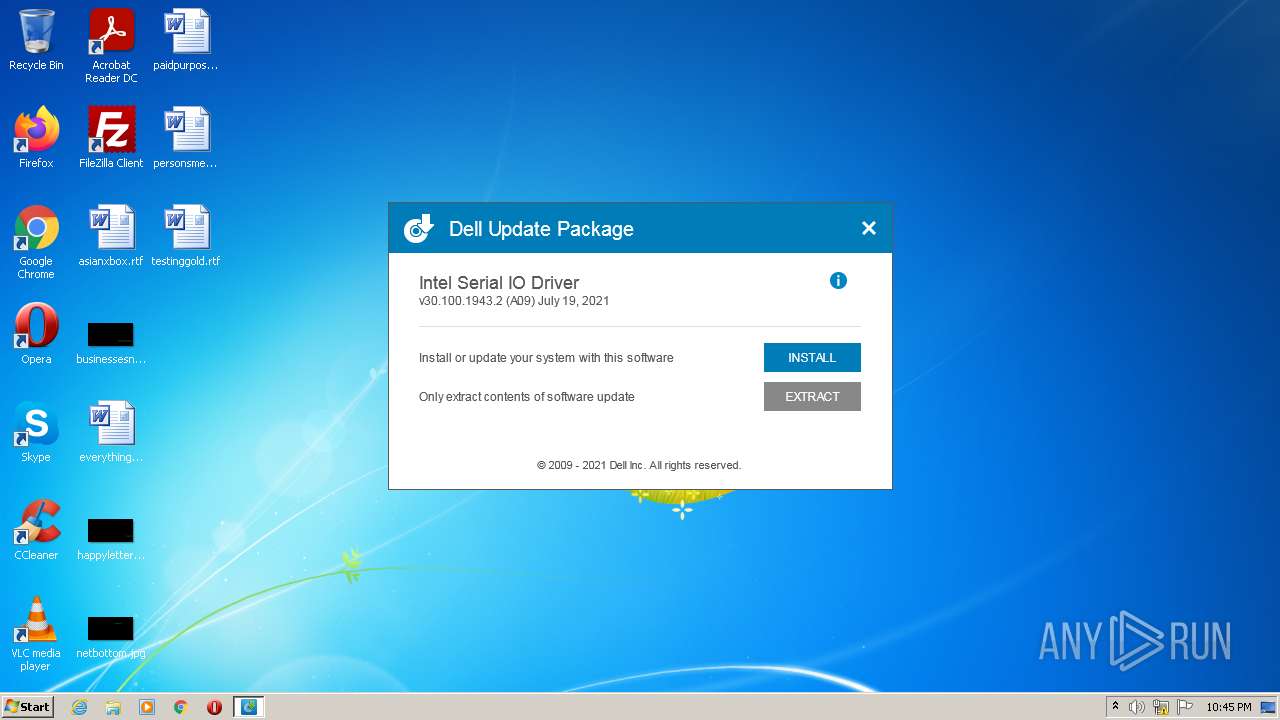
| download: | Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE |
| Full analysis: | https://app.any.run/tasks/4d248c59-6963-4584-8339-132729e67369 |
| Verdict: | Malicious activity |
| Analysis date: | July 27, 2022, 21:45:01 |
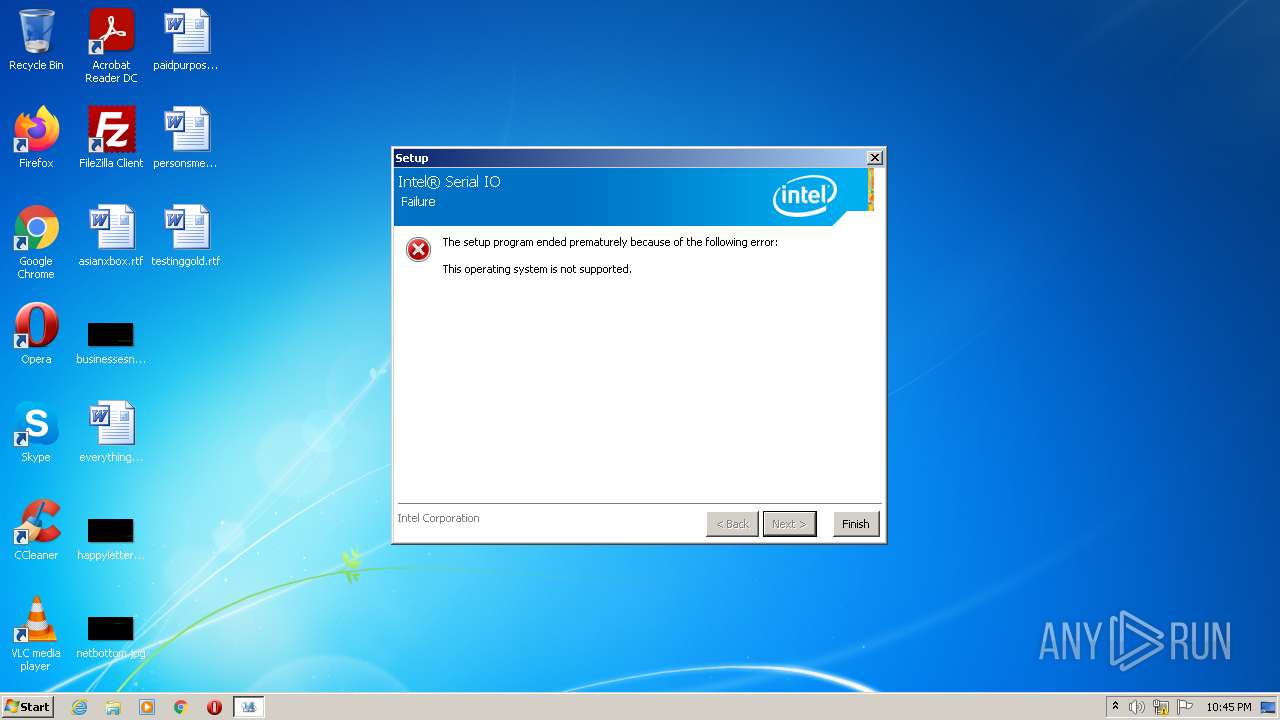
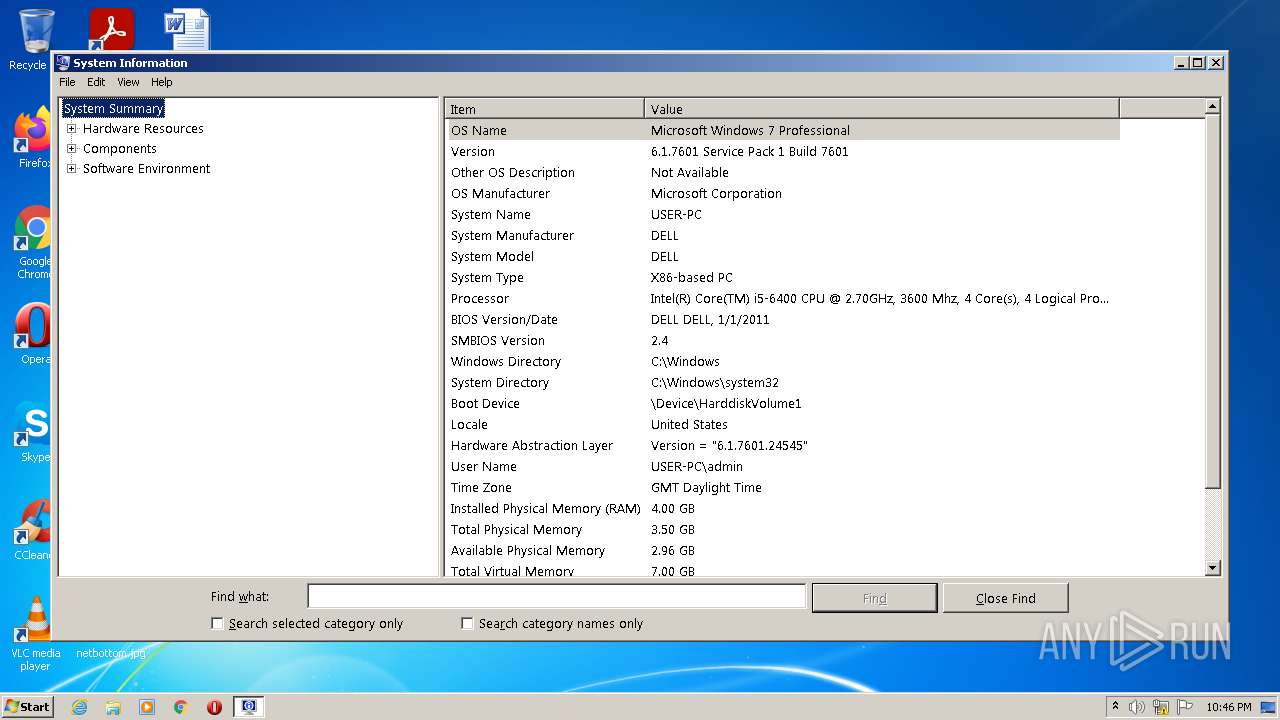
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9B62C902FB6C635170AC458A4783A84D |
| SHA1: | F8D39946775416F74A661A3480624ACEB73C4049 |
| SHA256: | E0555444B90851DDB59554AB7EDB5C4FBAF026F0C979B6698A211DDBFA853DA7 |
| SSDEEP: | 196608:Rkat80el1xR4RzSmdtx2Tsw2E7cRGo8sOgZo0aH0HbhwmOZjwbZjTbtu2th:Q1xCRbhTb42/ |
MALICIOUS
Drops executable file immediately after starts
- Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE (PID: 3804)
- miniunz.exe (PID: 3880)
- setup.exe (PID: 1936)
- SetupSerialIO.exe (PID: 2332)
Actions looks like stealing of personal data
- SetupSerialIO.exe (PID: 2332)
Application was dropped or rewritten from another process
- miniunz.exe (PID: 3880)
- SetupSerialIO.exe (PID: 2332)
- setup.exe (PID: 1936)
Loads dropped or rewritten executable
- miniunz.exe (PID: 3880)
- setup.exe (PID: 1936)
SUSPICIOUS
Reads Microsoft Outlook installation path
- Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE (PID: 3804)
Creates files in the program directory
- Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE (PID: 3804)
Reads the computer name
- Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE (PID: 3804)
Executable content was dropped or overwritten
- Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE (PID: 3804)
- miniunz.exe (PID: 3880)
- SetupSerialIO.exe (PID: 2332)
- setup.exe (PID: 1936)
Drops a file with a compile date too recent
- Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE (PID: 3804)
- miniunz.exe (PID: 3880)
- SetupSerialIO.exe (PID: 2332)
- setup.exe (PID: 1936)
Checks supported languages
- miniunz.exe (PID: 3880)
- SetupSerialIO.exe (PID: 2332)
- setup.exe (PID: 1936)
- Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE (PID: 3804)
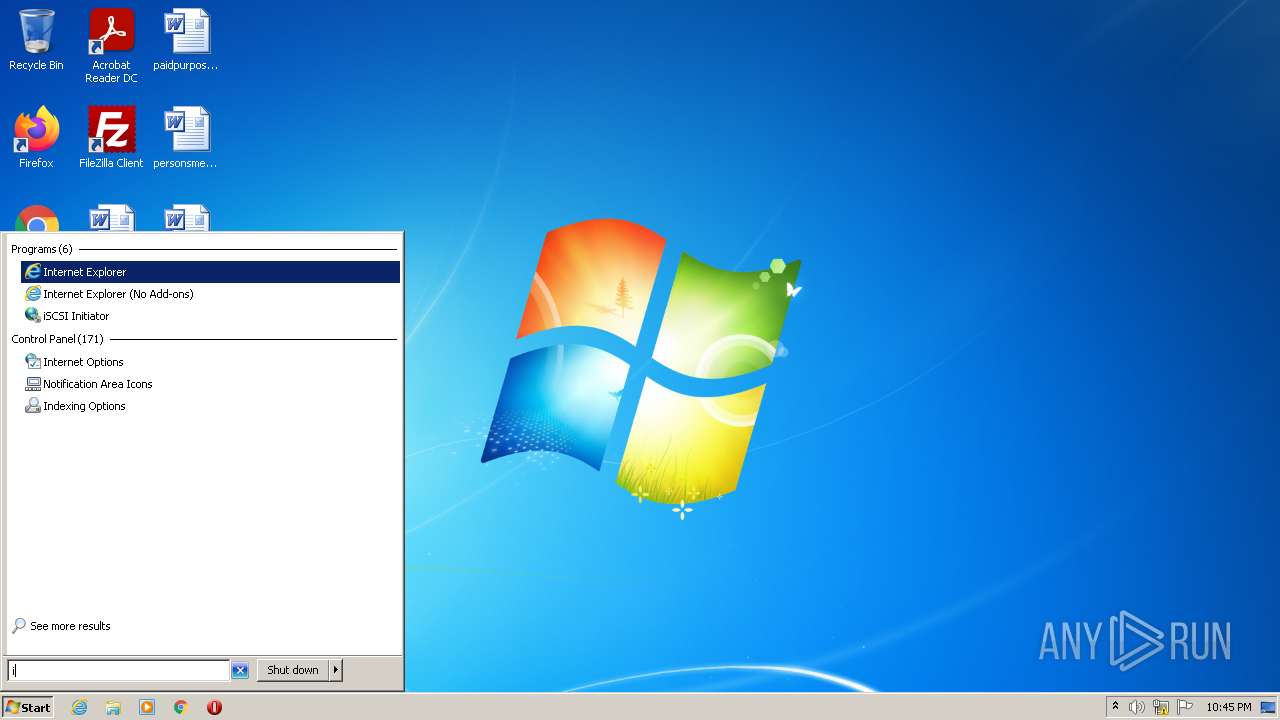
Reads internet explorer settings
- Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE (PID: 3804)
INFO
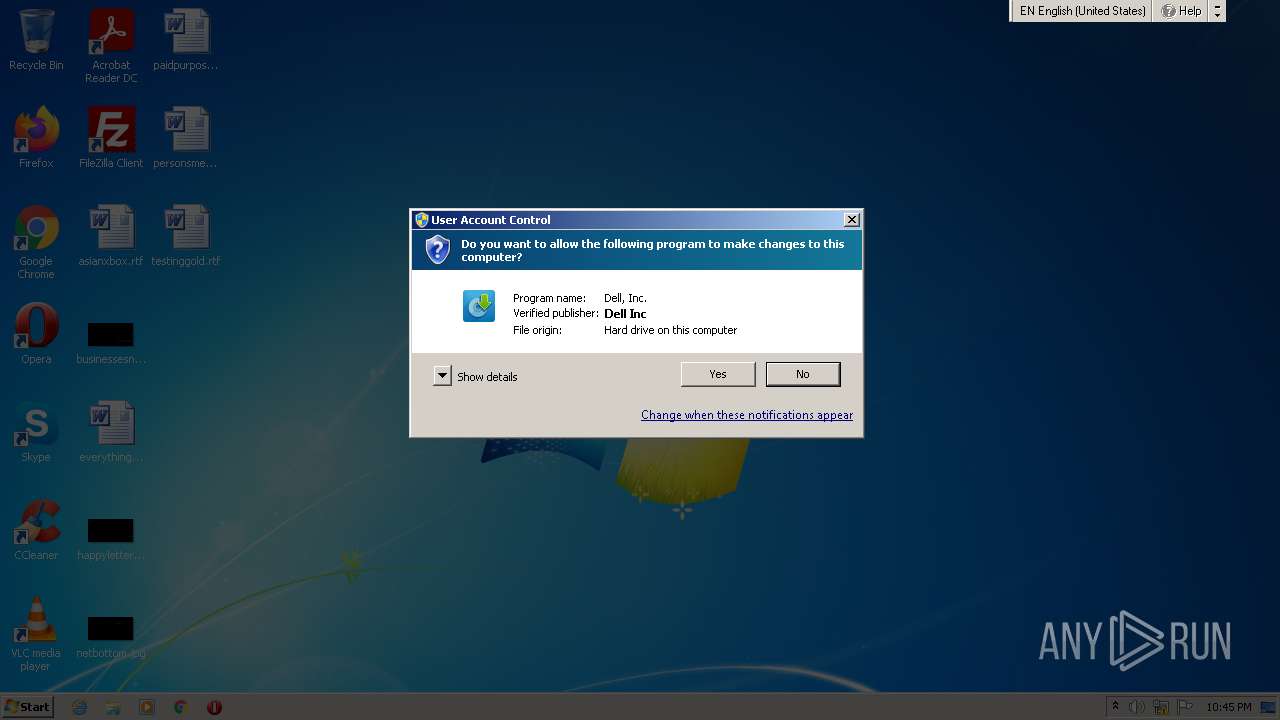
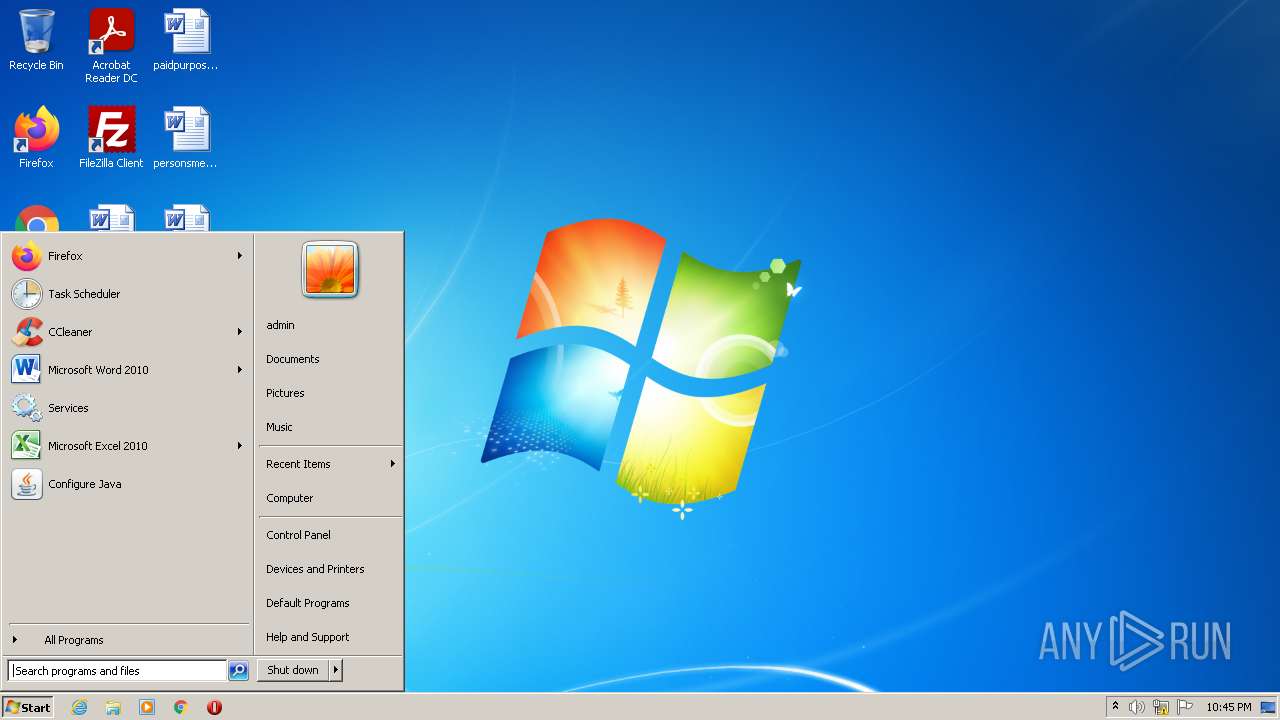
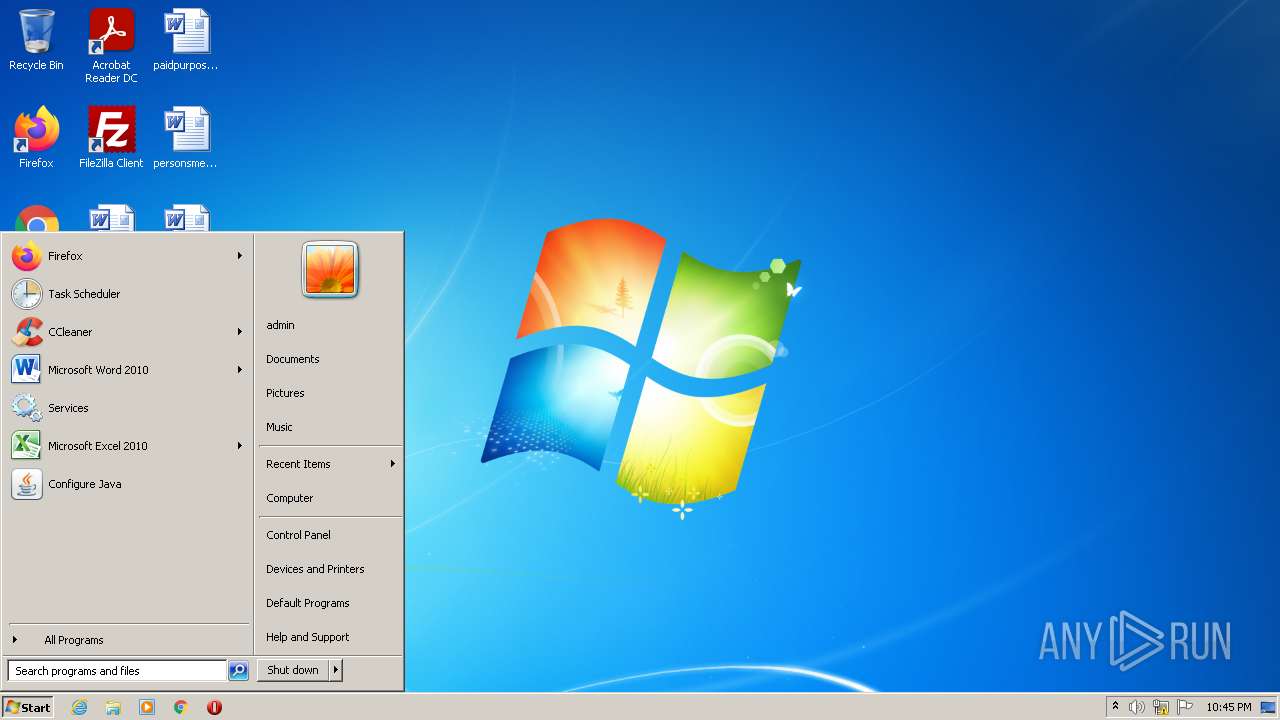
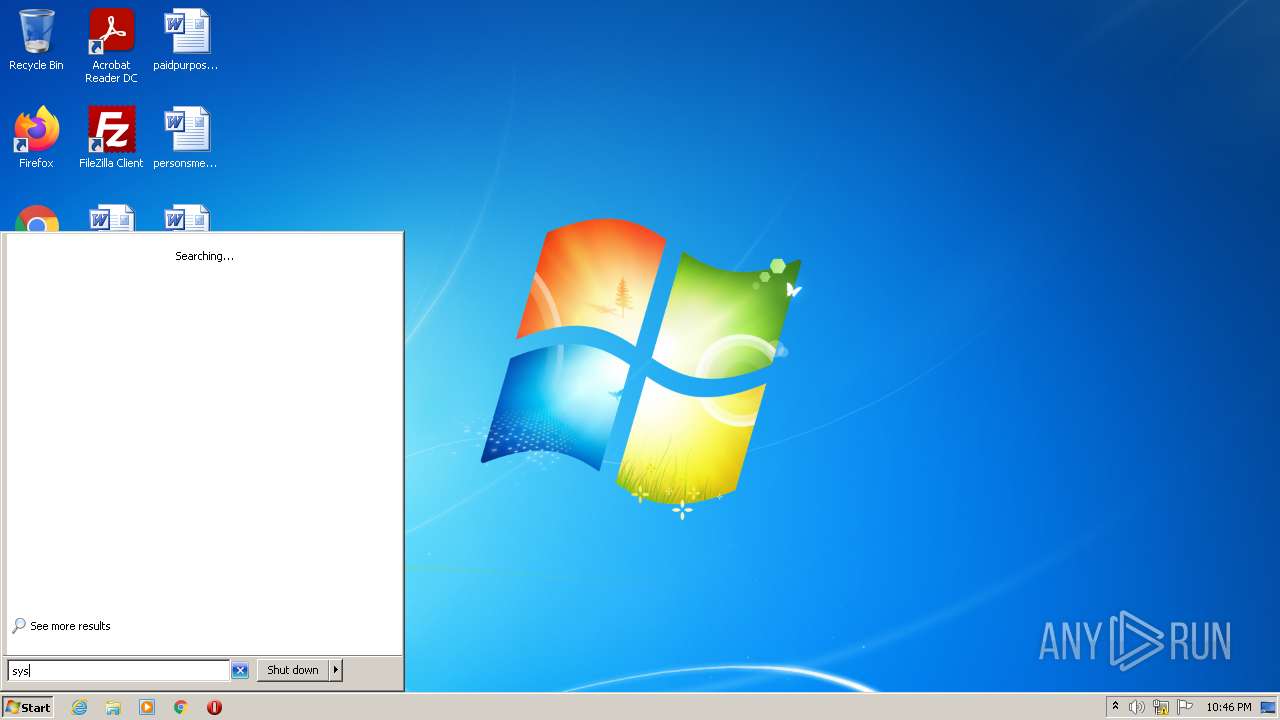
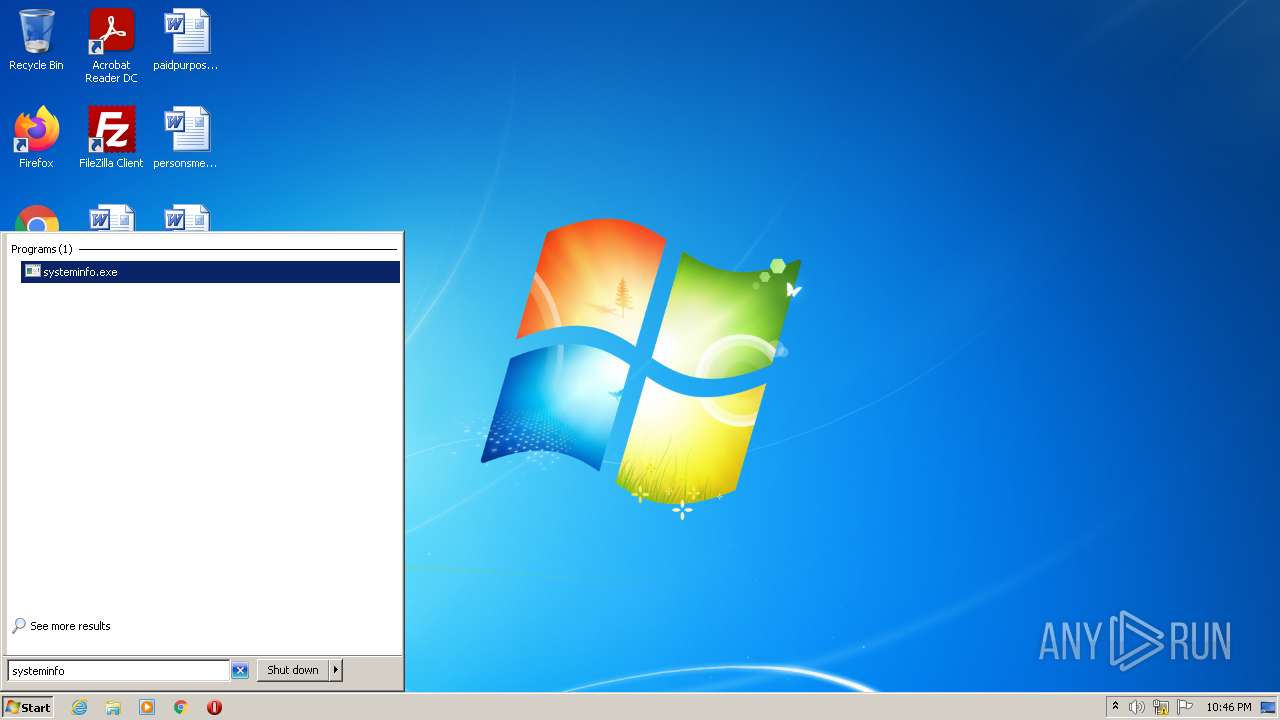
Manual execution by user
- msinfo32.exe (PID: 2532)
Reads the computer name
- msinfo32.exe (PID: 2532)
Checks supported languages
- msinfo32.exe (PID: 2532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| ProductVersion: | 30.100.1943.2 |
|---|---|
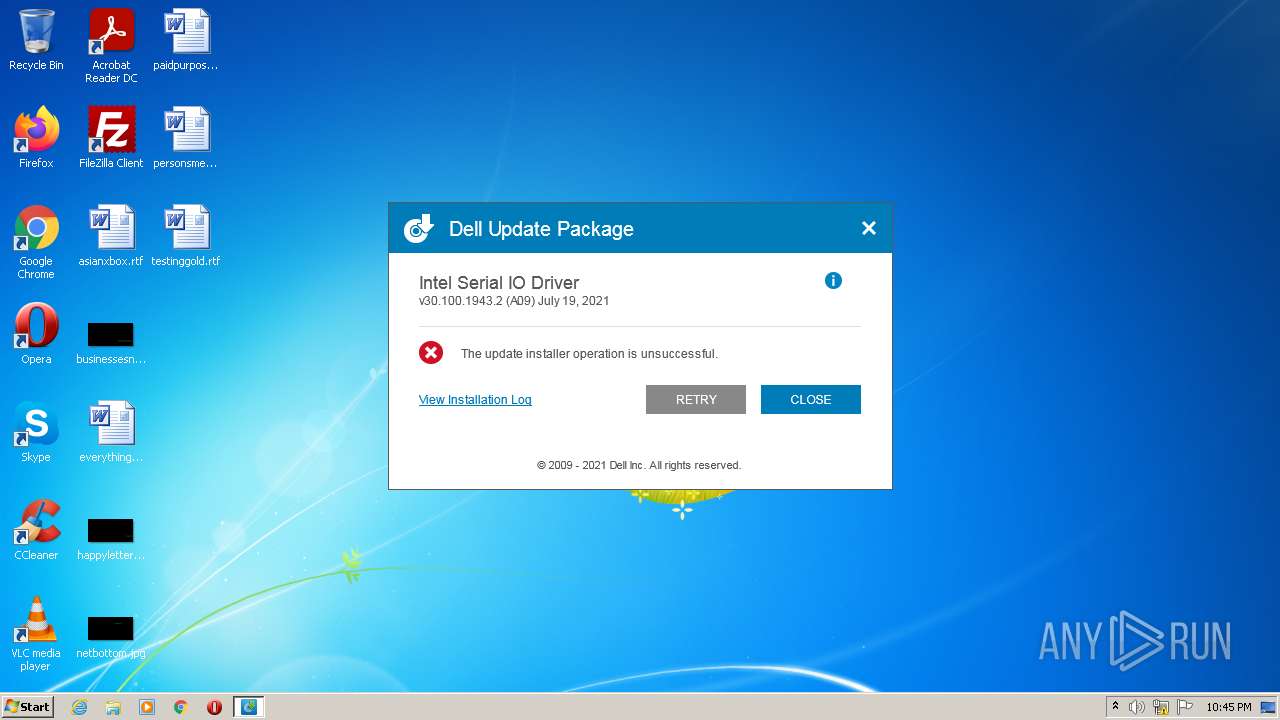
| ProductName: | Intel Serial IO Driver, 30.100.1943.2, A09 |
| OriginalFileName: | DUPFramework.exe |
| LegalCopyright: | Copyright (C) Dell Inc. 2021. All rights reserved. |
| InternalName: | DUPFramework.exe |
| FileVersion: | 004.008.007.000 |
| FileDescription: | Dell Update Package: Intel Serial IO Driver, 30.100.1943.2, A09 |
| CompanyName: | Dell Inc. |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 4.8.7.0 |
| FileVersionNumber: | 4.8.9.106 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x1fb4a |
| UninitializedDataSize: | - |
| InitializedDataSize: | 3369984 |
| CodeSize: | 5544960 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2021:07:29 07:14:55+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Total processes
45
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1936 | C:\Users\admin\AppData\Local\Temp\IIF229D.tmp\setup.exe /report C:\ProgramData\dell\drivers\121990f1-1e2e-444e-83fb-20834060c85e\DUP224F.tmp | C:\Users\admin\AppData\Local\Temp\IIF229D.tmp\setup.exe | SetupSerialIO.exe | ||||||||||||
User: admin Company: Intel Corporation Integrity Level: HIGH Description: Intel(R) Serial IO installer Exit code: 1603 Version: 3.0.2708.5 Modules
| |||||||||||||||
| 2332 | "C:\ProgramData\Dell\drivers\121990f1-1e2e-444e-83fb-20834060c85e\SetupSerialIO.exe" /report "C:\ProgramData\dell\drivers\121990f1-1e2e-444e-83fb-20834060c85e\DUP224F.tmp" | C:\ProgramData\Dell\drivers\121990f1-1e2e-444e-83fb-20834060c85e\SetupSerialIO.exe | Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE | ||||||||||||
User: admin Company: Intel Corporation Integrity Level: HIGH Description: Intel(R) Serial IO installer Exit code: 1603 Version: 3.0.2708.5 Modules
| |||||||||||||||
| 2532 | "C:\Windows\system32\msinfo32.exe" | C:\Windows\system32\msinfo32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: System Information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3180 | "C:\Users\admin\AppData\Local\Temp\Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE" | C:\Users\admin\AppData\Local\Temp\Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Dell Inc. Integrity Level: MEDIUM Description: Dell Update Package: Intel Serial IO Driver, 30.100.1943.2, A09 Exit code: 3221226540 Version: 004.008.007.000 Modules
