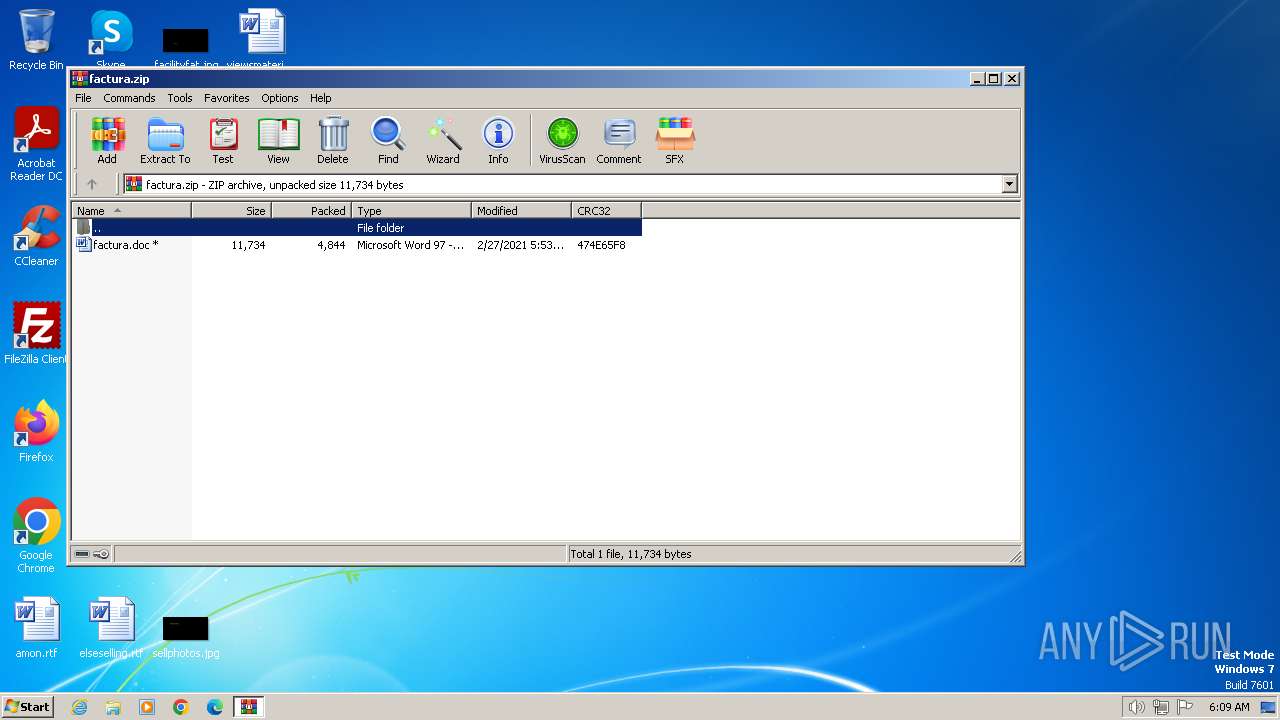
| download: | /factura.zip |
| Full analysis: | https://app.any.run/tasks/a56fc1db-8187-470b-8e98-6be9bc093f40 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2024, 05:09:46 |
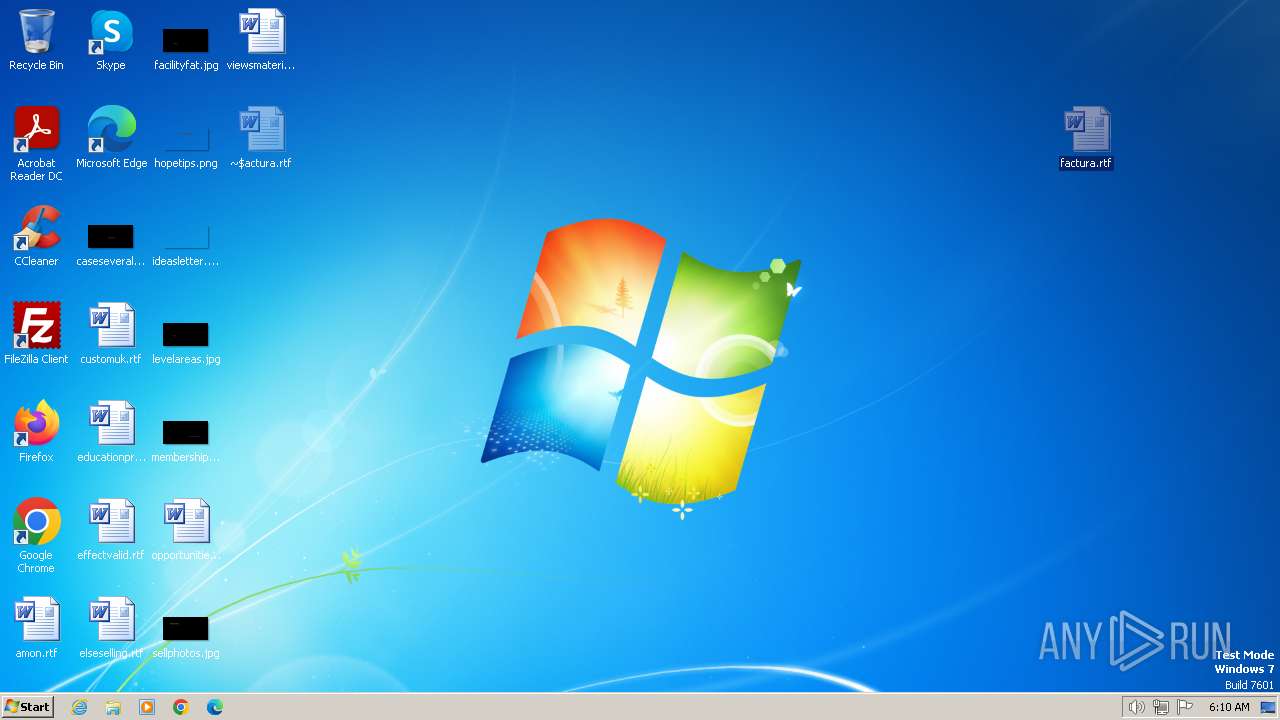
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
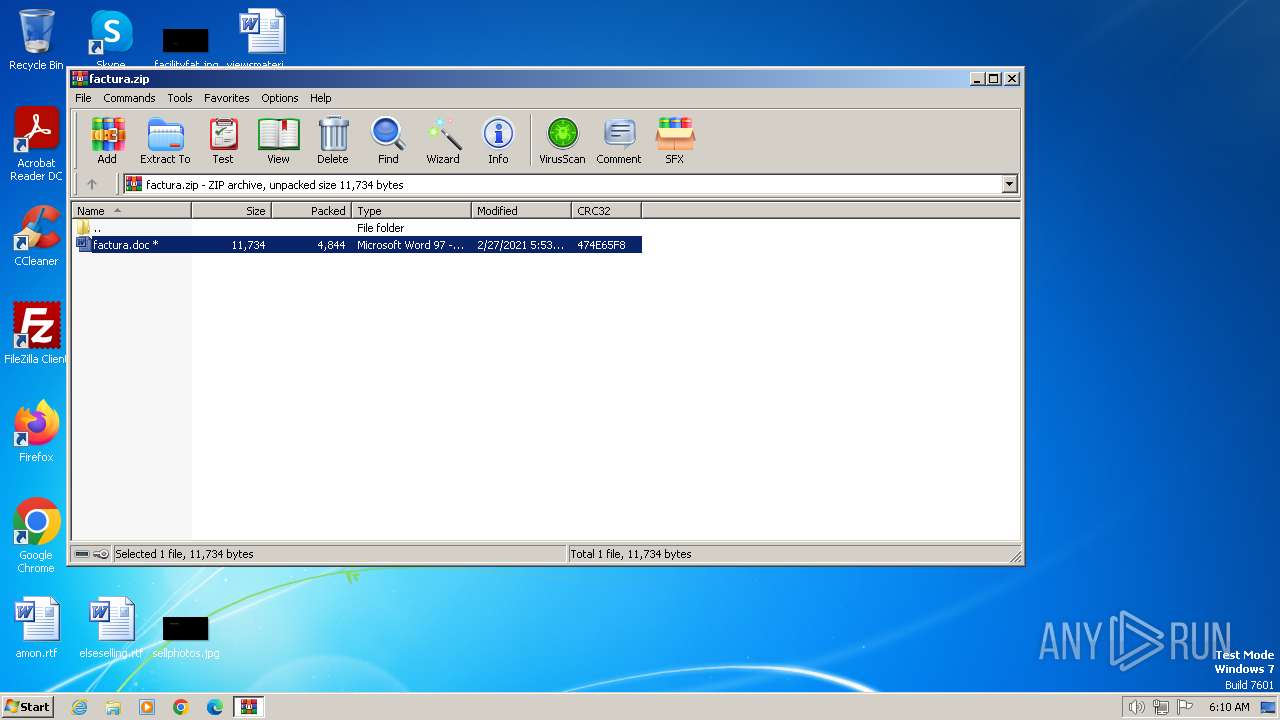
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | E109BE482E82D1BD14AF64D070D2670C |
| SHA1: | 30532B7EC2FE340939A18E8F328C17DDFA3276EF |
| SHA256: | DF9F9BED6685EEBA38DEFA87A755A0C8120F7B572094368E3AEF41829039980D |
| SSDEEP: | 96:pJpDQKSK6aetXennFi0A/Txzdxh40jV4/b23r/wF5fyY+zCGiM5oEo7k13e:p0KT6aetHfNz7iMVh/wDfyY+zCGiMPo3 |
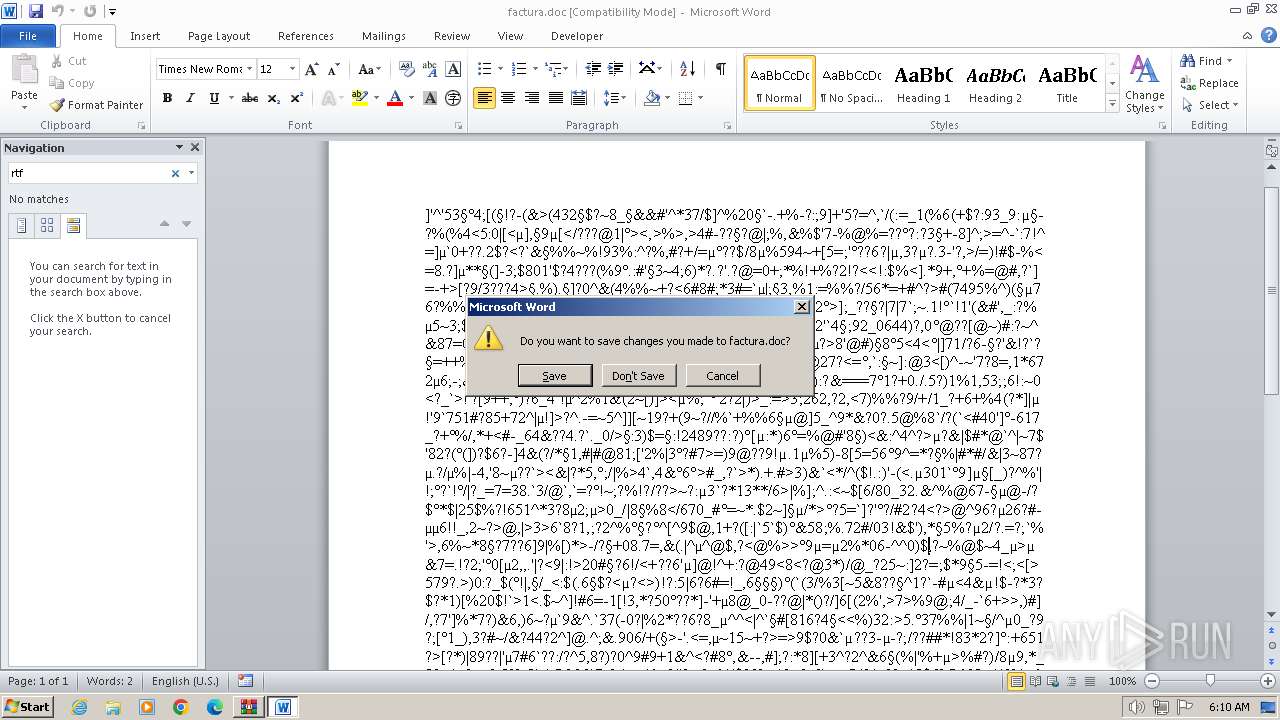
MALICIOUS
Equation Editor starts application (likely CVE-2017-11882)
- EQNEDT32.EXE (PID: 3540)
- EQNEDT32.EXE (PID: 2132)
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 2132)
- EQNEDT32.EXE (PID: 3540)
SUSPICIOUS
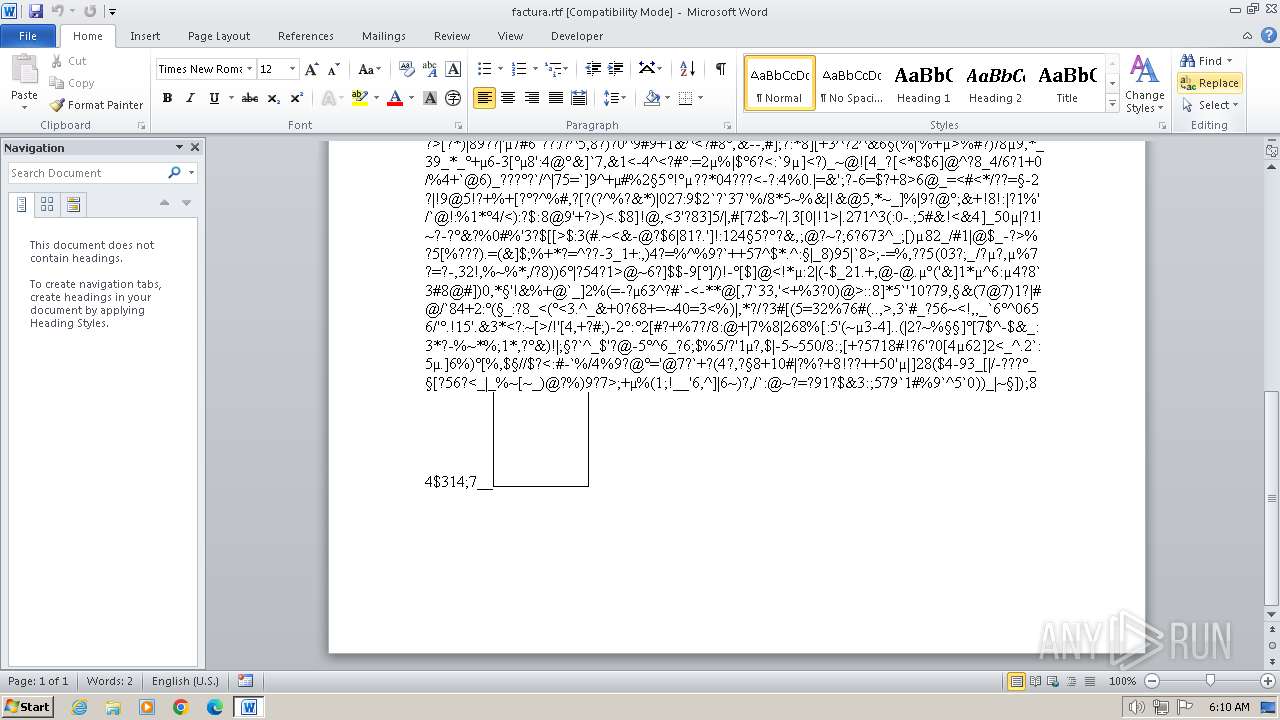
Non-standard symbols in registry
- WINWORD.EXE (PID: 2652)
- WINWORD.EXE (PID: 2888)
- WINWORD.EXE (PID: 2832)
Reads the Internet Settings
- EQNEDT32.EXE (PID: 2132)
- EQNEDT32.EXE (PID: 3540)
Reads security settings of Internet Explorer
- EQNEDT32.EXE (PID: 2132)
- EQNEDT32.EXE (PID: 3540)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 3040)
Checks supported languages
- EQNEDT32.EXE (PID: 2132)
- EQNEDT32.EXE (PID: 3540)
Reads the computer name
- EQNEDT32.EXE (PID: 2132)
- EQNEDT32.EXE (PID: 3540)
Checks proxy server information
- EQNEDT32.EXE (PID: 2132)
- EQNEDT32.EXE (PID: 3540)
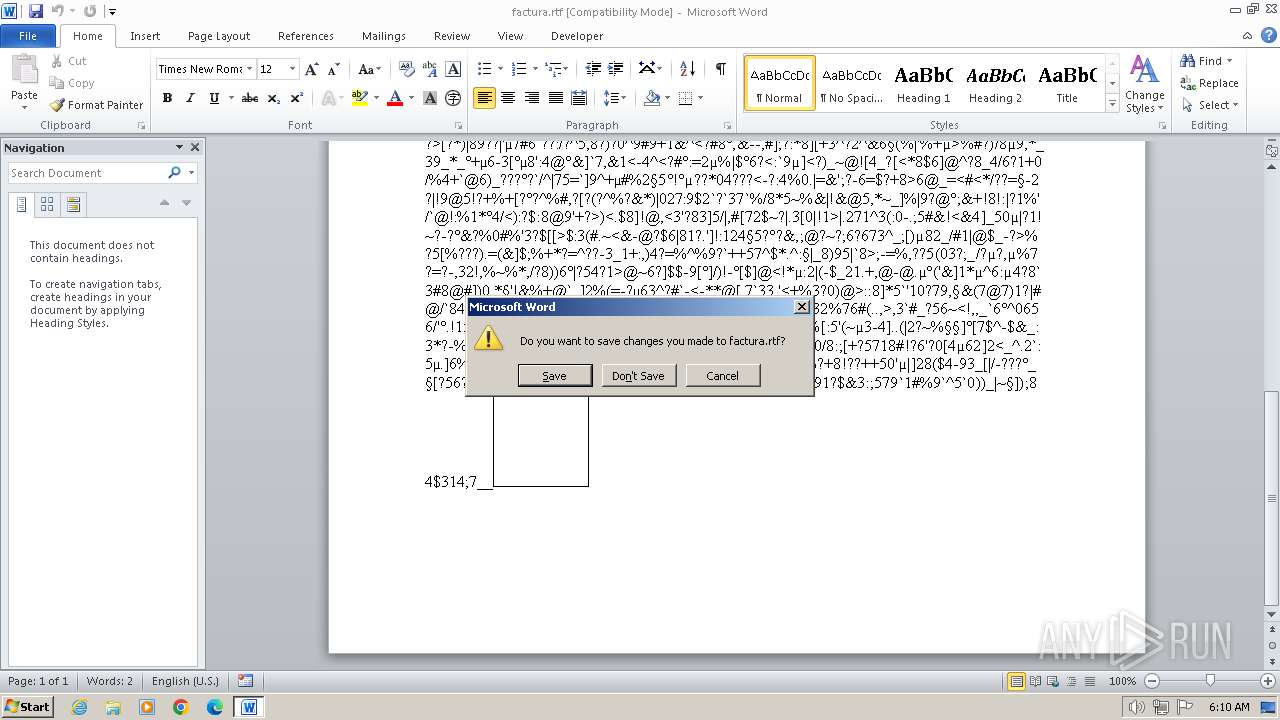
Manual execution by a user
- WINWORD.EXE (PID: 2888)
- WINWORD.EXE (PID: 2832)
Reads the machine GUID from the registry
- EQNEDT32.EXE (PID: 2132)
- EQNEDT32.EXE (PID: 3540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2021:02:27 08:53:06 |
| ZipCRC: | 0x474e65f8 |
| ZipCompressedSize: | 4844 |
| ZipUncompressedSize: | 11734 |
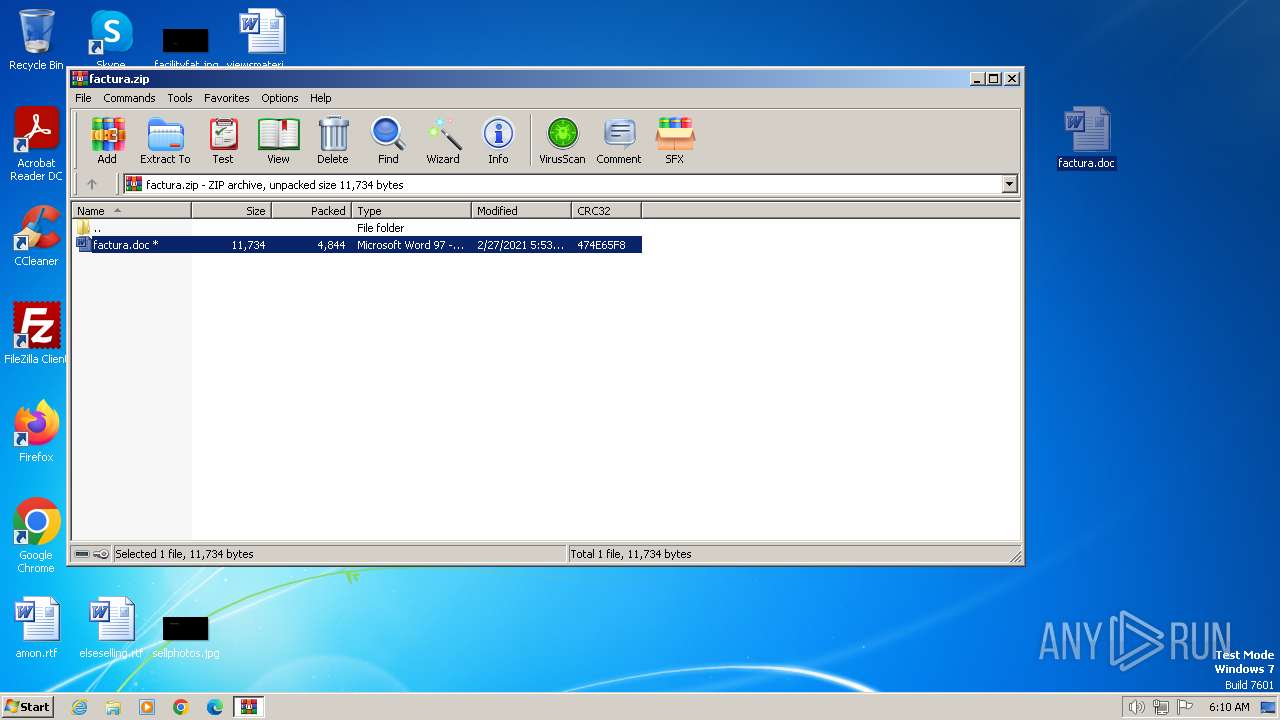
| ZipFileName: | factura.doc |
Total processes
44
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2132 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
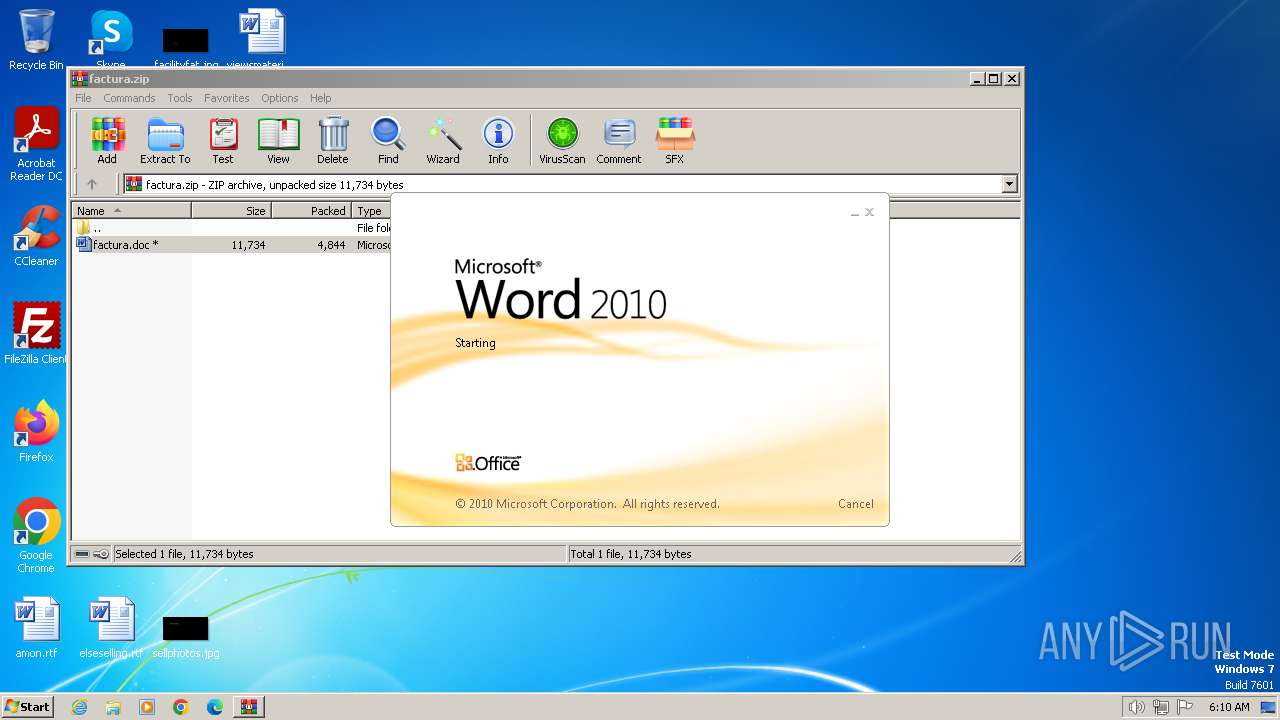
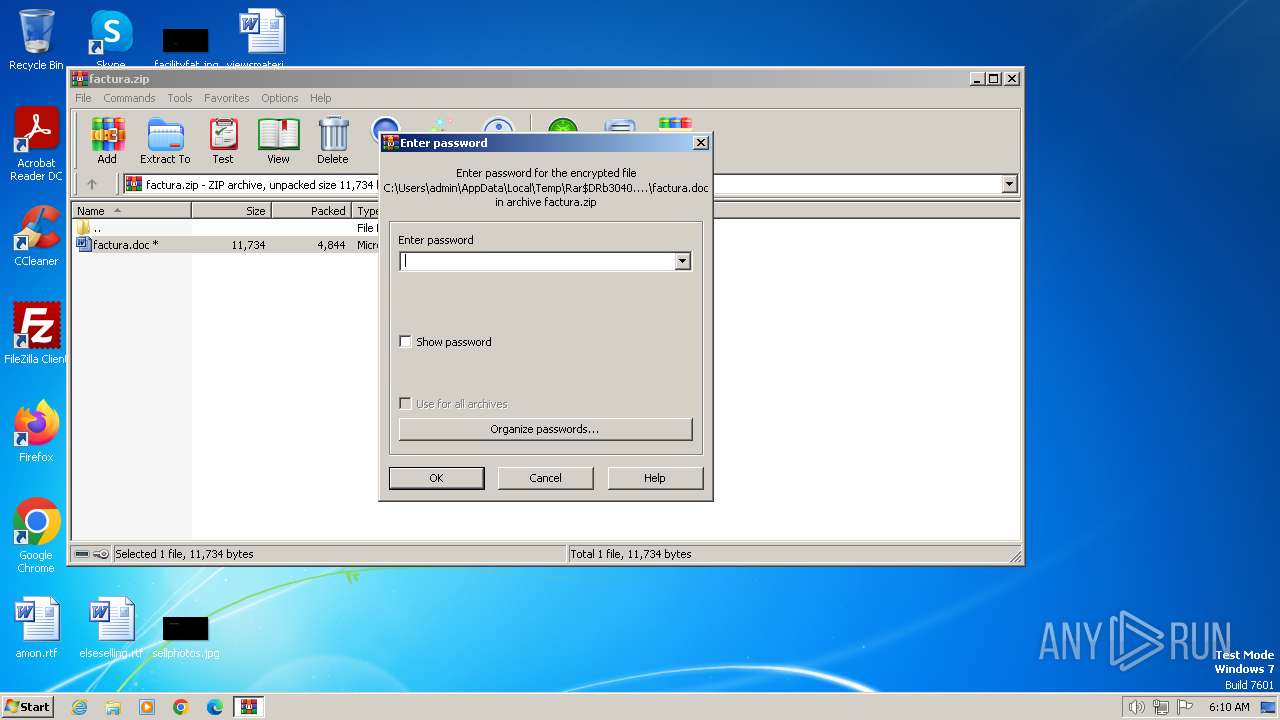
| 2652 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb3040.10928\factura.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2832 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\viewsmaterial.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2888 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\factura.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
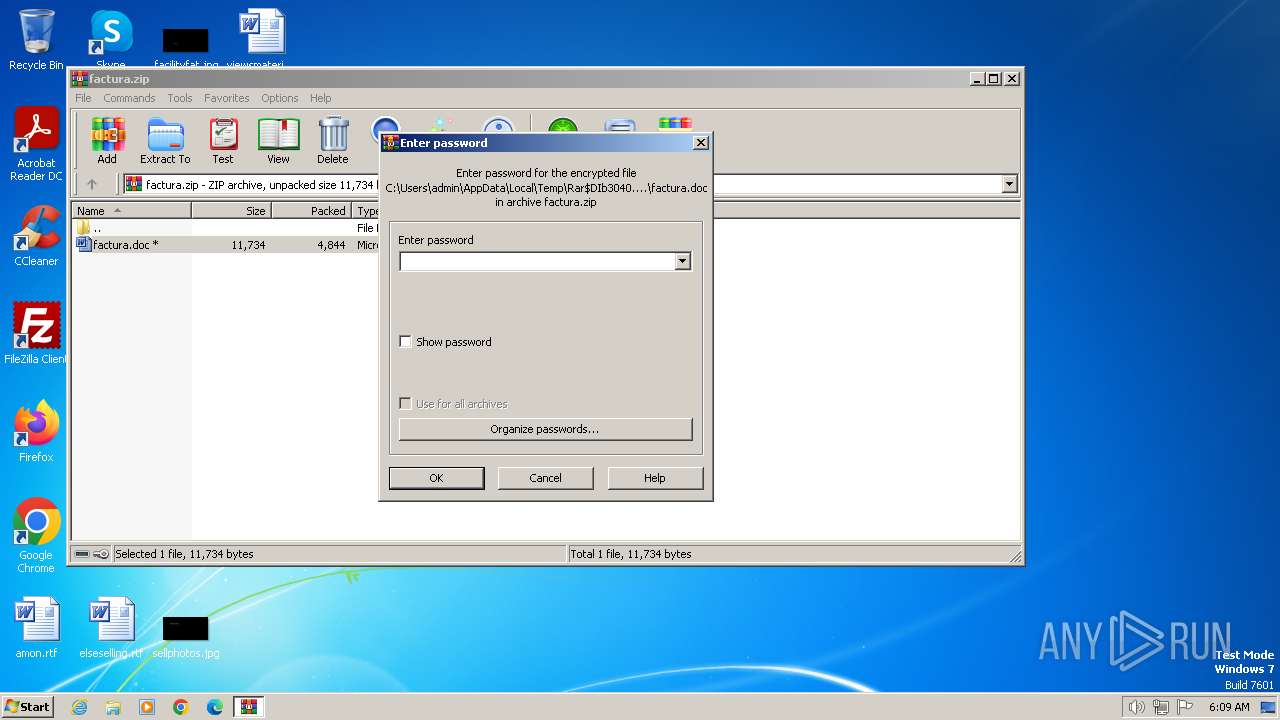
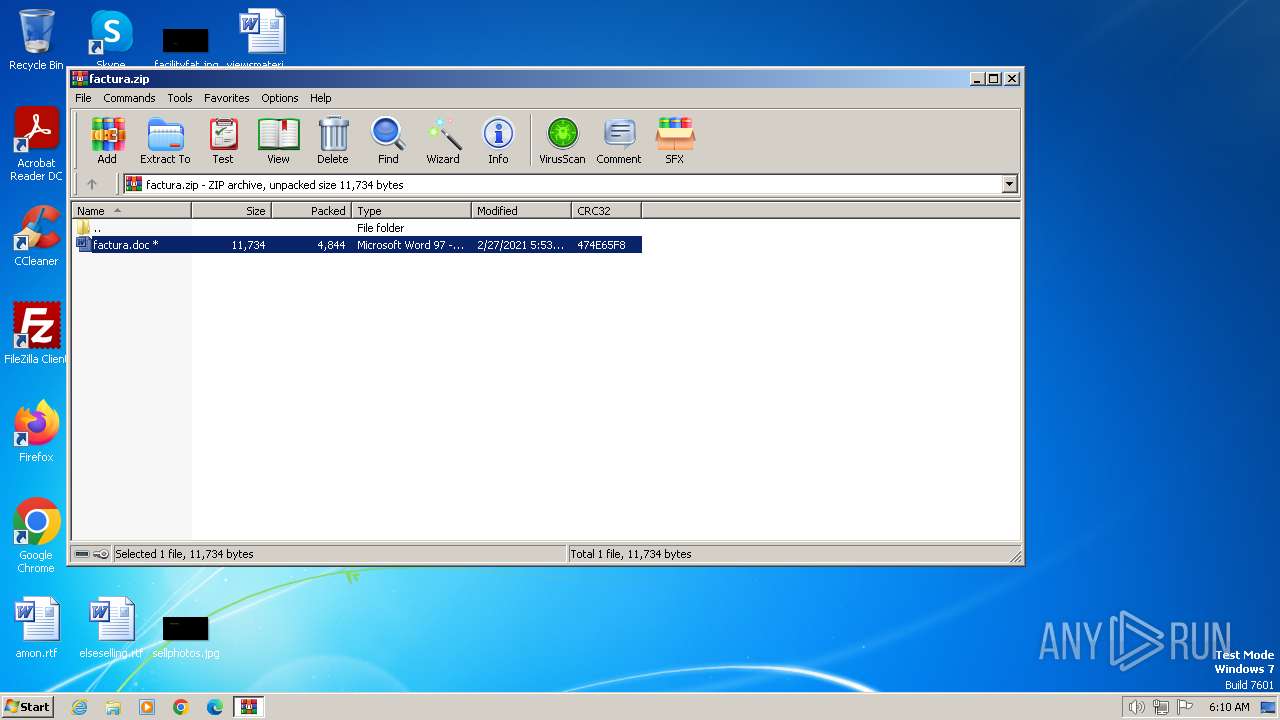
| 3040 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\factura.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3540 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 3221225547 Version: 00110900 Modules
| |||||||||||||||
Total events
22 857
Read events
21 395
Write events
580
Delete events
882
Modification events
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\factura.zip | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
11
Text files
3
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2652 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRFB83.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR773B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2832 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRB09A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2652 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{A7632872-AA0D-4D75-9ED9-EB9A6EF1A368}.tmp | binary | |
MD5:7427612B1C62216C66D5CA63A3348863 | SHA256:56C51085750EDB04713A7193B657C792D78C5900687A9EAD3735185D46124121 | |||
| 2652 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{2DADFFA3-1CB6-455C-8CCF-A0E2A989EB8A}.tmp | binary | |
MD5:430222558FD33DA814E58422E326420C | SHA256:577AA6BA5B8644F65ADA7655383323453ADF4C27B205CDAF0C765651EAEDA5F7 | |||
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\factura.rtf.LNK | lnk | |
MD5:D02FCFF0DD669746D232A5B429721826 | SHA256:15E0CE4E1232B4BC2BB807339726F7715508D16973B64D0F2162E6522B12432D | |||
| 2652 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:01382D8CD815C969E64D2EFE288CA2A2 | SHA256:0F79E5435496DD8C28ADE1E8351940934FB5BCB09CBF6BB13DFA1E534C849097 | |||
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:E6EA5C7AF015C6D2367FC29B01C1A999 | SHA256:A19357C328D242C474174C32AE6F6E88AFD6CC656C4360F88F7ECEA24FBF28AE | |||
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:8E68161760C26E29BD1787657264001E | SHA256:CD1D084158D2E1326076A45CDC634657D67DDC7FD970A3E304C7E14B9231B3E5 | |||
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{3F658801-FD5E-4229-A3F3-7A20822207C0}.tmp | binary | |
MD5:661EF4D1D455D63415D7294A4FB20846 | SHA256:5181E44E6414D8CACE02D11658BBC23DFE00A858D8E2C351CA07C172511A5AFD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
6
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2132 | EQNEDT32.EXE | GET | 404 | 185.36.74.48:80 | http://seed-bc.com/juop4/plwr/mklo/rbn/jan2.exe | unknown | — | — | unknown |
3540 | EQNEDT32.EXE | GET | 404 | 185.36.74.48:80 | http://seed-bc.com/juop4/plwr/mklo/rbn/jan2.exe | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2132 | EQNEDT32.EXE | 185.36.74.48:80 | seed-bc.com | Fastweb | IT | unknown |
3540 | EQNEDT32.EXE | 185.36.74.48:80 | seed-bc.com | Fastweb | IT | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
seed-bc.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2132 | EQNEDT32.EXE | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
3540 | EQNEDT32.EXE | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |