| File name: | readerdc_en_ka_cra_install.exe |
| Full analysis: | https://app.any.run/tasks/fec17061-8cfc-4f8e-9a0e-792b91a8566f |
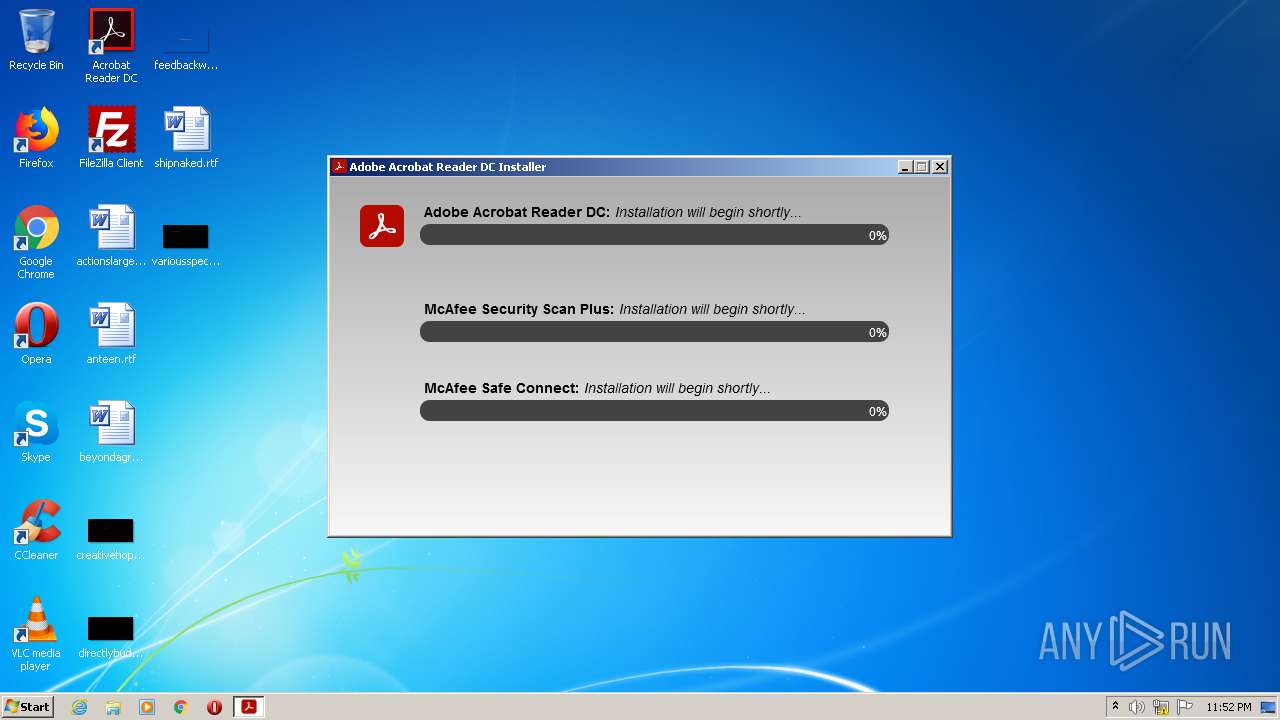
| Verdict: | Malicious activity |
| Analysis date: | August 29, 2020, 22:52:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, PECompact2 compressed |
| MD5: | 00228EC1BCFC2C154B3E3452998EFD4B |
| SHA1: | 4083DF58305132E63379A4B42AA9F3CF38B58D9E |
| SHA256: | DFE86C28752816D2DC59E85068C9D23282E4409752FBB73DA678F22CD868F8D1 |
| SSDEEP: | 24576:K5IUPxzqdjTu1i+VJzZqraM68xJg7c3HSIRn0+XVTe+lPomaQ:AuJTyisZSaM3rg7c3n0S3aG |
MALICIOUS
Application was dropped or rewritten from another process
- gtcheck.exe (PID: 2804)
- gccheck_small.exe (PID: 2216)
- gccheck_small.exe (PID: 3376)
Changes settings of System certificates
- readerdc_en_ka_cra_install.exe (PID: 300)
SUSPICIOUS
Reads internet explorer settings
- readerdc_en_ka_cra_install.exe (PID: 3172)
Reads Internet Cache Settings
- readerdc_en_ka_cra_install.exe (PID: 3172)
Adds / modifies Windows certificates
- readerdc_en_ka_cra_install.exe (PID: 300)
Creates files in the user directory
- readerdc_en_ka_cra_install.exe (PID: 3172)
Application launched itself
- readerdc_en_ka_cra_install.exe (PID: 3172)
Executable content was dropped or overwritten
- readerdc_en_ka_cra_install.exe (PID: 3172)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (v2.x) (54.1) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (38) |
| .exe | | | Win32 Executable (generic) (4.1) |
| .exe | | | Generic Win/DOS Executable (1.8) |
| .exe | | | DOS Executable Generic (1.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:08:07 19:08:16+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 2039808 |
| InitializedDataSize: | 2448896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.542 |
| ProductVersionNumber: | 2.0.0.542 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Adobe Inc |
| FileDescription: | Adobe Download Manager |
| FileVersion: | 2.0.0.542s |
| InternalName: | Adobe Download Manager |
| LegalCopyright: | Copyright 2019 Adobe Inc. All rights reserved. |
| OriginalFileName: | Adobe Download Manager |
| ProductName: | Adobe Download Manager |
| ProductVersion: | 2.0.0.542s |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Aug-2020 17:08:16 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 07-Aug-2020 17:08:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00452000 | 0x00123E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9998 |
.rsrc | 0x00453000 | 0x00006000 | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.81164 |
.reloc | 0x00459000 | 0x00000200 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.216207 |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
gdiplus.dll |
kernel32.dll |
ole32.dll |
Total processes
46
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Users\admin\AppData\Local\Temp\readerdc_en_ka_cra_install.exe" --pipename={59459B46-BB51-46D1-A153-16F63BA3DAAE} --pid=3172 | C:\Users\admin\AppData\Local\Temp\readerdc_en_ka_cra_install.exe | readerdc_en_ka_cra_install.exe | ||||||||||||
User: admin Company: Adobe Inc Integrity Level: HIGH Description: Adobe Download Manager Exit code: 0 Version: 2.0.0.542s Modules
| |||||||||||||||
| 2216 | "C:\Users\admin\AppData\Local\Adobe\F15E6EEF-BF7A-4297-BC33-58EA9E0E1E3F\gccheck_small.exe" -canOfferReactivation -shellMode:standard -brandCode:ARRC | C:\Users\admin\AppData\Local\Adobe\F15E6EEF-BF7A-4297-BC33-58EA9E0E1E3F\gccheck_small.exe | — | readerdc_en_ka_cra_install.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Pre-Install Exit code: 2 Version: 1.0 Modules
| |||||||||||||||
| 2804 | "C:\Users\admin\AppData\Local\Adobe\F15E6EEF-BF7A-4297-BC33-58EA9E0E1E3F\gtcheck.exe" | C:\Users\admin\AppData\Local\Adobe\F15E6EEF-BF7A-4297-BC33-58EA9E0E1E3F\gtcheck.exe | — | readerdc_en_ka_cra_install.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3172 | "C:\Users\admin\AppData\Local\Temp\readerdc_en_ka_cra_install.exe" | C:\Users\admin\AppData\Local\Temp\readerdc_en_ka_cra_install.exe | explorer.exe | ||||||||||||
User: admin Company: Adobe Inc Integrity Level: MEDIUM Description: Adobe Download Manager Exit code: 0 Version: 2.0.0.542s Modules
| |||||||||||||||
| 3376 | "C:\Users\admin\AppData\Local\Adobe\F15E6EEF-BF7A-4297-BC33-58EA9E0E1E3F\gccheck_small.exe" -chromeEligibilityTest -shellMode:standard | C:\Users\admin\AppData\Local\Adobe\F15E6EEF-BF7A-4297-BC33-58EA9E0E1E3F\gccheck_small.exe | — | readerdc_en_ka_cra_install.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Pre-Install Exit code: 2 Version: 1.0 Modules
| |||||||||||||||
Total events
494
Read events
460
Write events
32
Delete events
2
Modification events
| (PID) Process: | (3172) readerdc_en_ka_cra_install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3172) readerdc_en_ka_cra_install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3172) readerdc_en_ka_cra_install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3172) readerdc_en_ka_cra_install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3172) readerdc_en_ka_cra_install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (300) readerdc_en_ka_cra_install.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\139\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (300) readerdc_en_ka_cra_install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43 |
| Operation: | write | Name: | Blob |
Value: 04000000010000001000000087CE0B7B2A0E4900E158719B37A893720F00000001000000140000006DCA5BD00DCF1C0F327059D374B29CA6E3C50AA60300000001000000140000000563B8630D62D75ABBC8AB1E4BDFB5A899B24D431D00000001000000100000004F5F106930398D09107B40C3C7CA8F1C0B000000010000001200000044006900670069004300650072007400000014000000010000001400000045EBA2AFF492CB82312D518BA7A7219DF36DC80F6200000001000000200000003E9099B5015E8F486C00BCEA9D111EE721FABA355A89BCF1DF69561E3DC6325C5300000001000000230000003021301F06096086480186FD6C020130123010060A2B0601040182373C0101030200C0090000000100000034000000303206082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030306082B06010505070308190000000100000010000000749966CECC95C1874194CA7203F9B6202000000001000000BB030000308203B73082029FA00302010202100CE7E0E517D846FE8FE560FC1BF03039300D06092A864886F70D01010505003065310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312430220603550403131B4469676943657274204173737572656420494420526F6F74204341301E170D3036313131303030303030305A170D3331313131303030303030305A3065310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312430220603550403131B4469676943657274204173737572656420494420526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100AD0E15CEE443805CB187F3B760F97112A5AEDC269488AAF4CEF520392858600CF880DAA9159532613CB5B128848A8ADC9F0A0C83177A8F90AC8AE779535C31842AF60F98323676CCDEDD3CA8A2EF6AFB21F25261DF9F20D71FE2B1D9FE1864D2125B5FF9581835BC47CDA136F96B7FD4B0383EC11BC38C33D9D82F18FE280FB3A783D6C36E44C061359616FE599C8B766DD7F1A24B0D2BFF0B72DA9E60D08E9035C678558720A1CFE56D0AC8497C3198336C22E987D0325AA2BA138211ED39179D993A72A1E6FAA4D9D5173175AE857D22AE3F014686F62879C8B1DAE45717C47E1C0EB0B492A656B3BDB297EDAAA7F0B7C5A83F9516D0FFA196EB085F18774F0203010001A3633061300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E0416041445EBA2AFF492CB82312D518BA7A7219DF36DC80F301F0603551D2304183016801445EBA2AFF492CB82312D518BA7A7219DF36DC80F300D06092A864886F70D01010505000382010100A20EBCDFE2EDF0E372737A6494BFF77266D832E4427562AE87EBF2D5D9DE56B39FCCCE1428B90D97605C124C58E4D33D834945589735691AA847EA56C679AB12D8678184DF7F093C94E6B8262C20BD3DB32889F75FFF22E297841FE965EF87E0DFC16749B35DEBB2092AEB26ED78BE7D3F2BF3B726356D5F8901B6495B9F01059BAB3D25C1CCB67FC2F16F86C6FA6468EB812D94EB42B7FA8C1EDD62F1BE5067B76CBDF3F11F6B0C3607167F377CA95B6D7AF112466083D72704BE4BCE97BEC3672A6811DF80E70C3366BF130D146EF37F1F63101EFA8D1B256D6C8FA5B76101B1D2A326A110719DADE2C3F9C39951B72B0708CE2EE650B2A7FA0A452FA2F0F2 | |||
| (PID) Process: | (300) readerdc_en_ka_cra_install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\5FB7EE0633E259DBAD0C4C9AE6D38F1A61C7DC25 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000D474DE575C39B2D39C8583C5C065498A0F0000000100000014000000E35EF08D884F0A0ADE2F75E96301CE6230F213A80300000001000000140000005FB7EE0633E259DBAD0C4C9AE6D38F1A61C7DC251D00000001000000100000008F76B981D528AD4770088245E2031B630B0000000100000012000000440069006700690043006500720074000000140000000100000014000000B13EC36903F8BF4701D498261A0802EF63642BC36200000001000000200000007431E5F4C3C1CE4690774F0B61E05440883BA9A01ED00BA6ABD7806ED3B118CF5300000001000000230000003021301F06096086480186FD6C020130123010060A2B0601040182373C0101030200C0090000000100000034000000303206082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030306082B06010505070308190000000100000010000000BA4F3972E7AED9DCCDC210DB59DA13C92000000001000000C9030000308203C5308202ADA003020102021002AC5C266A0B409B8F0B79F2AE462577300D06092A864886F70D0101050500306C310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312B30290603550403132244696769436572742048696768204173737572616E636520455620526F6F74204341301E170D3036313131303030303030305A170D3331313131303030303030305A306C310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312B30290603550403132244696769436572742048696768204173737572616E636520455620526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100C6CCE573E6FBD4BBE52D2D32A6DFE5813FC9CD2549B6712AC3D5943467A20A1CB05F69A640B1C4B7B28FD098A4A941593AD3DC94D63CDB7438A44ACC4D2582F74AA5531238EEF3496D71917E63B6ABA65FC3A484F84F6251BEF8C5ECDB3892E306E508910CC4284155FBCB5A89157E71E835BF4D72093DBE3A38505B77311B8DB3C724459AA7AC6D00145A04B7BA13EB510A984141224E656187814150A6795C89DE194A57D52EE65D1C532C7E98CD1A0616A46873D03404135CA171D35A7C55DB5E64E13787305604E511B4298012F1793988A202117C2766B788B778F2CA0AA838AB0A64C2BF665D9584C1A1251E875D1A500B2012CC41BB6E0B5138B84BCB0203010001A3633061300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E04160414B13EC36903F8BF4701D498261A0802EF63642BC3301F0603551D23041830168014B13EC36903F8BF4701D498261A0802EF63642BC3300D06092A864886F70D010105050003820101001C1A0697DCD79C9F3C886606085721DB2147F82A67AABF183276401057C18AF37AD911658E35FA9EFC45B59ED94C314BB891E8432C8EB378CEDBE3537971D6E5219401DA55879A2464F68A66CCDE9C37CDA834B1699B23C89E78222B7043E35547316119EF58C5852F4E30F6A0311623C8E7E2651633CBBF1A1BA03DF8CA5E8B318B6008892D0C065C52B7C4F90A98D1155F9F12BE7C366338BD44A47FE4262B0AC497690DE98CE2C01057B8C876129155F24869D8BC2A025B0F44D42031DBF4BA70265D90609EBC4B17092FB4CB1E4368C90727C1D25CF7EA21B968129C3C9CBF9EFC805C9B63CDEC47AA252767A037F300827D54D7A9F8E92E13A377E81F4A | |||
| (PID) Process: | (3172) readerdc_en_ka_cra_install.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\139\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2804) gtcheck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Google Toolbar |
| Operation: | write | Name: | test |
Value: test | |||
Executable files
4
Suspicious files
0
Text files
48
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3172 | readerdc_en_ka_cra_install.exe | C:\Users\admin\AppData\Local\Temp\Adobe_ADMLogs\Adobe_ADM.log | text | |
MD5:— | SHA256:— | |||
| 3172 | readerdc_en_ka_cra_install.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\160[1] | html | |
MD5:— | SHA256:— | |||
| 3172 | readerdc_en_ka_cra_install.exe | C:\Users\admin\AppData\Local\Adobe\F15E6EEF-BF7A-4297-BC33-58EA9E0E1E3F\warning_icon_200.png | image | |
MD5:7395444416AB7A3D5A196E2F46269AFF | SHA256:59BC5272A4A2940EF7AAD07C960200135DD9909B3150C3322F0E62C1E40709B6 | |||
| 3172 | readerdc_en_ka_cra_install.exe | C:\Users\admin\AppData\Local\Adobe\F15E6EEF-BF7A-4297-BC33-58EA9E0E1E3F\progressbar_blue_active_100.png | image | |
MD5:BB94A177F10BF764D11F94D24A5DB5AA | SHA256:CAAFEA31074BA909EC57C9DCDD1B1C0256E5626939CC768B8A041FE42762E230 | |||
| 3172 | readerdc_en_ka_cra_install.exe | C:\Users\admin\AppData\Local\Adobe\F15E6EEF-BF7A-4297-BC33-58EA9E0E1E3F\progressbar_blue_active_200.png | image | |
MD5:0F78C8C46DAD3F68D060B406AA0BBF1F | SHA256:C08F7720960B2E21B1F8F106D80BCB1AF7C11433E3B35D7AE2994254A2A2583C | |||
| 3172 | readerdc_en_ka_cra_install.exe | C:\Users\admin\AppData\Local\Adobe\F15E6EEF-BF7A-4297-BC33-58EA9E0E1E3F\status_icon_check_150.png | image | |
MD5:AA02AB840568AD99107CDECE6621C3AC | SHA256:8743B4FEBE9F3C99E1C5B647255E6367DDAC8580E1388FEAF78E0BC84FBB1776 | |||
| 3172 | readerdc_en_ka_cra_install.exe | C:\Users\admin\AppData\Local\Adobe\F15E6EEF-BF7A-4297-BC33-58EA9E0E1E3F\progressbar_blue_active_125.png | image | |
MD5:5E3F8861E897F1D865A1DCA095AFB15A | SHA256:A2C424618DE66C97F91833FE2EDB4BB05E03561E60AC40405771D2DEBB8CCB41 | |||
| 3172 | readerdc_en_ka_cra_install.exe | C:\Users\admin\AppData\Local\Adobe\F15E6EEF-BF7A-4297-BC33-58EA9E0E1E3F\status_icon_caution_100.png | image | |
MD5:784ABEA138D9F1E5A1026162AF5BF2CD | SHA256:5C7B6B5456CAABC9D5A928AC892D9903836693960517C4E534A5DE1ACD6AE428 | |||
| 3172 | readerdc_en_ka_cra_install.exe | C:\Users\admin\AppData\Local\Adobe\F15E6EEF-BF7A-4297-BC33-58EA9E0E1E3F\status_icon_caution_150.png | image | |
MD5:CA3872EAE64C5BFD8D41198990B11950 | SHA256:3438623C461F8F141976A931D3C00F6877D07CF4A8B534AF1EF9FDFE8B0C6174 | |||
| 3172 | readerdc_en_ka_cra_install.exe | C:\Users\admin\AppData\Local\Adobe\F15E6EEF-BF7A-4297-BC33-58EA9E0E1E3F\status_icon_caution_125.png | image | |
MD5:4A2BF8C96F910B1B2AE63A9F4A0D4B8F | SHA256:0CB2F4EE1C451A8825EB8EDB45858B28345F73423C7A7AEF4168C46F7E3638BF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
15
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3172 | readerdc_en_ka_cra_install.exe | GET | 302 | 15.236.9.100:80 | http://stats.adobe.com/b/ss/adbacdcprod,adbadobenonacdcprod/1/H.25.4/s14022221564679?AQB=1&ndh=1&t=29%2F7%2F2020%2023%3A52%3A54%206%20-60&ce=UTF-8&ns=adobecorp&g=res%3A%2F%2FC%3A%5CUsers%5Cadmin%5CAppData%5CLocal%5CTemp%5Creaderdc_en_ka_cra_install.exe%2F160&c.&digitalData.&page.&pageInfo.&pageName=get.adobe.com%3Areader%3Ainstaller&language=en-US&template=ADM&siteSection=ADM&.pageInfo&.page&getAdobe.&productFamily=ACDC%20Downloads&platformEnvironment=ACDC_Reader&eventActionList=ADM%20Launched%7C&.getAdobe&adobe.&experienceCloud.&visitorService.&info.&version=VisitorAPI%20Not%20Present&.info&.visitorService&.experienceCloud&.adobe&.digitalData&.c&products=%3BReader%3B%3B&v18=New&v22=Saturday%20-%204%3A30PM&s=1280x720&c=32&j=1.5&v=Y&k=N&bw=620&bh=358&ct=lan&hp=N&AQE=1 | US | — | — | whitelisted |
3172 | readerdc_en_ka_cra_install.exe | GET | 200 | 15.236.9.100:80 | http://stats.adobe.com/b/ss/adbacdcprod,adbadobenonacdcprod/1/H.25.4/s14022221564679?AQB=1&pccr=true&vidn=2FA56E2385158690-400008E95E2E75F6&ndh=1&t=29%2F7%2F2020%2023%3A52%3A54%206%20-60&ce=UTF-8&ns=adobecorp&g=res%3A%2F%2FC%3A%5CUsers%5Cadmin%5CAppData%5CLocal%5CTemp%5Creaderdc_en_ka_cra_install.exe%2F160&c.&digitalData.&page.&pageInfo.&pageName=get.adobe.com%3Areader%3Ainstaller&language=en-US&template=ADM&siteSection=ADM&.pageInfo&.page&getAdobe.&productFamily=ACDC%20Downloads&platformEnvironment=ACDC_Reader&eventActionList=ADM%20Launched%7C&.getAdobe&adobe.&experienceCloud.&visitorService.&info.&version=VisitorAPI%20Not%20Present&.info&.visitorService&.experienceCloud&.adobe&.digitalData&.c&products=%3BReader%3B%3B&v18=New&v22=Saturday%20-%204%3A30PM&s=1280x720&c=32&j=1.5&v=Y&k=N&bw=620&bh=358&ct=lan&hp=N&AQE=1 | US | image | 43 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3172 | readerdc_en_ka_cra_install.exe | 193.104.215.66:443 | get.adobe.com | Level 3 Communications, Inc. | — | malicious |
3172 | readerdc_en_ka_cra_install.exe | 2.18.233.74:443 | dlmping2.adobe.com | Akamai International B.V. | — | whitelisted |
— | — | 2.18.233.74:443 | dlmping2.adobe.com | Akamai International B.V. | — | whitelisted |
— | — | 15.236.9.100:80 | stats.adobe.com | Hewlett-Packard Company | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
get.adobe.com |
| whitelisted |
dlmping2.adobe.com |
| whitelisted |
stats.adobe.com |
| whitelisted |
platformdl.adobe.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |