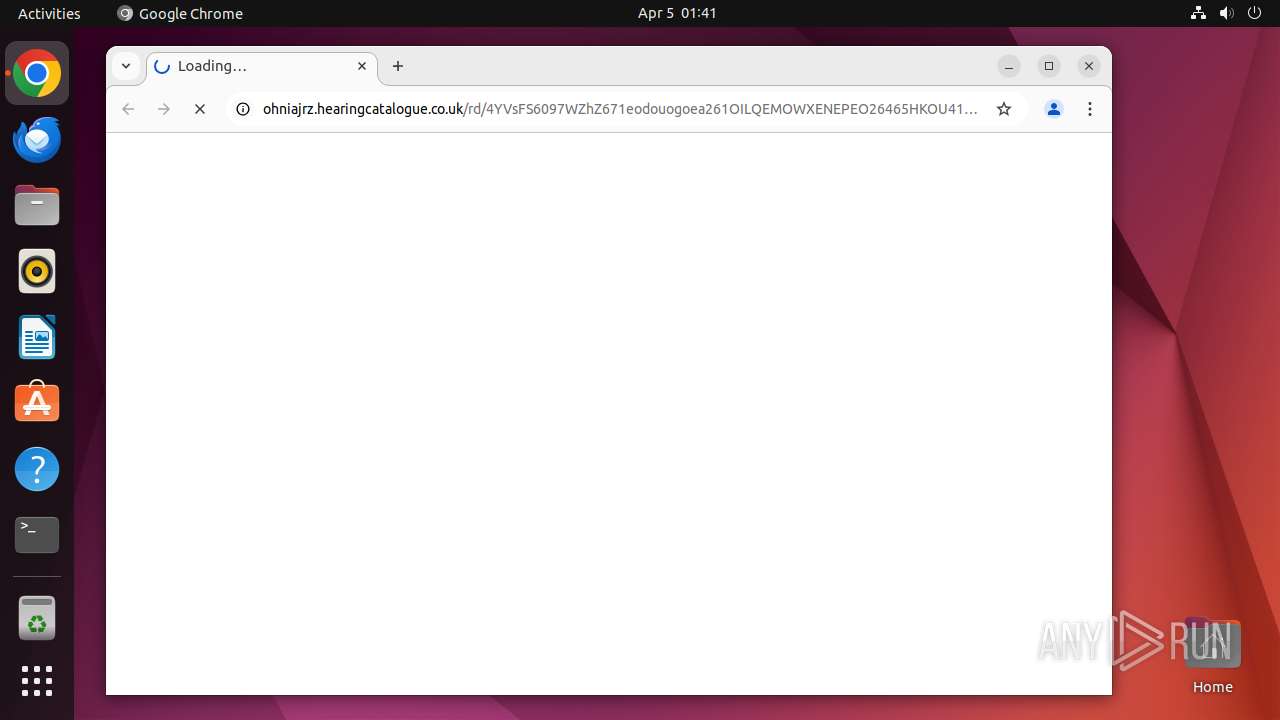
| URL: | http://ohniajrz.hearingcatalogue.co.uk/rd/4YVsFS6097WZhZ671eodouogoea261OILQEMOWXENEPEO26465HKOU41103l13?JKcHGAfWblTHC5XEF-cEDnCAQltG-oESVjs |
| Full analysis: | https://app.any.run/tasks/11fc9c76-df19-49c1-9fdf-bdeaf1a6a2e7 |
| Verdict: | Malicious activity |
| Analysis date: | April 05, 2025, 00:41:26 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MD5: | 32D977A5B538569FF6AB4145852EDE7F |
| SHA1: | E54ED1A308A4306CB38CE9D0CDA70B01AC422C21 |
| SHA256: | DF6E196584F51E147E480D86F09A31CFE2C6C0F60BA567D6F65880452455EFDF |
| SSDEEP: | 3:N1KRNLMEPPLNAEcnJZQALGFN8Hwy/NrBGDzJYy9uVXvUnvu/HU8LmrE3nWn:CfMEHLNA9qFN8HHFrQJ9uVXKS1LmY3Wn |
MALICIOUS
PHISHING has been detected (SURICATA)
- chrome (PID: 39529)
SUSPICIOUS
Executes commands using command-line interpreter
- sudo (PID: 39480)
- chrome (PID: 39481)
INFO
Checks timezone
- chrome (PID: 39481)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
297
Monitored processes
79
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 39479 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome http://ohniajrz\.hearingcatalogue\.co\.uk/rd/4YVsFS6097WZhZ671eodouogoea261OILQEMOWXENEPEO26465HKOU41103l13?JKcHGAfWblTHC5XEF-cEDnCAQltG-oESVjs " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 39480 | sudo -iu user google-chrome http://ohniajrz.hearingcatalogue.co.uk/rd/4YVsFS6097WZhZ671eodouogoea261OILQEMOWXENEPEO26465HKOU41103l13?JKcHGAfWblTHC5XEF-cEDnCAQltG-oESVjs | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 39481 | /usr/bin/google-chrome http://ohniajrz.hearingcatalogue.co.uk/rd/4YVsFS6097WZhZ671eodouogoea261OILQEMOWXENEPEO26465HKOU41103l13?JKcHGAfWblTHC5XEF-cEDnCAQltG-oESVjs | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 39482 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39483 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39484 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39485 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39486 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 39487 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 39488 | "/opt/google/chrome/chrome http://ohniajrz\.hearingcatalogue\.co\.uk/rd/4YVsFS6097WZhZ671eodouogoea261OILQEMOWXENEPEO26465HKOU41103l13?JKcHGAfWblTHC5XEF-cEDnCAQltG-oESV" | /opt/google/chrome/chrome | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
75
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 39481 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 39481 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 39481 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 39481 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 39481 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 39481 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 39526 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 39620 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 39637 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 39481 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
23
DNS requests
41
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 204 | 185.125.190.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
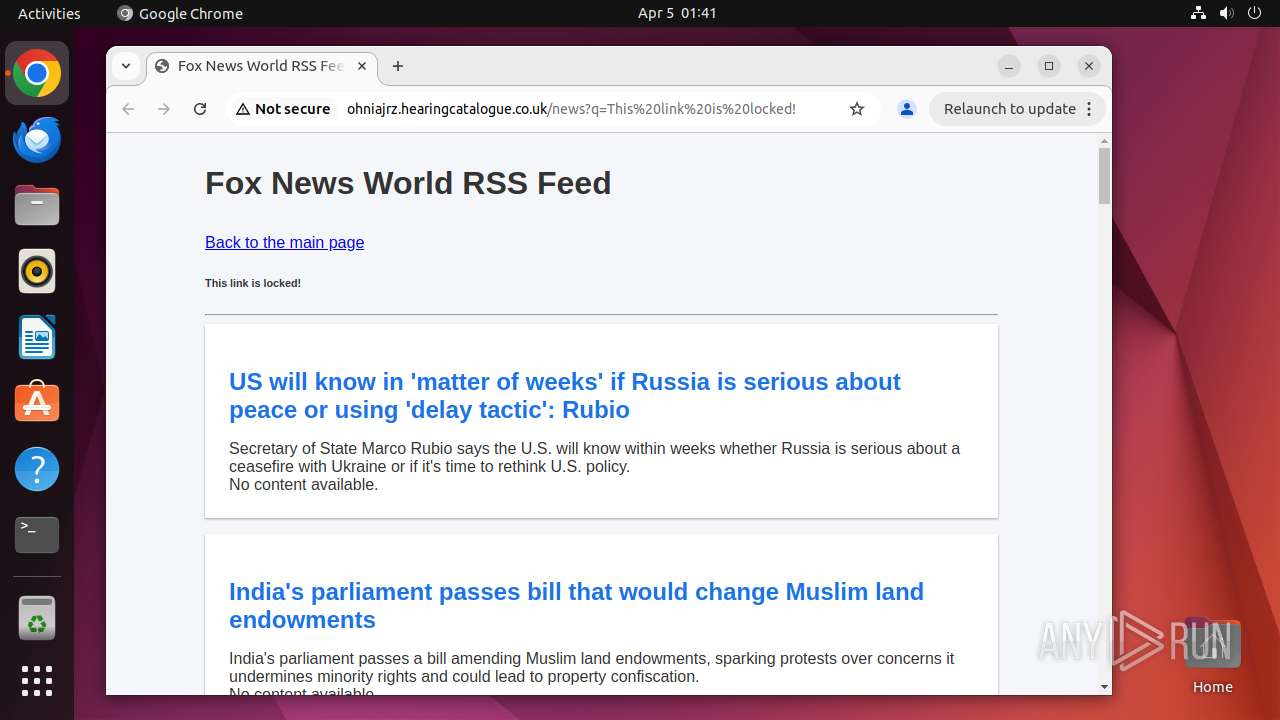
39529 | chrome | GET | 200 | 185.246.85.93:80 | http://ohniajrz.hearingcatalogue.co.uk/rd/4YVsFS6097WZhZ671eodouogoea261OILQEMOWXENEPEO26465HKOU41103l13?JKcHGAfWblTHC5XEF-cEDnCAQltG-oESVjs | unknown | — | — | unknown |
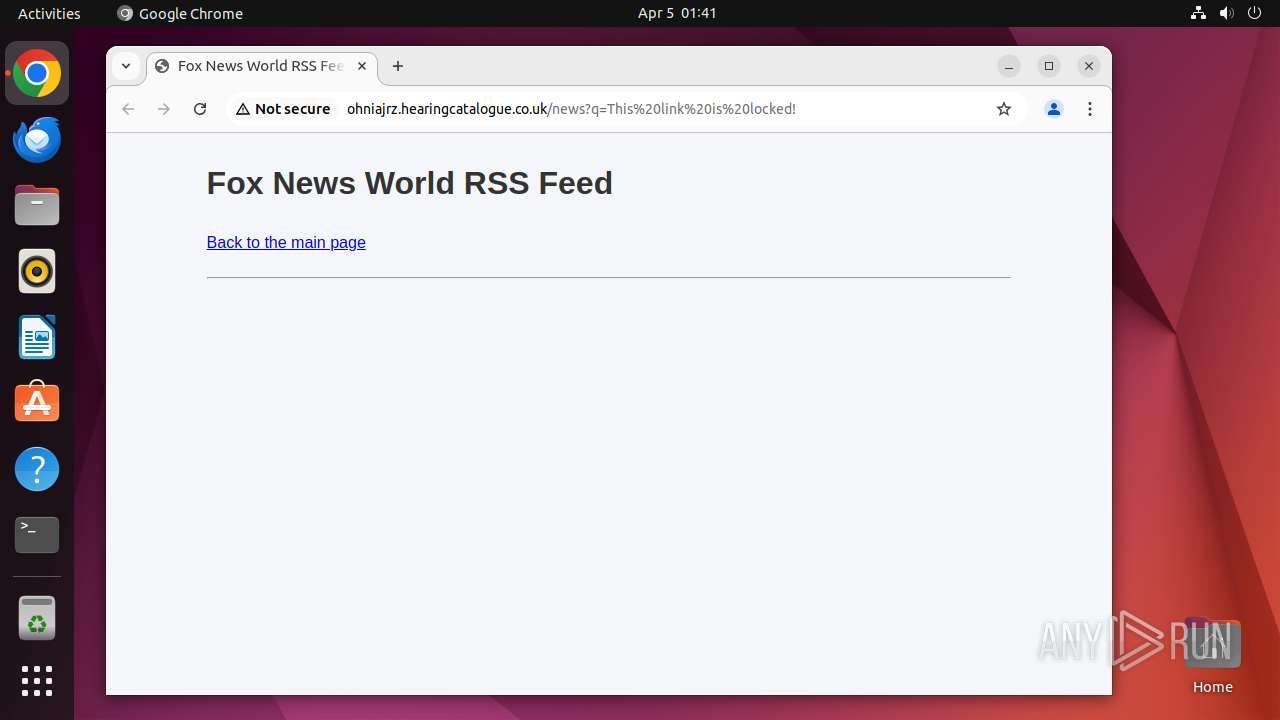
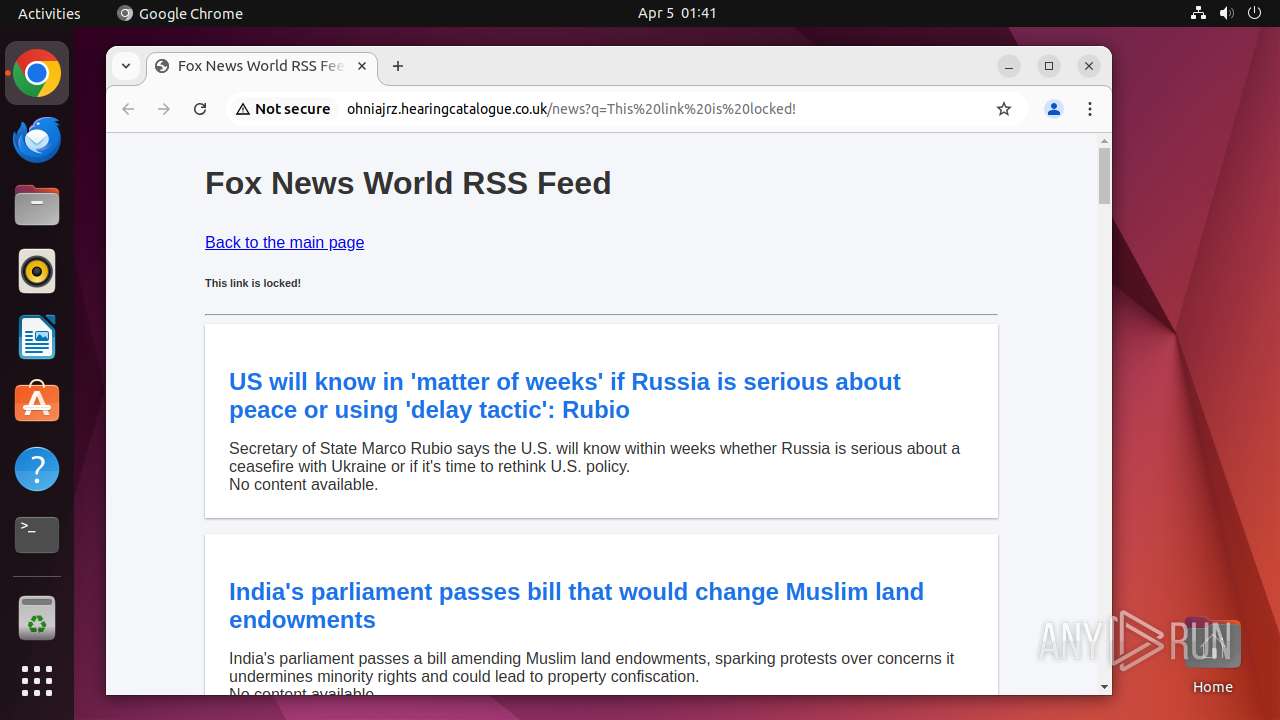
39529 | chrome | GET | 200 | 185.246.85.93:80 | http://ohniajrz.hearingcatalogue.co.uk/news?q=This%20link%20is%20locked! | unknown | — | — | unknown |
39529 | chrome | GET | 404 | 185.246.85.93:80 | http://ohniajrz.hearingcatalogue.co.uk/favicon.ico | unknown | — | — | unknown |
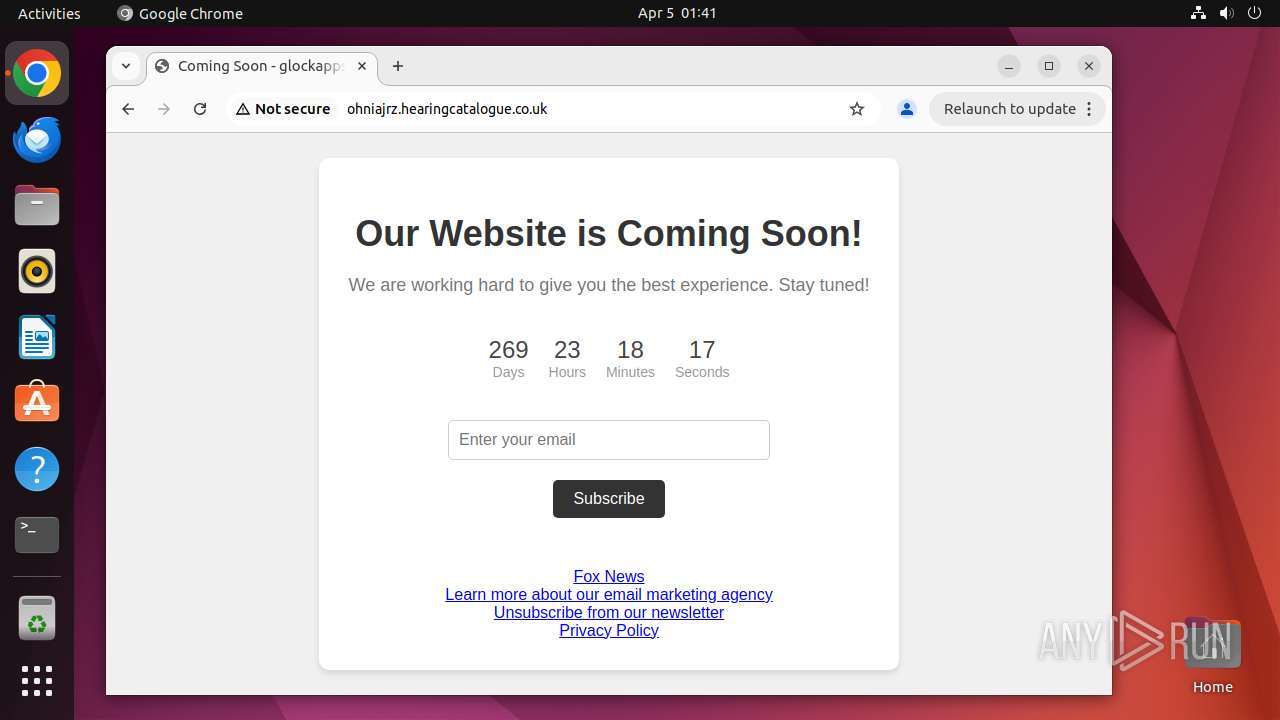
39529 | chrome | GET | 200 | 185.246.85.93:80 | http://ohniajrz.hearingcatalogue.co.uk/ | unknown | — | — | unknown |
39529 | chrome | GET | 200 | 185.246.85.93:80 | http://ohniajrz.hearingcatalogue.co.uk/assets/styles.css | unknown | — | — | unknown |
39529 | chrome | GET | 200 | 185.246.85.93:80 | http://ohniajrz.hearingcatalogue.co.uk/t/4YVsFS6097WZhZ671eodouogoea261OILQEMOWXENEPEO26465HKOU41103l13?JKcHGAfWblTHC5XEF-cEDnCAQltG-oESVjs | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.98:80 | — | Canonical Group Limited | GB | unknown |
39529 | chrome | 142.251.143.67:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
39529 | chrome | 142.251.143.42:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
39529 | chrome | 185.246.85.93:443 | ohniajrz.hearingcatalogue.co.uk | Ikoula Net SAS | FR | unknown |
39529 | chrome | 185.246.85.93:80 | ohniajrz.hearingcatalogue.co.uk | Ikoula Net SAS | FR | unknown |
39529 | chrome | 172.217.218.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
39529 | chrome | 146.75.121.91:443 | google-ohttp-relay-safebrowsing.fastly-edge.com | FASTLY | US | unknown |
39529 | chrome | 151.101.2.132:443 | feeds.foxnews.com | FASTLY | US | whitelisted |
39529 | chrome | 142.250.181.227:443 | update.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
ohniajrz.hearingcatalogue.co.uk |
| unknown |
accounts.google.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
feeds.foxnews.com |
| whitelisted |
moxie.foxnews.com |
| whitelisted |
4.100.168.192.in-addr.arpa |
| unknown |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
39529 | chrome | Possible Social Engineering Attempted | REDIRECT [ANY.RUN] Fake Market FoxWhoops Evil Redirect |
39529 | chrome | Possible Social Engineering Attempted | REDIRECT [ANY.RUN] Fake Market FoxWhoops Evil Redirect |
39529 | chrome | Possible Social Engineering Attempted | REDIRECT [ANY.RUN] Fake Market FoxWhoops Evil Redirect |