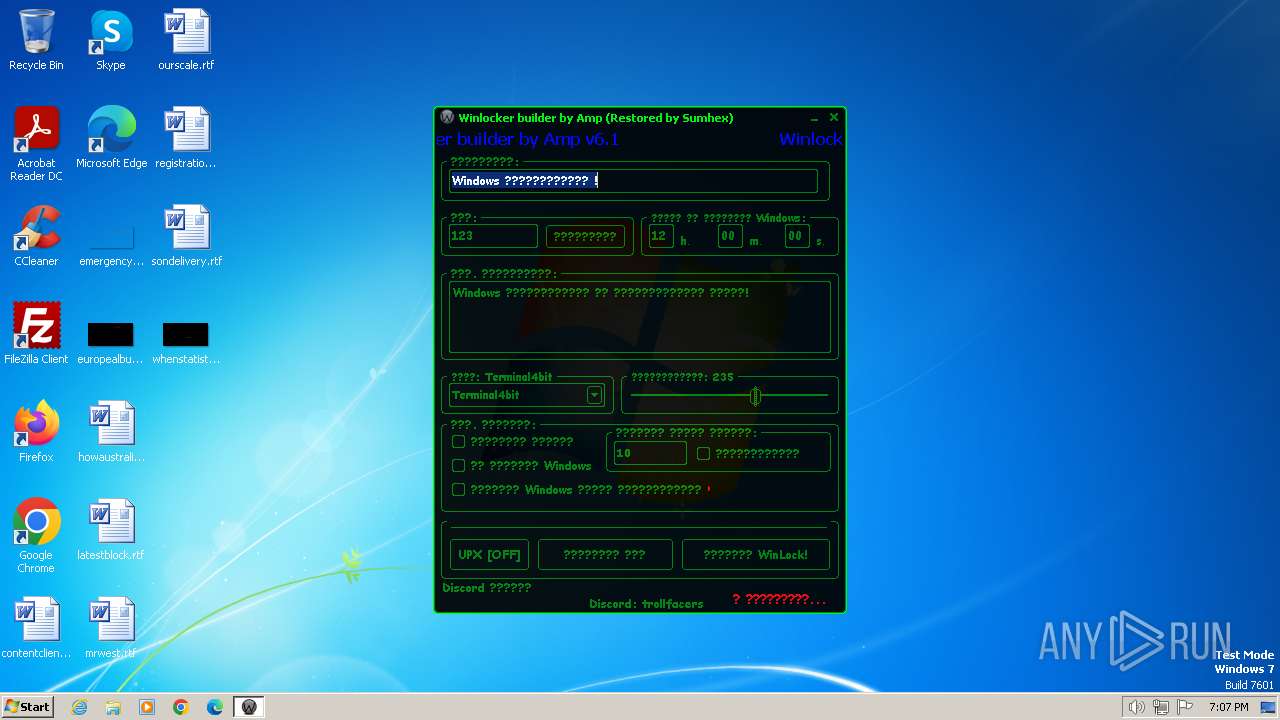
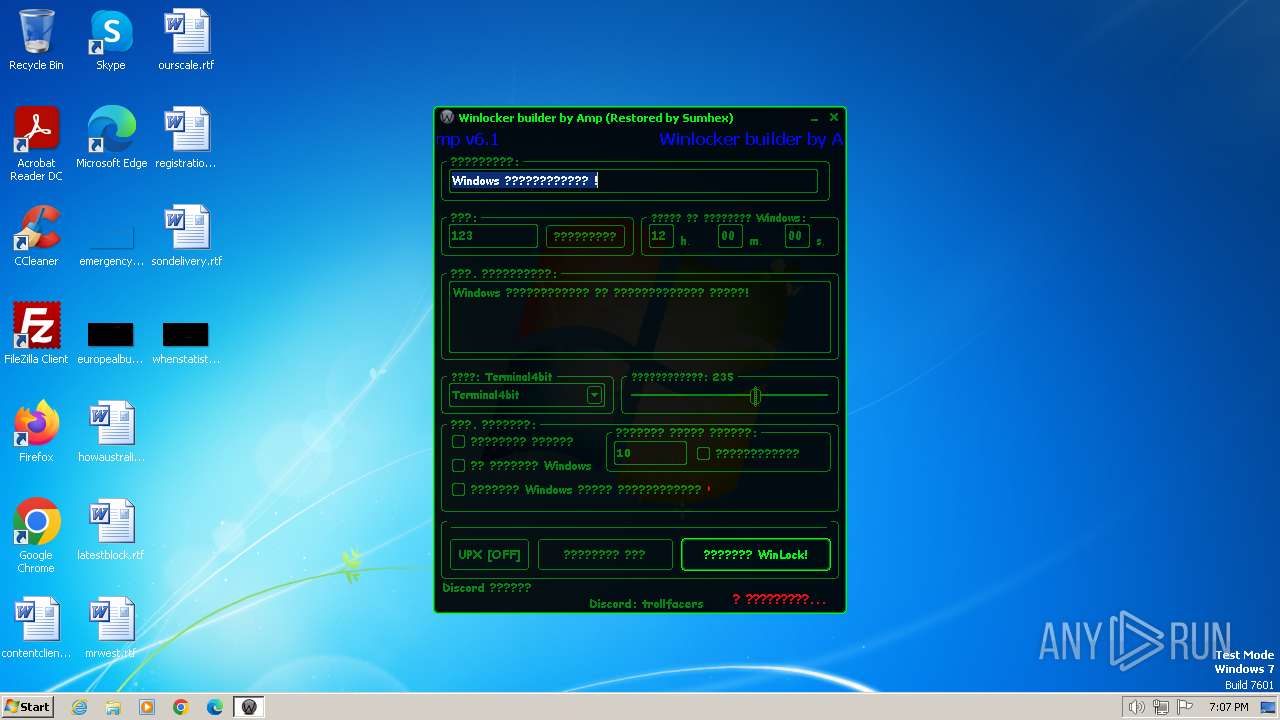
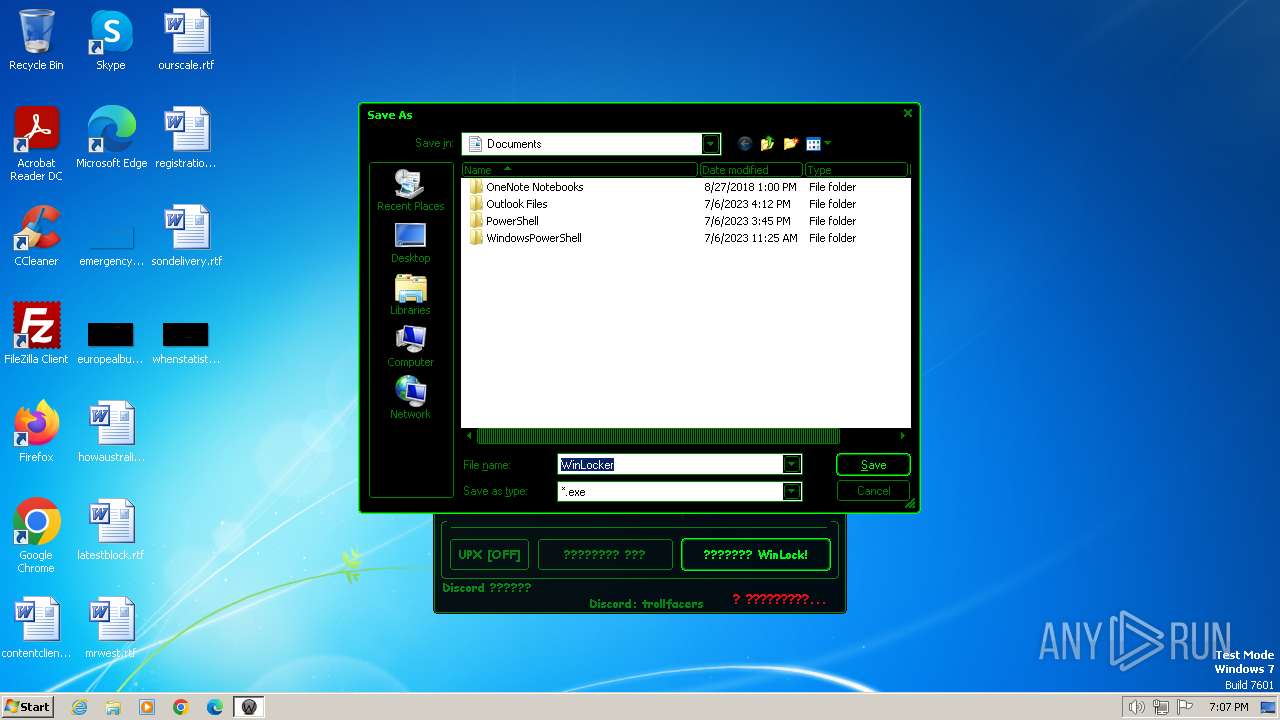
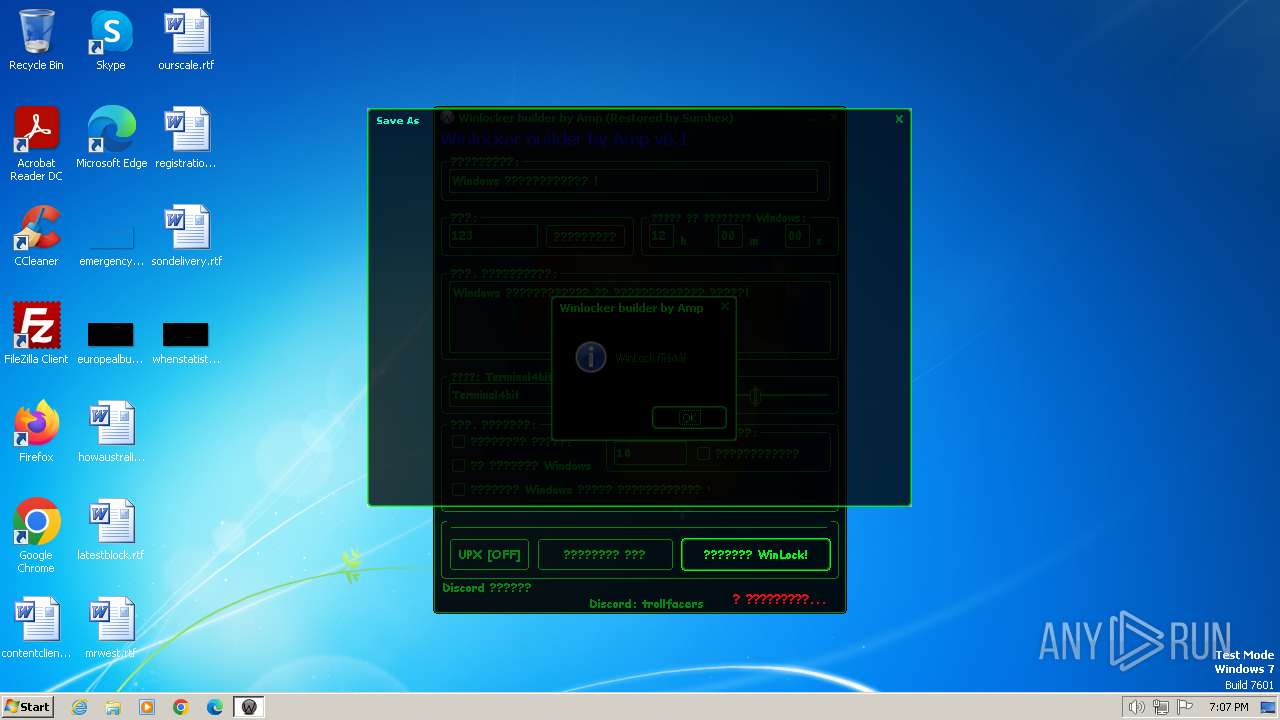
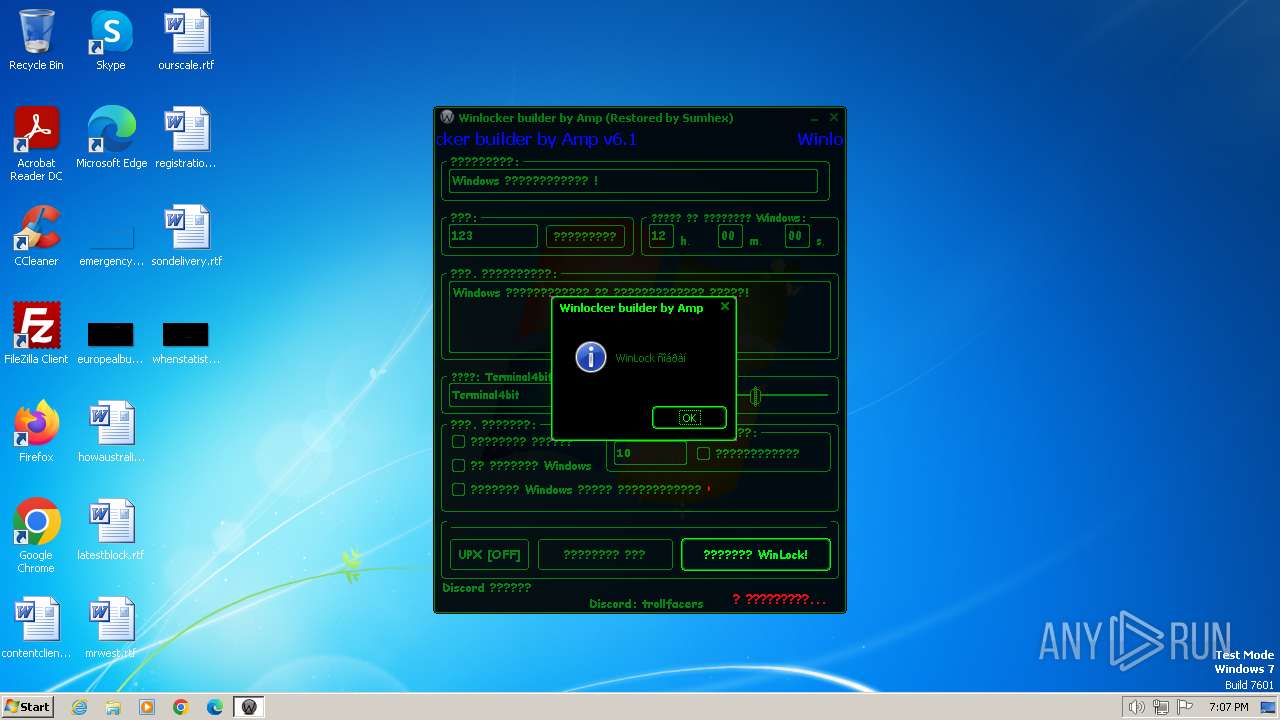
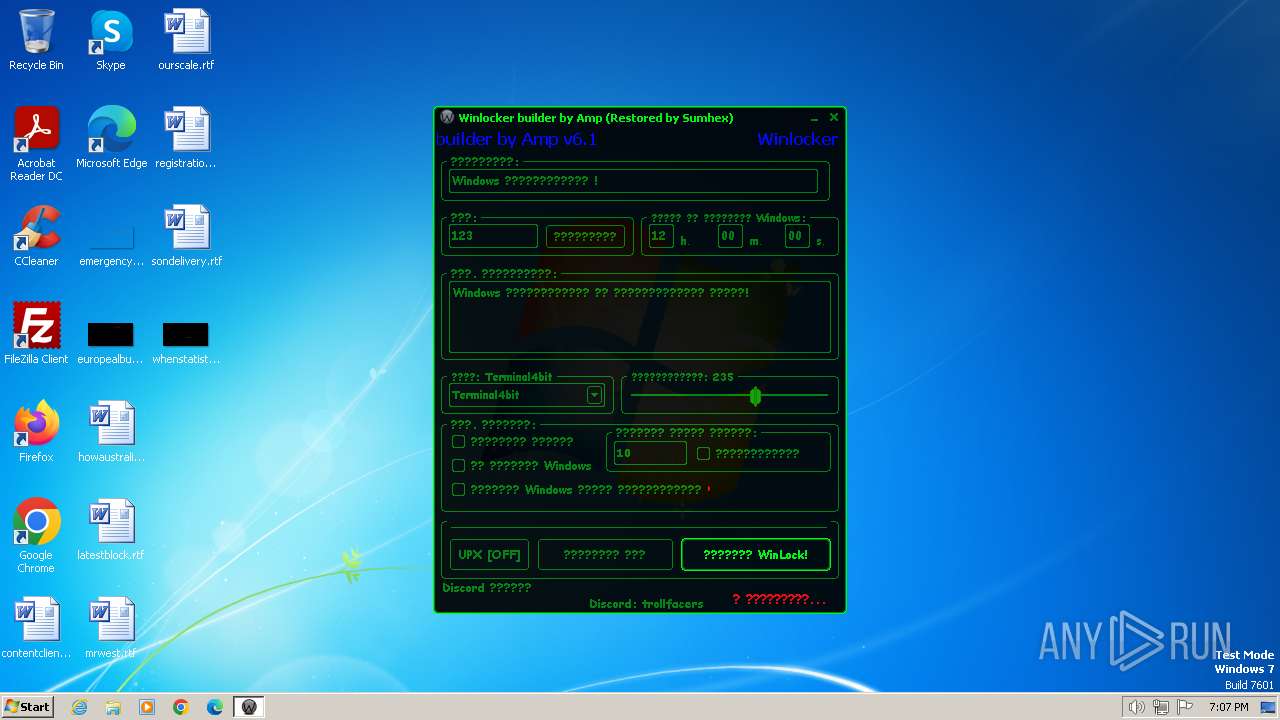
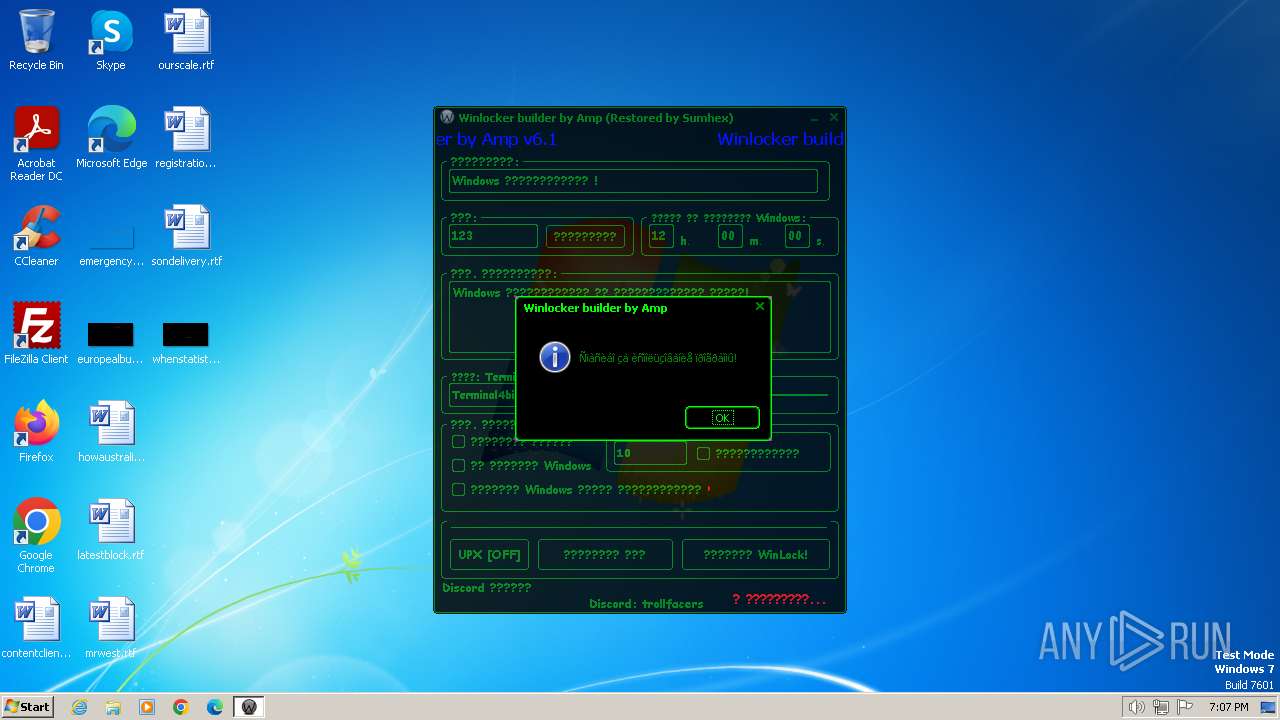
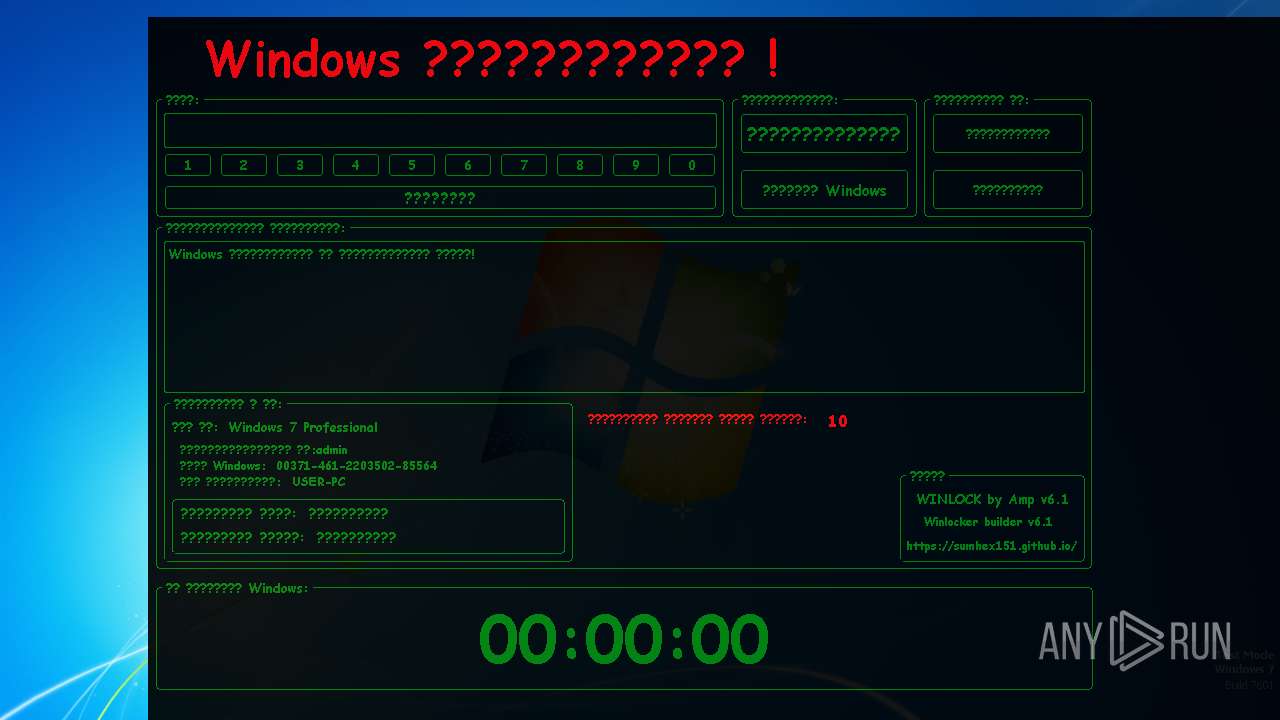
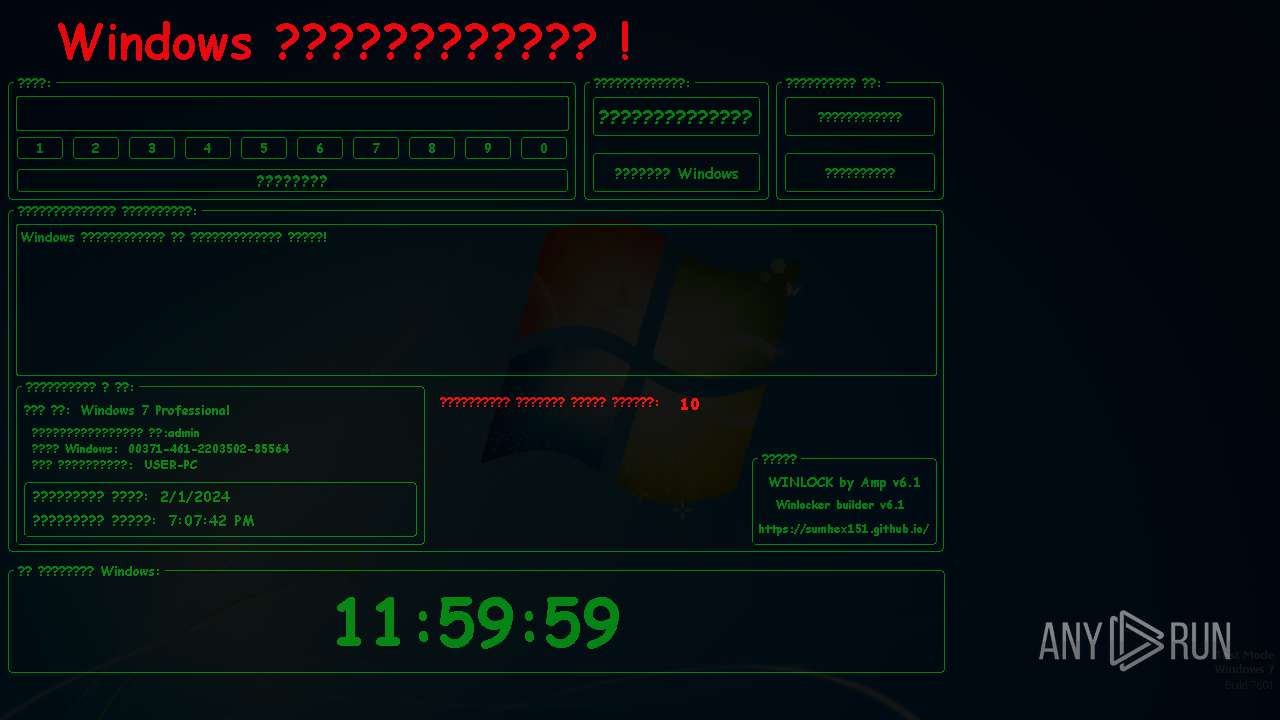
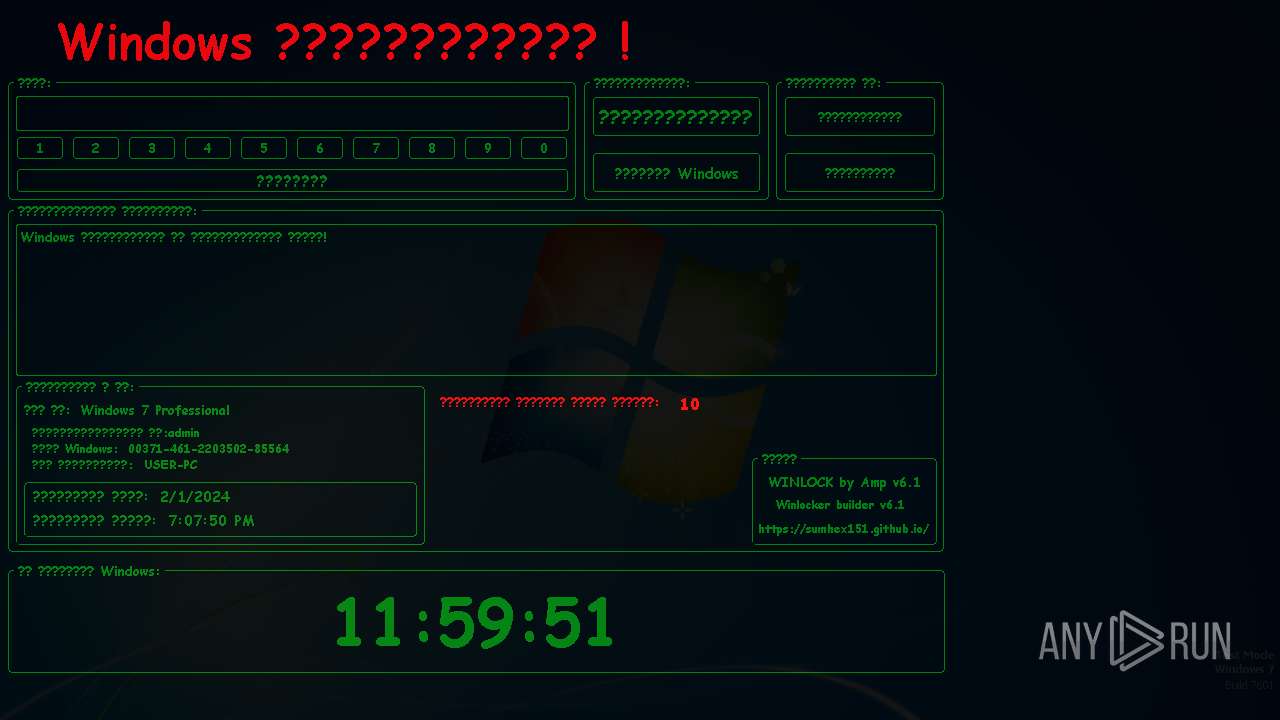
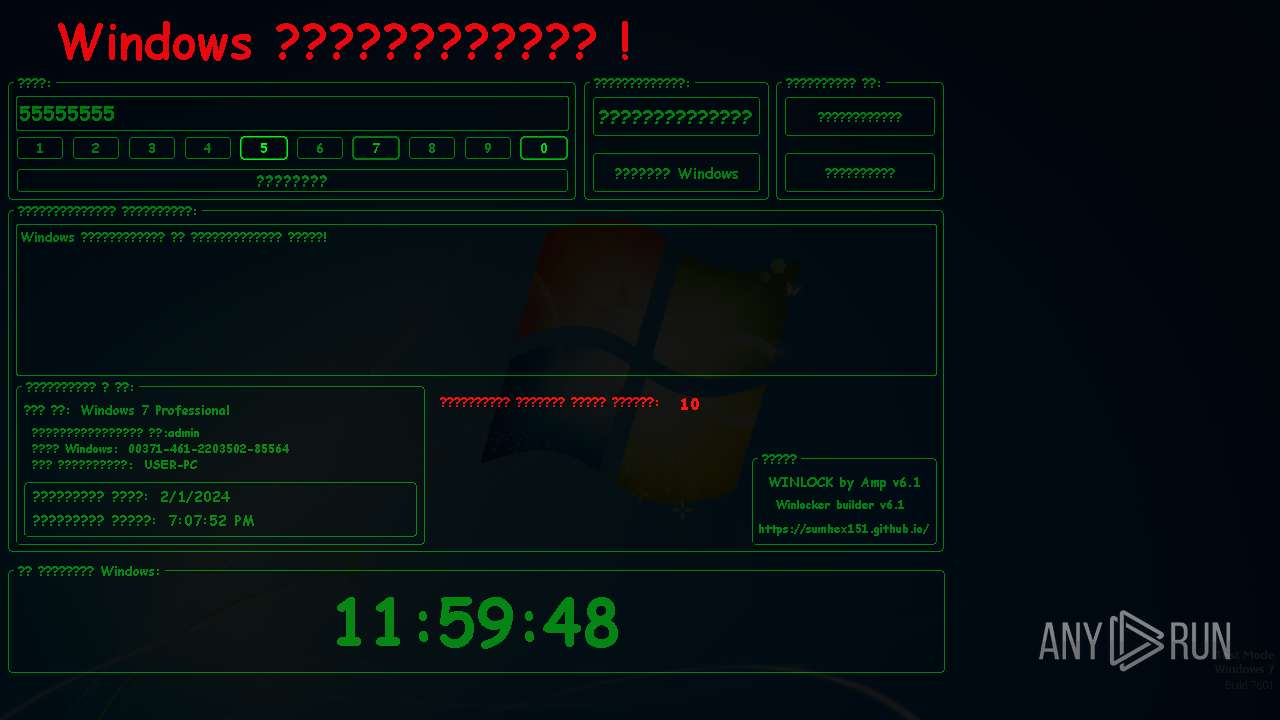
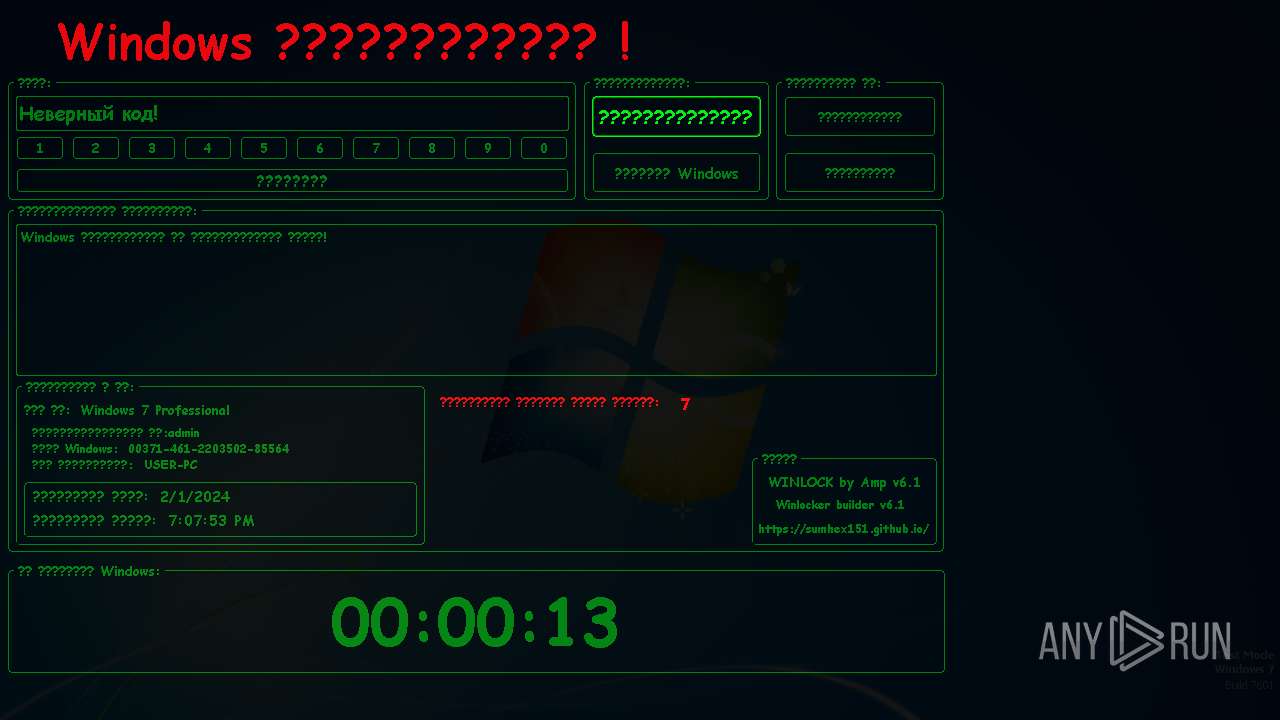
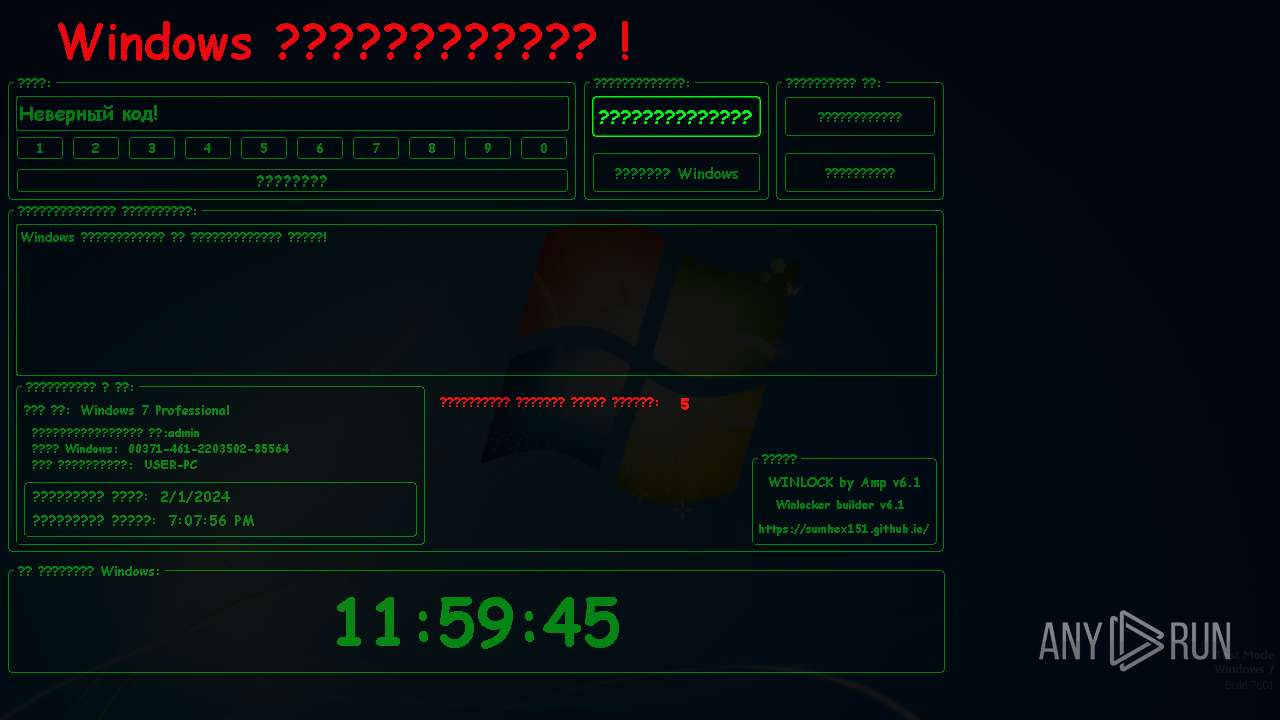
| File name: | Winlocker builder by Amp v6.1.exe |
| Full analysis: | https://app.any.run/tasks/ac7f5fe6-ad01-4fbf-bb44-5d0ac0be6017 |
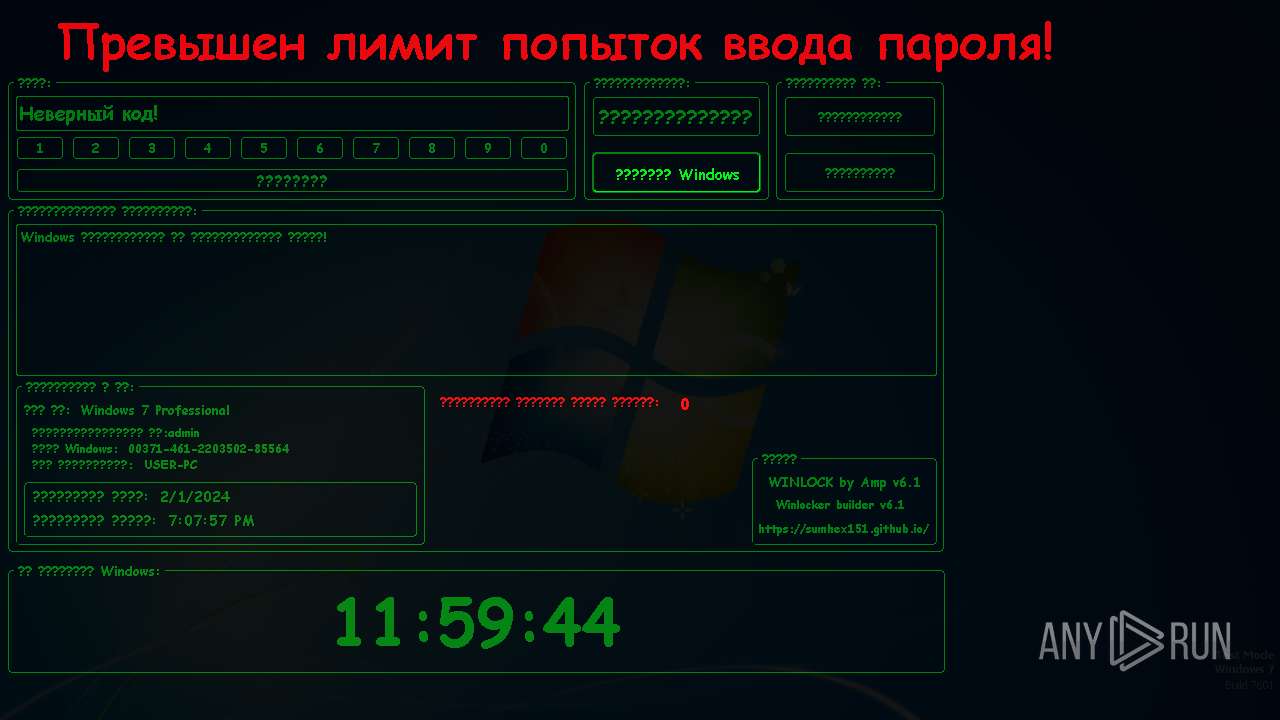
| Verdict: | Malicious activity |
| Analysis date: | February 01, 2024, 19:07:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | FREE-DOS executable (COM), UPX compressed |
| MD5: | E142B5538058CE6B3A93418FAE3FF592 |
| SHA1: | 701F7417E23B45D97D670BB559761F8127642B6C |
| SHA256: | E0690E6BA71039E1BE5161E7E93FFC7A7882F57A5D38E3F7D4E9A8FFCE080F93 |
| SSDEEP: | 98304:8/DGbDy5BTb/R6y6SD6n6wh9bc2YGF7nJnC7JHXoNLquNkW5kQf57//pfRkMva/w:5ijhG |
MALICIOUS
Drops the executable file immediately after the start
- Winlocker builder by Amp v6.1.exe (PID: 1264)
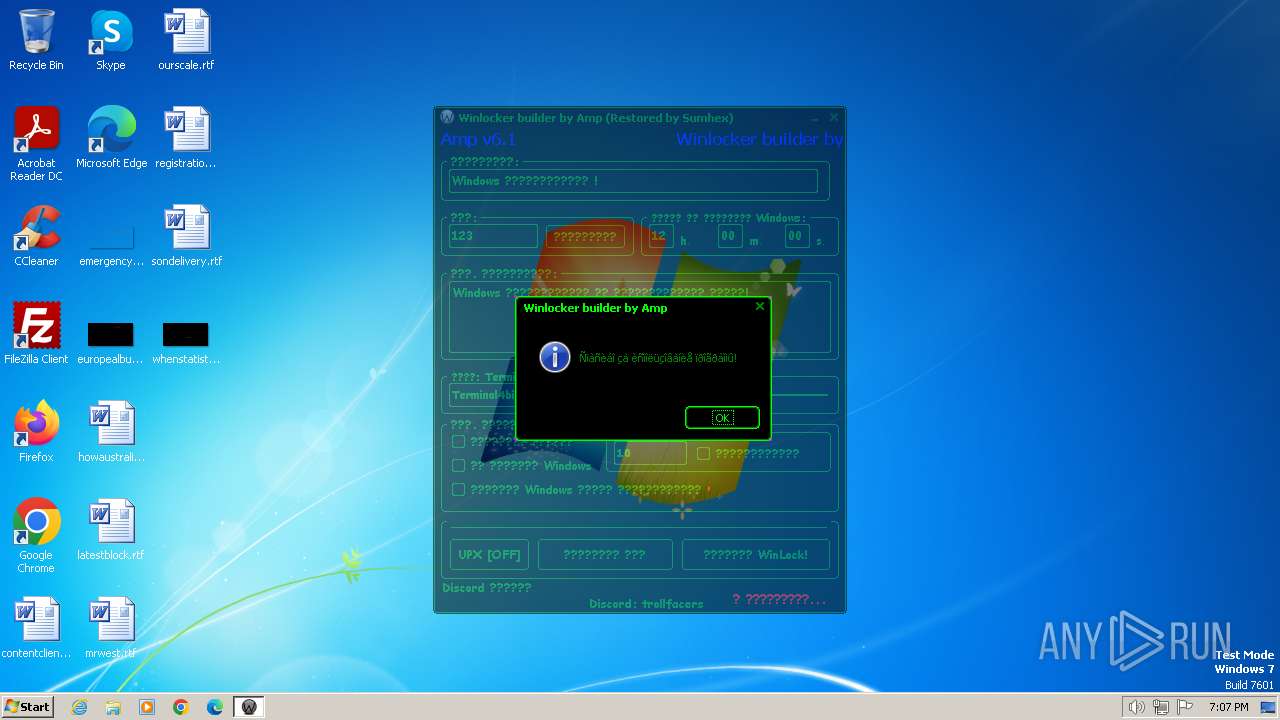
UAC/LUA settings modification
- WinLocker.exe (PID: 2228)
SUSPICIOUS
Reads the Internet Settings
- Winlocker builder by Amp v6.1.exe (PID: 1264)
Executable content was dropped or overwritten
- Winlocker builder by Amp v6.1.exe (PID: 1264)
Reads the Windows owner or organization settings
- WinLocker.exe (PID: 2228)
INFO
Checks supported languages
- Winlocker builder by Amp v6.1.exe (PID: 1264)
- WinLocker.exe (PID: 2228)
Reads the machine GUID from the registry
- Winlocker builder by Amp v6.1.exe (PID: 1264)
Manual execution by a user
- WinLocker.exe (PID: 3024)
- explorer.exe (PID: 1344)
