| File name: | informes.vbs |
| Full analysis: | https://app.any.run/tasks/1b22f2b1-7dba-4958-b66e-9ed229224fec |
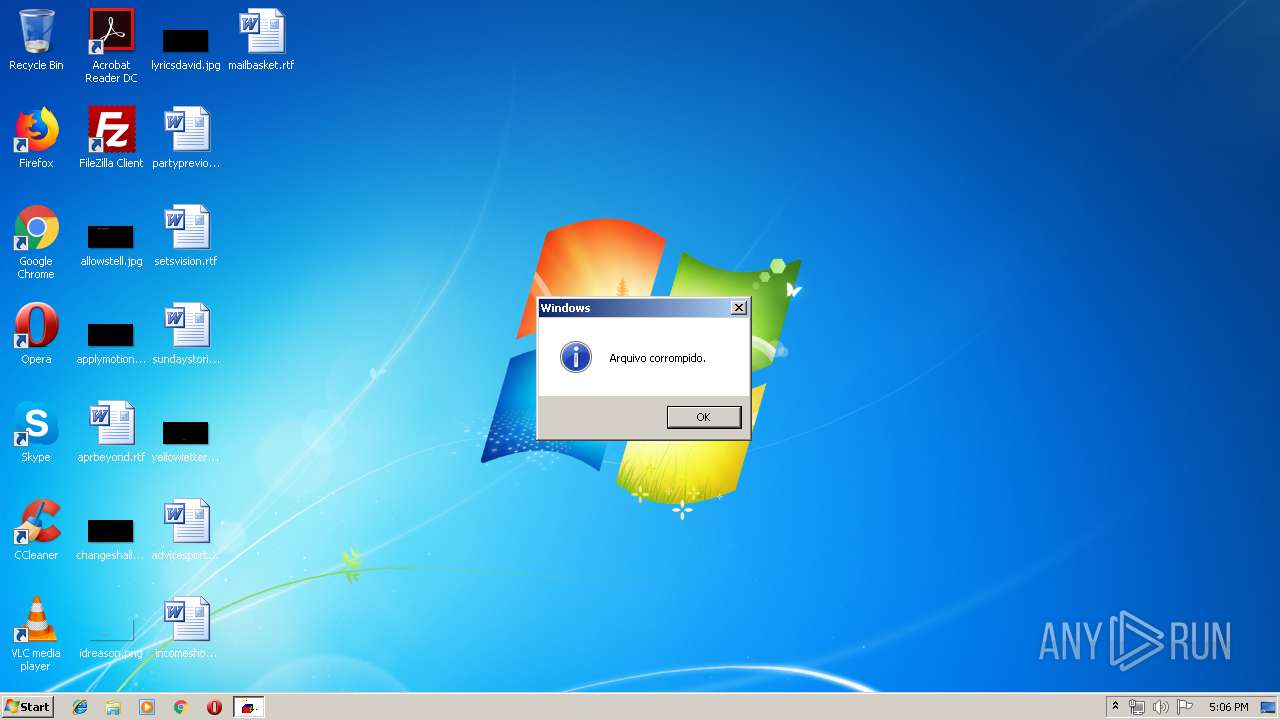
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 16:06:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 4B1814ECF468197AFA1B16608AC6903C |
| SHA1: | 6A9A58C8767A888B01DF92CB9F10802CECBA51CC |
| SHA256: | DFED13F92D7CF367D166BBF97FEC49B3F94AC240769602175125D99644602C36 |
| SSDEEP: | 96:fSosKUs4yG9eR97IyPmgBBSf0Dkne/9om+pbrzNhp:MO4yG07Iy+6BSMoQebrF |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
33
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2840 | c:\MOPRTUbce\lucuxeottm.exe | c:\MOPRTUbce\lucuxeottm.exe | — | WScript.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3016 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\informes.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
118
Read events
97
Write events
21
Delete events
0
Modification events
| (PID) Process: | (3016) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3016) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3016) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3016) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3016) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3016) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3016) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3016) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3016) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3016) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3016 | WScript.exe | C:\MOPRTUbce\lucuxeottm.exe | — | |
MD5:— | SHA256:— | |||
| 3016 | WScript.exe | \Device\HarddiskVolume2\MOPRTUbce\UU.ini | — | |
MD5:— | SHA256:— | |||
| 3016 | WScript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\dkoapjfdkopdfd[1].zip | compressed | |
MD5:— | SHA256:— | |||
| 3016 | WScript.exe | C:\MOPRTUbce\bk.ini | text | |
MD5:— | SHA256:— | |||
| 3016 | WScript.exe | C:\MOPRTUbce\egiijlnnoqsstvwwyyABBDFFGGIJJ.zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
0
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3016 | WScript.exe | GET | 200 | 191.239.246.123:80 | http://191.239.246.123/vem2019/index.php | BR | — | — | suspicious |
3016 | WScript.exe | GET | 200 | 191.239.246.123:80 | http://191.239.246.123/down2019/dkoapjfdkopdfd.zip | BR | compressed | 2.56 Mb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3016 | WScript.exe | 191.239.246.123:80 | — | Microsoft Corporation | BR | suspicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3016 | WScript.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
3016 | WScript.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Loader (Trojan.Agent.DDSA) Requesting Zip Archive |