| |||||||||||||||
| 3804 | "C:\Users\admin\AppData\Local\Temp\Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE" | C:\Users\admin\AppData\Local\Temp\Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Dell Inc. Integrity Level: HIGH Description: Dell Update Package: Intel Serial IO Driver, 30.100.1943.2, A09 Exit code: 3 Version: 004.008.007.000 Modules
| |||||||||||||||
| 3880 | -x C:\Users\admin\AppData\Local\Temp\INTEL-~1.EXE -o -d c:\PROGRA~2\dell\drivers\121990~1 | c:\PROGRA~2\dell\drivers\121990~1\miniunz.exe | Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
759
Read events
746
Write events
13
Delete events
0
Modification events
| (PID) Process: | (3804) Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3804) Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3804) Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3804) Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3804) Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3804) Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3804) Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3804) Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3804) Intel-Serial-IO-Driver_6CYP4_WIN_30.100.1943.2_A09_04.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
63
Suspicious files
2
Text files
31
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3880 | miniunz.exe | C:\PROGRA~2\dell\drivers\121990~1\package.xml | binary | |
MD5:— | SHA256:— | |||
| 3880 | miniunz.exe | C:\PROGRA~2\dell\drivers\121990~1\production\Windows10-x64\0\Drivers\WU\ialpss2_i2c_skl.cat | cat | |
MD5:— | SHA256:— | |||
| 3880 | miniunz.exe | C:\PROGRA~2\dell\drivers\121990~1\production\Windows10-x64\0\Drivers\WU\iaLPSS2_GPIO2_SKL.inf | txt | |
MD5:— | SHA256:— | |||
| 3880 | miniunz.exe | C:\PROGRA~2\dell\drivers\121990~1\production\Windows10-x64\0\Drivers\WU\iaLPSS2_I2C.sys | executable | |
MD5:— | SHA256:— | |||
| 3880 | miniunz.exe | C:\PROGRA~2\dell\drivers\121990~1\mup.xml | xml | |
MD5:— | SHA256:— | |||
| 3880 | miniunz.exe | C:\PROGRA~2\dell\drivers\121990~1\production\Windows10-x64\0\Drivers\WU\ialpss2_gpio2_skl.cat | cat | |
MD5:— | SHA256:— | |||
| 3880 | miniunz.exe | C:\PROGRA~2\dell\drivers\121990~1\production\Windows10-x64\0\Drivers\WU\iaLPSS2_I2C_SKL.inf | txt | |
MD5:— | SHA256:— | |||
| 3880 | miniunz.exe | C:\PROGRA~2\dell\drivers\121990~1\production\Windows10-x64\0\Drivers\WU\iaLPSS2_SPI.sys | executable | |
MD5:— | SHA256:— | |||
| 3880 | miniunz.exe | C:\PROGRA~2\dell\drivers\121990~1\production\Windows10-x64\0\Drivers\WU\iaLPSS2_UART2.sys | executable | |
MD5:— | SHA256:— | |||
| 3880 | miniunz.exe | C:\PROGRA~2\dell\drivers\121990~1\production\Windows10-x64\0\Drivers\WU\ialpss2_uart2_skl.cat | cat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report