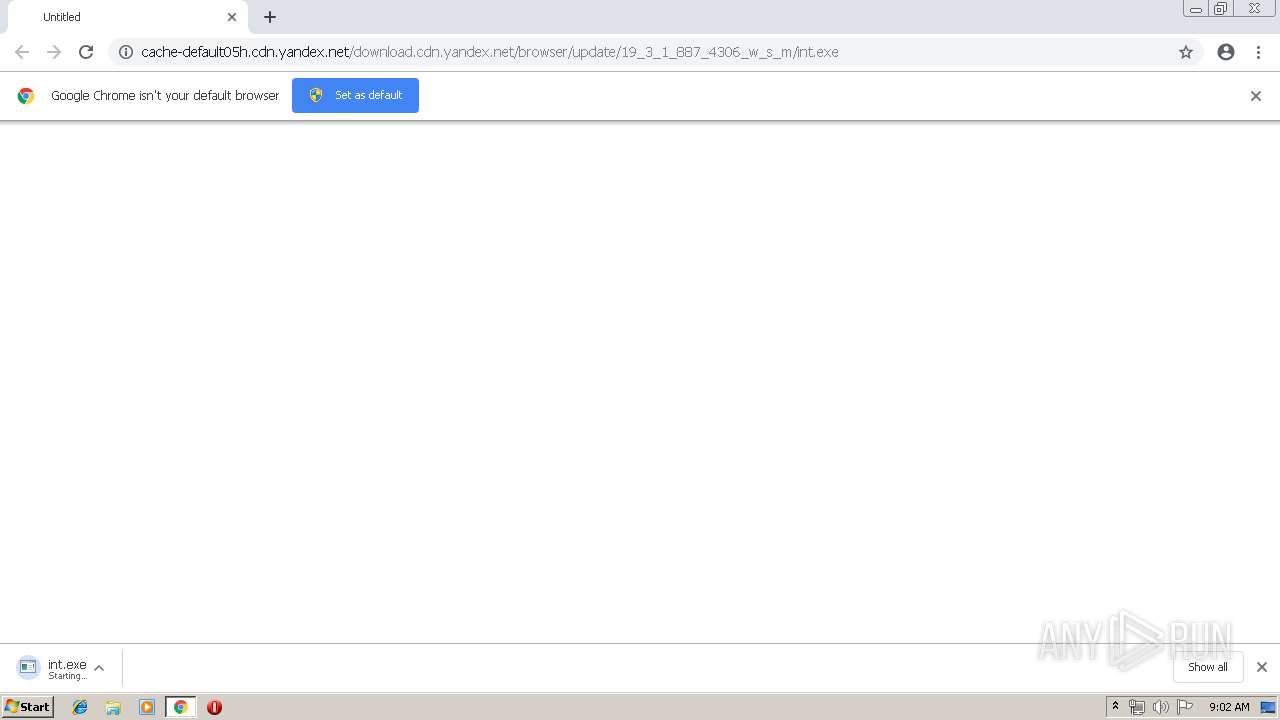
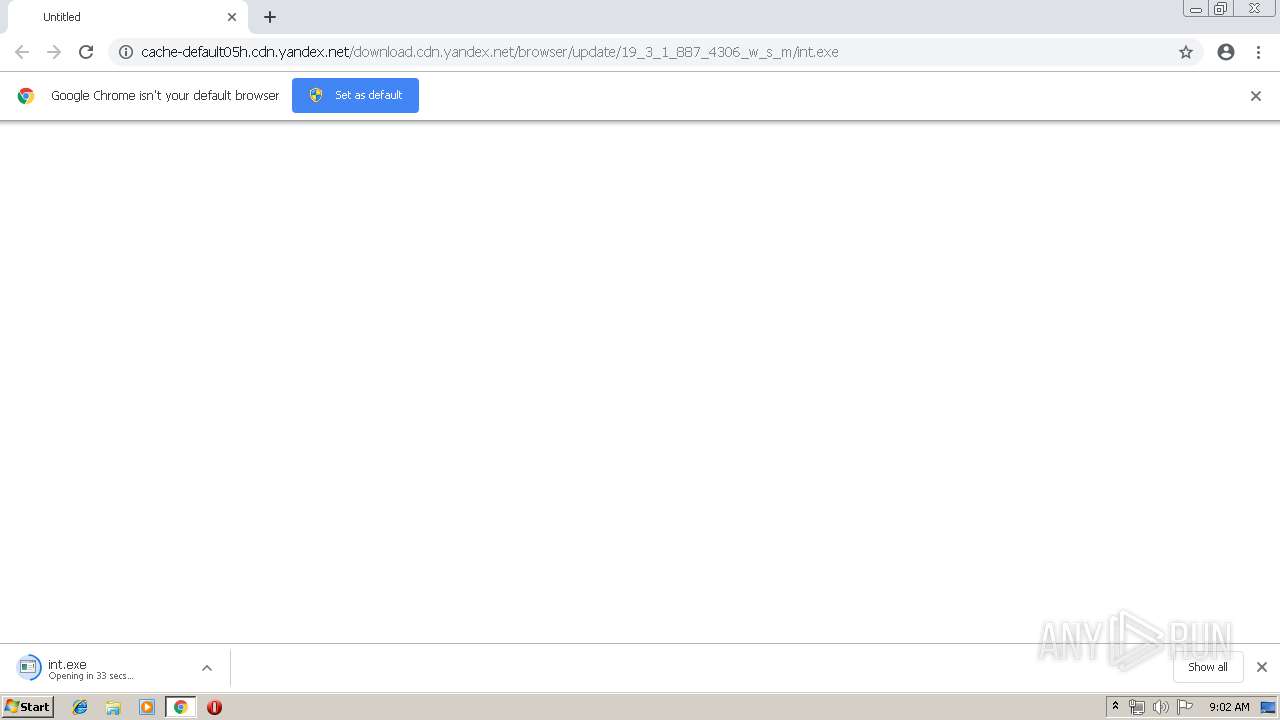
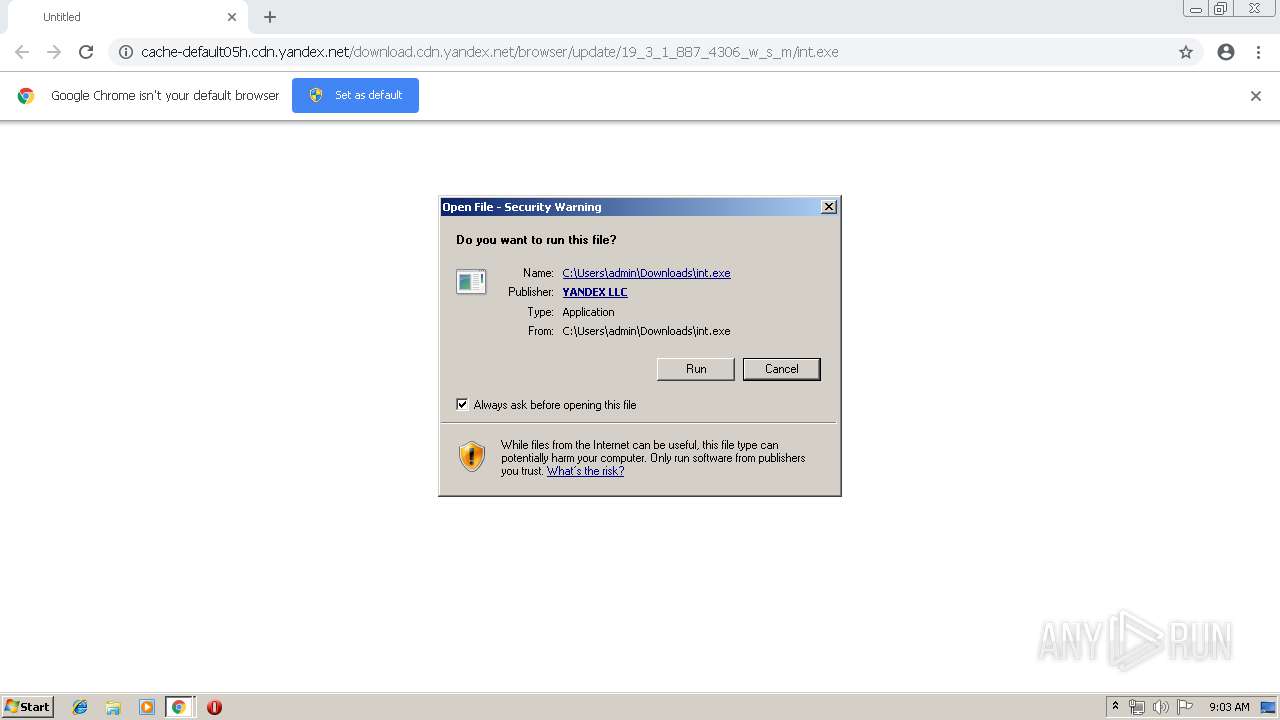
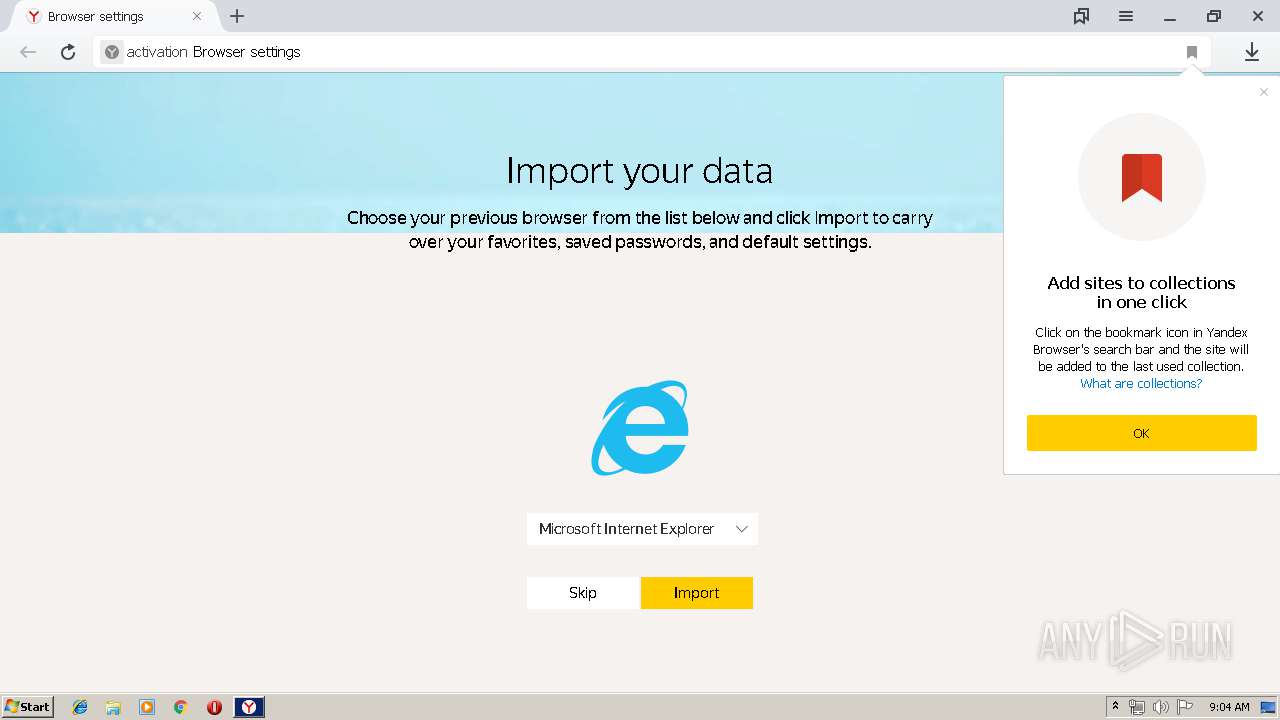
| URL: | http://cache-default05h.cdn.yandex.net/download.cdn.yandex.net/browser/update/19_3_1_887_4306_w_s_m/int.exe |
| Full analysis: | https://app.any.run/tasks/7f9023d4-1002-4f84-9df7-0a095a40fe9e |
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2019, 08:02:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1266320D2957BDE6A0D8F8114B45E3DE |
| SHA1: | 2B4894F98685B3696039649850B5AD01A2690159 |
| SHA256: | DF87B43C791A532BED325C7126FFE005AA1C1FC07C79AE215D48A3FAA4FDBE0C |
| SSDEEP: | 3:N1KdE8BmXR64BU+KMLGX4APi/kRgk9g:CGdzU+KML+Wk9g |
MALICIOUS
Application was dropped or rewritten from another process
- int.exe (PID: 4024)
- setup.exe (PID: 3036)
- setup.exe (PID: 2720)
- setup.exe (PID: 2288)
- service_update.exe (PID: 456)
- service_update.exe (PID: 2300)
- service_update.exe (PID: 3200)
- service_update.exe (PID: 3360)
- service_update.exe (PID: 3228)
- service_update.exe (PID: 3560)
- clidmgr.exe (PID: 3480)
- clidmgr.exe (PID: 2224)
- clidmgr.exe (PID: 2176)
- browser.exe (PID: 2396)
- browser.exe (PID: 2272)
- browser.exe (PID: 3156)
- browser.exe (PID: 3244)
- browser.exe (PID: 3284)
- service_update.exe (PID: 608)
- service_update.exe (PID: 3712)
- clidmgr.exe (PID: 1924)
- browser.exe (PID: 1336)
- browser.exe (PID: 3484)
- browser.exe (PID: 2872)
- browser.exe (PID: 3820)
- browser.exe (PID: 3056)
- browser.exe (PID: 2960)
- browser.exe (PID: 1548)
- browser.exe (PID: 2956)
- browser.exe (PID: 880)
- browser.exe (PID: 3748)
- browser.exe (PID: 2908)
- browser.exe (PID: 3192)
- browser.exe (PID: 3868)
- browser.exe (PID: 2108)
- browser.exe (PID: 3644)
- browser.exe (PID: 1700)
- browser.exe (PID: 2876)
- browser.exe (PID: 3816)
- browser.exe (PID: 2192)
- browser.exe (PID: 1008)
- browser.exe (PID: 2408)
- browser.exe (PID: 3480)
- browser.exe (PID: 2472)
- browser.exe (PID: 2520)
- browser.exe (PID: 3736)
- browser.exe (PID: 3404)
- browser.exe (PID: 2832)
- browser.exe (PID: 3860)
- browser.exe (PID: 4032)
- browser.exe (PID: 1000)
- browser.exe (PID: 2604)
- browser.exe (PID: 2976)
- browser.exe (PID: 3588)
- browser.exe (PID: 2940)
- browser.exe (PID: 3028)
- browser.exe (PID: 2932)
- browser.exe (PID: 1080)
- browser.exe (PID: 3264)
Changes settings of System certificates
- setup.exe (PID: 3036)
Loads the Task Scheduler COM API
- service_update.exe (PID: 2300)
- browser.exe (PID: 2396)
- browser.exe (PID: 3868)
- browser.exe (PID: 3480)
Loads the Task Scheduler DLL interface
- service_update.exe (PID: 3712)
- service_update.exe (PID: 3228)
- browser.exe (PID: 2396)
- browser.exe (PID: 3868)
- browser.exe (PID: 3480)
Loads dropped or rewritten executable
- chrome.exe (PID: 3488)
- browser.exe (PID: 2272)
- browser.exe (PID: 2396)
- browser.exe (PID: 3156)
- browser.exe (PID: 3284)
- browser.exe (PID: 3244)
- browser.exe (PID: 1548)
- browser.exe (PID: 2956)
- browser.exe (PID: 3820)
- browser.exe (PID: 3484)
- browser.exe (PID: 1336)
- browser.exe (PID: 2872)
- browser.exe (PID: 2960)
- browser.exe (PID: 880)
- browser.exe (PID: 2908)
- browser.exe (PID: 3748)
- browser.exe (PID: 3868)
- browser.exe (PID: 2108)
- browser.exe (PID: 3192)
- browser.exe (PID: 3644)
- browser.exe (PID: 3056)
- browser.exe (PID: 3816)
- browser.exe (PID: 2192)
- browser.exe (PID: 2876)
- browser.exe (PID: 1700)
- browser.exe (PID: 3480)
- browser.exe (PID: 1008)
- browser.exe (PID: 2408)
- browser.exe (PID: 2520)
- browser.exe (PID: 2472)
- browser.exe (PID: 3736)
- browser.exe (PID: 3404)
- browser.exe (PID: 2832)
- browser.exe (PID: 3860)
- browser.exe (PID: 4032)
- browser.exe (PID: 2604)
- browser.exe (PID: 2932)
- browser.exe (PID: 2976)
- browser.exe (PID: 1000)
- browser.exe (PID: 3588)
- browser.exe (PID: 2940)
- browser.exe (PID: 3028)
- browser.exe (PID: 1080)
- browser.exe (PID: 3264)
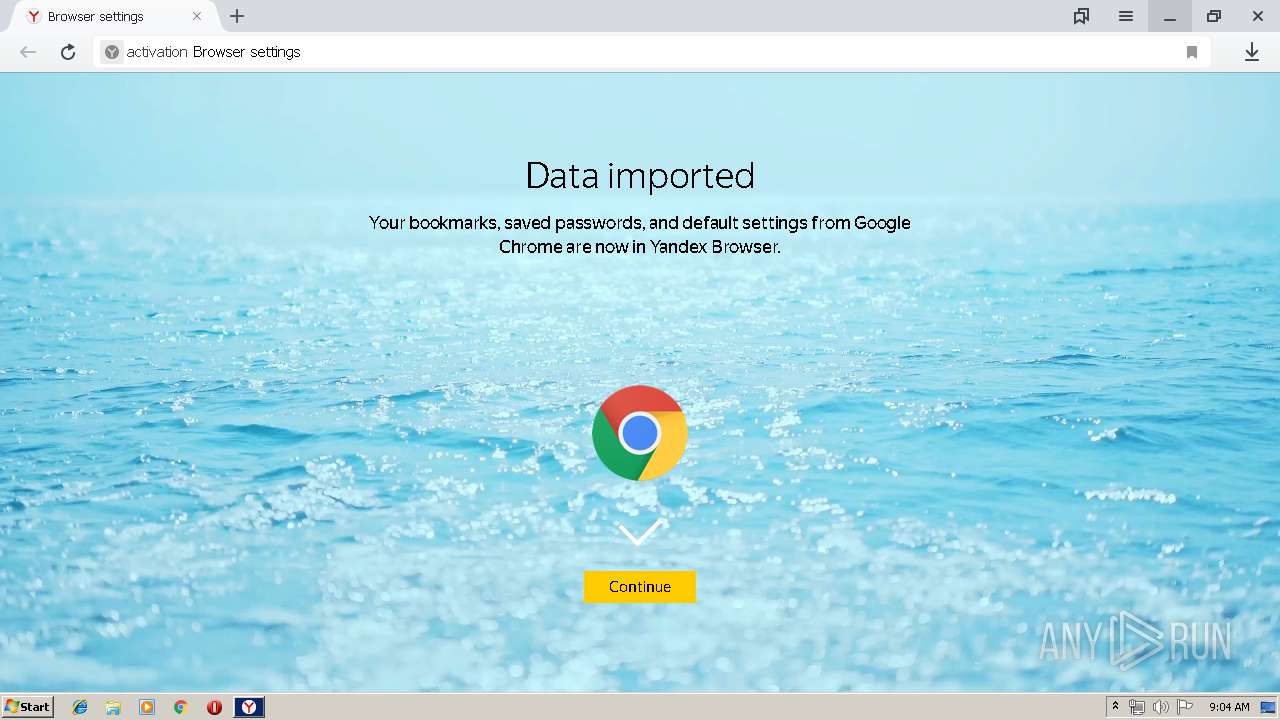
Actions looks like stealing of personal data
- browser.exe (PID: 2396)
- browser.exe (PID: 3868)
- browser.exe (PID: 3480)
SUSPICIOUS
Application launched itself
- setup.exe (PID: 3036)
- setup.exe (PID: 2720)
- service_update.exe (PID: 456)
- service_update.exe (PID: 3228)
- browser.exe (PID: 2396)
- browser.exe (PID: 3868)
- browser.exe (PID: 3480)
Executable content was dropped or overwritten
- chrome.exe (PID: 2656)
- int.exe (PID: 4024)
- setup.exe (PID: 3036)
- service_update.exe (PID: 3560)
- service_update.exe (PID: 3200)
Creates files in the user directory
- setup.exe (PID: 3036)
- clidmgr.exe (PID: 1924)
Adds / modifies Windows certificates
- setup.exe (PID: 3036)
Modifies the open verb of a shell class
- setup.exe (PID: 3036)
Creates files in the program directory
- service_update.exe (PID: 3200)
Starts itself from another location
- service_update.exe (PID: 3200)
Creates files in the Windows directory
- service_update.exe (PID: 456)
- service_update.exe (PID: 3228)
- service_update.exe (PID: 3712)
- service_update.exe (PID: 608)
Creates a software uninstall entry
- setup.exe (PID: 3036)
Removes files from Windows directory
- service_update.exe (PID: 456)
- service_update.exe (PID: 608)
Reads the cookies of Google Chrome
- browser.exe (PID: 2472)
- browser.exe (PID: 3588)
INFO
Application launched itself
- chrome.exe (PID: 2656)
Dropped object may contain Bitcoin addresses
- setup.exe (PID: 3036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
109
Monitored processes
70
Malicious processes
20
Suspicious processes
28
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files\Yandex\YandexBrowser\19.3.1.887\service_update.exe" --run-as-service | C:\Program Files\Yandex\YandexBrowser\19.3.1.887\service_update.exe | services.exe | ||||||||||||
User: SYSTEM Company: YANDEX LLC Integrity Level: SYSTEM Description: Yandex Exit code: 0 Version: 19.3.1.887 Modules
| |||||||||||||||
| 608 | "C:\Program Files\Yandex\YandexBrowser\19.3.1.887\service_update.exe" --statistics=https://api.browser.yandex.ru/installstats/send/dtype=stred/pid=457/cid=72992/path=extended_stat/vars=-action=5_unused,-brand_id=unknown,-error=FONT_NOT_FOUND,-installer_type=4,-launched=false,-old_style=0,-old_ver=,-result=0,-stage=error,-target=5,-ui=57FF2337_691F_433E_805F_F25C5C8560E8/* | C:\Program Files\Yandex\YandexBrowser\19.3.1.887\service_update.exe | service_update.exe | ||||||||||||
User: SYSTEM Company: YANDEX LLC Integrity Level: SYSTEM Description: Yandex Exit code: 0 Version: 19.3.1.887 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa60f18,0x6fa60f28,0x6fa60f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 880 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe" --type=gpu-process --field-trial-handle=968,3844670145946564608,16692557394644116678,131072 --disable-gpu-sandbox --use-gl=disabled --user-id=E5F3AD3F-8715-4346-8DF7-DF6AD44971FE --brand-id=int --gpu-preferences=KAAAAAAAAACAAwCAAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2220842872171163786 --mojo-platform-channel-handle=3136 /prefetch:2 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: MEDIUM Description: Yandex Exit code: 0 Version: 19.3.1.887 Modules
| |||||||||||||||
| 1000 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe" --type=utility --field-trial-handle=912,22456217470558861,12810672542548302485,131072 --lang=en-US --service-sandbox-type=utility --user-id=E5F3AD3F-8715-4346-8DF7-DF6AD44971FE --brand-id=int --service-request-channel-token=12728452198412013517 --process-name="Data Decoder Service" --mojo-platform-channel-handle=2276 --ignored=" --type=renderer " /prefetch:8 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: LOW Description: Yandex Exit code: 0 Version: 19.3.1.887 Modules
| |||||||||||||||
| 1008 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Yandex\YandexBrowser\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Yandex\YandexBrowser\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Yandex\YandexBrowser\User Data" --url=https://crash-reports.browser.yandex.net/submit --annotation=install_date=1554537838 --annotation=machine_id=5f735395d68db0638bd0a2a58101e17a --annotation=main_process_pid=3480 --annotation=metrics_client_id=ab9be06889494580b060c19638e06910 --annotation=plat=Win32 --annotation=prod=Yandex --annotation=session_logout=False --annotation=ver=19.3.1.887 --initial-client-data=0xa4,0xac,0xb0,0xa0,0xb4,0x6f942270,0x6f942280,0x6f94228c,0xa8 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: MEDIUM Description: Yandex Exit code: 0 Version: 19.3.1.887 Modules
| |||||||||||||||
| 1080 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe" --broupdater-stat-bits --broupdater-stat-name=dayuse --bits_job_guid={BEABEA76-82A4-4B71-A8F8-81686A88C84E} | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | svchost.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: MEDIUM Description: Yandex Exit code: 0 Version: 19.3.1.887 Modules
| |||||||||||||||
| 1336 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe" --type=renderer --field-trial-handle=968,3844670145946564608,16692557394644116678,131072 --disable-gpu-compositing --service-pipe-token=18179754226048661161 --lang=en-US --user-id=E5F3AD3F-8715-4346-8DF7-DF6AD44971FE --brand-id=int --help-url=https://api.browser.yandex.com/redirect/help/ --user-agent-info --translate-security-origin=https://yastatic.net --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18179754226048661161 --renderer-client-id=8 --mojo-platform-channel-handle=3400 /prefetch:1 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: LOW Description: Yandex Exit code: 0 Version: 19.3.1.887 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,16757165573614761929,13464838209277135556,131072 --enable-features=PasswordImport --service-pipe-token=6284979753361739862 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6284979753361739862 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1548 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe" --type=renderer --field-trial-handle=968,3844670145946564608,16692557394644116678,131072 --disable-gpu-compositing --service-pipe-token=770750895410710792 --lang=en-US --user-id=E5F3AD3F-8715-4346-8DF7-DF6AD44971FE --brand-id=int --help-url=https://api.browser.yandex.com/redirect/help/ --user-agent-info --translate-security-origin=https://yastatic.net --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=770750895410710792 --renderer-client-id=6 --mojo-platform-channel-handle=3368 /prefetch:1 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: LOW Description: Yandex Exit code: 0 Version: 19.3.1.887 Modules
| |||||||||||||||
Total events
4 237
Read events
3 542
Write events
677
Delete events
18
Modification events
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2656-13199011344670875 |
Value: 259 | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
36
Suspicious files
268
Text files
478
Unknown types
77
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a736f6b4-4a34-4361-bbdc-ab43e203ff8b.tmp | — | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
4
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2232 | chrome.exe | GET | — | 37.140.166.229:80 | http://cache-default05h.cdn.yandex.net/download.cdn.yandex.net/browser/update/19_3_1_887_4306_w_s_m/int.exe | RU | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2232 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2232 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2232 | chrome.exe | 37.140.166.229:80 | cache-default05h.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
2232 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cache-default05h.cdn.yandex.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2232 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2232 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2396 | browser.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
— | — | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
Process | Message |
|---|---|
clidmgr.exe | GetLoggedCreds_WTSSessionInfo(): szUserName = admin, szDomain = USER-PC, dwSessionId = 1
|
clidmgr.exe | GetSidFromEnumSess(): i = 0 : szUserName = Administrator, szDomain = USER-PC, dwSessionId = 0
|
clidmgr.exe | GetSidFromEnumSess(): LsaEnumerateLogonSessions() lpszSid = ê |
clidmgr.exe | GetSidFromEnumSess(): LsaEnumerateLogonSessions() lpszSid = S-1-5-21-1302019708-1500728564-335382590-1000
|
clidmgr.exe | GetLoggedCreds_WTSSessionInfo(): szUserName = admin, szDomain = USER-PC, dwSessionId = 1
|
clidmgr.exe | GetSidFromEnumSess(): i = 0 : szUserName = Administrator, szDomain = USER-PC, dwSessionId = 0
|
clidmgr.exe | GetSidFromEnumSess(): ProfileImagePath(1) = C:\Users\admin
|
clidmgr.exe | GetSidFromEnumSess(): LsaEnumerateLogonSessions() lpszSid = S-1-5-21-1302019708-1500728564-335382590-1000
|
clidmgr.exe | GetLoggedCreds_WTSSessionInfo(): szUserName = admin, szDomain = USER-PC, dwSessionId = 1
|
clidmgr.exe | GetSidFromEnumSess(): i = 0 : szUserName = Administrator, szDomain = USER-PC, dwSessionId = 0
|