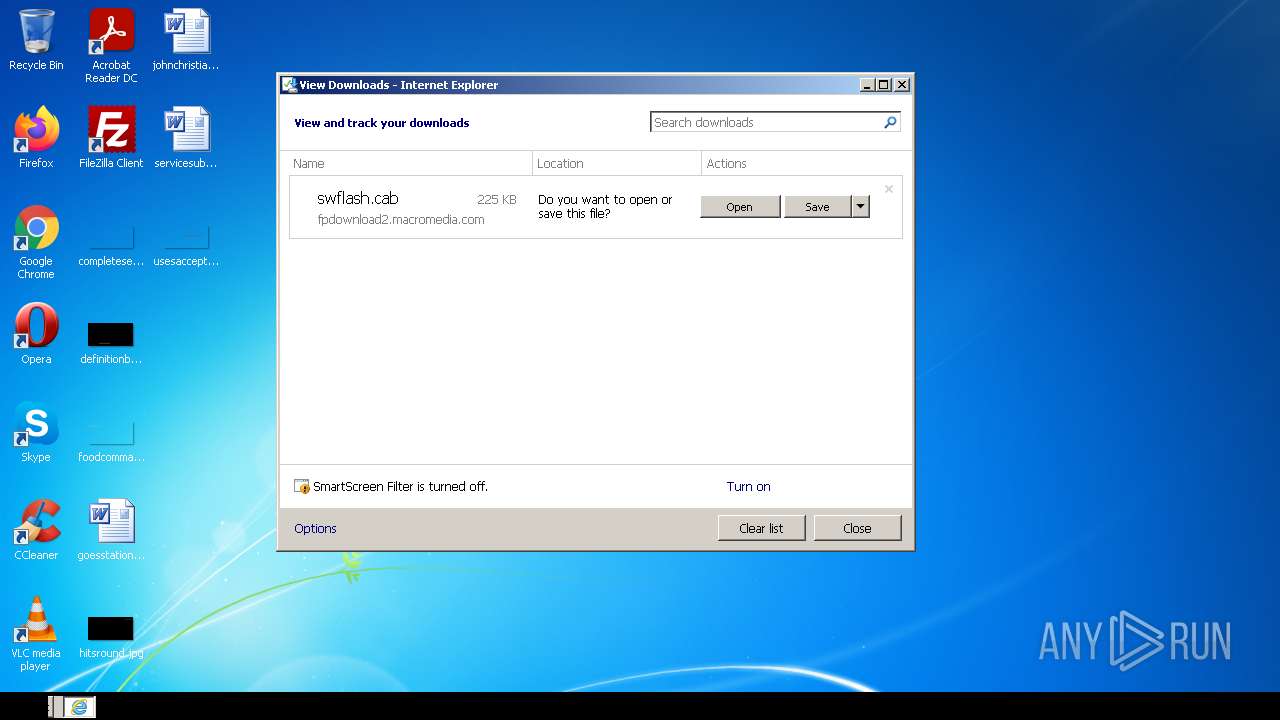
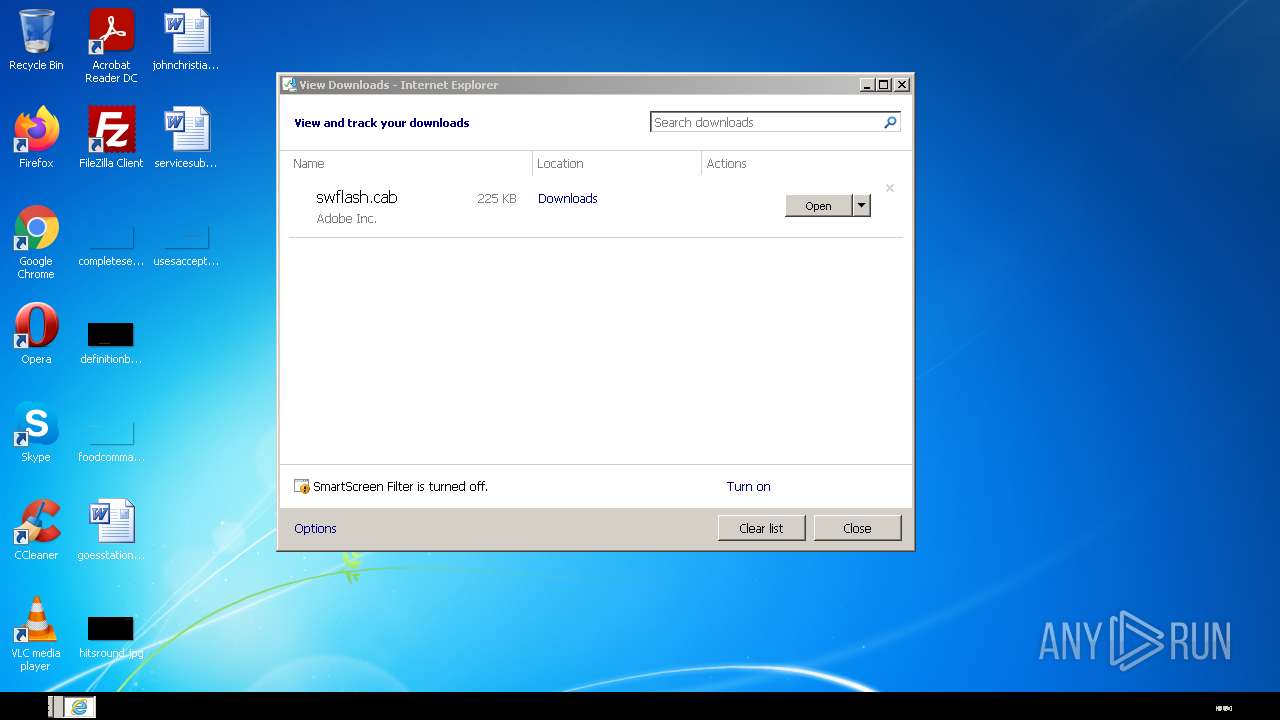
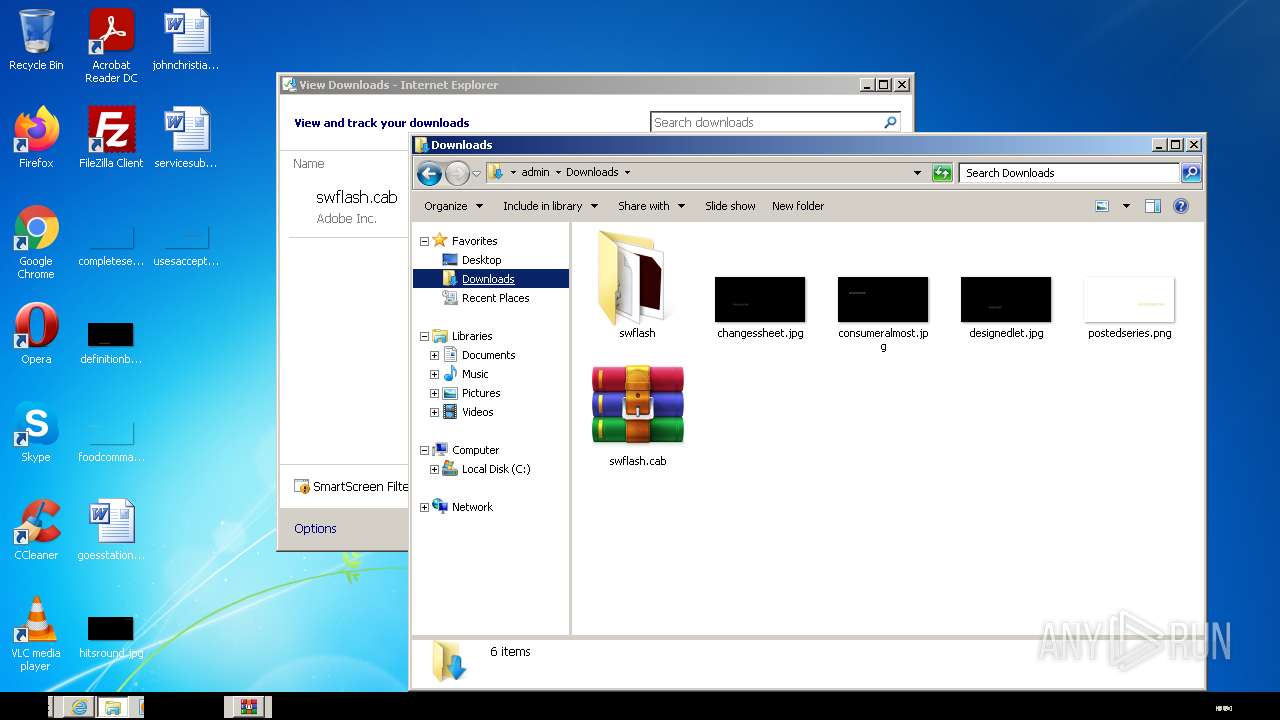
| URL: | http://fpdownload2.macromedia.com/get/shockwave/cabs/flash/swflash.cab |
| Full analysis: | https://app.any.run/tasks/47240e97-2ffb-4acf-9327-ae92bec7f344 |
| Verdict: | Malicious activity |
| Analysis date: | January 26, 2022, 08:12:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 984058DDF0848DD17C9D84B11C79B2BF |
| SHA1: | D24F347214266A347D1FAD714DBDD58C09617D5B |
| SHA256: | DF8A6AFF454CF23202CB3426AE3735EFCE8EA3AF81A6E2819DC2D44D0E1C92A5 |
| SSDEEP: | 3:N1KYZJ5rvyqRlmd+ETEHn:CYZJ5rKqlmQEIH |
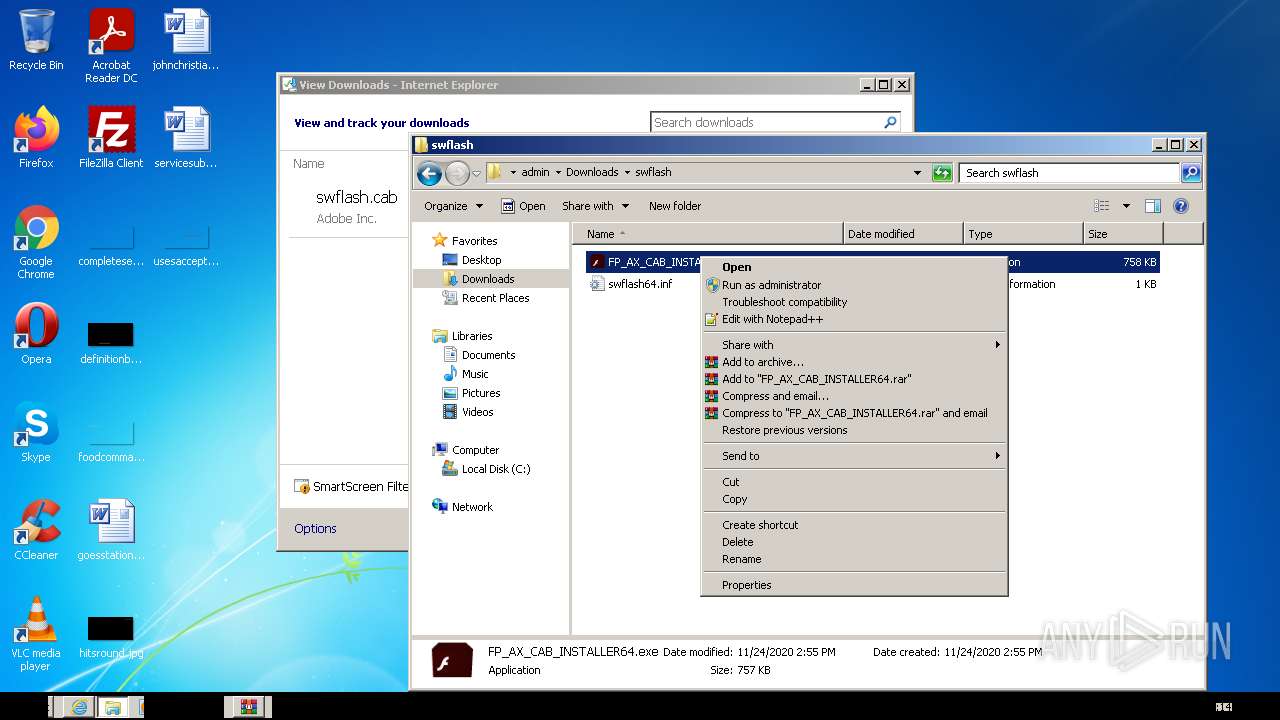
MALICIOUS
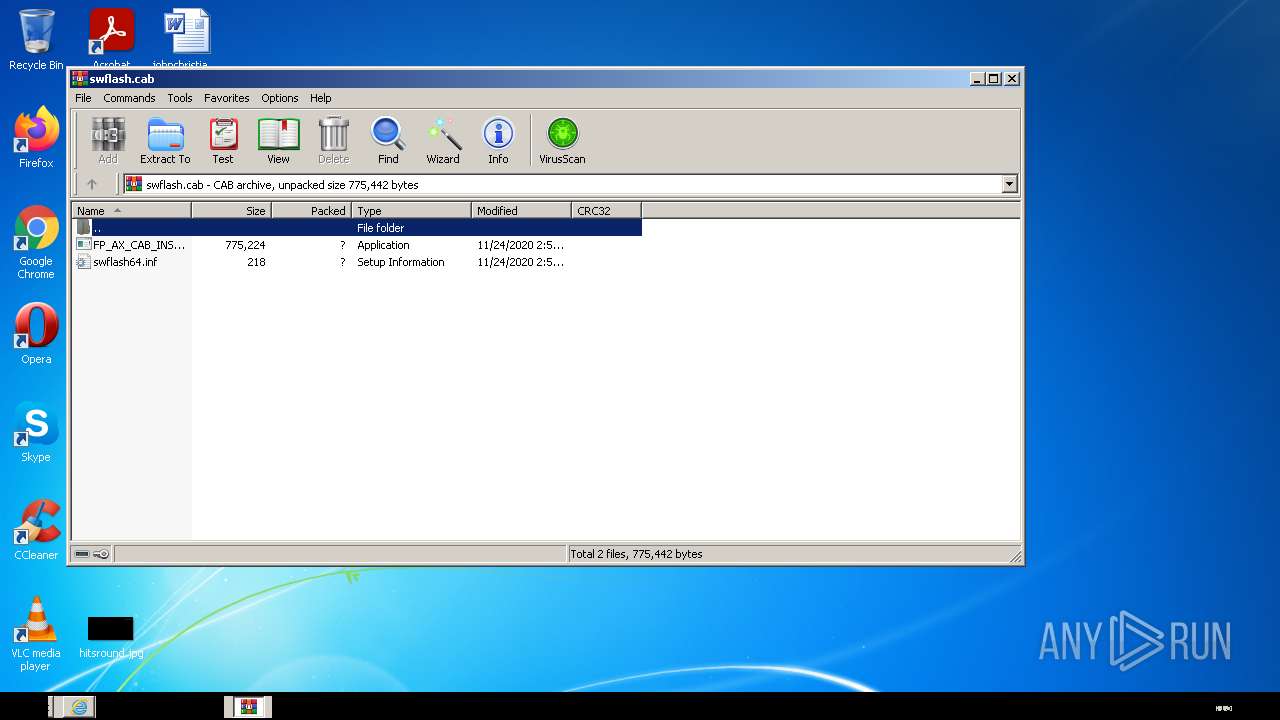
Application was dropped or rewritten from another process
- FP_AX_CAB_INSTALLER64.exe (PID: 2820)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2504)
- iexplore.exe (PID: 1272)
Checks supported languages
- WinRAR.exe (PID: 1076)
- FP_AX_CAB_INSTALLER64.exe (PID: 2820)
Reads the computer name
- WinRAR.exe (PID: 1076)
- FP_AX_CAB_INSTALLER64.exe (PID: 2820)
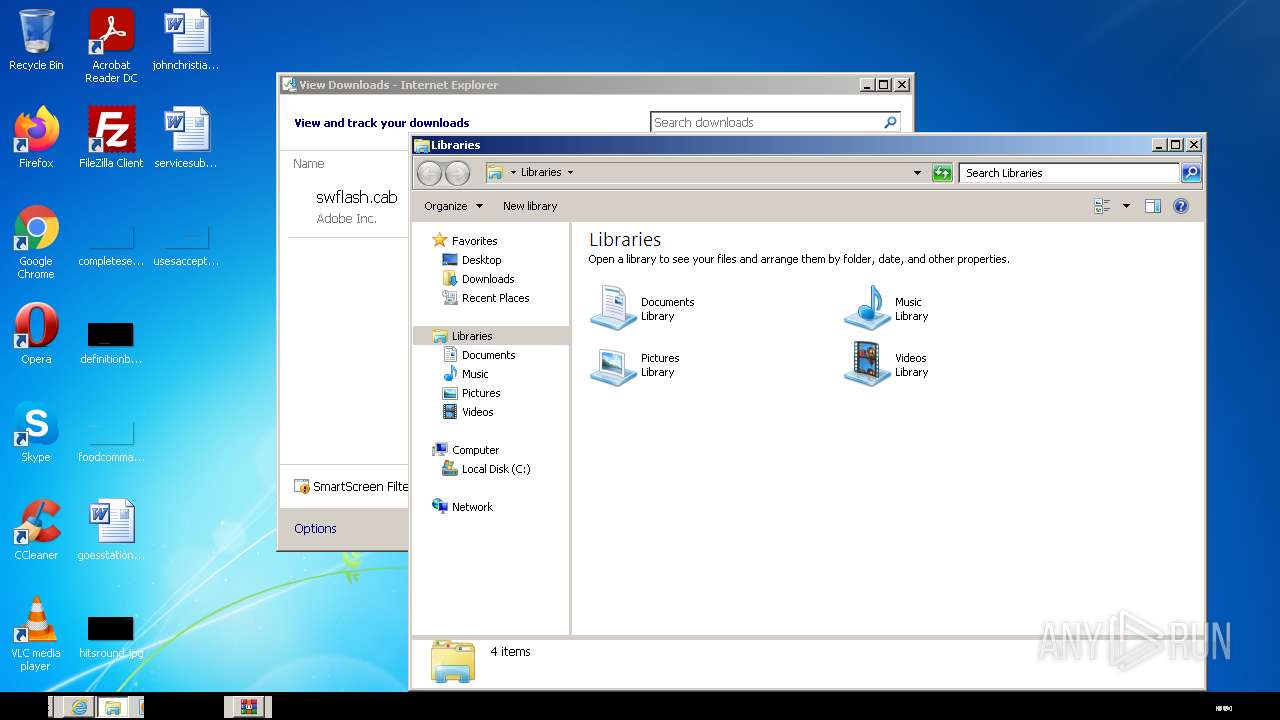
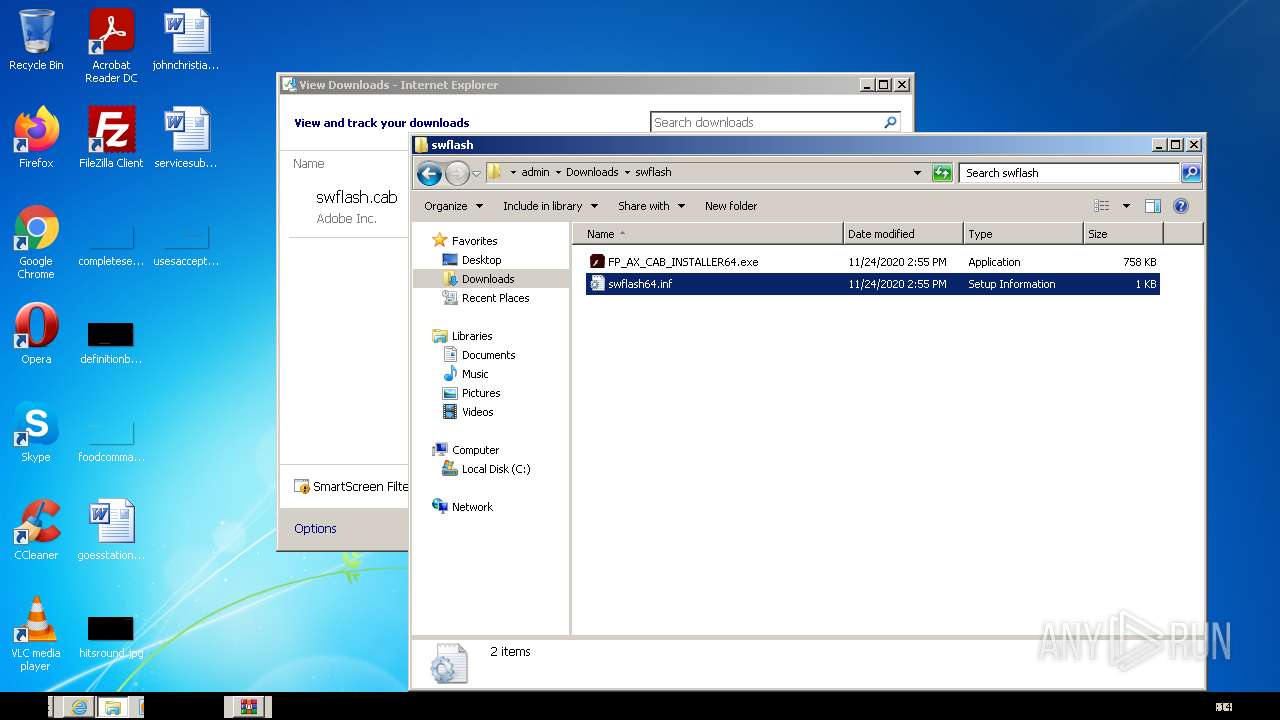
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1076)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1076)
Removes files from Windows directory
- FP_AX_CAB_INSTALLER64.exe (PID: 2820)
Starts Internet Explorer
- FP_AX_CAB_INSTALLER64.exe (PID: 2820)
INFO
Checks supported languages
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 2504)
- explorer.exe (PID: 2368)
- iexplore.exe (PID: 3740)
- iexplore.exe (PID: 1272)
Changes internet zones settings
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 3740)
Reads the date of Windows installation
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 3740)
Reads the computer name
- iexplore.exe (PID: 2504)
- iexplore.exe (PID: 3148)
- explorer.exe (PID: 2368)
- iexplore.exe (PID: 3740)
- iexplore.exe (PID: 1272)
Checks Windows Trust Settings
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 1272)
- iexplore.exe (PID: 3740)
Reads settings of System Certificates
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 1272)
- iexplore.exe (PID: 3740)
Application launched itself
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 3740)
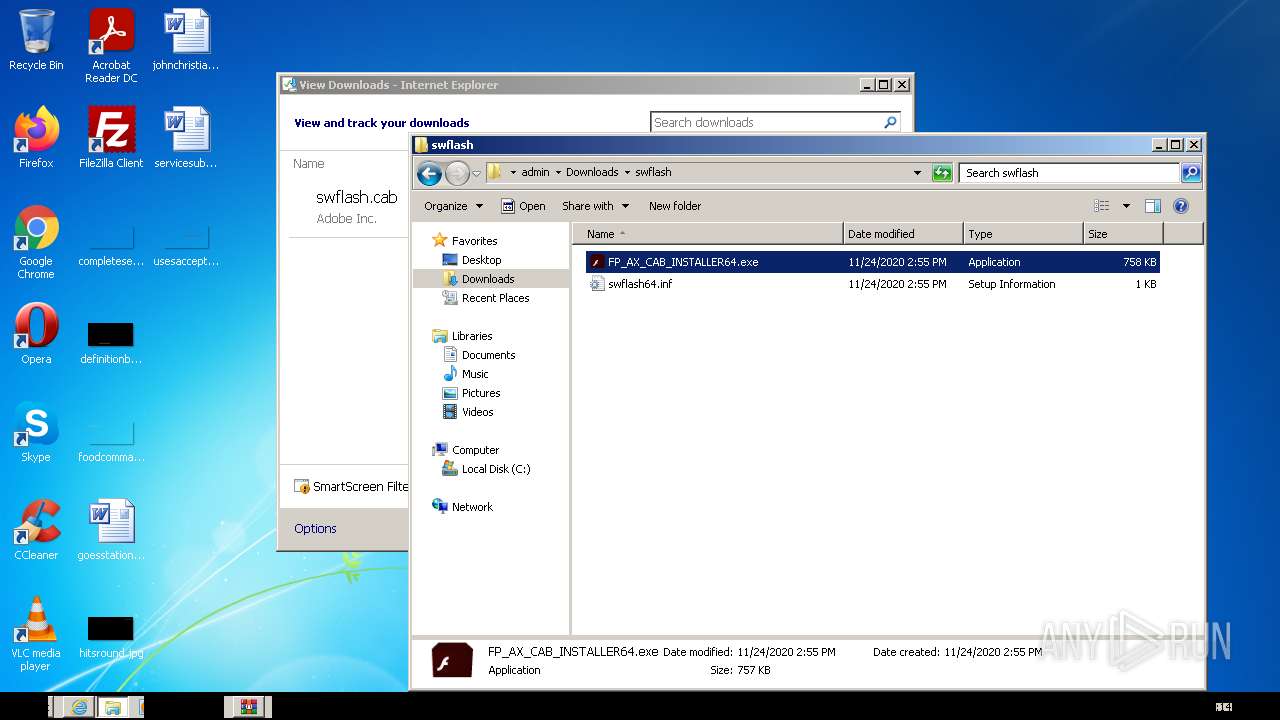
Manual execution by user
- explorer.exe (PID: 2368)
- FP_AX_CAB_INSTALLER64.exe (PID: 2820)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3148)
Changes settings of System certificates
- iexplore.exe (PID: 3148)
Creates files in the user directory
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 1272)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3148)
Reads internet explorer settings
- iexplore.exe (PID: 1272)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
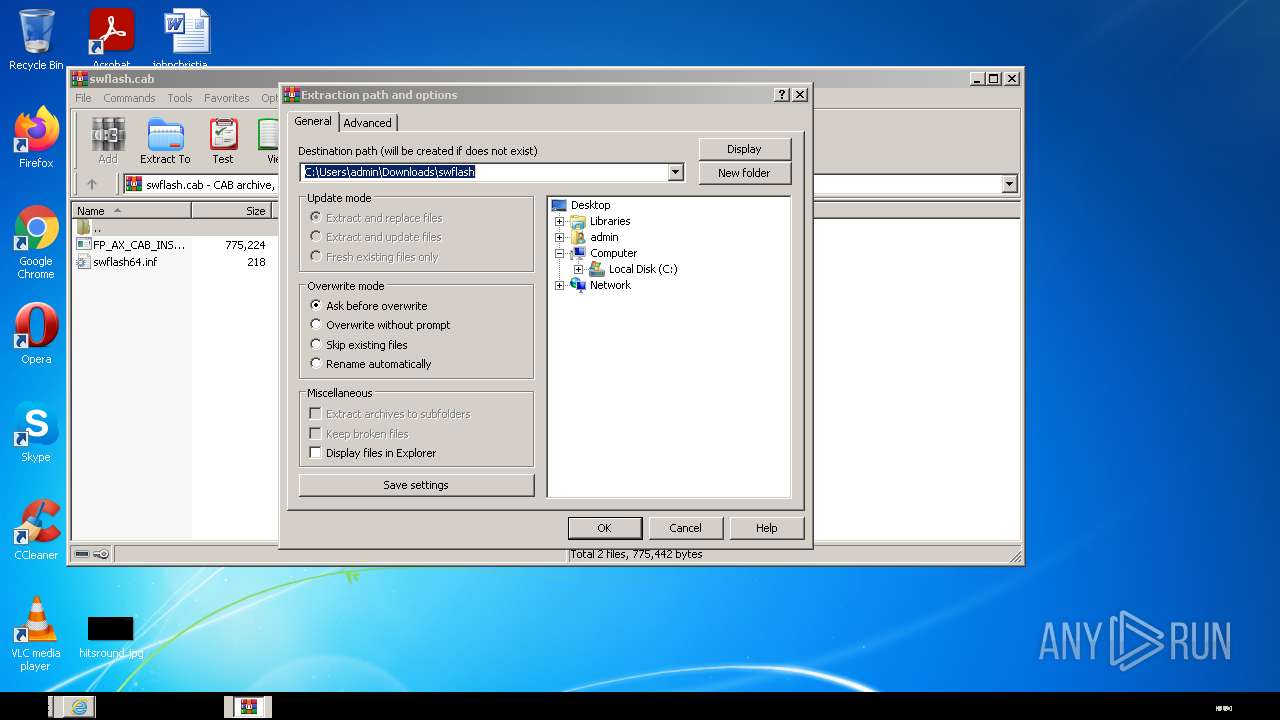
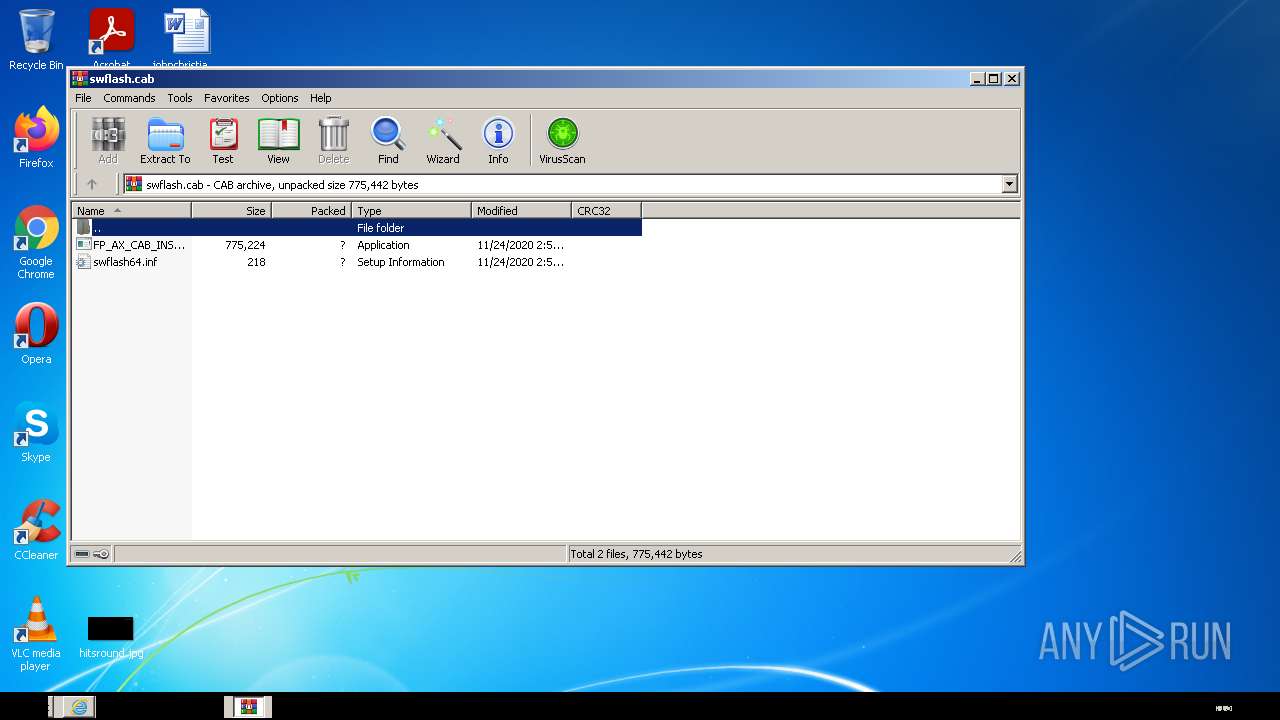
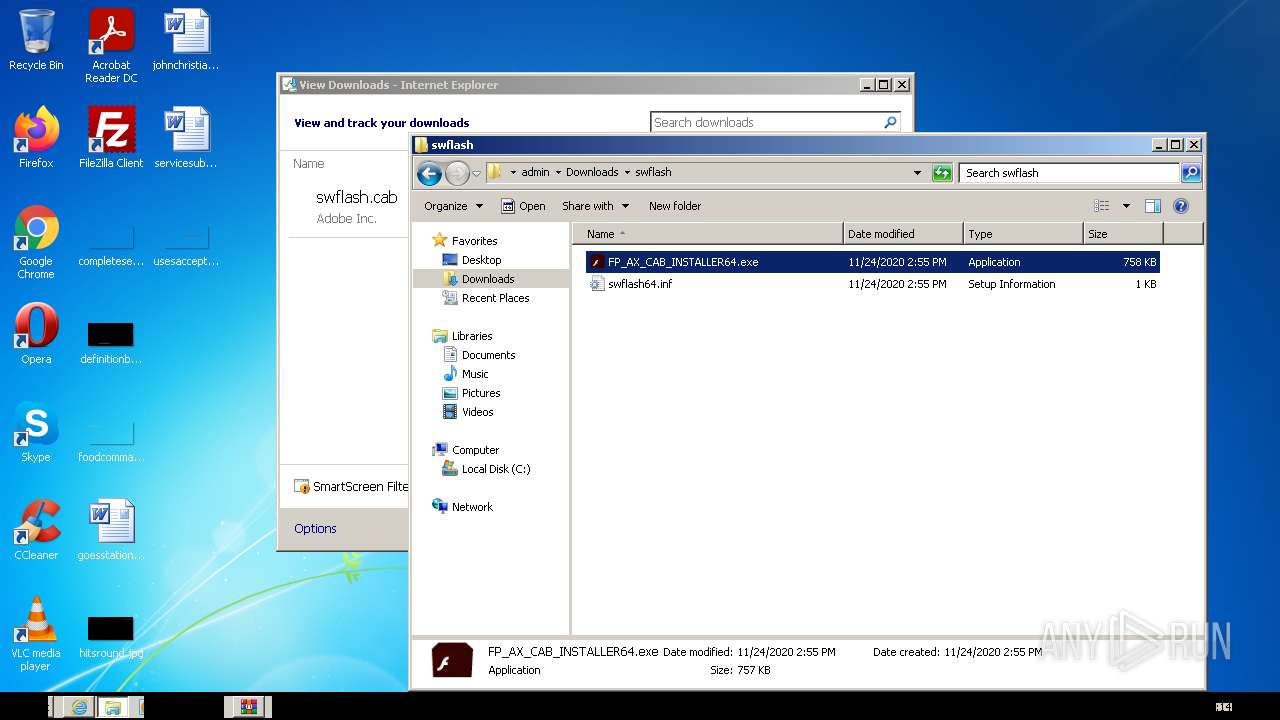
| 1076 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\swflash.cab" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1272 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3740 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
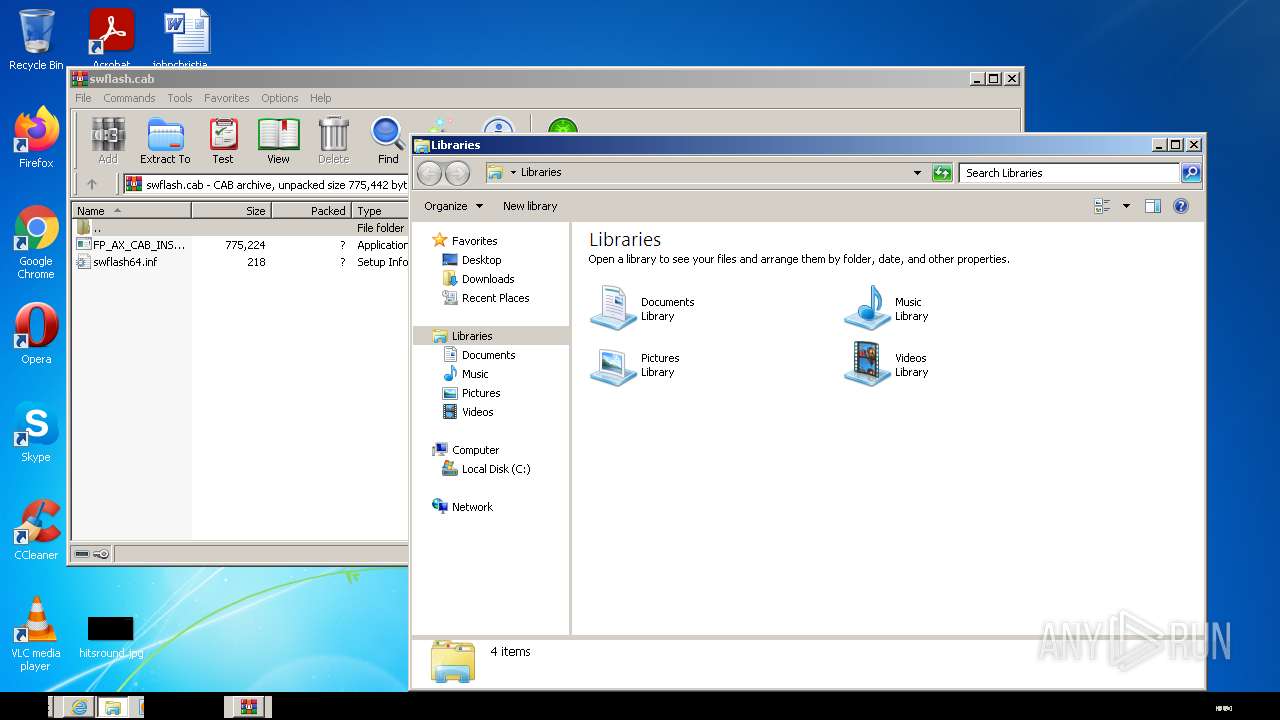
| 2368 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3148 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2820 | "C:\Users\admin\Downloads\swflash\FP_AX_CAB_INSTALLER64.exe" | C:\Users\admin\Downloads\swflash\FP_AX_CAB_INSTALLER64.exe | Explorer.EXE | ||||||||||||
User: admin Company: Adobe Integrity Level: HIGH Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,465 Modules
| |||||||||||||||
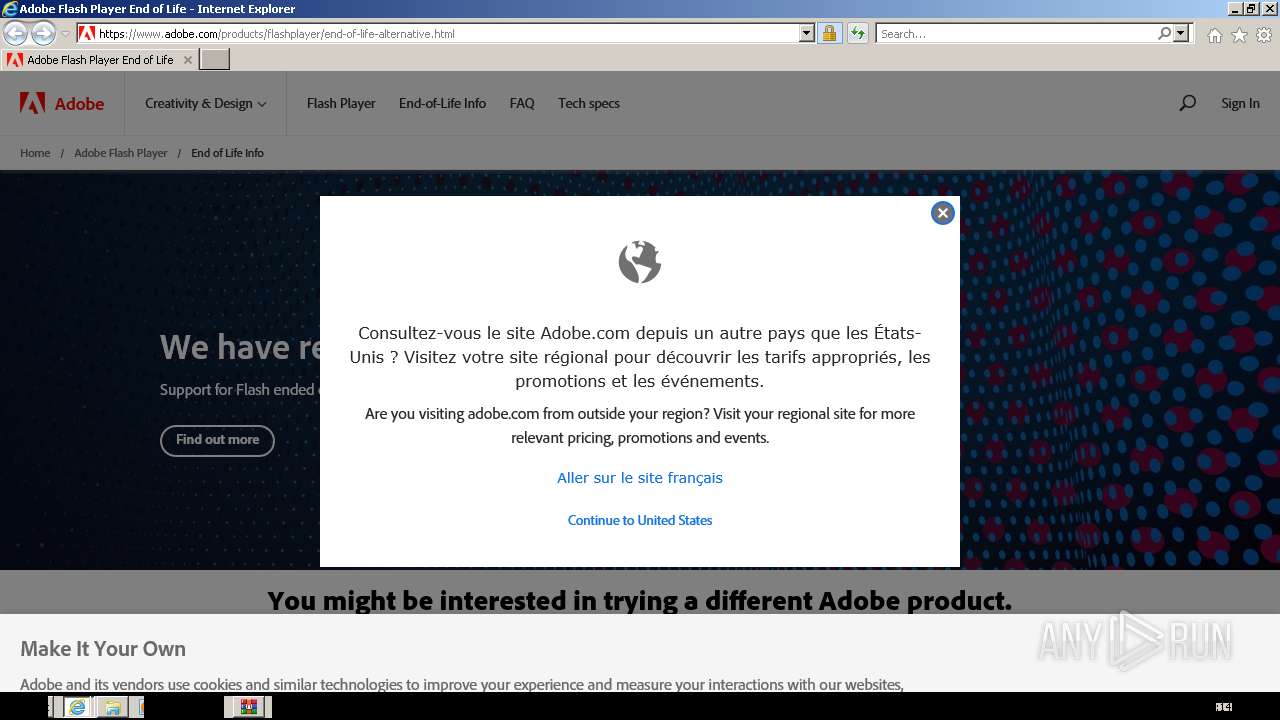
| 3148 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://fpdownload2.macromedia.com/get/shockwave/cabs/flash/swflash.cab" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3740 | "C:\Program Files\Internet Explorer\iexplore.exe" https://get3.adobe.com/flashplayer/update/activex | C:\Program Files\Internet Explorer\iexplore.exe | FP_AX_CAB_INSTALLER64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
20 482
Read events
20 205
Write events
273
Delete events
4
Modification events
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30937740 | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30937740 | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
28
Text files
101
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\swflash[1].cab | compressed | |
MD5:— | SHA256:— | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB977F73CCFBA8614.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{BD80C707-7E7F-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\NH2XRQ99.txt | text | |
MD5:— | SHA256:— | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\0DQS7WXV.txt | text | |
MD5:— | SHA256:— | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\LNYQD8SM.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
71
DNS requests
31
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1272 | iexplore.exe | GET | 301 | 2.22.32.164:80 | http://get3.adobe.com/flashplayer/update/activex/ | unknown | — | — | whitelisted |
3148 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1272 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
3148 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
1272 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1272 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1272 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAPcXPipNqNLgWgvPi2Uwnc%3D | US | der | 471 b | whitelisted |
1272 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAiUAg1J7ie9IHbDN8v5koI%3D | US | der | 471 b | whitelisted |
1272 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAxxknKj%2B5cHRgkONH6PG5I%3D | US | der | 471 b | whitelisted |
1272 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAR01OSeHJor2P8HiOg6iA4%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2504 | iexplore.exe | 92.123.225.11:80 | fpdownload2.macromedia.com | Akamai International B.V. | — | suspicious |
2504 | iexplore.exe | 92.123.225.35:80 | fpdownload2.macromedia.com | Akamai International B.V. | — | suspicious |
3148 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3148 | iexplore.exe | 95.140.236.0:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | GB | whitelisted |
3148 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3148 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
3148 | iexplore.exe | 104.111.242.51:443 | go.microsoft.com | Akamai International B.V. | NL | unknown |
3148 | iexplore.exe | 13.92.246.37:443 | query.prod.cms.msn.com | Microsoft Corporation | US | whitelisted |
1272 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fpdownload2.macromedia.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |
query.prod.cms.msn.com |
| whitelisted |
get3.adobe.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2504 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |