| File name: | 2.exe |
| Full analysis: | https://app.any.run/tasks/84205732-48aa-491c-9774-edffc9bd714c |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2019, 13:54:39 |
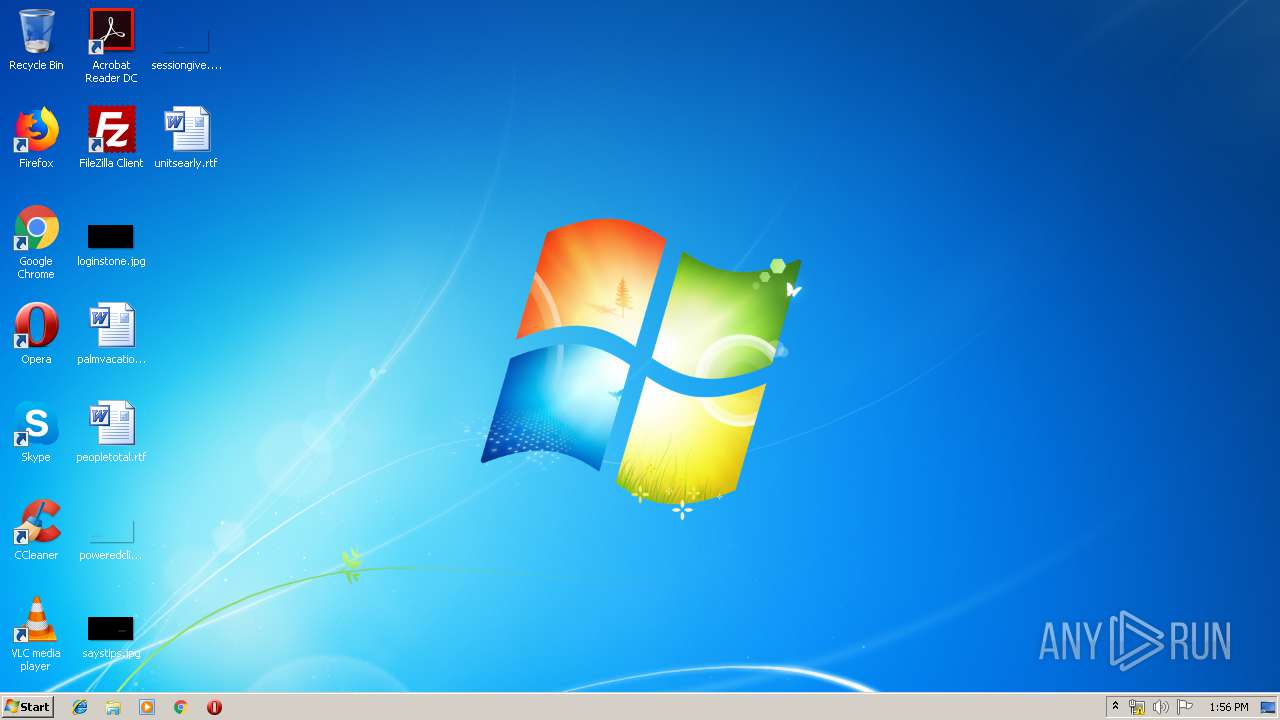
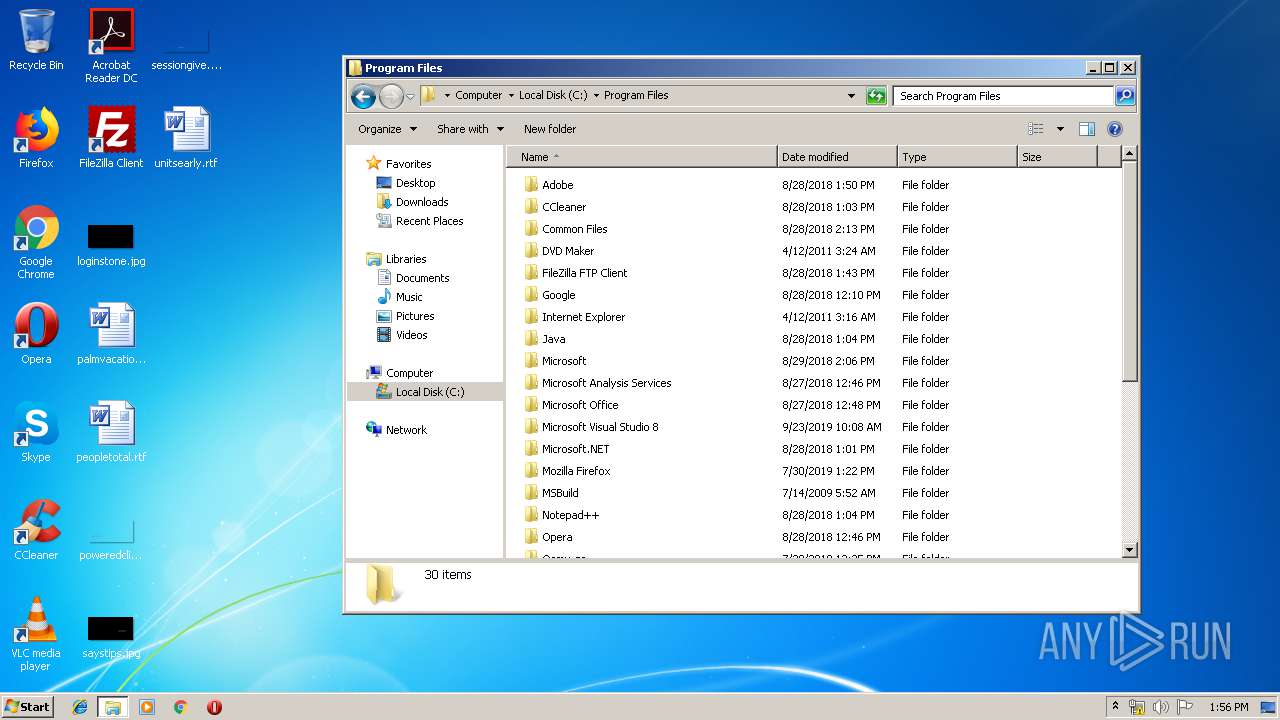
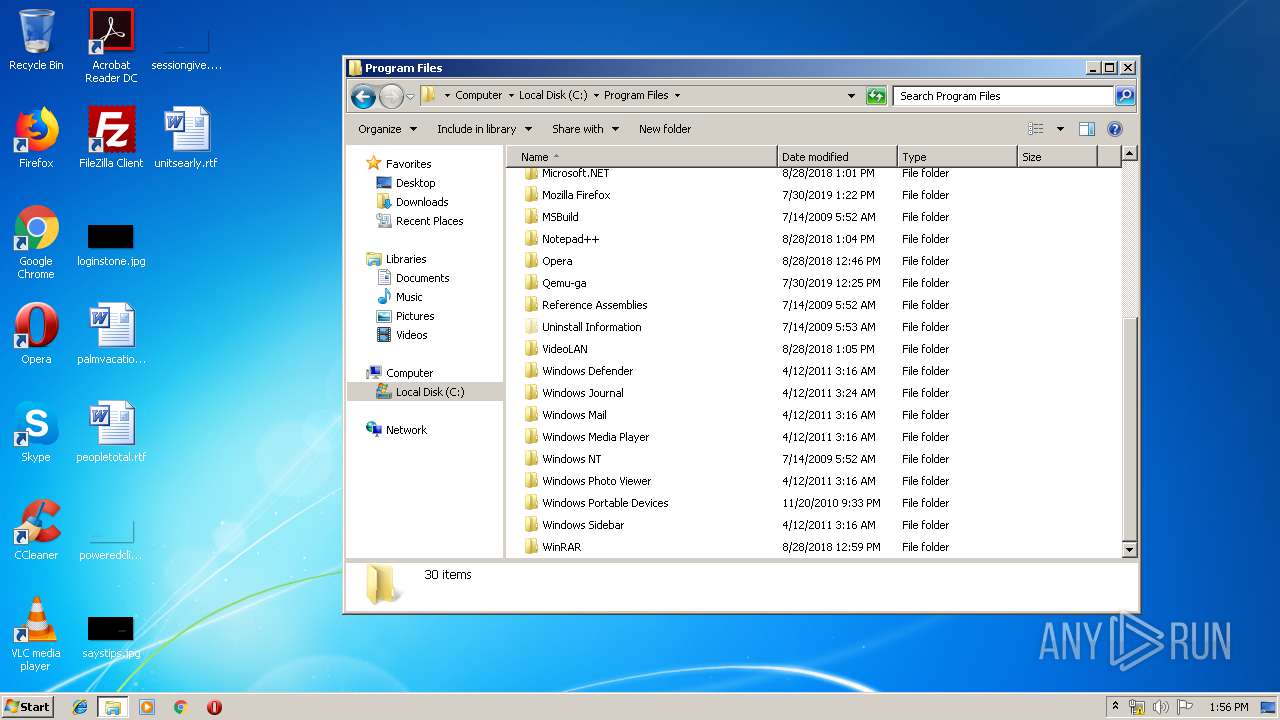
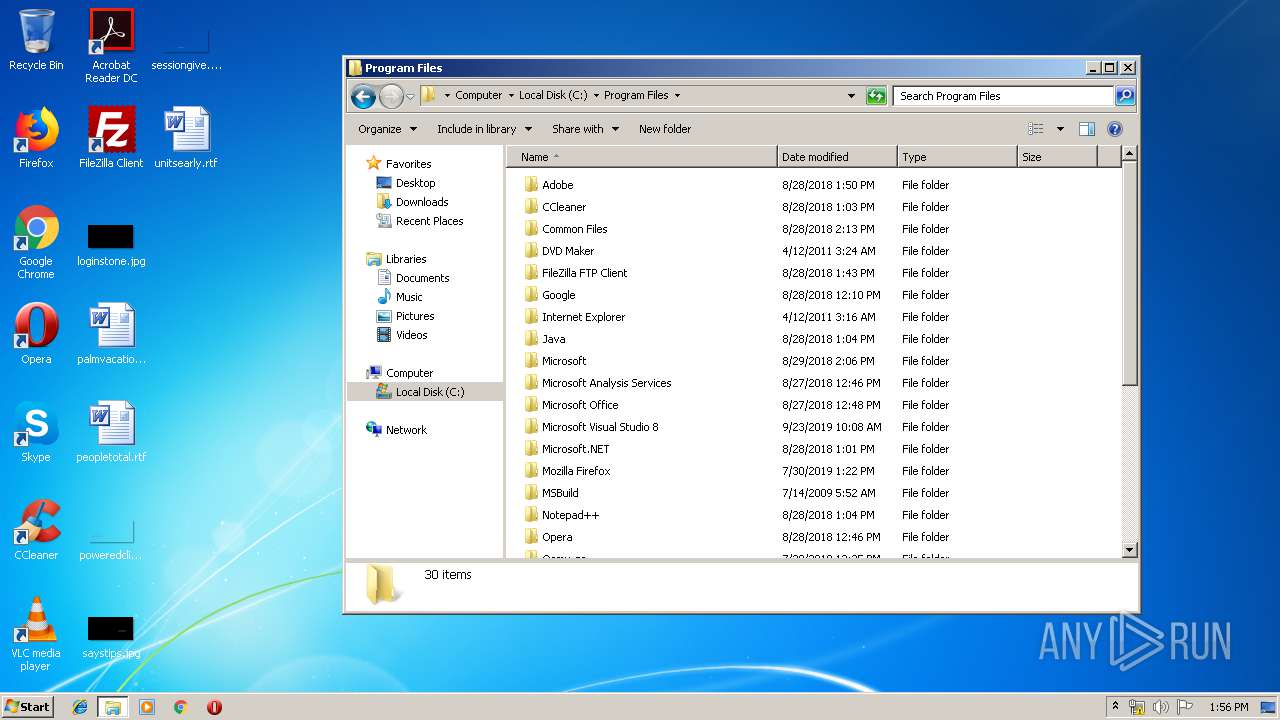
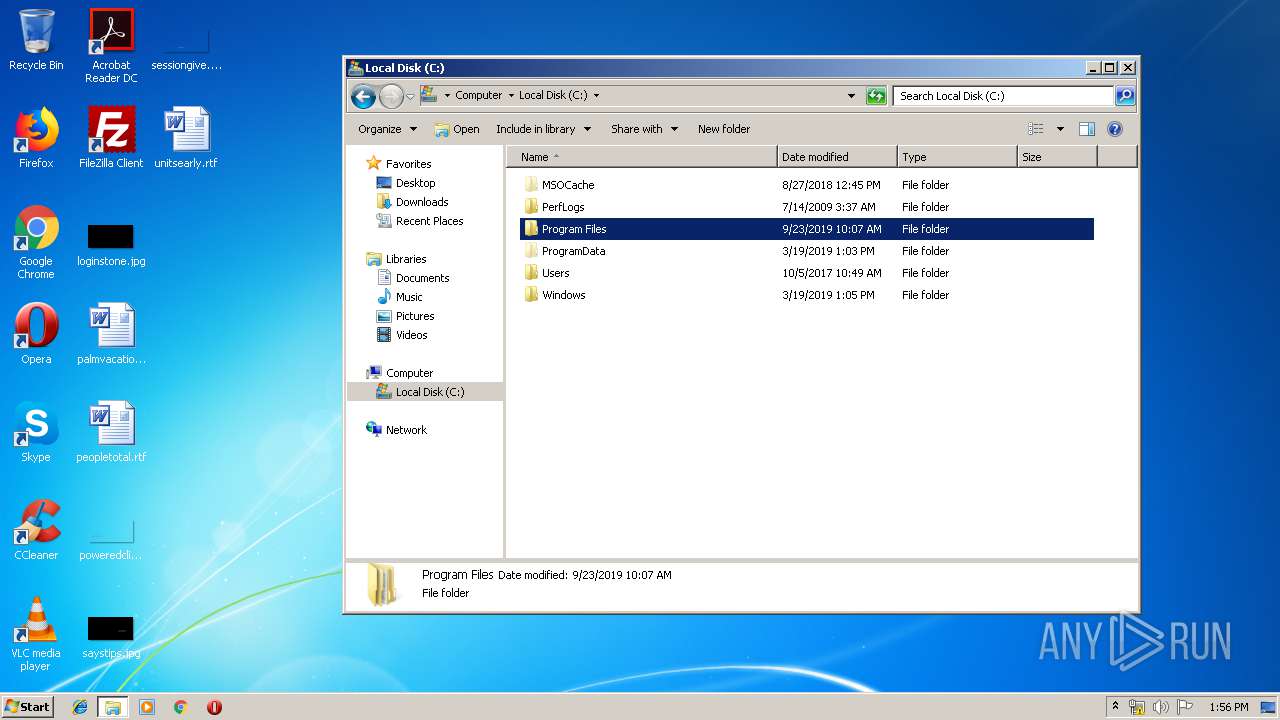
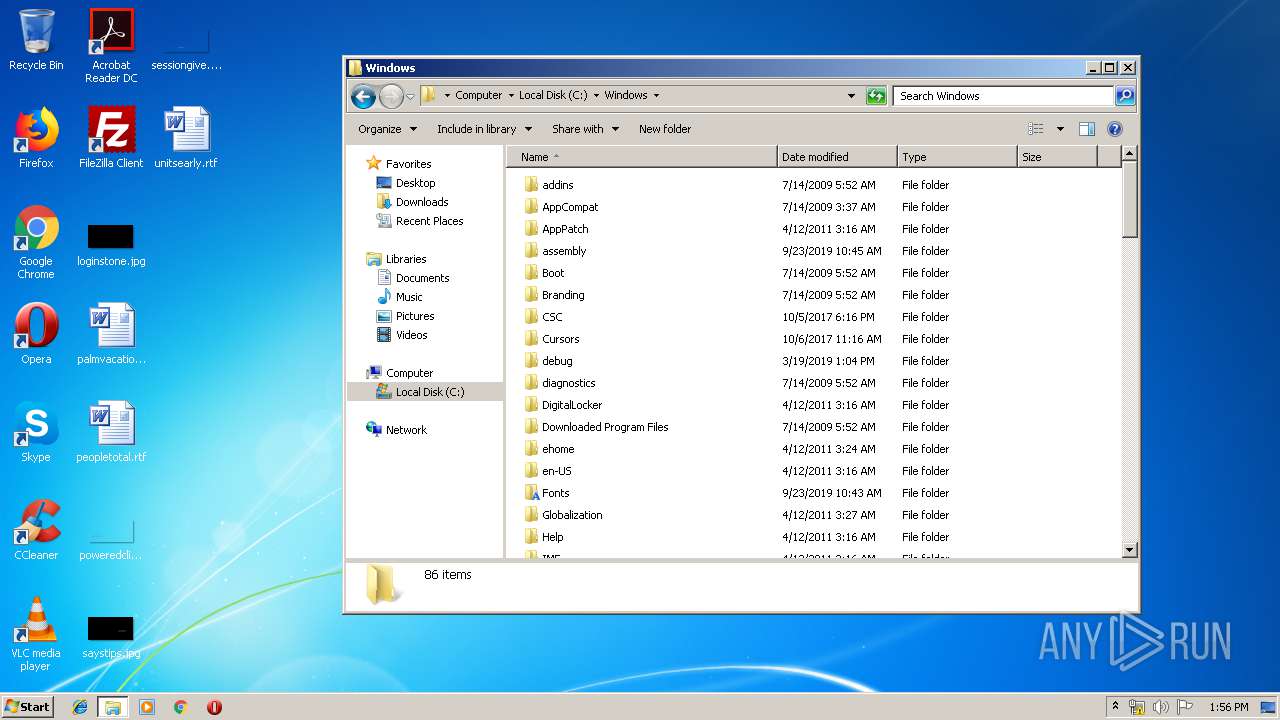
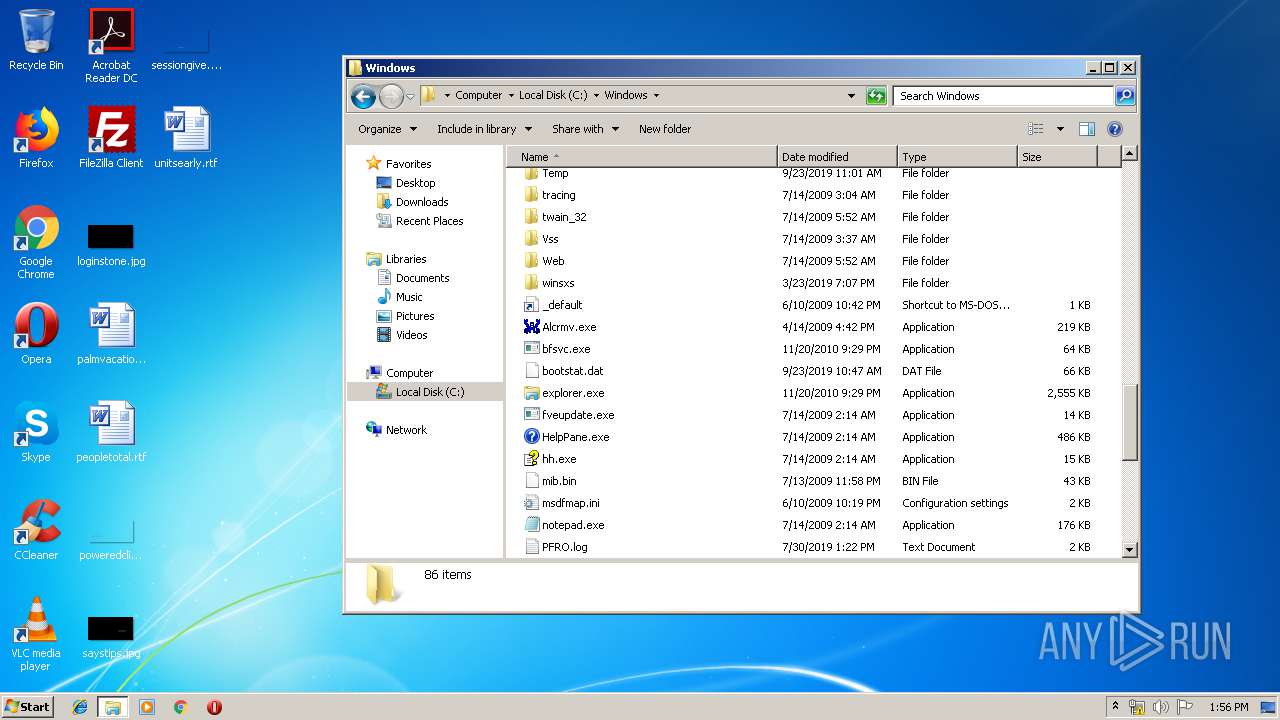
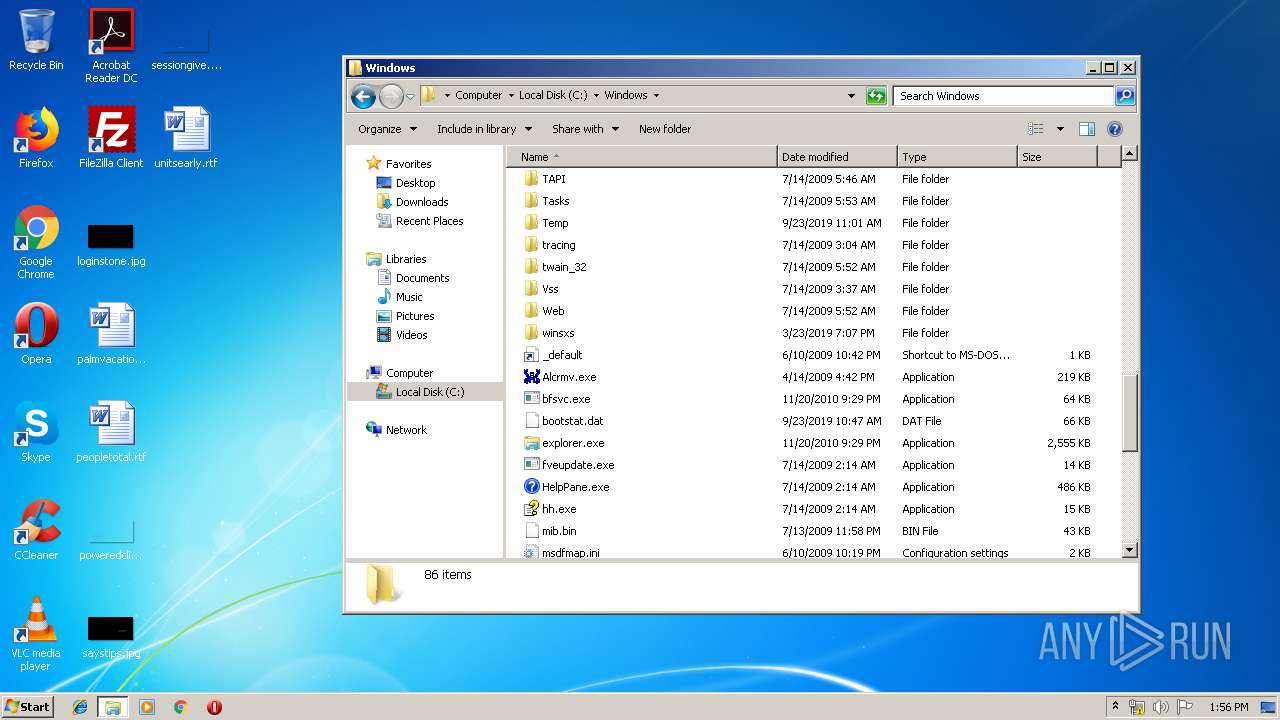
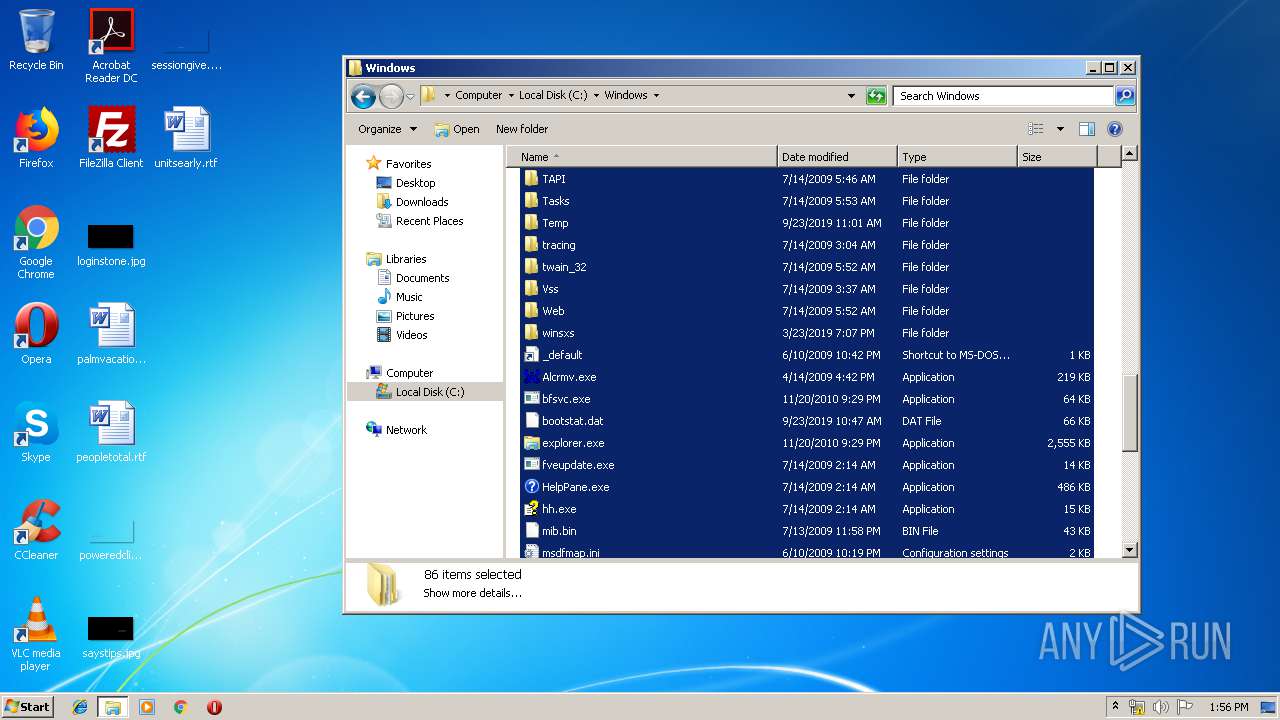
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8EBAEC0E763C2D3DB79FBD881A90E223 |
| SHA1: | 9349919955E30628DFF405302E49FB2A39E439DD |
| SHA256: | DFA89732E3FDB8C98C9F0476388C1CCC883BBAC5581306C0BE938CAB7ADB513A |
| SSDEEP: | 49152:apiE8vllnXrbRHSJe+KMry05OnZ2a8V6U+fImnTznUbFhRfCh:l7PRHSJ6hEOkHX+l/2FHfCh |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 1416)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:08:22 09:49:11+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 645120 |
| InitializedDataSize: | 182272 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x51c000 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.30.0 |
| ProductVersionNumber: | 1.1.30.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | - |
| FileVersion: | 1.1.30.00 |
| InternalName: | - |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | 1.1.30.00 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Aug-2018 07:49:11 |
| Detected languages: |
|
| FileDescription: | - |
| FileVersion: | 1.1.30.00 |
| InternalName: | - |
| LegalCopyright: | - |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | 1.1.30.00 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 22-Aug-2018 07:49:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00001000 | 0x000CC000 | 0x0005C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.98029 | |
.rsrc | 0x000CD000 | 0x00005AC8 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.67232 |
.idata | 0x000D3000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.2888 |
0x000D4000 | 0x0029D000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.256865 | |
wxofntza | 0x00371000 | 0x001AB000 | 0x001AA800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.94982 |
ignywmau | 0x0051C000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.72265 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.33598 | 1159 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.37027 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.67639 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.84157 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.3349 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.46964 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.56056 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
159 | 2.45849 | 48 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
160 | 2.02322 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
205 | 6.9362 | 232 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
comctl32.dll |
kernel32.dll |
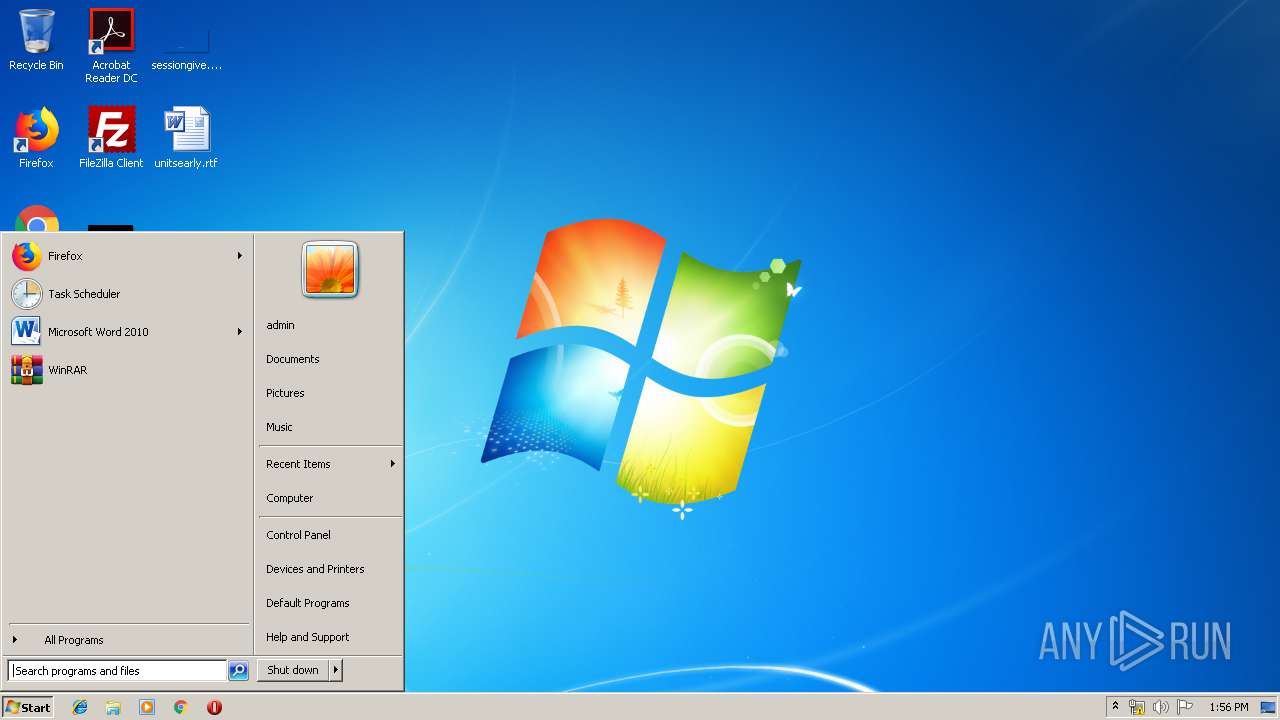
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
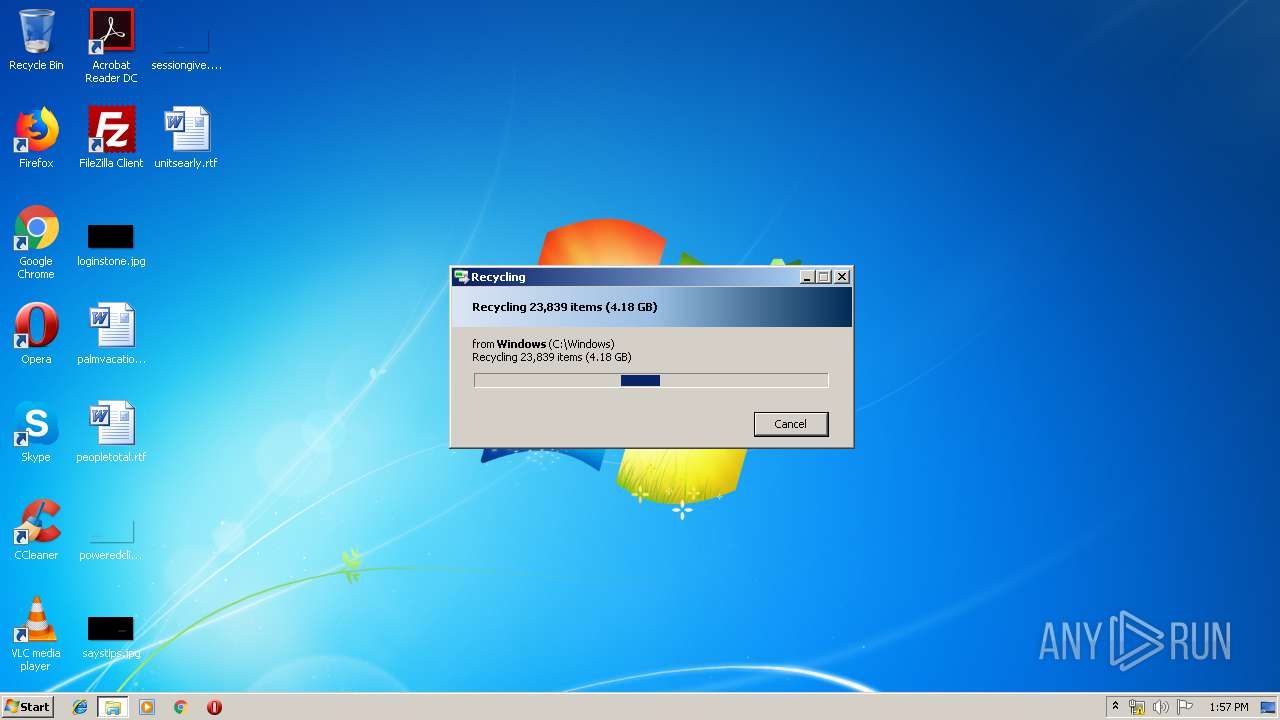
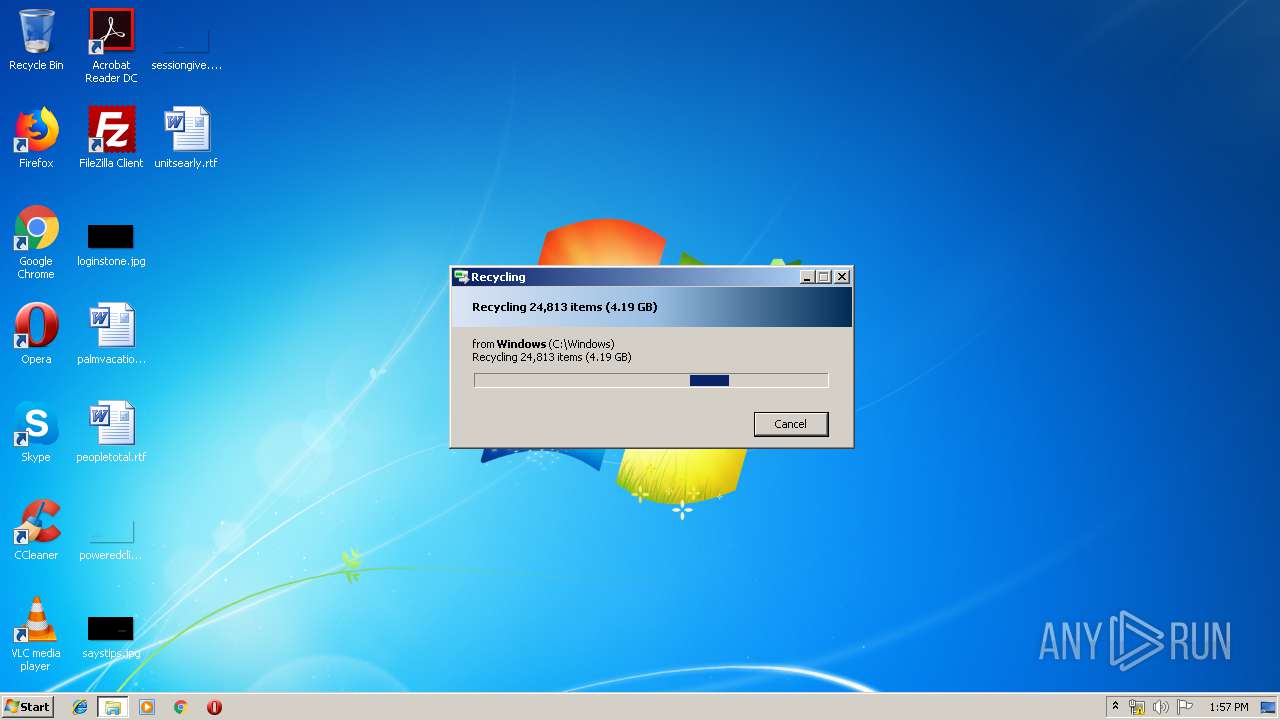
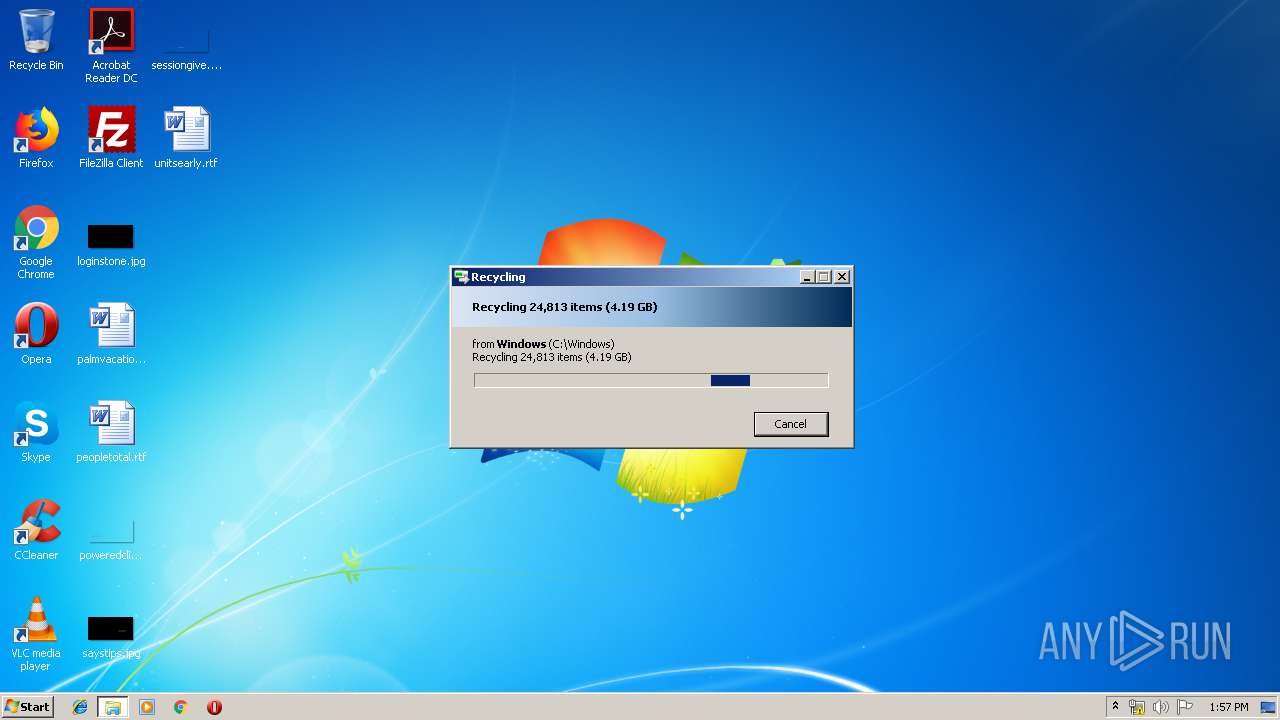
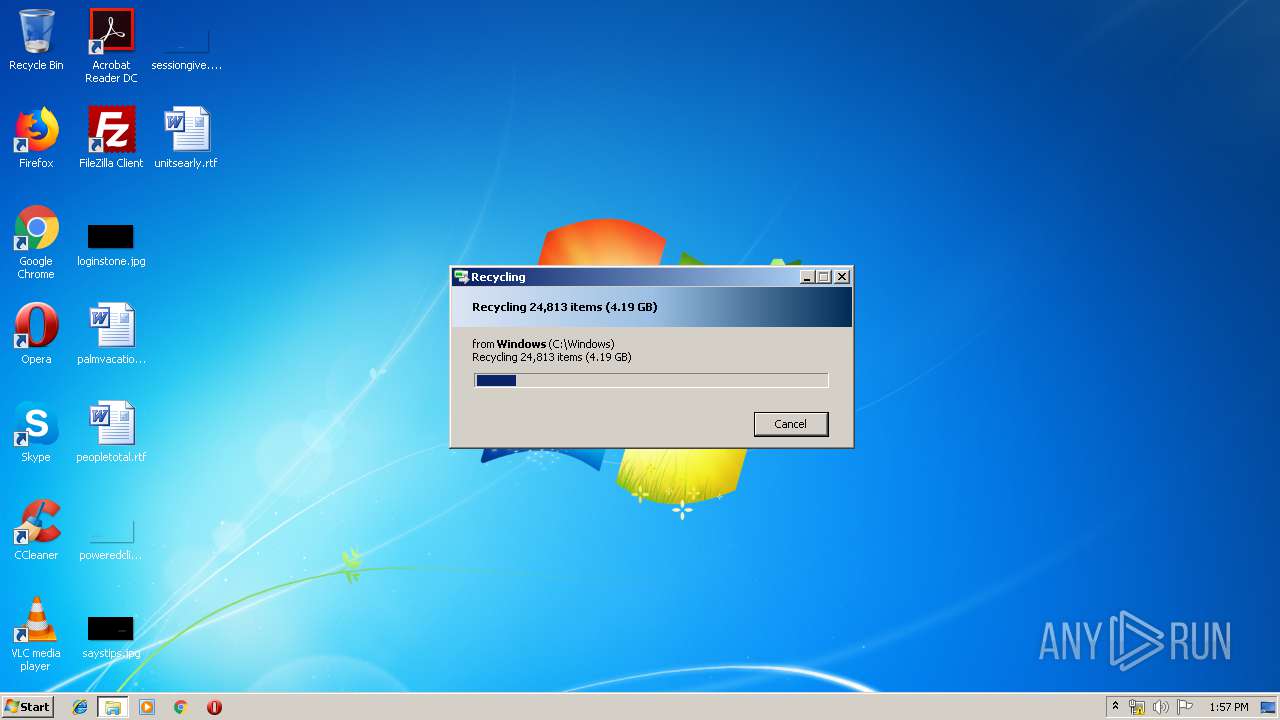
Behavior graph
Click at the process to see the details
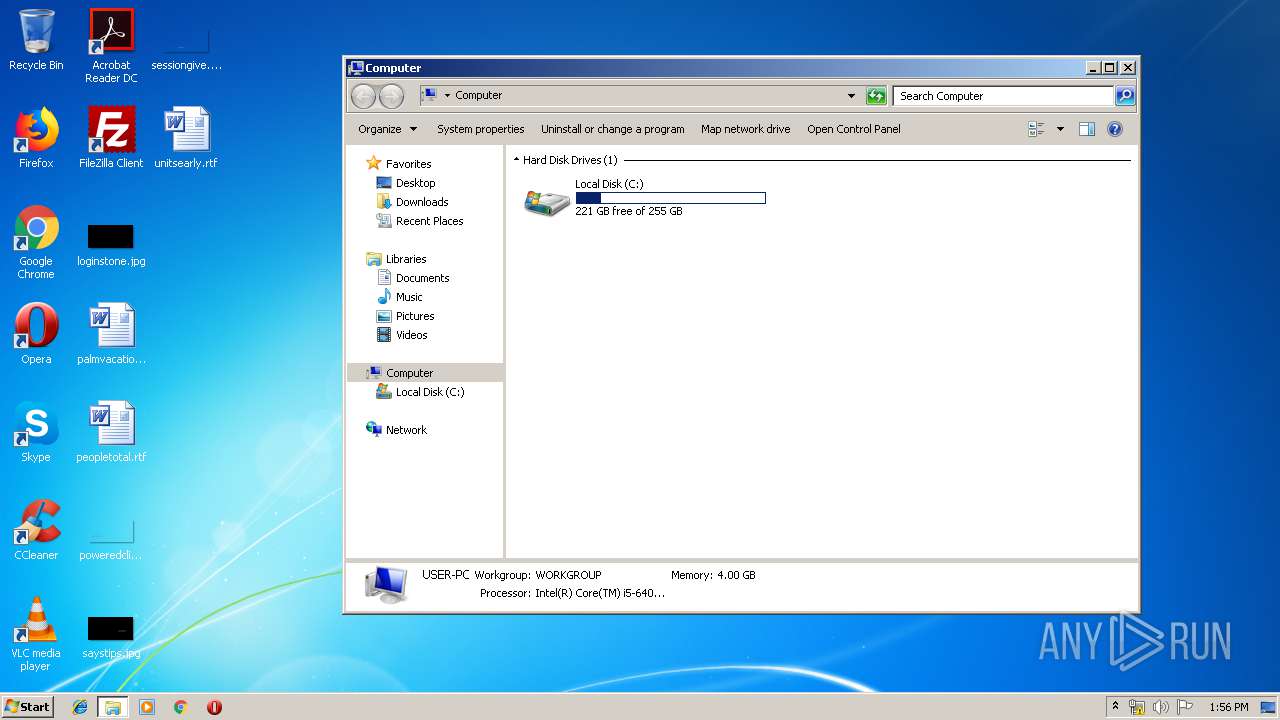
Process information
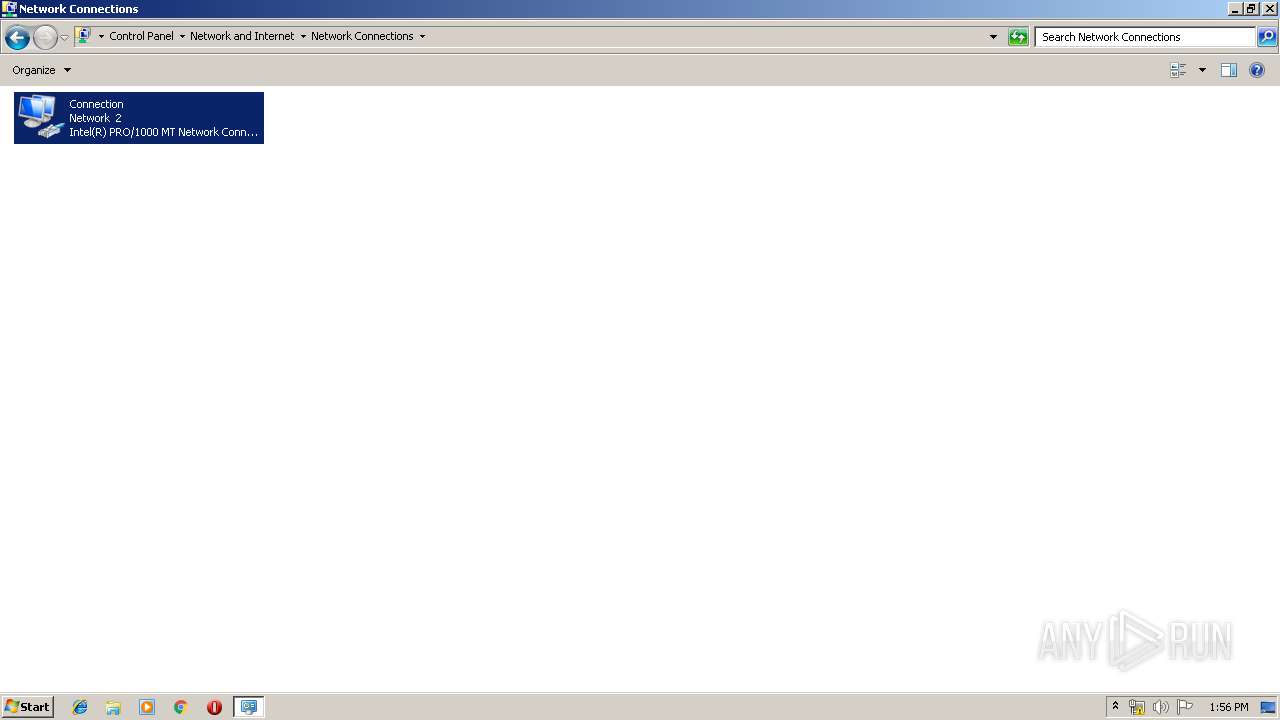
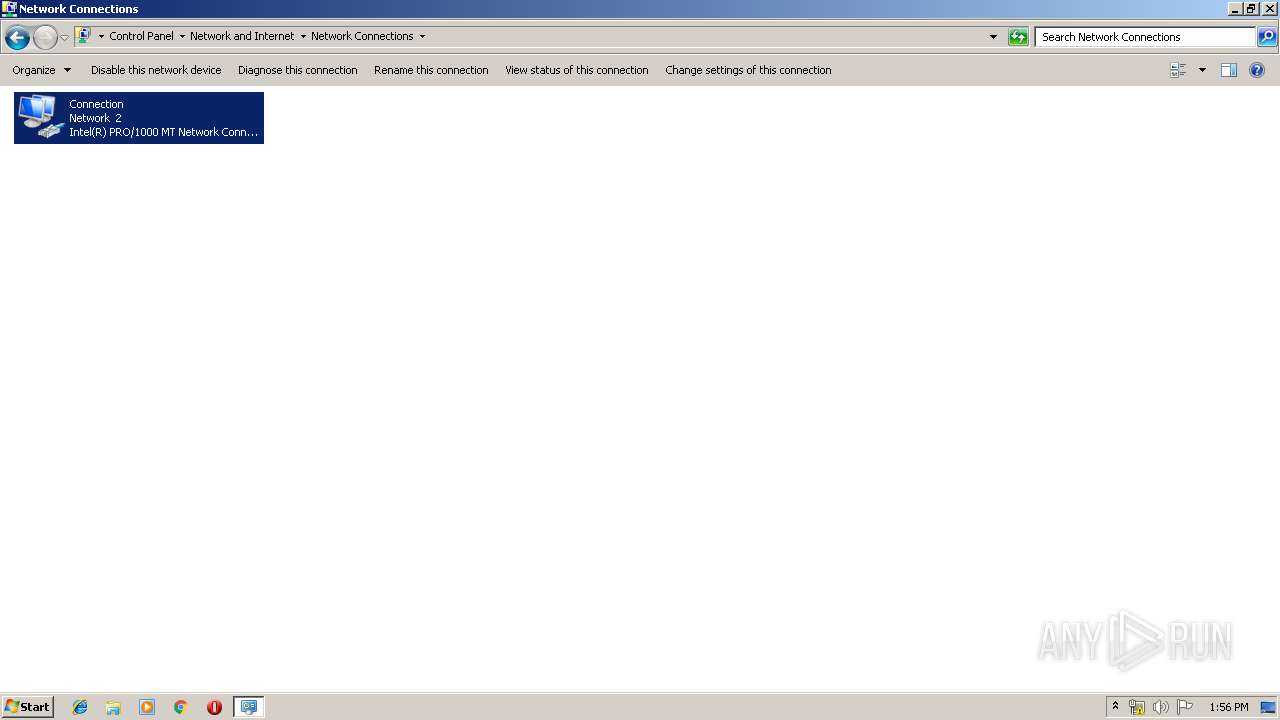
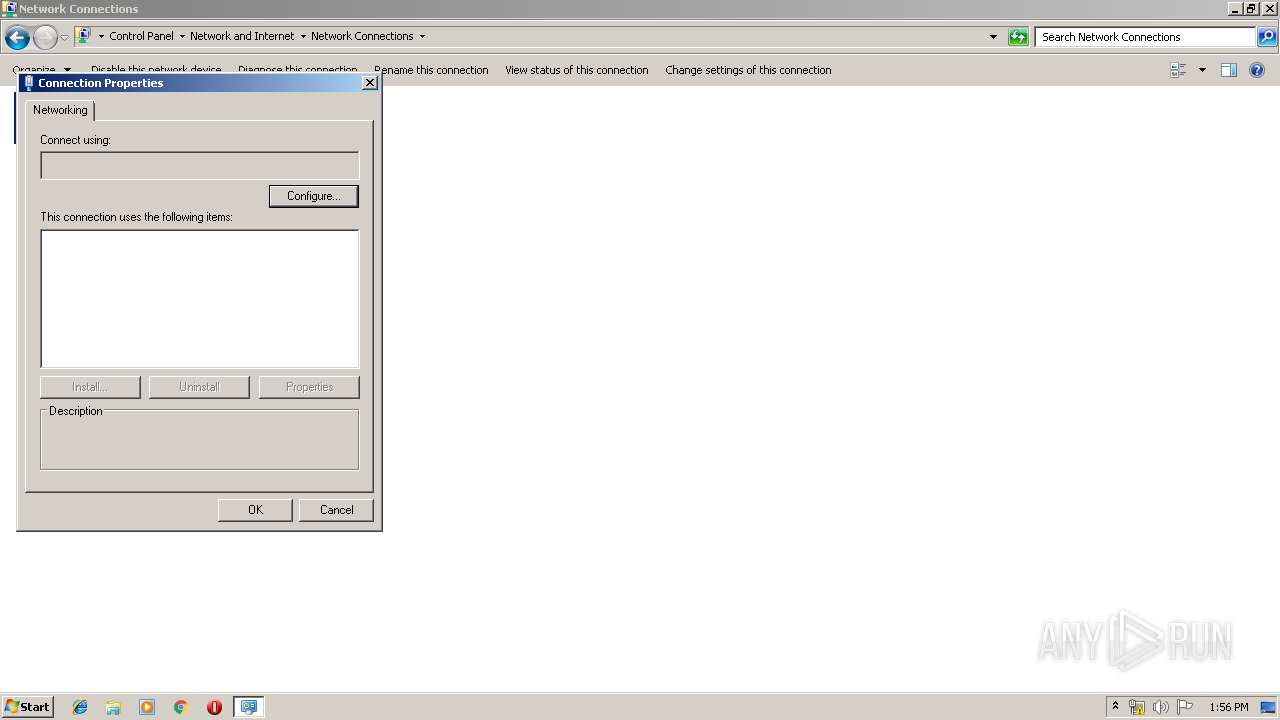
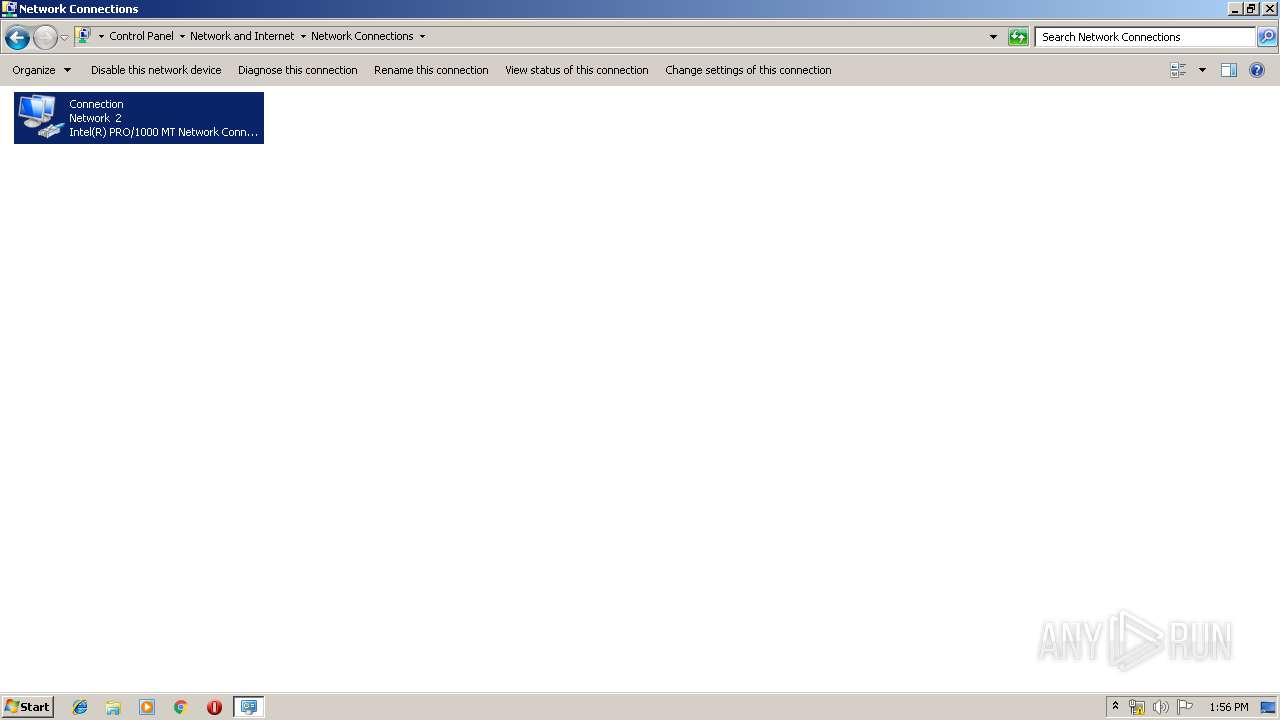
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1416 | C:\Windows\system32\DllHost.exe /Processid:{7007ACD1-3202-11D1-AAD2-00805FC1270E} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1600 | "C:\Users\admin\AppData\Local\Temp\2.exe" | C:\Users\admin\AppData\Local\Temp\2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.1.30.00 Modules
| |||||||||||||||
Total events
205
Read events
148
Write events
56
Delete events
1
Modification events
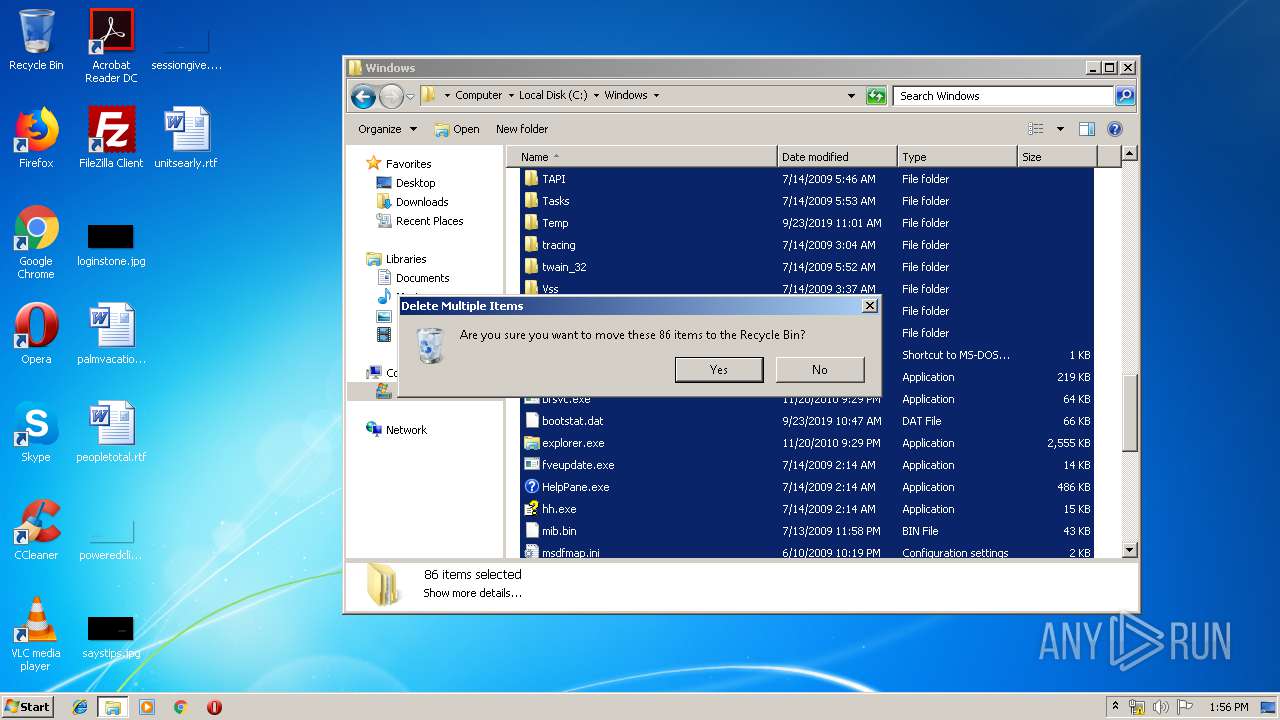
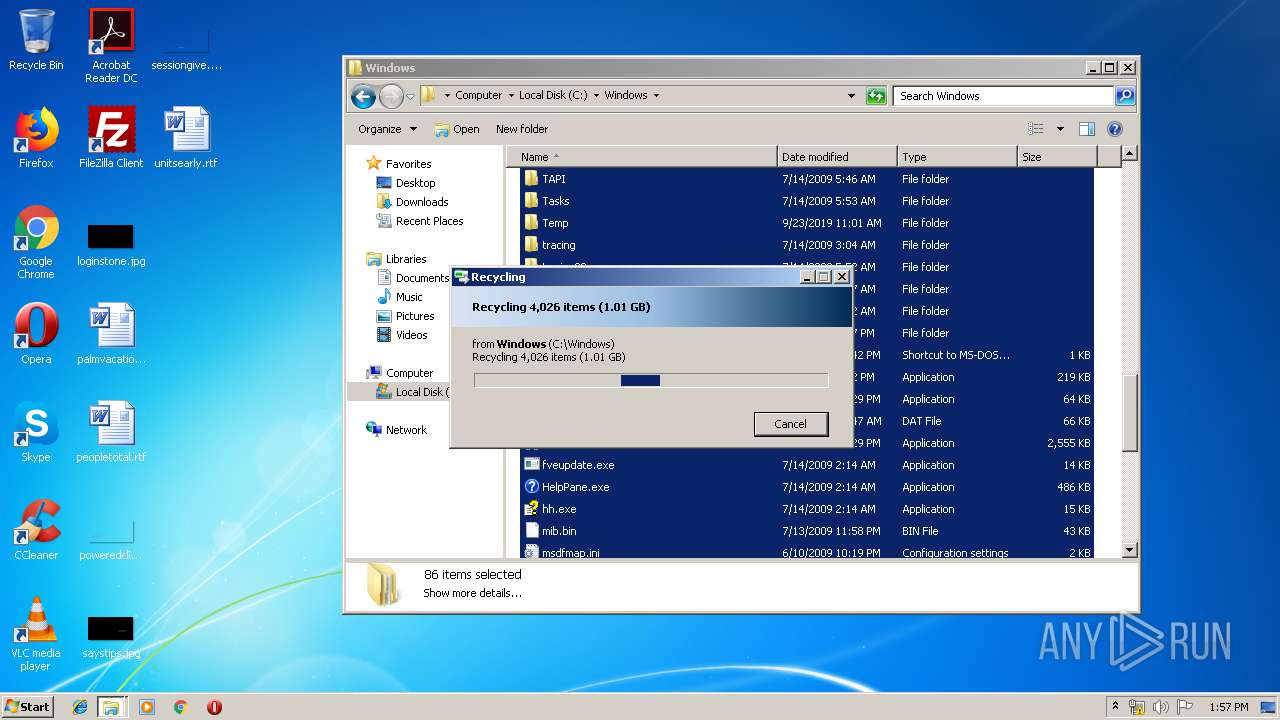
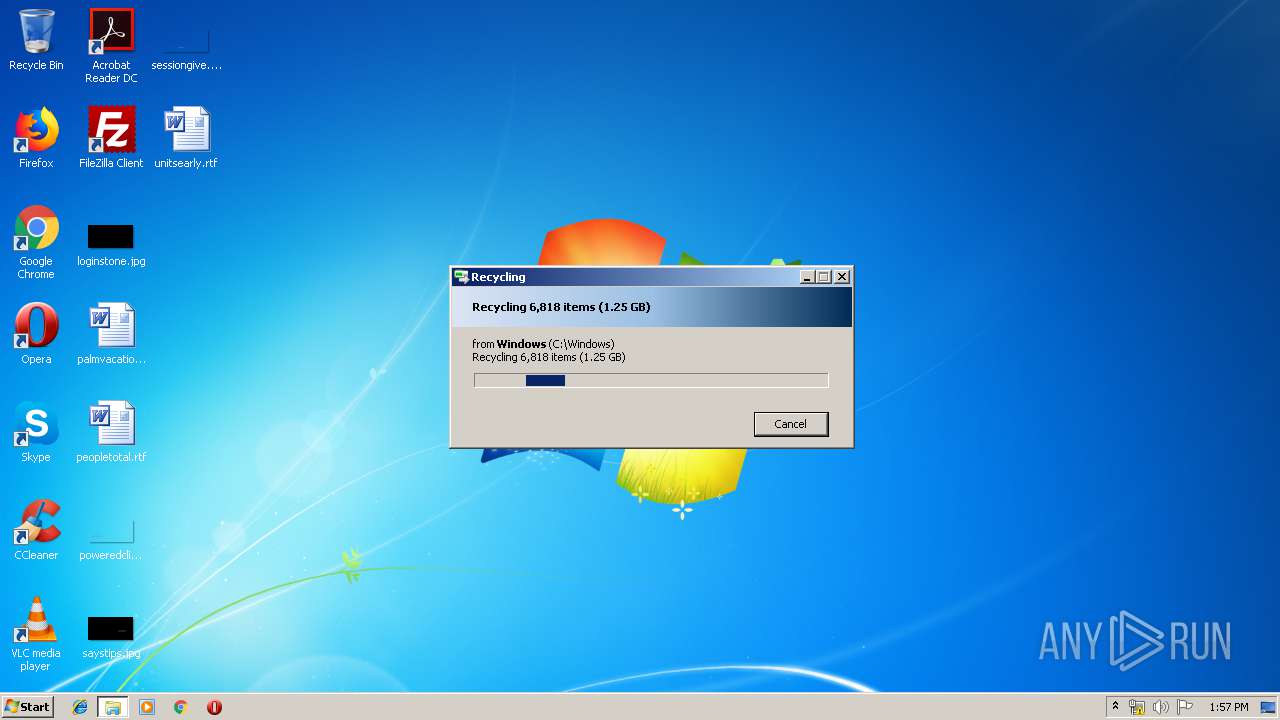
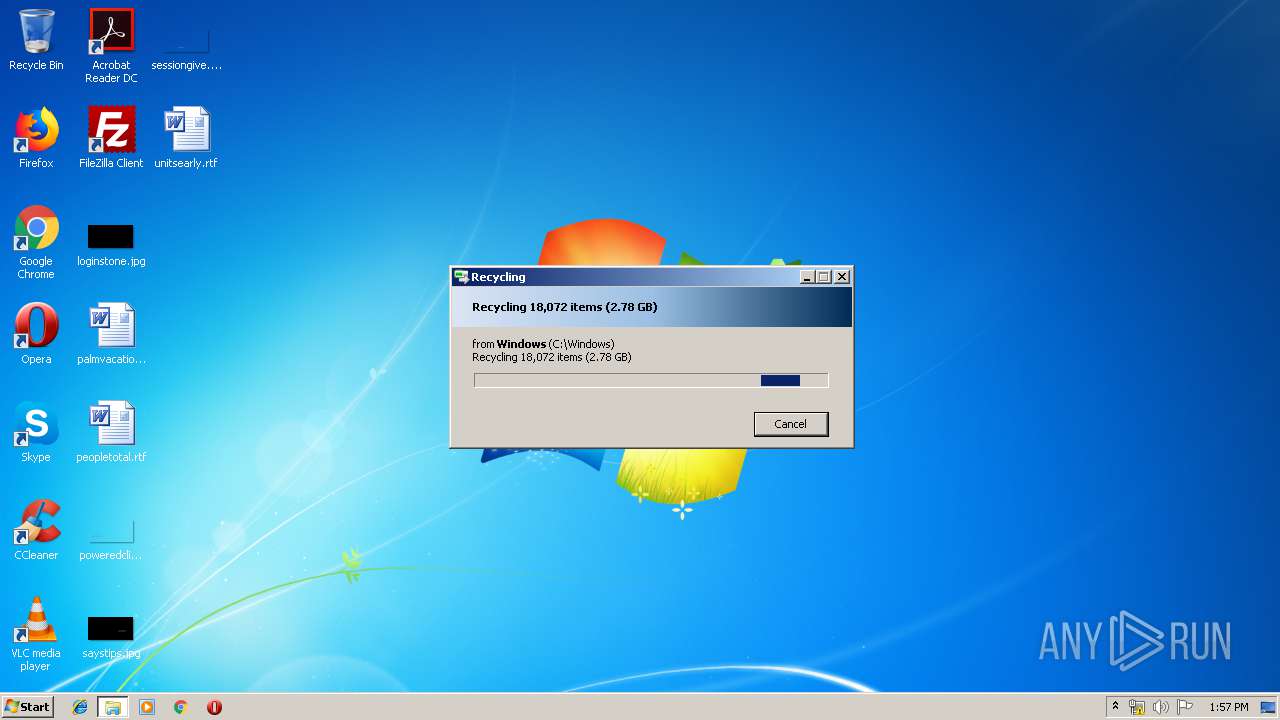
| (PID) Process: | (1600) 2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1600) 2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (1600) 2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (1600) 2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (1600) 2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (1600) 2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
| (PID) Process: | (1600) 2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\2_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1600) 2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\2_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1600) 2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\2_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1600) 2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\2_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
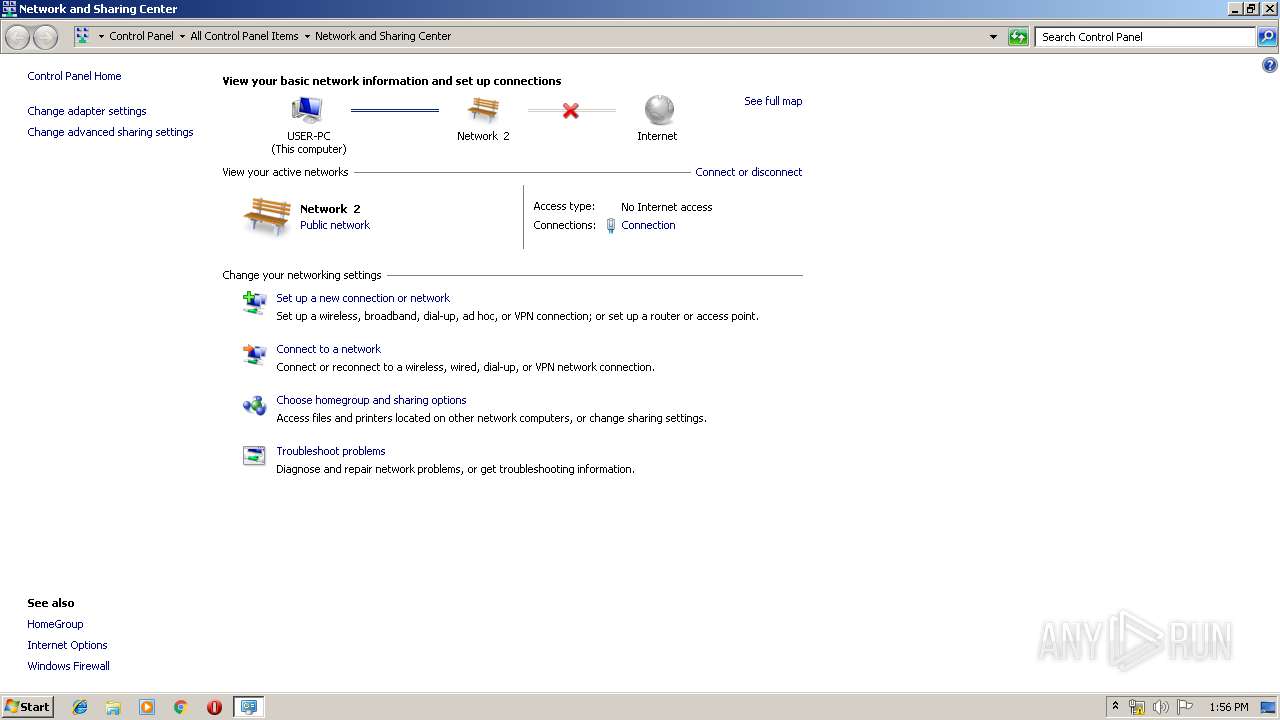
TCP/UDP connections
5
DNS requests
2
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1600 | 2.exe | 88.99.66.31:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
1600 | 2.exe | 18.205.93.0:443 | bitbucket.org | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iplogger.org |
| shared |
bitbucket.org |
| shared |
Threats
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
2.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|