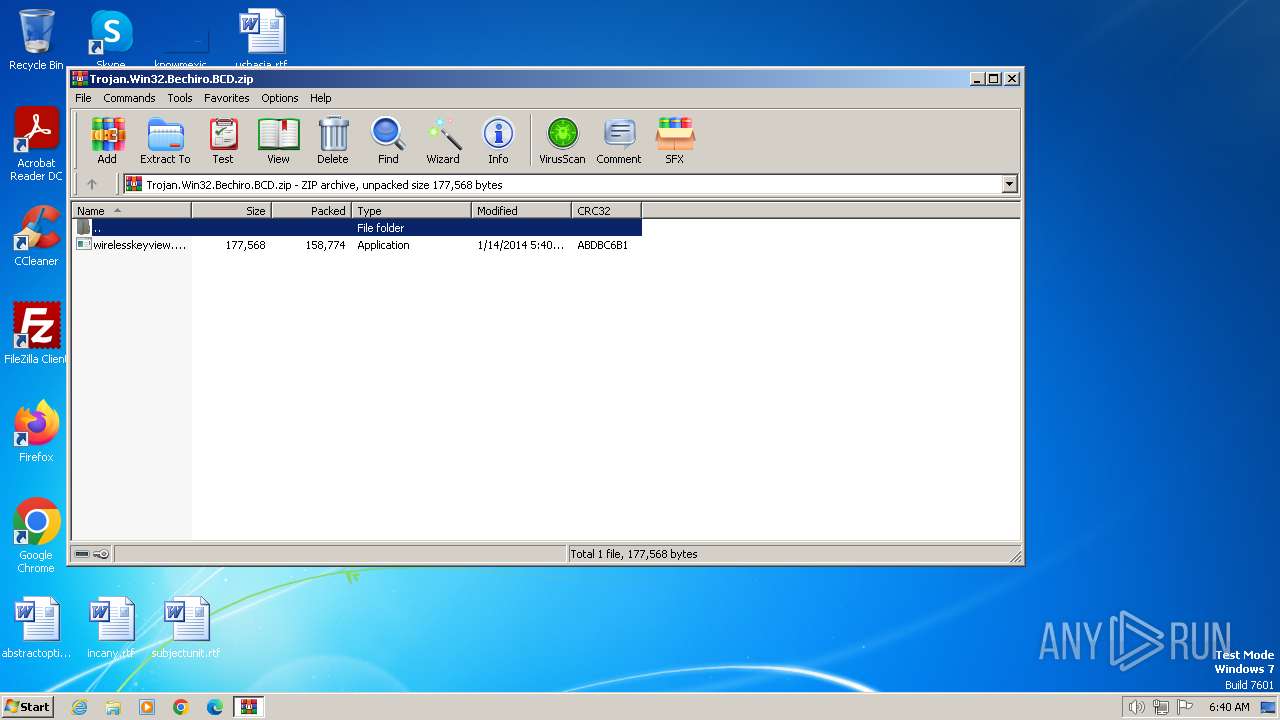
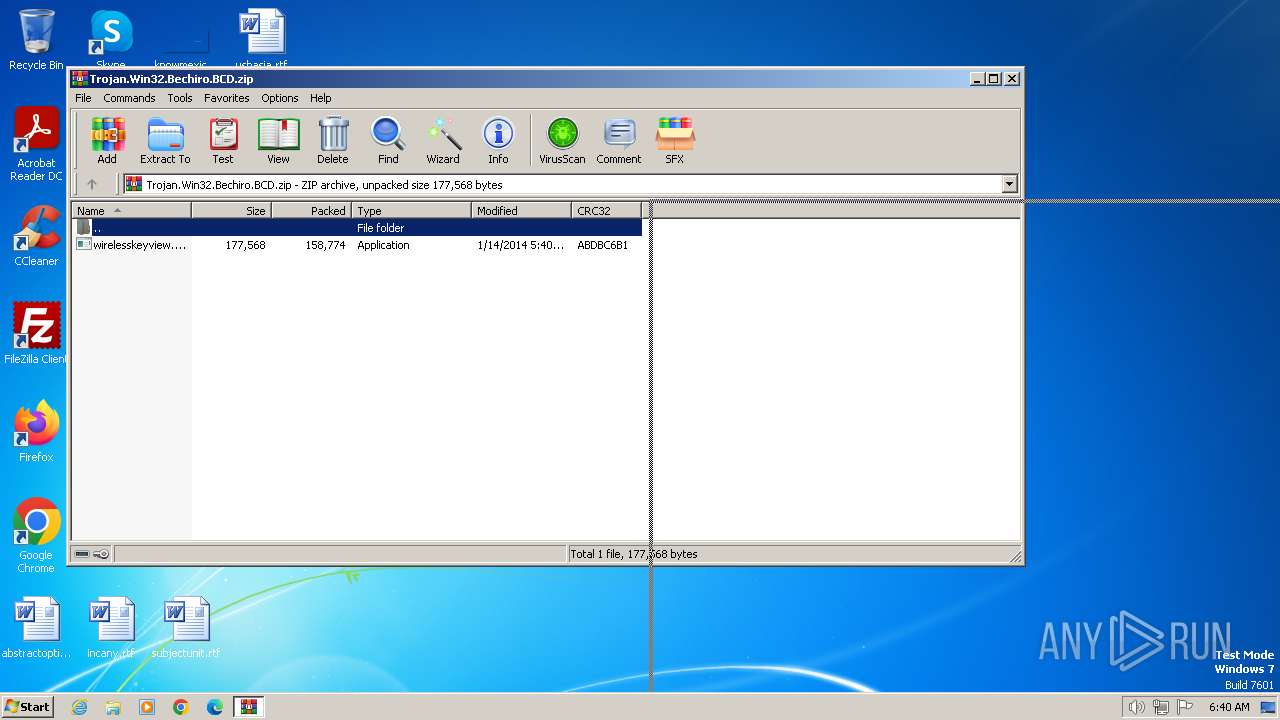
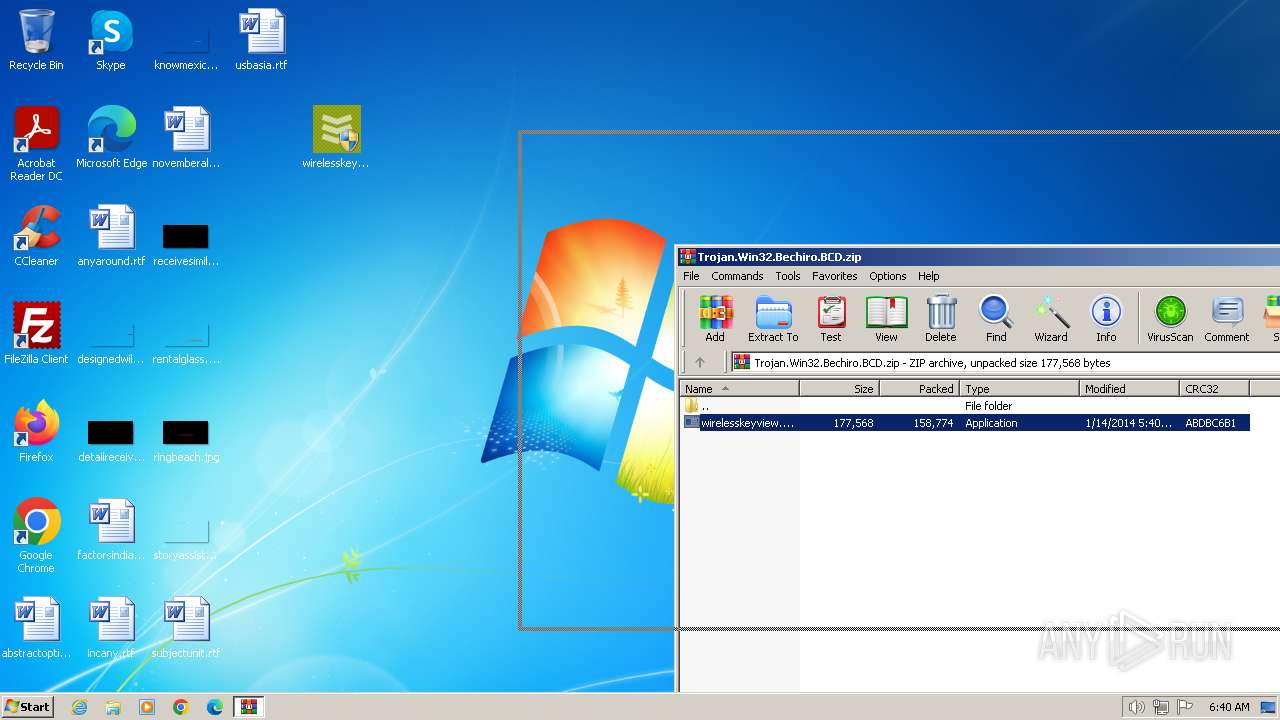
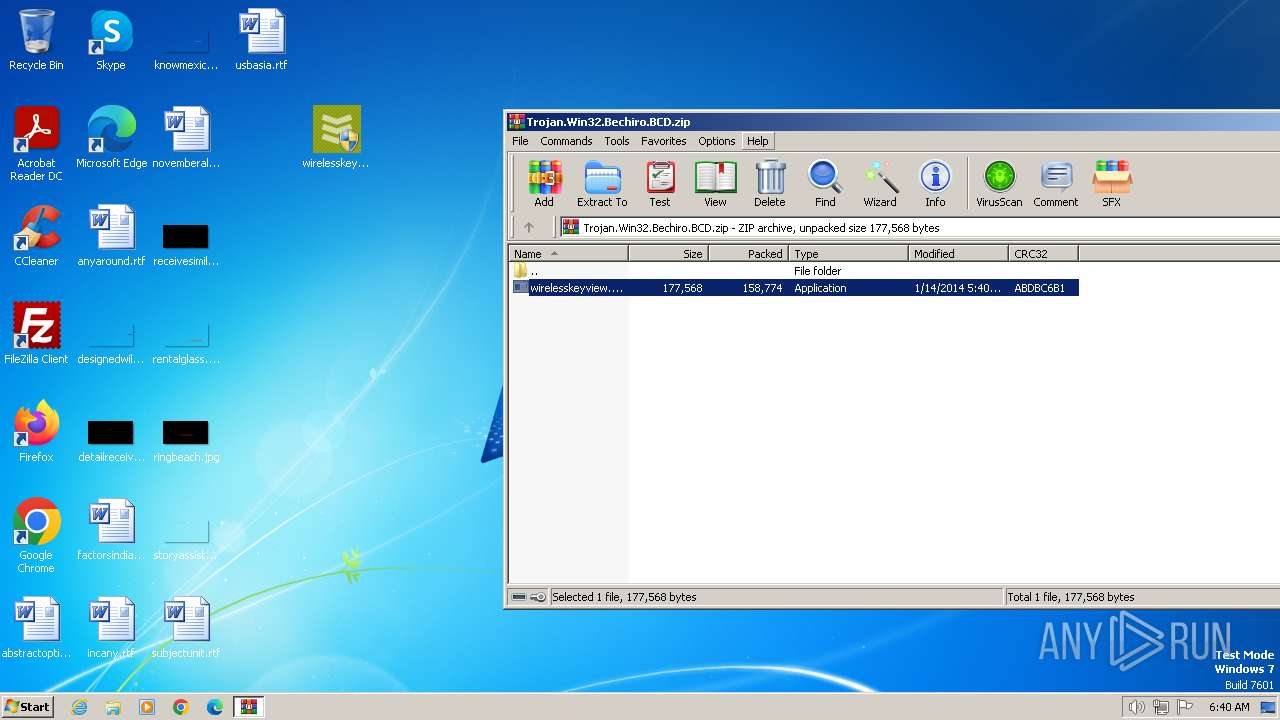
| File name: | Trojan.Win32.Bechiro.BCD.zip |
| Full analysis: | https://app.any.run/tasks/370127e2-90d2-4b90-8ed7-5d7a1db15b90 |
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2024, 06:40:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 2728F56DED381F275F11EEC9DAF8D68B |
| SHA1: | 664DD7FE30F1BB70152E4288E161F264F8FE79D5 |
| SHA256: | E0438C7752E11B4198A4F62B86BE72737CFB7865777B6CDC8166872AE857A061 |
| SSDEEP: | 6144:6zkZrIVdVf2/Tm3Qs3ndXgt/nQiMx3+ZP8D:k4sBO/T6Qynhgtf0xKP8D |
MALICIOUS
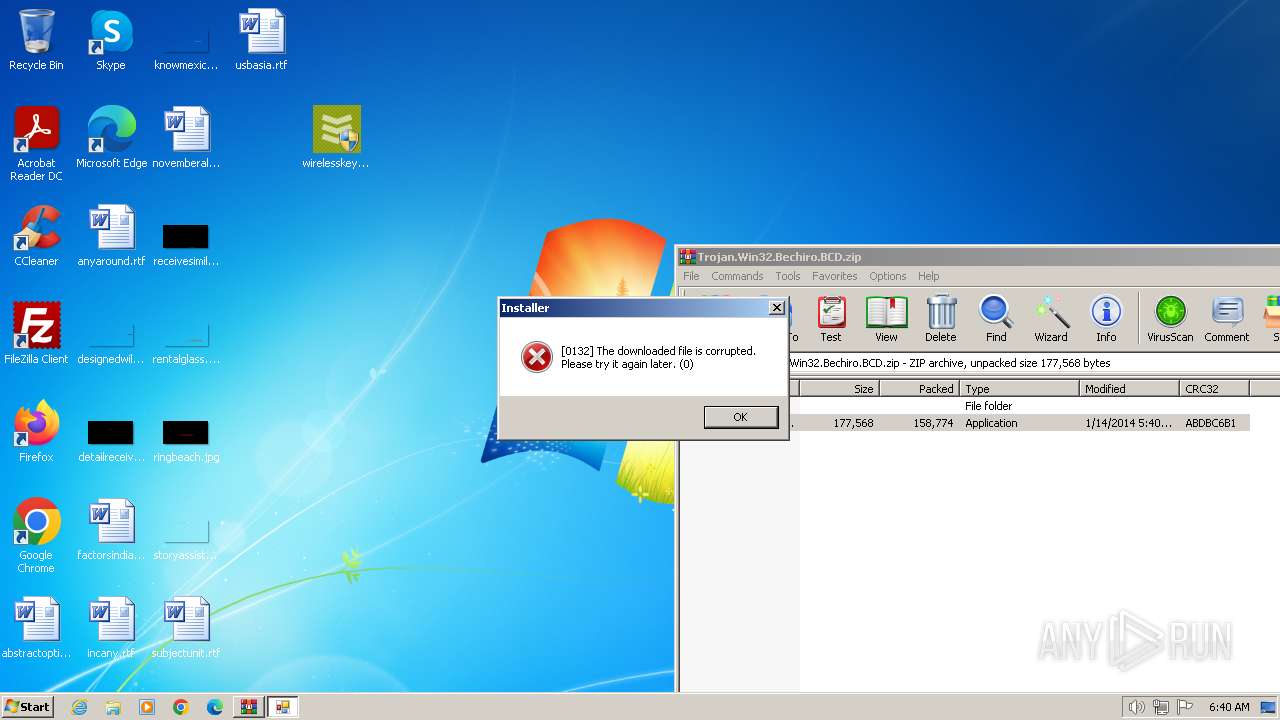
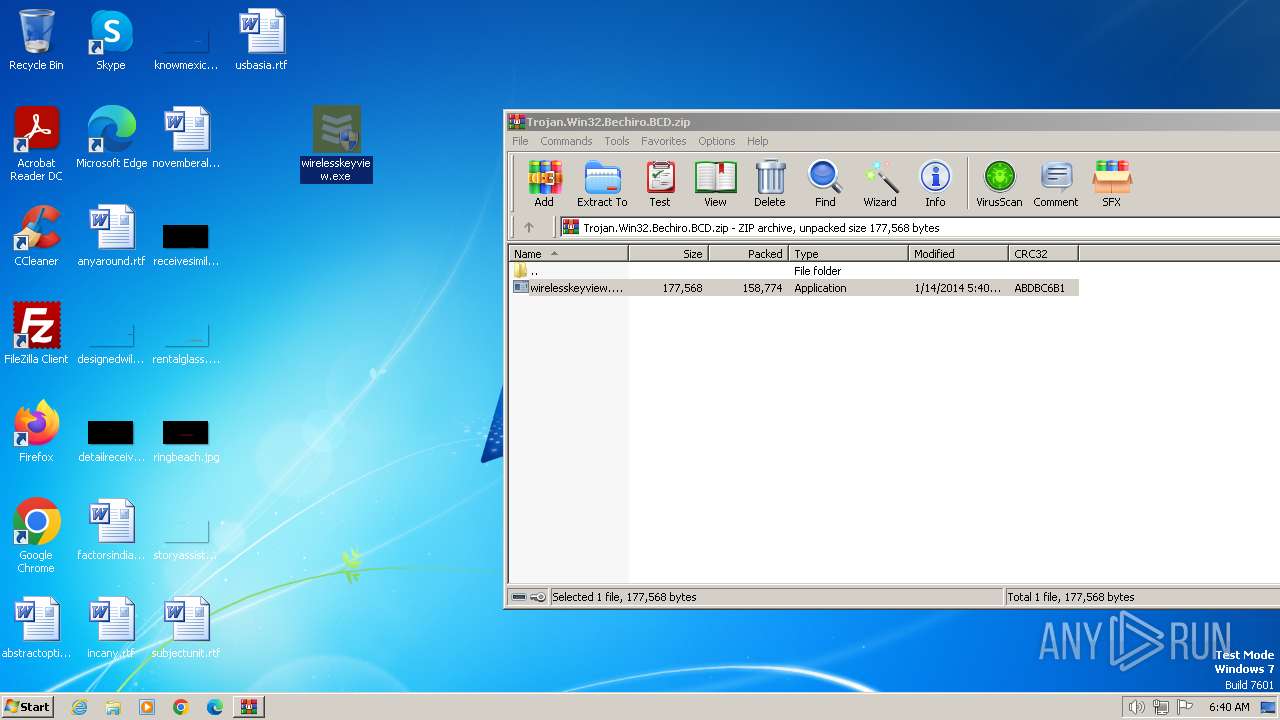
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2632)
- wirelesskeyview.exe (PID: 2828)
- wirelesskeyview.exe (PID: 1484)
SUSPICIOUS
Reads the Internet Settings
- wirelesskeyview.exe (PID: 2828)
- wirelesskeyview.exe (PID: 1484)
Executable content was dropped or overwritten
- wirelesskeyview.exe (PID: 2828)
- wirelesskeyview.exe (PID: 1484)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2632)
Checks supported languages
- wirelesskeyview.exe (PID: 2828)
- ins2352.exe (PID: 2728)
- wirelesskeyview.exe (PID: 1484)
- ins2421.exe (PID: 3028)
Reads the computer name
- wirelesskeyview.exe (PID: 2828)
- ins2352.exe (PID: 2728)
- wirelesskeyview.exe (PID: 1484)
- ins2421.exe (PID: 3028)
Reads Environment values
- ins2352.exe (PID: 2728)
- ins2421.exe (PID: 3028)
Reads the machine GUID from the registry
- ins2352.exe (PID: 2728)
- ins2421.exe (PID: 3028)
Create files in a temporary directory
- wirelesskeyview.exe (PID: 2828)
- wirelesskeyview.exe (PID: 1484)
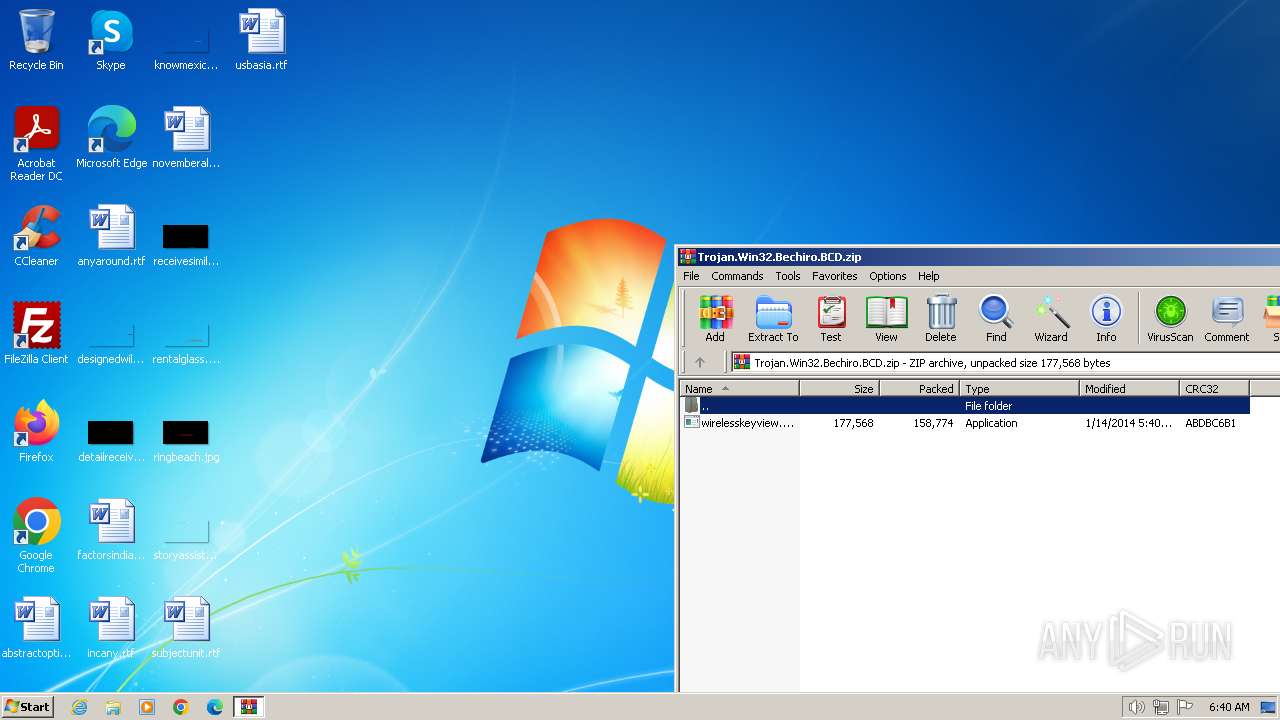
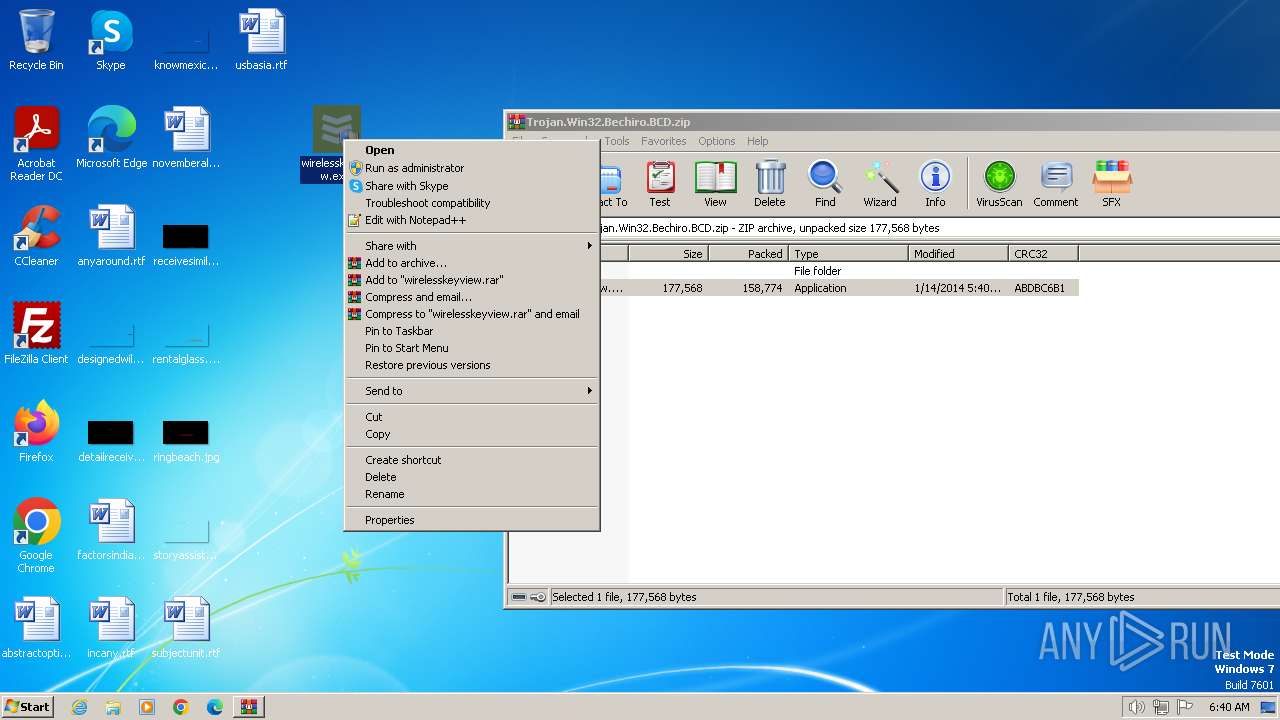
Manual execution by a user
- wirelesskeyview.exe (PID: 2828)
- wirelesskeyview.exe (PID: 1904)
- wirelesskeyview.exe (PID: 1484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2014:01:14 07:40:26 |
| ZipCRC: | 0xabdbc6b1 |
| ZipCompressedSize: | 158774 |
| ZipUncompressedSize: | 177568 |
| ZipFileName: | wirelesskeyview.exe |
Total processes
49
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1484 | "C:\Users\admin\Desktop\wirelesskeyview.exe" | C:\Users\admin\Desktop\wirelesskeyview.exe | explorer.exe | ||||||||||||
User: admin Company: *Rapiddown* Integrity Level: HIGH Description: Setup Manager Exit code: 0 Version: 1.0.0.30 Modules
| |||||||||||||||
| 1904 | "C:\Users\admin\Desktop\wirelesskeyview.exe" | C:\Users\admin\Desktop\wirelesskeyview.exe | — | explorer.exe | |||||||||||
User: admin Company: *Rapiddown* Integrity Level: MEDIUM Description: Setup Manager Exit code: 3221226540 Version: 1.0.0.30 Modules
| |||||||||||||||
| 2632 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Trojan.Win32.Bechiro.BCD.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2728 | "C:\Users\admin\AppData\Local\Temp\n2352\ins2352.exe" ins.exe /e4878377 /u4fe0cf9f-1fe4-4abb-905a-57915bc06f2f | C:\Users\admin\AppData\Local\Temp\n2352\ins2352.exe | wirelesskeyview.exe | ||||||||||||
User: admin Company: ·Rapiddown· Integrity Level: HIGH Description: ·Appsinstall Exit code: 23 Version: 3.0.26.4 Modules
| |||||||||||||||
| 2828 | "C:\Users\admin\Desktop\wirelesskeyview.exe" | C:\Users\admin\Desktop\wirelesskeyview.exe | explorer.exe | ||||||||||||
User: admin Company: *Rapiddown* Integrity Level: HIGH Description: Setup Manager Exit code: 0 Version: 1.0.0.30 Modules
| |||||||||||||||
| 3028 | "C:\Users\admin\AppData\Local\Temp\n2421\ins2421.exe" ins.exe /e4878377 /u4fe0cf9f-1fe4-4abb-905a-57915bc06f2f | C:\Users\admin\AppData\Local\Temp\n2421\ins2421.exe | wirelesskeyview.exe | ||||||||||||
User: admin Company: ·Rapiddown· Integrity Level: HIGH Description: ·Appsinstall Exit code: 0 Version: 3.0.26.4 Modules
| |||||||||||||||
Total events
3 510
Read events
3 485
Write events
25
Delete events
0
Modification events
| (PID) Process: | (2632) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2828) wirelesskeyview.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2632 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2632.40482\wirelesskeyview.exe | executable | |
MD5:0D06681F63F3026260AA1E15D86520A0 | SHA256:2C7B1C5C51F6952E7B8D0AC8137BC890F0EDB43F878D0E356A4BDBE1AB325127 | |||
| 2828 | wirelesskeyview.exe | C:\Users\admin\AppData\Local\Temp\n2352\ins2352.exe | executable | |
MD5:895CB5AB5FFB2F8DDE5E3CDC7A84BFFC | SHA256:44DC4038B14A188209ACABBDF44CCE73B5AABD7B4EA27D643E3231EC91F2090D | |||
| 1484 | wirelesskeyview.exe | C:\Users\admin\AppData\Local\Temp\n2421\ins2421.exe | executable | |
MD5:895CB5AB5FFB2F8DDE5E3CDC7A84BFFC | SHA256:44DC4038B14A188209ACABBDF44CCE73B5AABD7B4EA27D643E3231EC91F2090D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
8
DNS requests
2
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2728 | ins2352.exe | GET | 200 | 13.248.148.254:80 | http://api.socdn.com/installer/4fe0cf9f-1fe4-4abb-905a-57915bc06f2f/4878377/config | unknown | html | 2.21 Kb | unknown |
3028 | ins2421.exe | GET | — | 13.248.148.254:80 | http://api.socdn.com/installer/4fe0cf9f-1fe4-4abb-905a-57915bc06f2f/4878377/config | unknown | — | — | unknown |
2728 | ins2352.exe | POST | 403 | 13.248.148.254:80 | http://api.socdn.com/installer/4fe0cf9f-1fe4-4abb-905a-57915bc06f2f/4878377/event | unknown | html | 138 b | unknown |
3028 | ins2421.exe | GET | — | 13.248.148.254:80 | http://api.socdn.com/installer/4fe0cf9f-1fe4-4abb-905a-57915bc06f2f/4878377/config | unknown | — | — | unknown |
3028 | ins2421.exe | GET | — | 13.248.148.254:80 | http://api.socdn.com/installer/4fe0cf9f-1fe4-4abb-905a-57915bc06f2f/4878377/config | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2728 | ins2352.exe | 13.248.148.254:80 | api.socdn.com | AMAZON-02 | US | unknown |
3028 | ins2421.exe | 13.248.148.254:80 | api.socdn.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.socdn.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2728 | ins2352.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent (DownloadMR) |
2728 | ins2352.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent (DownloadMR) |
3028 | ins2421.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent (DownloadMR) |
3028 | ins2421.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent (DownloadMR) |
4 ETPRO signatures available at the full report