- WinLocker.exe (PID: 2228)
Reads the computer name
- Winlocker builder by Amp v6.1.exe (PID: 1264)
- WinLocker.exe (PID: 2228)
Reads product name
- WinLocker.exe (PID: 2228)
Reads Environment values
- WinLocker.exe (PID: 2228)
Reads Windows Product ID
- WinLocker.exe (PID: 2228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 2355200 |
| InitializedDataSize: | 98304 |
| UninitializedDataSize: | 15732736 |
| EntryPoint: | 0x113fb00 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
46
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1264 | "C:\Users\admin\AppData\Local\Temp\Winlocker builder by Amp v6.1.exe" | C:\Users\admin\AppData\Local\Temp\Winlocker builder by Amp v6.1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1344 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
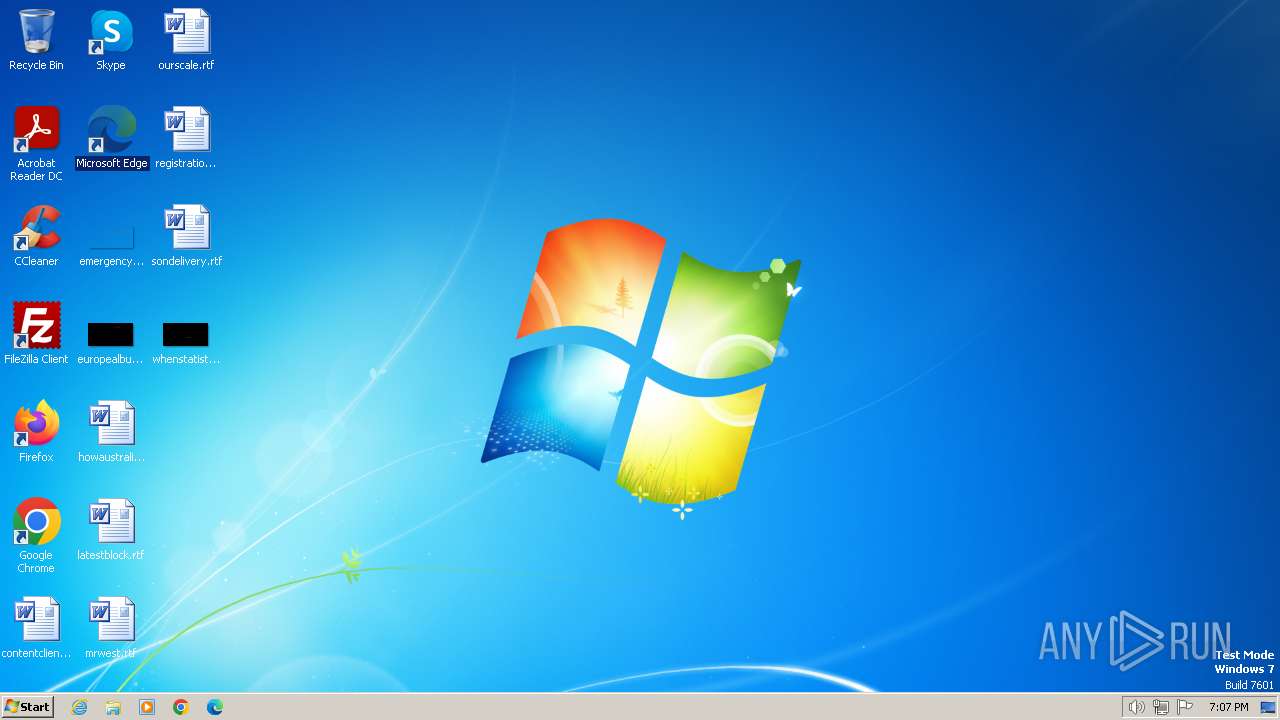
| 2228 | "C:\Users\admin\Documents\WinLocker.exe" | C:\Users\admin\Documents\WinLocker.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1073807364 Modules
| |||||||||||||||
| 3024 | "C:\Users\admin\Documents\WinLocker.exe" | C:\Users\admin\Documents\WinLocker.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
2 093
Read events
2 068
Write events
24
Delete events
1
Modification events
| (PID) Process: | (1264) Winlocker builder by Amp v6.1.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1264) Winlocker builder by Amp v6.1.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1264) Winlocker builder by Amp v6.1.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 010000000200000006000000000000000B000000070000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (1264) Winlocker builder by Amp v6.1.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 020000000100000006000000000000000B000000070000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (1264) Winlocker builder by Amp v6.1.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlgLegacy |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (1264) Winlocker builder by Amp v6.1.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlgLegacy |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (1264) Winlocker builder by Amp v6.1.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlgLegacy |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
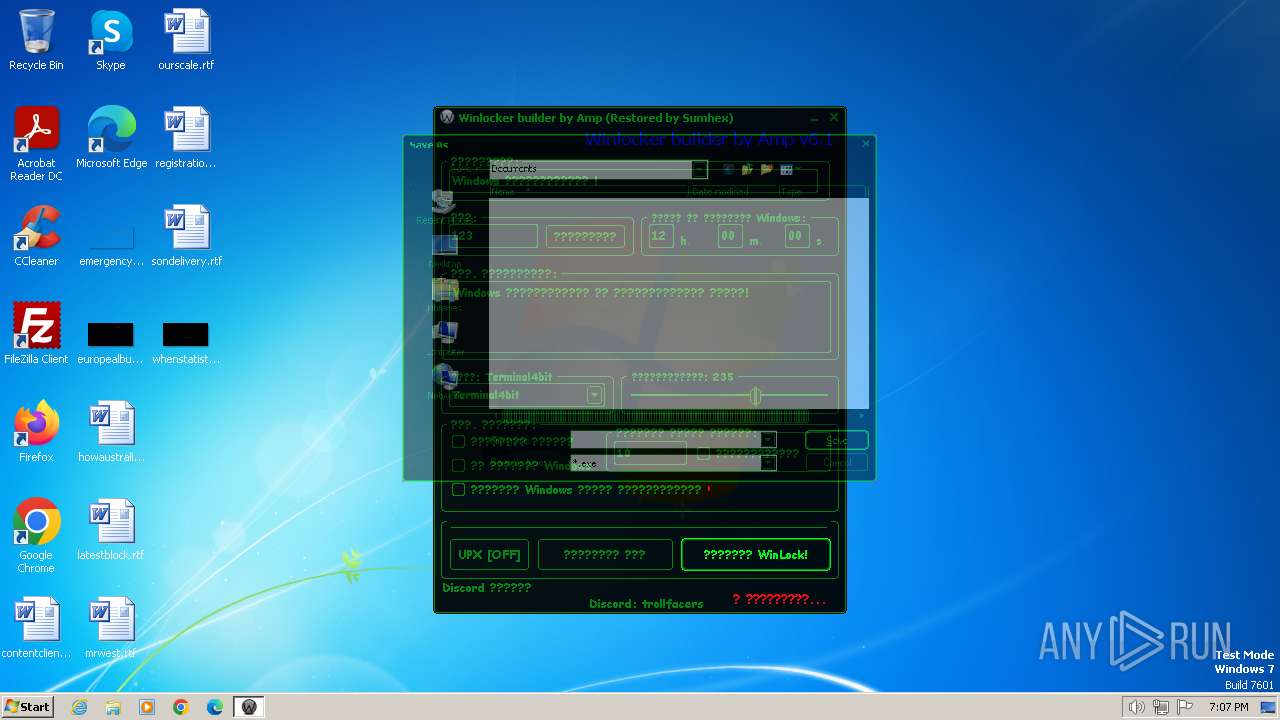
| (PID) Process: | (1264) Winlocker builder by Amp v6.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRULegacy |
| Operation: | write | Name: | MRUListEx |
Value: 0000000001000000FFFFFFFF | |||
| (PID) Process: | (1264) Winlocker builder by Amp v6.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\* |
| Operation: | write | Name: | MRUListEx |
Value: 0C0000000B0000000A00000009000000080000000700000006000000050000000400000003000000020000000100000000000000FFFFFFFF | |||
| (PID) Process: | (1264) Winlocker builder by Amp v6.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | delete value | Name: | 4 |
Value: 570069006E006C006F0063006B006500720020006200750069006C00640065007200200062007900200041006D0070002000760036002E0031002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000006601000066000000990300000202000000000000000000000000000000000000000000000000000000000000000000000100000000000000 | |||
Executable files
19
Suspicious files
0
Text files
2
Unknown types
0
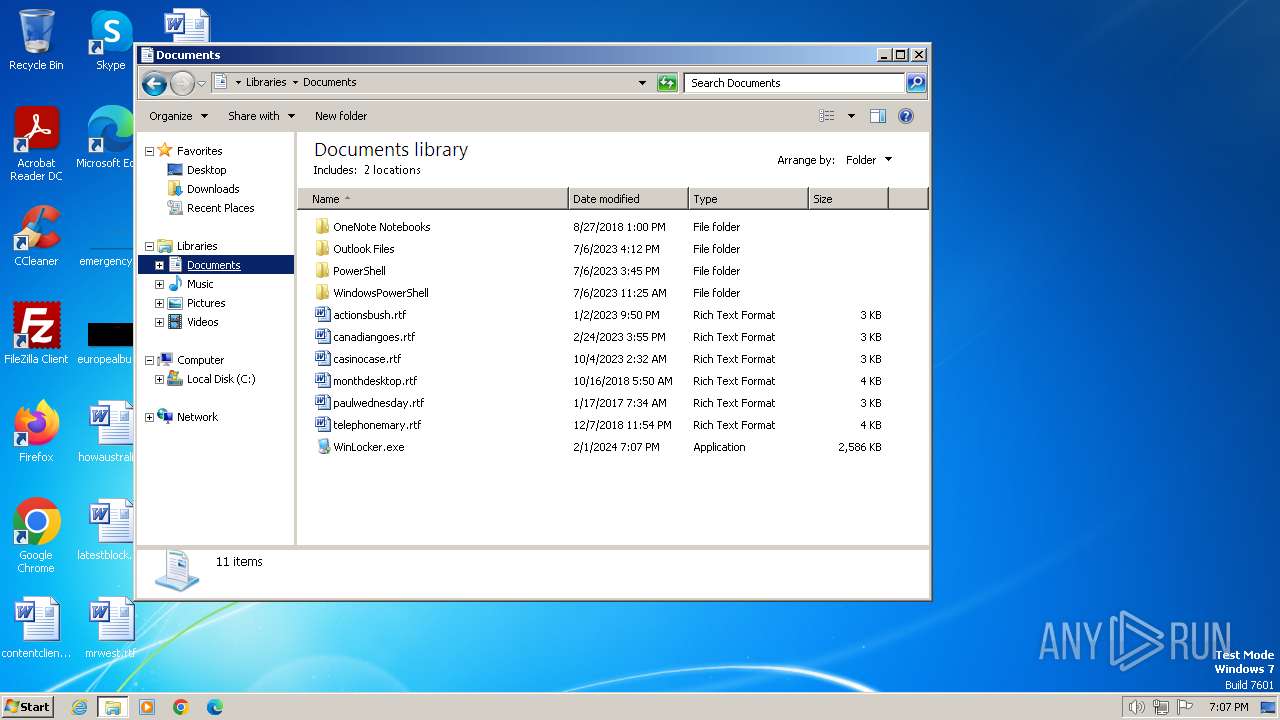
Dropped files
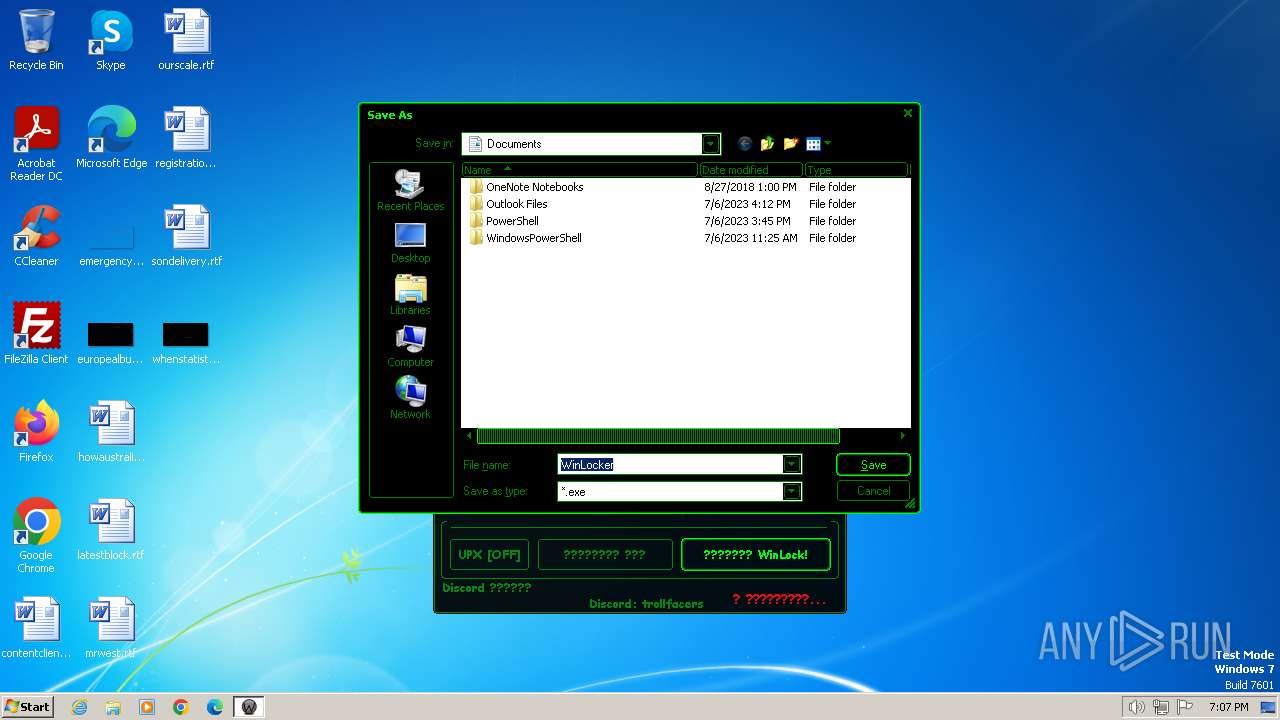
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1264 | Winlocker builder by Amp v6.1.exe | C:\Users\admin\Documents\RCX674F.tmp | executable | |
MD5:358892808A12189C3F27440F6937F8A9 | SHA256:40BF4D259314915DAE5B274E536396C3927C082EF42C7B92177B54488CF29565 | |||
| 1264 | Winlocker builder by Amp v6.1.exe | C:\Users\admin\Documents\RCX680D.tmp | executable | |
MD5:7DD1B32F99786E0570641621CF2764BF | SHA256:737C88AECD73D6ED4AB4EF0E024DABE4D3B0D71B630B571817D43AD69578A4CE | |||
| 1264 | Winlocker builder by Amp v6.1.exe | C:\Users\admin\Documents\WinLocker.exe | executable | |
MD5:C9748A0276A5A468232BDB92D184E605 | SHA256:0D9B12C49E28B267C790057853361ACDFB8955E08A50E89F3BE1B39707491618 | |||
| 1264 | Winlocker builder by Amp v6.1.exe | C:\Users\admin\Documents\RCX6671.tmp | executable | |
MD5:D40E6E0CFDC9E818FCF3557C098E640C | SHA256:FB3E89CA73611CCE57BAFEF1994E05C5429E49987049AB8A85D118B4785F827A | |||
| 1264 | Winlocker builder by Amp v6.1.exe | C:\Users\admin\Documents\RCX65C3.tmp | executable | |
MD5:D468488C28EC2D71A15DCD57BA2ACD50 | SHA256:2C2EAA092C04BFE74F37EC5BF41E2DDBD87F97A0D44B3501CBB9A173F5309584 | |||
| 1264 | Winlocker builder by Amp v6.1.exe | C:\Users\admin\Documents\RCX6612.tmp | executable | |
MD5:28097BD71CB12F96D23A1B2994AA9C42 | SHA256:3D3C53B4530B2DA570C2E684A4948EDD738BBF0C277D55C44A7E24A4956E7CA5 | |||
| 1264 | Winlocker builder by Amp v6.1.exe | C:\Users\admin\Documents\RCX66C0.tmp | executable | |
MD5:C050309936AD879AE66AA1C6FFC16506 | SHA256:E1A75A58C1BBDB0CAD25805E34AE989C8BAD2E557EDFC1DB7B2D14EC741C7D20 | |||
| 1264 | Winlocker builder by Amp v6.1.exe | C:\Users\admin\Documents\RCX678E.tmp | executable | |
MD5:FFCA78D9720C755D36DE0C66E85F84EA | SHA256:5C0591F7CC2DF6E629B3011FFDA975E84A48EBFE583B5C2C9AE8DE1C3E9BA883 | |||
| 1264 | Winlocker builder by Amp v6.1.exe | C:\Users\admin\Documents\RCX6700.tmp | executable | |
MD5:853E27E42F9FCF641CE1BC80D1BD19CE | SHA256:1198C8E4B471E11C690443C8751BE6F9CB5E960C0BA198B147D20F9EF12DCF56 | |||
| 1264 | Winlocker builder by Amp v6.1.exe | C:\Users\admin\Documents\RCX67DE.tmp | executable | |
MD5:7244A2CF60E149FFAA0D48BAB05AE4DF | SHA256:37225AF6CF56D2C96C65373BCA18257F910D45D2084C66A714E67263AFC43970 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |