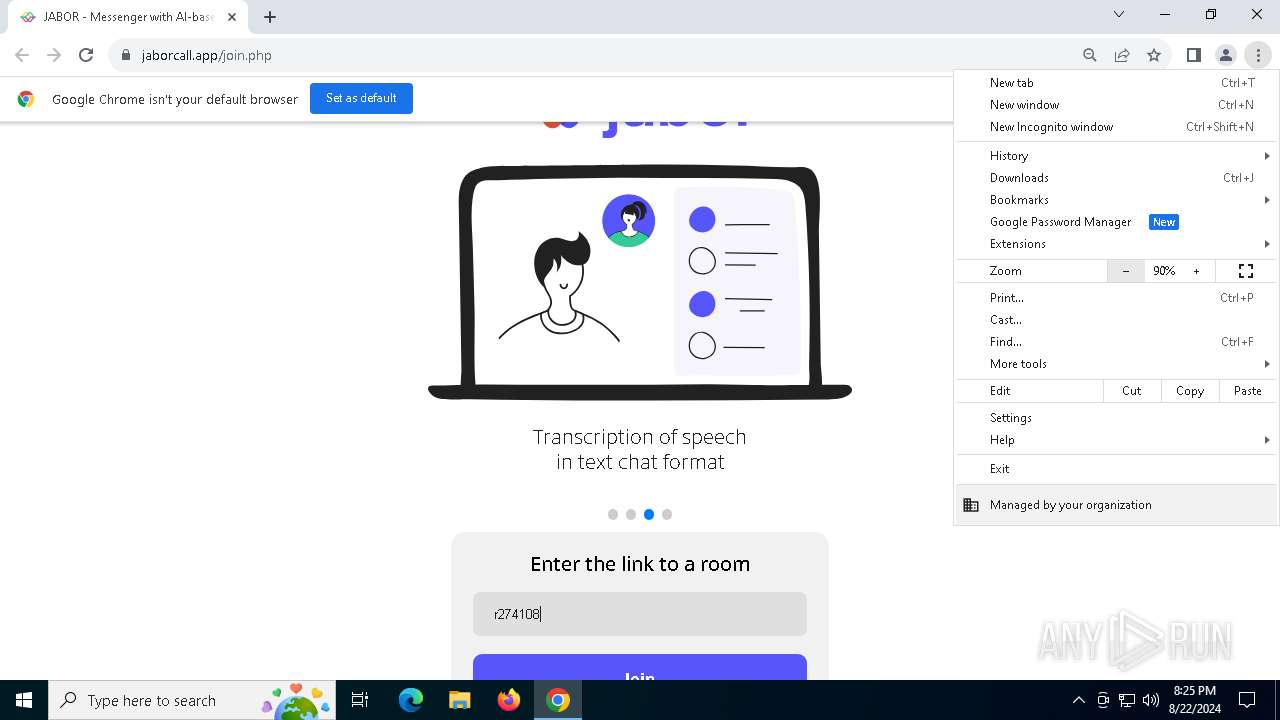
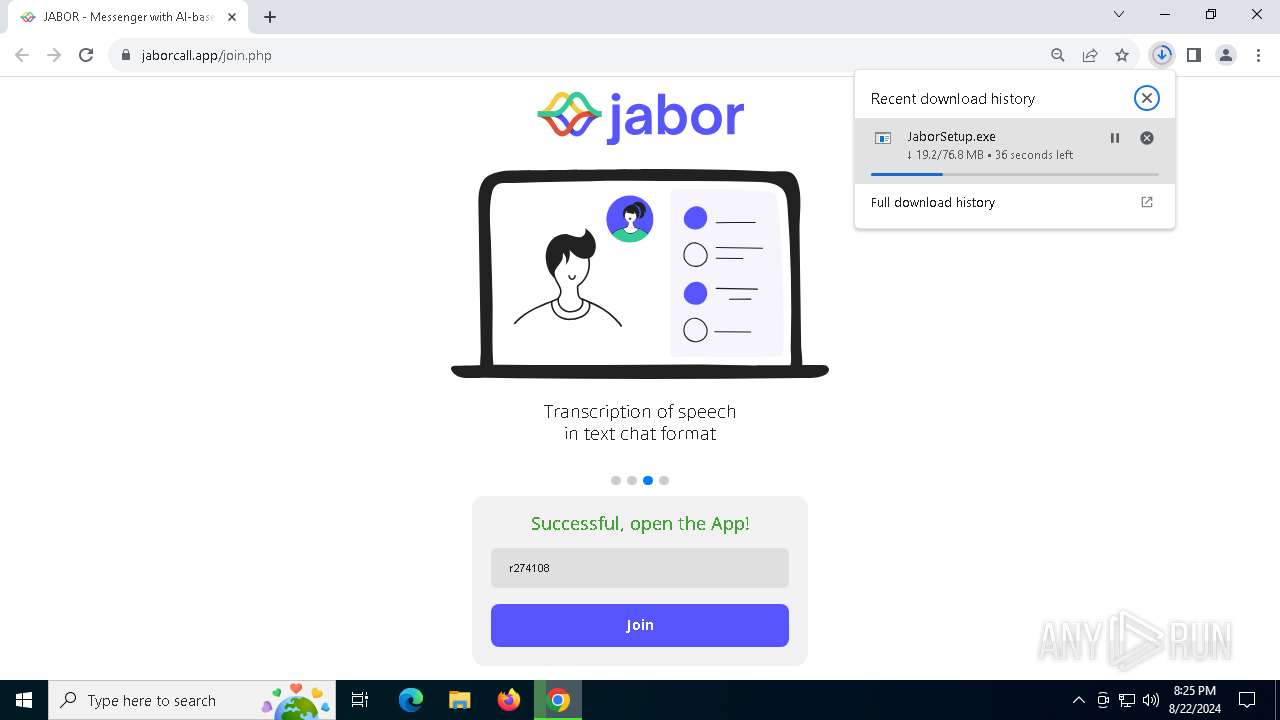
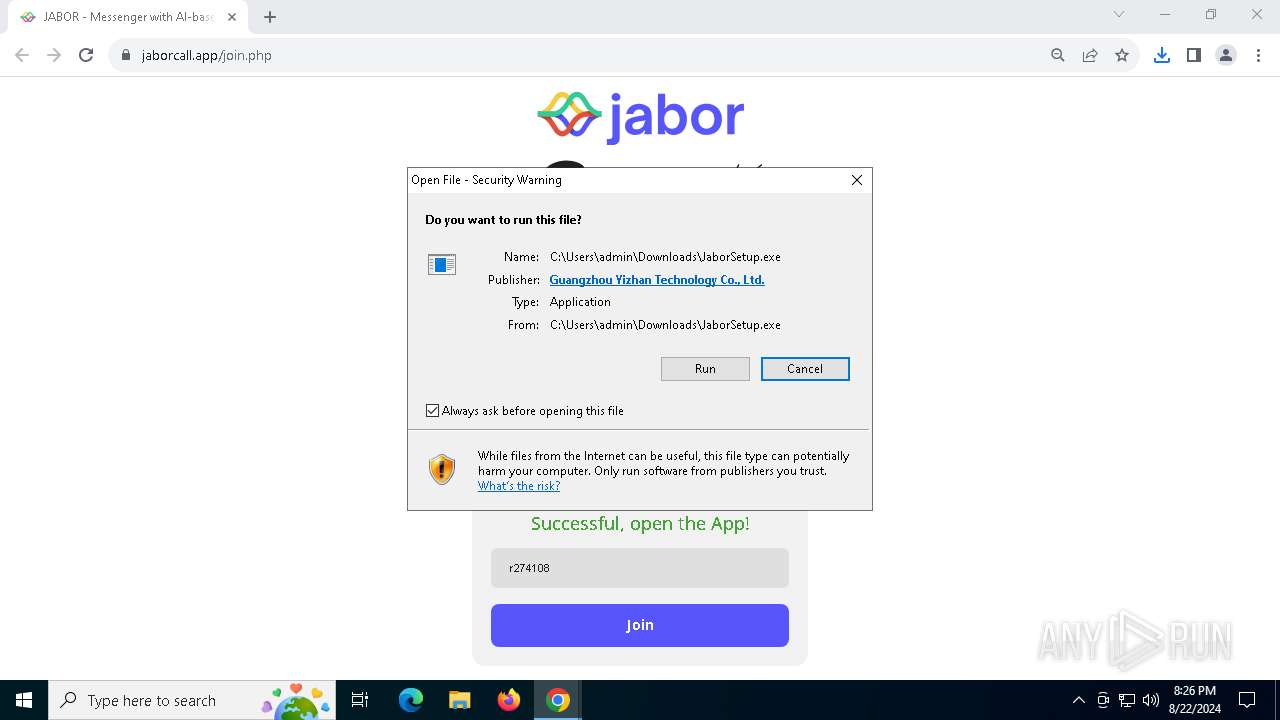
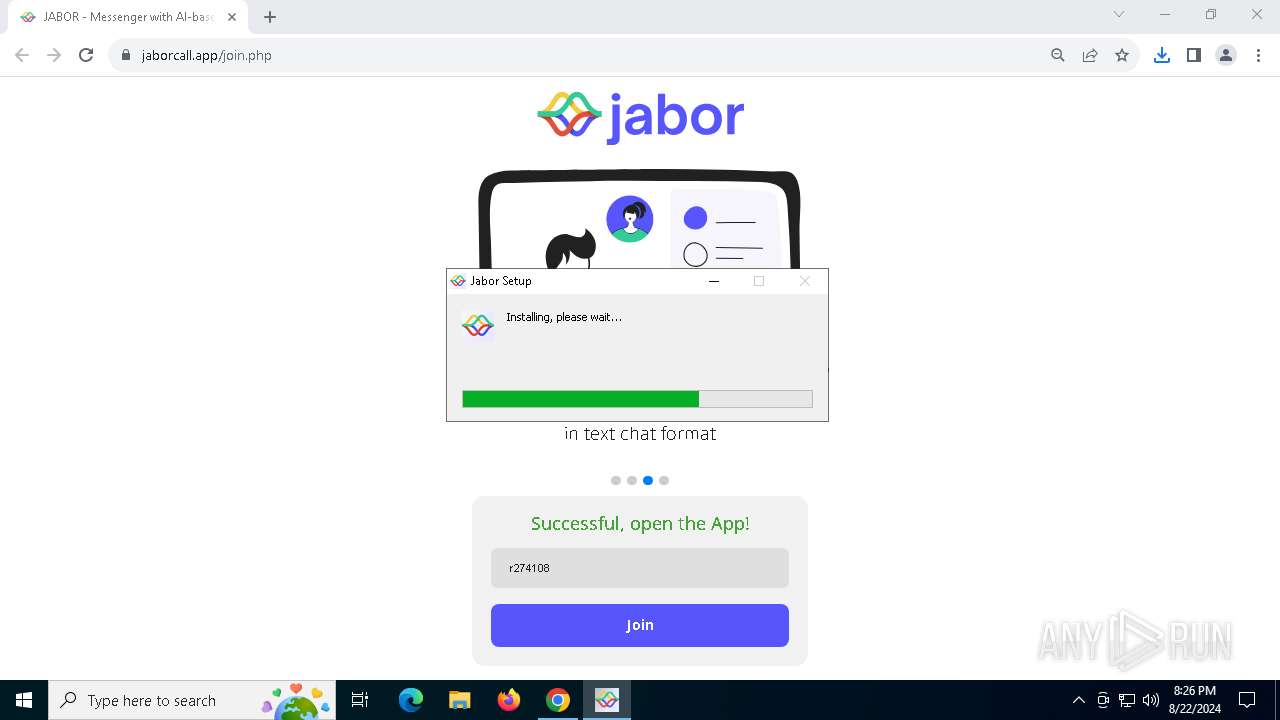
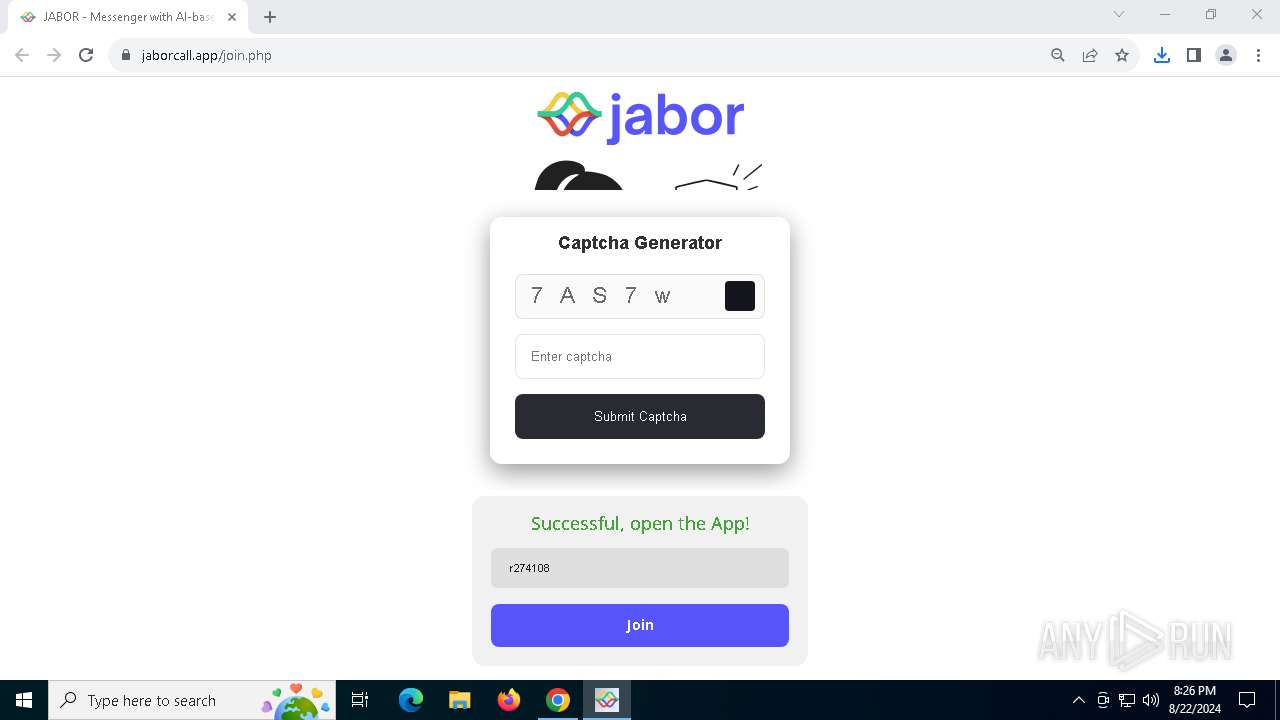
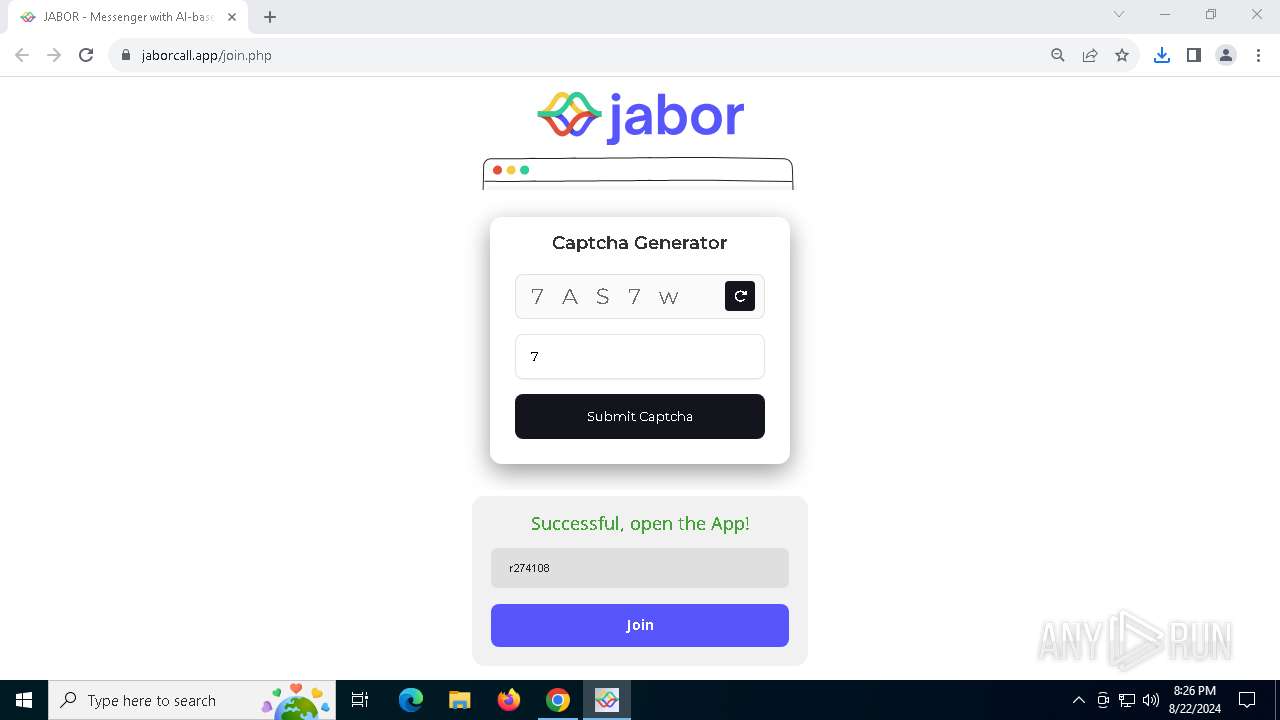
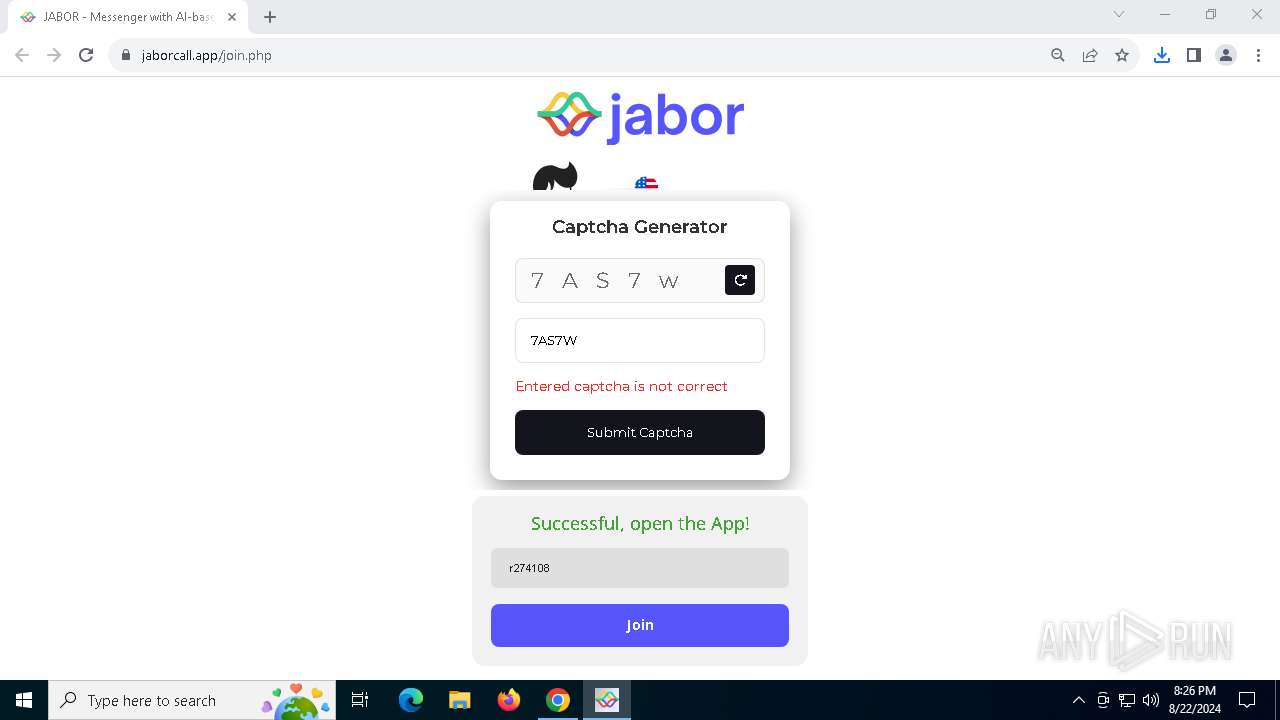
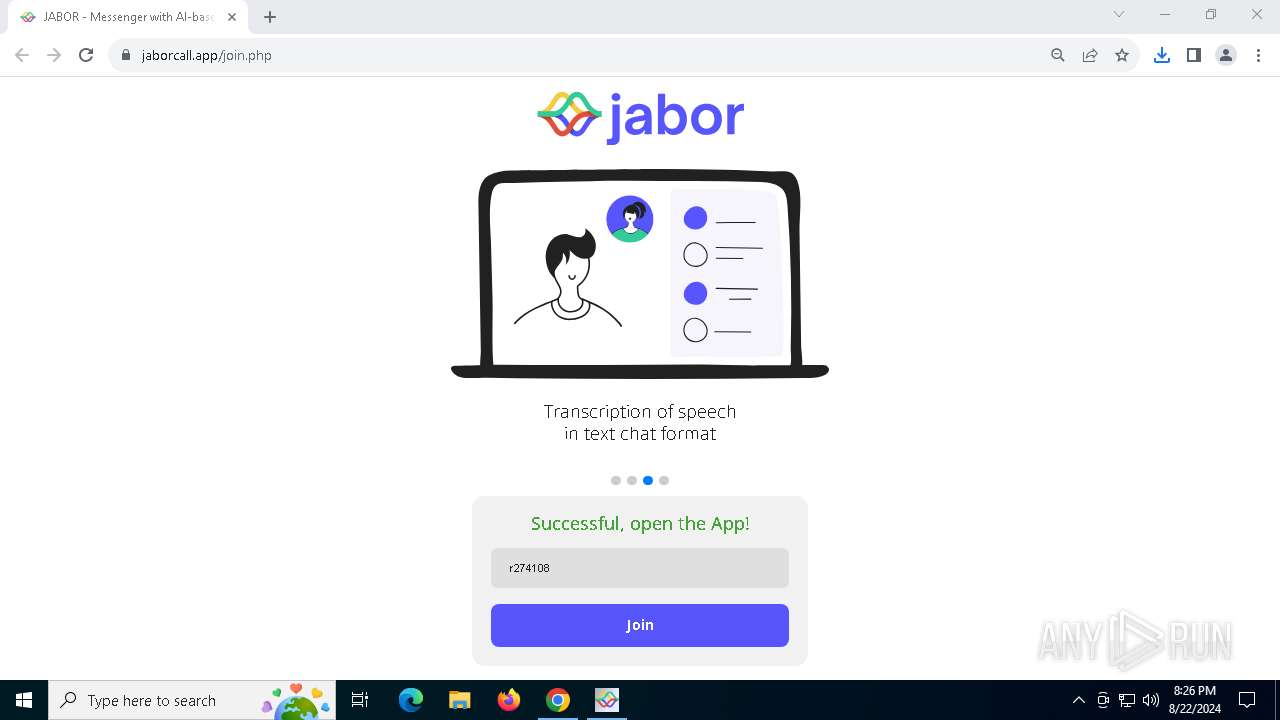
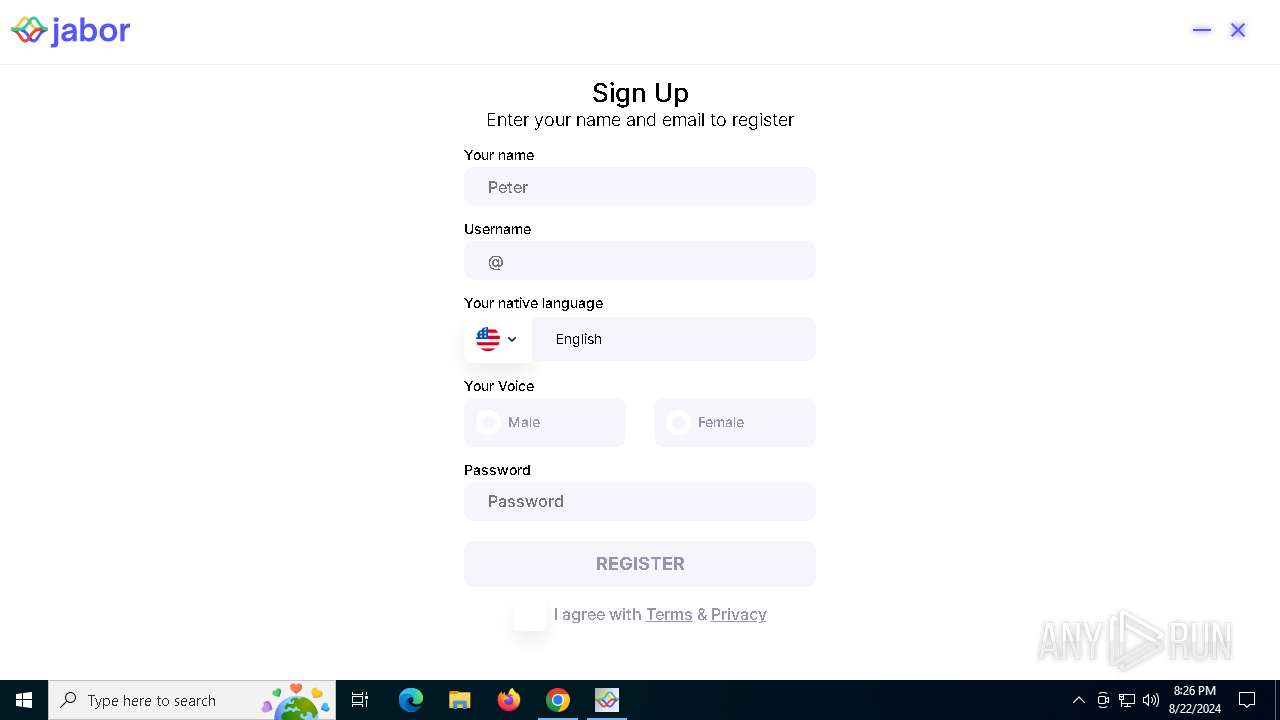
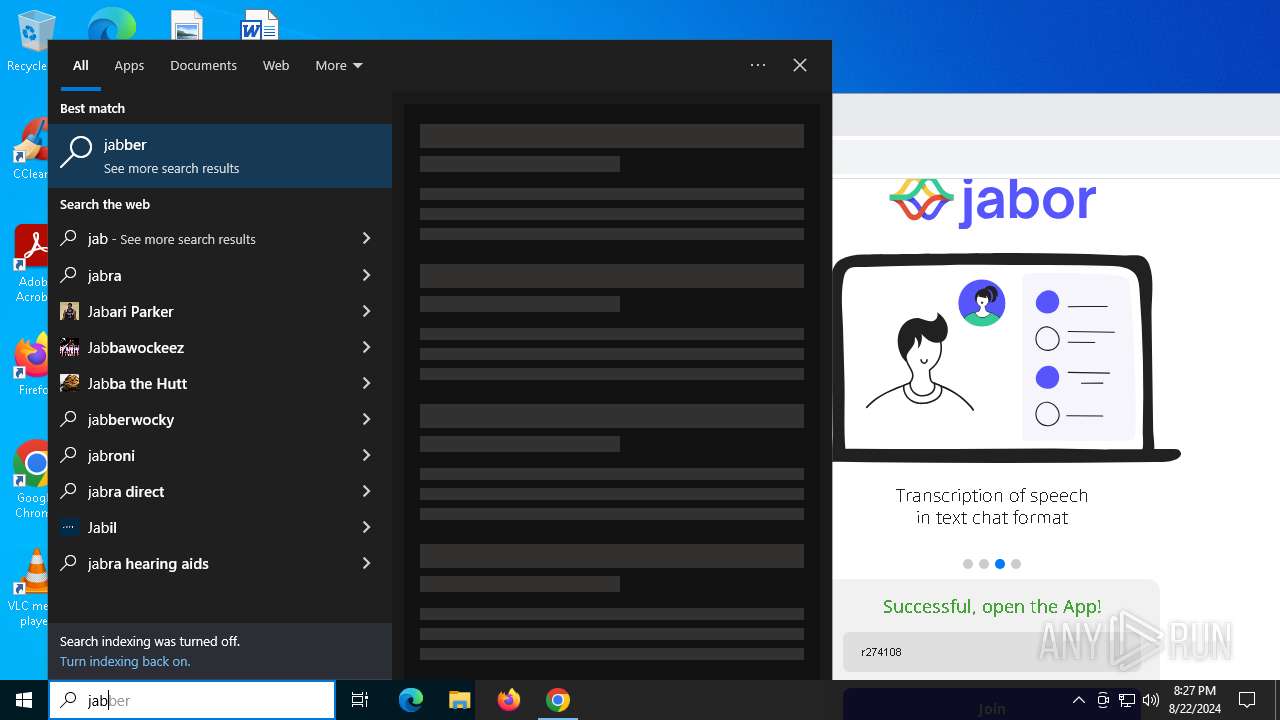
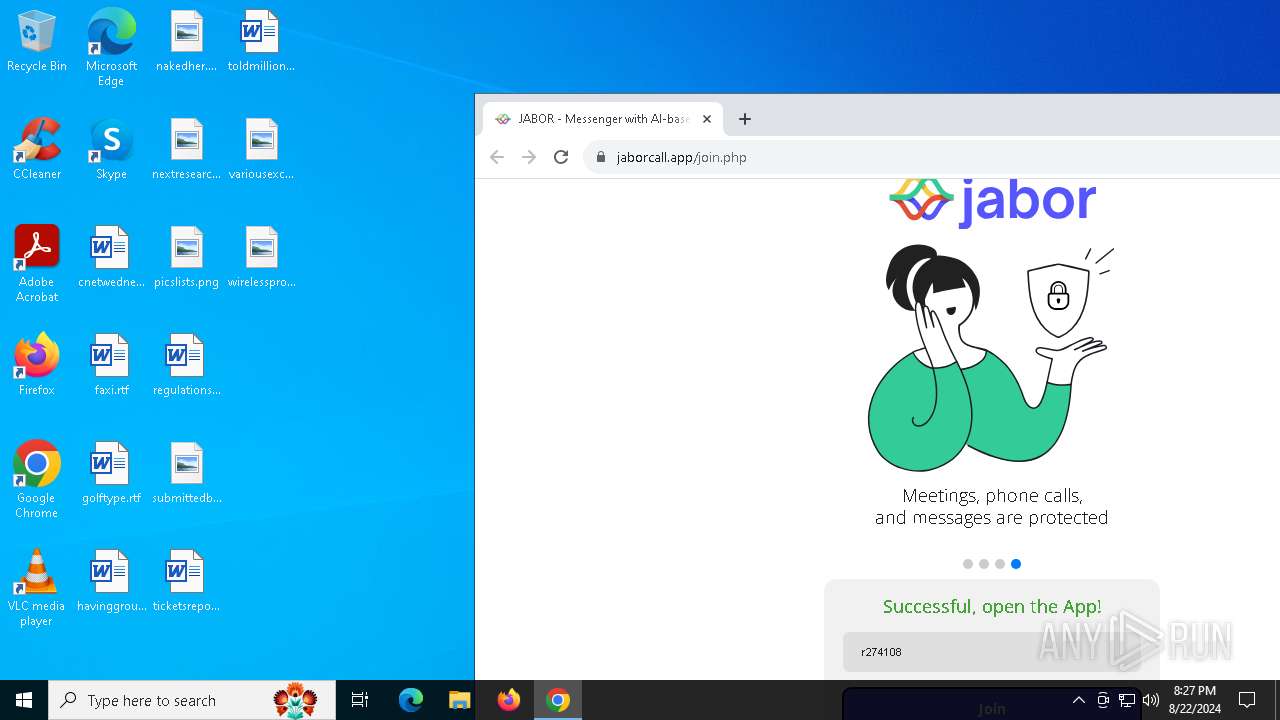
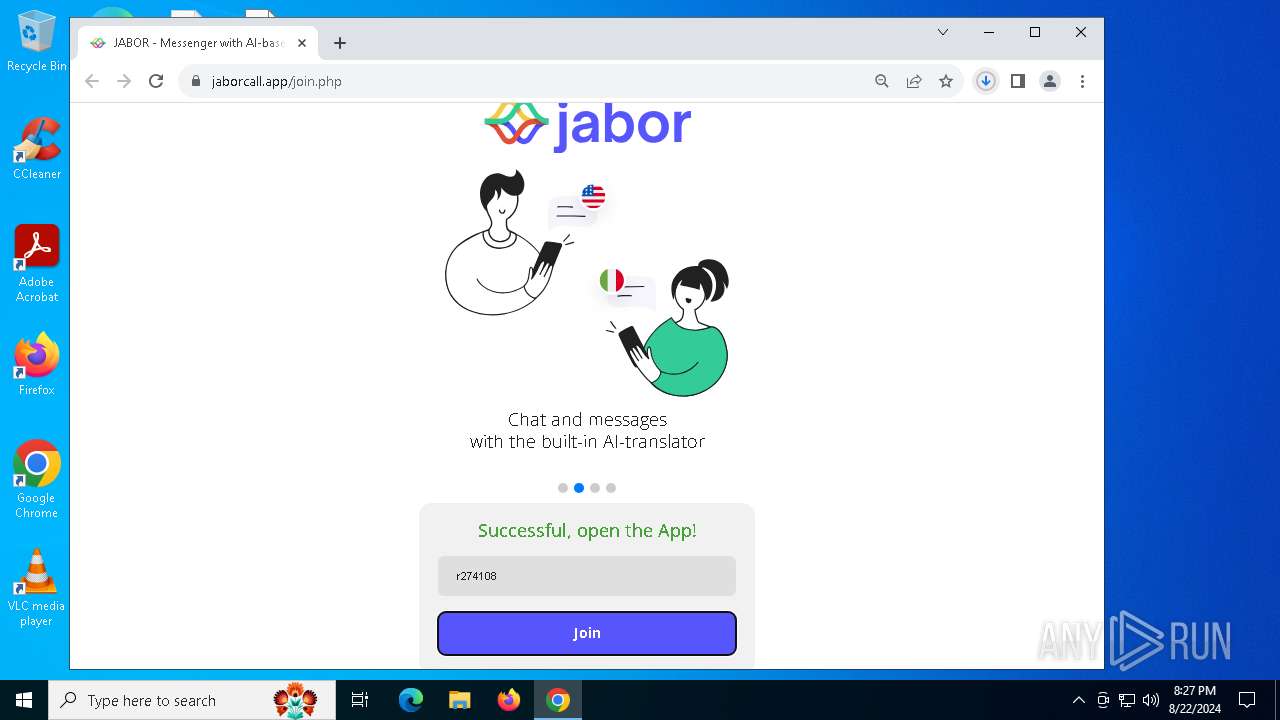
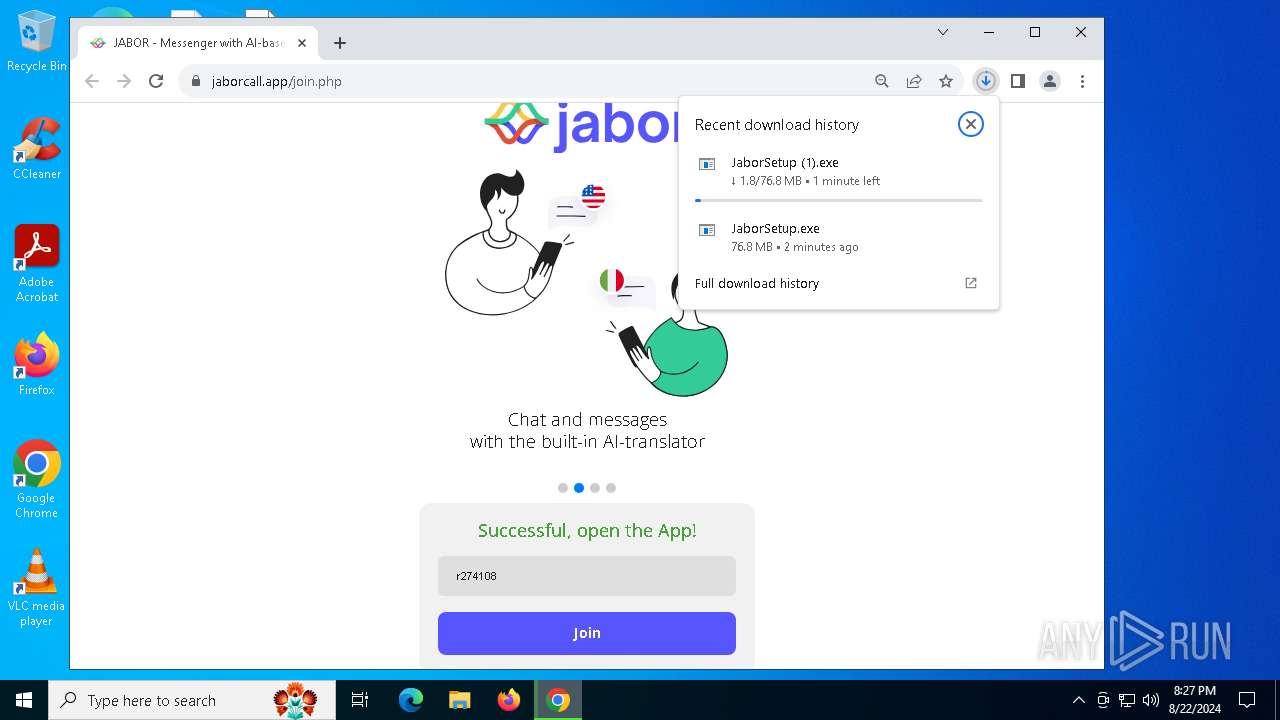
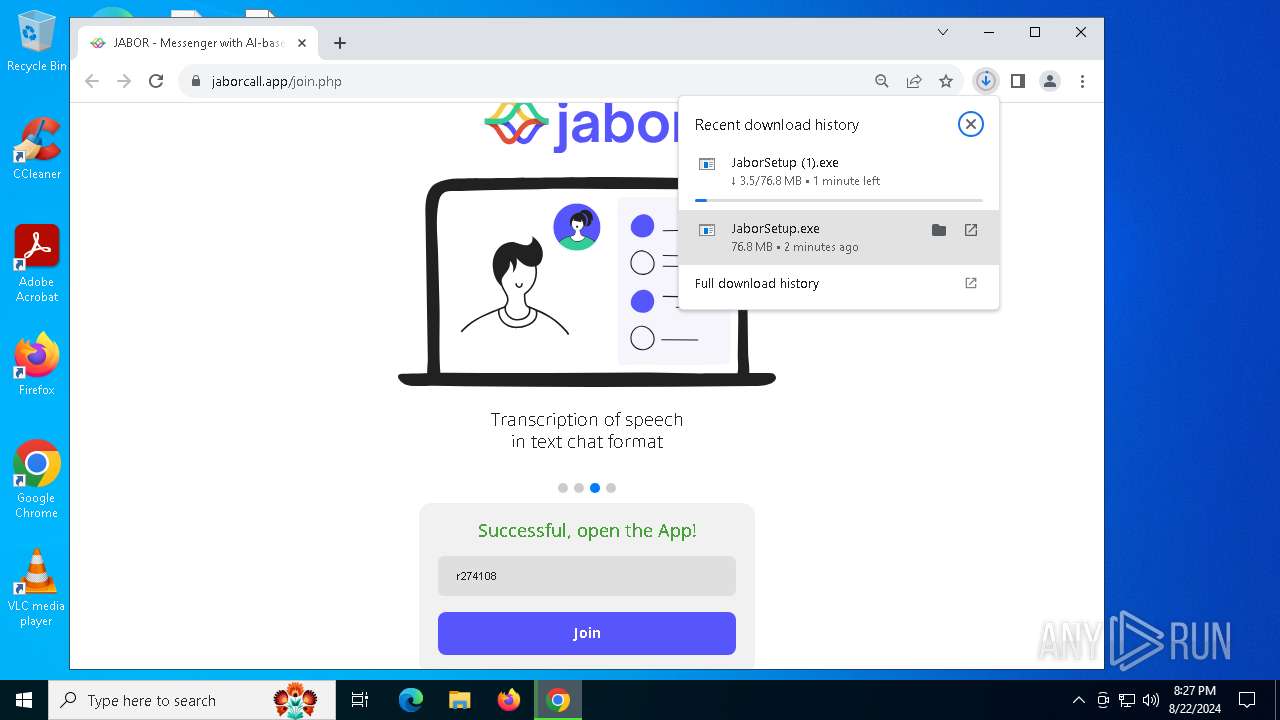
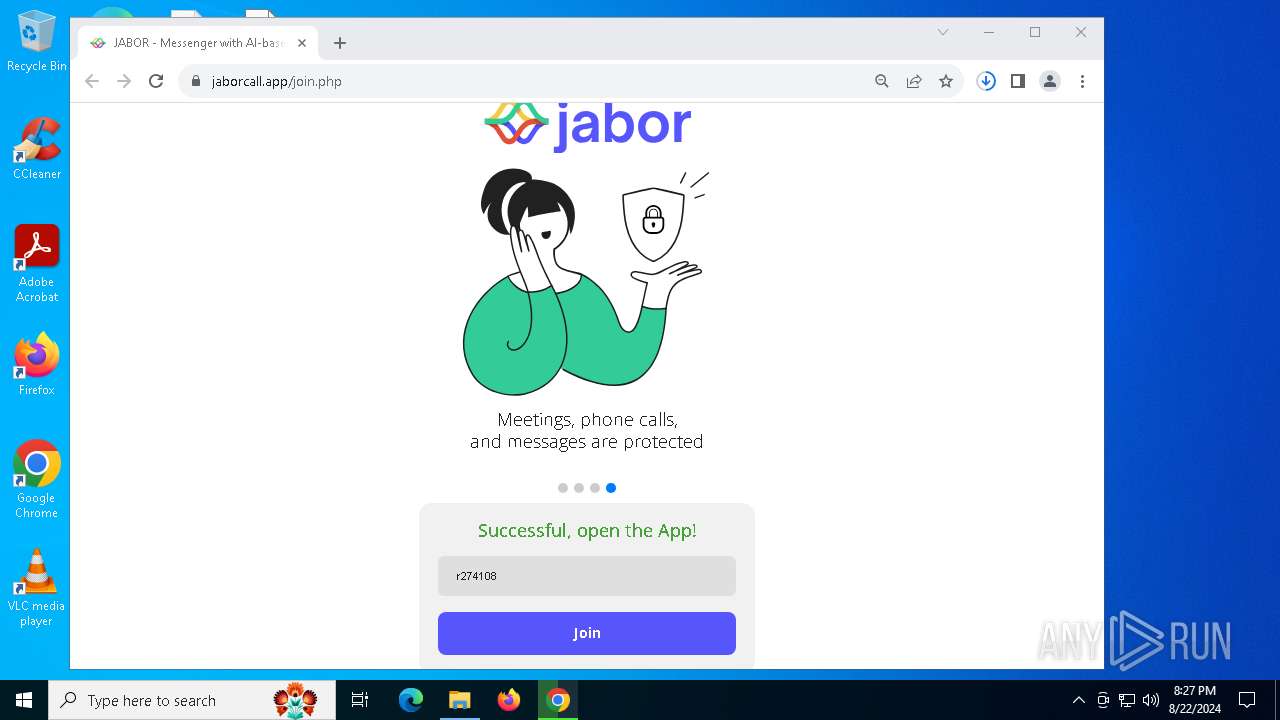
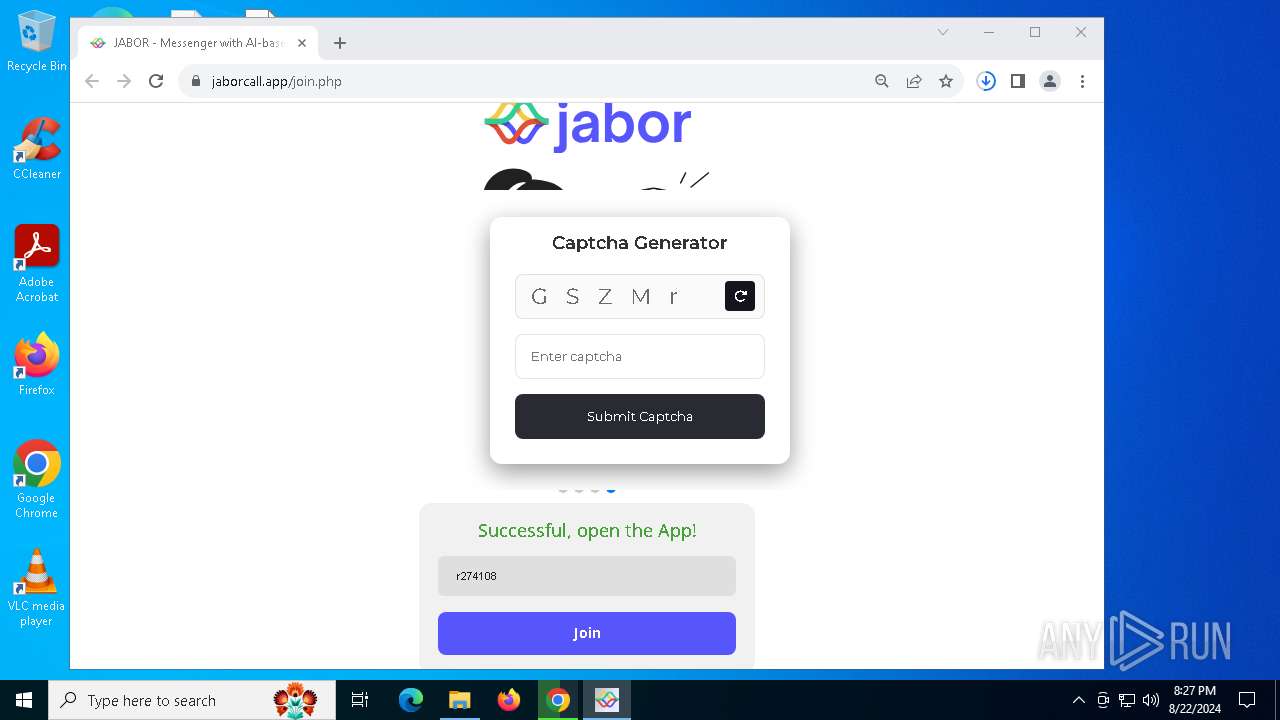
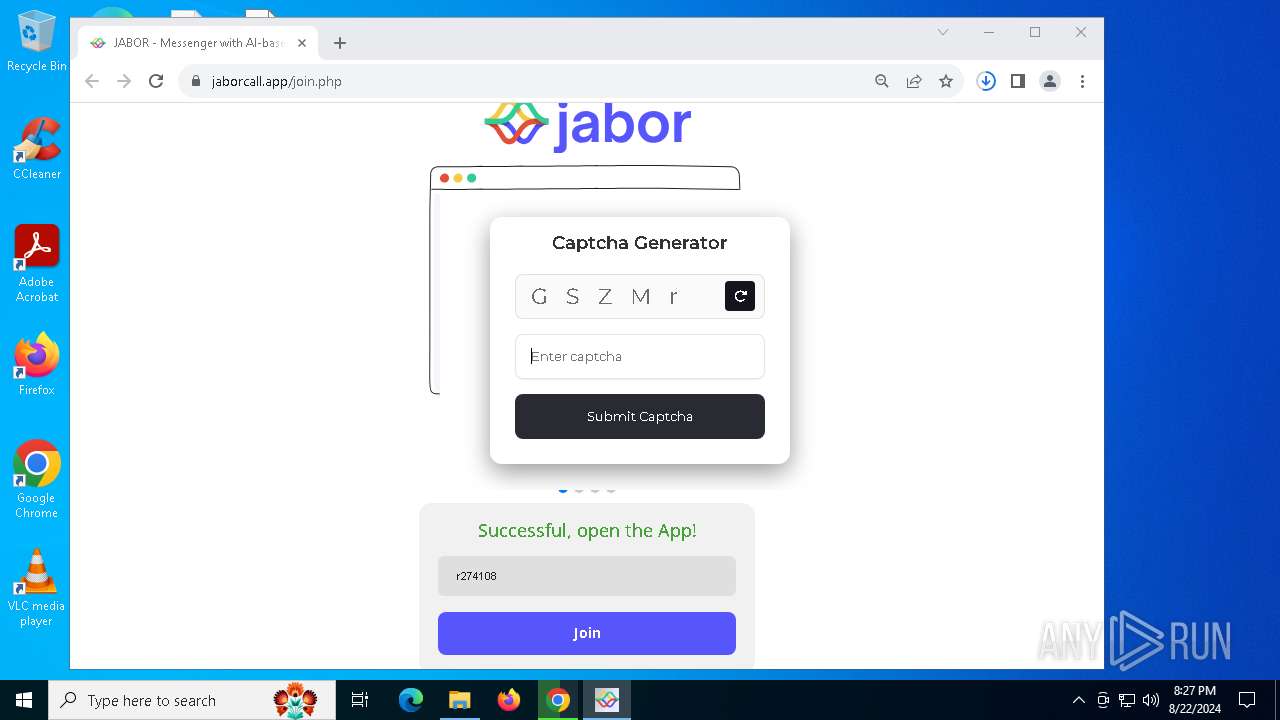
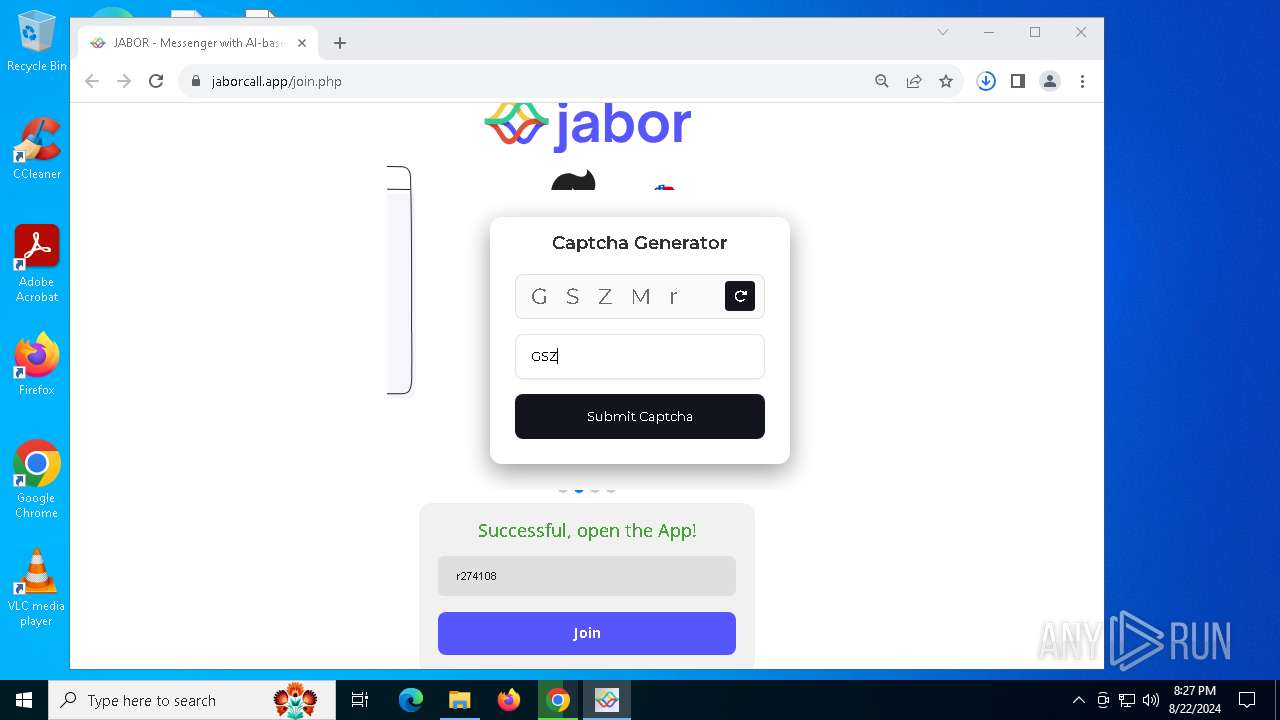
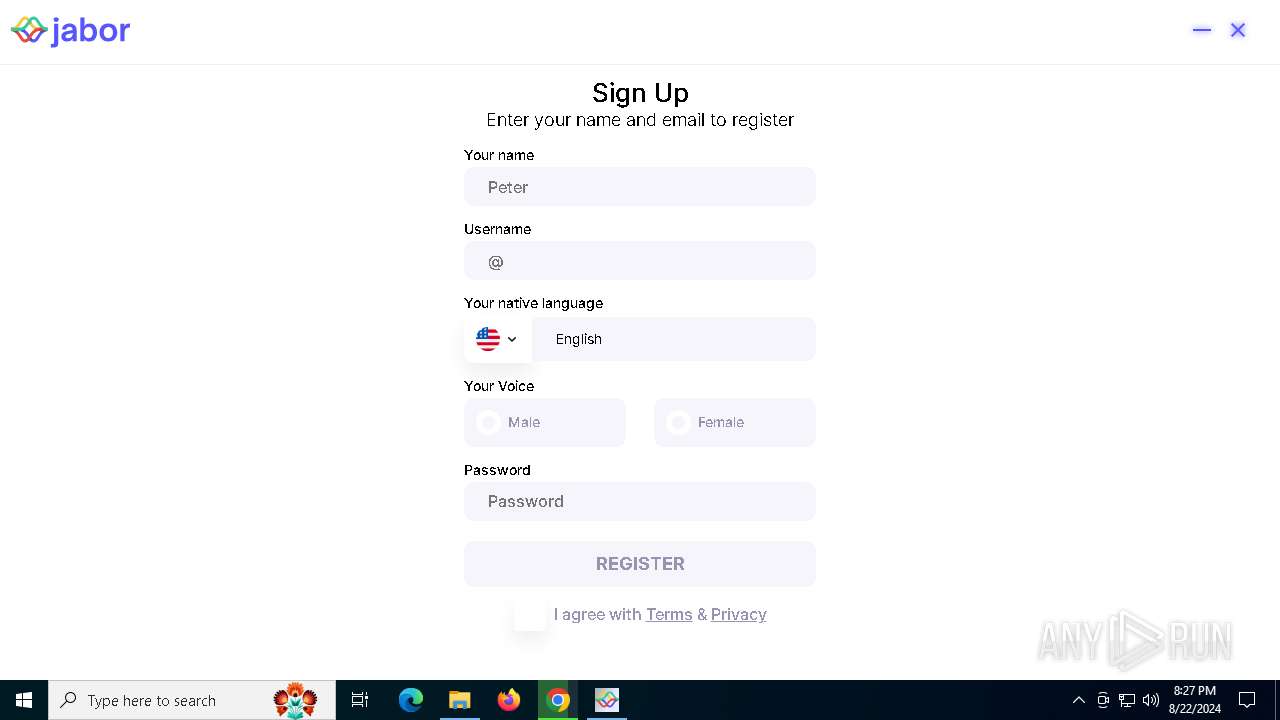
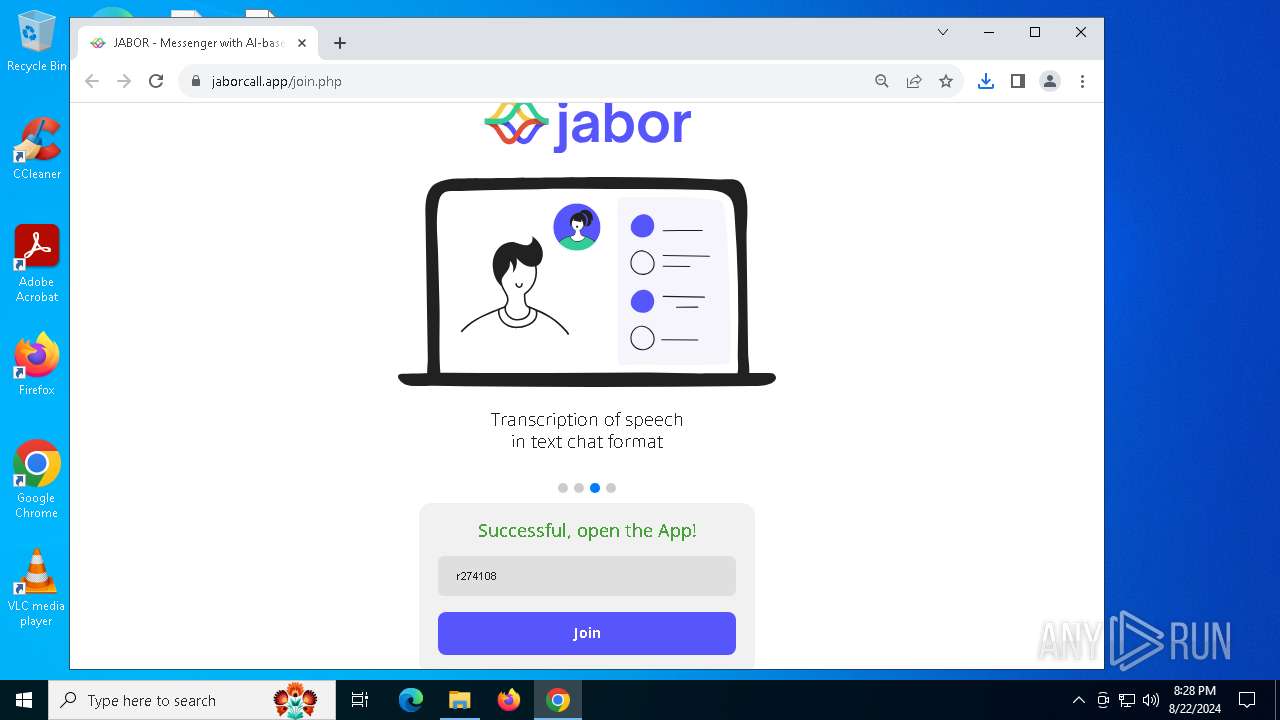
| URL: | https://jaborcall.app/join.php |
| Full analysis: | https://app.any.run/tasks/f0216f15-1eb8-4b09-b8f0-ed0af0b5026b |
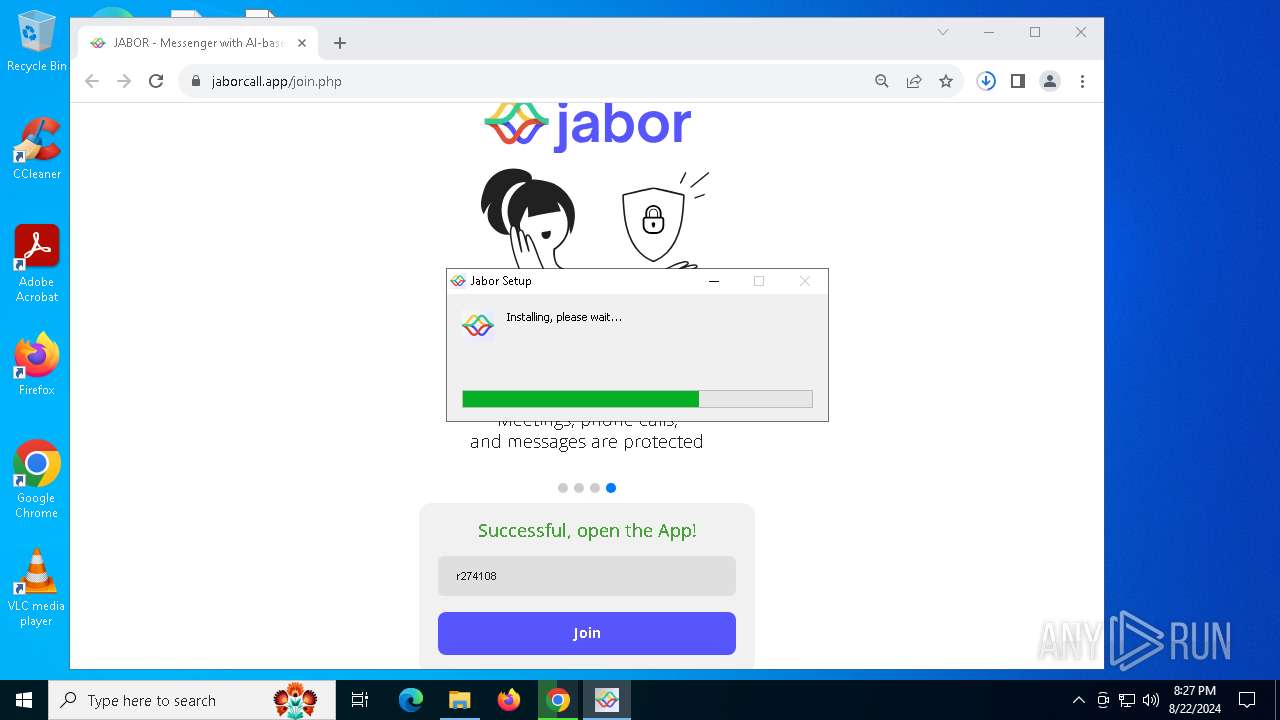
| Verdict: | Malicious activity |
| Analysis date: | August 22, 2024, 20:24:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 82117A183C1BC2D890AF8C72DD490BB8 |
| SHA1: | 0123CDFF774E496A30F7F58C220CA26E9216FA7C |
| SHA256: | E017372F60C64756D94BB52BC80AE6C8167782F14455C4D25F0E5825B1A12579 |
| SSDEEP: | 3:N80MGf/KPvV:27Gk9 |
MALICIOUS
Changes powershell execution policy (Unrestricted)
- Jabor.exe (PID: 4252)
- Jabor.exe (PID: 4060)
SUSPICIOUS
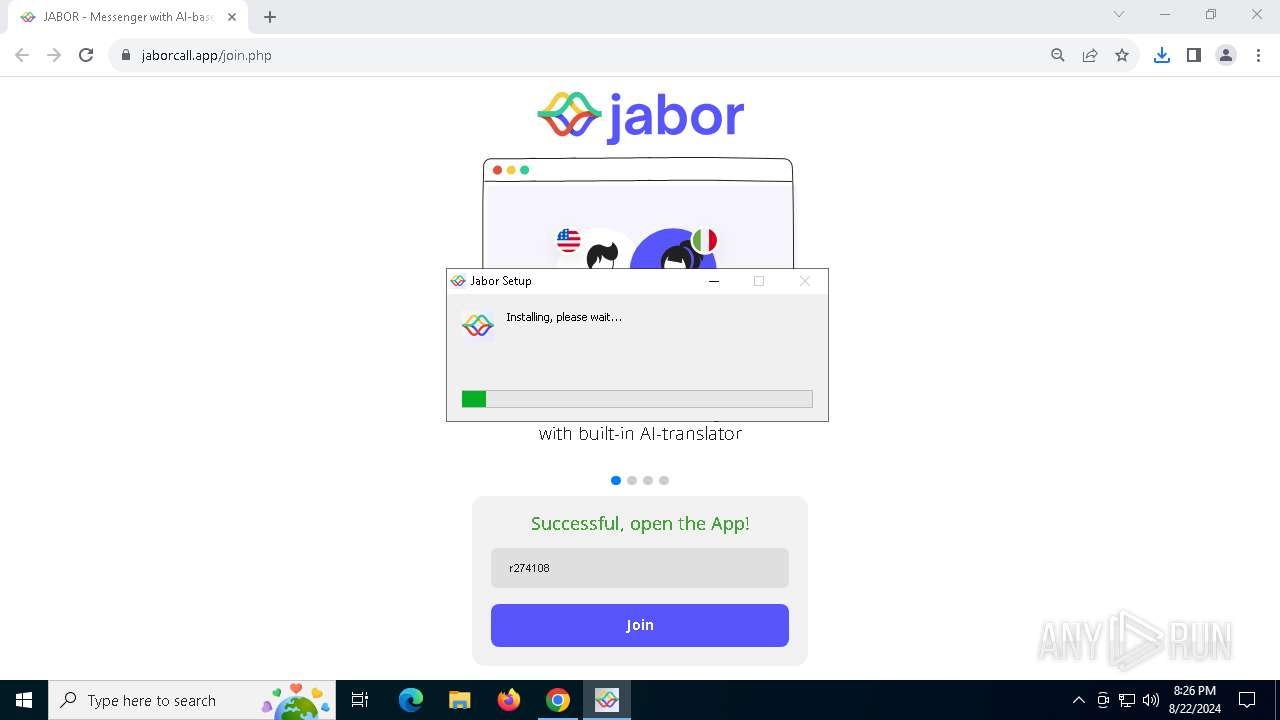
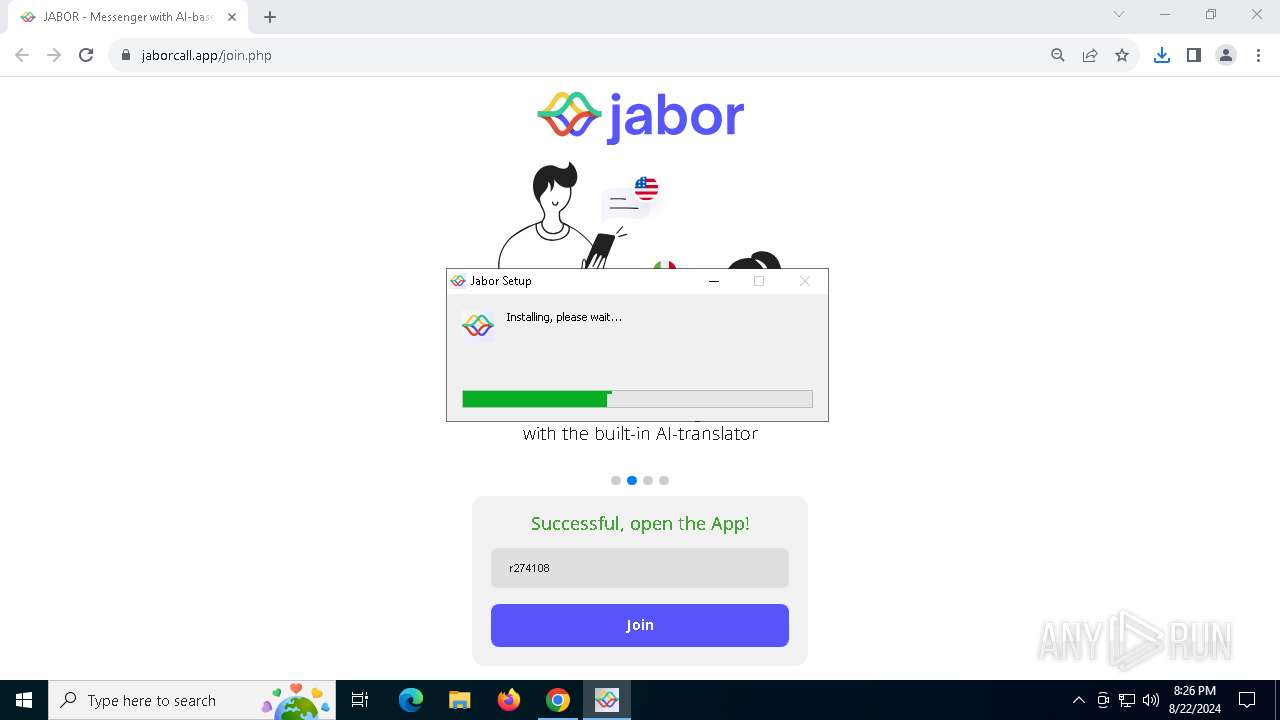
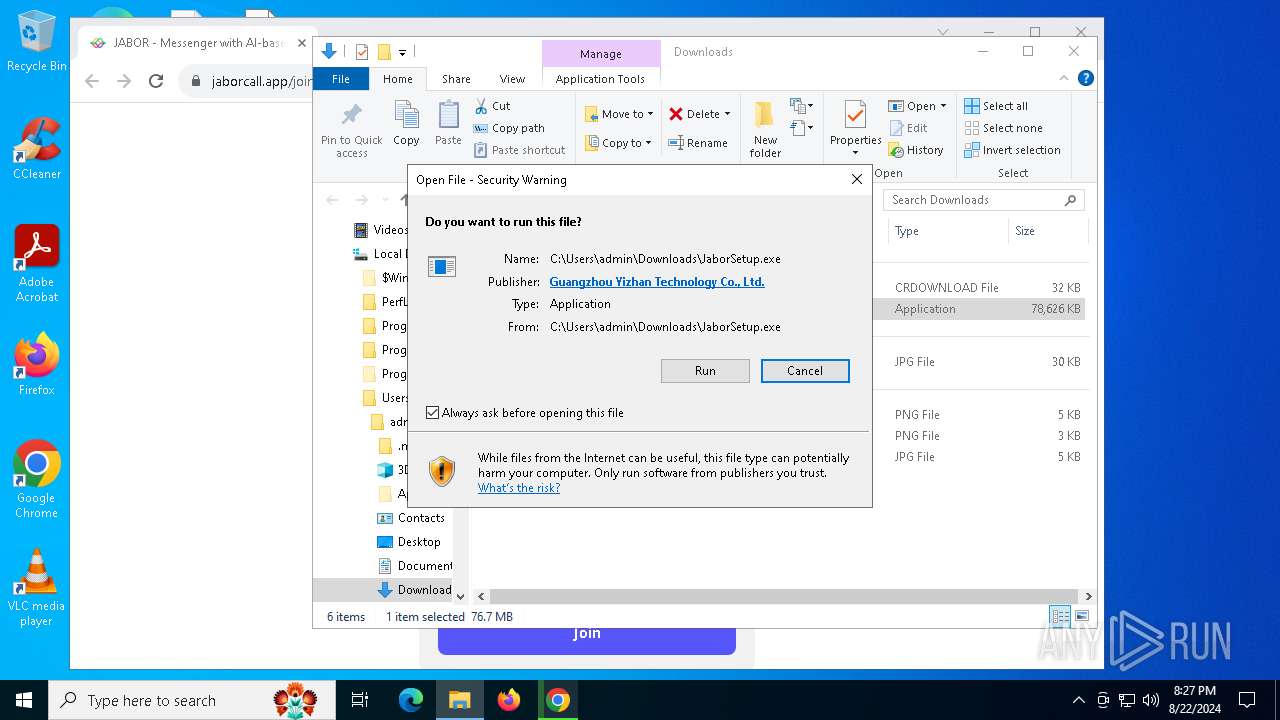
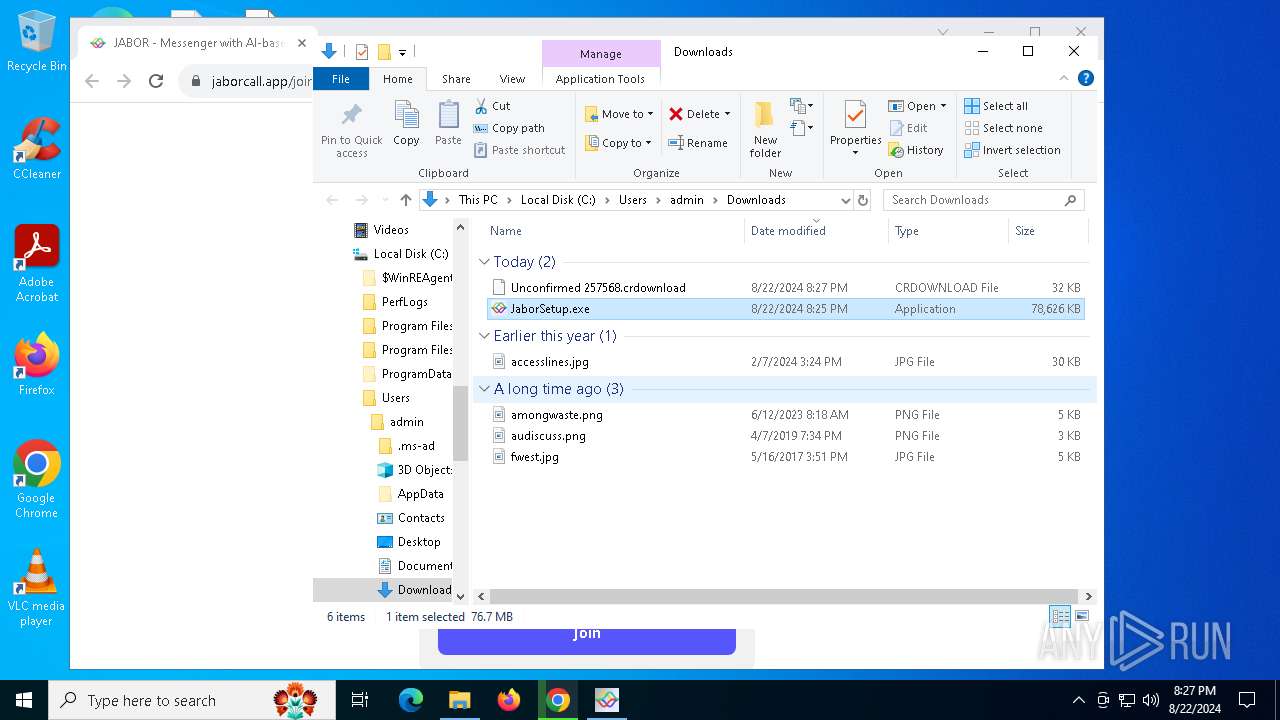
The process creates files with name similar to system file names
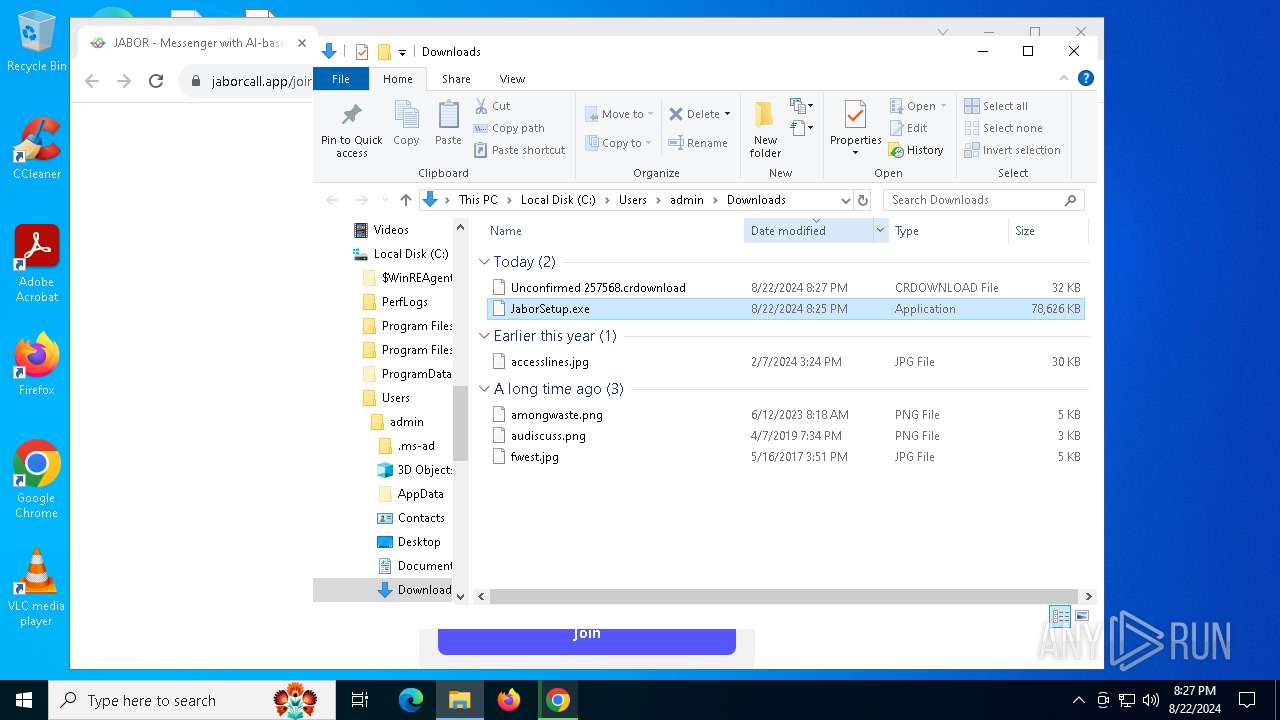
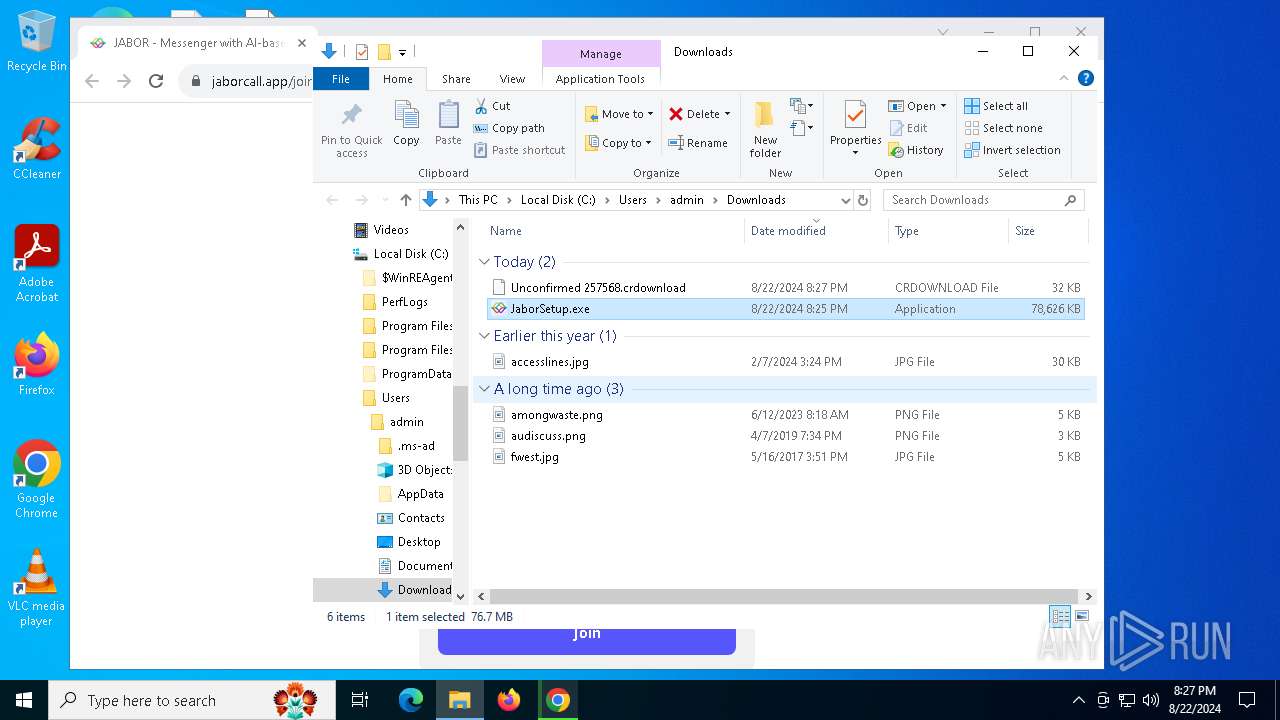
- JaborSetup.exe (PID: 6336)
- JaborSetup.exe (PID: 7528)
- old-uninstaller.exe (PID: 8120)
Malware-specific behavior (creating "System.dll" in Temp)
- JaborSetup.exe (PID: 6336)
- JaborSetup.exe (PID: 7528)
- old-uninstaller.exe (PID: 8120)
Executable content was dropped or overwritten
- JaborSetup.exe (PID: 6336)
- JaborSetup.exe (PID: 7528)
- old-uninstaller.exe (PID: 8120)
Drops 7-zip archiver for unpacking
- JaborSetup.exe (PID: 6336)
- JaborSetup.exe (PID: 7528)
Process drops legitimate windows executable
- JaborSetup.exe (PID: 6336)
- old-uninstaller.exe (PID: 8120)
- JaborSetup.exe (PID: 7528)
Reads security settings of Internet Explorer
- JaborSetup.exe (PID: 6336)
- JaborSetup.exe (PID: 7528)
Drops the executable file immediately after the start
- JaborSetup.exe (PID: 6336)
- JaborSetup.exe (PID: 7528)
- old-uninstaller.exe (PID: 8120)
Creates a software uninstall entry
- JaborSetup.exe (PID: 6336)
- JaborSetup.exe (PID: 7528)
Application launched itself
- Jabor.exe (PID: 1964)
- Jabor.exe (PID: 7540)
Starts CMD.EXE for commands execution
- Jabor.exe (PID: 4292)
- Jabor.exe (PID: 4252)
- Jabor.exe (PID: 7936)
- Jabor.exe (PID: 4060)
Starts application with an unusual extension
- cmd.exe (PID: 1636)
- cmd.exe (PID: 3116)
- cmd.exe (PID: 740)
- cmd.exe (PID: 6332)
Starts POWERSHELL.EXE for commands execution
- Jabor.exe (PID: 4252)
- Jabor.exe (PID: 4060)
The process bypasses the loading of PowerShell profile settings
- Jabor.exe (PID: 4252)
- Jabor.exe (PID: 4060)
The process hides Powershell's copyright startup banner
- Jabor.exe (PID: 4252)
- Jabor.exe (PID: 4060)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 5920)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4668)
- cmd.exe (PID: 1108)
Searches for installed software
- JaborSetup.exe (PID: 7528)
INFO
Application launched itself
- chrome.exe (PID: 6532)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6532)
Executable content was dropped or overwritten
- chrome.exe (PID: 368)
- chrome.exe (PID: 6532)
Checks supported languages
- JaborSetup.exe (PID: 6336)
- Jabor.exe (PID: 1964)
- Jabor.exe (PID: 5900)
- Jabor.exe (PID: 4292)
- chcp.com (PID: 5096)
- Jabor.exe (PID: 4252)
- chcp.com (PID: 1280)
- JaborSetup.exe (PID: 7528)
- old-uninstaller.exe (PID: 8120)
- Jabor.exe (PID: 7540)
- Jabor.exe (PID: 7448)
- Jabor.exe (PID: 5692)
- Jabor.exe (PID: 7936)
- chcp.com (PID: 6396)
- Jabor.exe (PID: 4060)
- chcp.com (PID: 5292)
- Jabor.exe (PID: 7824)
The process uses the downloaded file
- chrome.exe (PID: 6456)
- chrome.exe (PID: 6532)
- JaborSetup.exe (PID: 6336)
- JaborSetup.exe (PID: 7528)
- chrome.exe (PID: 7112)
Create files in a temporary directory
- JaborSetup.exe (PID: 6336)
- Jabor.exe (PID: 1964)
- JaborSetup.exe (PID: 7528)
- old-uninstaller.exe (PID: 8120)
- Jabor.exe (PID: 7540)
Reads the computer name
- JaborSetup.exe (PID: 6336)
- Jabor.exe (PID: 1964)
- Jabor.exe (PID: 5692)
- Jabor.exe (PID: 5900)
- Jabor.exe (PID: 4252)
- JaborSetup.exe (PID: 7528)
- Jabor.exe (PID: 7540)
- Jabor.exe (PID: 7448)
- Jabor.exe (PID: 7824)
- Jabor.exe (PID: 4060)
Creates files or folders in the user directory
- JaborSetup.exe (PID: 6336)
- Jabor.exe (PID: 1964)
- Jabor.exe (PID: 5900)
- JaborSetup.exe (PID: 7528)
- Jabor.exe (PID: 7540)
- Jabor.exe (PID: 7824)
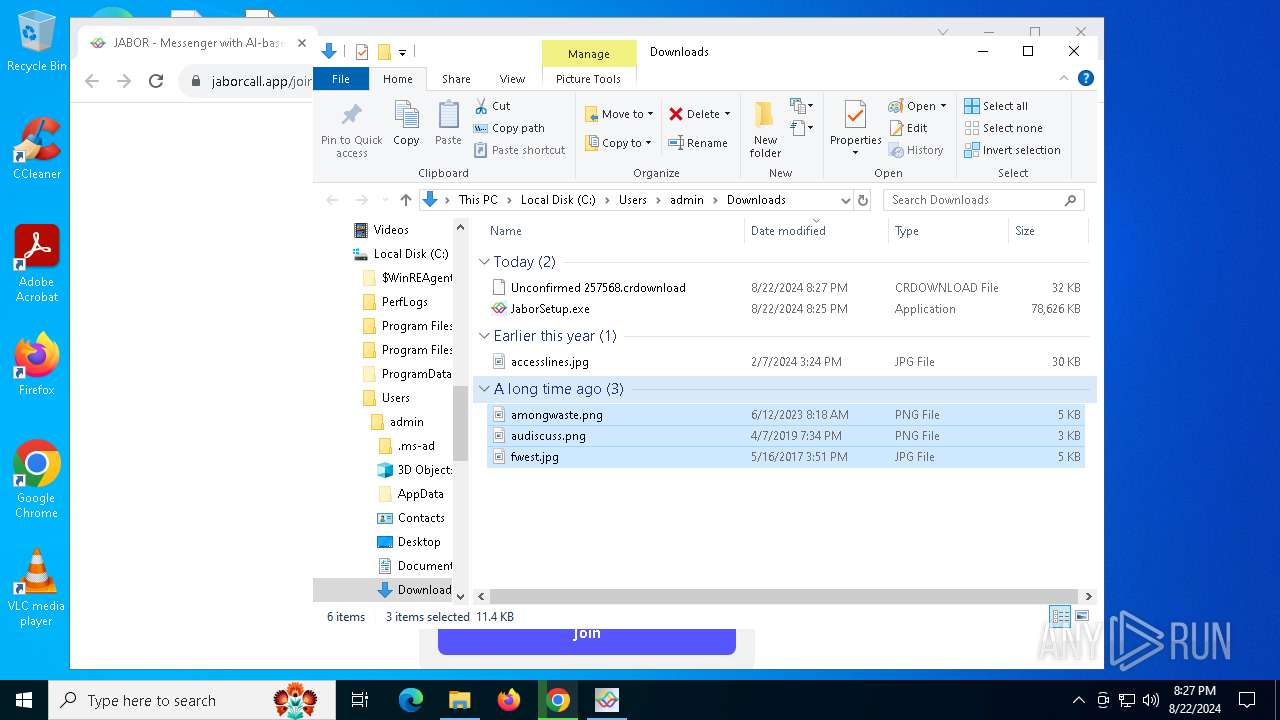
Manual execution by a user
- Jabor.exe (PID: 1964)
- JaborSetup.exe (PID: 7528)
- Jabor.exe (PID: 7540)
Checks proxy server information
- Jabor.exe (PID: 1964)
- Jabor.exe (PID: 7540)
Reads the machine GUID from the registry
- Jabor.exe (PID: 1964)
- Jabor.exe (PID: 7540)
Process checks computer location settings
- Jabor.exe (PID: 1964)
- Jabor.exe (PID: 4292)
- Jabor.exe (PID: 4252)
- Jabor.exe (PID: 7540)
- Jabor.exe (PID: 7936)
- Jabor.exe (PID: 4060)
Reads Environment values
- Jabor.exe (PID: 4292)
- Jabor.exe (PID: 4252)
- Jabor.exe (PID: 7936)
- Jabor.exe (PID: 4060)
Reads product name
- Jabor.exe (PID: 4292)
- Jabor.exe (PID: 4252)
- Jabor.exe (PID: 7936)
- Jabor.exe (PID: 4060)
Changes the display of characters in the console
- chcp.com (PID: 5096)
- chcp.com (PID: 1280)
- chcp.com (PID: 6396)
- chcp.com (PID: 5292)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3700)
- powershell.exe (PID: 4760)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 5136)
- powershell.exe (PID: 3104)
- powershell.exe (PID: 6416)
- powershell.exe (PID: 7352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
287
Monitored processes
143
Malicious processes
6
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | C:\WINDOWS\system32\cmd.exe /d /s /c "echo %COMPUTERNAME%.%USERDNSDOMAIN%" | C:\Windows\System32\cmd.exe | — | Jabor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5416 --field-trial-handle=1892,i,8281068637786403972,7380218695664484483,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 368 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 400 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 448 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 740 | C:\WINDOWS\system32\cmd.exe /d /s /c "chcp" | C:\Windows\System32\cmd.exe | — | Jabor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 788 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1108 | C:\WINDOWS\system32\cmd.exe /d /s /c "findstr /C:"Detected boot environment" "%windir%\Panther\setupact.log"" | C:\Windows\System32\cmd.exe | — | Jabor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | chcp | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
253 877
Read events
253 368
Write events
409
Delete events
100
Modification events
| (PID) Process: | (6532) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6532) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6532) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6532) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6532) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6532) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6532) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6532) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6532) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6532) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
59
Suspicious files
498
Text files
139
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF11e721.TMP | — | |
MD5:— | SHA256:— | |||
| 6532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF11e730.TMP | — | |
MD5:— | SHA256:— | |||
| 6532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:FCE53E052E5CF7C20819320F374DEA88 | SHA256:CD95DE277E746E92CC2C53D9FC92A8F6F0C3EDFB7F1AD9A4E9259F927065BC89 | |||
| 6532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:FC81892AC822DCBB09441D3B58B47125 | SHA256:FB077C966296D02D50CCBF7F761D2A3311A206A784A7496F331C2B0D6AD205C8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
77
DNS requests
66
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6216 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
6436 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4604 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6216 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
6216 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
6216 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
6216 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
6216 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
6216 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
6216 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1360 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1616 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6784 | chrome.exe | 188.114.97.3:443 | jaborcall.app | CLOUDFLARENET | NL | unknown |
6532 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6784 | chrome.exe | 142.251.31.84:443 | accounts.google.com | GOOGLE | US | unknown |
6784 | chrome.exe | 142.250.186.42:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
876 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
jaborcall.app |
| unknown |
accounts.google.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
www.google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5900 | Jabor.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5900 | Jabor.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |