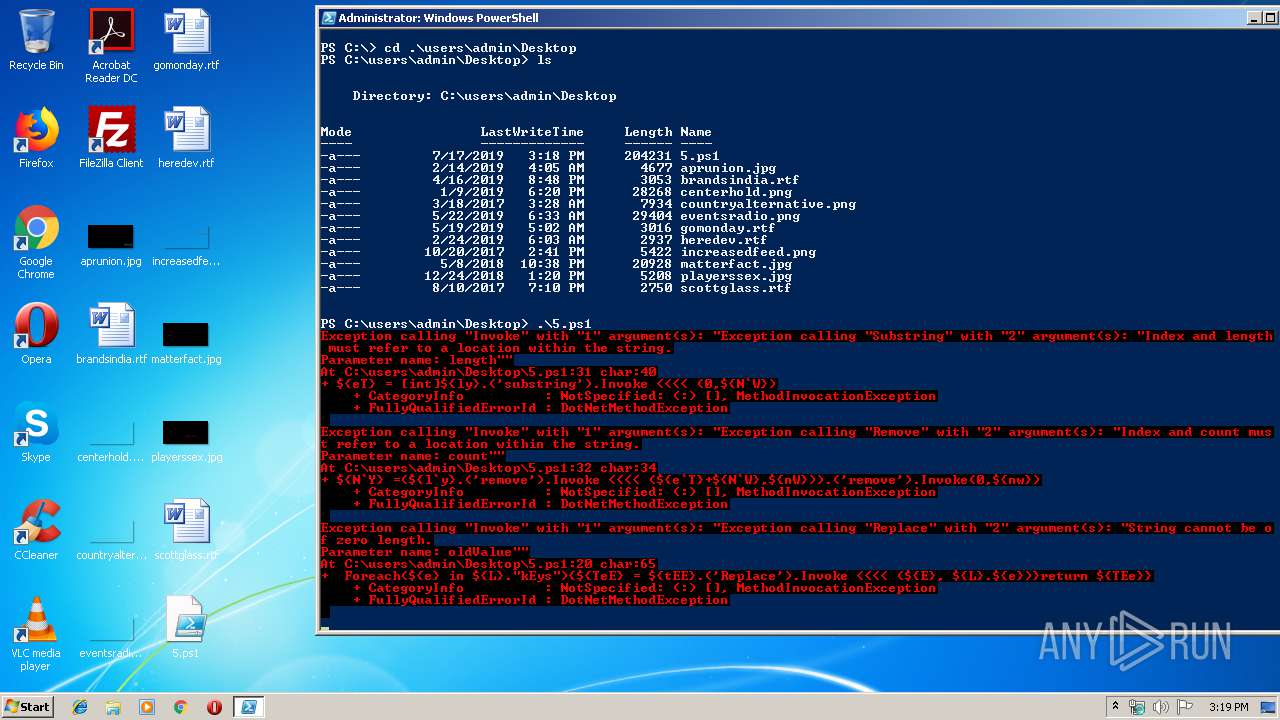
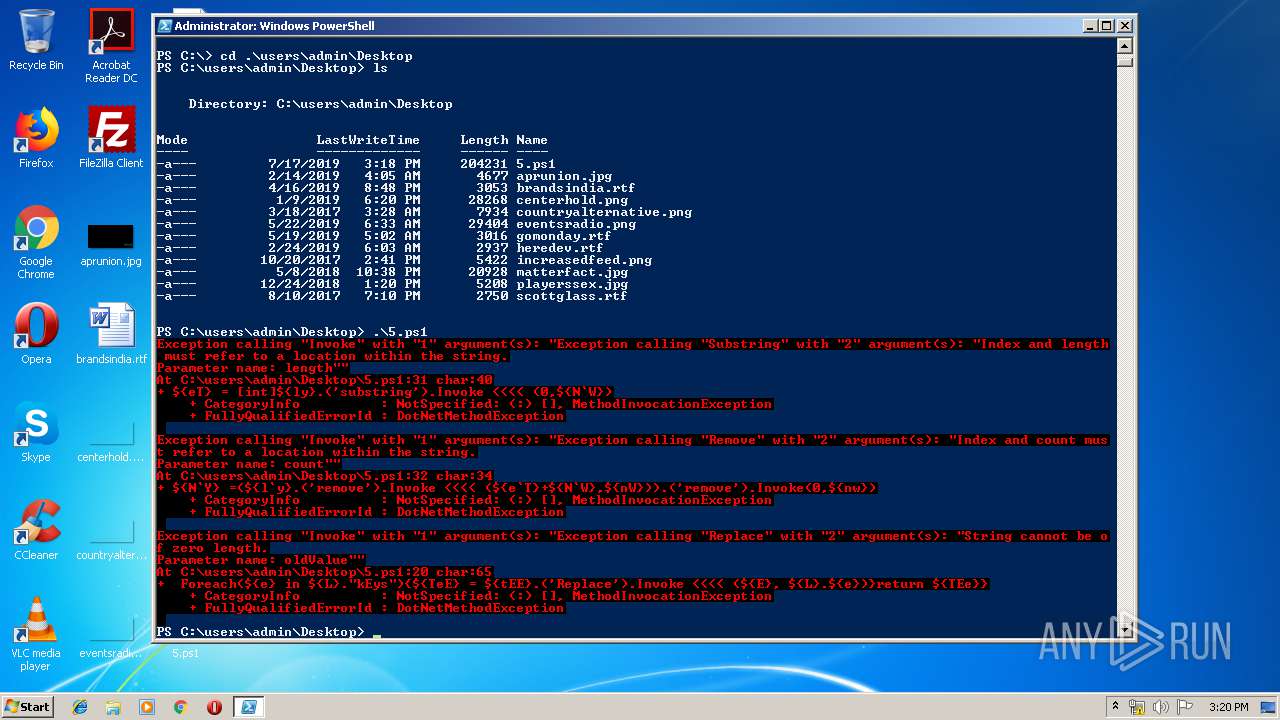
| File name: | 5.ps1 |
| Full analysis: | https://app.any.run/tasks/eb640642-203a-42da-9ec3-683e3c404ff4 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 14:18:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 08A4278642F937D61B02A9EF60C83078 |
| SHA1: | F2084F693424057327330E69F4D1E599C56268CB |
| SHA256: | DFE7255A4A1B1F5F226EE7BCE639867B4E7645553968B6DB42D0C8612D8A12A6 |
| SSDEEP: | 3072:FMgY8xwcxSobO+gK6teENkvhKxrVmhJKmIGbE4p/0+X/FdqWL3Eh/+g:FMgY11QO8EGv5bbEV+9dZL3mmg |
MALICIOUS
Changes settings of System certificates
- powershell.exe (PID: 2096)
SUSPICIOUS
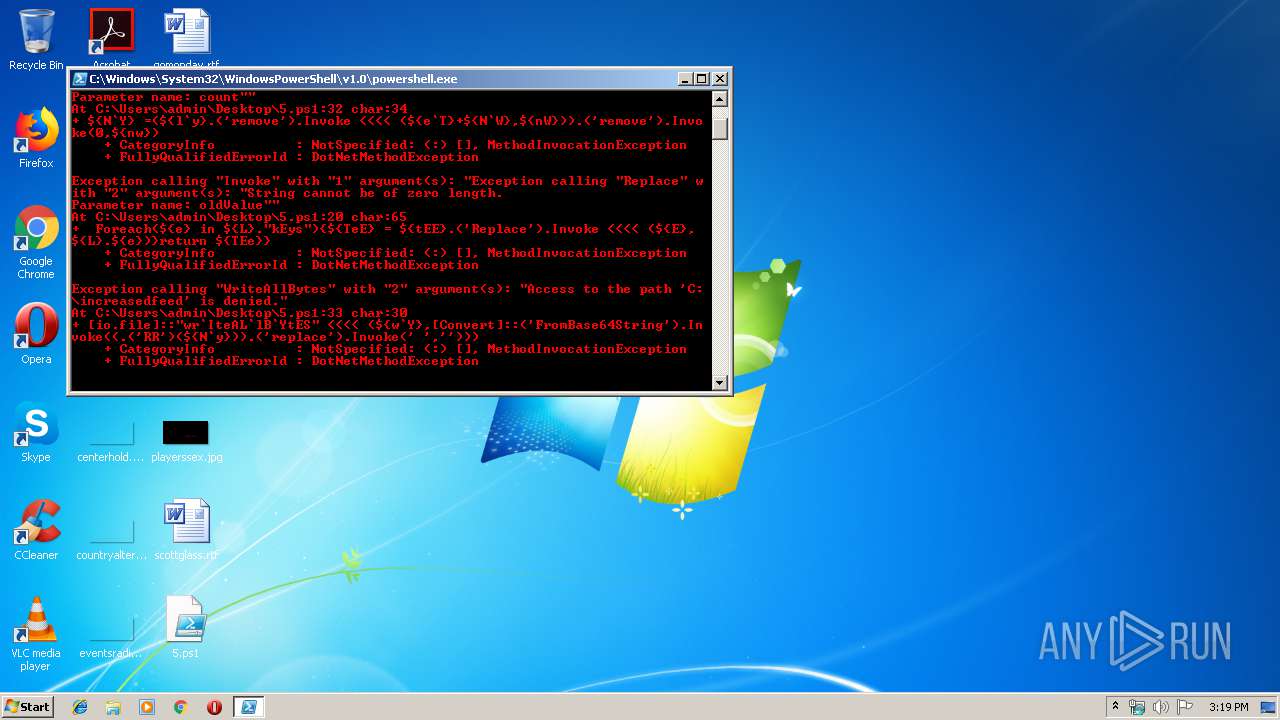
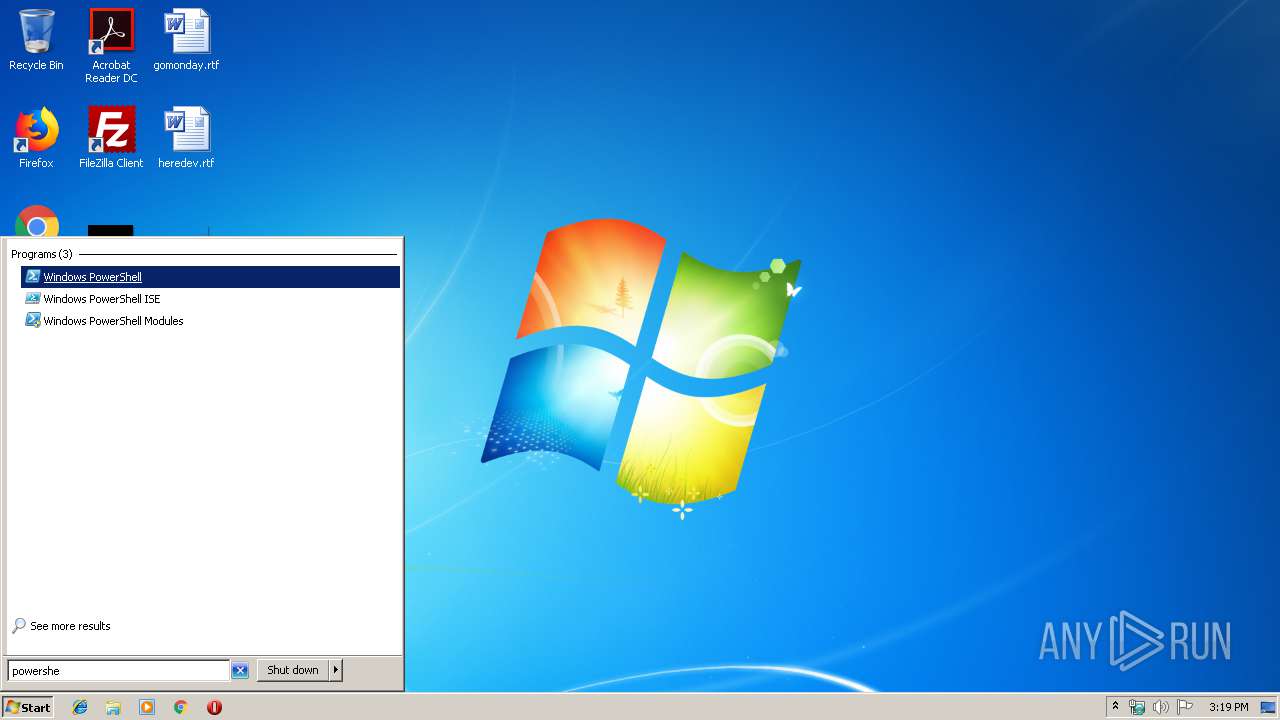
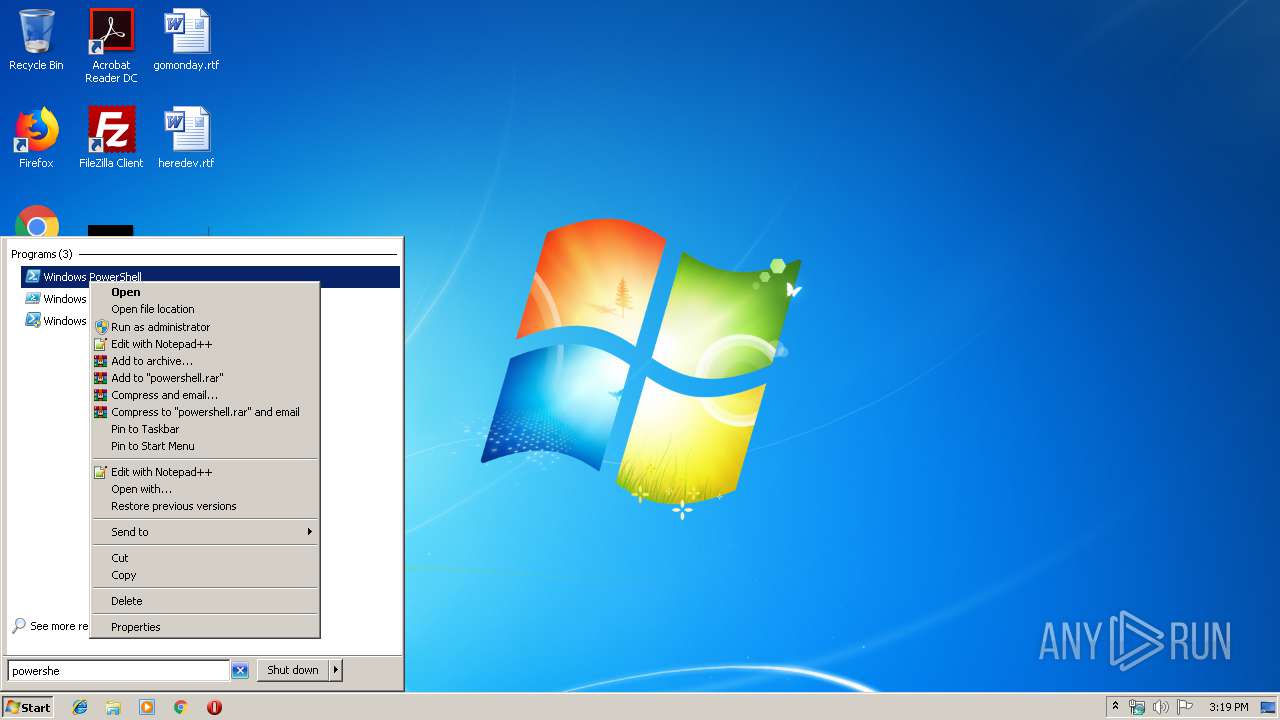
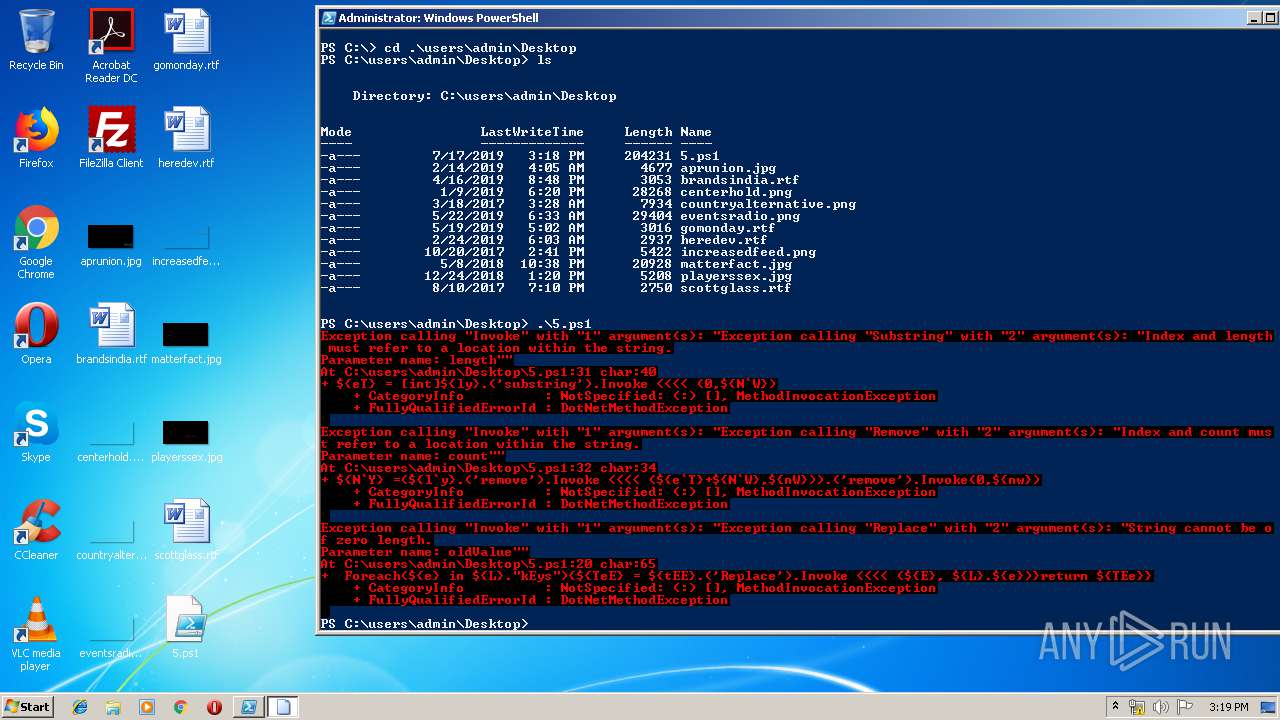
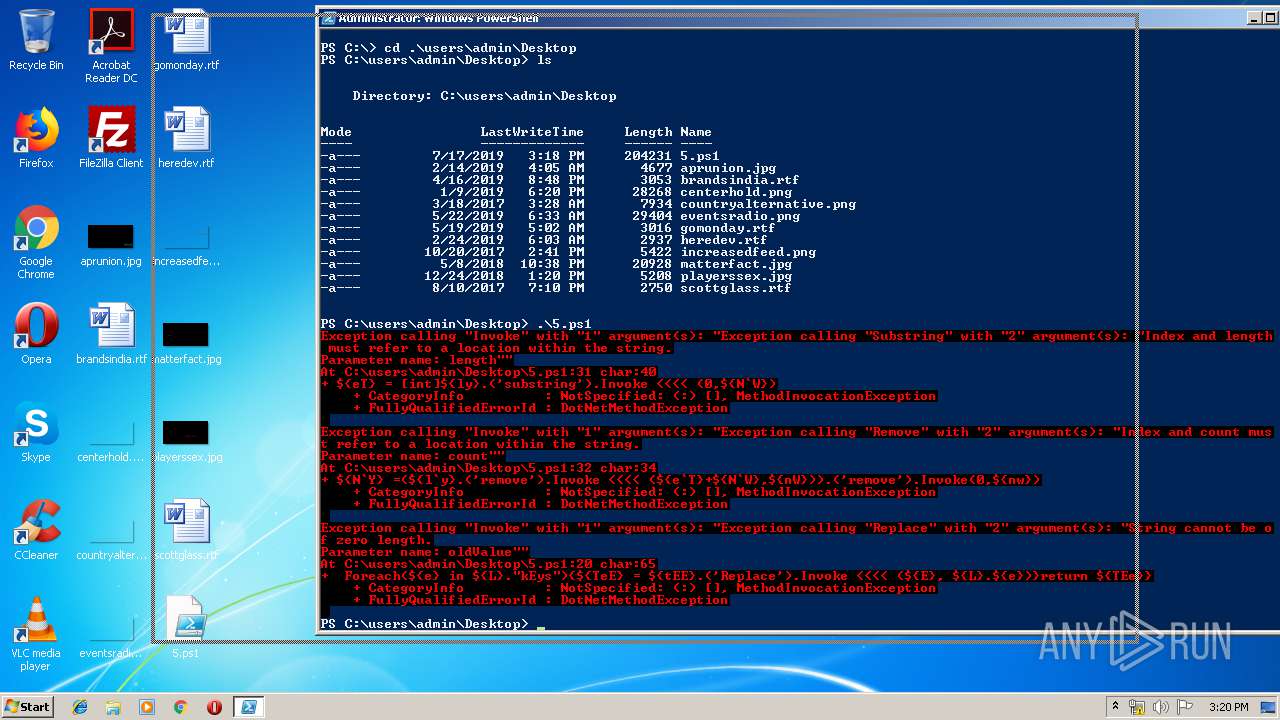
PowerShell script executed
- powershell.exe (PID: 3620)
- powershell.exe (PID: 2096)
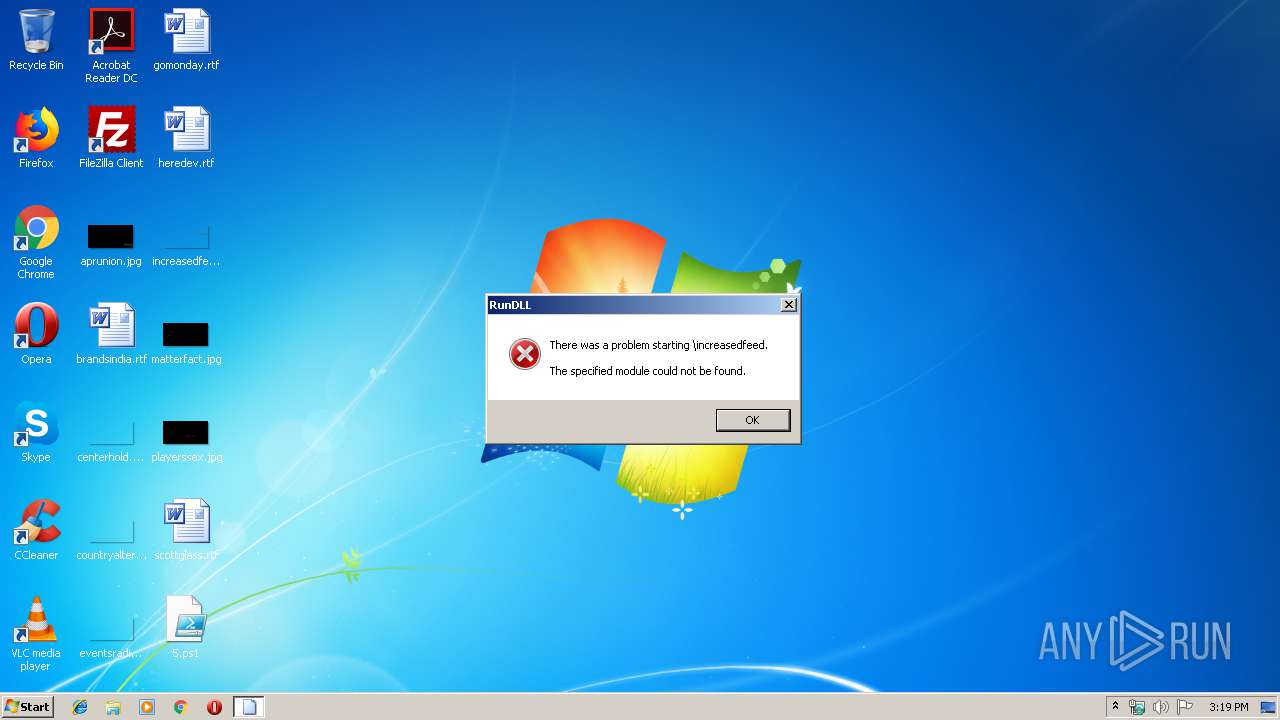
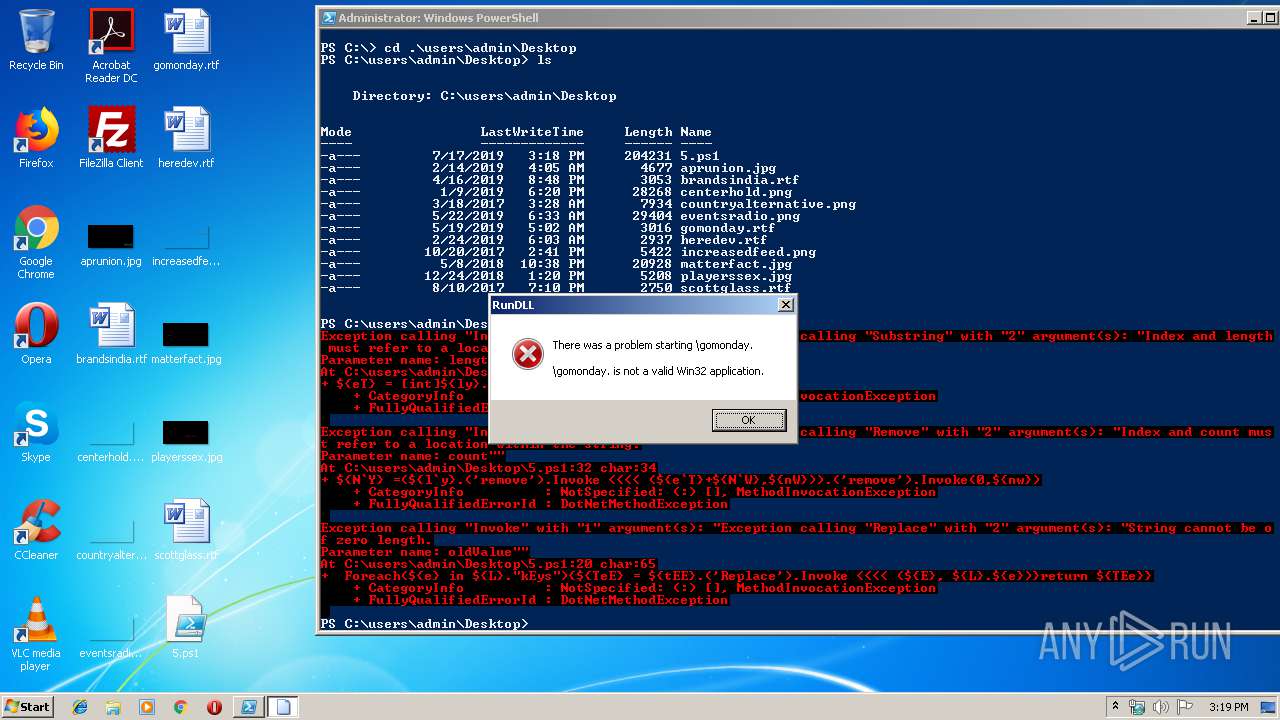
Uses RUNDLL32.EXE to load library
- powershell.exe (PID: 3620)
- powershell.exe (PID: 2096)
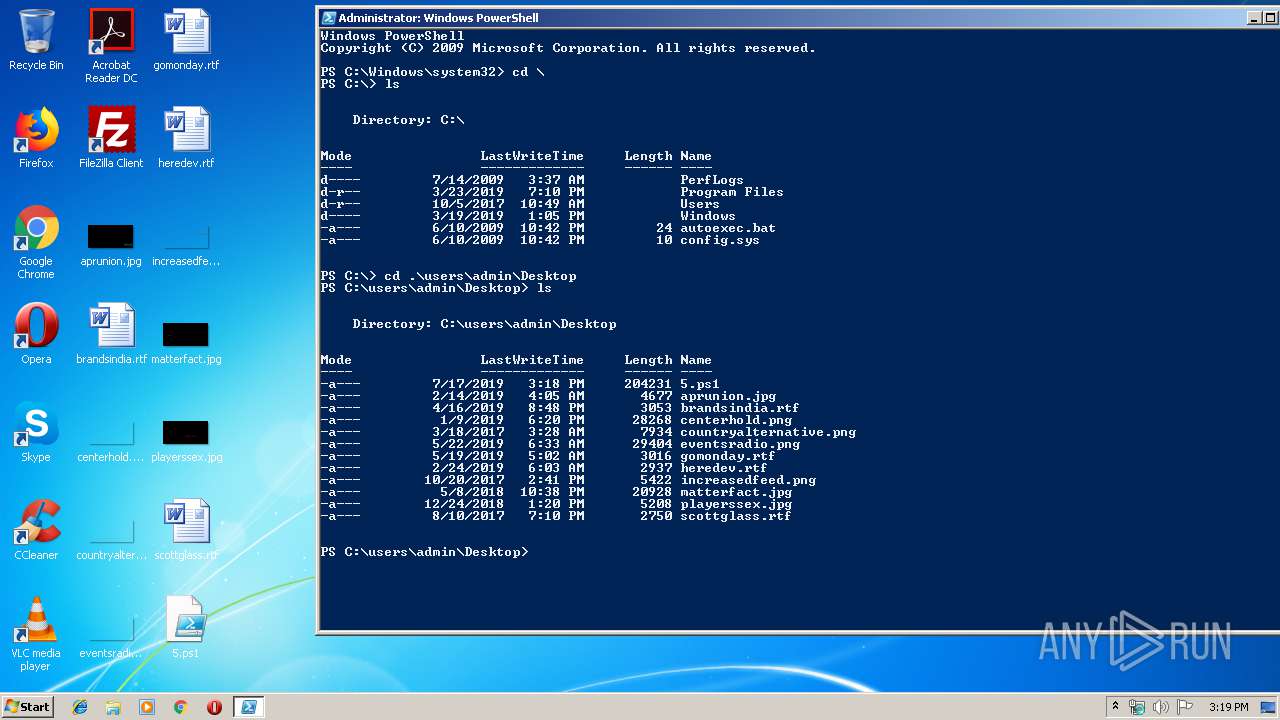
Creates files in the user directory
- powershell.exe (PID: 3620)
- powershell.exe (PID: 2096)
Adds / modifies Windows certificates
- powershell.exe (PID: 2096)
INFO
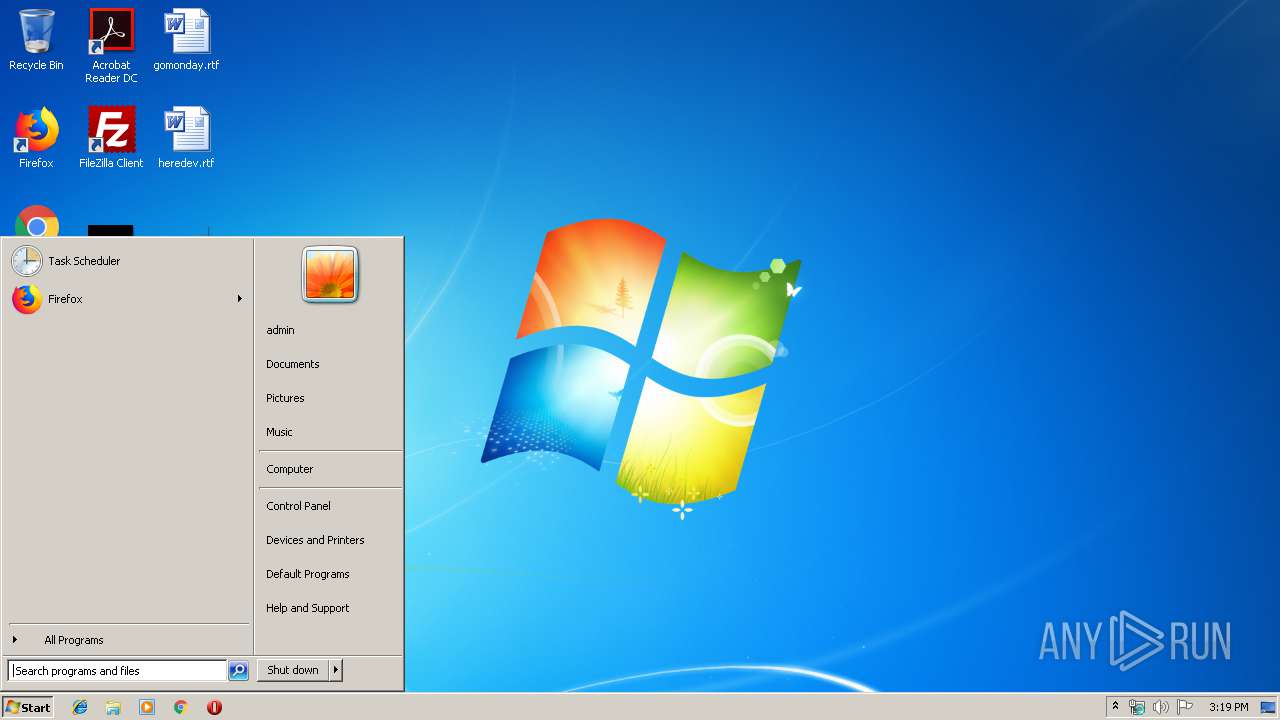
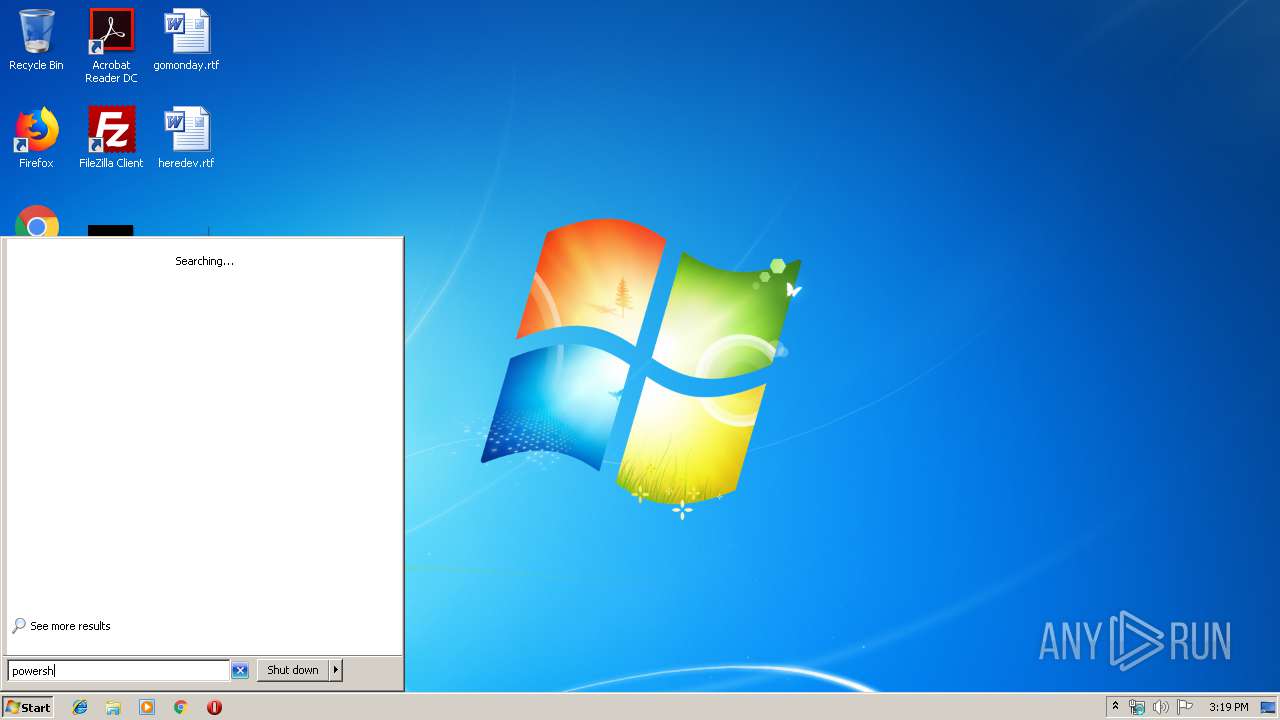
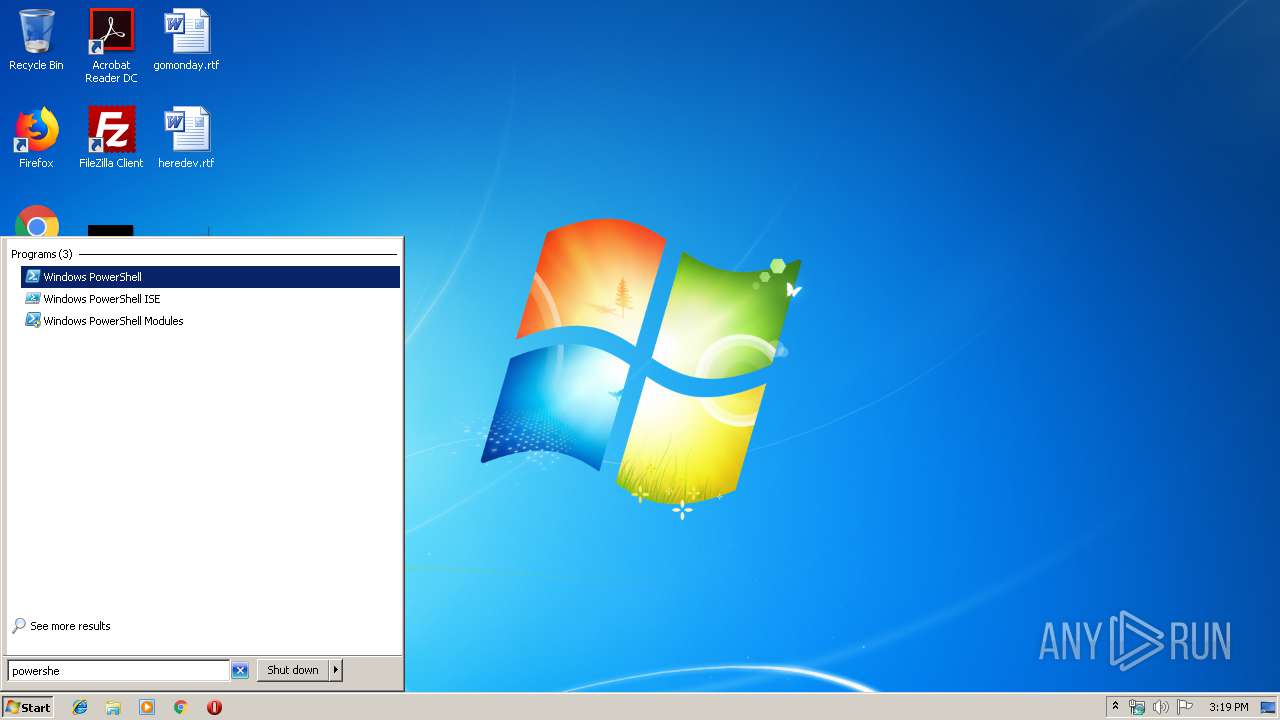
Manual execution by user
- powershell.exe (PID: 2096)
Reads settings of System Certificates
- powershell.exe (PID: 3620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
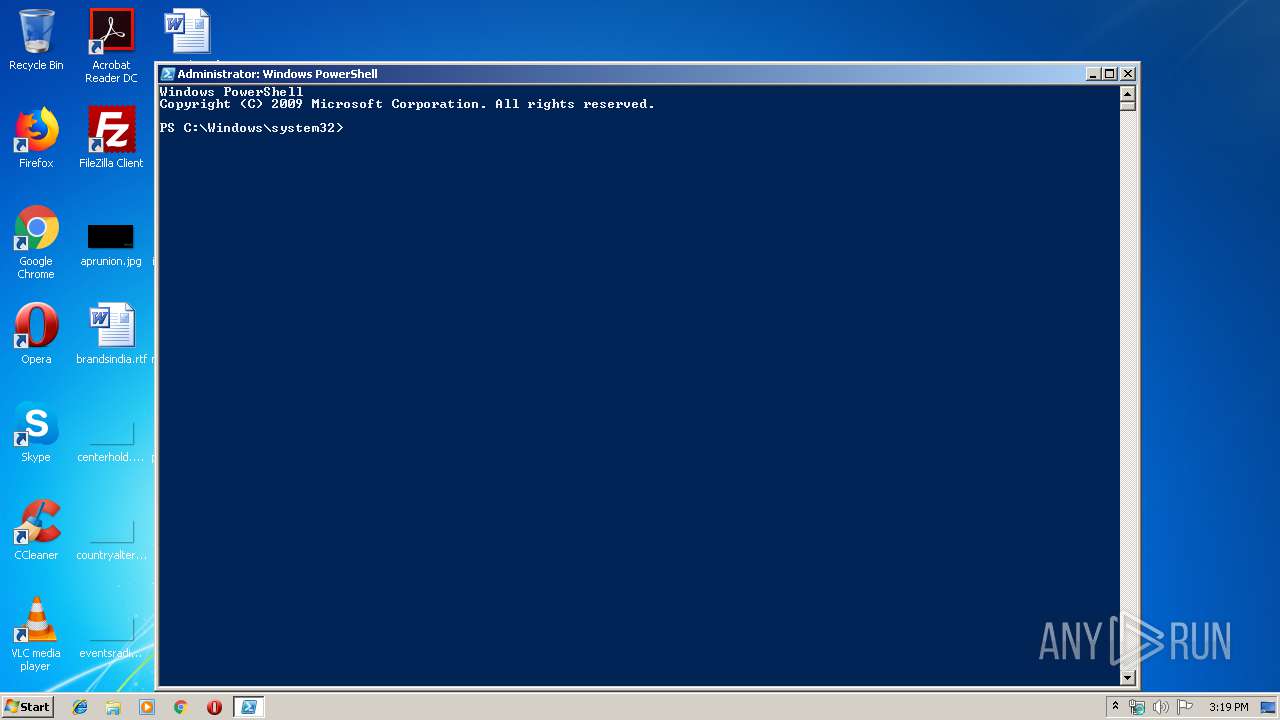
| 2096 | "C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe" | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3156 | "C:\Windows\system32\rundll32.exe" InetCpl.cpl ClearMyTracksByProcess 260 | C:\Windows\system32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
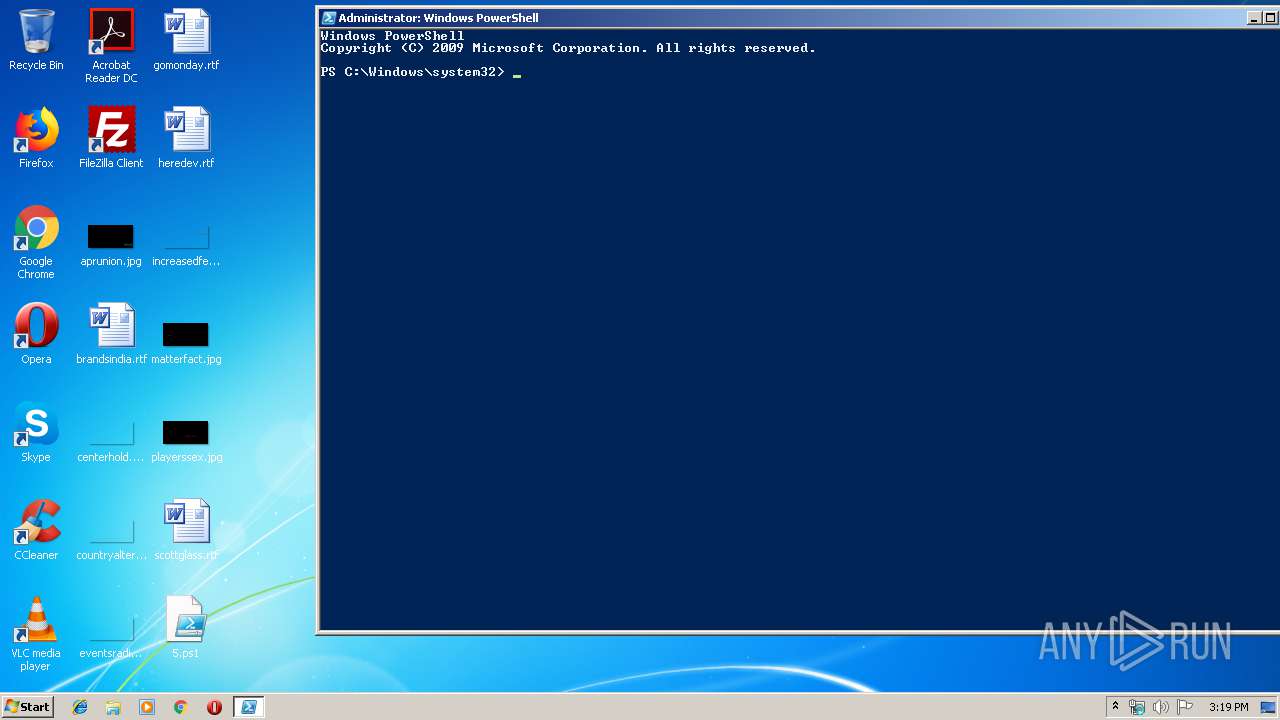
| 3620 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\5.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3676 | "C:\Windows\system32\rundll32.exe" /s \gomonday. DllRegisterServer | C:\Windows\system32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3804 | "C:\Windows\system32\rundll32.exe" InetCpl.cpl ClearMyTracksByProcess 260 | C:\Windows\system32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3860 | "C:\Windows\system32\rundll32.exe" /s \increasedfeed. DllRegisterServer | C:\Windows\system32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
522
Read events
371
Write events
151
Delete events
0
Modification events
| (PID) Process: | (3620) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3620) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3620) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
4
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3620 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\N6X19A006AQ9T4O0IE78.temp | — | |
MD5:— | SHA256:— | |||
| 3156 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\~DF7D7F75ADFF4C3FC0.TMP | — | |
MD5:— | SHA256:— | |||
| 3156 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\~DFDFC80D3CDC5D0B1A.TMP | — | |
MD5:— | SHA256:— | |||
| 3156 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\~DFD5F42FB9846AAE44.TMP | — | |
MD5:— | SHA256:— | |||
| 3156 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\~DF574A4A9ED6FE6193.TMP | — | |
MD5:— | SHA256:— | |||
| 2096 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\IUAJYVR3HVF6ARCOSLHE.temp | — | |
MD5:— | SHA256:— | |||
| 3804 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\~DF6DDBF6E563430655.TMP | — | |
MD5:— | SHA256:— | |||
| 3804 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\~DFECE5D1809D5E7BF1.TMP | — | |
MD5:— | SHA256:— | |||
| 3804 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\~DF22E3068A261CD5CC.TMP | — | |
MD5:— | SHA256:— | |||
| 3804 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\~DFC3DE2FDC51F75772.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3620 | powershell.exe | 185.158.249.75:443 | woeiuyfgowe.xyz | easystores GmbH | NL | suspicious |
2096 | powershell.exe | 185.158.249.75:443 | woeiuyfgowe.xyz | easystores GmbH | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
woeiuyfgowe.xyz |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3620 | powershell.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
2096 | powershell.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |