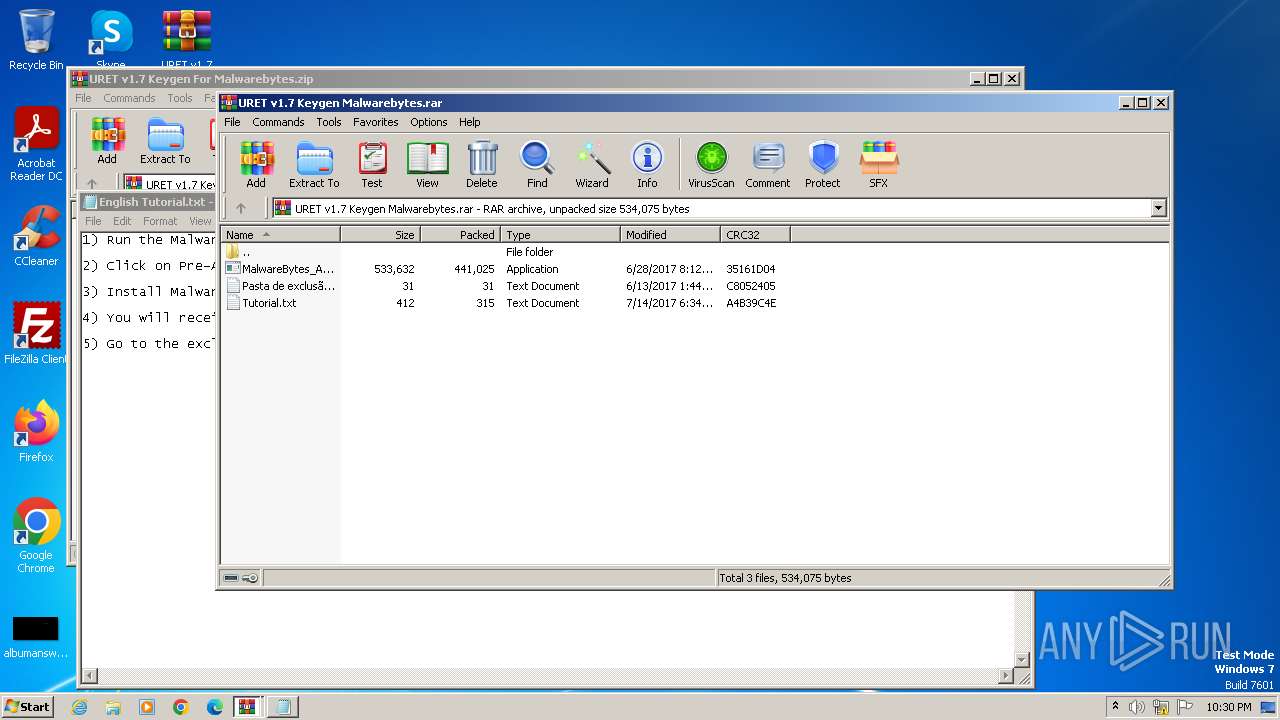
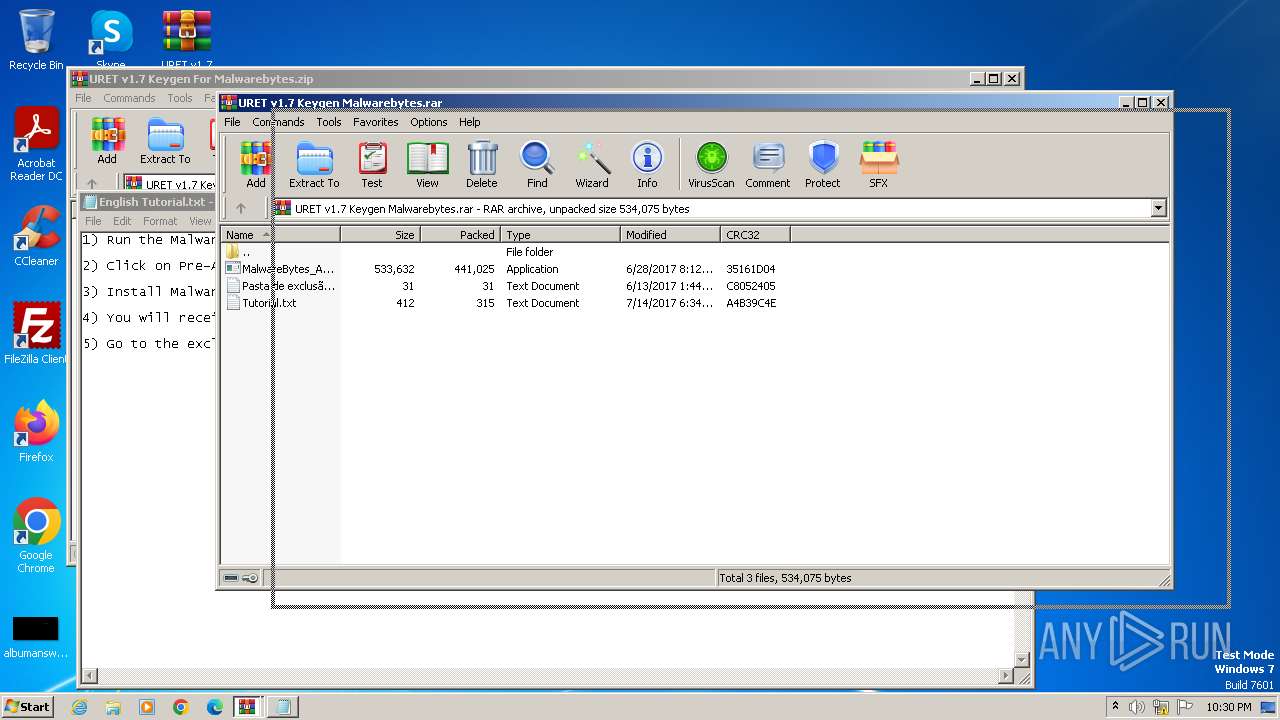
| 1620 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa1620.15454\URET v1.7 Keygen Malwarebytes.rar | compressed | |
MD5:DE7E46FE549A6B1866FA95823B2251B0 | SHA256:9EA7FB86A816A5126CC81235B6CDF885DF5921BEA436582C79C410845E2EE0BD | |||
| 2292 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2292.17575\Tutorial.txt | text | |
MD5:819F090666638D7AADA0A5F448FAB510 | SHA256:3933A2F4F693A38DF61D80221A09089AB031B62F8260A9DF4D525386640EB342 | |||
| 3116 | MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe | C:\ProgramData\Malwarebytes\Malwarebytes Anti-Malware\Configuration\license.conf | binary | |
MD5:88A1F7F17383A9D7C1152ECF2E4E3134 | SHA256:C624D20E4F6BA44C6D91473C4E951FBF14B271F209CBB0A6094CA4C8023FF0EE | |||
| 2292 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2292.17575\MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe | executable | |
MD5:31CEA736B899295526B0F750BFC5362B | SHA256:6AB07188EF43720F78D19FBCBDF31A65768C27FCAE0899E9DC96106A5589C574 | |||
| 1620 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa1620.16557\English Tutorial.txt | text | |
MD5:EB0CDB47EF9C36A8F859A1D5F5FA6864 | SHA256:3F6F94CEFE37D4B94074EC879851A763394B3B7678669F1FF33FF3643C1E8375 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1108 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |