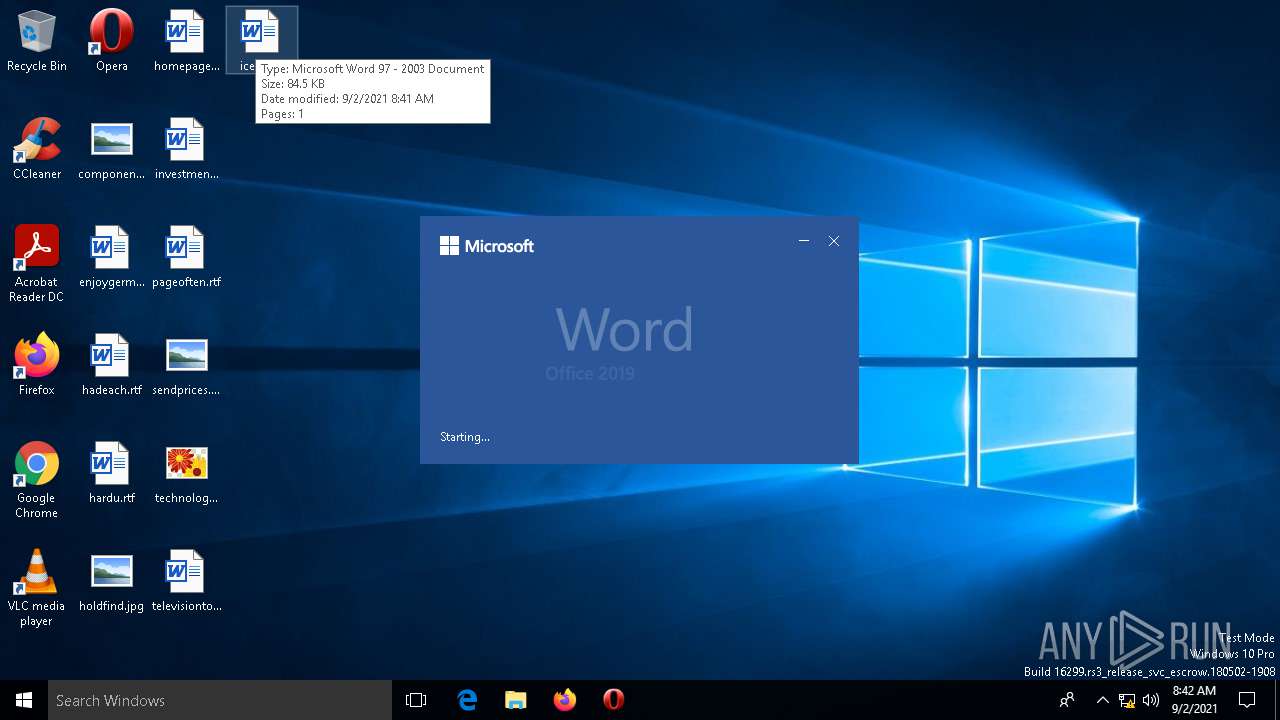
| File name: | ice2.doc |
| Full analysis: | https://app.any.run/tasks/c760c094-9b59-4052-b25e-207390e60f58 |
| Verdict: | Malicious activity |
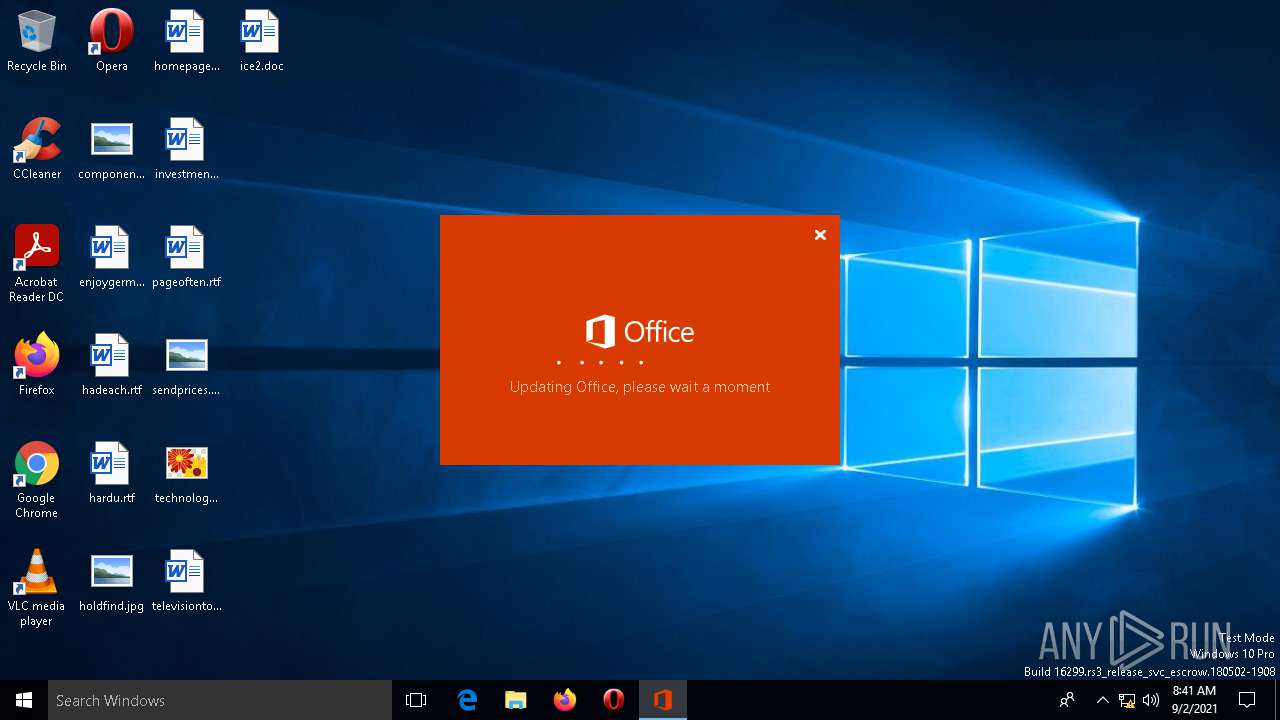
| Analysis date: | September 02, 2021, 08:41:03 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Author: admin, Template: Normal, Last Saved By: Windows, Revision Number: 2, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Aug 30 10:37:00 2021, Last Saved Time/Date: Mon Aug 30 10:37:00 2021, Number of Pages: 1, Number of Words: 97, Number of Characters: 12785, Security: 0 |
| MD5: | 6480699E92A13679EA6BDE827624C178 |
| SHA1: | 18101B3C16234F86B0C43071173C7E11559111D0 |
| SHA256: | DFC093ABF3EBC7AFC2E3E4341DD069694B8FAF7F8B04F15CB674C6B74C7055B8 |
| SSDEEP: | 768:uWLniP0nXmMv4QGVp+BW87CuwJIfXAvFpjoPm/PGDQwM8OAHwrmRwua+maY:uWLniP+srVIEfJTjGQPoQwMRAHBa+ma |
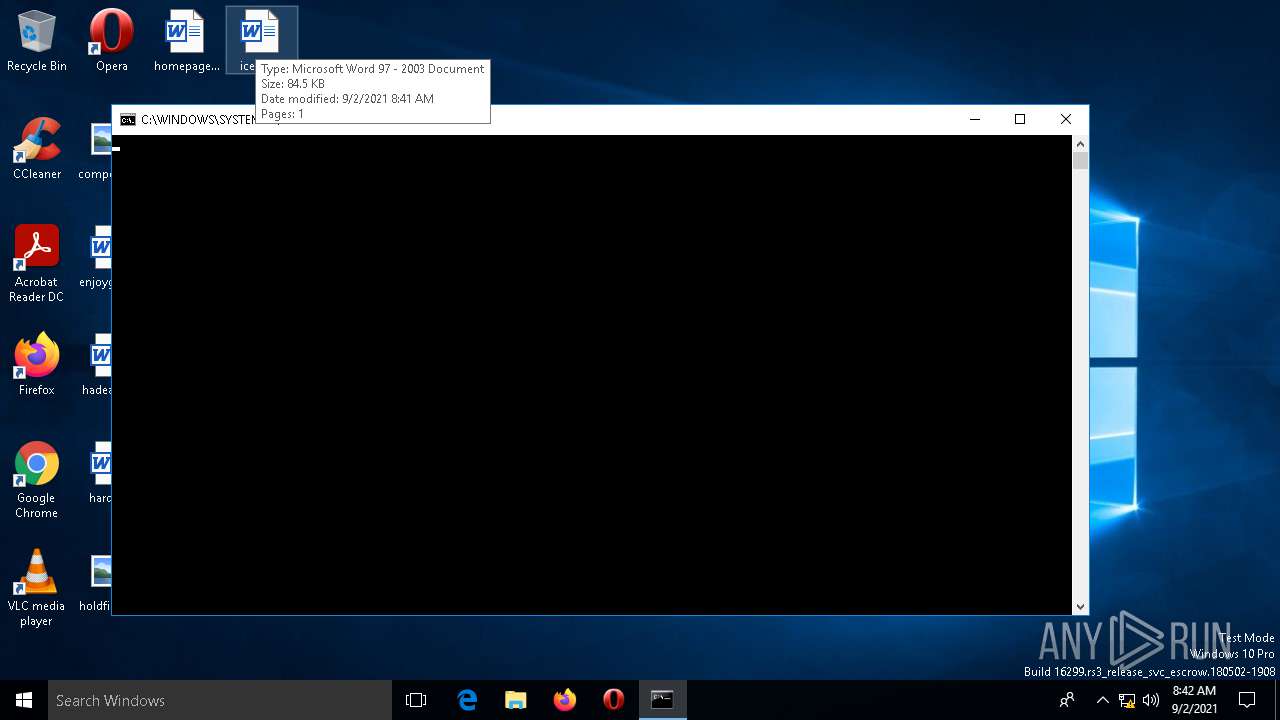
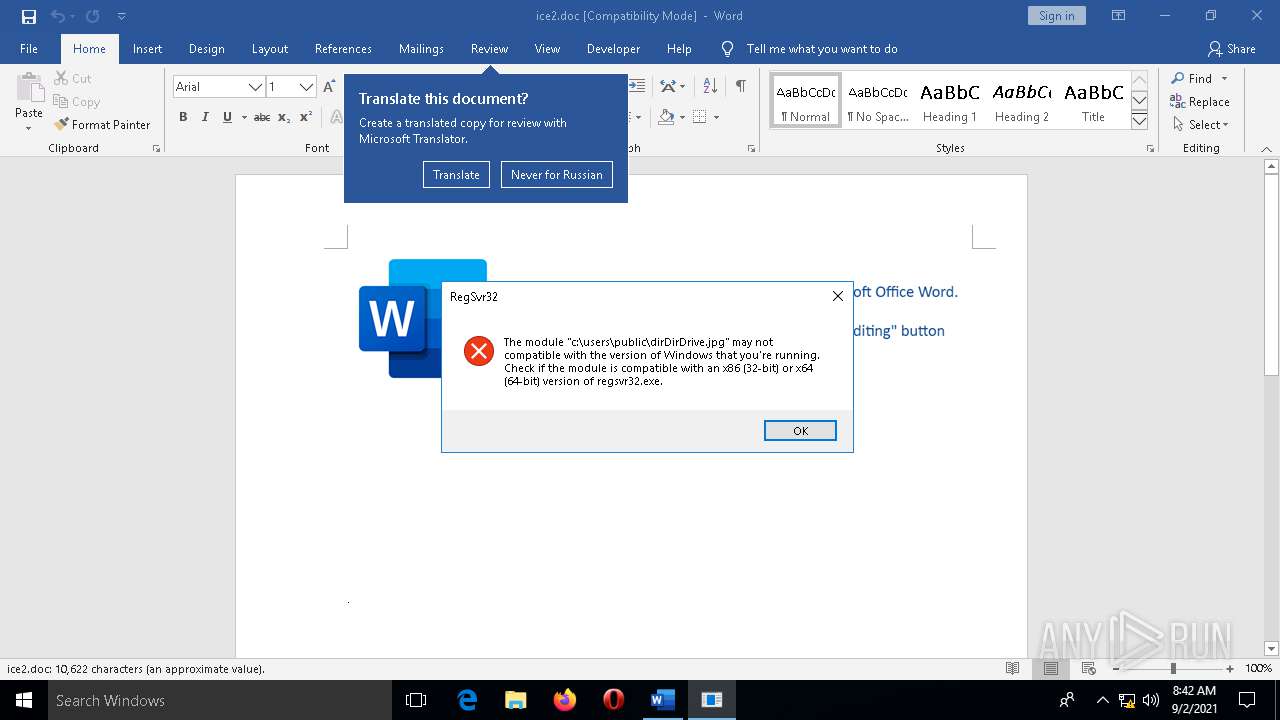
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2660)
Scans artifacts that could help determine the target
- OfficeC2RClient.exe (PID: 564)
SUSPICIOUS
Checks supported languages
- OfficeC2RClient.exe (PID: 564)
Reads the computer name
- OfficeC2RClient.exe (PID: 564)
- TiWorker.exe (PID: 1060)
Reads Environment values
- OfficeC2RClient.exe (PID: 564)
Reads the date of Windows installation
- taskmgr.exe (PID: 3408)
Executed via COM
- TiWorker.exe (PID: 1060)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2660)
- OfficeC2RClient.exe (PID: 564)
Reads the computer name
- WINWORD.EXE (PID: 2660)
- taskmgr.exe (PID: 3408)
Checks supported languages
- WINWORD.EXE (PID: 2660)
- taskmgr.exe (PID: 3408)
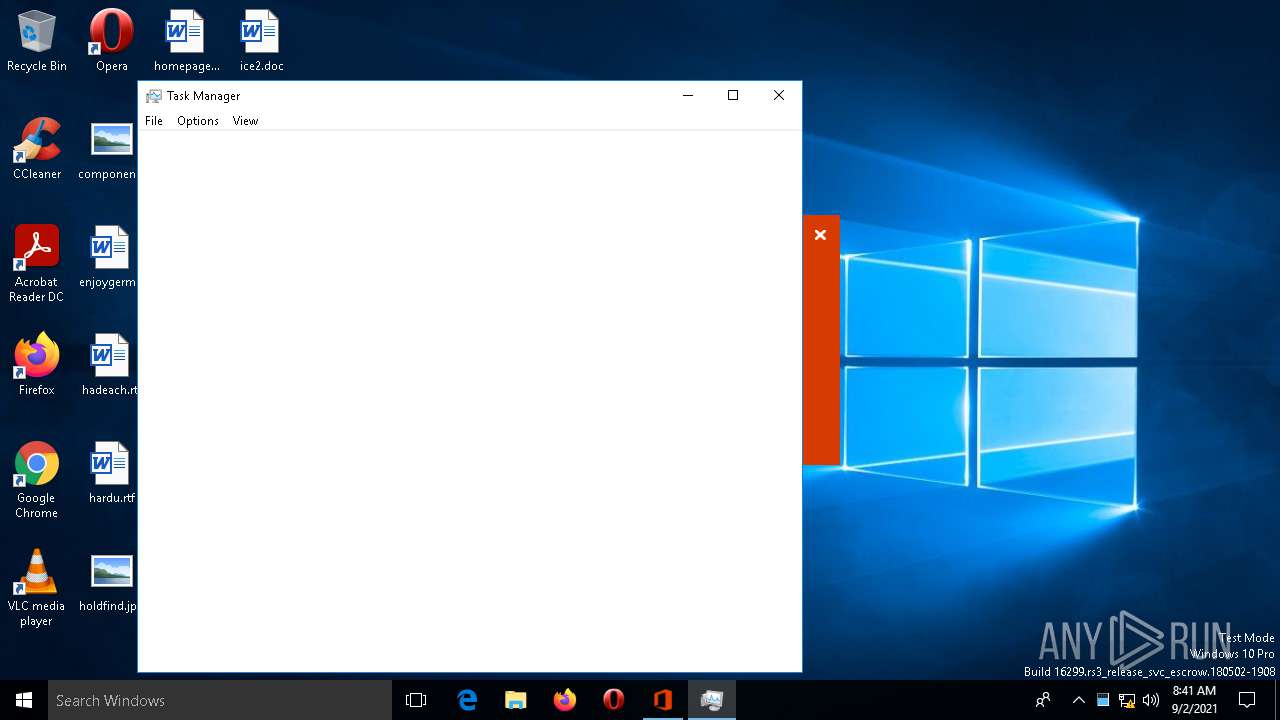
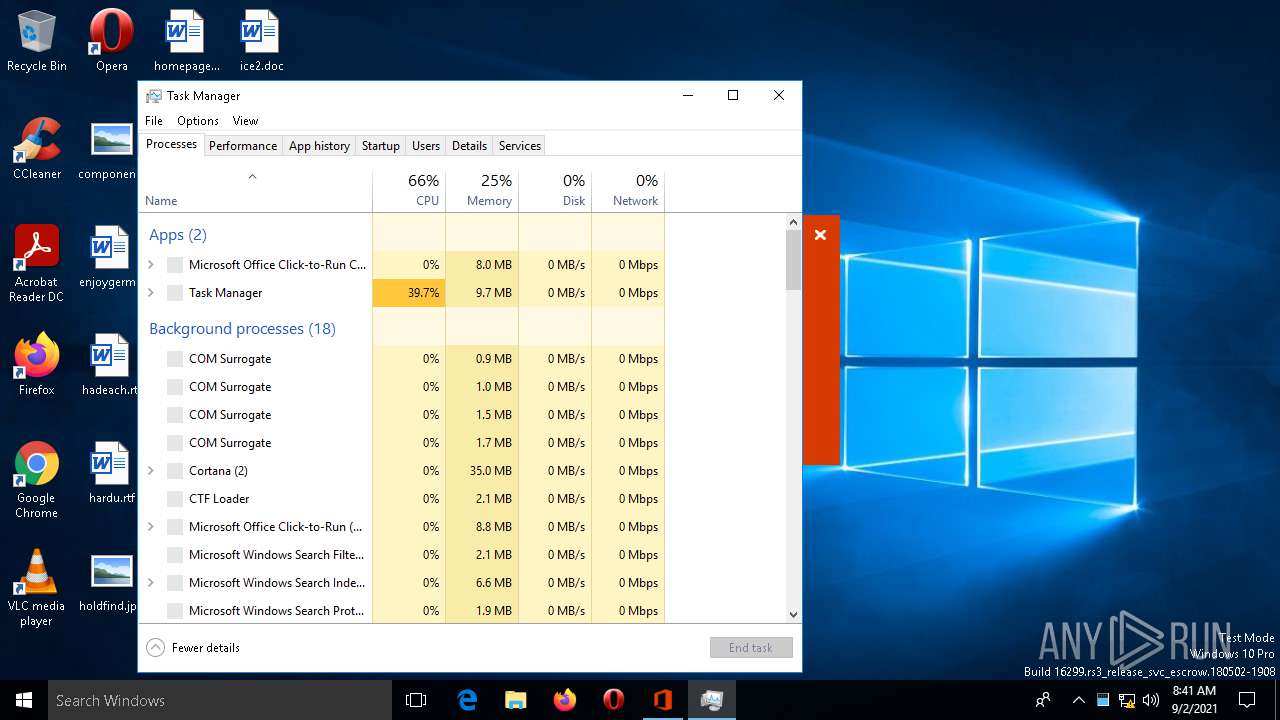
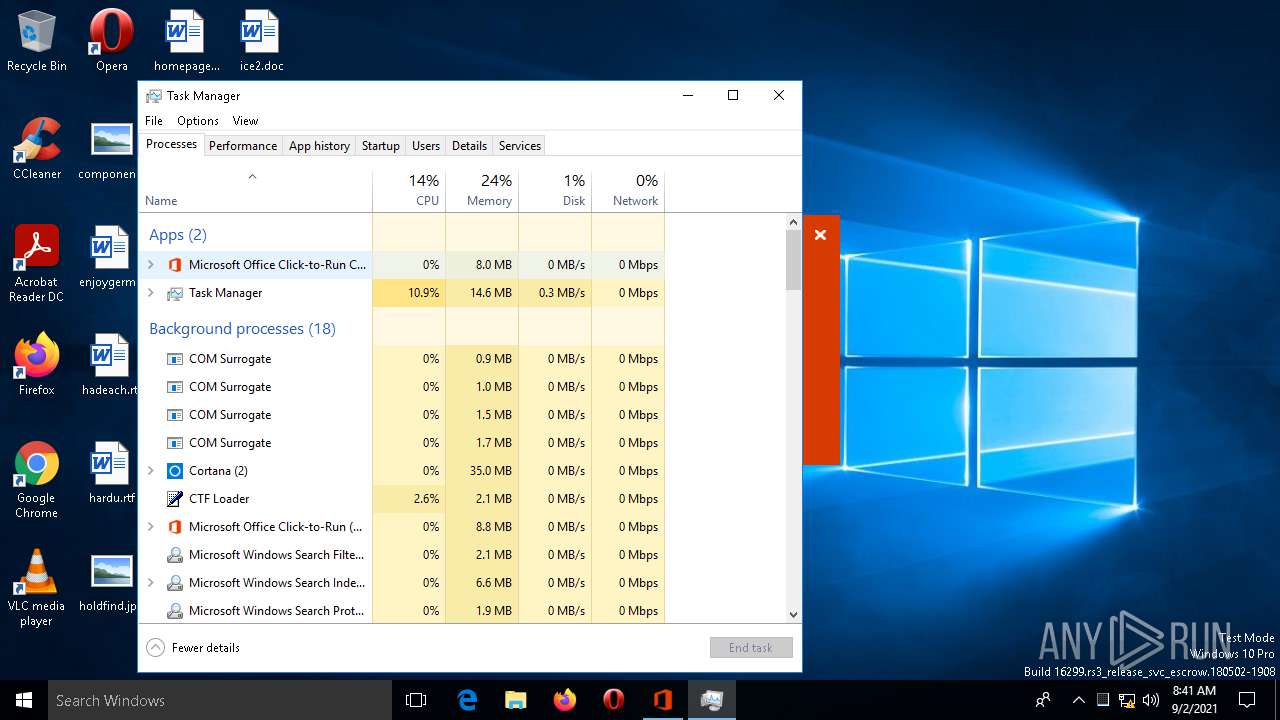
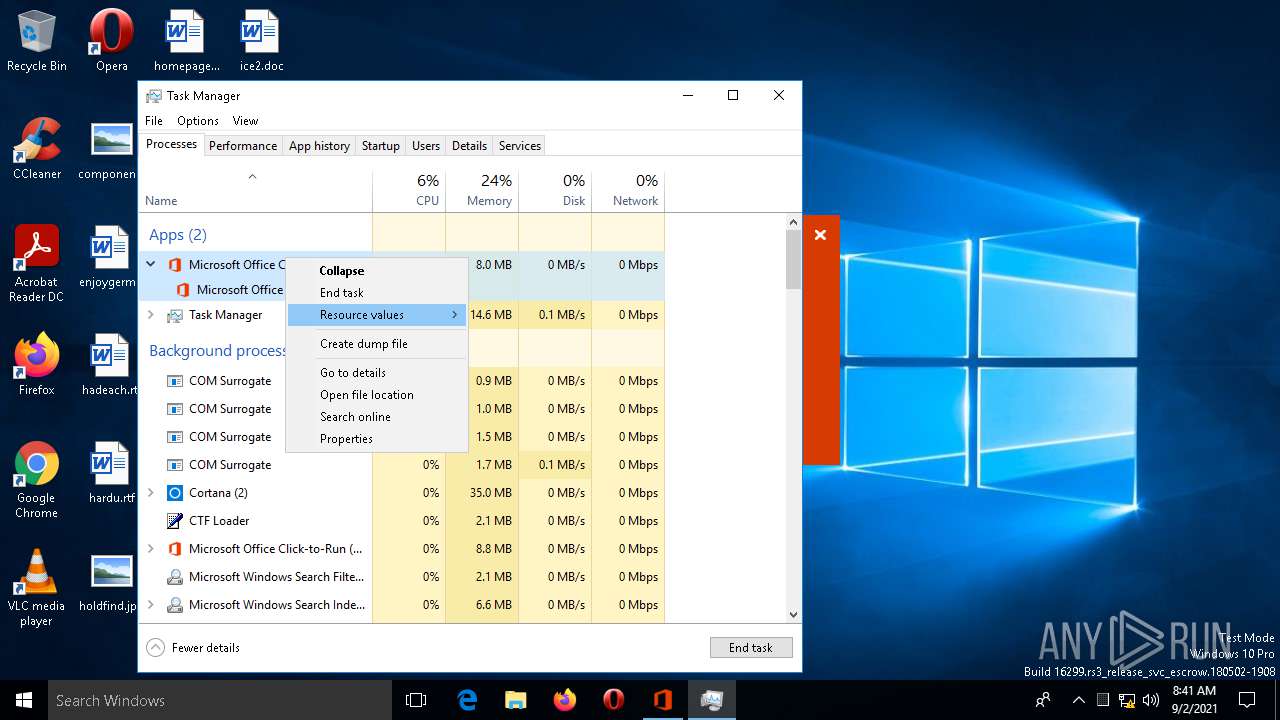
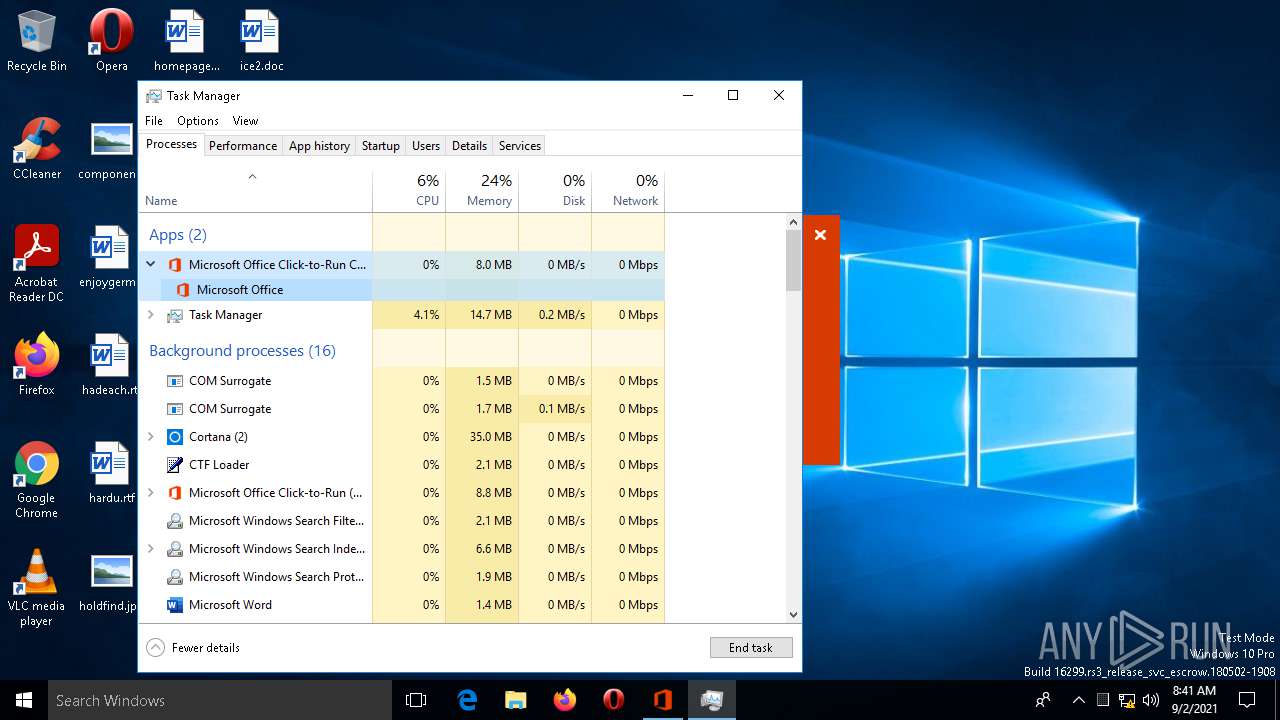
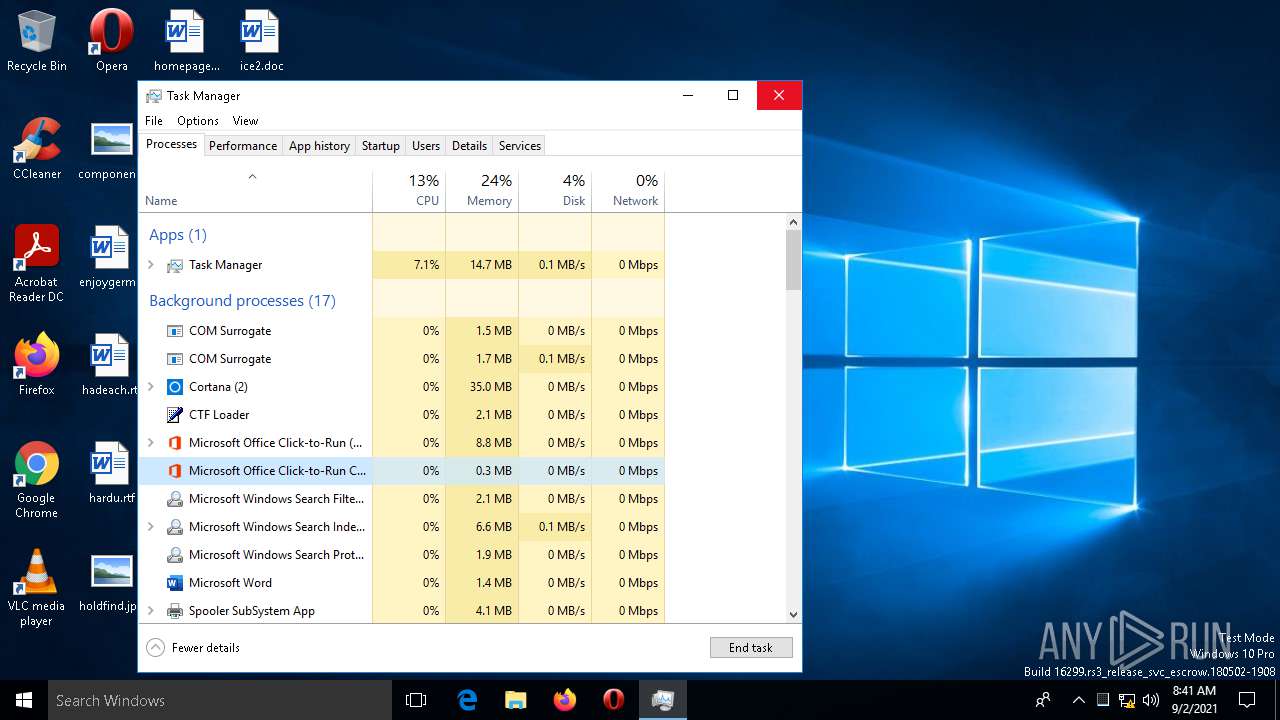
Manual execution by user
- taskmgr.exe (PID: 3304)
- taskmgr.exe (PID: 3408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserType: | ???????? Microsoft Word 97-2003 |
|---|---|
| CompObjUserTypeLen: | 32 |
| HeadingPairs: |
|
| TitleOfParts: | - |
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| ScaleCrop: | No |
| AppVersion: | 16 |
| CharCountWithSpaces: | 12875 |
| Paragraphs: | 7 |
| Lines: | 34 |
| Bytes: | 26624 |
| Company: | - |
| Manager: | - |
| Category: | - |
| CodePage: | Windows Cyrillic |
| Security: | None |
| Characters: | 12785 |
| Words: | 97 |
| Pages: | 1 |
| ModifyDate: | 2021:08:30 09:37:00 |
| CreateDate: | 2021:08:30 09:37:00 |
| TotalEditTime: | - |
| Software: | Microsoft Office Word |
| RevisionNumber: | 2 |
| LastModifiedBy: | Пользователь Windows |
| Template: | Normal |
| Comments: | - |
| Keywords: | - |
| Author: | admin |
| Subject: | - |
| Title: | - |
Total processes
105
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
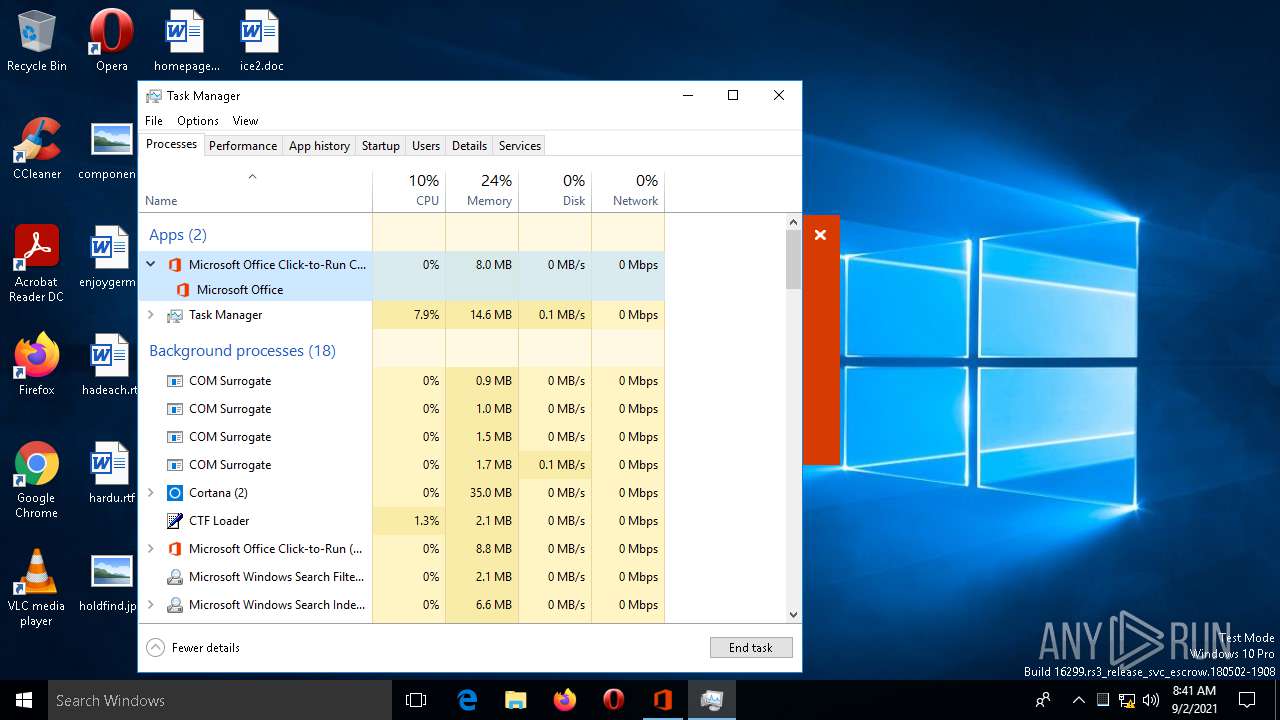
| 564 | OfficeC2RClient.exe /error PID=2660 ProcessName="Microsoft Word" UIType=3 ErrorSource=0x8b10082a ErrorCode=0x800706ba ShowUI=1 | C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeC2RClient.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office Click-to-Run Client Exit code: 1 Version: 16.0.12026.20264 Modules
| |||||||||||||||
| 1060 | C:\WINDOWS\winsxs\x86_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.16299.428_none_bae6269479a24372\TiWorker.exe -Embedding | C:\WINDOWS\winsxs\x86_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.16299.428_none_bae6269479a24372\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Desktop\ice2.doc" /o "" | C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 1073807364 Version: 16.0.12026.20264 Modules
| |||||||||||||||
| 3304 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\WINDOWS\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3408 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\WINDOWS\system32\taskmgr.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 458
Read events
2 431
Write events
23
Delete events
4
Modification events
| (PID) Process: | (564) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (564) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (564) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (564) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (564) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (564) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (564) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (564) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
| (PID) Process: | (564) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ru-ru |
Value: 2 | |||
| (PID) Process: | (564) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | tr-tr |
Value: 2 | |||
Executable files
0
Suspicious files
2
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 564 | OfficeC2RClient.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\officec2rclient.exe.db-wal | binary | |
MD5:— | SHA256:— | |||
| 564 | OfficeC2RClient.exe | C:\Users\admin\AppData\Local\Temp\.ses | text | |
MD5:— | SHA256:— | |||
| 564 | OfficeC2RClient.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\officec2rclient.exe.db-shm | binary | |
MD5:— | SHA256:— | |||
| 1060 | TiWorker.exe | C:\WINDOWS\Logs\CBS\CBS.log | text | |
MD5:— | SHA256:— | |||
| 564 | OfficeC2RClient.exe | C:\Users\admin\AppData\Local\Temp\DESKTOP-JGLLJLD-20210902-0841.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
9
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 185.53.46.11:80 | http://francopublicg.com/bmdff/81345/4OeQWty831KK2b98WaBhoHsCtZxaMLdmpfjaX8b5uFG/63910/yt2nxB/77015/59pAA/8yLnkGbUicYeCPtQnMwHaMsg638wKiUWdJB/6zBuB/YYb0Ep2I7EwTtT/galax10?sid=j2GNOqeoka2THdHZh2iUVCrnXpd&sid=ck60wJogKzsBY&1OS=Xkhcn8ZMMkcm7uEg&user=lYDCXVh4VHhDBJJxQ&tY2=FQJaQNAkeGyTxP7XY&sid=hPpvER | DE | html | 206 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | Microsoft Corporation | GB | whitelisted |
3988 | WaaSMedic.exe | 51.124.78.146:443 | — | Microsoft Corporation | GB | whitelisted |
— | — | 185.53.46.11:80 | francopublicg.com | — | DE | suspicious |
— | — | 52.109.60.0:443 | ogma.osi.office.net | Microsoft Corporation | IN | unknown |
— | — | 52.168.117.170:443 | self.events.data.microsoft.com | Microsoft Corporation | US | suspicious |
— | — | 13.107.42.23:443 | config.edge.skype.com | Microsoft Corporation | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| malicious |
self.events.data.microsoft.com |
| whitelisted |
time.windows.com |
| whitelisted |
francopublicg.com |
| suspicious |
ogma.osi.office.net |
| whitelisted |