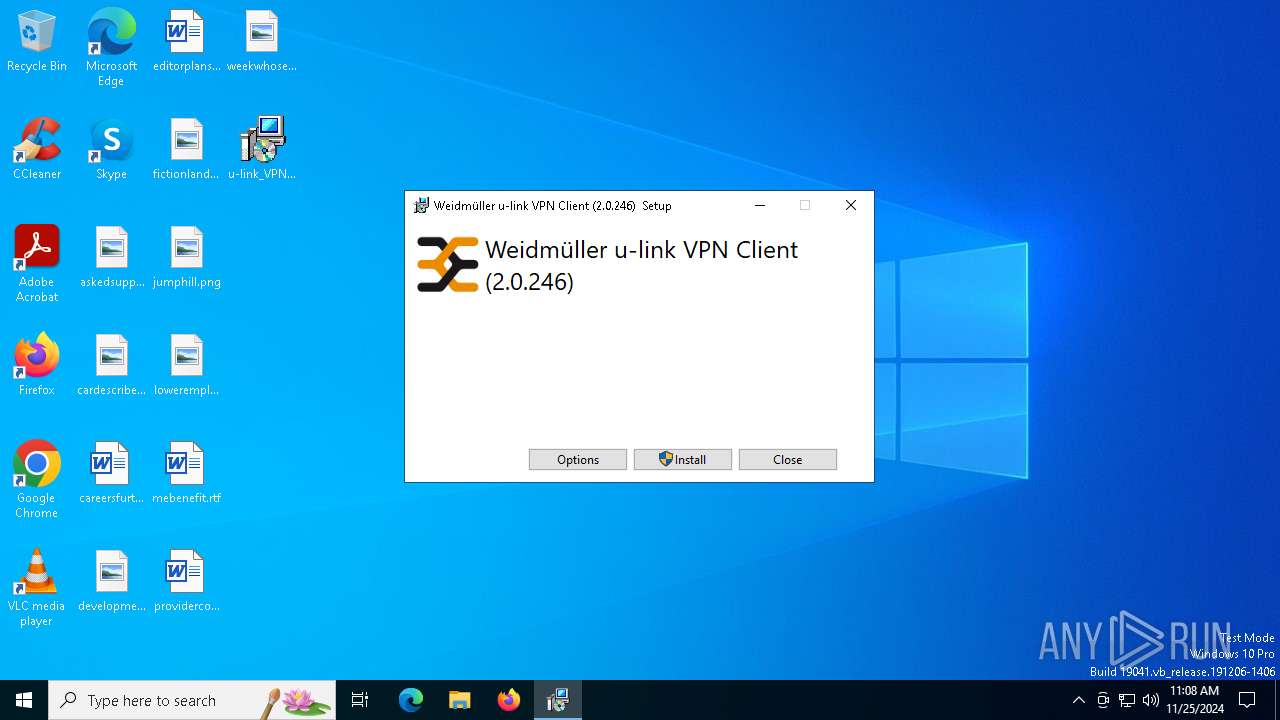
| File name: | u-link_VPN-Client_Setup_V2.0.246.exe |
| Full analysis: | https://app.any.run/tasks/74ccfe9f-32c6-435c-abeb-ba29a2002ee7 |
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2024, 11:08:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 42D6A63989E4DCB6B330F7BD86BA6BB4 |
| SHA1: | 3E4686ADFBBFE2E5FD5F229E690C9CE564DA419B |
| SHA256: | E057144F709F3310FADC24A31F8F8F2997D77A40D9B32C45A72C441BC1A2143D |
| SSDEEP: | 98304:Q1svXJG6gIS6p1m9aKTx6lOn8ofmXVF2K1ni4eGDYzGYoYxuR+sWT3TAa+rK+vr+:fD/M458B3/XJYpx67iGyW3qHtk+YTUb |
MALICIOUS
No malicious indicators.SUSPICIOUS
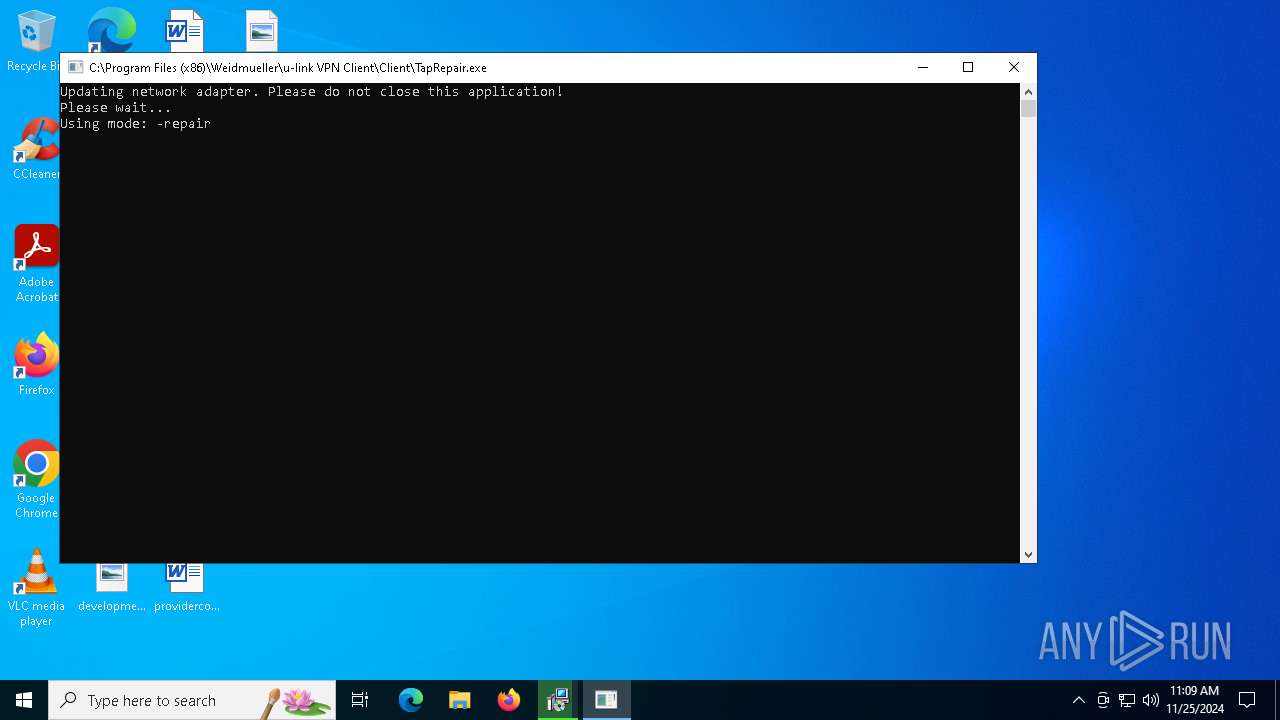
Executable content was dropped or overwritten
- u-link_VPN-Client_Setup_V2.0.246.exe (PID: 396)
- u-linkSetup.exe (PID: 4824)
- u-link_VPN-Client_Setup_V2.0.246.exe (PID: 5696)
- drvinst.exe (PID: 6508)
- drvinst.exe (PID: 6560)
Executes as Windows Service
- VSSVC.exe (PID: 3928)
- adsrtsvc.exe (PID: 2280)
- AWCPVPNClientService.exe (PID: 1620)
Starts itself from another location
- u-link_VPN-Client_Setup_V2.0.246.exe (PID: 5696)
Process drops legitimate windows executable
- msiexec.exe (PID: 5388)
The process drops C-runtime libraries
- msiexec.exe (PID: 5388)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 5388)
- drvinst.exe (PID: 6508)
- drvinst.exe (PID: 6560)
INFO
Manages system restore points
- SrTasks.exe (PID: 5268)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:22 22:14:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 314368 |
| InitializedDataSize: | 164352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x302e5 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.246.0 |
| ProductVersionNumber: | 2.0.246.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Weidmüller |
| FileDescription: | Weidmüller u-link VPN Client (2.0.246) |
| FileVersion: | 2.0.246 |
| InternalName: | setup |
| LegalCopyright: | Copyright© 2012-2015, Weidmüller |
| OriginalFileName: | u-linkSetup.exe |
| ProductName: | Weidmüller u-link VPN Client (2.0.246) |
| ProductVersion: | 2.0.246 |
Total processes
155
Monitored processes
31
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | "C:\Users\admin\Desktop\u-link_VPN-Client_Setup_V2.0.246.exe" | C:\Users\admin\Desktop\u-link_VPN-Client_Setup_V2.0.246.exe | explorer.exe | ||||||||||||
User: admin Company: Weidmüller Integrity Level: MEDIUM Description: Weidmüller u-link VPN Client (2.0.246) Exit code: 3010 Version: 2.0.246 Modules
| |||||||||||||||
| 628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1620 | "C:\Program Files (x86)\Weidmueller\u-link VPN Client\Client\AWCPVPNClientService.exe" | C:\Program Files (x86)\Weidmueller\u-link VPN Client\Client\AWCPVPNClientService.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: CP.VPN.Client.Service Version: 1.0.0.0 | |||||||||||||||
| 1864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certadd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2132 | certadd.exe "C:\Program Files (x86)\ads-tec\VPN\DigiCertHighAssuranceEVRootCA.crt" | C:\Program Files (x86)\ads-tec\VPN\certadd.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: ads-tec GmbH Integrity Level: SYSTEM Description: Big-LinX Certificate Importer Application Exit code: 0 Version: 2, 0, 246, 0 | |||||||||||||||
| 2280 | certadd.exe "C:\Program Files (x86)\ads-tec\VPN\DigiCertAssuredIDRootCA.crt" | C:\Program Files (x86)\ads-tec\VPN\certadd.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: ads-tec GmbH Integrity Level: SYSTEM Description: Big-LinX Certificate Importer Application Exit code: 0 Version: 2, 0, 246, 0 | |||||||||||||||
| 2280 | "C:\Program Files (x86)\ads-tec\x86Shared\adsrtsvc.exe" | C:\Program Files (x86)\ads-tec\x86Shared\adsrtsvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: ads-tec GmbH Integrity Level: SYSTEM Description: ads-tec route manager service Version: 2, 0, 246, 0 | |||||||||||||||
| 2292 | certadd.exe "C:\Program Files (x86)\ads-tec\VPN\openvpn236.cer" TrustedPublisher | C:\Program Files (x86)\ads-tec\VPN\certadd.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: ads-tec GmbH Integrity Level: SYSTEM Description: Big-LinX Certificate Importer Application Exit code: 0 Version: 2, 0, 246, 0 | |||||||||||||||
| 2792 | "C:\Program Files (x86)\ads-tec\VPN\ovpnpath.exe" | C:\Program Files (x86)\ads-tec\VPN\ovpnpath.exe | — | msiexec.exe | |||||||||||
User: admin Company: ads-tec GmbH Integrity Level: HIGH Description: Big-LinX OpenVPN path correction tool Exit code: 0 Version: 2, 0, 246, 0 | |||||||||||||||
| 3524 | "C:\ProgramData\Package Cache\FAD421EF191B76363EB7ACCB7B4DD704715972A7\deloldstuff.exe" Run | C:\ProgramData\Package Cache\FAD421EF191B76363EB7ACCB7B4DD704715972A7\deloldstuff.exe | — | u-linkSetup.exe | |||||||||||
User: admin Company: ads-tec GmbH Integrity Level: HIGH Description: Big-LinX Chainer old version uninstaller Exit code: 0 Version: 2, 0, 246, 0 | |||||||||||||||
Total events
1 465
Read events
1 394
Write events
62
Delete events
9
Modification events
| (PID) Process: | (4932) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000A922F0672A3FDB014413000004170000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4824) u-linkSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000A922F0672A3FDB01D812000008140000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4932) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000037F426682A3FDB014413000004170000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4932) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000037F426682A3FDB014413000004170000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4932) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000F65729682A3FDB014413000004170000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4932) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000041BD2B682A3FDB014413000004170000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4932) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (4932) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000FAECA2682A3FDB014413000004170000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4932) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000007951A5682A3FDB0144130000D0050000E8030000010000000000000000000000B2C0C2DF29CBA44AA36DC8A7F0FEB99500000000000000000000000000000000 | |||
| (PID) Process: | (3928) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000E643B1682A3FDB01580F0000F80E0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
110
Suspicious files
79
Text files
48
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4932 | dllhost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5696 | u-link_VPN-Client_Setup_V2.0.246.exe | C:\Users\admin\AppData\Local\Temp\{AA666D83-D866-4F17-BA04-515691FE7653}\vpn.msi | — | |
MD5:— | SHA256:— | |||
| 5696 | u-link_VPN-Client_Setup_V2.0.246.exe | C:\Users\admin\AppData\Local\Temp\{AA666D83-D866-4F17-BA04-515691FE7653}\biglinxclient.msi | — | |
MD5:— | SHA256:— | |||
| 4932 | dllhost.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{dfc2c0b2-cb29-4aa4-a36d-c8a7f0feb995}_OnDiskSnapshotProp | binary | |
MD5:32442AE9F7B328DC9316F4C78BECD9BB | SHA256:A23C5FD020528CB7448E9CA83E54B897BD57882DFF448BF8C15EF5023E4B203A | |||
| 4824 | u-linkSetup.exe | C:\ProgramData\Package Cache\.unverified\vpn.msi | — | |
MD5:— | SHA256:— | |||
| 4824 | u-linkSetup.exe | C:\ProgramData\Package Cache\{F14DDA7E-F978-451D-940D-469C000F6B8E}v2.0.246\vpn.msi | — | |
MD5:— | SHA256:— | |||
| 5696 | u-link_VPN-Client_Setup_V2.0.246.exe | C:\Users\admin\AppData\Local\Temp\{AA666D83-D866-4F17-BA04-515691FE7653}\.ba\wixstdba.dll | executable | |
MD5:87C8A7EA44E8EE0D9358E25B7DCD397D | SHA256:B7DE0A0CA3A94738747ABD708E30BA1F9638A8C8B7D8173C76D4F39FAE3D9346 | |||
| 5696 | u-link_VPN-Client_Setup_V2.0.246.exe | C:\Users\admin\AppData\Local\Temp\{AA666D83-D866-4F17-BA04-515691FE7653}\.ba\thm.xml | xml | |
MD5:5B5070F96B08ED2A8CACBAEA527FC61D | SHA256:FA4E97EAB6B047D49C12E0DA9191D95A6055FC1D5BCBD78F30D56278567BB665 | |||
| 4824 | u-linkSetup.exe | C:\ProgramData\Package Cache\.unverified\biglinxclient.msi | — | |
MD5:— | SHA256:— | |||
| 4824 | u-linkSetup.exe | C:\ProgramData\Package Cache\{9A25BC85-98A0-495A-9021-9B2CC06E8AD0}v2.0.246\biglinxclient.msi | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
21
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
876 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | — | 973 b | whitelisted |
876 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | — | 973 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 104.126.37.153:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
876 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
876 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
876 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |