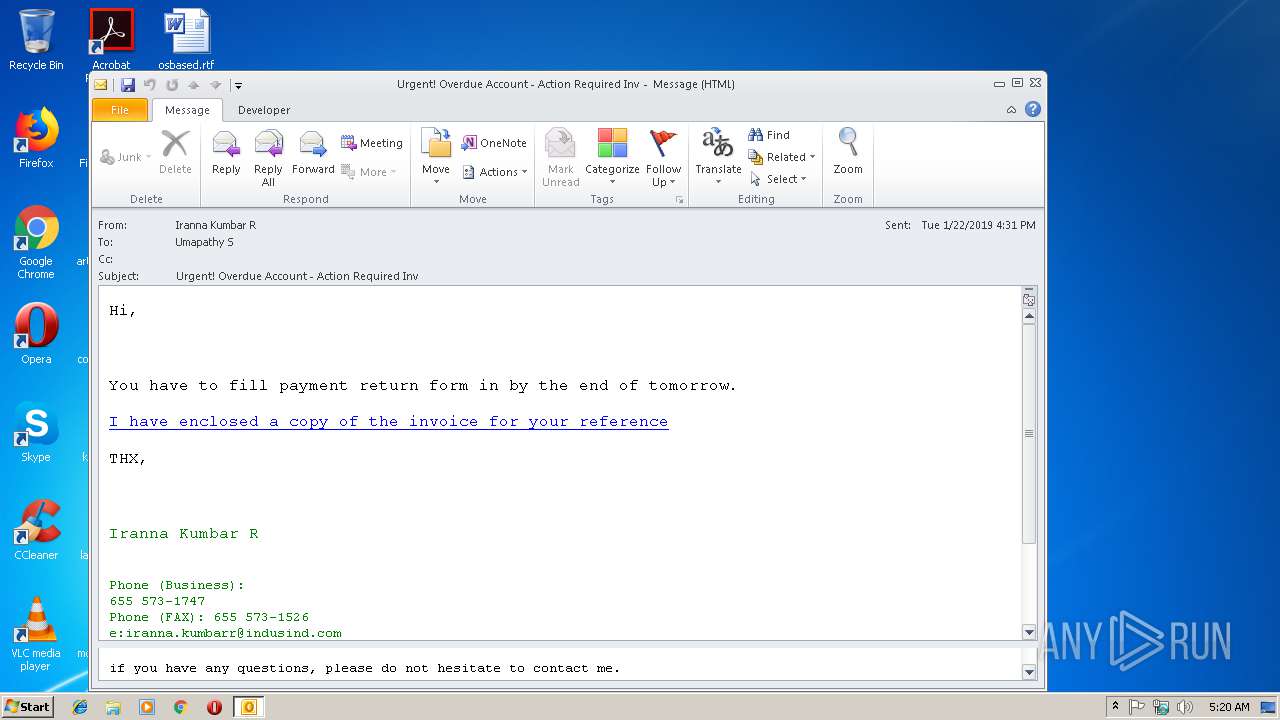
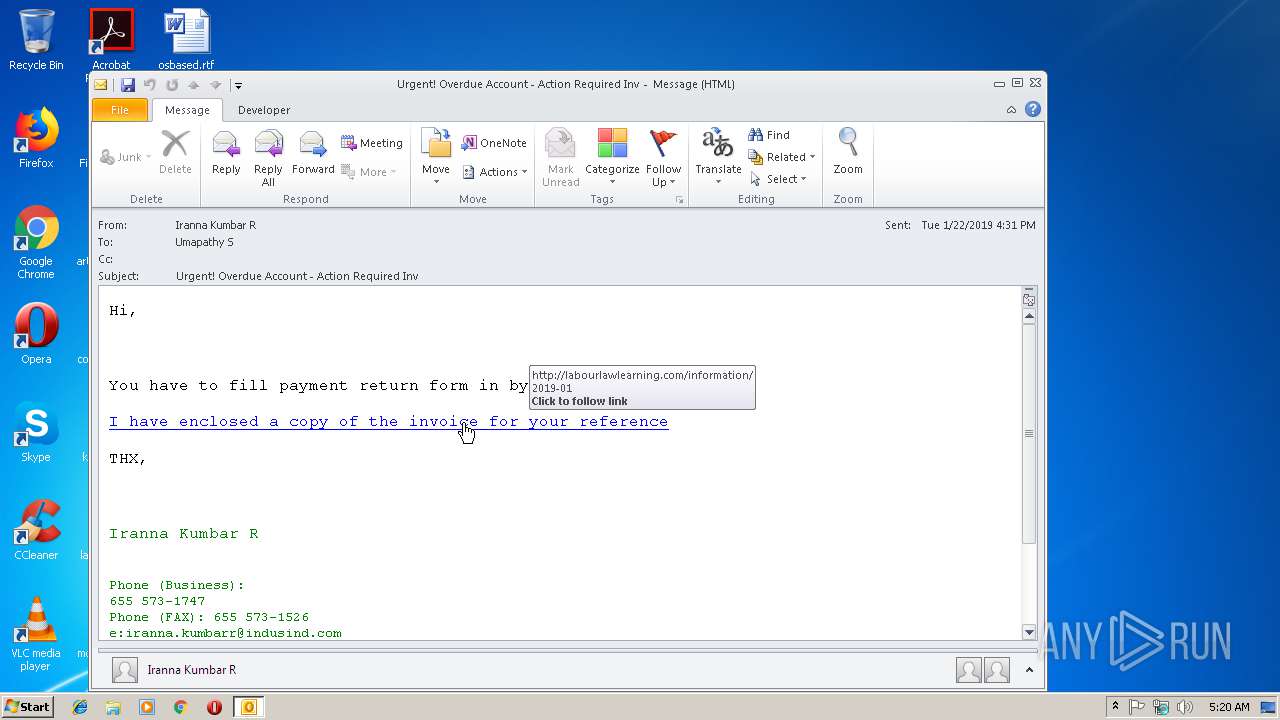
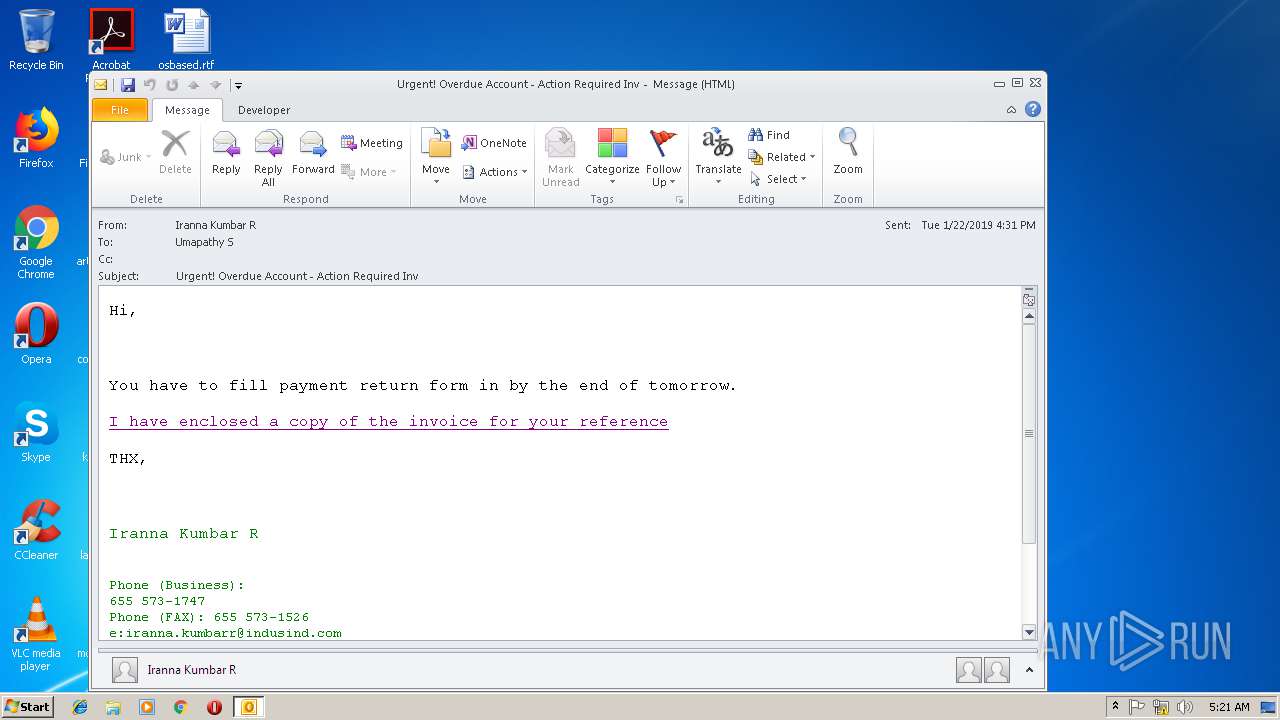
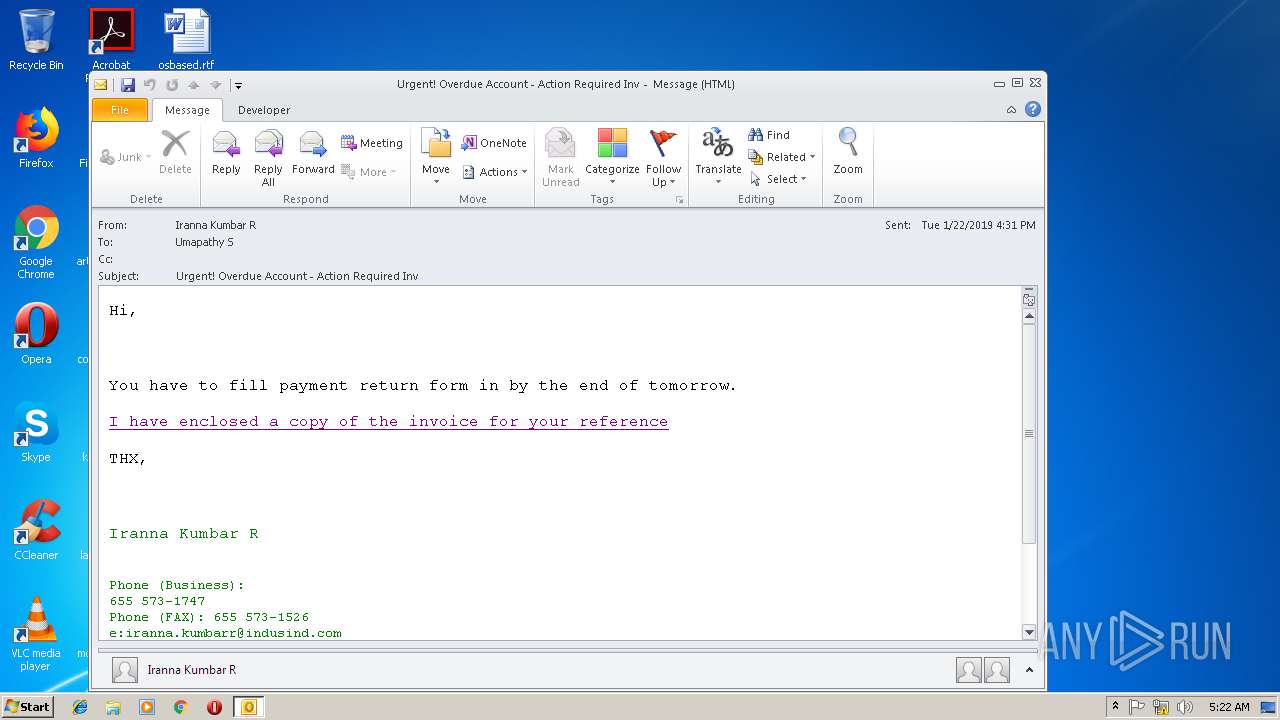
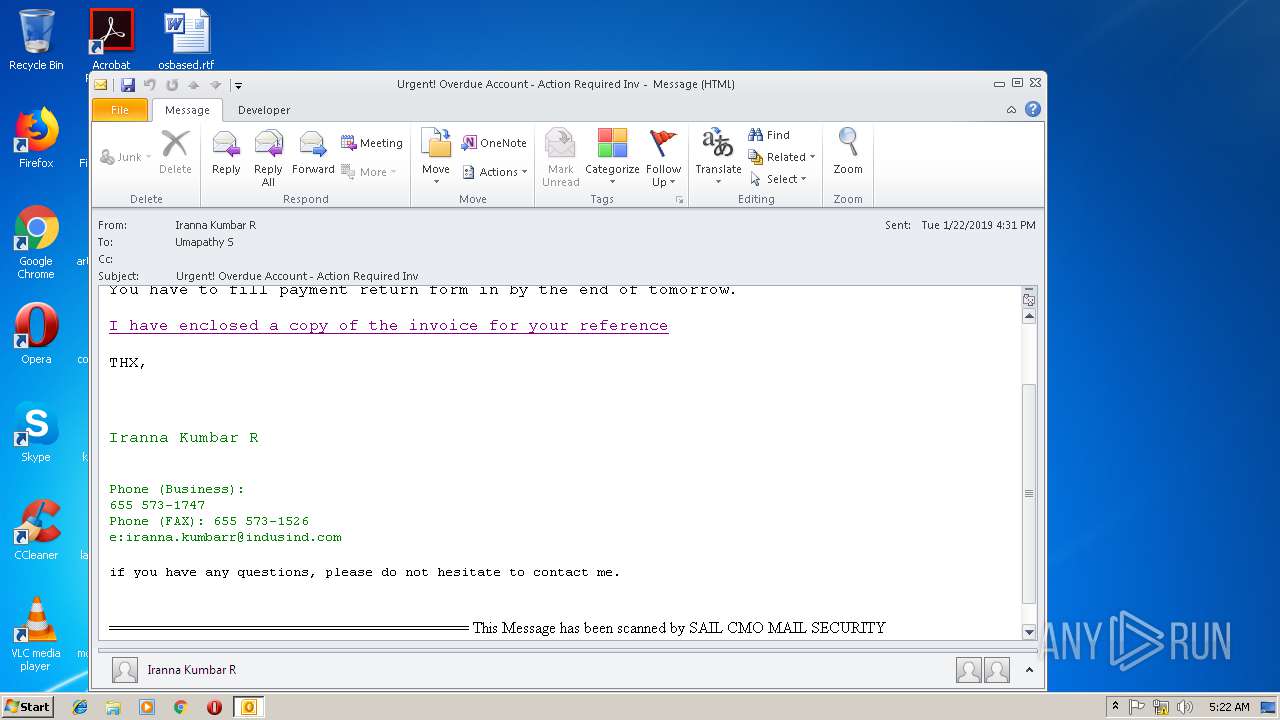
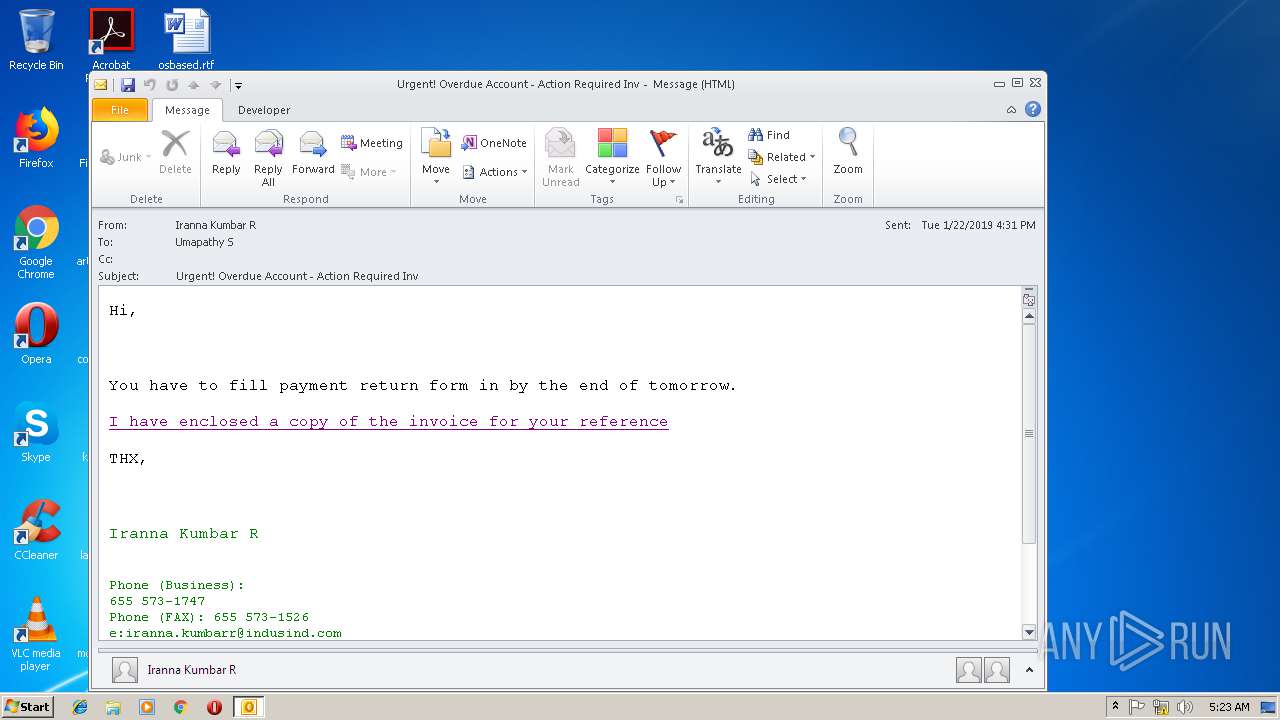
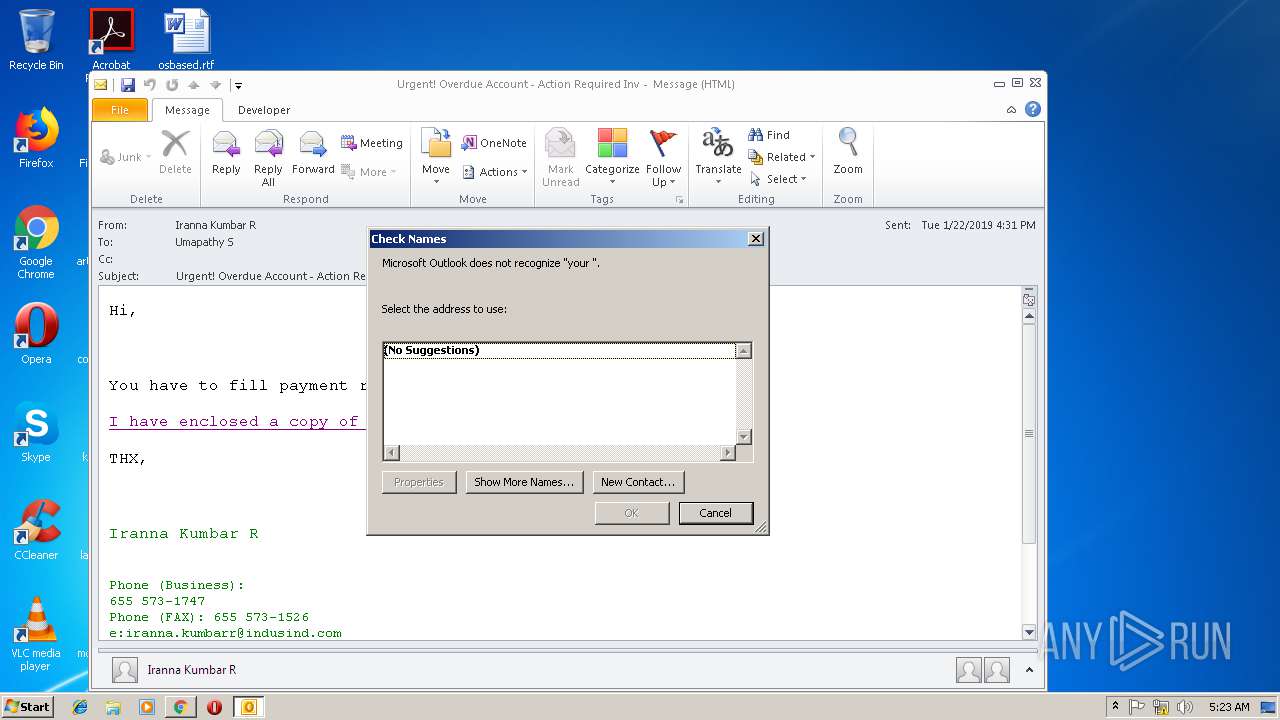
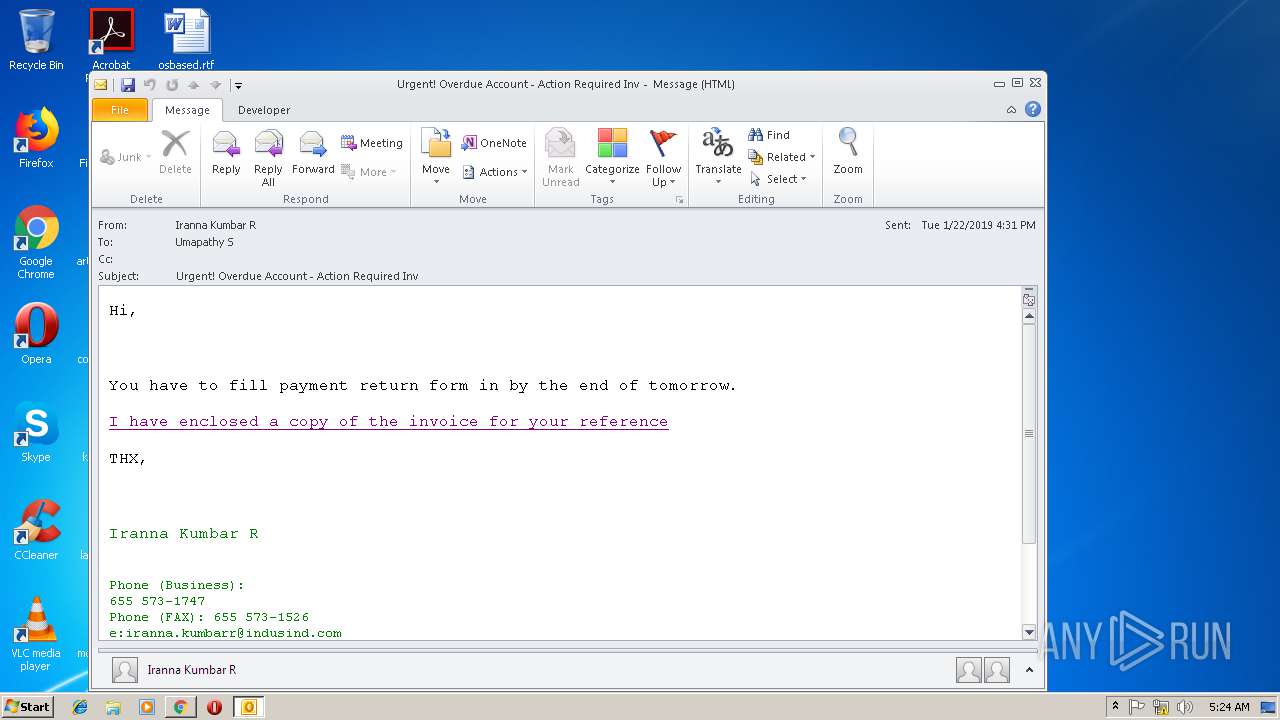
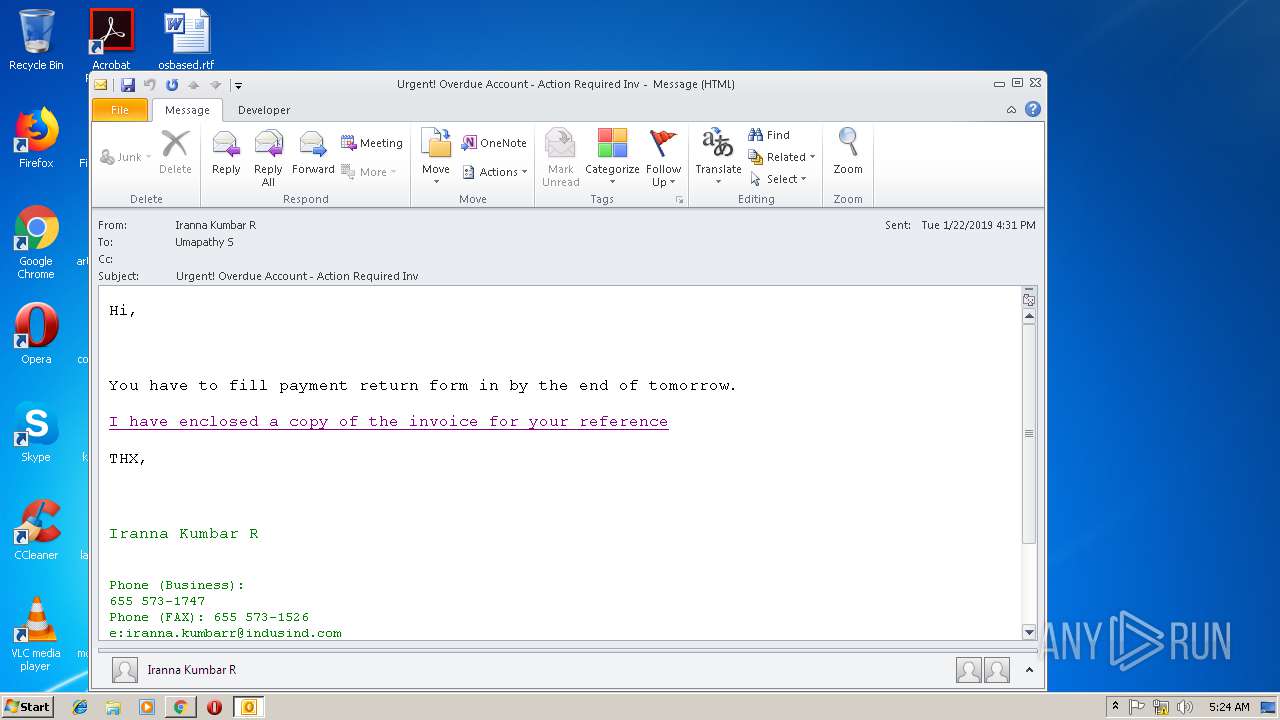
| File name: | Urgent! Overdue Account - Action Required Inv.msg |
| Full analysis: | https://app.any.run/tasks/0c7ee521-a560-42fd-a595-922dc10c65a8 |
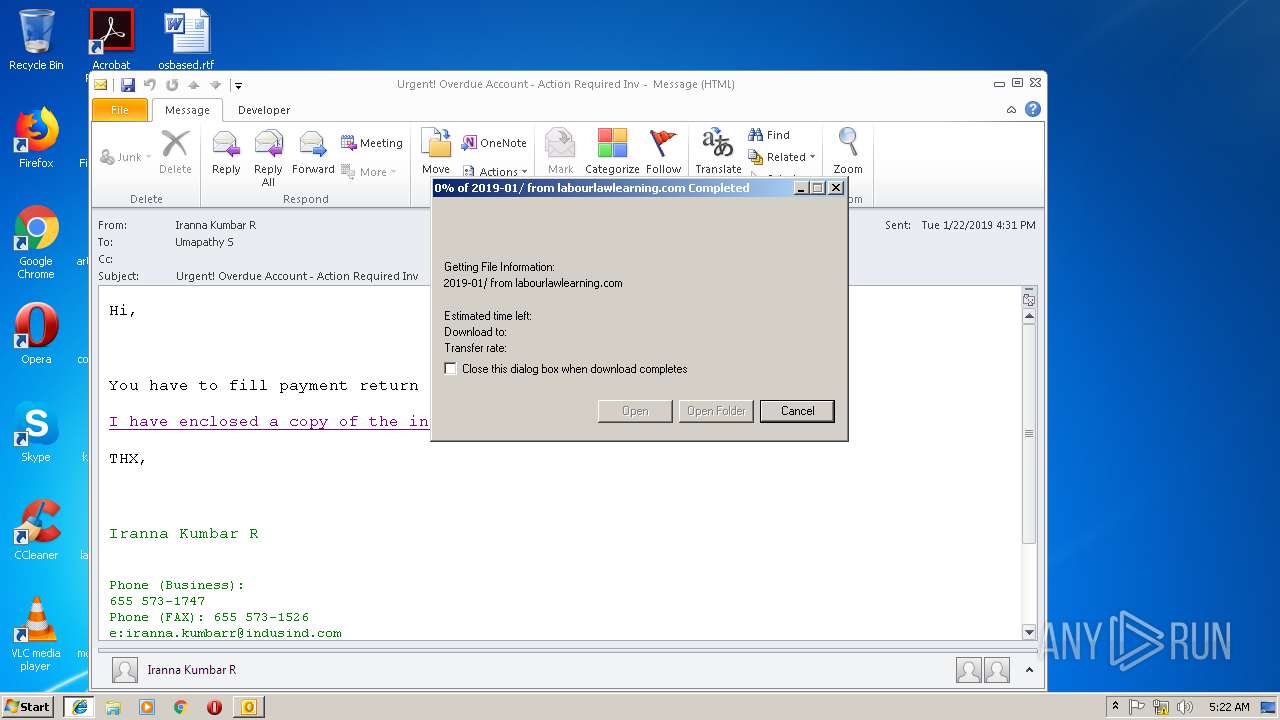
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 23, 2019, 05:20:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 8C92679BA7FAD0ED456156EC1A745303 |
| SHA1: | 413758903C35032DEADC2E768CCAFD93A1C95794 |
| SHA256: | DFECD325EB3A040CCA55186267EF905E91F2F396C1B58AA5D6CD0F4CD706AE30 |
| SSDEEP: | 1536:J1WW6W2WFfR0xTJgQisS7WWfWYMWtWeXqybkwvzWtyybtV:J3R0xTJgbshWXqybN7WtyybtV |
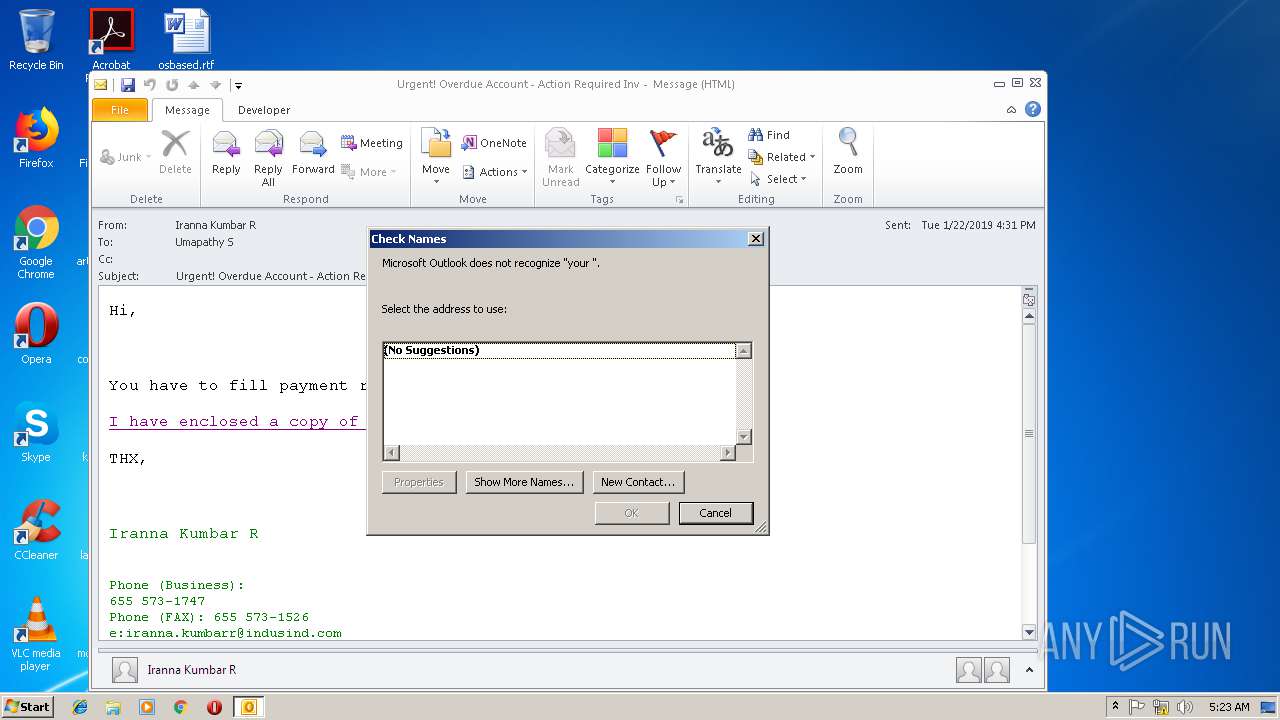
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3384)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3384)
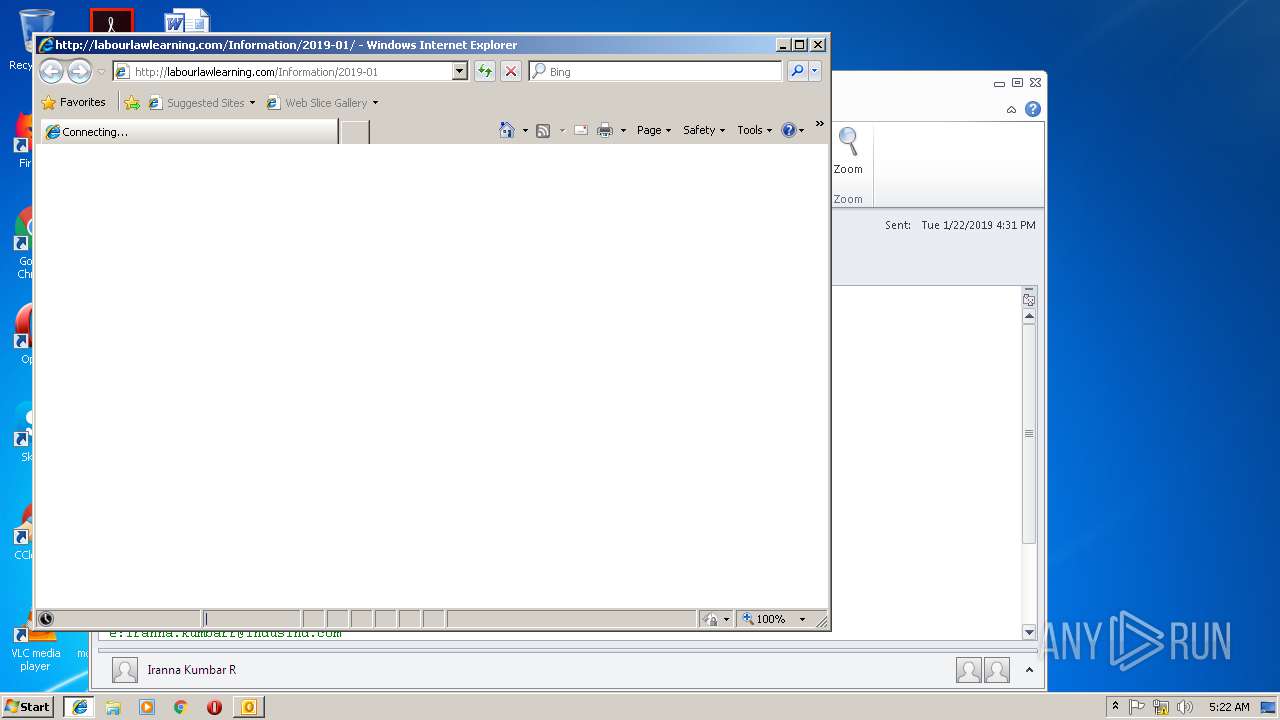
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3384)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3384)
Application launched itself
- WINWORD.EXE (PID: 2432)
Starts Microsoft Office Application
- chrome.exe (PID: 2904)
- WINWORD.EXE (PID: 2432)
INFO
Application launched itself
- iexplore.exe (PID: 2820)
- iexplore.exe (PID: 3652)
- iexplore.exe (PID: 2256)
- chrome.exe (PID: 2904)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3384)
- WINWORD.EXE (PID: 2432)
- WINWORD.EXE (PID: 3748)
Changes internet zones settings
- iexplore.exe (PID: 2820)
- iexplore.exe (PID: 3652)
- iexplore.exe (PID: 2256)
Reads Internet Cache Settings
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 1224)
- iexplore.exe (PID: 2600)
- chrome.exe (PID: 2904)
Reads internet explorer settings
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 2600)
Creates files in the user directory
- iexplore.exe (PID: 2820)
- iexplore.exe (PID: 2256)
- WINWORD.EXE (PID: 2432)
Reads settings of System Certificates
- chrome.exe (PID: 2904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
55
Monitored processes
22
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1224 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3652 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6bb900b0,0x6bb900c0,0x6bb900cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
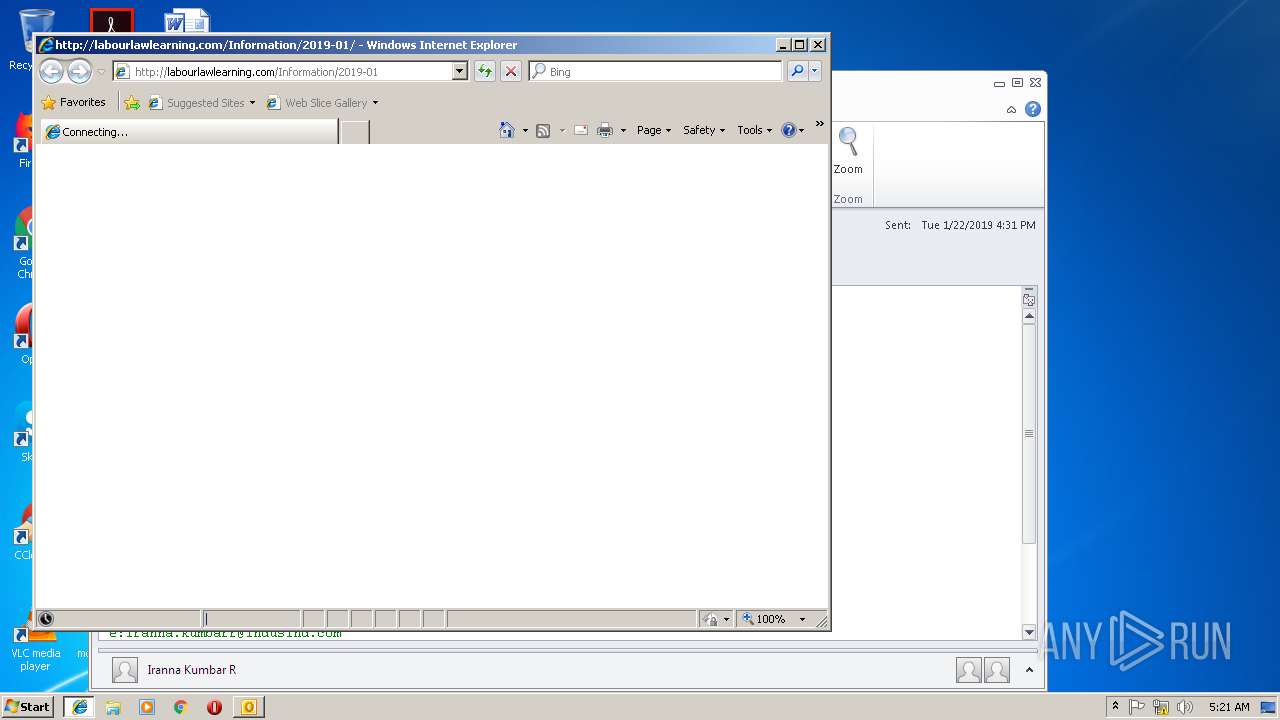
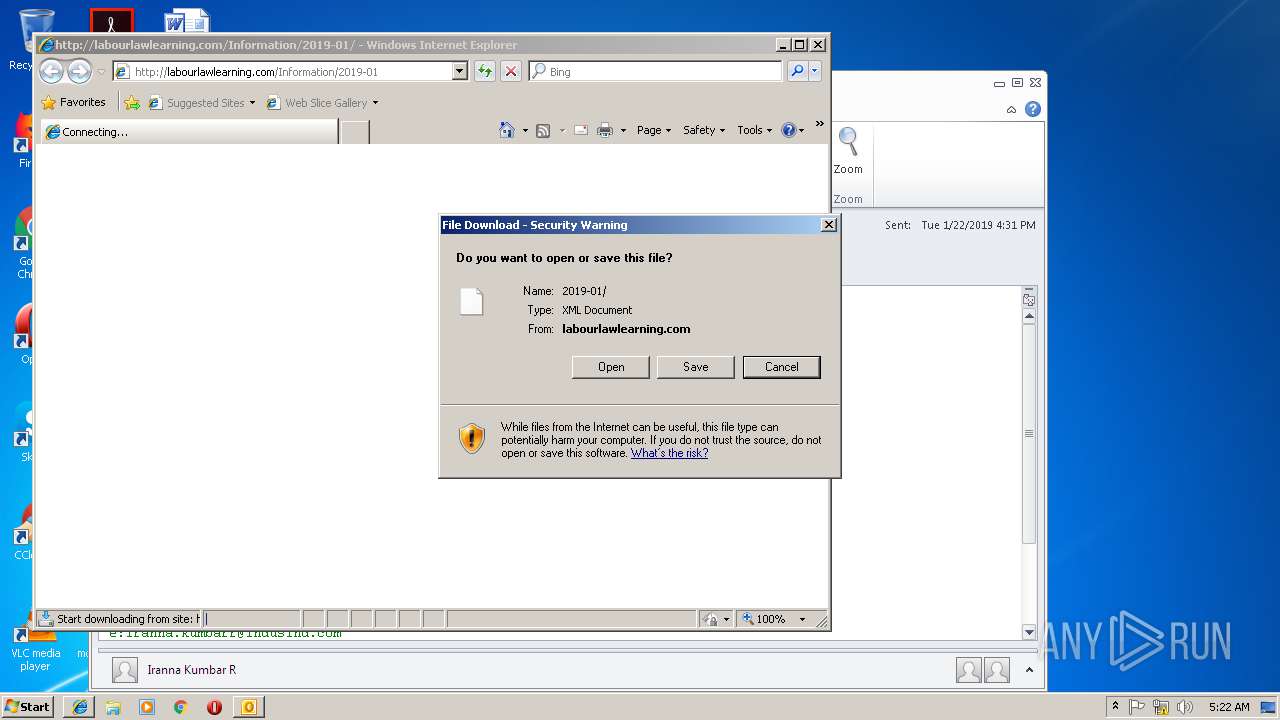
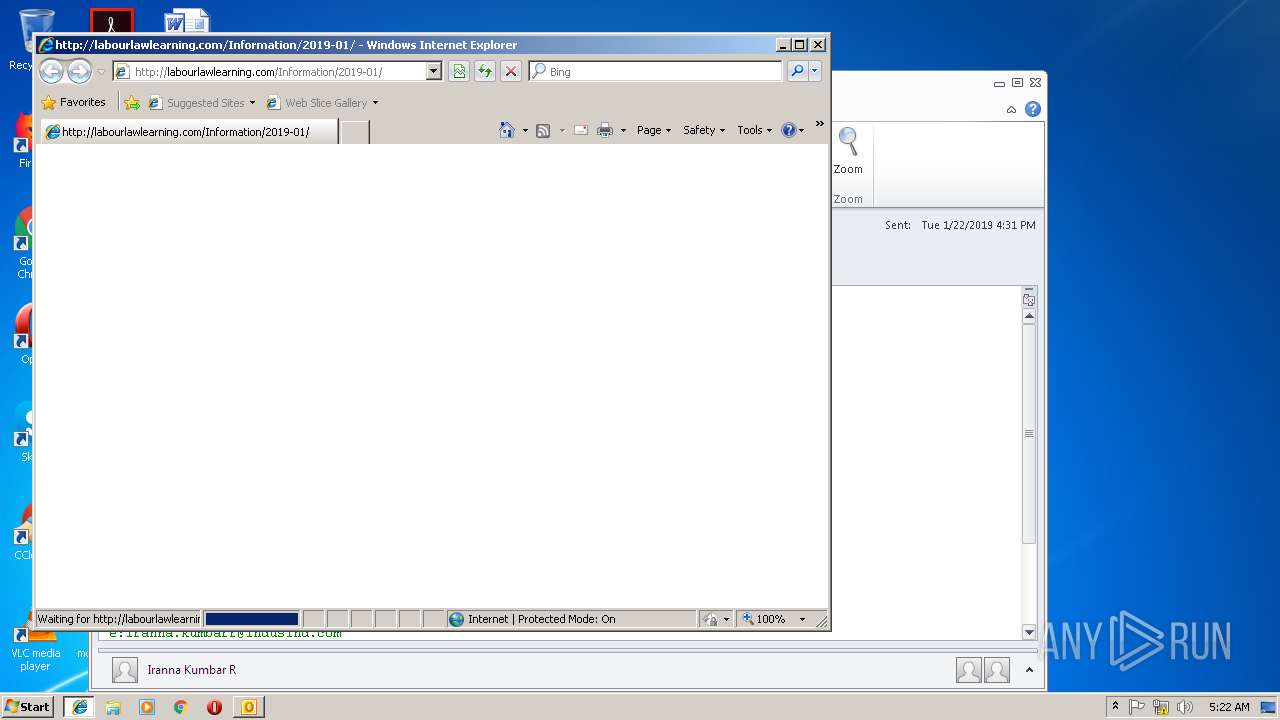
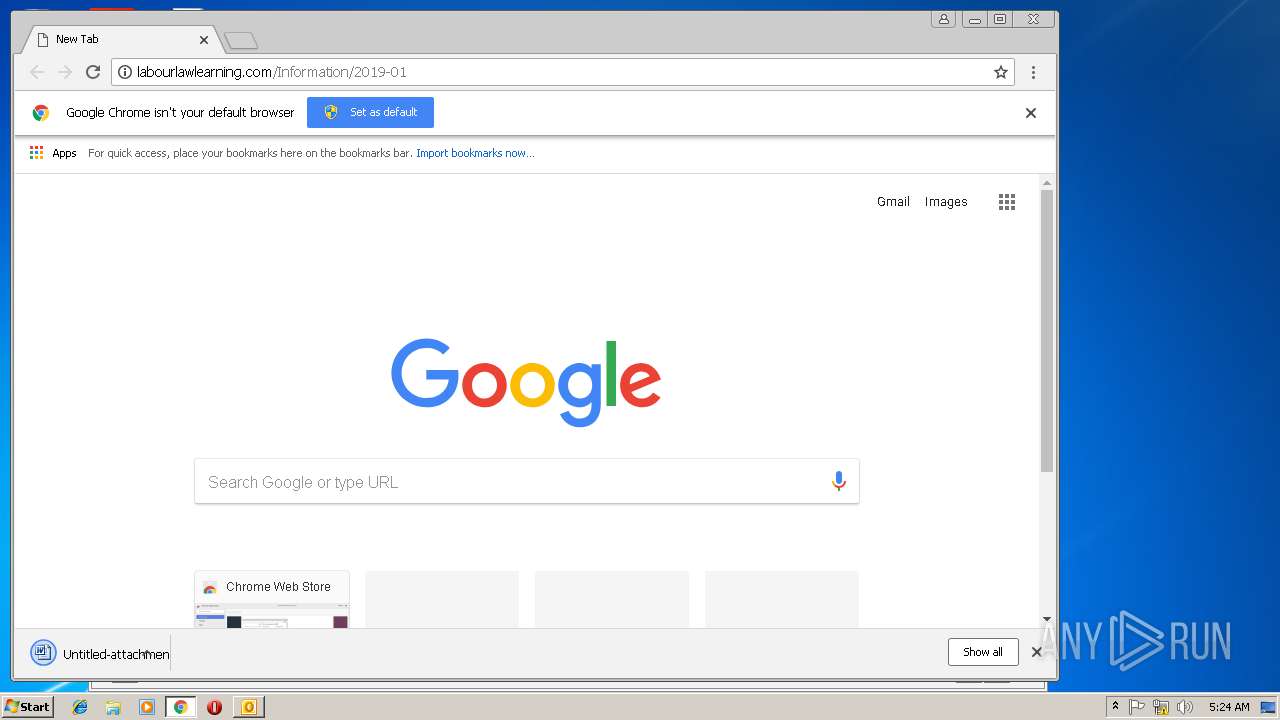
| 2256 | "C:\Program Files\Internet Explorer\iexplore.exe" http://labourlawlearning.com/Information/2019-01 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=944,11568411343572776224,5821961721258438607,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=4DFFD121A0181FCEE39D1C9E0CD7B976 --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\Untitled-attachment-23012019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,11568411343572776224,5821961721258438607,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=B1DE52E90F88CE06911ECBDE5F924AB0 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B1DE52E90F88CE06911ECBDE5F924AB0 --renderer-client-id=10 --mojo-platform-channel-handle=2356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2256 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=944,11568411343572776224,5821961721258438607,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=9F73D71B6F92BAD252FCBF3C814F6660 --mojo-platform-channel-handle=2068 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,11568411343572776224,5821961721258438607,131072 --enable-features=PasswordImport --service-pipe-token=E006059B5165B06A6A4293C2BCDB1CAD --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E006059B5165B06A6A4293C2BCDB1CAD --renderer-client-id=5 --mojo-platform-channel-handle=1916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2820 | "C:\Program Files\Internet Explorer\iexplore.exe" http://labourlawlearning.com/Information/2019-01 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 563
Read events
3 605
Write events
924
Delete events
34
Modification events
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | cc& |
Value: 63632600380D0000010000000000000000000000 | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 380D0000AEF85067DBB2D40100000000 | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219877920 | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1312227349 | |||
Executable files
0
Suspicious files
60
Text files
110
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR87D3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2820 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2820 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2820 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC5F6F783AC6AF374.TMP | — | |
MD5:— | SHA256:— | |||
| 2820 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF4A147A69B799E46C.TMP | — | |
MD5:— | SHA256:— | |||
| 2820 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFBB730B680DE7F256.TMP | — | |
MD5:— | SHA256:— | |||
| 2820 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\F81ULMMW34HS5ZZR9N0E.temp | — | |
MD5:— | SHA256:— | |||
| 3652 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3652 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
28
DNS requests
18
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3384 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
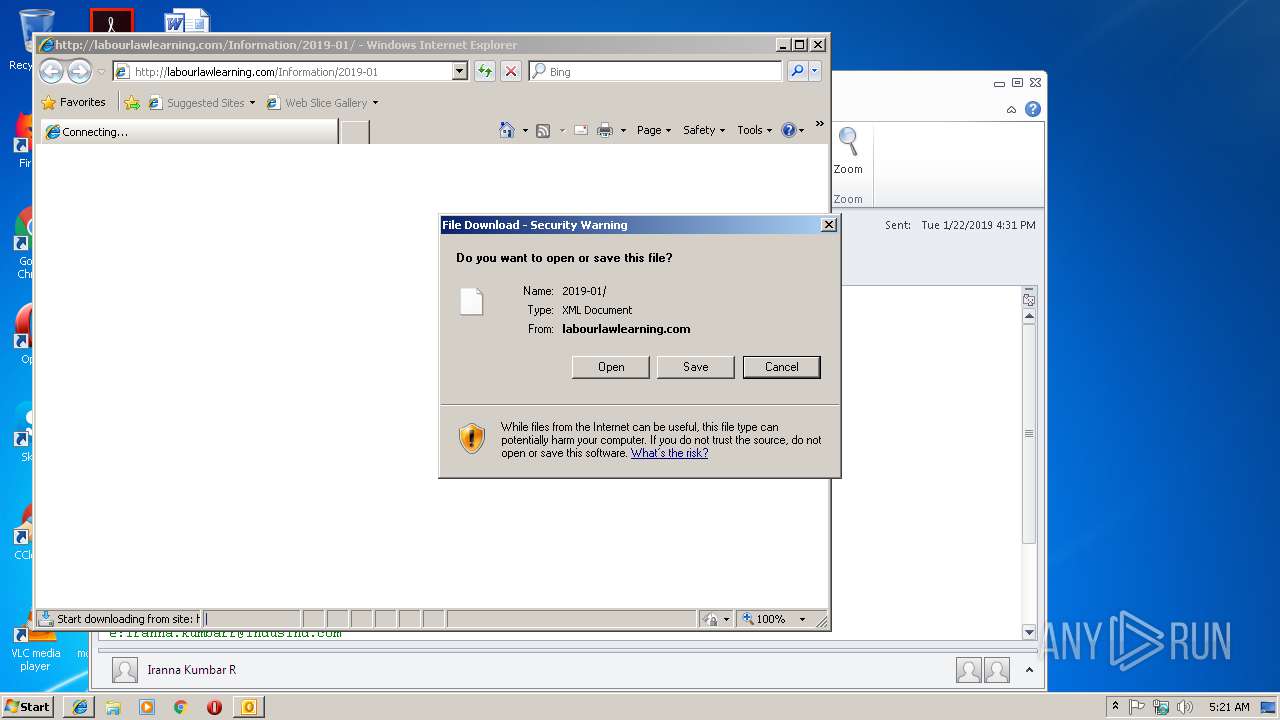
2256 | iexplore.exe | GET | 200 | 87.229.71.152:80 | http://labourlawlearning.com/favicon.ico | HU | — | — | malicious |
2820 | iexplore.exe | GET | 200 | 87.229.71.152:80 | http://labourlawlearning.com/favicon.ico | HU | — | — | malicious |
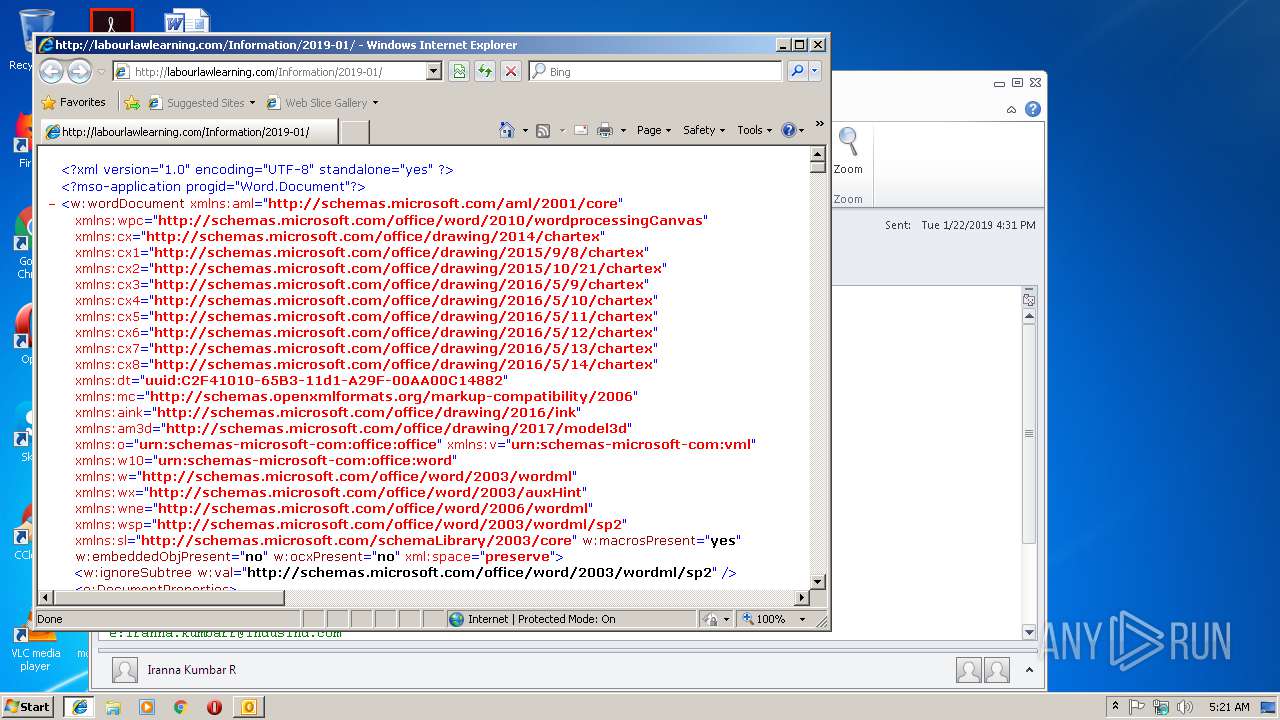
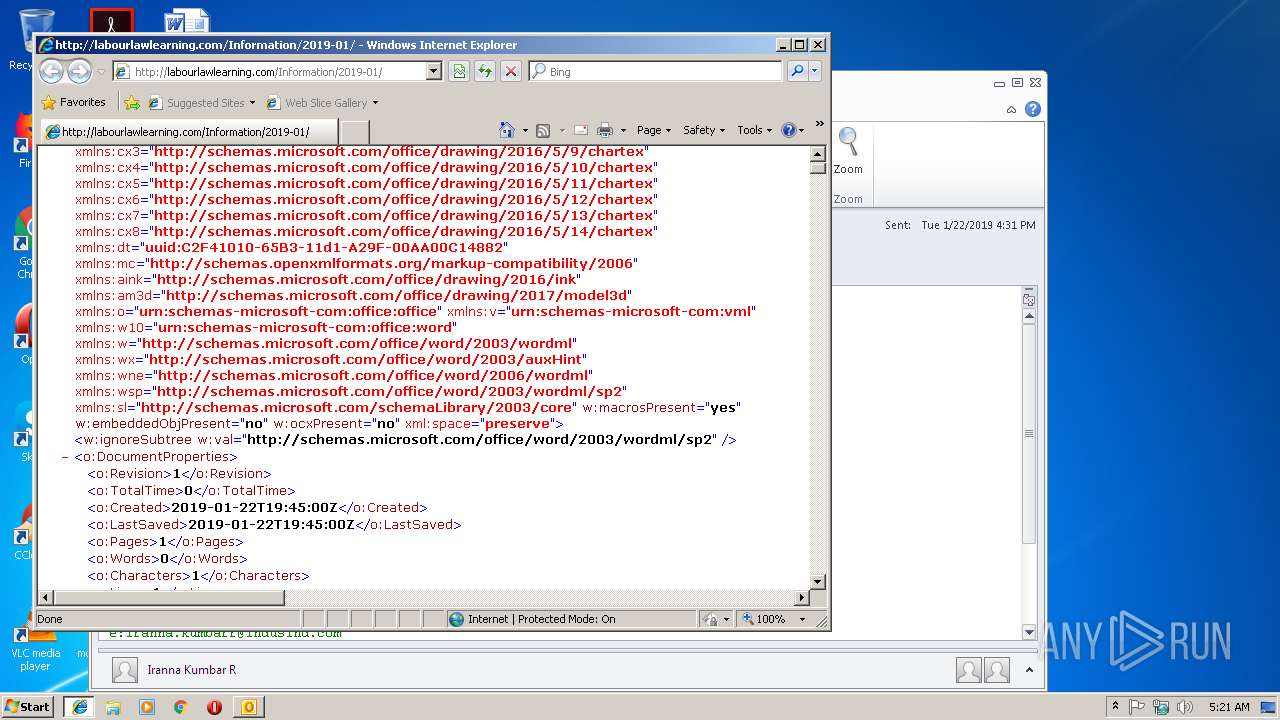
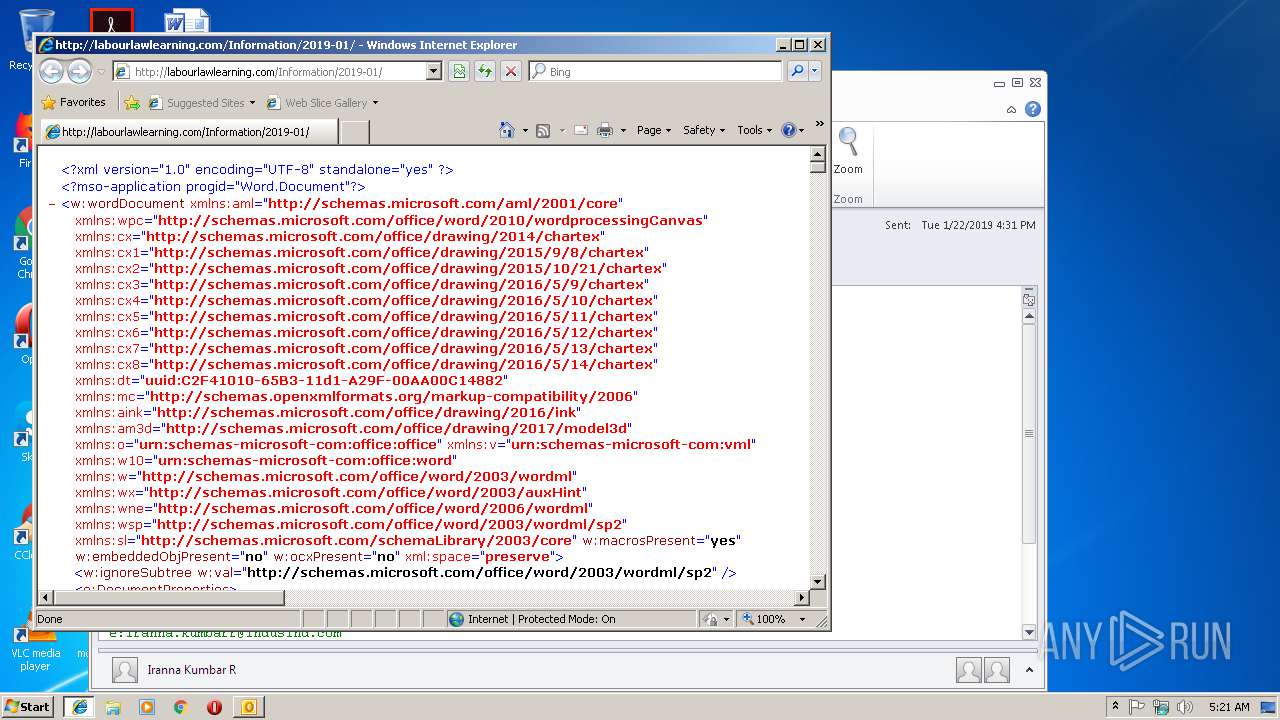
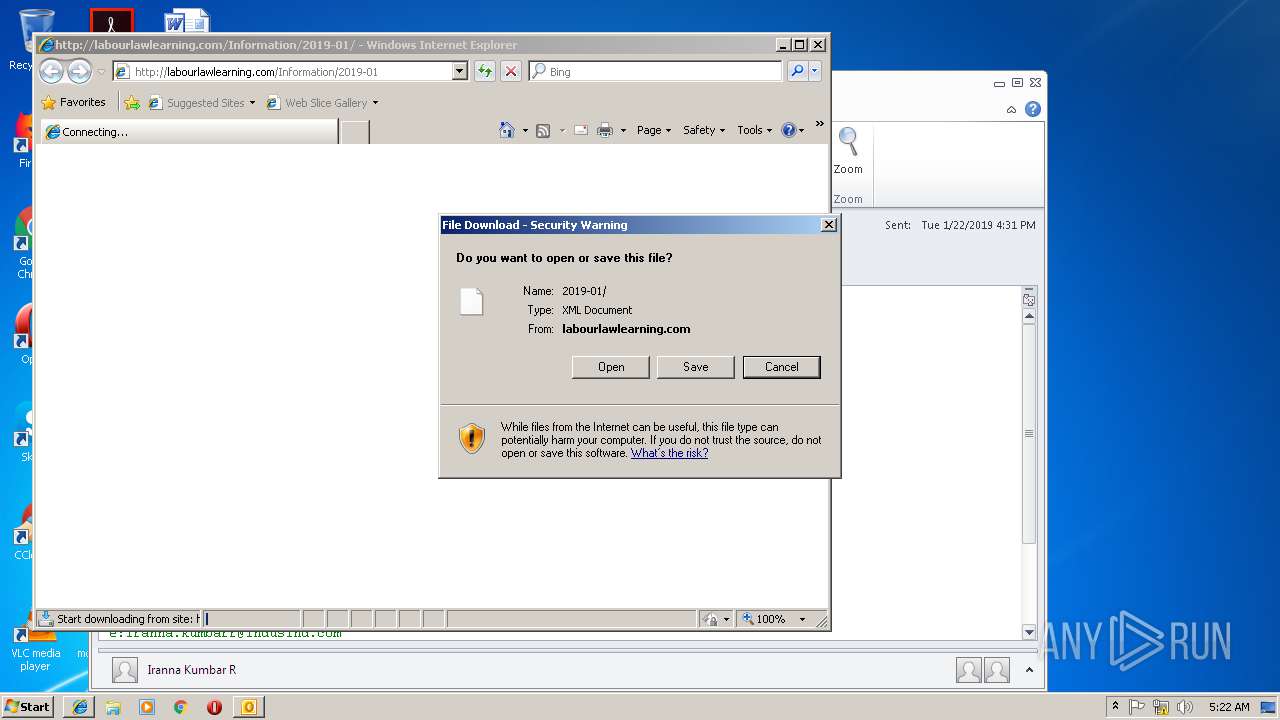
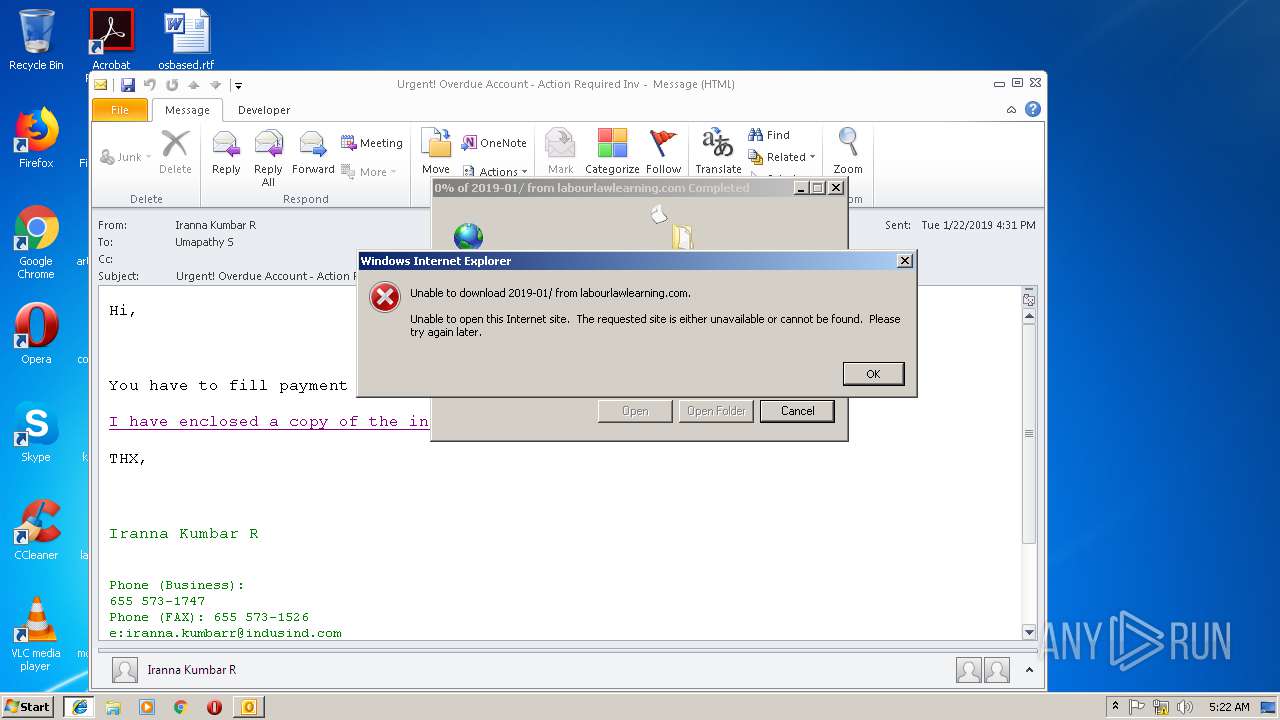
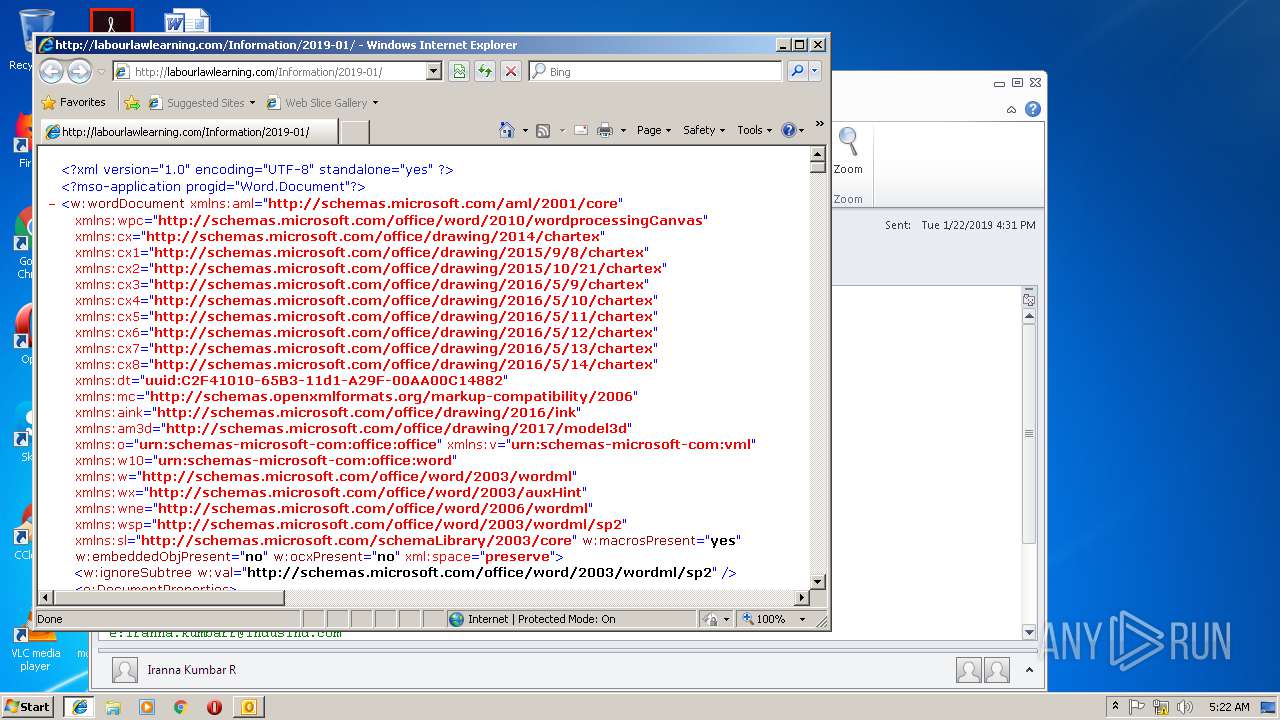
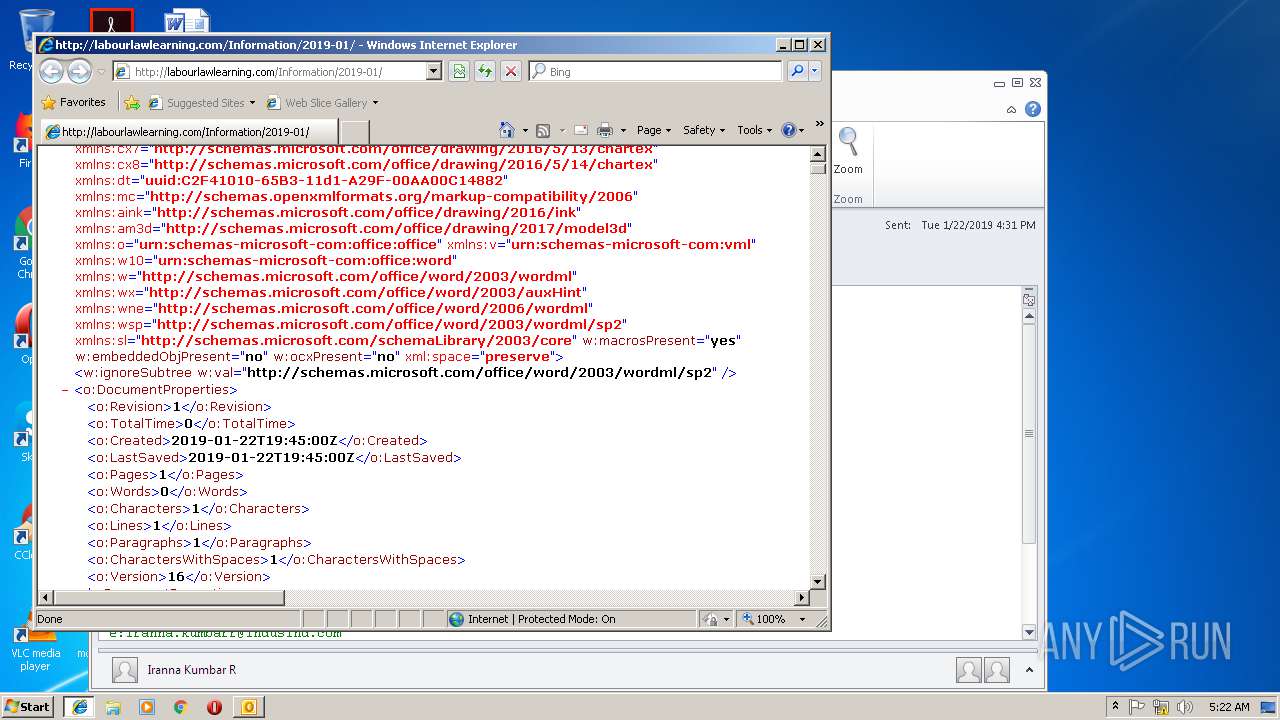
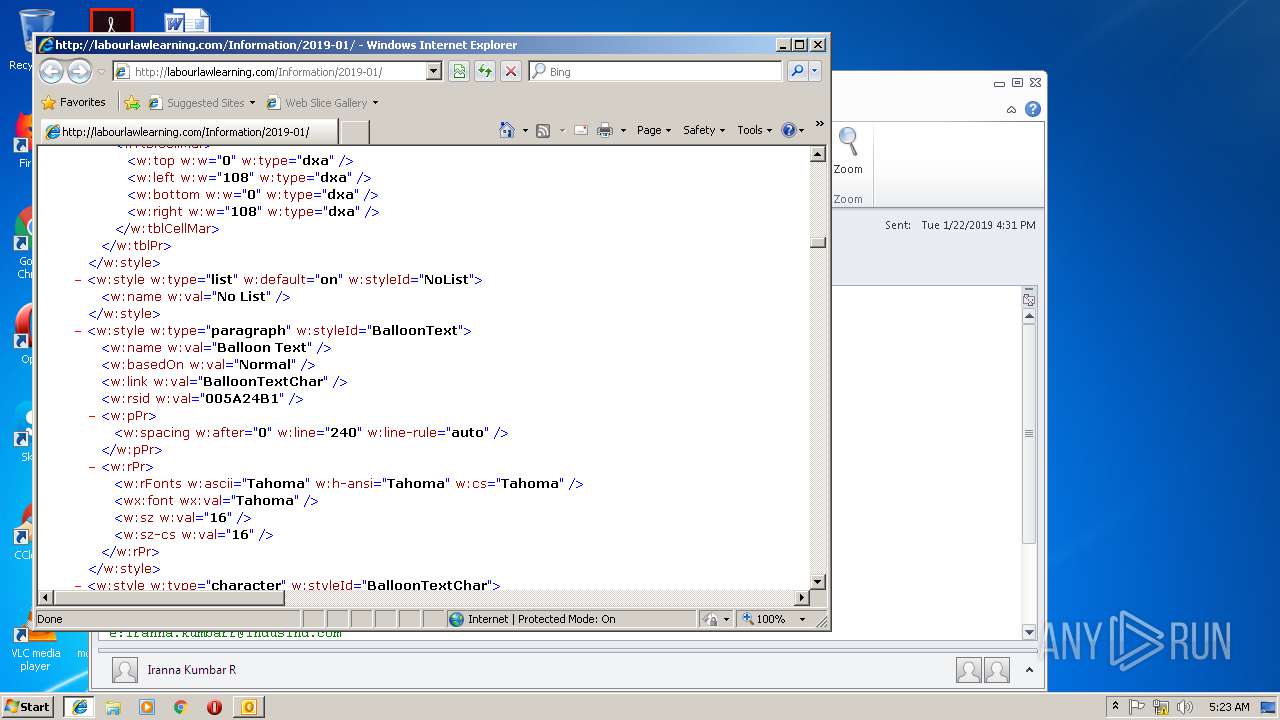
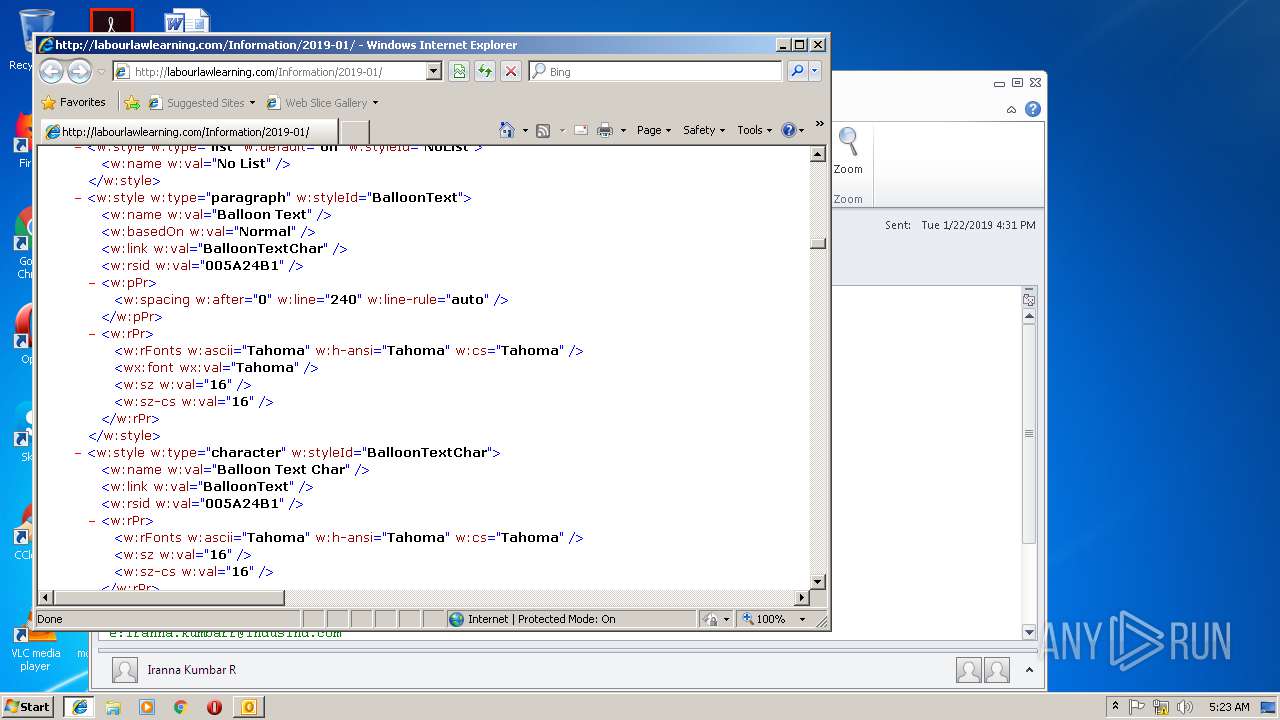
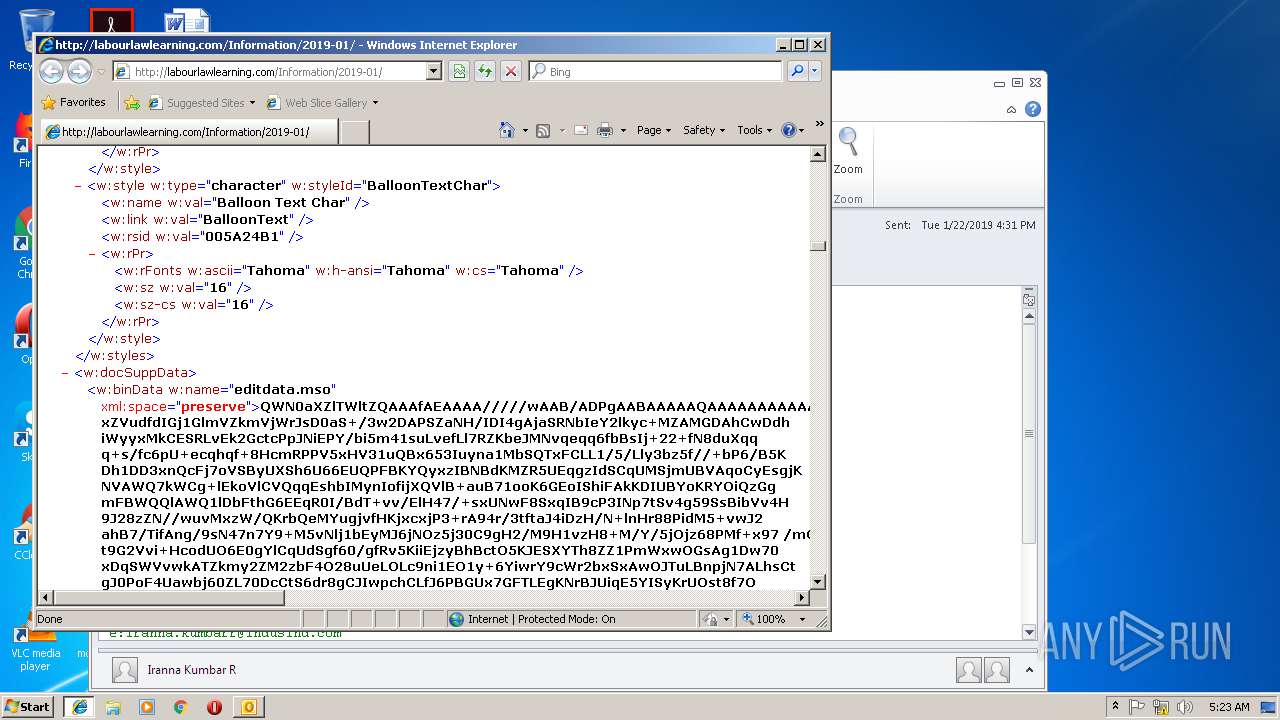
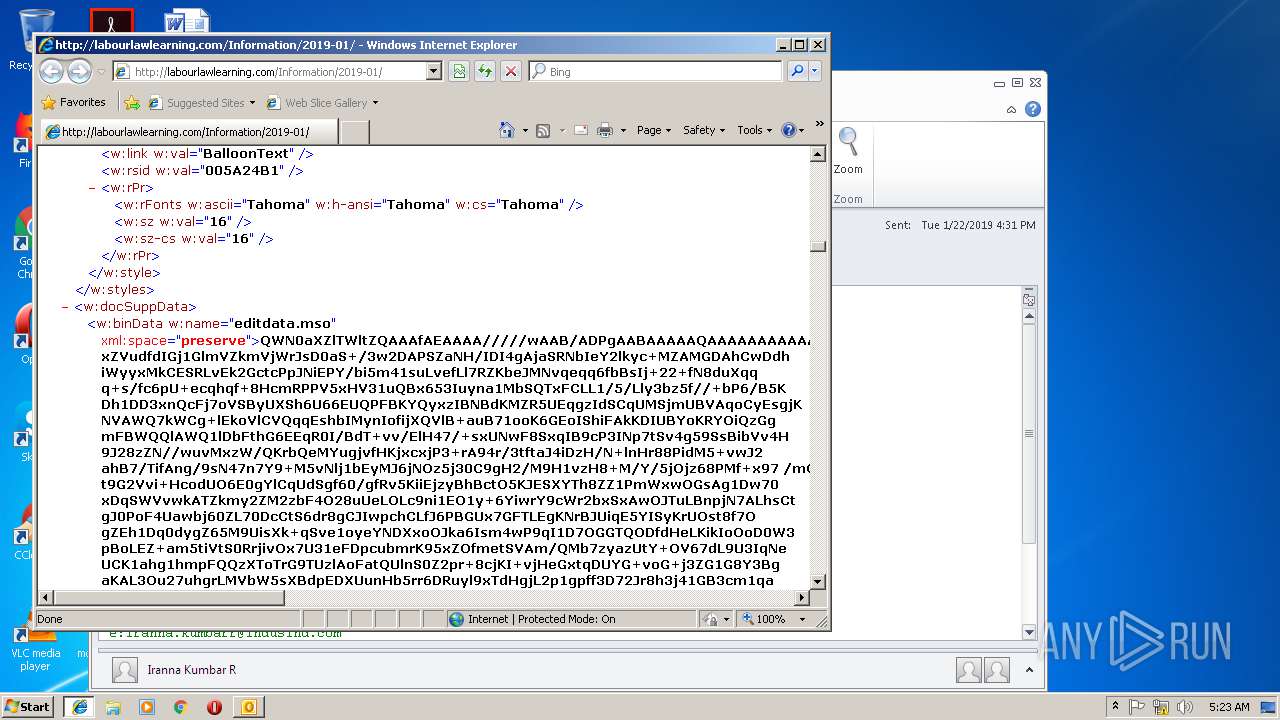
2600 | iexplore.exe | GET | 200 | 87.229.71.152:80 | http://labourlawlearning.com/Information/2019-01/ | HU | xml | 201 Kb | malicious |
3560 | iexplore.exe | GET | 301 | 87.229.71.152:80 | http://labourlawlearning.com/Information/2019-01 | HU | html | 257 b | malicious |
2600 | iexplore.exe | GET | 301 | 87.229.71.152:80 | http://labourlawlearning.com/Information/2019-01 | HU | html | 257 b | malicious |
1224 | iexplore.exe | GET | 301 | 87.229.71.152:80 | http://labourlawlearning.com/Information/2019-01 | HU | html | 257 b | malicious |
2904 | chrome.exe | GET | 200 | 87.229.71.152:80 | http://labourlawlearning.com/Information/2019-01/ | HU | xml | 201 Kb | malicious |
2904 | chrome.exe | GET | 301 | 87.229.71.152:80 | http://labourlawlearning.com/Information/2019-01 | HU | html | 257 b | malicious |
1224 | iexplore.exe | GET | 200 | 87.229.71.152:80 | http://labourlawlearning.com/Information/2019-01/ | HU | xml | 201 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2904 | chrome.exe | 172.217.22.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2904 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3384 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3560 | iexplore.exe | 87.229.71.152:80 | labourlawlearning.com | Deninet KFT | HU | malicious |
2820 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2820 | iexplore.exe | 87.229.71.152:80 | labourlawlearning.com | Deninet KFT | HU | malicious |
1224 | iexplore.exe | 87.229.71.152:80 | labourlawlearning.com | Deninet KFT | HU | malicious |
3652 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2600 | iexplore.exe | 87.229.71.152:80 | labourlawlearning.com | Deninet KFT | HU | malicious |
2904 | chrome.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
labourlawlearning.com |
| malicious |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3560 | iexplore.exe | A Network Trojan was detected | ET TROJAN Possible malicious Office doc hidden in XML file |
1224 | iexplore.exe | A Network Trojan was detected | ET TROJAN Possible malicious Office doc hidden in XML file |
2600 | iexplore.exe | A Network Trojan was detected | ET TROJAN Possible malicious Office doc hidden in XML file |
2904 | chrome.exe | A Network Trojan was detected | ET TROJAN Possible malicious Office doc hidden in XML file |