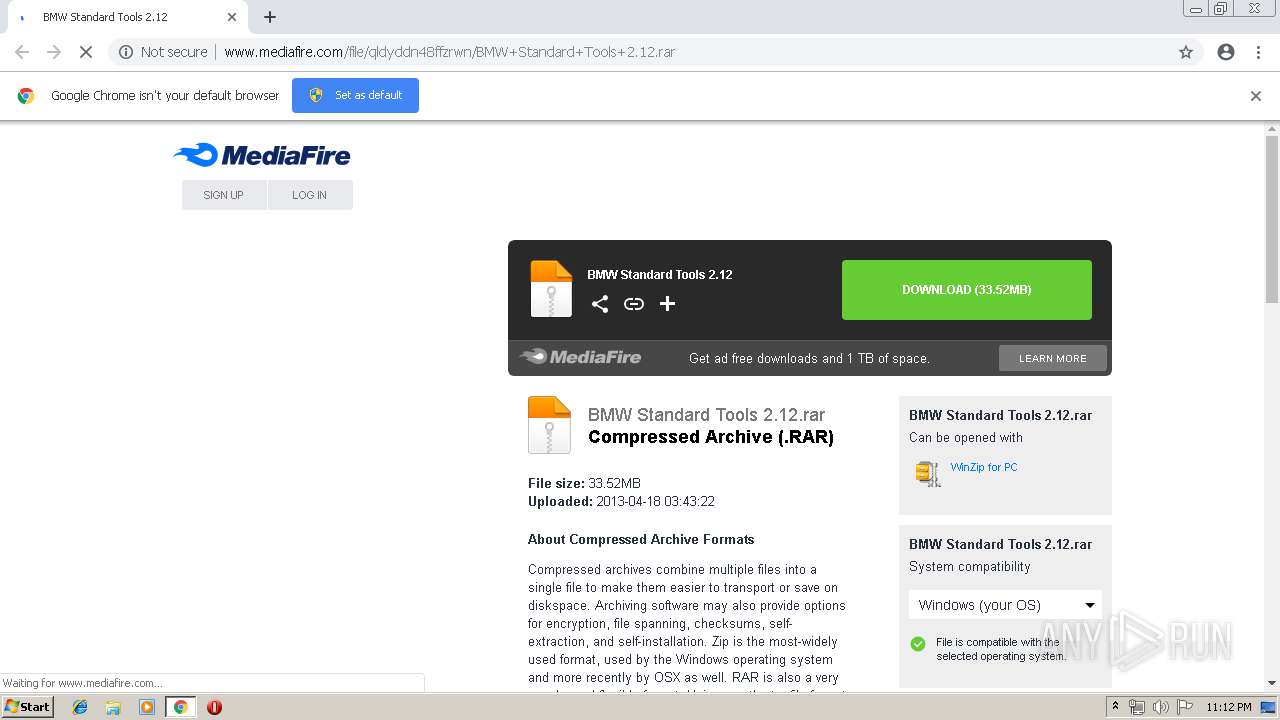
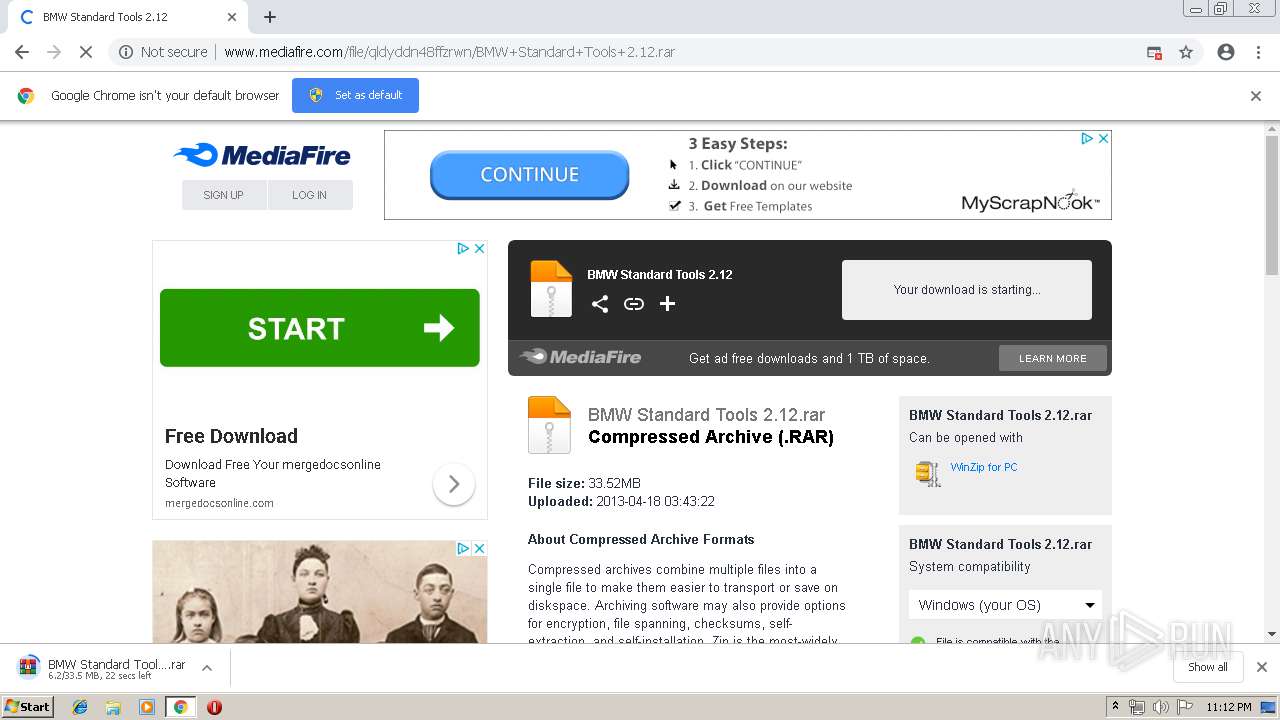
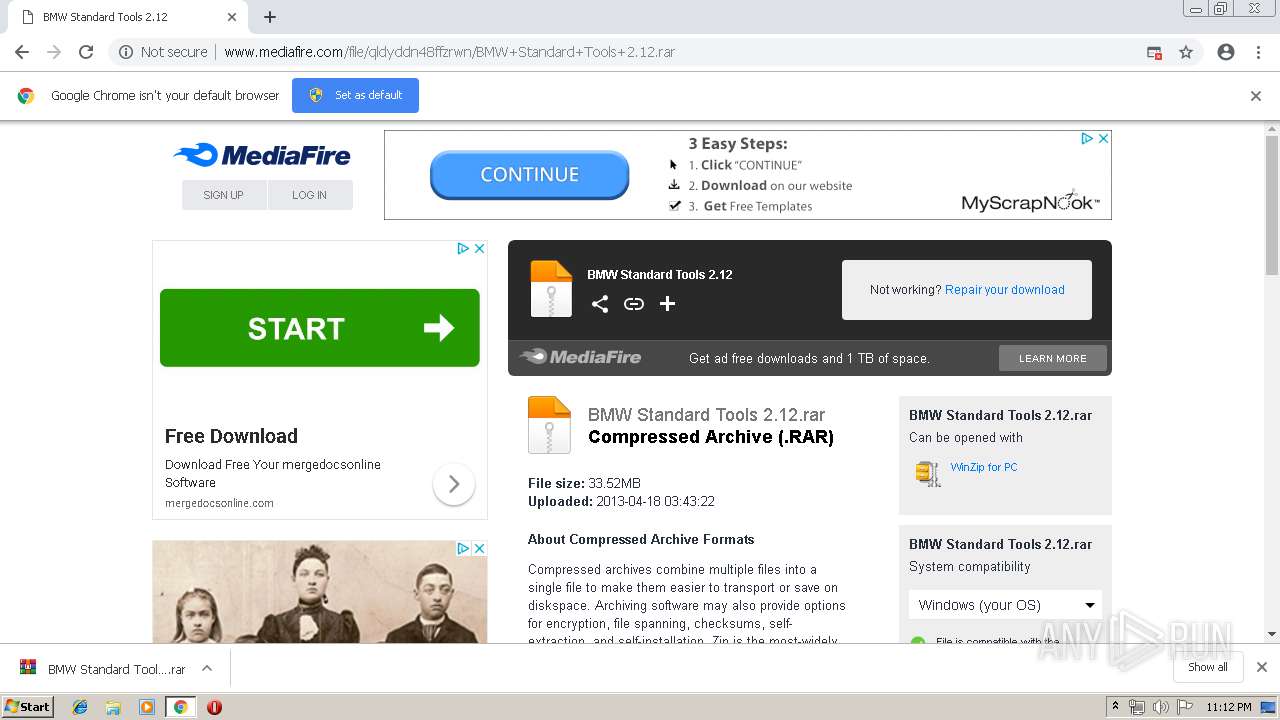
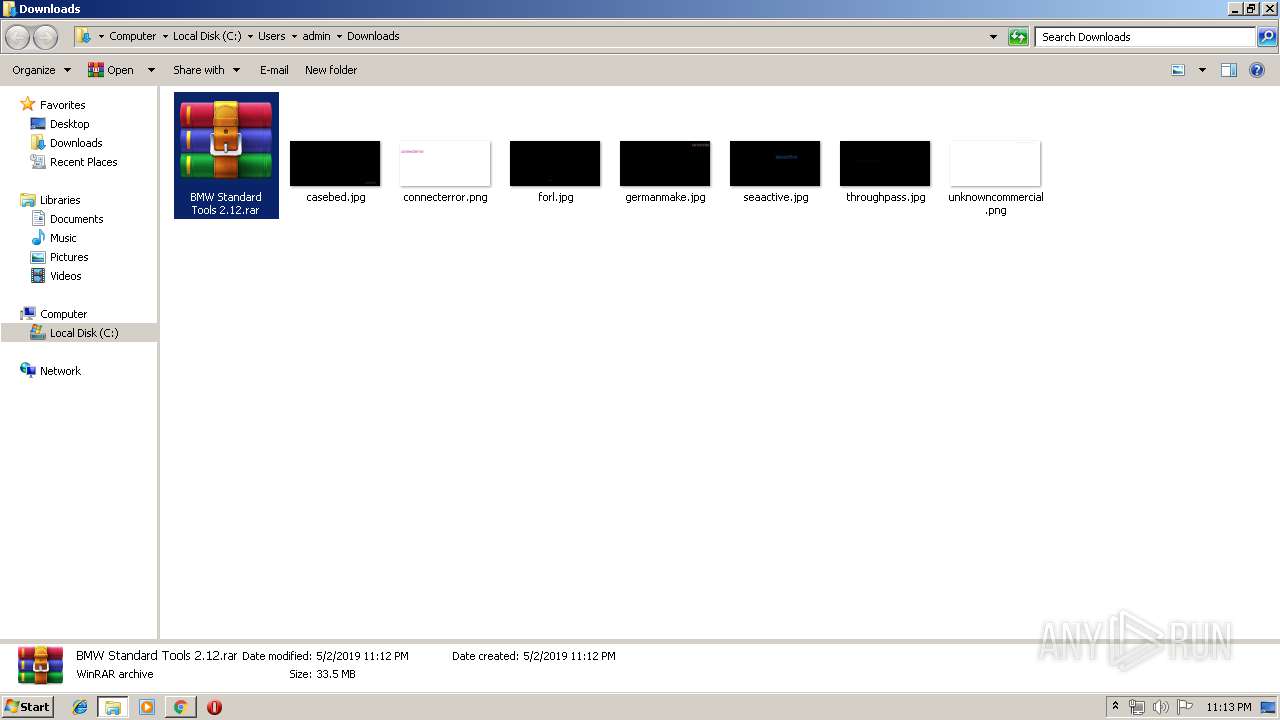
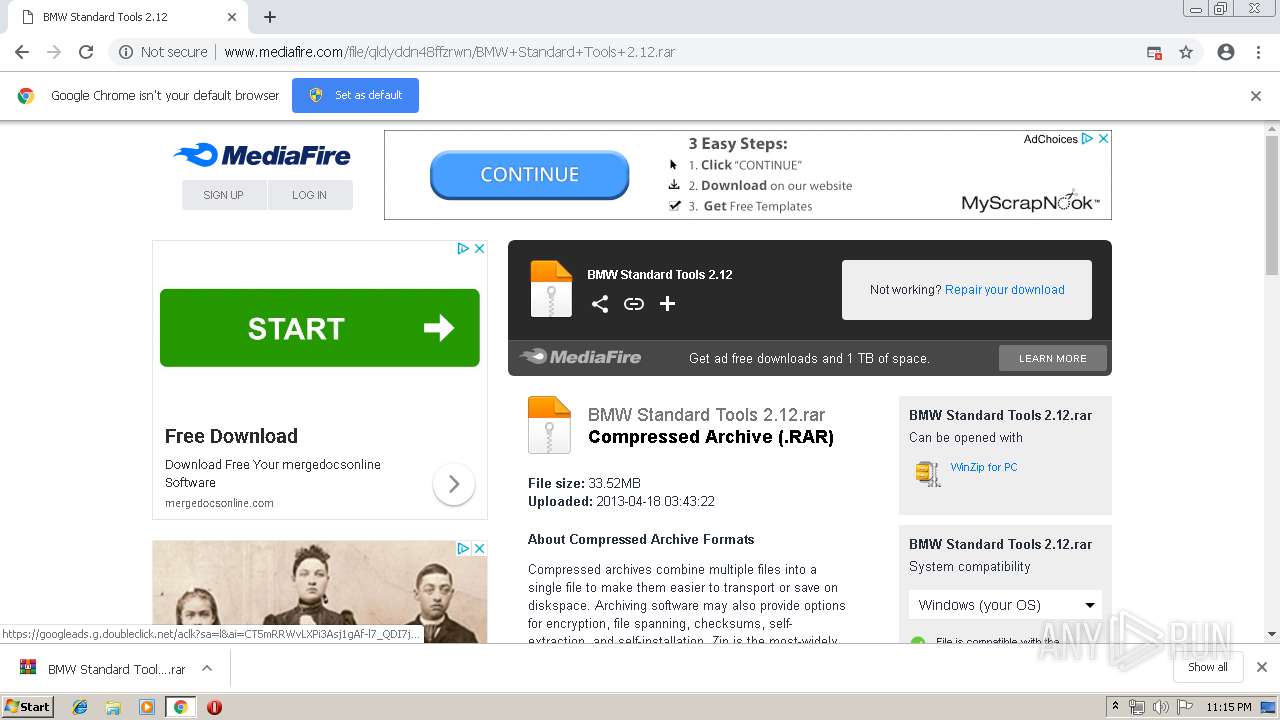
| URL: | http://www.mediafire.com/file/qldyddn48ffzrwn/BMW+Standard+Tools+2.12.rar |
| Full analysis: | https://app.any.run/tasks/5587fdf1-5a37-44ac-b6fc-1845046b2d27 |
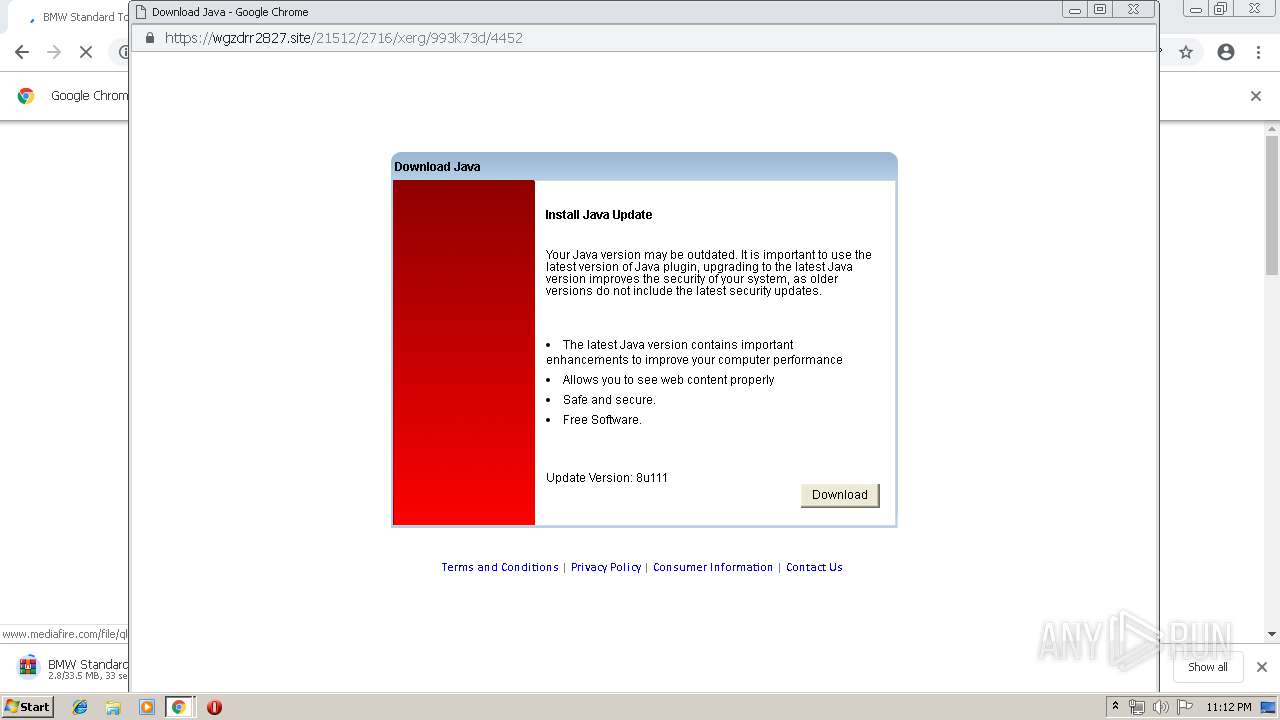
| Verdict: | Malicious activity |
| Analysis date: | May 02, 2019, 22:12:03 |
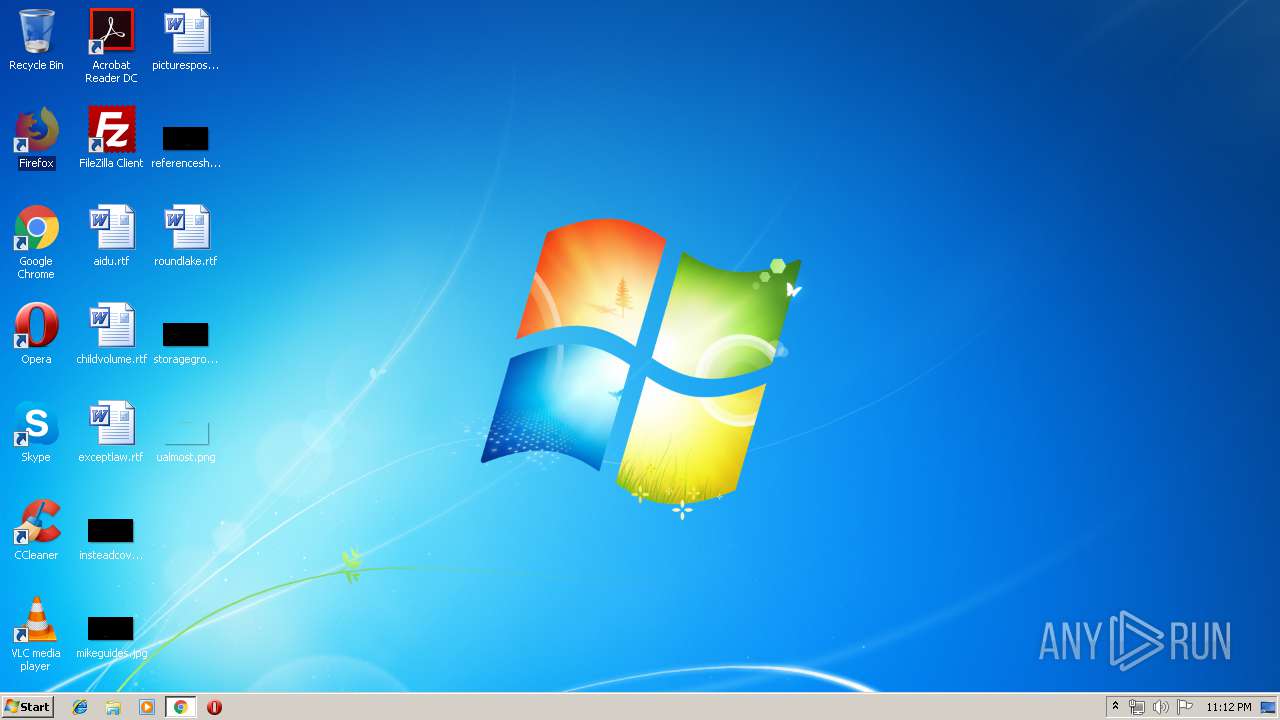
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 89541F05F20611CB46BC9EE533CF812E |
| SHA1: | 72E920411851E0423891D3CBD2BBA678AC909586 |
| SHA256: | E06BB3D7E641642382471BEB5C9F8560E7979CAE31B9EB8C36758D6F462EA1CE |
| SSDEEP: | 3:N1KJS4w3eGUoQq3Dm+oyZoEBGUbUX:Cc4w3eG8q3S+o1EB/UX |
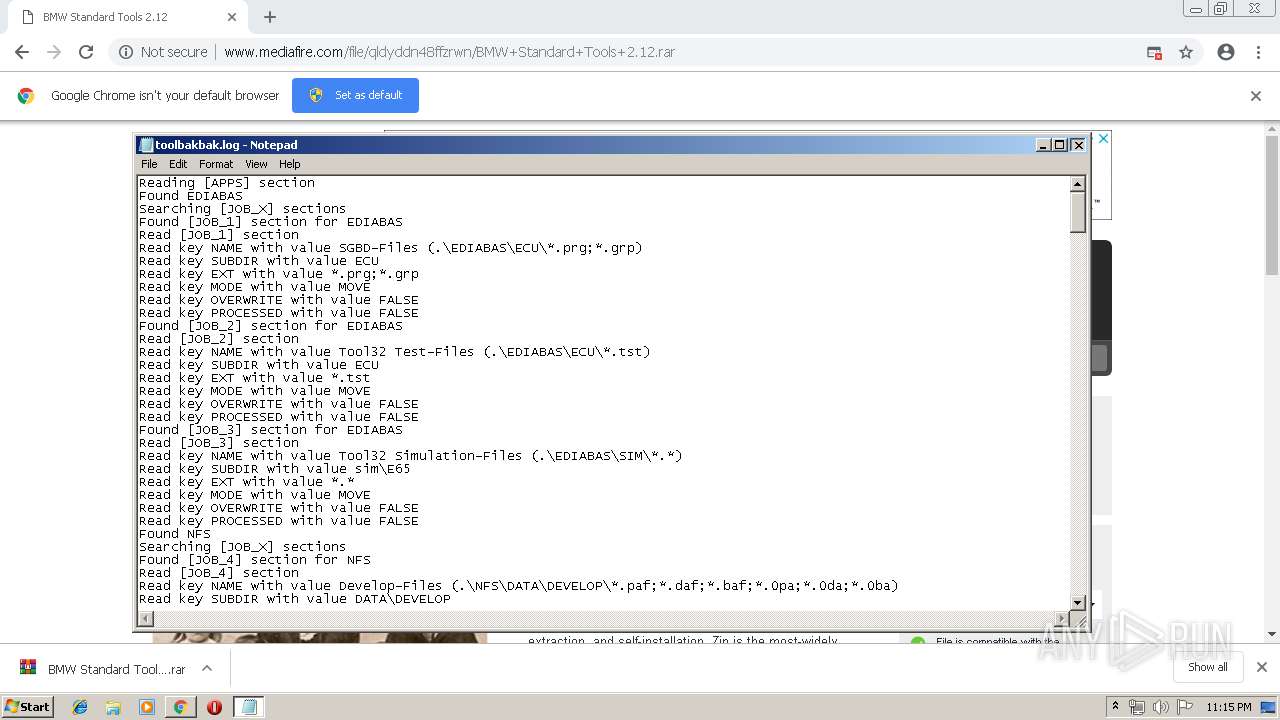
MALICIOUS
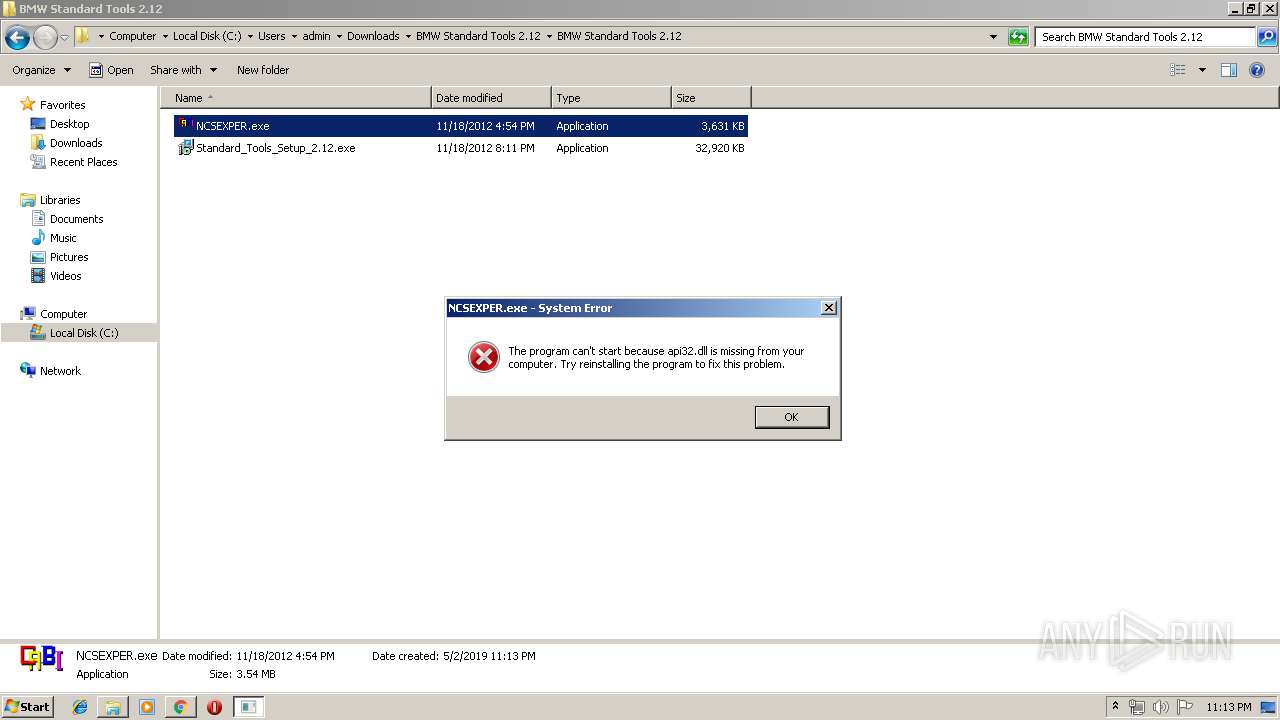
Application was dropped or rewritten from another process
- NCSEXPER.exe (PID: 2616)
- REGSVR32.EXE (PID: 2940)
- REGSVR32.EXE (PID: 2972)
- NCSEXPER.exe (PID: 892)
- EBAS32.EXE (PID: 3108)
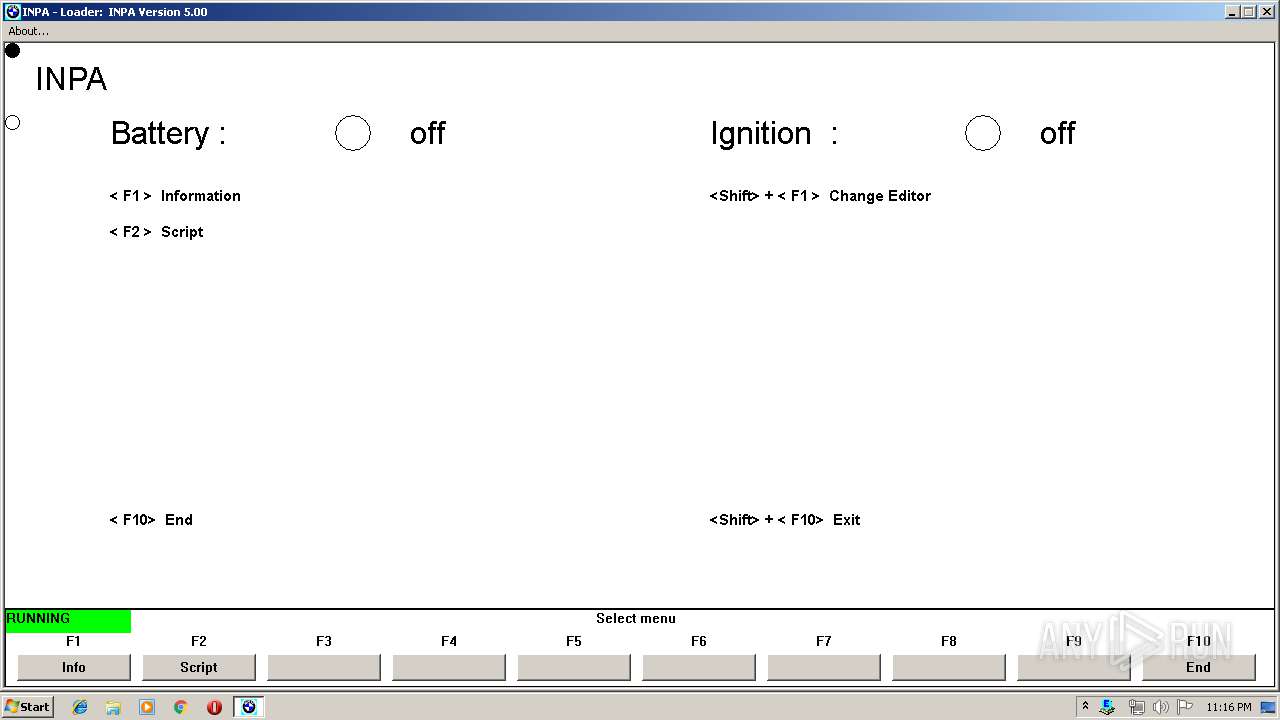
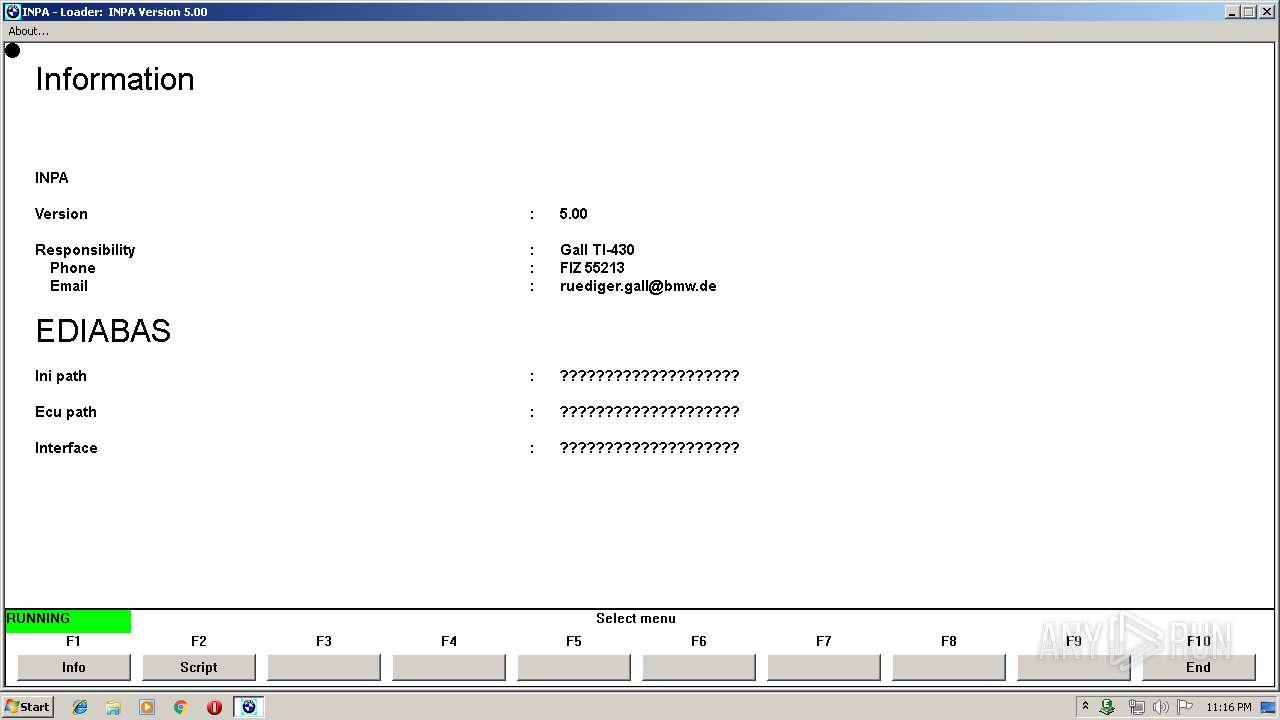
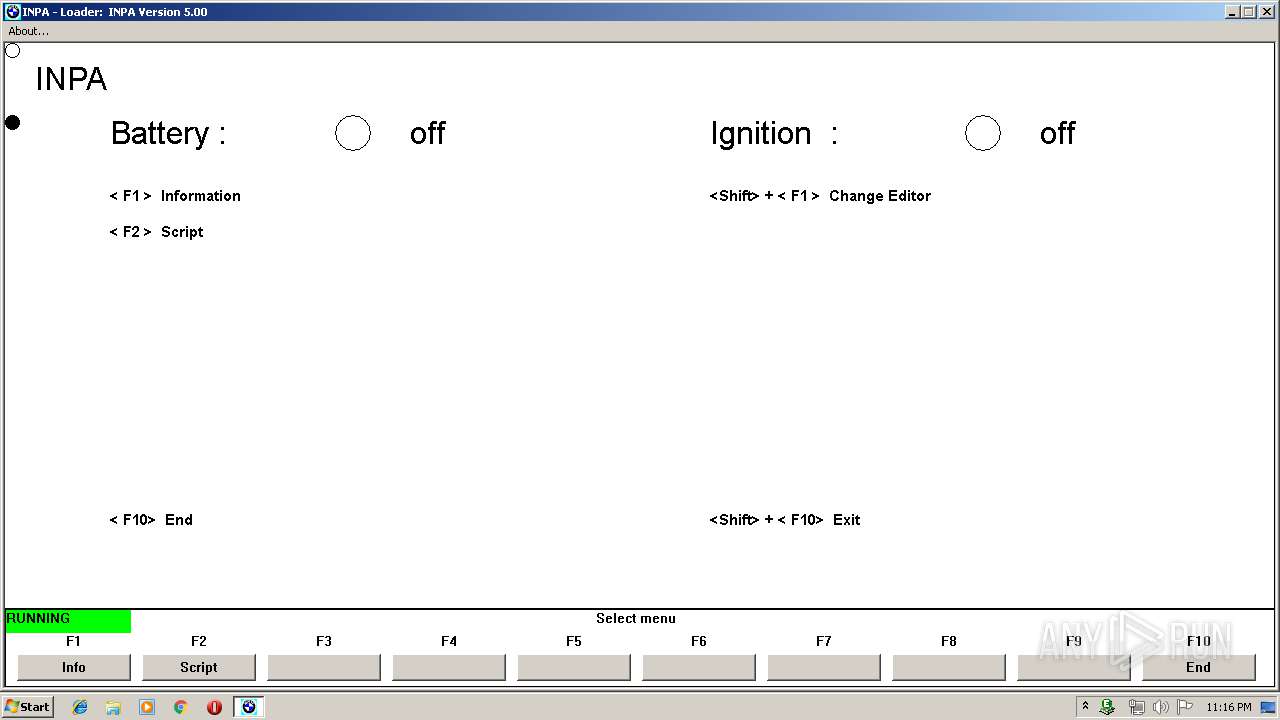
- INPALOAD.exe (PID: 2884)
Starts NET.EXE for service management
- cmd.exe (PID: 2748)
Loads dropped or rewritten executable
- REGSVR32.EXE (PID: 2972)
- NCSEXPER.exe (PID: 892)
- INPALOAD.exe (PID: 2884)
SUSPICIOUS
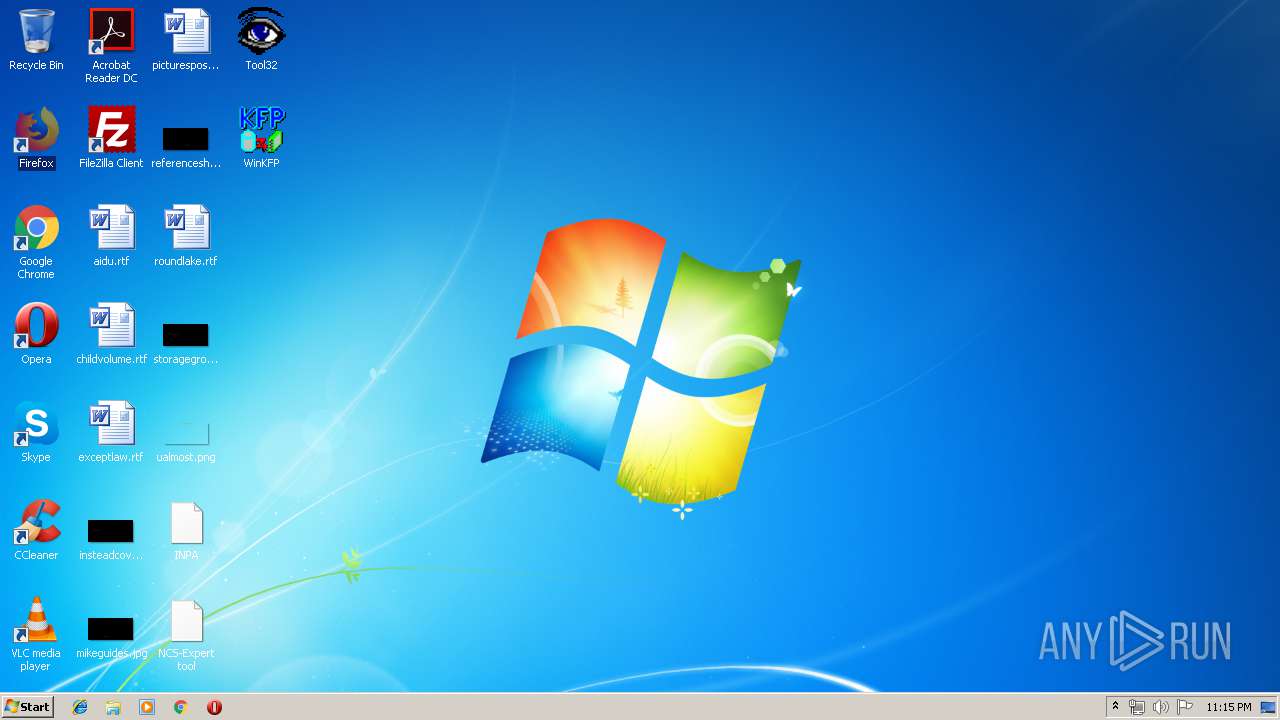
Modifies files in Chrome extension folder
- chrome.exe (PID: 3880)
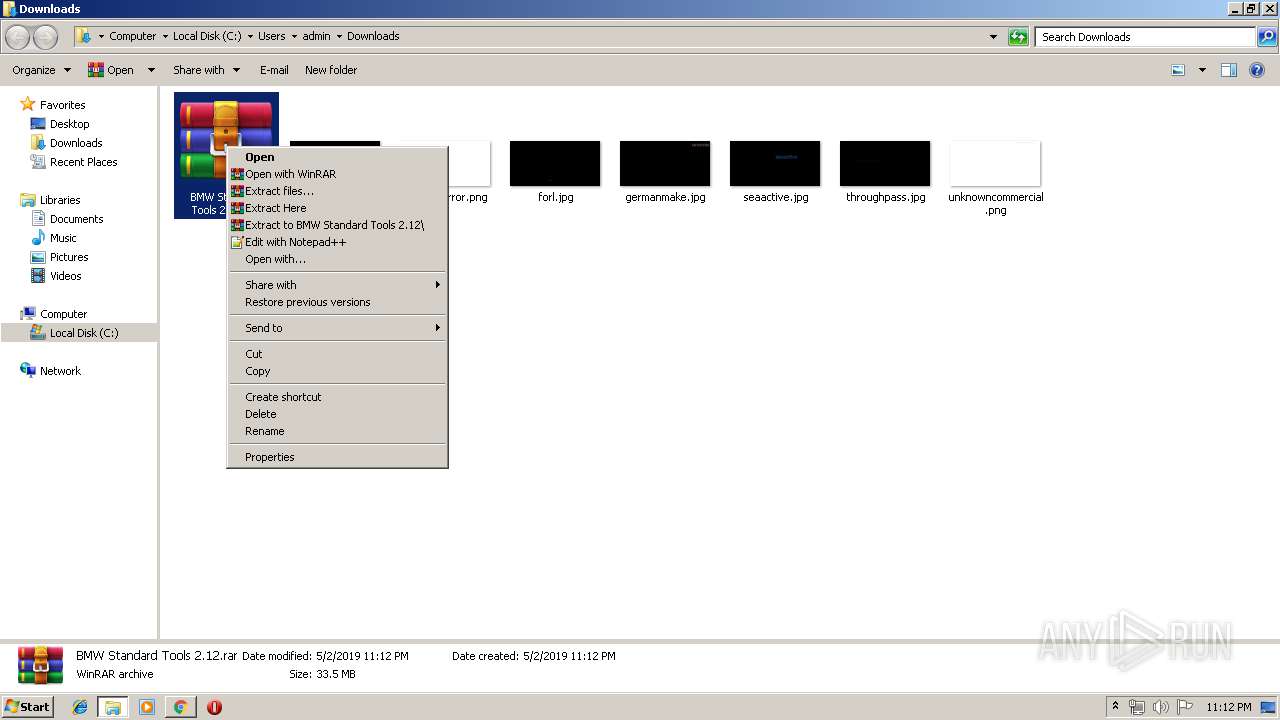
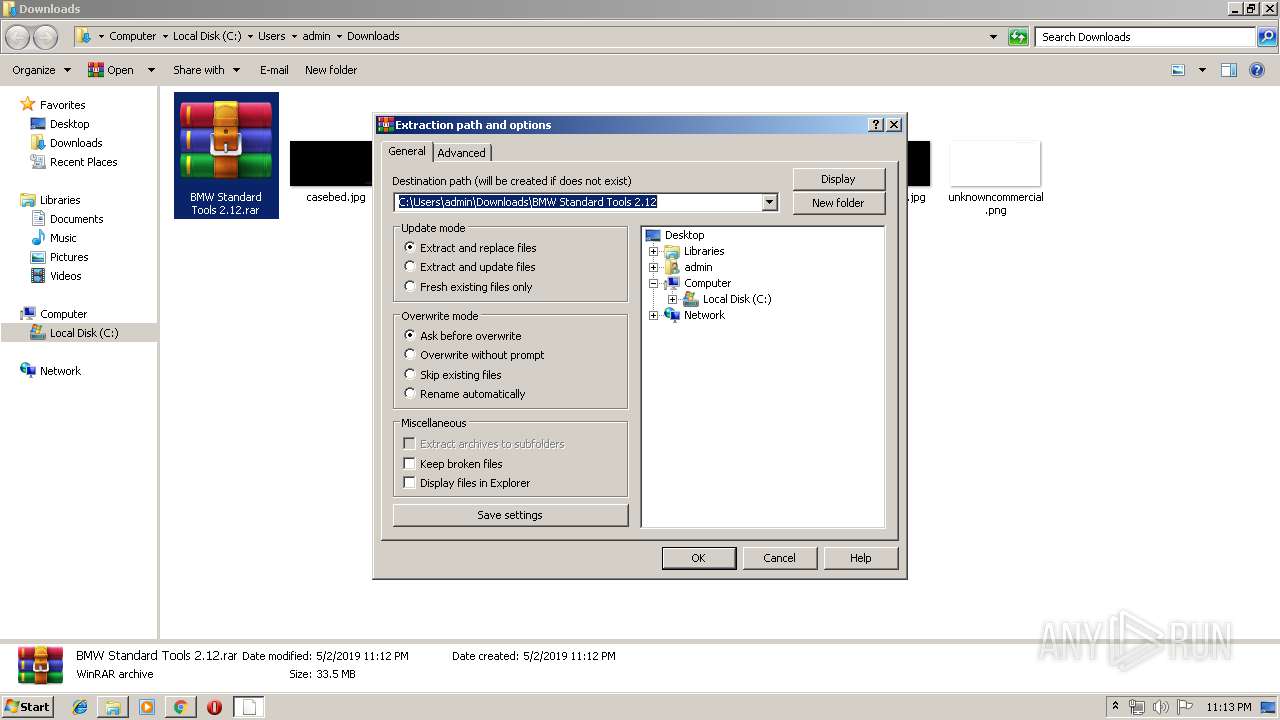
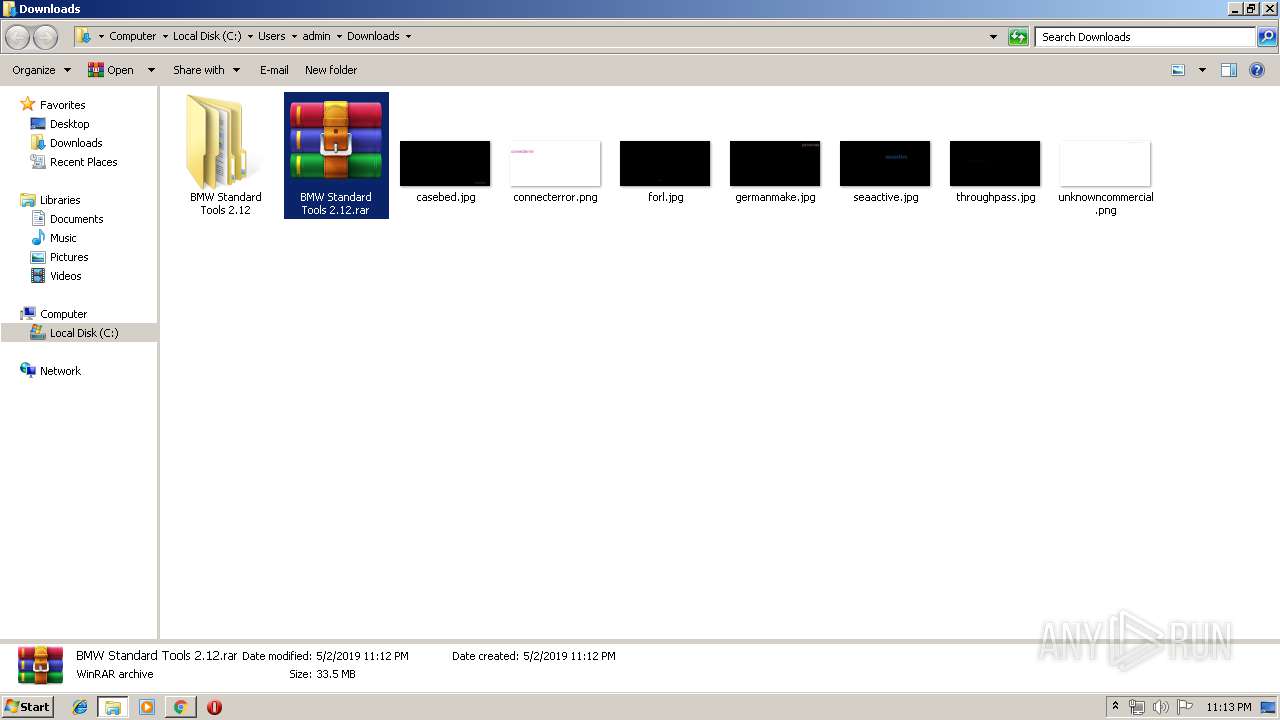
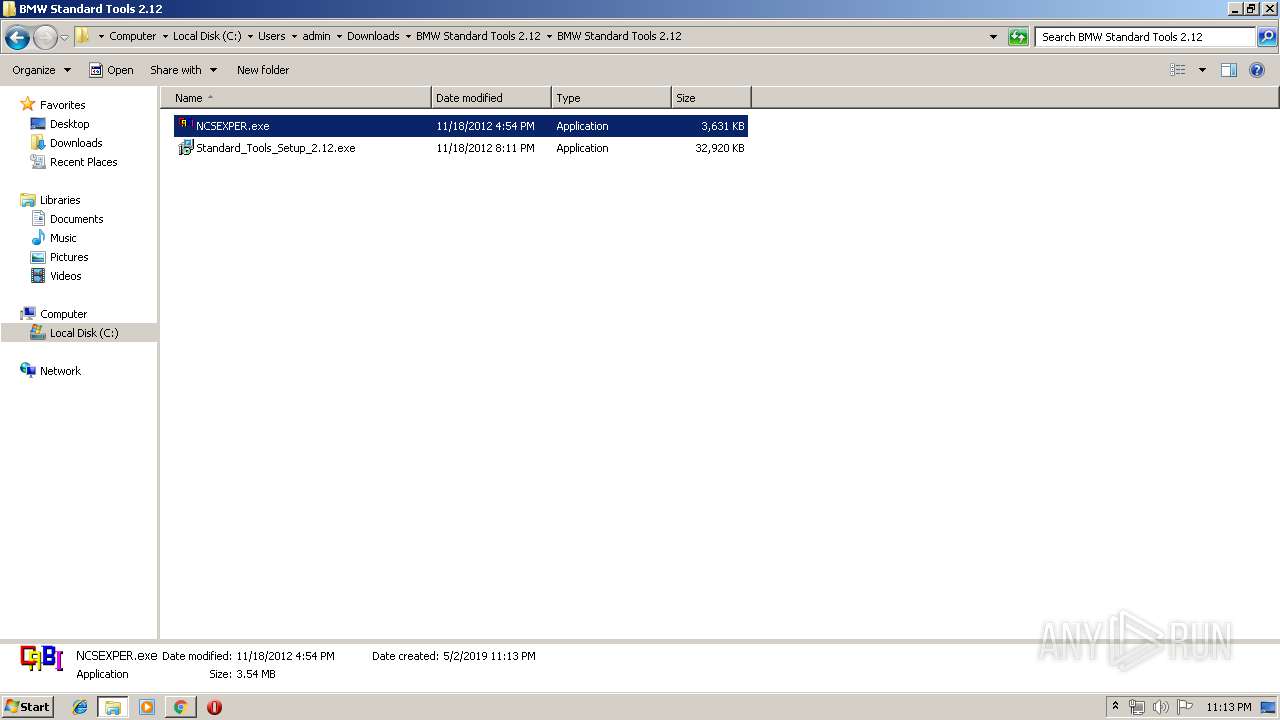
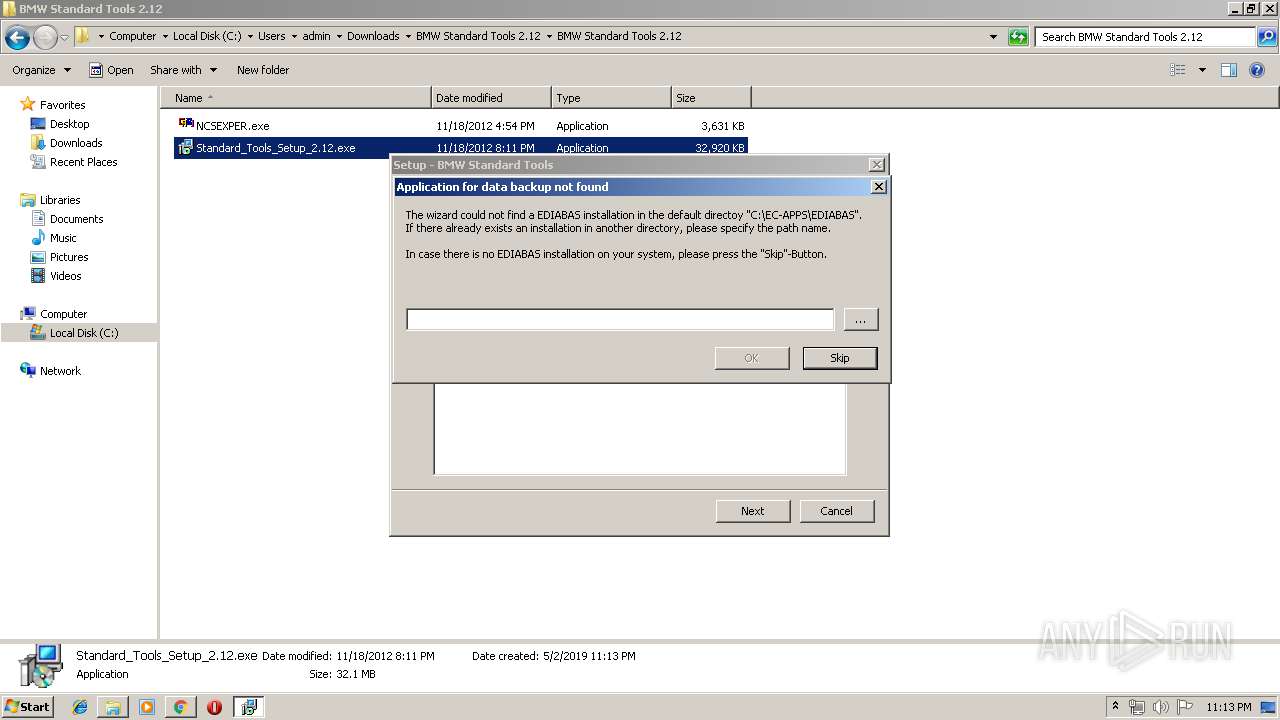
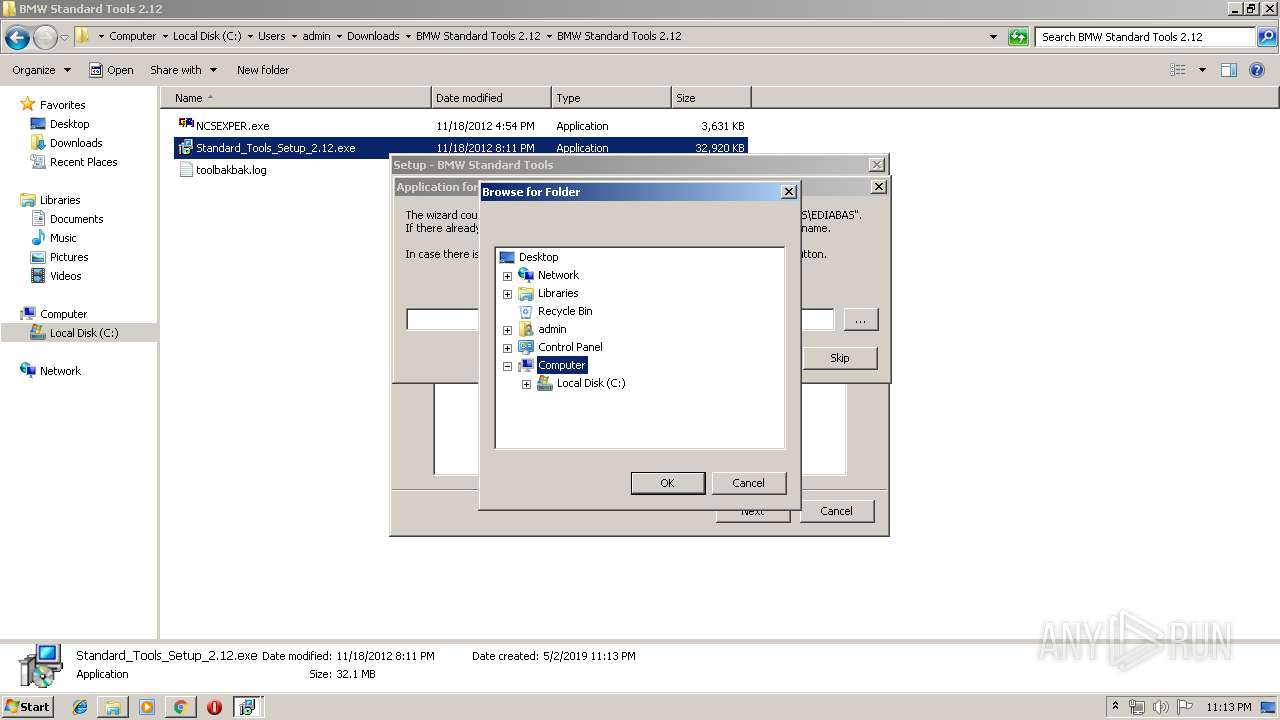
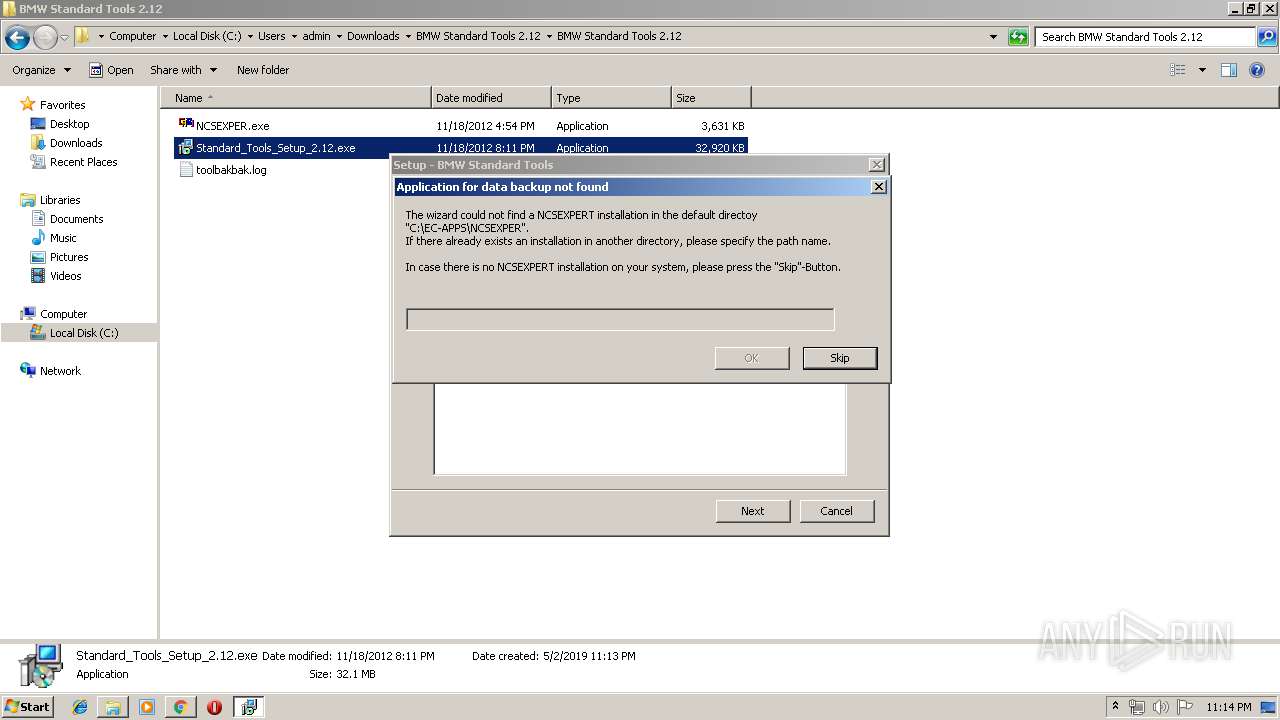
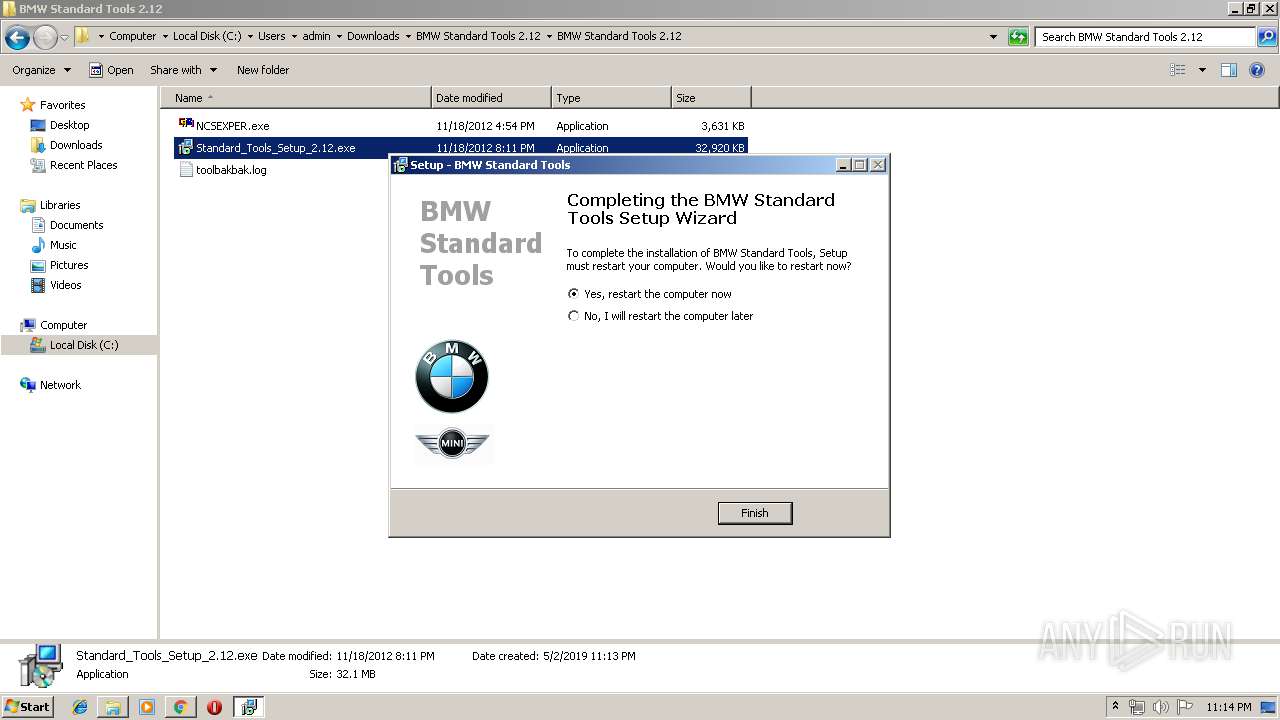
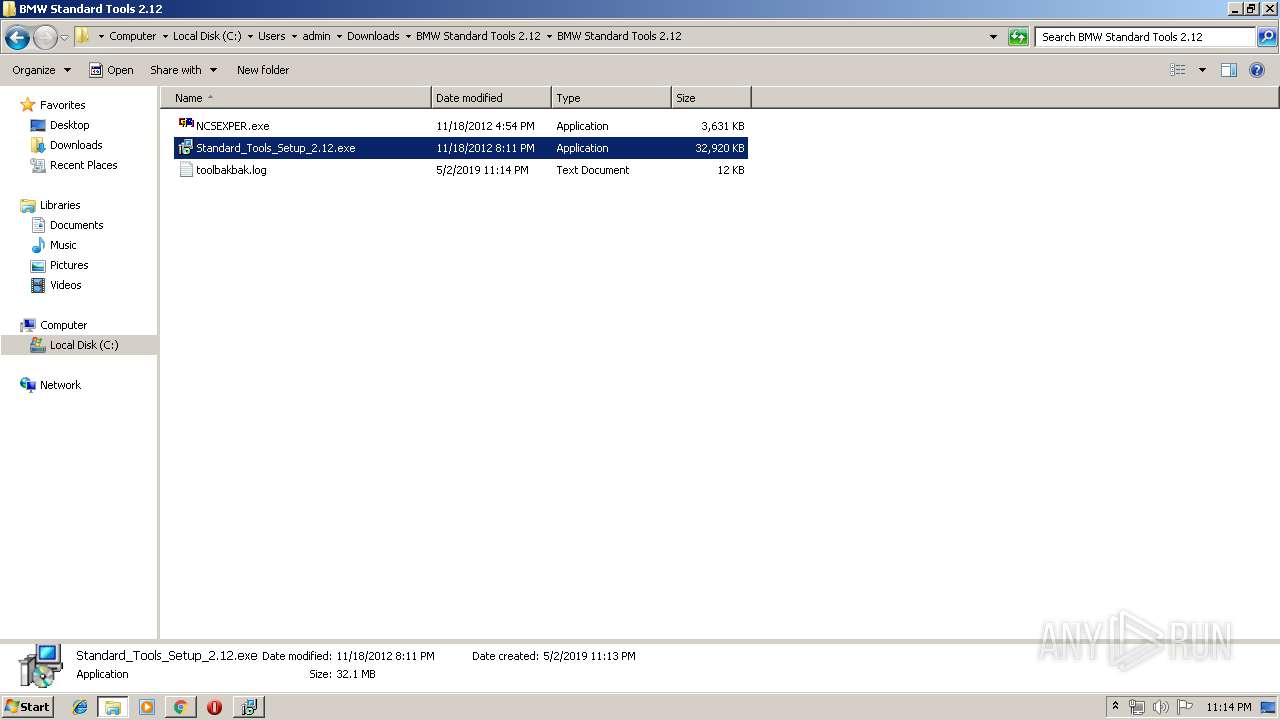
Executable content was dropped or overwritten
- Standard_Tools_Setup_2.12.exe (PID: 2600)
- Standard_Tools_Setup_2.12.exe (PID: 1636)
- WinRAR.exe (PID: 2960)
- Standard_Tools_Setup_2.12.tmp (PID: 1536)
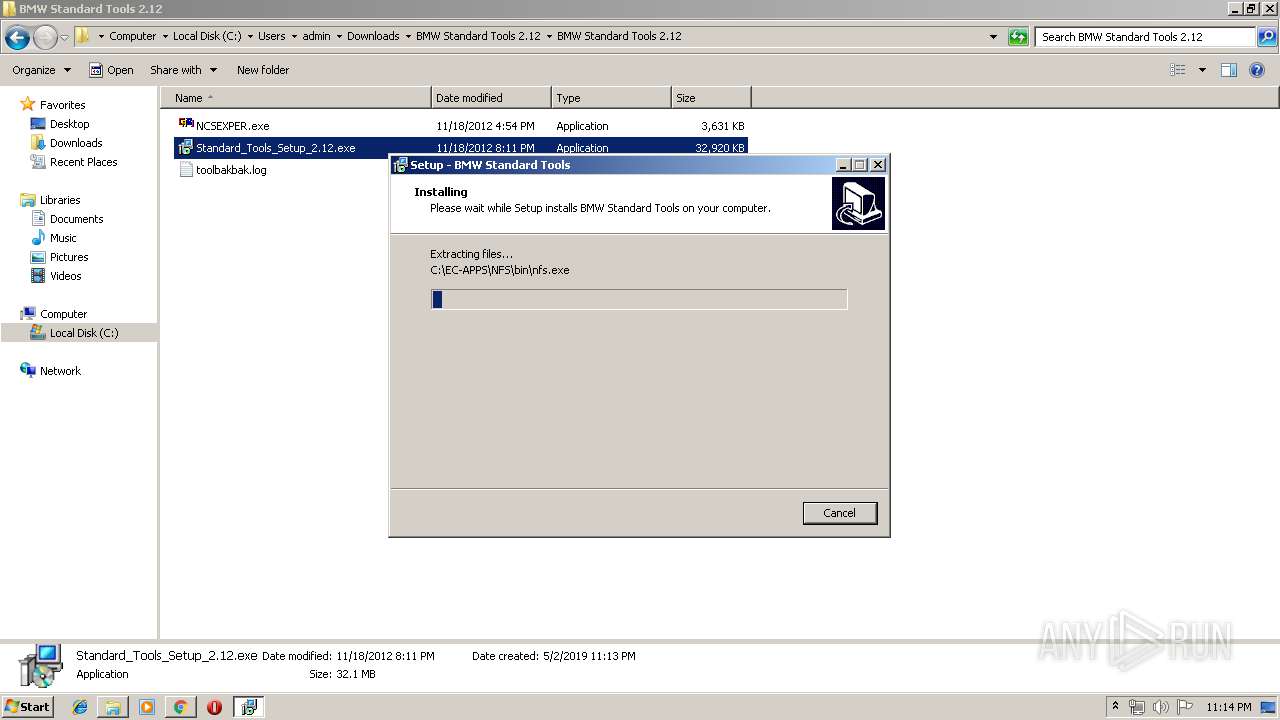
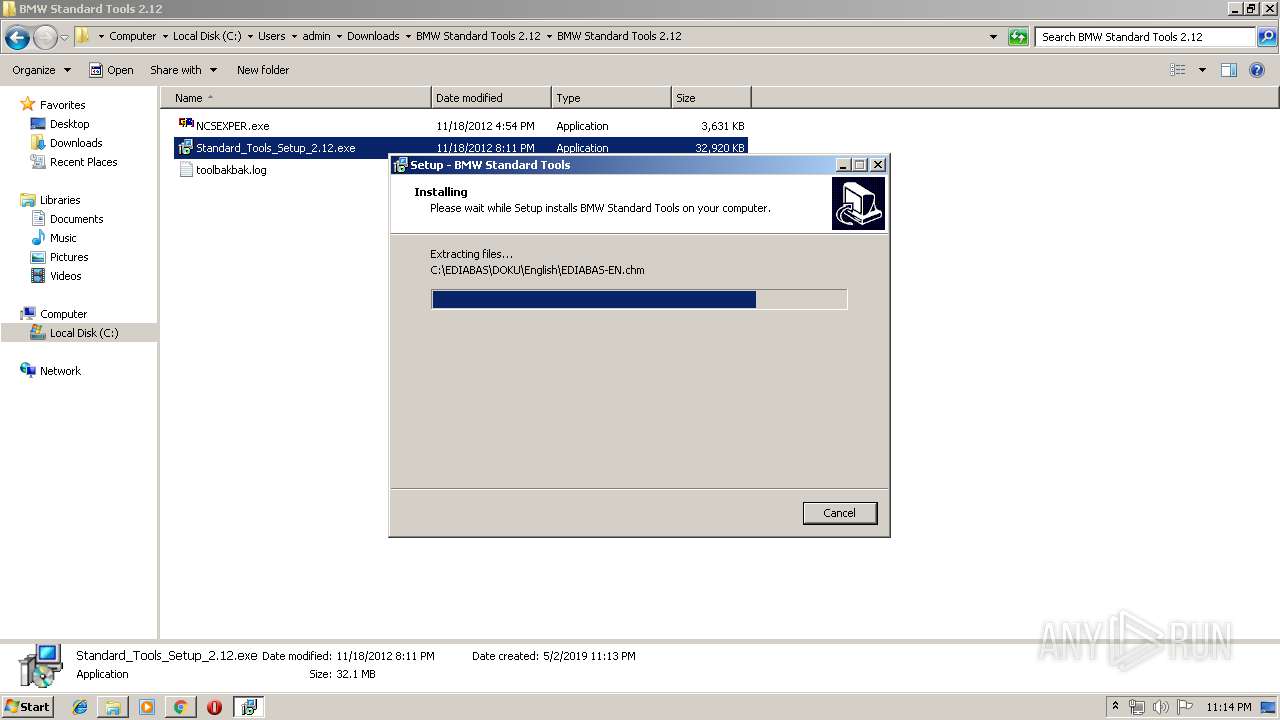
Creates files in the Windows directory
- Standard_Tools_Setup_2.12.tmp (PID: 1536)
Creates files in the user directory
- Standard_Tools_Setup_2.12.tmp (PID: 1536)
Starts CMD.EXE for commands execution
- Standard_Tools_Setup_2.12.tmp (PID: 1536)
Creates or modifies windows services
- Standard_Tools_Setup_2.12.tmp (PID: 1536)
INFO
Application launched itself
- chrome.exe (PID: 3880)
Application was dropped or rewritten from another process
- Standard_Tools_Setup_2.12.tmp (PID: 2532)
- Standard_Tools_Setup_2.12.tmp (PID: 1536)
- envinst.exe (PID: 1656)
- envinst.exe (PID: 3428)
Loads dropped or rewritten executable
- Standard_Tools_Setup_2.12.tmp (PID: 1536)
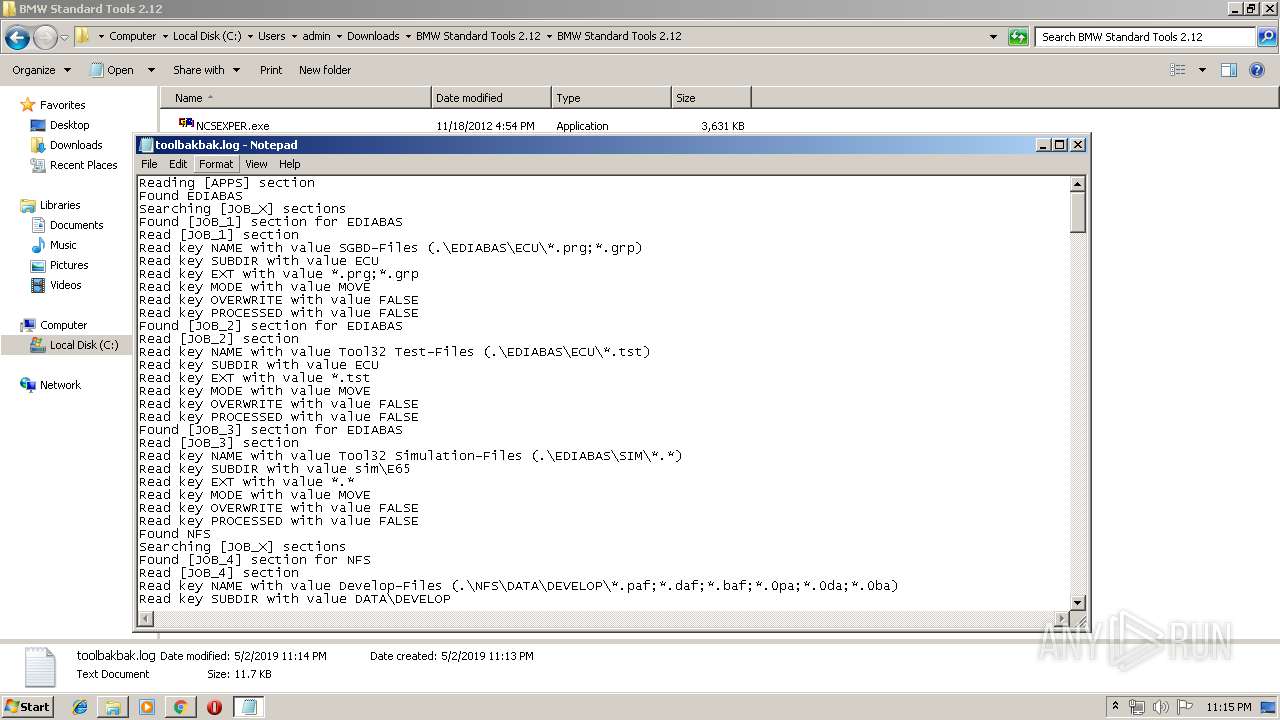
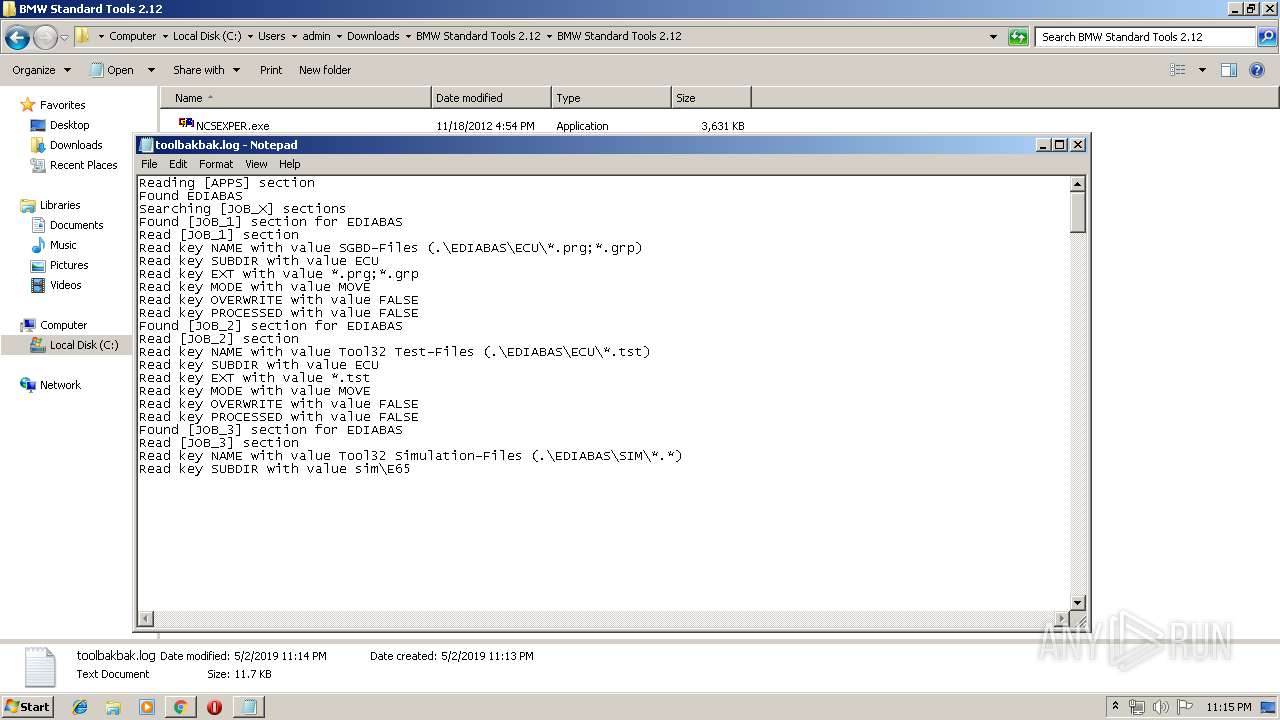
Dropped object may contain Bitcoin addresses
- Standard_Tools_Setup_2.12.tmp (PID: 1536)
Creates files in the program directory
- Standard_Tools_Setup_2.12.tmp (PID: 1536)
Creates a software uninstall entry
- Standard_Tools_Setup_2.12.tmp (PID: 1536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
94
Monitored processes
50
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3888 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14062609751235198334 --mojo-platform-channel-handle=6160 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14956340544507894595 --mojo-platform-channel-handle=3384 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8788986143574911879 --mojo-platform-channel-handle=2016 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
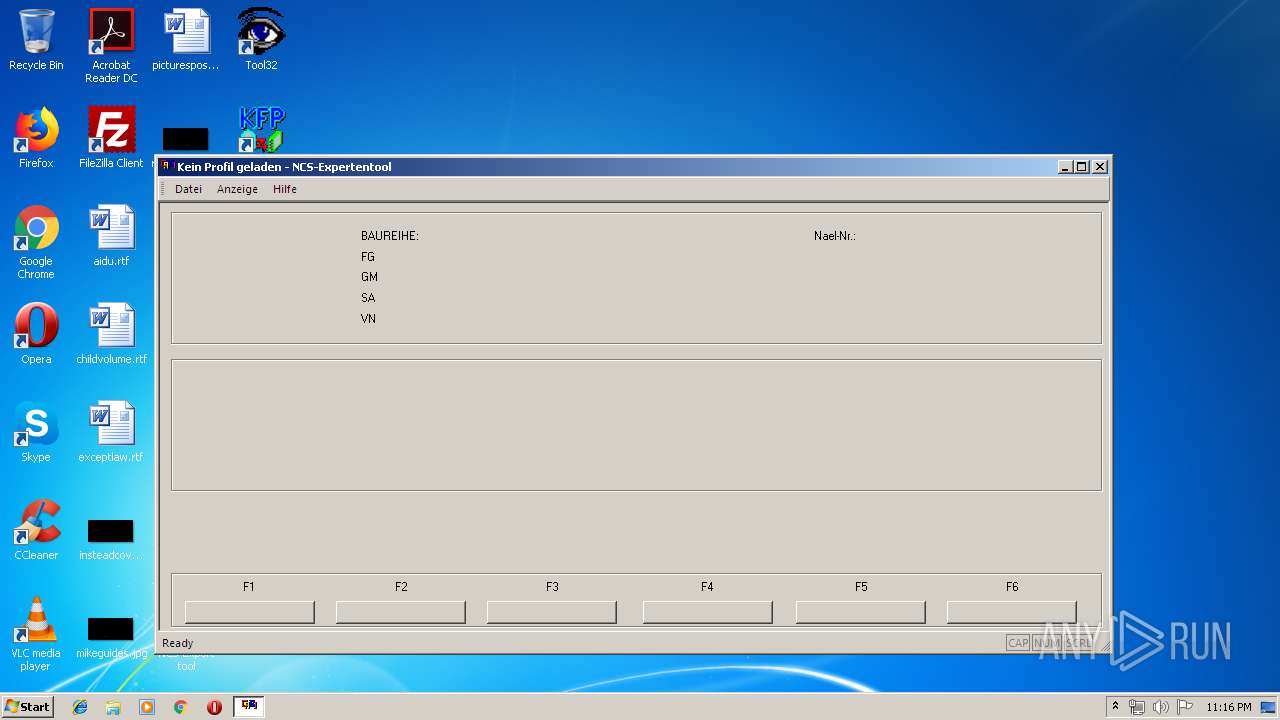
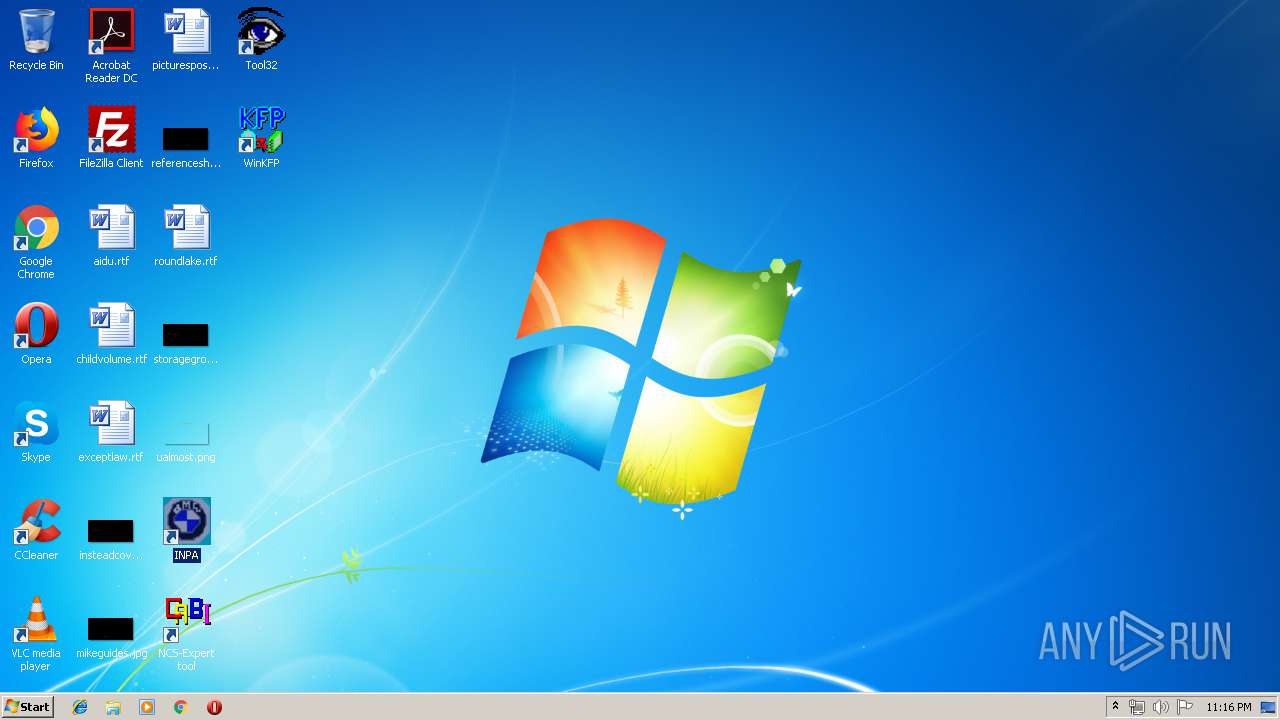
| 892 | "C:\NCSEXPER\BIN\NCSEXPER.exe" | C:\NCSEXPER\BIN\NCSEXPER.exe | — | explorer.exe | |||||||||||
User: admin Company: Softing Project Services GmbH Integrity Level: MEDIUM Description: NCS-Expertentool Exit code: 0 Version: 4.0.1.0 Modules
| |||||||||||||||
| 1060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6632360934180166340 --mojo-platform-channel-handle=6404 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1256 | net stop carserver | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14130454634220161862 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14130454634220161862 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6352 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17152363334188467644 --mojo-platform-channel-handle=944 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
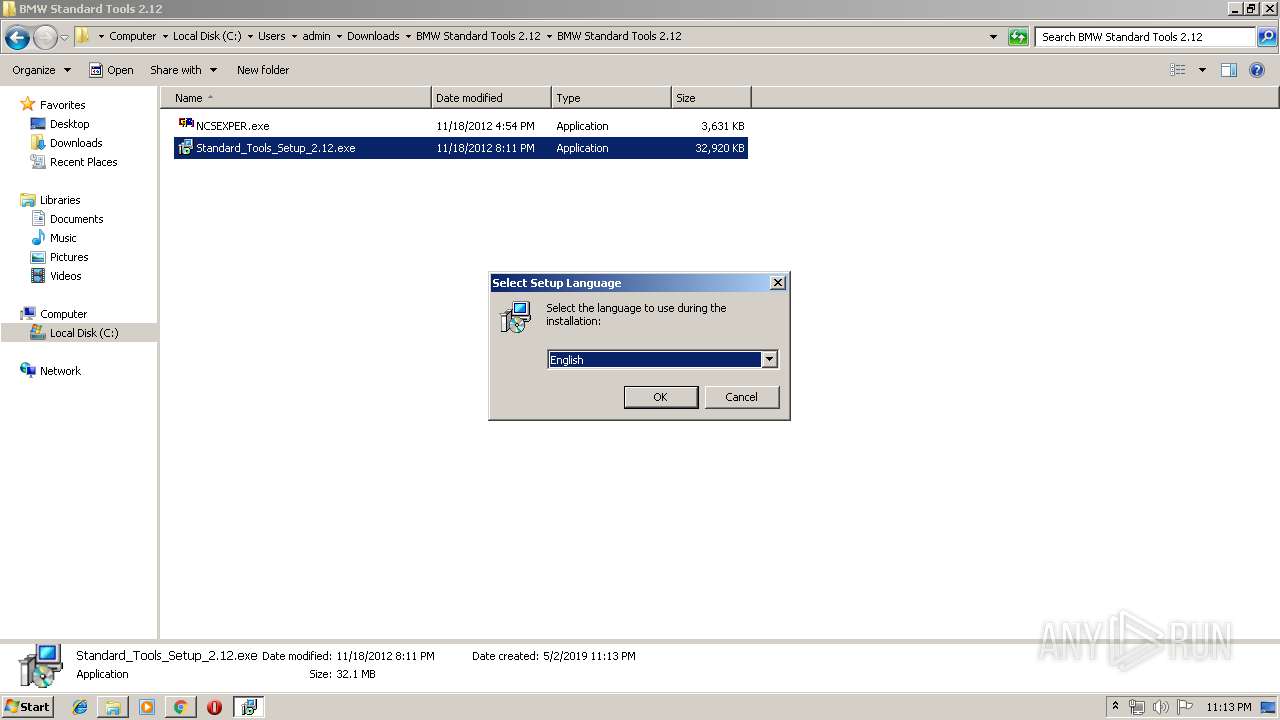
| 1536 | "C:\Users\admin\AppData\Local\Temp\is-QG0UF.tmp\Standard_Tools_Setup_2.12.tmp" /SL5="$501D4,33407133,54272,C:\Users\admin\Downloads\BMW Standard Tools 2.12\BMW Standard Tools 2.12\Standard_Tools_Setup_2.12.exe" /SPAWNWND=$500EC /NOTIFYWND=$501E6 | C:\Users\admin\AppData\Local\Temp\is-QG0UF.tmp\Standard_Tools_Setup_2.12.tmp | Standard_Tools_Setup_2.12.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
1 797
Read events
1 587
Write events
198
Delete events
12
Modification events
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3880-13201308737581875 |
Value: 259 | |||
Executable files
123
Suspicious files
195
Text files
300
Unknown types
53
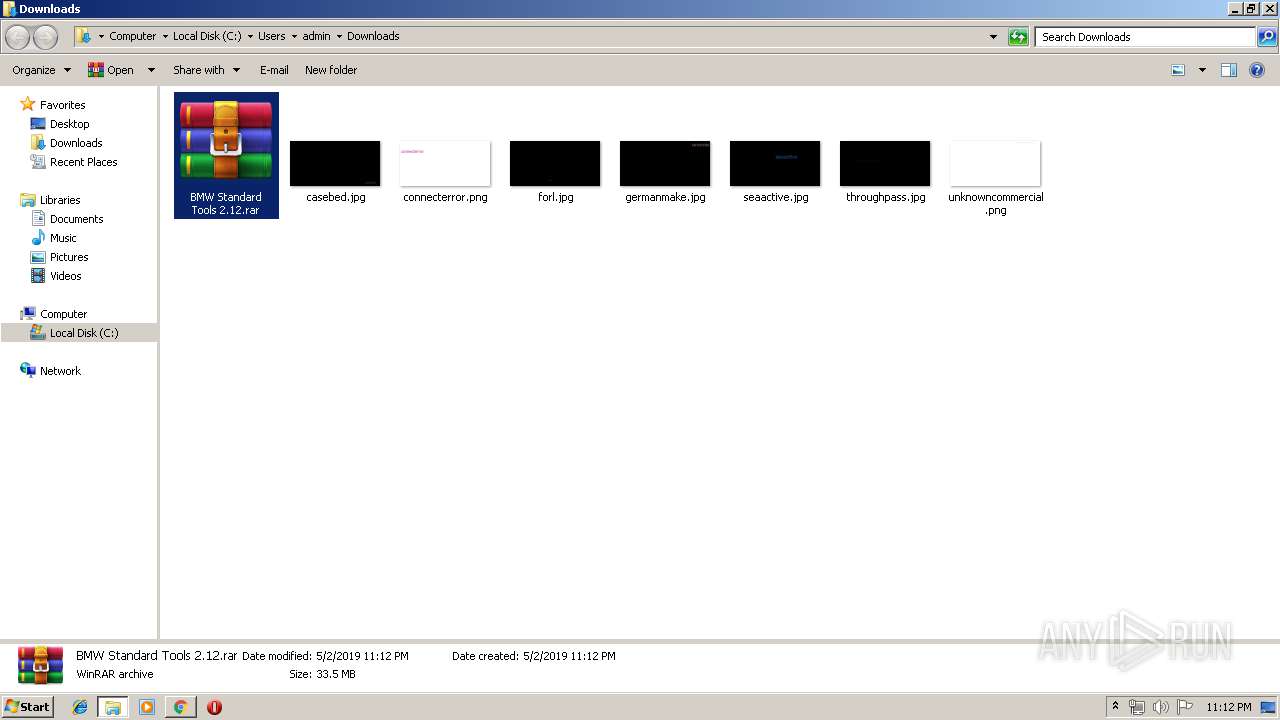
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b347af01-10c4-42f9-bebe-2f24cd9b4336.tmp | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
86
TCP/UDP connections
130
DNS requests
84
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3880 | chrome.exe | GET | 200 | 104.19.194.29:80 | http://www.mediafire.com/file/qldyddn48ffzrwn/BMW+Standard+Tools+2.12.rar | US | html | 48.5 Kb | shared |
3880 | chrome.exe | GET | 200 | 104.19.194.29:80 | http://www.mediafire.com/images/icons/svg_light/icons_sprite.svg | US | image | 8.19 Kb | shared |
3880 | chrome.exe | GET | 200 | 104.19.195.29:80 | http://static.mediafire.com/images/backgrounds/download/apps_list_sprite-v3.png | US | image | 7.36 Kb | shared |
3880 | chrome.exe | GET | 200 | 172.217.22.14:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | text | 726 b | whitelisted |
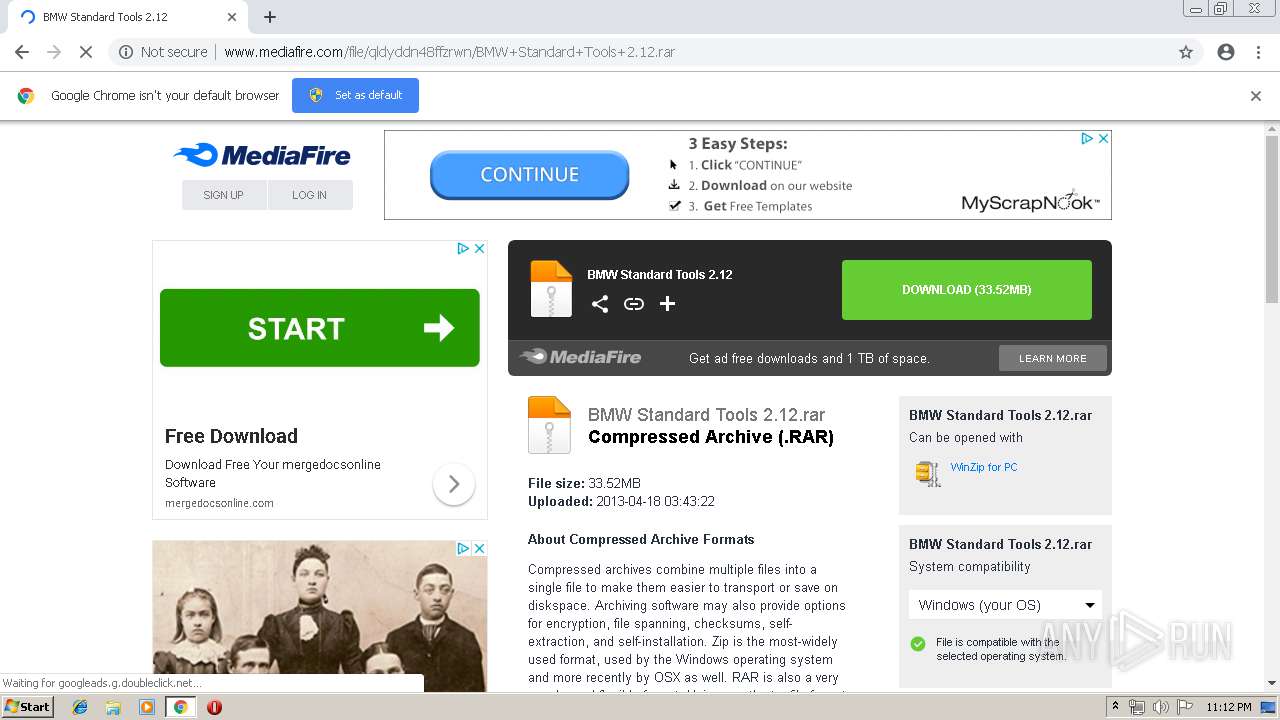
3880 | chrome.exe | GET | 200 | 104.18.92.64:80 | http://cdn.engine.addroplet.com/Scripts/infinity.js.aspx?guid=5ff0fb62-0643-4ff1-aaee-c737f9ffc0e0 | US | text | 71.6 Kb | whitelisted |
3880 | chrome.exe | GET | 200 | 104.19.194.29:80 | http://www.mediafire.com/templates/linkto/ads.php?o=0&d=1&t=0 | US | html | 3.25 Kb | shared |
3880 | chrome.exe | GET | 302 | 2.16.186.51:80 | http://b.scorecardresearch.com/b?c1=8&c2=18203330&rn=0.6006802448688517&c7=http%3A%2F%2Fwww.mediafire.com%2Ffile%2Fqldyddn48ffzrwn%2FBMW%2BStandard%2BTools%2B2.12.rar&c3=1&c4=&c5=&c6=&c10=&c15=&c16=&c8=BMW%20Standard%20Tools%202.12&c9=&cv=1.8 | unknown | compressed | 708 b | whitelisted |
3880 | chrome.exe | GET | 200 | 104.18.92.64:80 | http://cdn.engine.addroplet.com/Scripts/MediaScripts/b.js?v=4 | US | text | 66.1 Kb | whitelisted |
3880 | chrome.exe | GET | 200 | 172.217.22.98:80 | http://www.googletagservices.com/tag/js/gpt.js | US | text | 10.3 Kb | whitelisted |
3880 | chrome.exe | GET | 200 | 104.19.195.29:80 | http://static.mediafire.com/images/filetype/file-zip-v3.png | US | image | 1.83 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3880 | chrome.exe | 104.19.195.29:80 | www.mediafire.com | Cloudflare Inc | US | shared |
3880 | chrome.exe | 172.217.22.14:80 | translate.google.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 172.217.23.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 104.18.92.64:80 | cdn.engine.addroplet.com | Cloudflare Inc | US | shared |
3880 | chrome.exe | 216.58.205.234:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 216.58.205.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 172.217.18.110:443 | google.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 104.17.72.92:80 | cdn.engine.addroplet.com | Cloudflare Inc | US | shared |
3880 | chrome.exe | 2.16.186.51:80 | b.scorecardresearch.com | Akamai International B.V. | — | whitelisted |
3880 | chrome.exe | 172.217.22.98:80 | www.googletagservices.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.mediafire.com |
| shared |
accounts.google.com |
| shared |
www.googletagmanager.com |
| whitelisted |
translate.google.com |
| whitelisted |
static.mediafire.com |
| shared |
download698.mediafire.com |
| suspicious |
facebook.com |
| whitelisted |
blog.mediafire.com |
| whitelisted |
google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3880 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
3880 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
Process | Message |
|---|---|
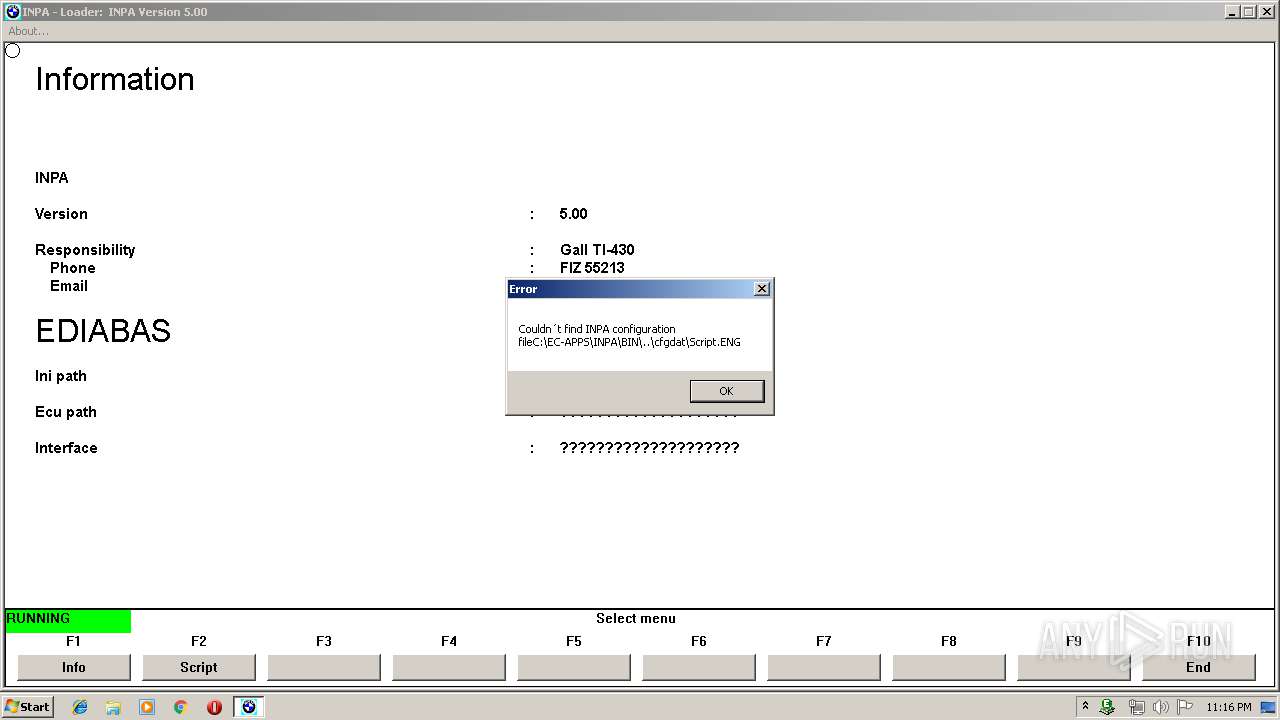
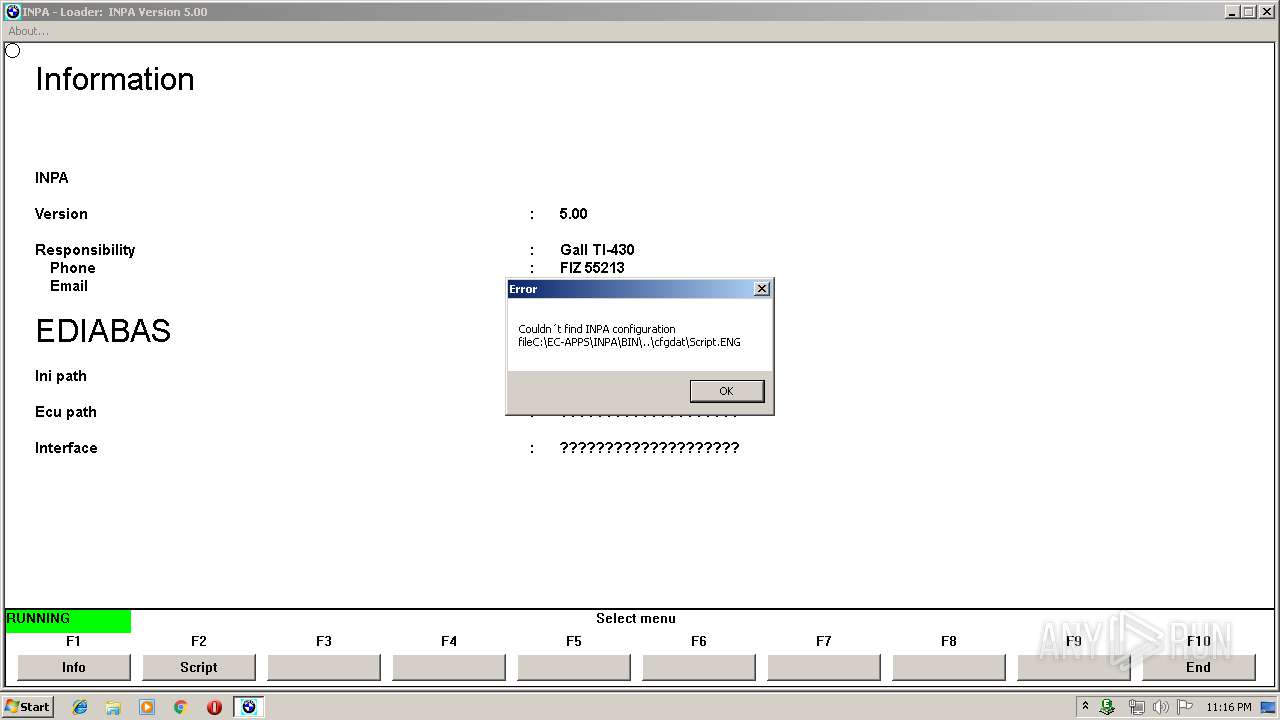
INPALOAD.exe | CStdGateway::Shutdown Kill Gateway thread
|
INPALOAD.exe | CStdGateway::Shutdown Kill Gateway thread
|