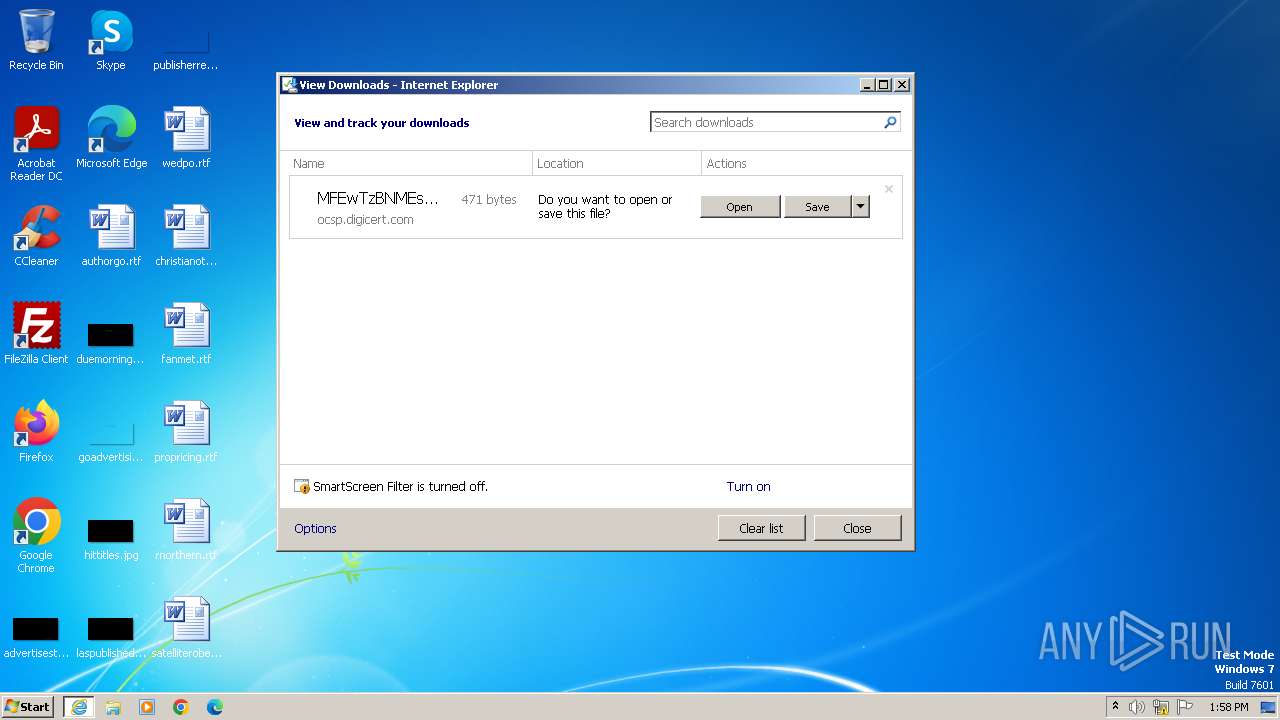
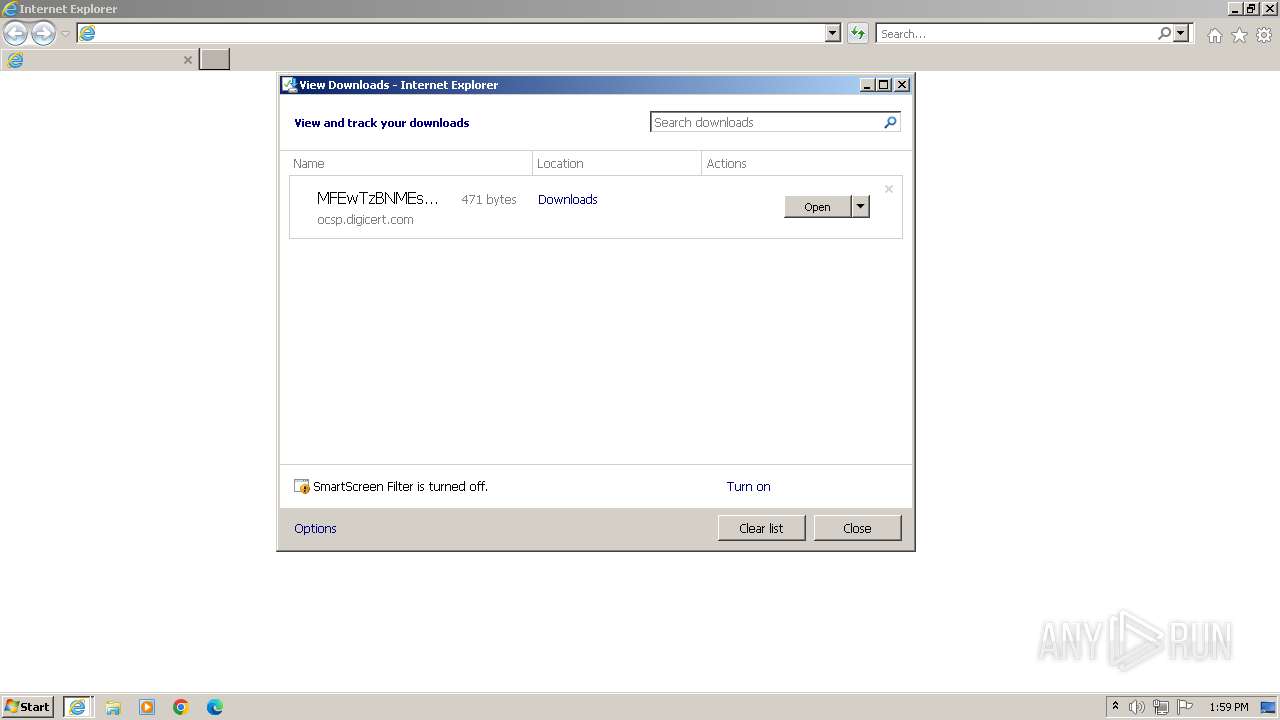
| URL: | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D |
| Full analysis: | https://app.any.run/tasks/eee75092-31bb-4b3c-a2fb-49eaf3212741 |
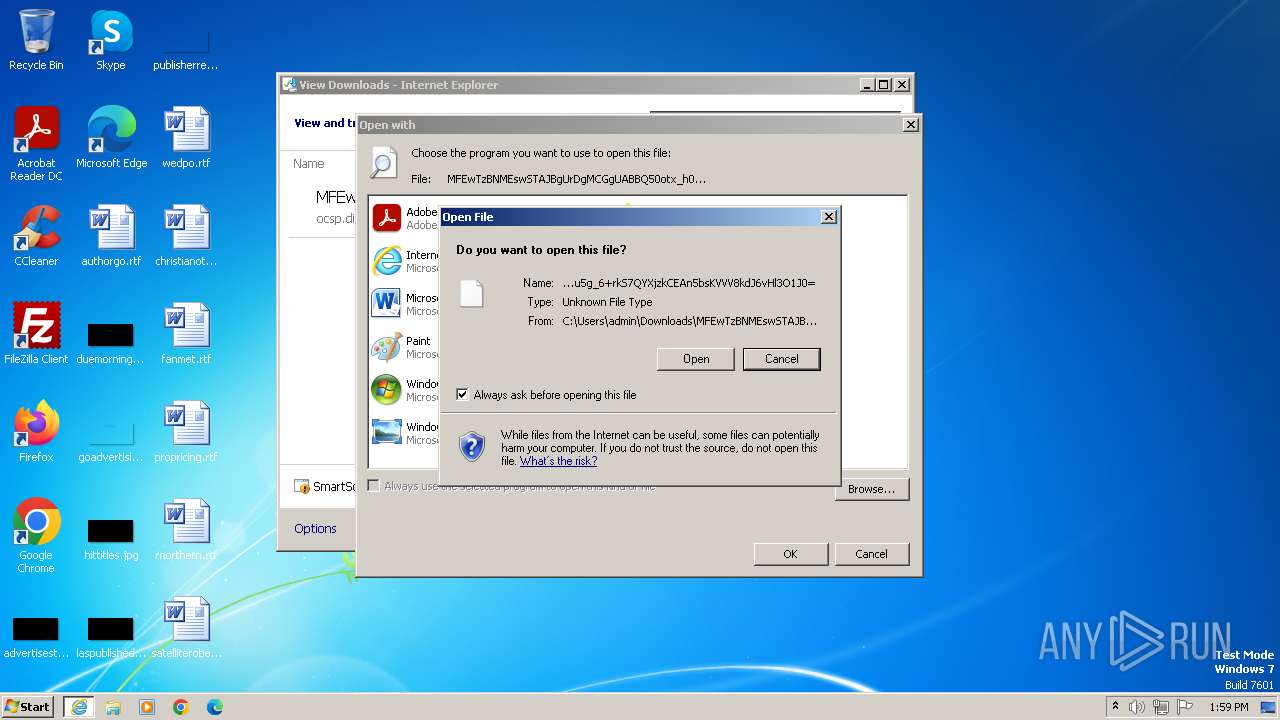
| Verdict: | Malicious activity |
| Analysis date: | November 13, 2023, 13:58:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 9A972CC732101875851E3DD2992515BA11A68087 |
| SHA256: | E0583FC2CF8255F983056BDED43CF92088F789670849F6A7C22E89287F8CFB80 |
| SSDEEP: | 3:N1KRGWVGkG6xfHhrVCR0TSv03sZ1/4F5LjM3YhkHpfxu7m7:CgWVGTEhrVCSTSi41aVhkHXuk |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- rundll32.exe (PID: 3688)
- rundll32.exe (PID: 3728)
- rundll32.exe (PID: 4072)
Uses RUNDLL32.EXE to load library
- iexplore.exe (PID: 3436)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 3612)
- wmpnscfg.exe (PID: 3844)
Manual execution by a user
- wmpnscfg.exe (PID: 3612)
- wmpnscfg.exe (PID: 3844)
Application launched itself
- iexplore.exe (PID: 3436)
Reads the computer name
- wmpnscfg.exe (PID: 3612)
- wmpnscfg.exe (PID: 3844)
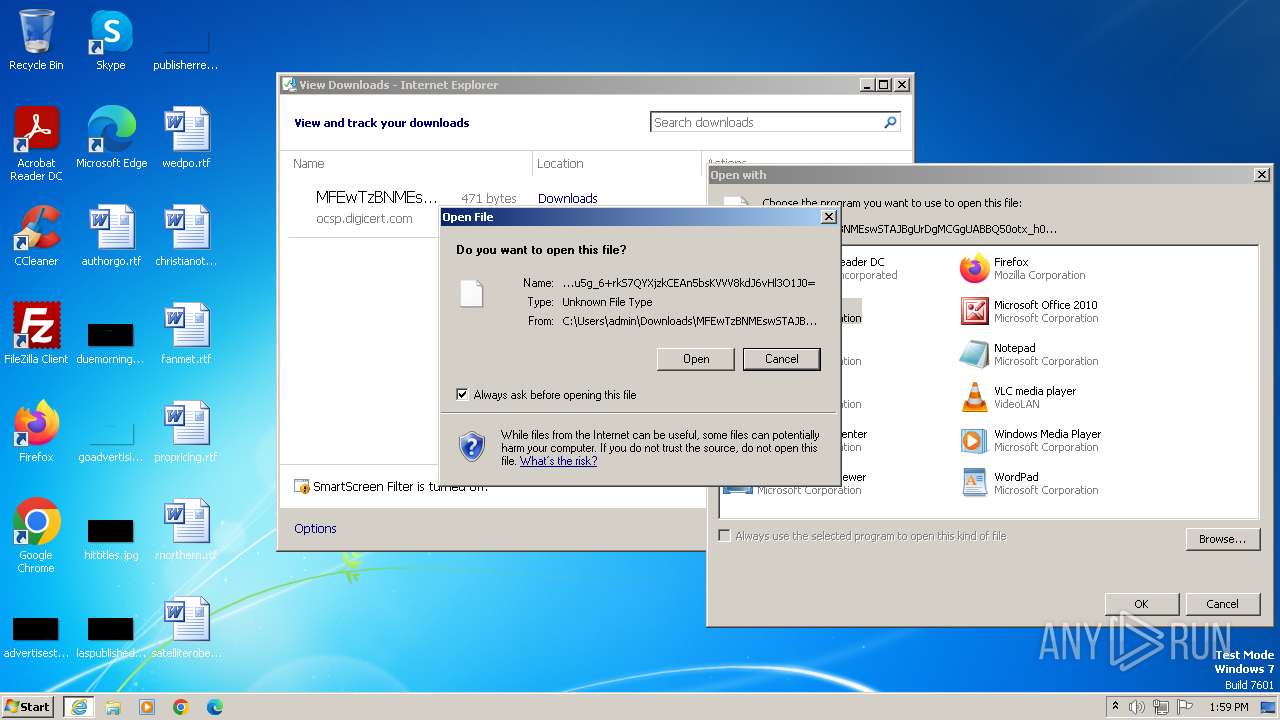
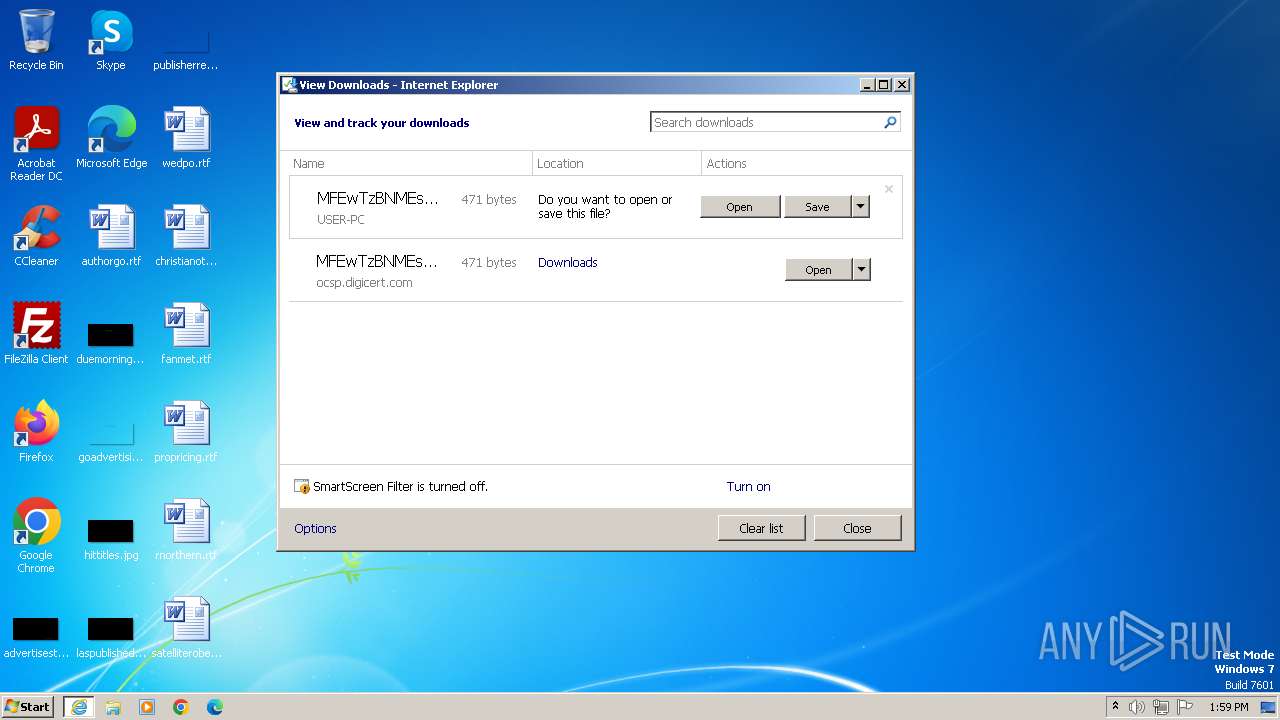
The process uses the downloaded file
- rundll32.exe (PID: 3688)
- iexplore.exe (PID: 3308)
- rundll32.exe (PID: 3728)
- iexplore.exe (PID: 3436)
- rundll32.exe (PID: 4072)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3612)
- wmpnscfg.exe (PID: 3844)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 3688)
- rundll32.exe (PID: 3728)
- rundll32.exe (PID: 4072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
9
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3308 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3436 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3436 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3612 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
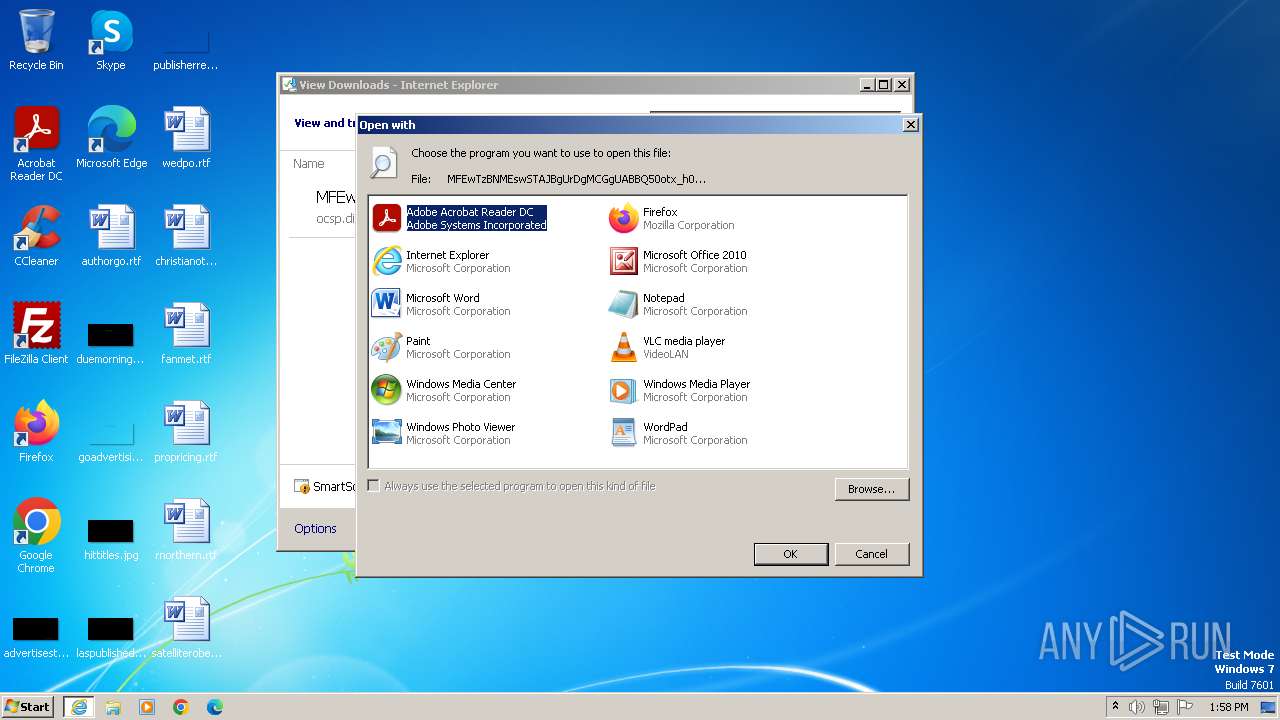
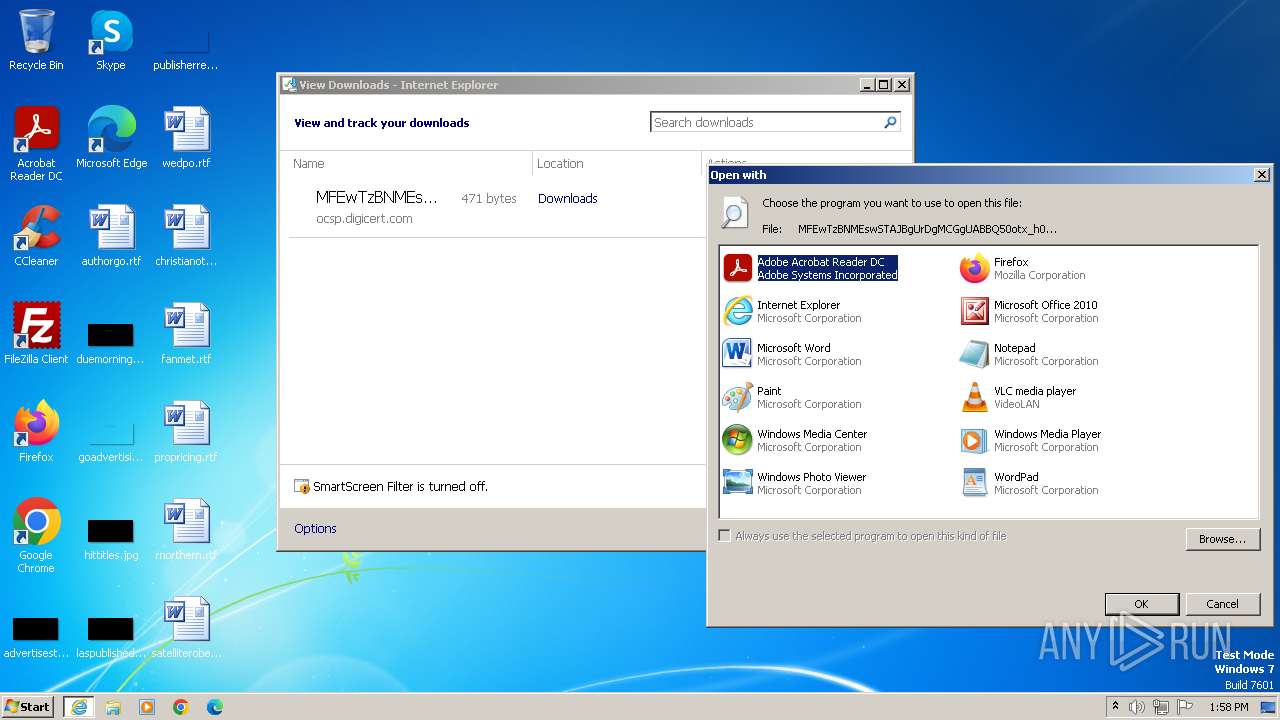
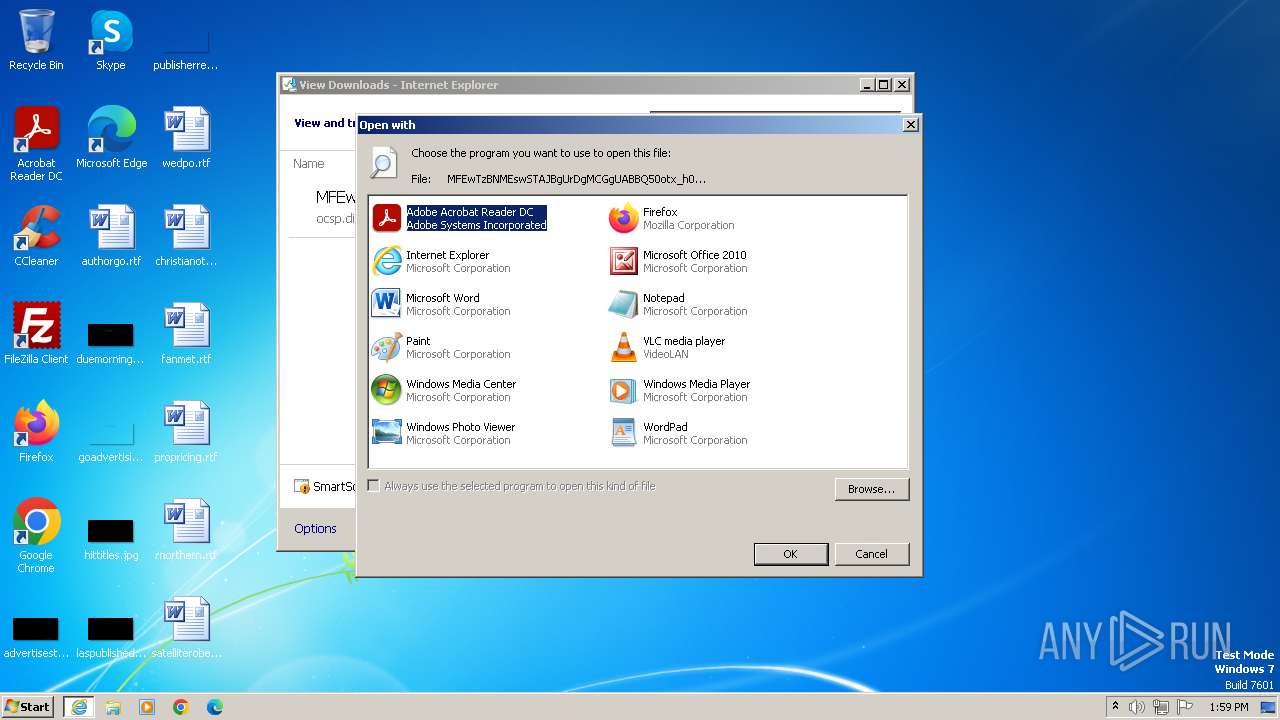
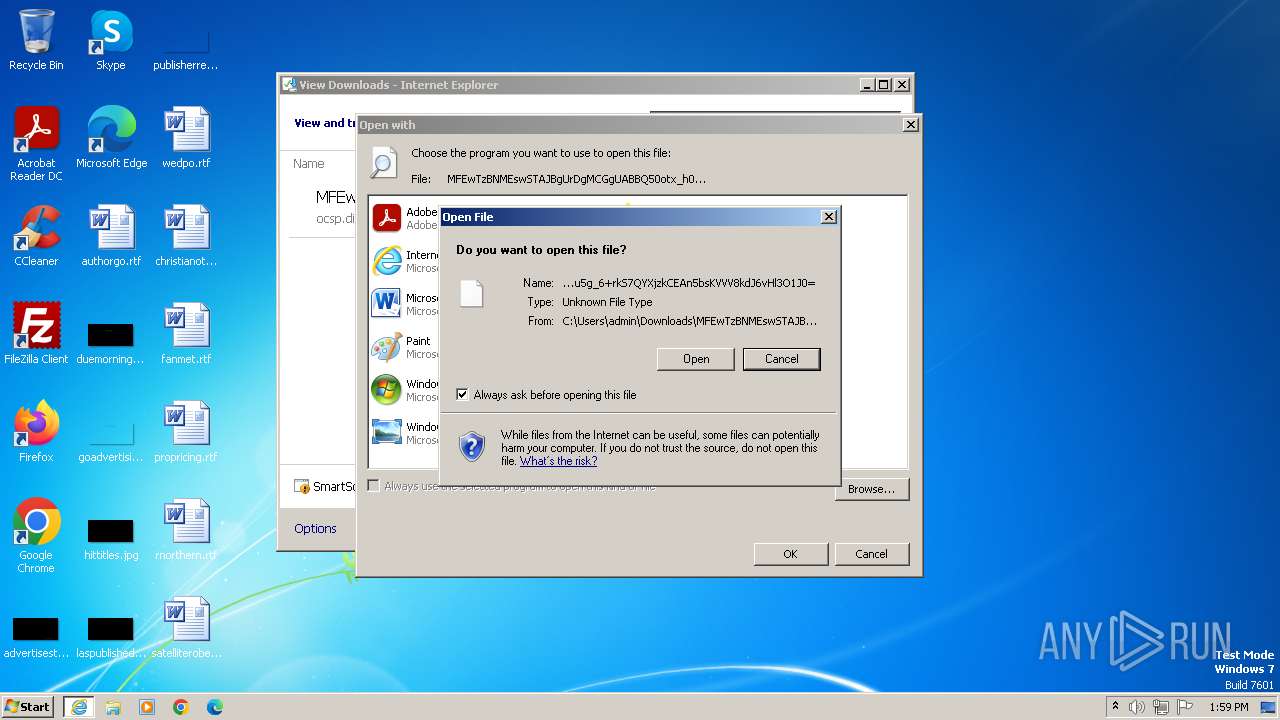
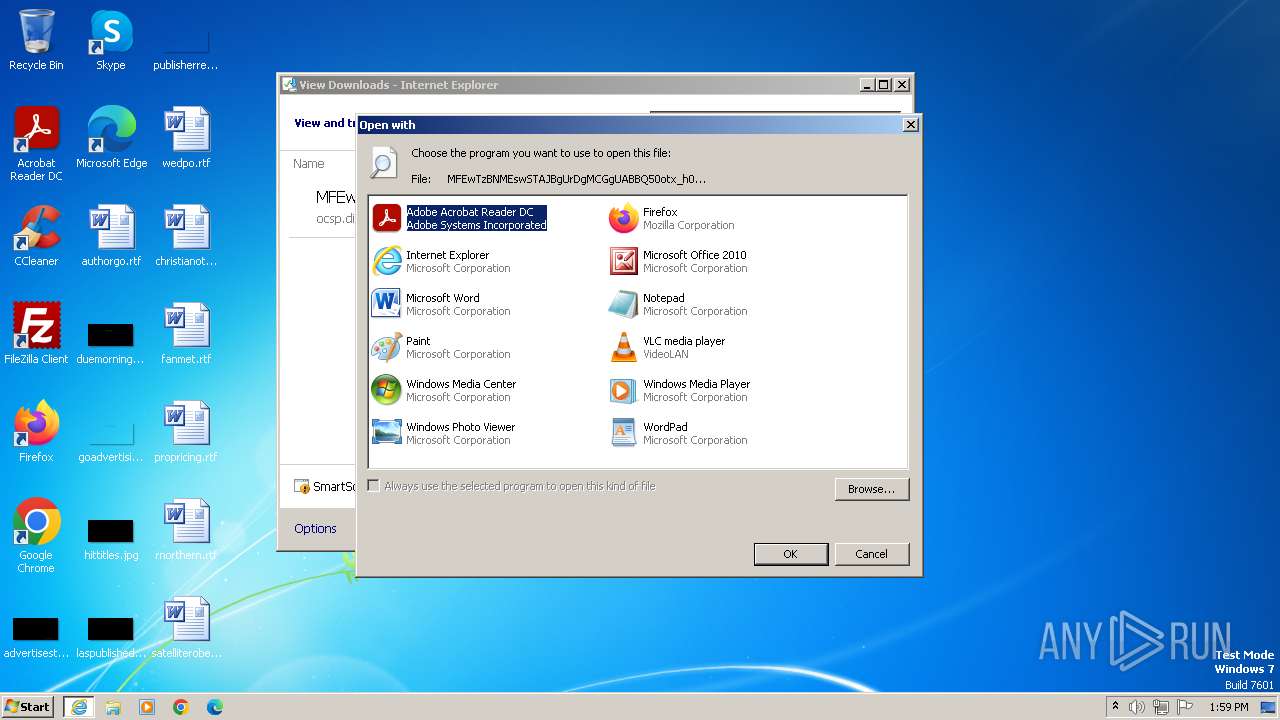
| 3688 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx_h0Ztl+z8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g_6+rkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0= | C:\Windows\System32\rundll32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3728 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx_h0Ztl+z8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g_6+rkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0= | C:\Windows\System32\rundll32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3844 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3940 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\Downloads\MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx_h0Ztl+z8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g_6+rkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0= | C:\Program Files\Internet Explorer\iexplore.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
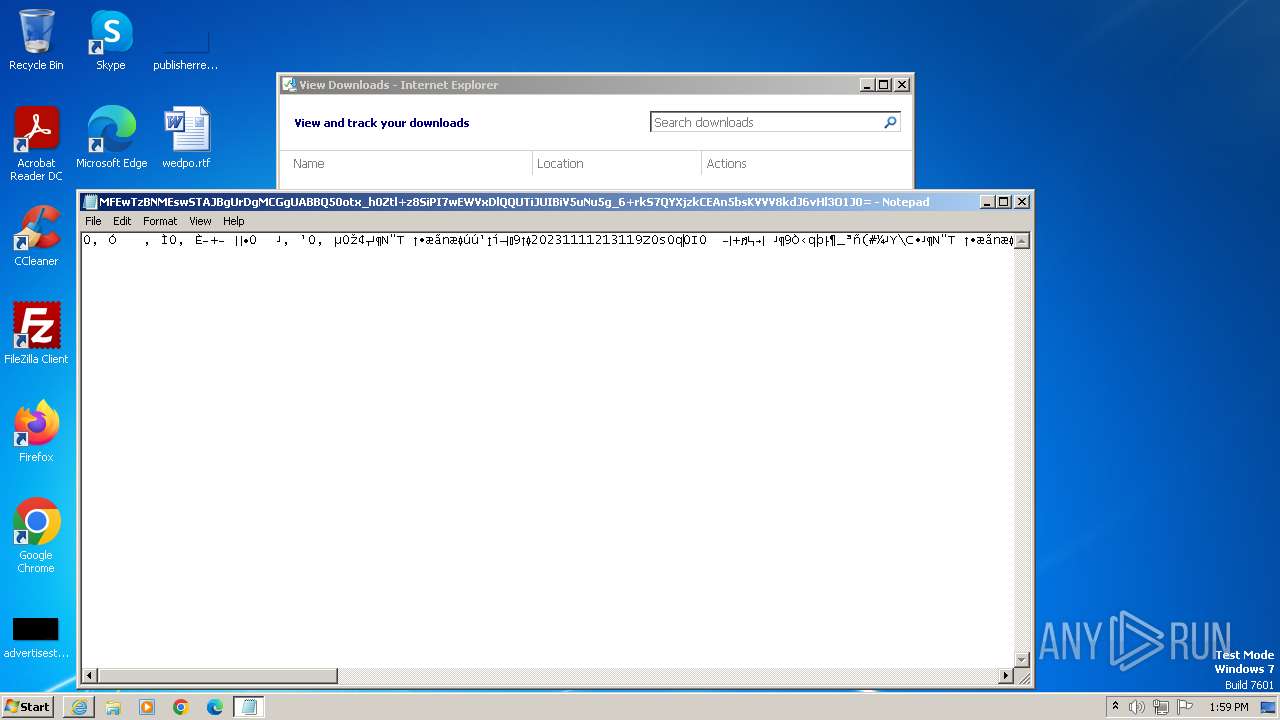
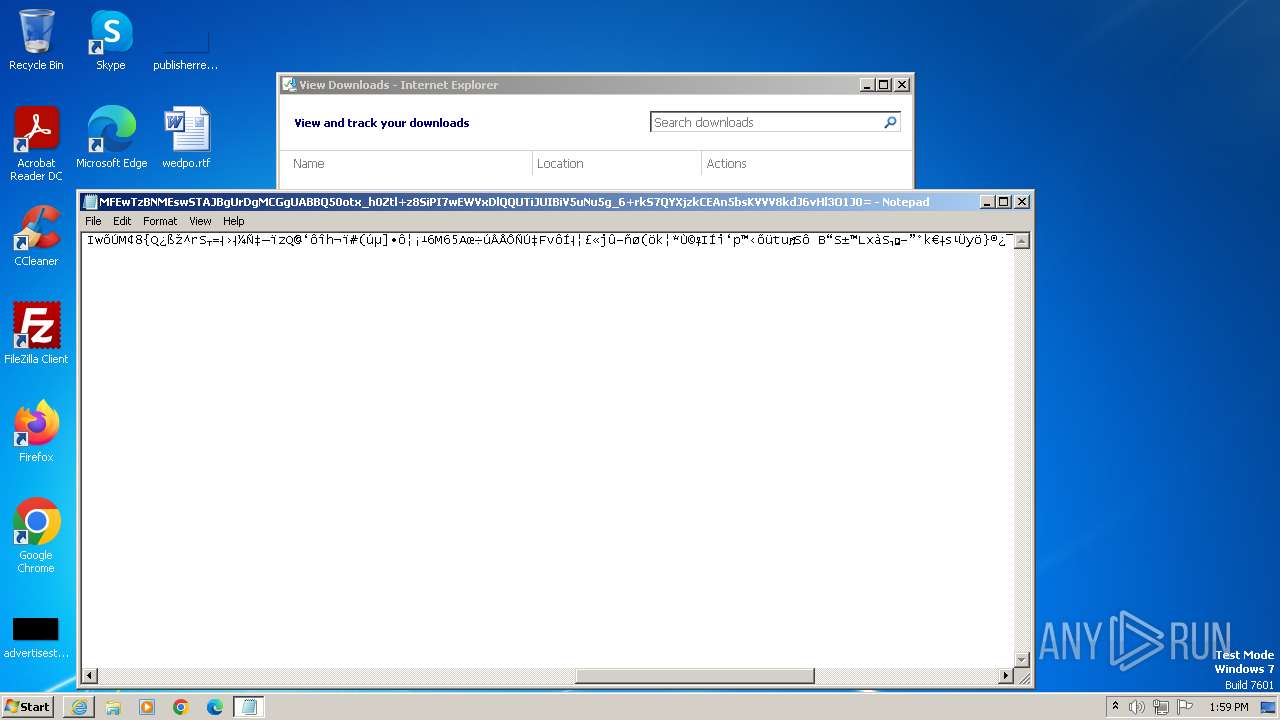
| 4020 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx_h0Ztl+z8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g_6+rkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0= | C:\Windows\System32\notepad.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4072 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx_h0Ztl+z8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g_6+rkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0= | C:\Windows\System32\rundll32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 991
Read events
9 795
Write events
190
Delete events
6
Modification events
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000059010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3436) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
0
Suspicious files
16
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
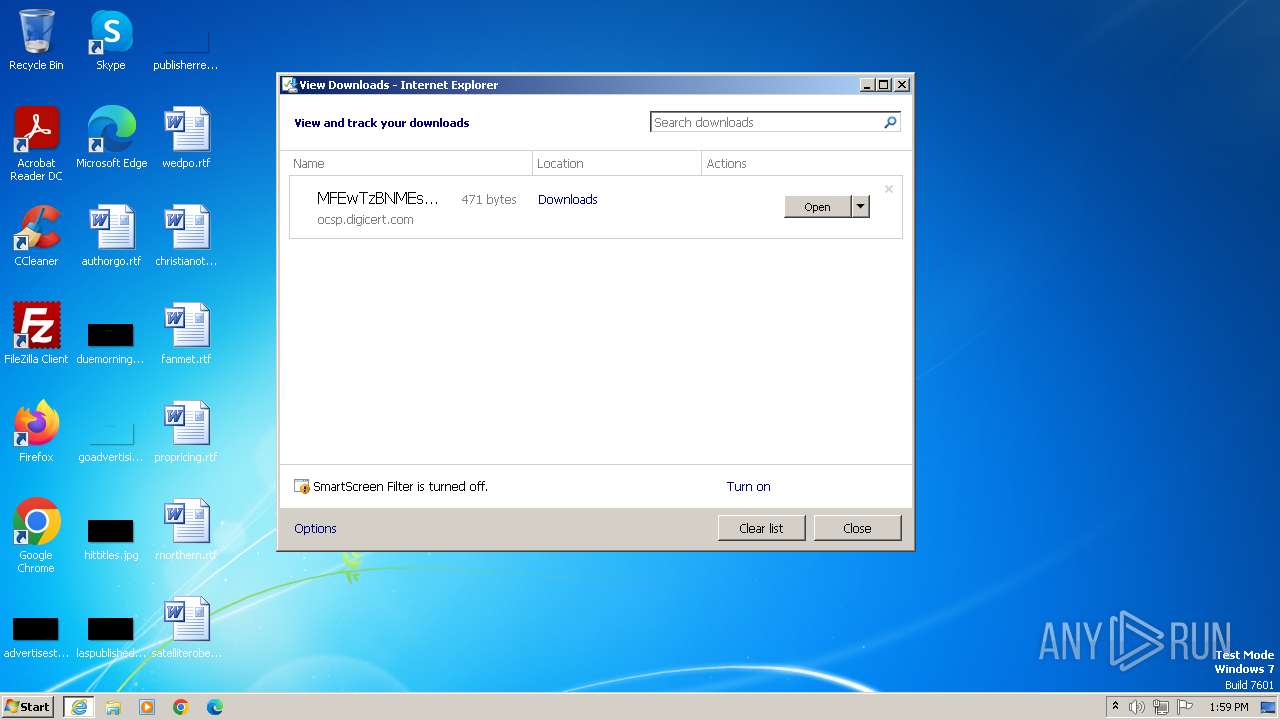
| 3308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx_h0Ztl+z8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g_6+rkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0=[1] | binary | |
MD5:C5E3763A7BB945AF4D50A9C6E3233B6B | SHA256:AC0AB5387FBAAA94EDE8376B2B7E782252925AEB13DE4CEAD28F34F0FB83A658 | |||
| 3436 | iexplore.exe | C:\Users\admin\Downloads\MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx_h0Ztl+z8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g_6+rkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0=.th27sxy.partial:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 3308 | iexplore.exe | C:\Users\admin\Downloads\MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx_h0Ztl+z8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g_6+rkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0=.th27sxy.partial | binary | |
MD5:C5E3763A7BB945AF4D50A9C6E3233B6B | SHA256:AC0AB5387FBAAA94EDE8376B2B7E782252925AEB13DE4CEAD28F34F0FB83A658 | |||
| 3436 | iexplore.exe | C:\Users\admin\Downloads\MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx_h0Ztl+z8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g_6+rkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0= | binary | |
MD5:C5E3763A7BB945AF4D50A9C6E3233B6B | SHA256:AC0AB5387FBAAA94EDE8376B2B7E782252925AEB13DE4CEAD28F34F0FB83A658 | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF40D3156563D5D1E8.TMP | binary | |
MD5:53E2E57B7135DED65B68445C46ED033D | SHA256:4501B67131CD52C2AEF79CBCF4B242CDFF5BBC49543F097ADA475CC03D2217CB | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{BE02CFB5-822C-11EE-A826-12A9866C77DE}.dat | binary | |
MD5:B224ED772EF6F17CA7787E2E9143E48F | SHA256:7FD404328DC66D139FCD4191E53377FD1F210FDDBA57553FD49CAFEA8FA360FD | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB535243497191A13.TMP | binary | |
MD5:569A3BDDCBECDB176BBFE8B43D84F0D0 | SHA256:3A815176300F4B1B8C8258CA2D103E4BBF0A347761A6DA4ABF66007BE2148979 | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:4FACD85B00E382BD14B9E9C278147494 | SHA256:01E9204D9E6E96A744A29384C9C8A340659EDE5EA638A7B1F93DB97B6482256B | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{CEF142D7-822C-11EE-A826-12A9866C77DE}.dat | binary | |
MD5:DB84AECF965C3E81E61147E6B9B820EC | SHA256:1F1B31406D10F25E0736C8863B9151EFF3F230A3A30D703FF6CBCC9F6B4ED519 | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
10
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3436 | iexplore.exe | GET | 200 | 67.26.81.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?bbc732cc317d41a6 | unknown | compressed | 4.66 Kb | unknown |
3436 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3436 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
3436 | iexplore.exe | 67.26.81.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
3436 | iexplore.exe | 192.229.221.95:80 | — | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |