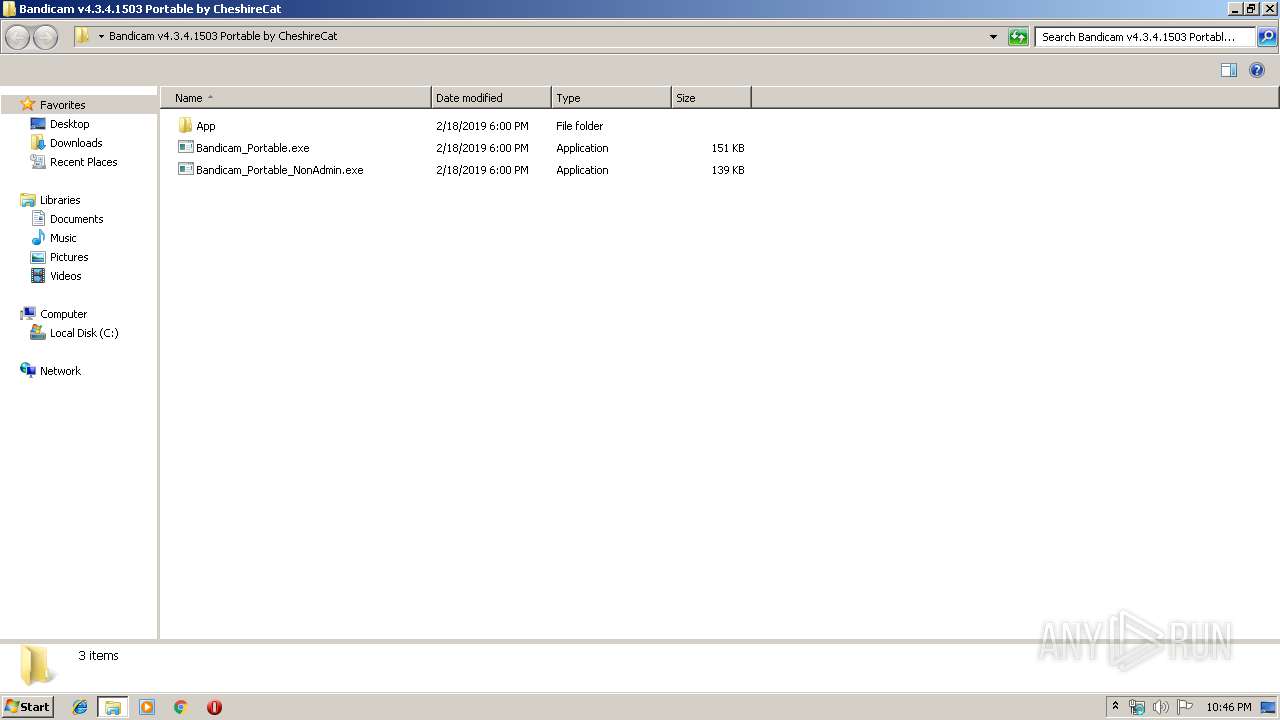
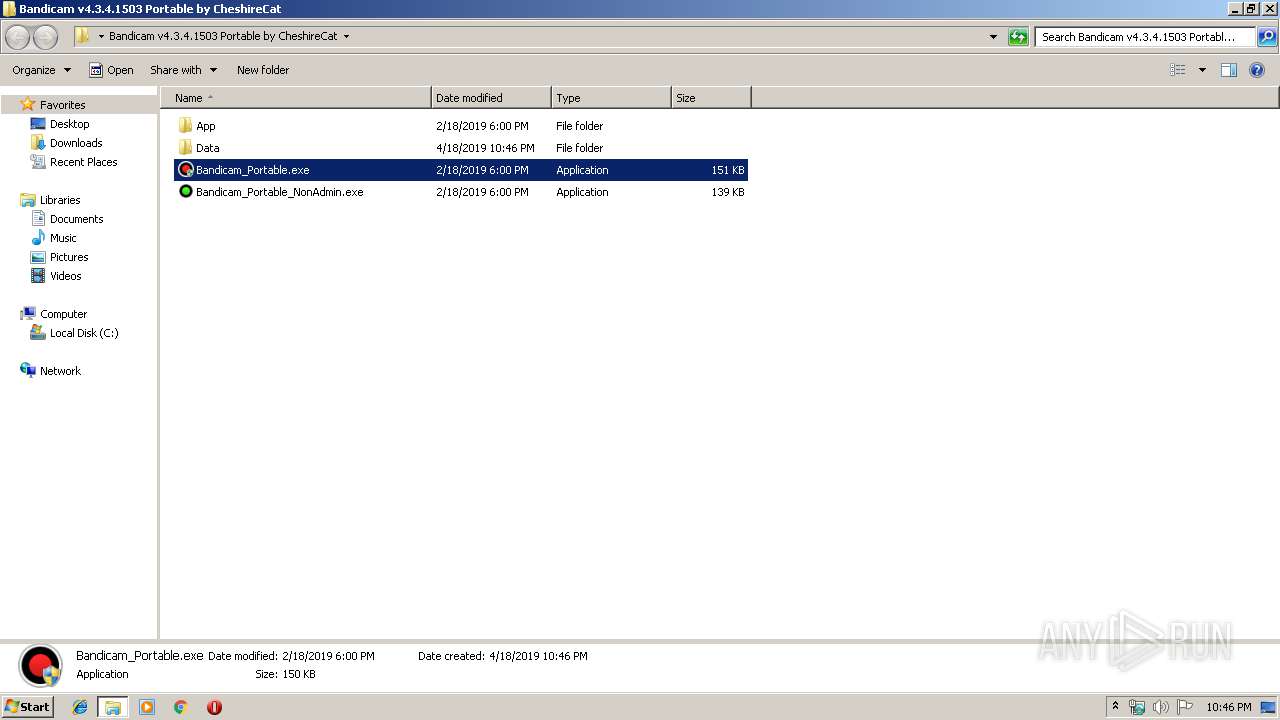
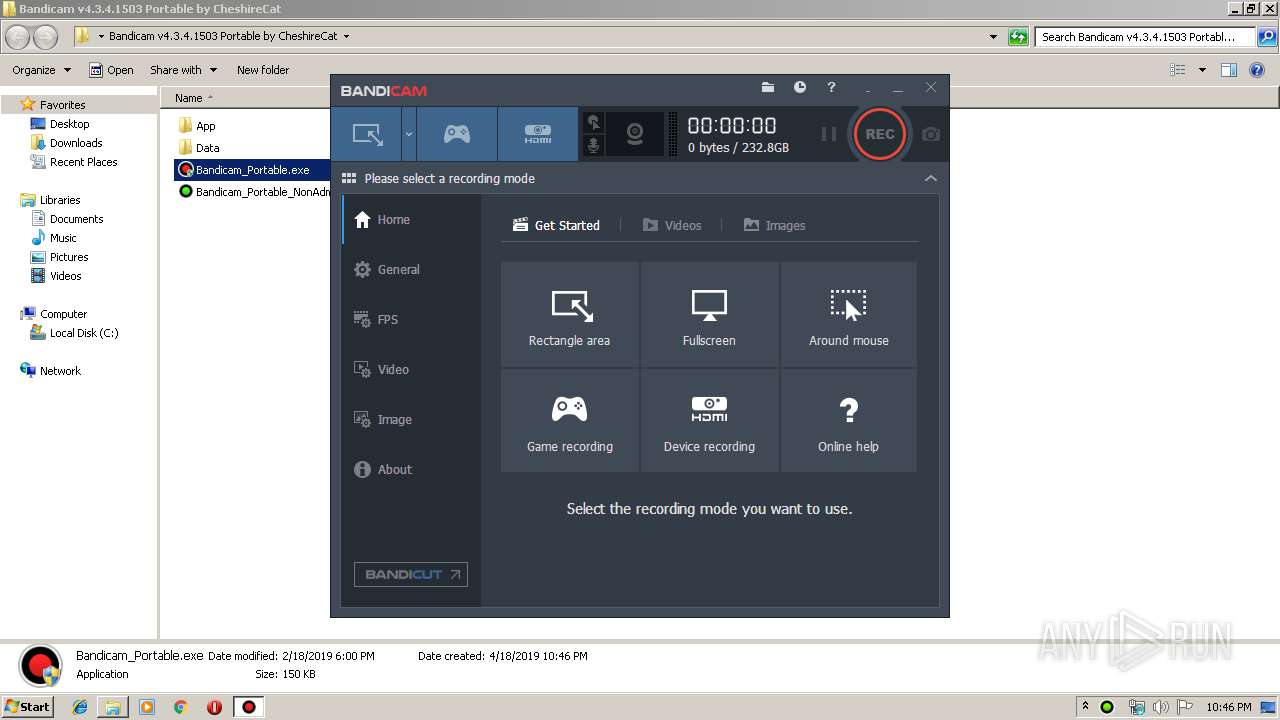
| File name: | Bandicam v4.3.4.1503 Portable by CheshireCat.exe |
| Full analysis: | https://app.any.run/tasks/735c8da7-db1d-4455-8372-ddd06b38b412 |
| Verdict: | Malicious activity |
| Analysis date: | April 18, 2019, 21:45:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 615B552234D0D78796E3A14860CD5CE9 |
| SHA1: | 916F16C45EE9A88B4A5711EA7E3A83D626BCC4B8 |
| SHA256: | E00AD8DC3AD18E468478BCB23FFB6D576CFCE453BCD80C8FFD096D59DCBABEE0 |
| SSDEEP: | 393216:1ZOPa1hlsYAArAPODpM+5+oTNFZSNxPZ42fKFz:GCzfZrAu6UTNHYZVE |
MALICIOUS
Application was dropped or rewritten from another process
- bdcam.exe (PID: 2612)
- bdcam.exe (PID: 3064)
- bdcam.exe (PID: 2476)
- Bandicam_Portable.exe (PID: 3008)
- Bandicam_Portable.exe (PID: 3344)
Loads dropped or rewritten executable
- bdcam.exe (PID: 2612)
- Bandicam_Portable.exe (PID: 3344)
- rundll32.exe (PID: 2876)
- bdcam.exe (PID: 3064)
- explorer.exe (PID: 252)
SUSPICIOUS
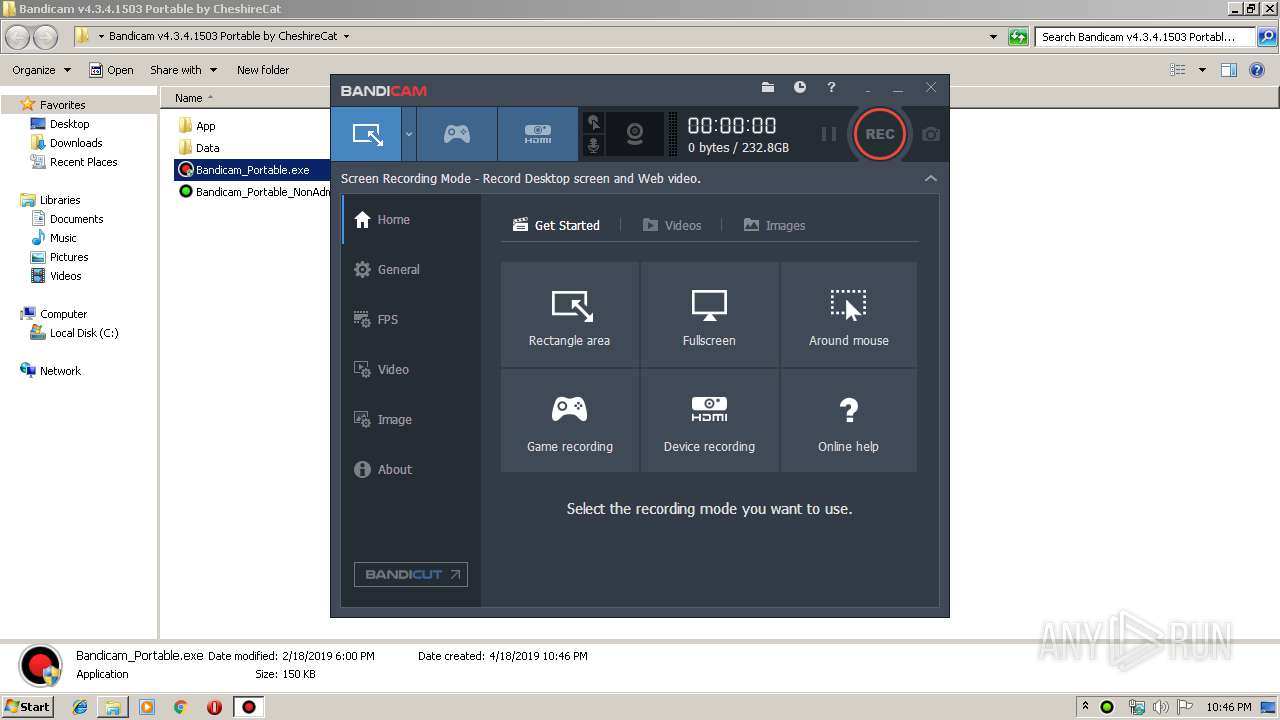
Changes IE settings (feature browser emulation)
- Bandicam_Portable.exe (PID: 3344)
Executable content was dropped or overwritten
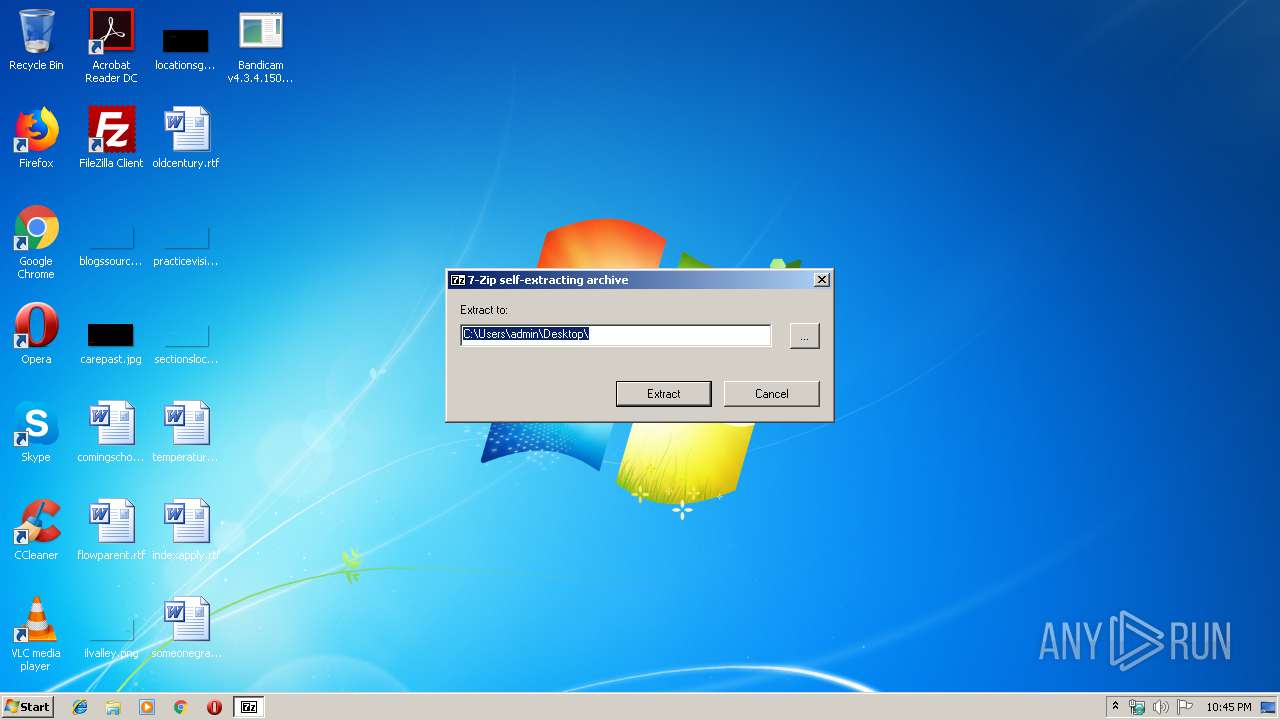
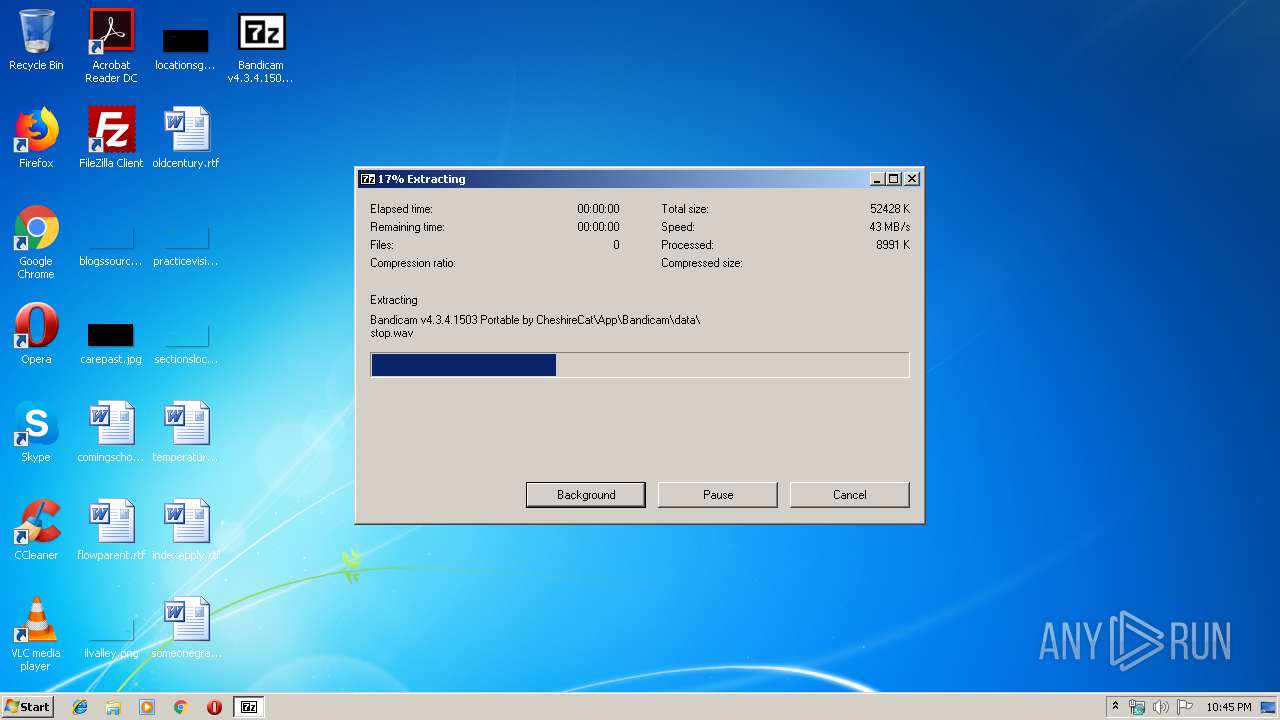
- Bandicam v4.3.4.1503 Portable by CheshireCat.exe (PID: 3992)
- Bandicam_Portable.exe (PID: 3344)
Uses RUNDLL32.EXE to load library
- bdcam.exe (PID: 2612)
INFO
Dropped object may contain Bitcoin addresses
- Bandicam v4.3.4.1503 Portable by CheshireCat.exe (PID: 3992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:21 17:00:00+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 168960 |
| InitializedDataSize: | 53248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x277c6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 19.0.0.0 |
| ProductVersionNumber: | 19.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z SFX |
| FileVersion: | 19 |
| InternalName: | 7z.sfx |
| LegalCopyright: | Copyright (c) 1999-2018 Igor Pavlov |
| OriginalFileName: | 7z.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 19 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Feb-2019 16:00:00 |
| Detected languages: |
|
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z SFX |
| FileVersion: | 19.00 |
| InternalName: | 7z.sfx |
| LegalCopyright: | Copyright (c) 1999-2018 Igor Pavlov |
| OriginalFilename: | 7z.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 19.00 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Feb-2019 16:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000293F5 | 0x00029400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67671 |
.rdata | 0x0002B000 | 0x00006500 | 0x00006600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.42967 |
.data | 0x00032000 | 0x0000453C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.39005 |
.sxdata | 0x00037000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_LNK_INFO, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00038000 | 0x00002090 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.16079 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.40193 | 688 | UNKNOWN | English - United States | RT_VERSION |
2 | 1.68942 | 296 | UNKNOWN | English - United States | RT_ICON |
26 | 1.80688 | 62 | UNKNOWN | English - United States | RT_STRING |
28 | 1.93734 | 66 | UNKNOWN | English - United States | RT_STRING |
29 | 2.18408 | 96 | UNKNOWN | English - United States | RT_STRING |
64 | 1.20724 | 48 | UNKNOWN | English - United States | RT_STRING |
97 | 3.34731 | 1088 | UNKNOWN | English - United States | RT_DIALOG |
188 | 3.1595 | 524 | UNKNOWN | English - United States | RT_STRING |
189 | 2.80372 | 228 | UNKNOWN | English - United States | RT_STRING |
207 | 1.43775 | 52 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
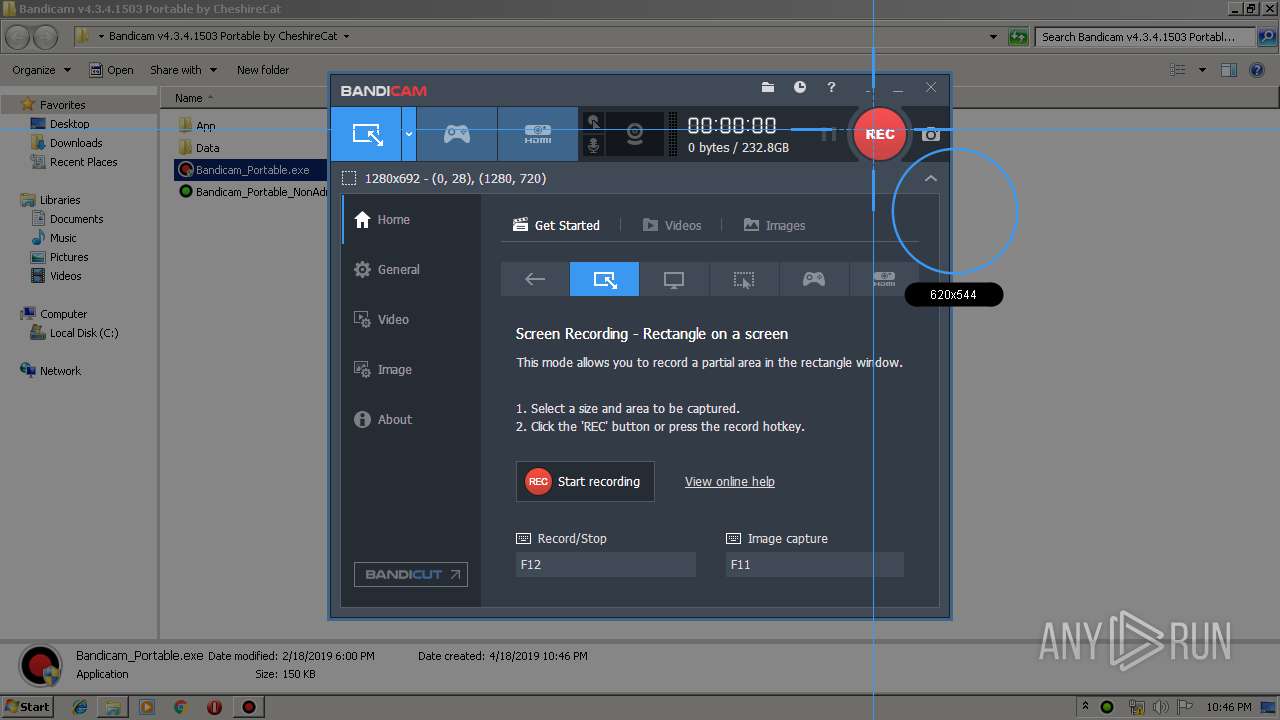
Total processes
43
Monitored processes
8
Malicious processes
2
Suspicious processes
3
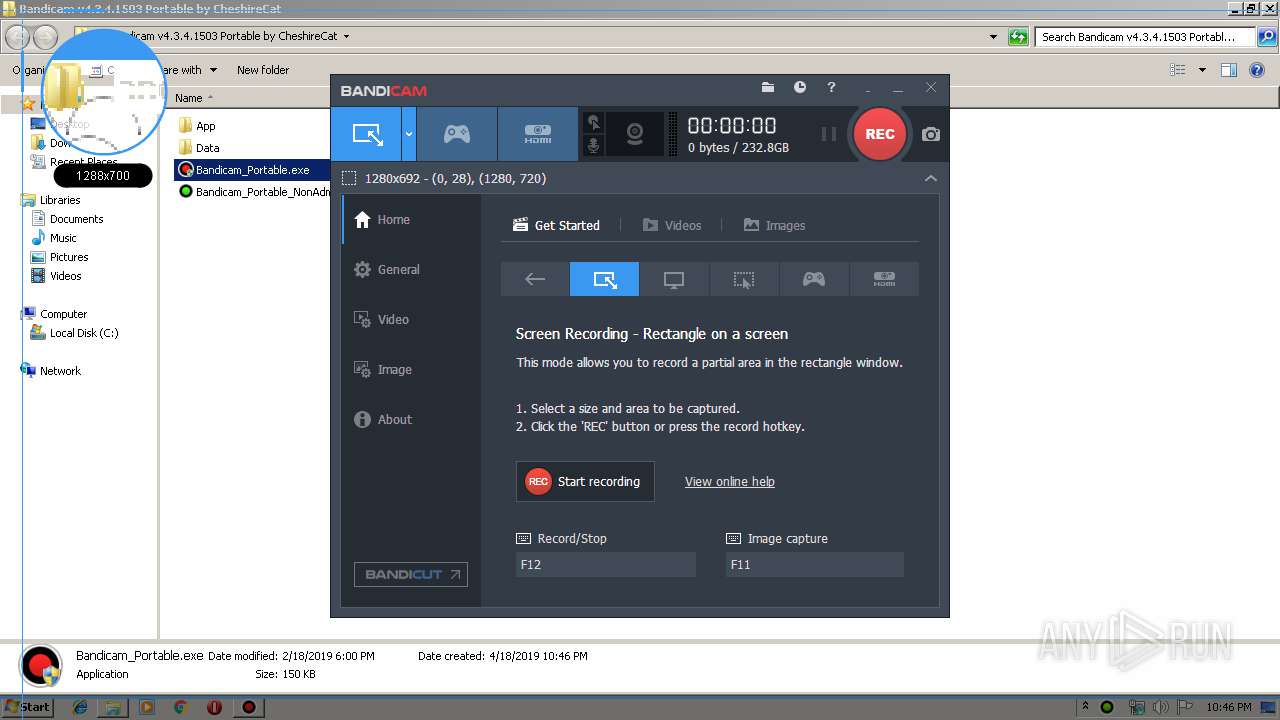
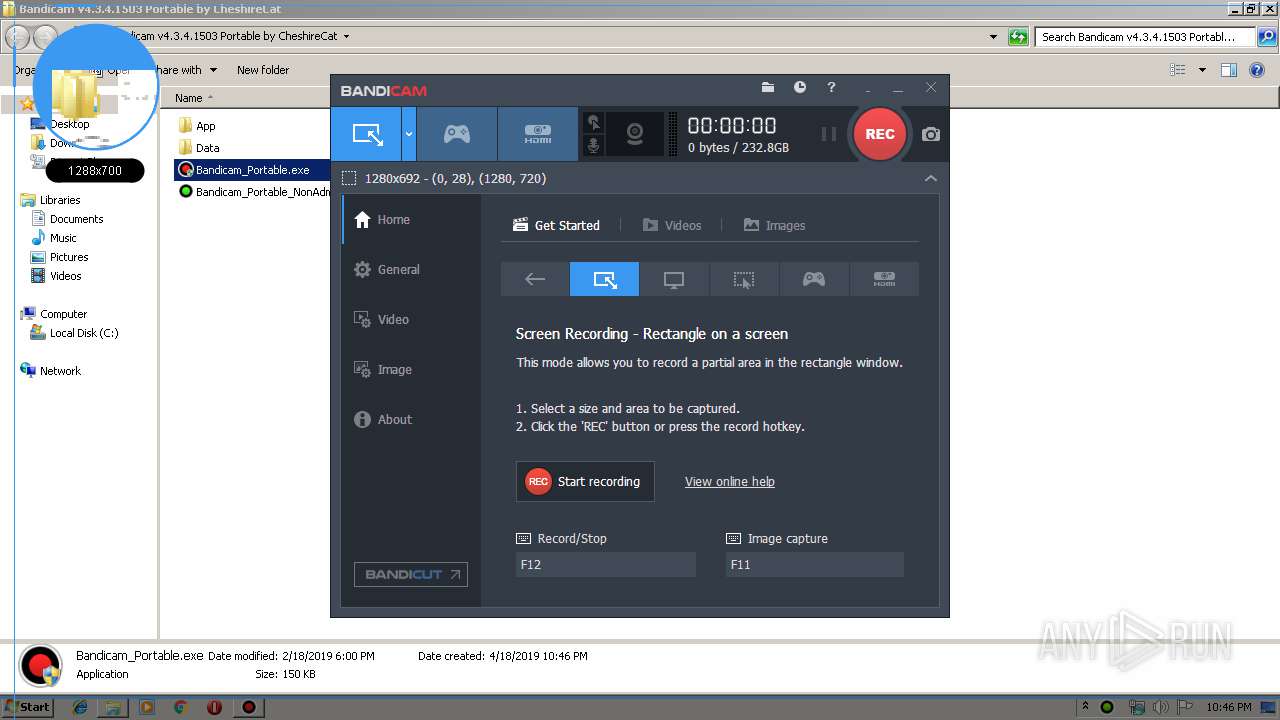
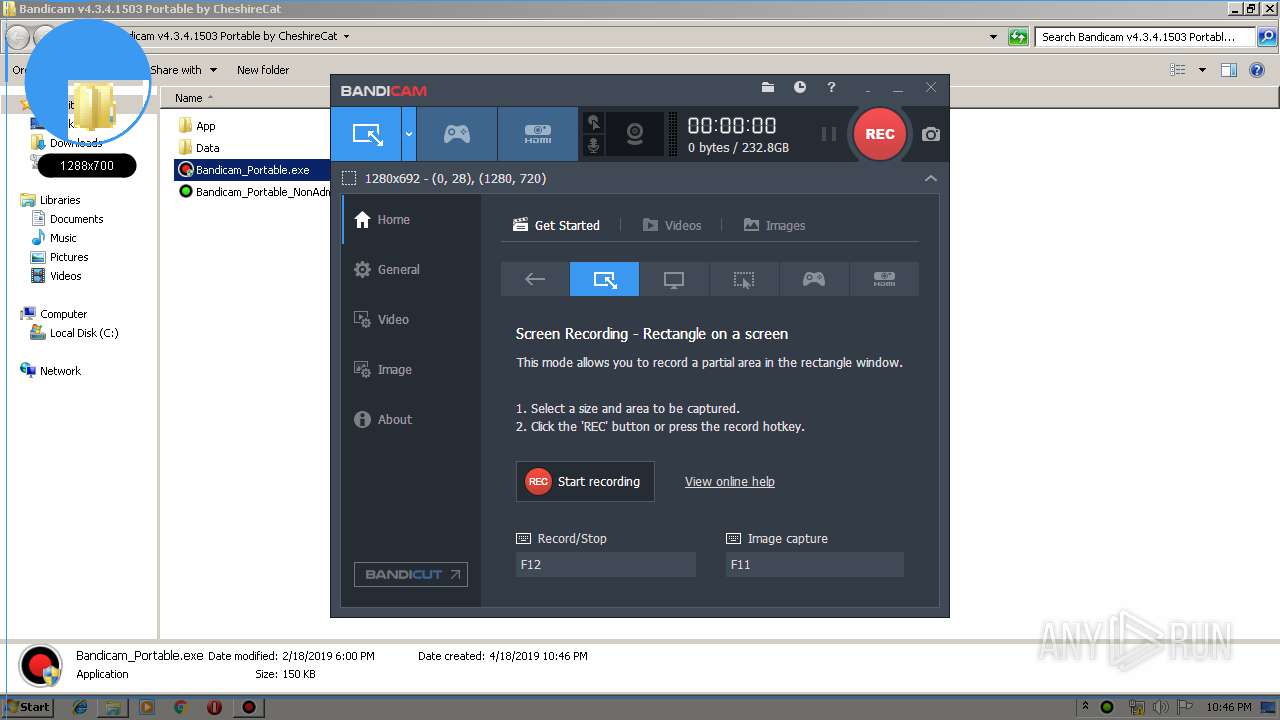
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2476 | "C:\Users\admin\AppData\Local\Temp\Bandicam.tmp\bdcam.exe" | C:\Users\admin\AppData\Local\Temp\Bandicam.tmp\bdcam.exe | — | Bandicam_Portable.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2612 | "C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\App\Bandicam\bdcam.exe" /install | C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\App\Bandicam\bdcam.exe | — | Bandicam_Portable.exe | |||||||||||
User: admin Company: Bandicam Company Integrity Level: HIGH Description: Bandicam - bdcam.exe Exit code: 0 Version: 4.3.4.1503 Modules
| |||||||||||||||
| 2876 | "C:\Windows\system32\rundll32.exe" "C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\App\Bandicam\bdcamvk32.dll",RegDll | C:\Windows\system32\rundll32.exe | — | bdcam.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3008 | "C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\Bandicam_Portable.exe" | C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\Bandicam_Portable.exe | — | explorer.exe | |||||||||||
User: admin Company: CheshireCat Integrity Level: MEDIUM Description: Bandicam Portable Exit code: 3221226540 Version: 4.3.0.0 Modules
| |||||||||||||||
| 3064 | "C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\App\Bandicam\bdcam.exe" 0 0 | C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\App\Bandicam\bdcam.exe | — | Bandicam_Portable.exe | |||||||||||
User: admin Company: Bandicam Company Integrity Level: HIGH Description: Bandicam - bdcam.exe Exit code: 0 Version: 4.3.4.1503 Modules
| |||||||||||||||
| 3344 | "C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\Bandicam_Portable.exe" | C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\Bandicam_Portable.exe | explorer.exe | ||||||||||||
User: admin Company: CheshireCat Integrity Level: HIGH Description: Bandicam Portable Exit code: 0 Version: 4.3.0.0 Modules
| |||||||||||||||
| 3992 | "C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat.exe" | C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z SFX Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
Total events
5 571
Read events
4 776
Write events
795
Delete events
0
Modification events
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\Qrfxgbc\Onaqvpnz i4.3.4.1503 Cbegnoyr ol PurfuverPng.rkr |
Value: 000000000000000000000000EC120000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000400000002000000D48600000200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F020200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F020200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F02 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0000000001000000070000000200000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\Qrfxgbc\Onaqvpnz i4.3.4.1503 Cbegnoyr ol PurfuverPng.rkr |
Value: 0000000000000000000000008A180000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000400000002000000728C00000200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F020200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F020200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F02 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | 8 |
Value: A200310000000000664E645F100042414E4449437E312E3135300000860008000400EFBE924EC0AD924EC0AD2A000000CA440000000007000000000000000000000000000000420061006E0064006900630061006D002000760034002E0033002E0034002E003100350030003300200050006F0072007400610062006C00650020006200790020004300680065007300680069007200650043006100740000001C000000 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 080000000000000001000000070000000200000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\8 |
| Operation: | write | Name: | NodeSlot |
Value: 95 | |||
Executable files
21
Suspicious files
1
Text files
63
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3992 | Bandicam v4.3.4.1503 Portable by CheshireCat.exe | C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\App\Bandicam\data\language.dat | text | |
MD5:4E8892BF271652903B1C83F77939430D | SHA256:5B00AABD18AE2A82FB440990D5D13AACB9D30C2FA0288F992CD1D9C022BE2838 | |||
| 3992 | Bandicam v4.3.4.1503 Portable by CheshireCat.exe | C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\App\Bandicam\bandicam.ini | text | |
MD5:D046EFABEB9B9777A43C31B7B6F79BB8 | SHA256:A13E80A9891989BE50090CF712B27BB473EA59B238C149CA9AB2CD6C66F338CA | |||
| 3992 | Bandicam v4.3.4.1503 Portable by CheshireCat.exe | C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\App\Bandicam\bdcamvk32.json | text | |
MD5:A57121E4D19A606946CCDE17F46E833D | SHA256:03975B3513B256E8AB6194634F0AAD0FAAC698581535908885EB07DCBCFA3E54 | |||
| 3992 | Bandicam v4.3.4.1503 Portable by CheshireCat.exe | C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\App\Bandicam\bdcam64.bin | executable | |
MD5:2E2A83322DB942F01EBF01C8648E6449 | SHA256:0D7B3E0F9D9AEE4BFEBA9AAEE84C1BD57BDB141F4EF20AF4727FA1563D26FF24 | |||
| 3992 | Bandicam v4.3.4.1503 Portable by CheshireCat.exe | C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\App\Bandicam\lang\Bulgarian.ini | text | |
MD5:D5236D3D89A278F43103C3BDFEA19087 | SHA256:C3B0DB353639DC5D2C65D20DE7ACA43B748503AD0D9A1FBEF57ED08B11FF4978 | |||
| 3992 | Bandicam v4.3.4.1503 Portable by CheshireCat.exe | C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\App\Bandicam\lang\Belarusian.ini | text | |
MD5:015073F2C7ADEA85A5241257B10F6937 | SHA256:325A4EE1DCFF650D69508BD645D838B7B315037166F1E0BE309F4B5F5136D523 | |||
| 3992 | Bandicam v4.3.4.1503 Portable by CheshireCat.exe | C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\App\Bandicam\lang\Bosnian.ini | text | |
MD5:82D7E2A53ED040A4614C4F1CFF8F921C | SHA256:DD02B98C0721C882E674DB3D64F602321FF6BF28EC6302197EAA51A9A243E397 | |||
| 3992 | Bandicam v4.3.4.1503 Portable by CheshireCat.exe | C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\App\Bandicam\data\effects.dat | gmc | |
MD5:8125C864B0D52FF4B3230F7FC8C5D553 | SHA256:6A94947827CF2D12B8CC203BFC38633AB2BB46CE6BCA3A365B5196F0CB922272 | |||
| 3992 | Bandicam v4.3.4.1503 Portable by CheshireCat.exe | C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\App\Bandicam\lang\Azerbaijani.ini | text | |
MD5:CE714A8C82FEA54815B00B2C966D263A | SHA256:63D098964A4756BA0B60FACC5674266D556B12799785DF871835050396778005 | |||
| 3992 | Bandicam v4.3.4.1503 Portable by CheshireCat.exe | C:\Users\admin\Desktop\Bandicam v4.3.4.1503 Portable by CheshireCat\App\Bandicam\lang\Arabic.ini | text | |
MD5:4FCEFA45A3339BF59A796DE01D58A2AC | SHA256:3B25B7662CADAC700149632B33A1A195C86953300F4672A8A8B2EB58D389D97C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report