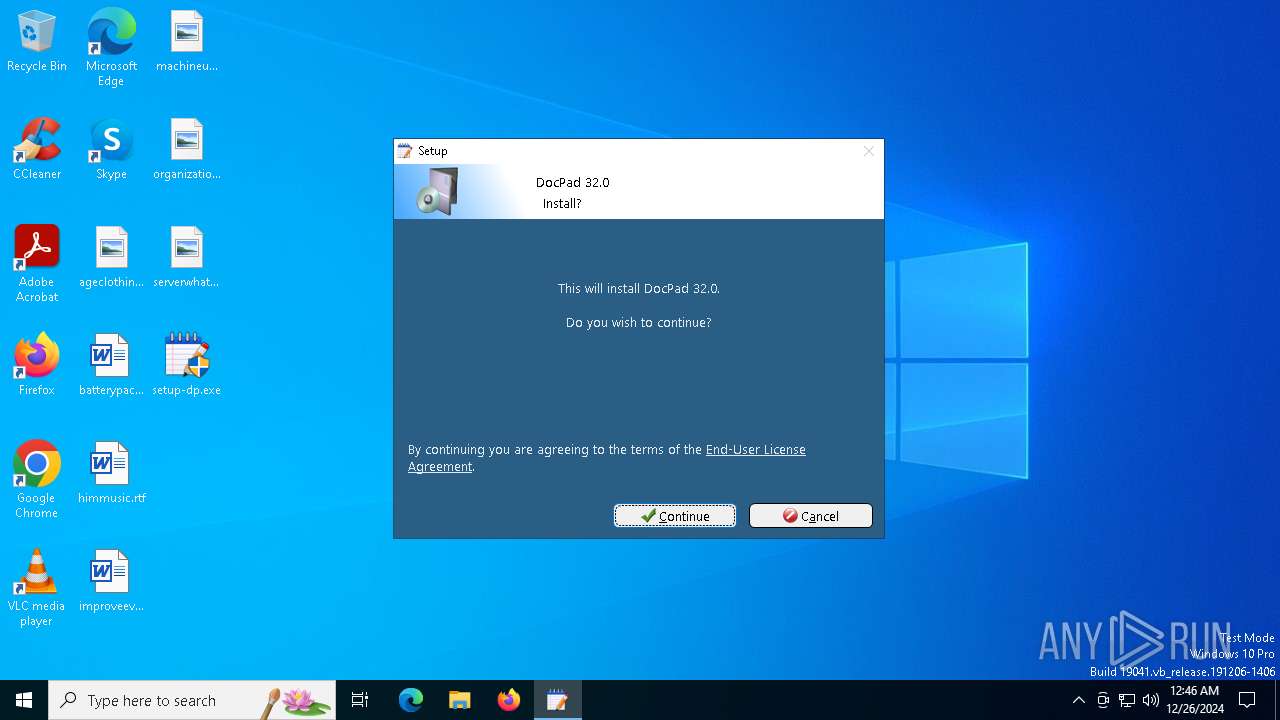
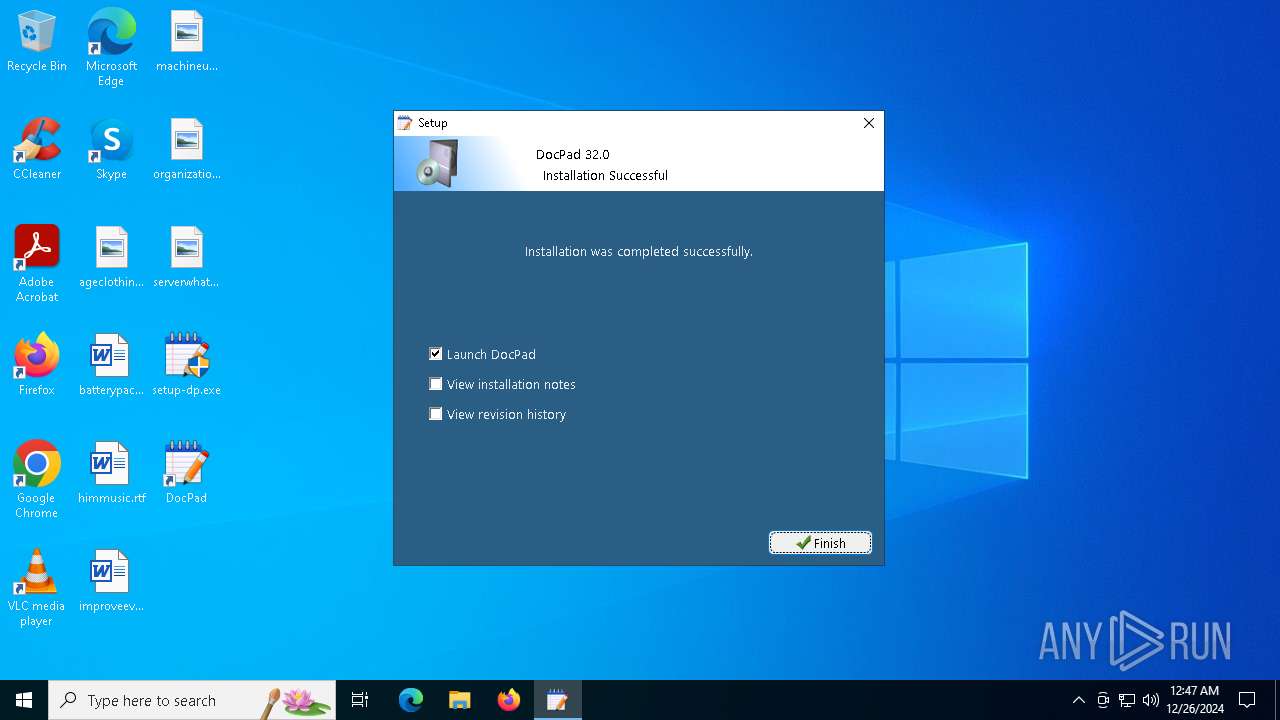
| File name: | setup-dp.exe |
| Full analysis: | https://app.any.run/tasks/fe127198-0d02-4a0d-9888-9a11d9e1af97 |
| Verdict: | Malicious activity |
| Analysis date: | December 26, 2024, 00:46:18 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 285347925E7985CCCC5752A1FCDBB5C2 |
| SHA1: | 6AB3DA7D3157253324A0C526052776C37CF3BCBC |
| SHA256: | E047617AEDC8BF097F7BADB219AAAFC6C2C0E912A1AD444EDA206C313C558030 |
| SSDEEP: | 196608:4f6Q4eBAmfYL28Jc3GlYeay0IkVcfapxCO:4Z488iZdvcipN |
MALICIOUS
No malicious indicators.SUSPICIOUS
Searches for installed software
- setup-dp.exe (PID: 4500)
Reads security settings of Internet Explorer
- setup-dp.exe (PID: 4500)
- docpad.exe (PID: 3436)
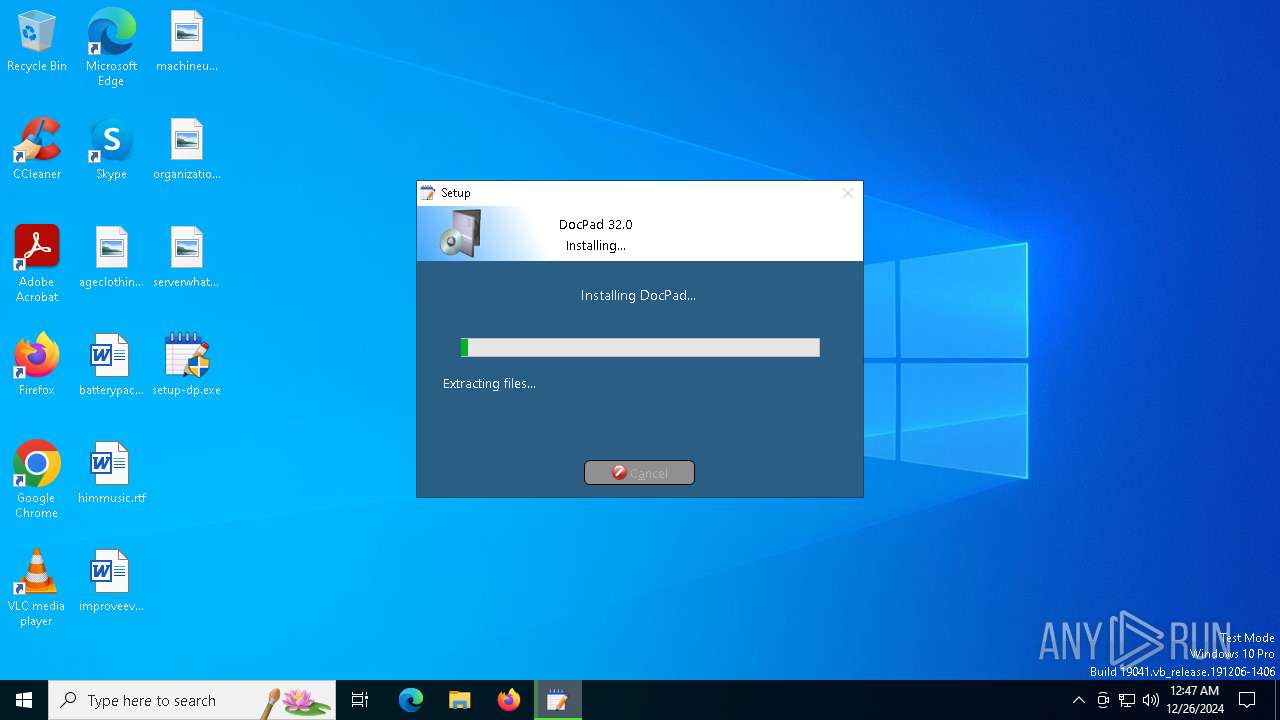
Executable content was dropped or overwritten
- cmd.exe (PID: 5240)
- setup-dp.exe (PID: 4500)
Executing commands from a ".bat" file
- setup-dp.exe (PID: 4500)
Starts CMD.EXE for commands execution
- setup-dp.exe (PID: 4500)
Starts application with an unusual extension
- cmd.exe (PID: 5240)
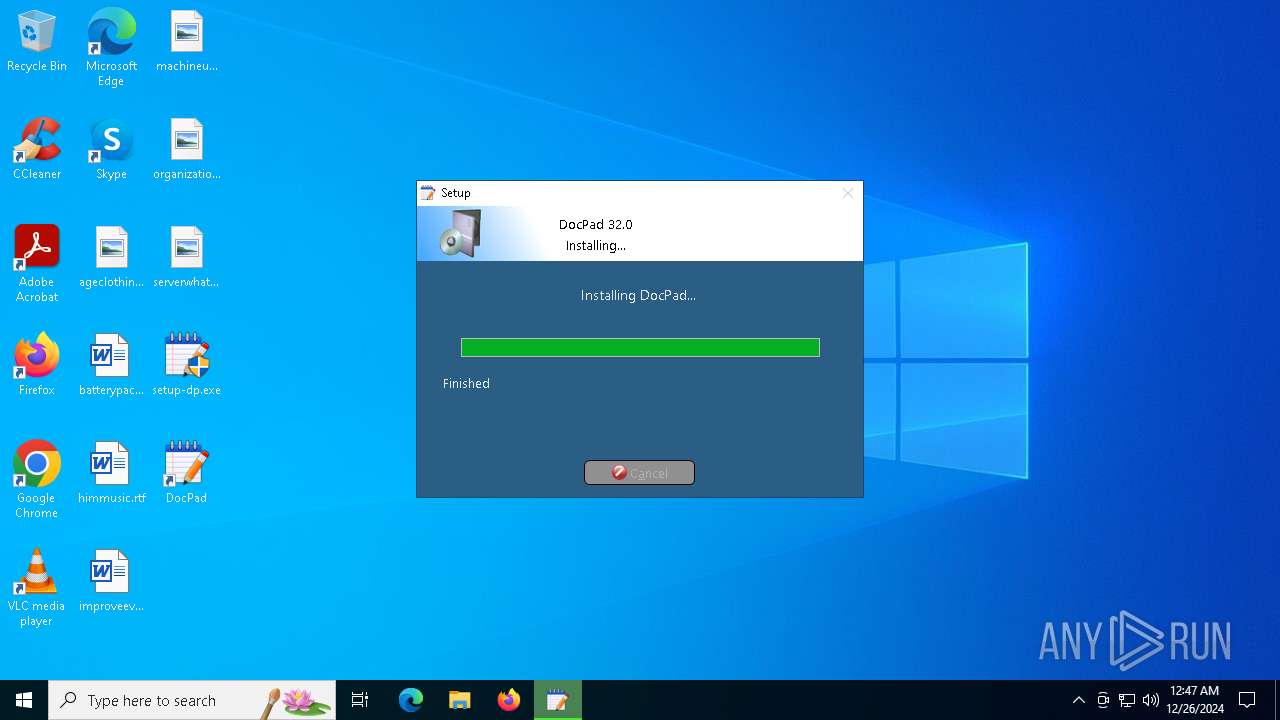
Creates a software uninstall entry
- setup-dp.exe (PID: 4500)
INFO
Reads the computer name
- setup-dp.exe (PID: 4500)
- docpad.exe (PID: 3436)
The sample compiled with english language support
- setup-dp.exe (PID: 4500)
- cmd.exe (PID: 5240)
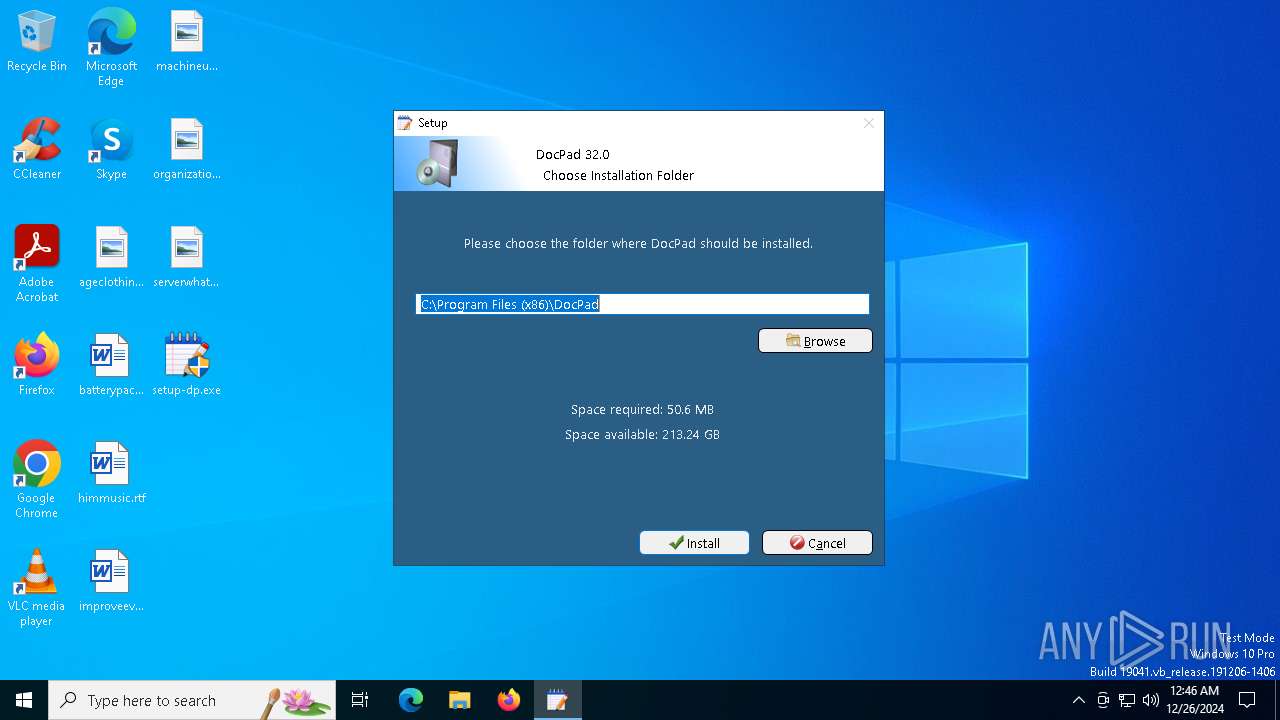
Creates files or folders in the user directory
- setup-dp.exe (PID: 4500)
Creates files in the program directory
- setup-dp.exe (PID: 4500)
- cmd.exe (PID: 5240)
Checks supported languages
- setup-dp.exe (PID: 4500)
- chcp.com (PID: 644)
- docpad.exe (PID: 3436)
Create files in a temporary directory
- setup-dp.exe (PID: 4500)
Changes the display of characters in the console
- cmd.exe (PID: 5240)
Checks proxy server information
- setup-dp.exe (PID: 4500)
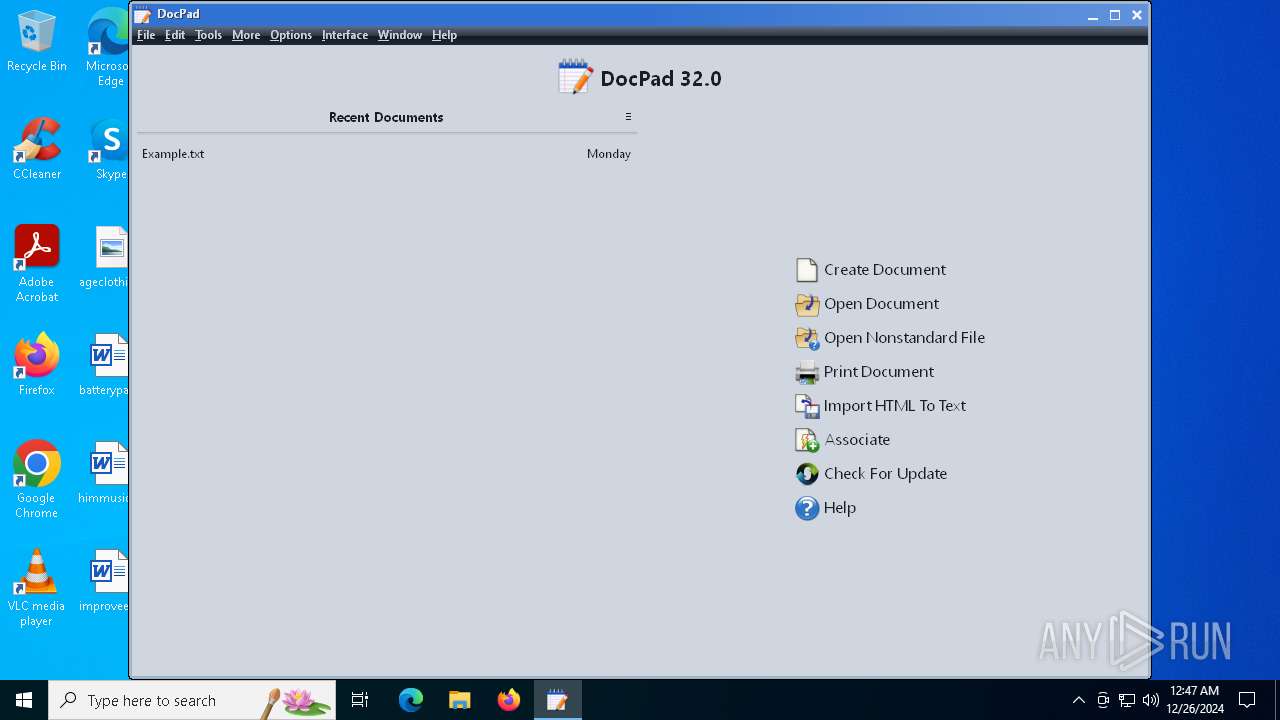
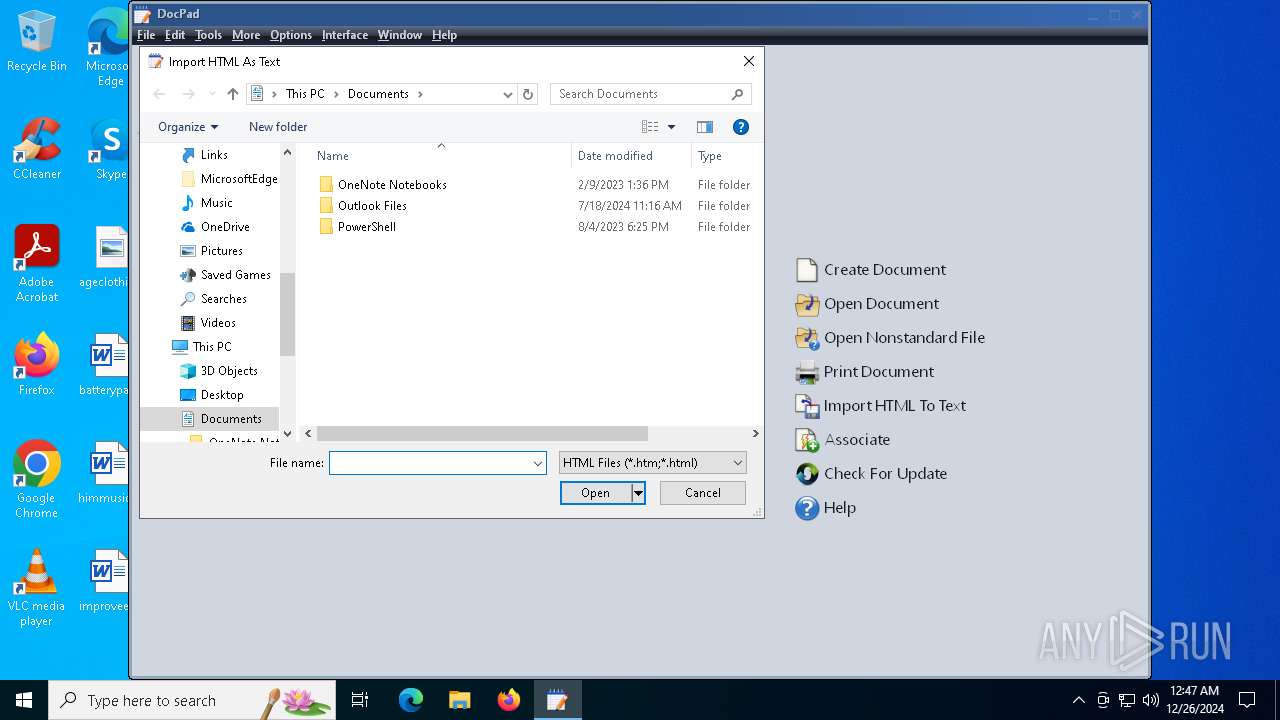
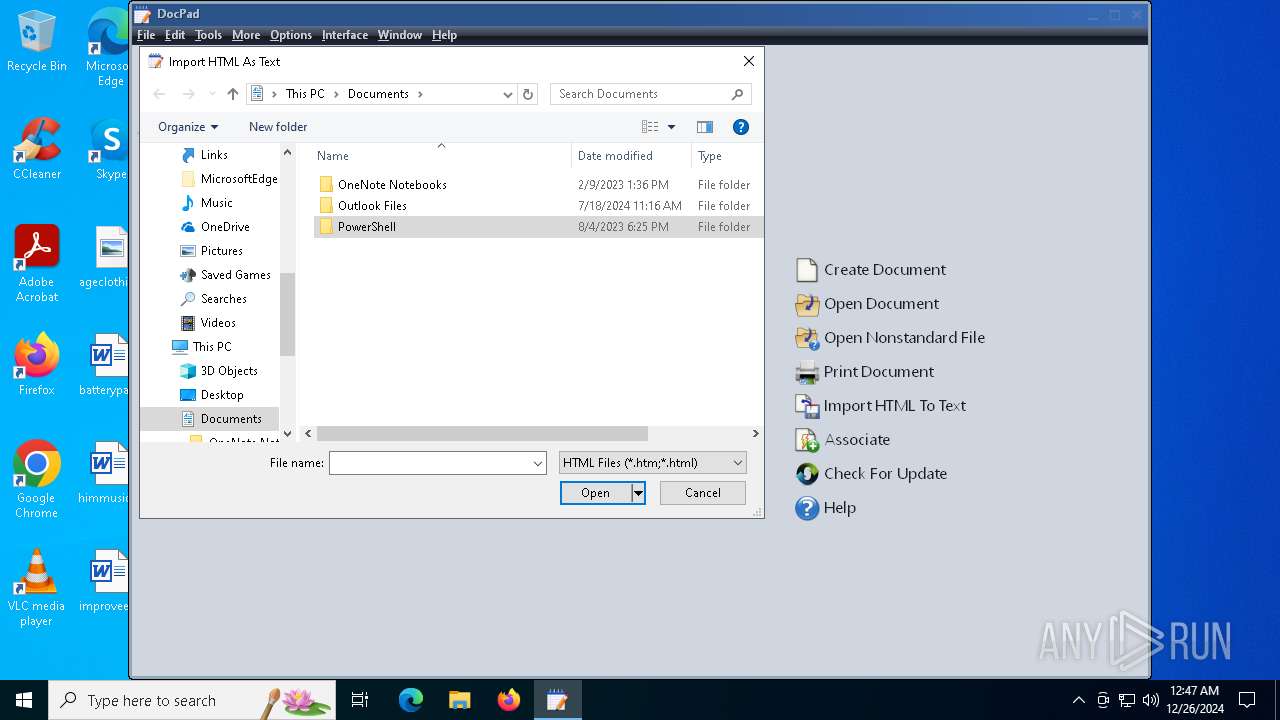
Manual execution by a user
- docpad.exe (PID: 3436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:12:23 21:08:51+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 871424 |
| InitializedDataSize: | 13852672 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa8ec0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 32.0.0.0 |
| ProductVersionNumber: | 32.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileDescription: | Installer for DocPad |
| ProductName: | DocPad |
| CompanyName: | Gammadyne |
| LegalCopyright: | Copyright (C) 2024 by Gammadyne |
| ProductVersion: | 32 |
| FileVersion: | 32 |
Total processes
126
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | chcp 1252 | C:\Windows\SysWOW64\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3436 | "C:\Program Files (x86)\DocPad\docpad.exe" | C:\Program Files (x86)\DocPad\docpad.exe | — | explorer.exe | |||||||||||
User: admin Company: Gammadyne Corporation Integrity Level: MEDIUM Description: DocPad Version: 32.0 Modules
| |||||||||||||||
| 4500 | "C:\Users\admin\Desktop\setup-dp.exe" | C:\Users\admin\Desktop\setup-dp.exe | explorer.exe | ||||||||||||
User: admin Company: Gammadyne Integrity Level: HIGH Description: Installer for DocPad Exit code: 0 Version: 32.0 Modules
| |||||||||||||||
| 4592 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5240 | "C:\WINDOWS\system32\cmd.exe" /c "C:\PROGRA~2\DocPad\SETUPBAT.BAT > C:\PROGRA~2\DocPad\cs_batch.log" | C:\Windows\SysWOW64\cmd.exe | setup-dp.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5892 | "C:\Users\admin\Desktop\setup-dp.exe" | C:\Users\admin\Desktop\setup-dp.exe | — | explorer.exe | |||||||||||
User: admin Company: Gammadyne Integrity Level: MEDIUM Description: Installer for DocPad Exit code: 3221226540 Version: 32.0 Modules
| |||||||||||||||
Total events
4 369
Read events
4 246
Write events
116
Delete events
7
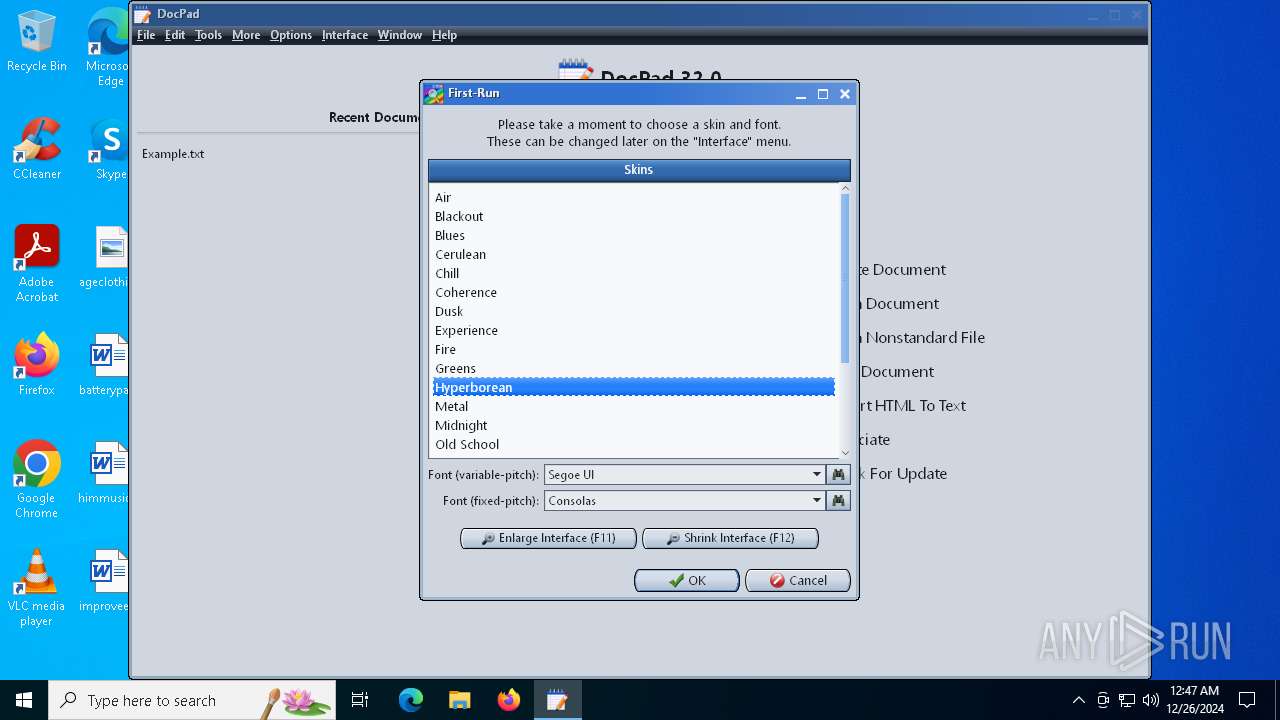
Modification events
| (PID) Process: | (4500) setup-dp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\System-G\Air.skin |
Value: 1 | |||
| (PID) Process: | (4500) setup-dp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\System-G\Blackout.skin |
Value: 1 | |||
| (PID) Process: | (4500) setup-dp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\System-G\Blues.skin |
Value: 1 | |||
| (PID) Process: | (4500) setup-dp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\System-G\Cerulean.skin |
Value: 1 | |||
| (PID) Process: | (4500) setup-dp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\System-G\Chill.skin |
Value: 1 | |||
| (PID) Process: | (4500) setup-dp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\System-G\Coherence.skin |
Value: 1 | |||
| (PID) Process: | (4500) setup-dp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\System-G\Dusk.skin |
Value: 1 | |||
| (PID) Process: | (4500) setup-dp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\System-G\Experience.skin |
Value: 1 | |||
| (PID) Process: | (4500) setup-dp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\System-G\Fire.skin |
Value: 1 | |||
| (PID) Process: | (4500) setup-dp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\System-G\Greens.skin |
Value: 1 | |||
Executable files
4
Suspicious files
11
Text files
35
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4500 | setup-dp.exe | C:\Program Files (x86)\DocPad\help10010.gdfc | binary | |
MD5:E9DE7C2FABDE52275502B4AF454D4474 | SHA256:E2FB6B4595655542698F67D6D1CECC35056249AEC9639D1DD074D3E3BF6F2F06 | |||
| 4500 | setup-dp.exe | C:\Program Files (x86)\DocPad\eula.txt | text | |
MD5:7747A61AF745C2B889F611D758C374BF | SHA256:D73F57E77B6EF1AF2F4400B27C3AF1B475CBCB17A4B5E676E4950E73DE212BD7 | |||
| 4500 | setup-dp.exe | C:\Program Files (x86)\Common Files\System-G\Cerulean.skin | text | |
MD5:8F860A5F0A37944FAE37C64BFE816F3A | SHA256:B320804D1B614502E10C60BC1E2904572DE578FA64AFFFF380271AC9417DFDB2 | |||
| 4500 | setup-dp.exe | C:\Program Files (x86)\Common Files\System-G\Midnight.skin | text | |
MD5:C31A9EEF121A83C3D4BF1FBD2353686E | SHA256:D1EACD4B61765F0C6933AB17AEE5E6276C14F13335A7926DC0DE31BC8393AAE3 | |||
| 4500 | setup-dp.exe | C:\Program Files (x86)\DocPad\docpad.exe | executable | |
MD5:EB0A4882821F1EF9EB15B0E99BE8BCFD | SHA256:14D00F356BE399262243EA6CD049CE30B506D7BB1793FD34DEA0A966B651343A | |||
| 4500 | setup-dp.exe | C:\Program Files (x86)\DocPad\readme.txt | text | |
MD5:831286735831BC1B1CD42354451378EB | SHA256:860FAF62C301D3949C265E47193854812CFC564EEACD8C804374190CFE212C2E | |||
| 4500 | setup-dp.exe | C:\Program Files (x86)\Common Files\System-G\Fire.skin | text | |
MD5:E010C179DAD5BF47CD412285A387D369 | SHA256:F6E624289EED7E8E0EFAC65BC11C0A6AD35117838860B0AB005FDB3488B6A87B | |||
| 4500 | setup-dp.exe | C:\Program Files (x86)\Common Files\System-G\Coherence.skin | text | |
MD5:CA141474F39864329DBF3648BE7C176B | SHA256:9BF74F51C62EAE9D466254BE00F06D9005B57AC9D7A55E26994554BA0E946714 | |||
| 4500 | setup-dp.exe | C:\Program Files (x86)\DocPad\systemg.gdfc | binary | |
MD5:04F47A1AB395C05694938D2C3AB91463 | SHA256:1F14BA48FEDFA5E5D768AE15CB4DAD46F102F4CA0E4FA76EC94D3EAA96692104 | |||
| 4500 | setup-dp.exe | C:\Program Files (x86)\Common Files\System-G\Hyperborean.skin | text | |
MD5:023AE4BA80AA2468B158B43F6B7409B3 | SHA256:7EEA786BA683B1754C6B761506909E3E00168FB28A22EE77D3DC573E3E126209 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
20
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6072 | svchost.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6072 | svchost.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4500 | setup-dp.exe | GET | 200 | 96.43.130.227:80 | http://act.gammadyne.com/install.php?t=16&p=10010&v=32.0&s=5F85EECB7F5A4158 | unknown | — | — | unknown |
4500 | setup-dp.exe | GET | 200 | 96.43.130.227:80 | http://act.gammadyne.com/install.php?t=9&p=10010&v=32.0&s=5F85EECB7F5A4158 | unknown | — | — | unknown |
4500 | setup-dp.exe | GET | 200 | 96.43.130.227:80 | http://act.gammadyne.com/install.php?t=15&p=10010&v=32.0&s=5F85EECB7F5A4158 | unknown | — | — | unknown |
— | — | POST | 204 | 2.21.110.146:443 | https://www.bing.com/threshold/xls.aspx | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6072 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6072 | svchost.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
6072 | svchost.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4500 | setup-dp.exe | 96.43.130.227:80 | act.gammadyne.com | JOESDATACENTER | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.21.110.139:443 | www.bing.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
act.gammadyne.com |
| unknown |
www.bing.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |