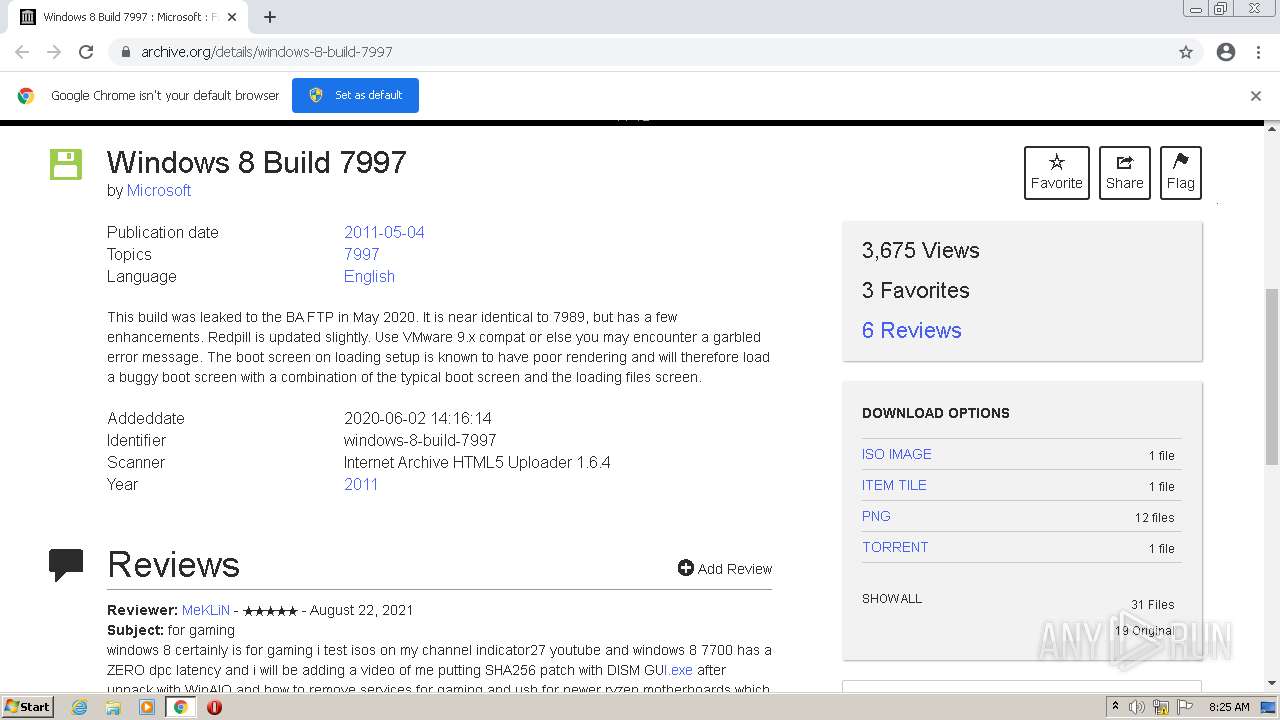
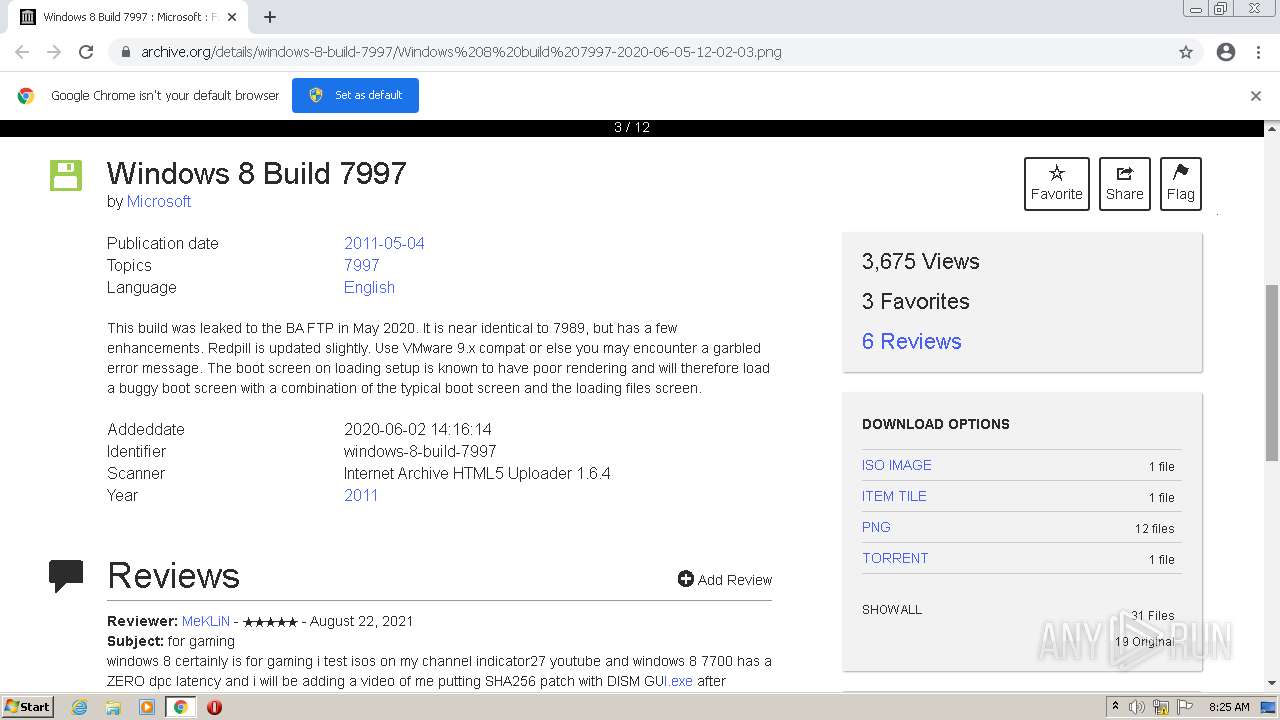
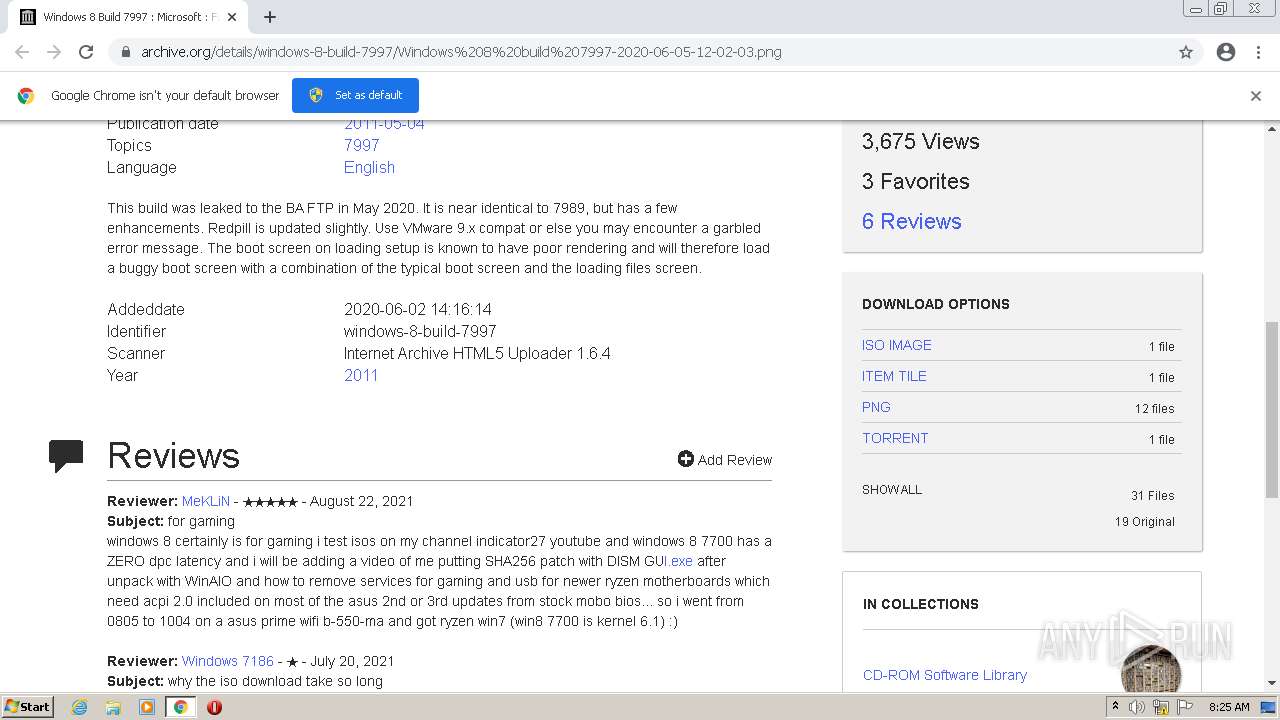
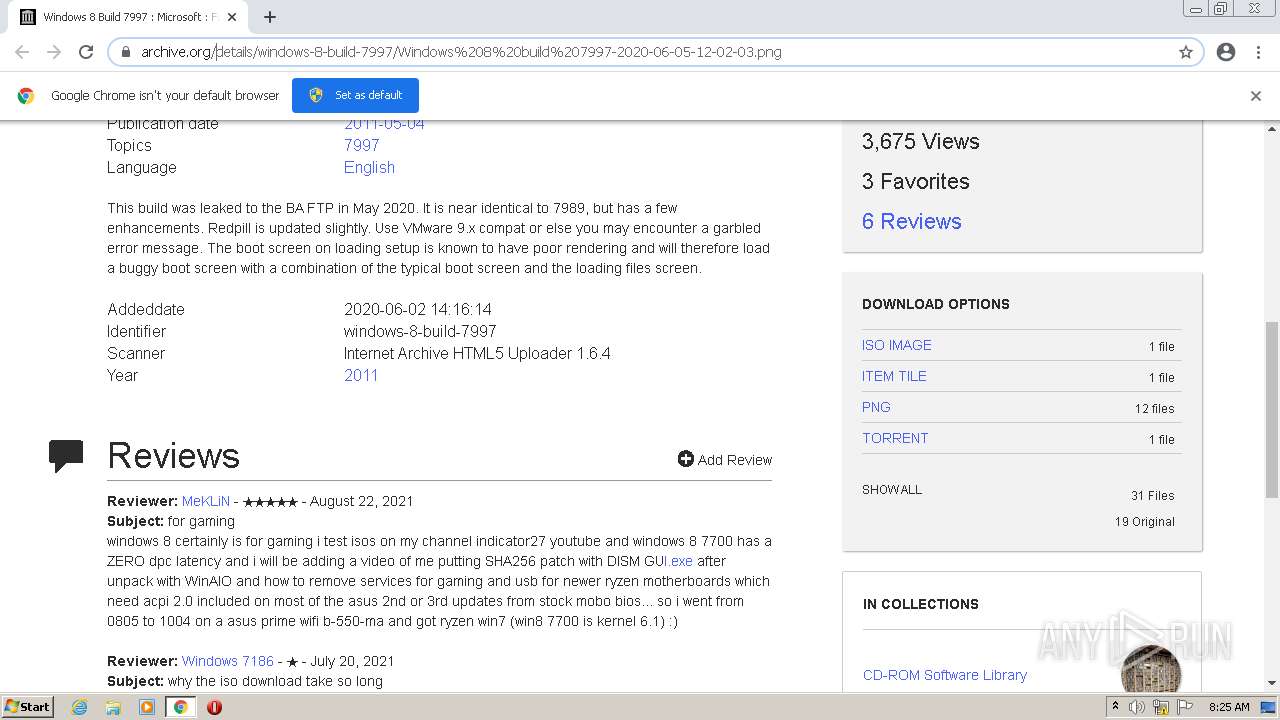
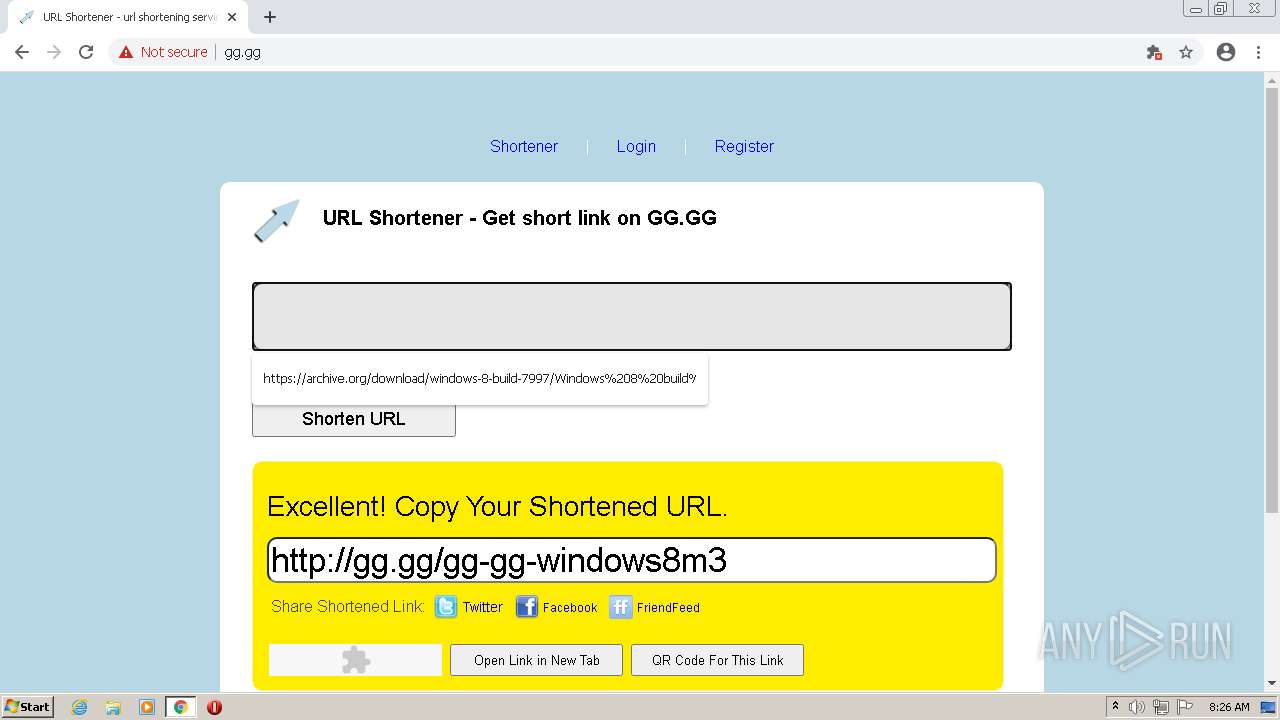
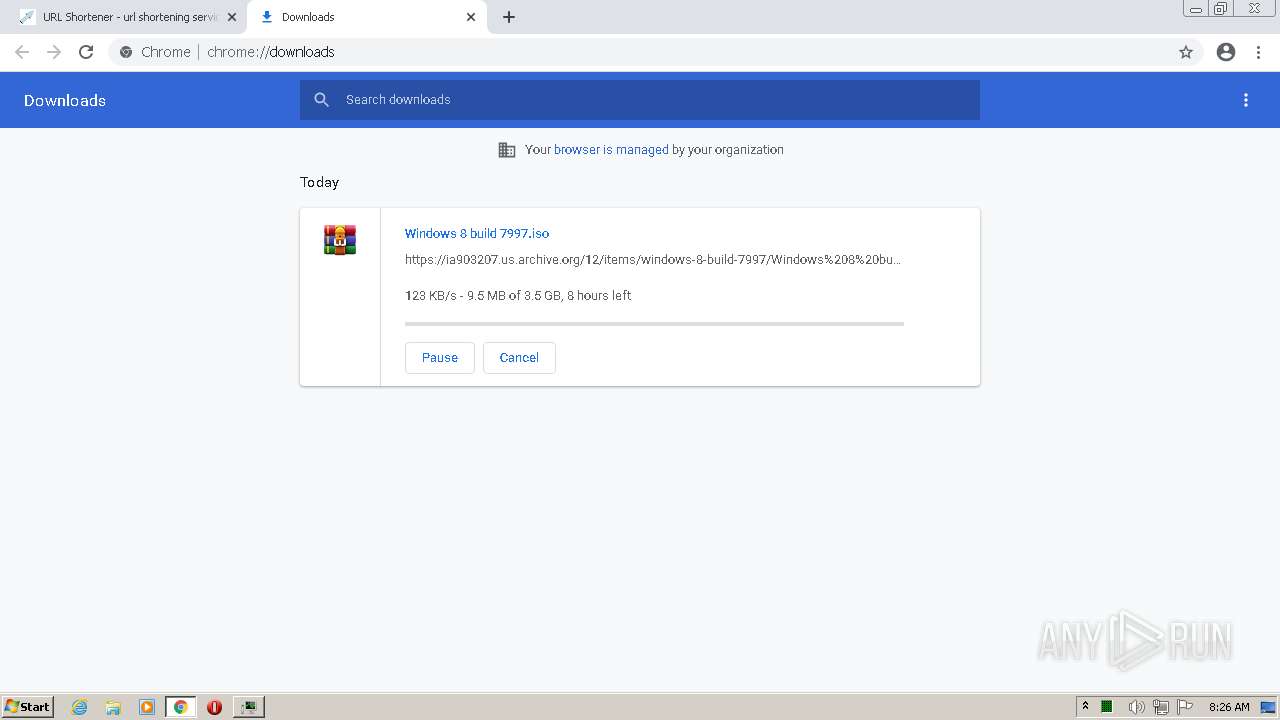
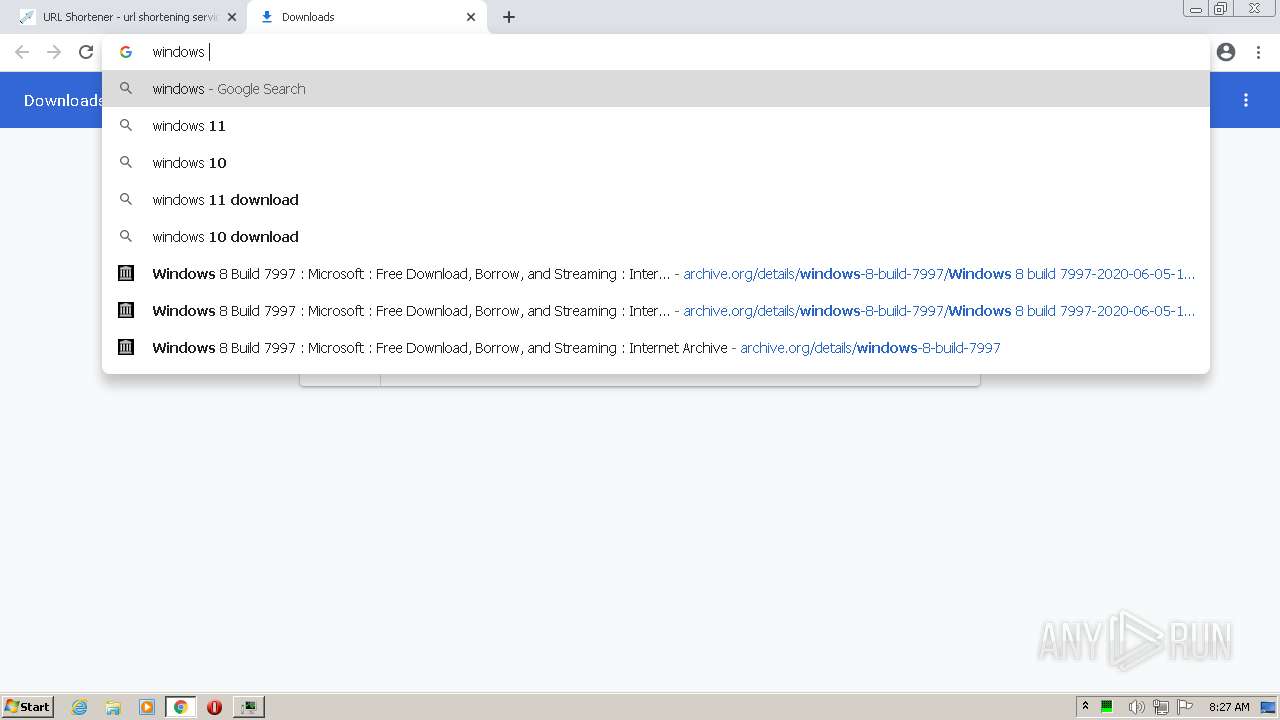
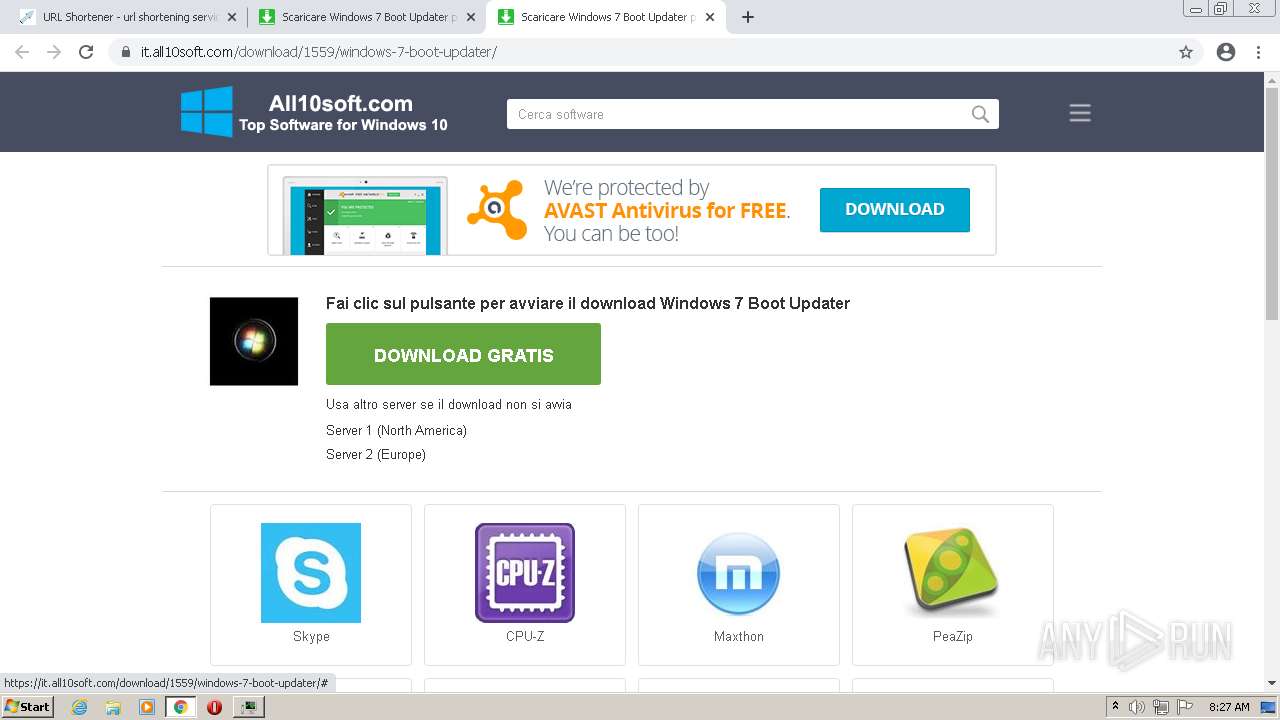
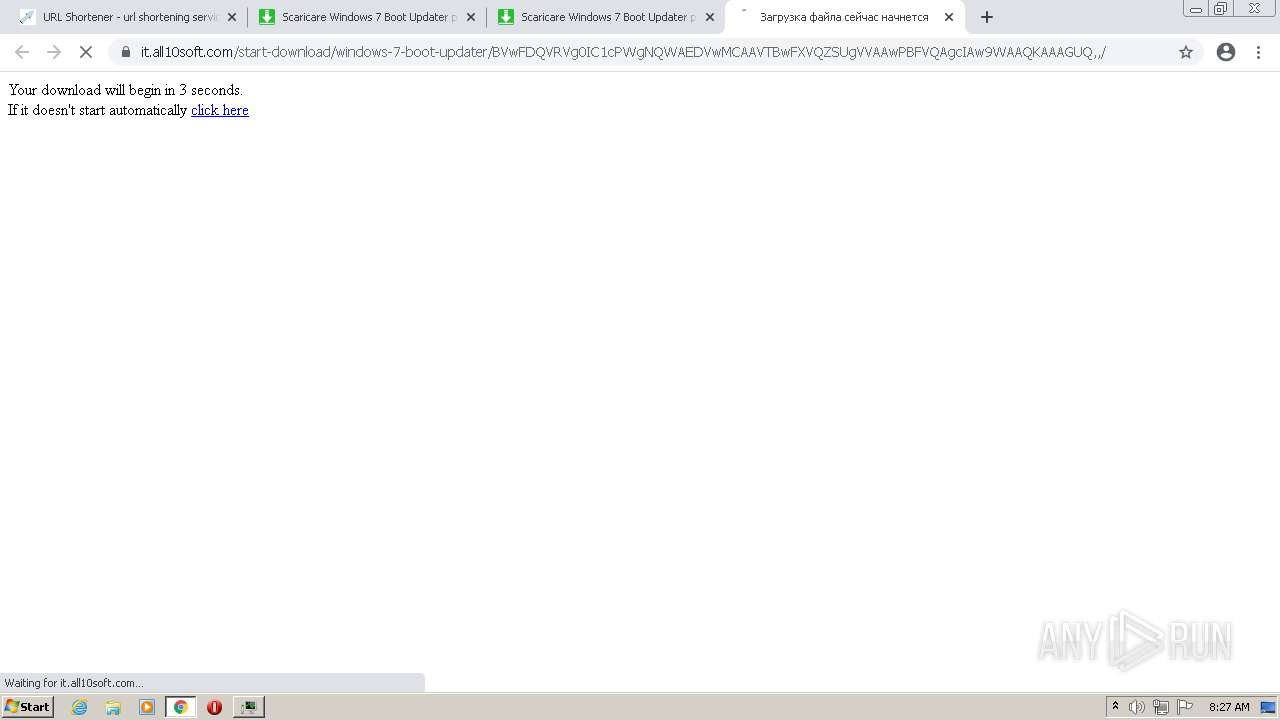
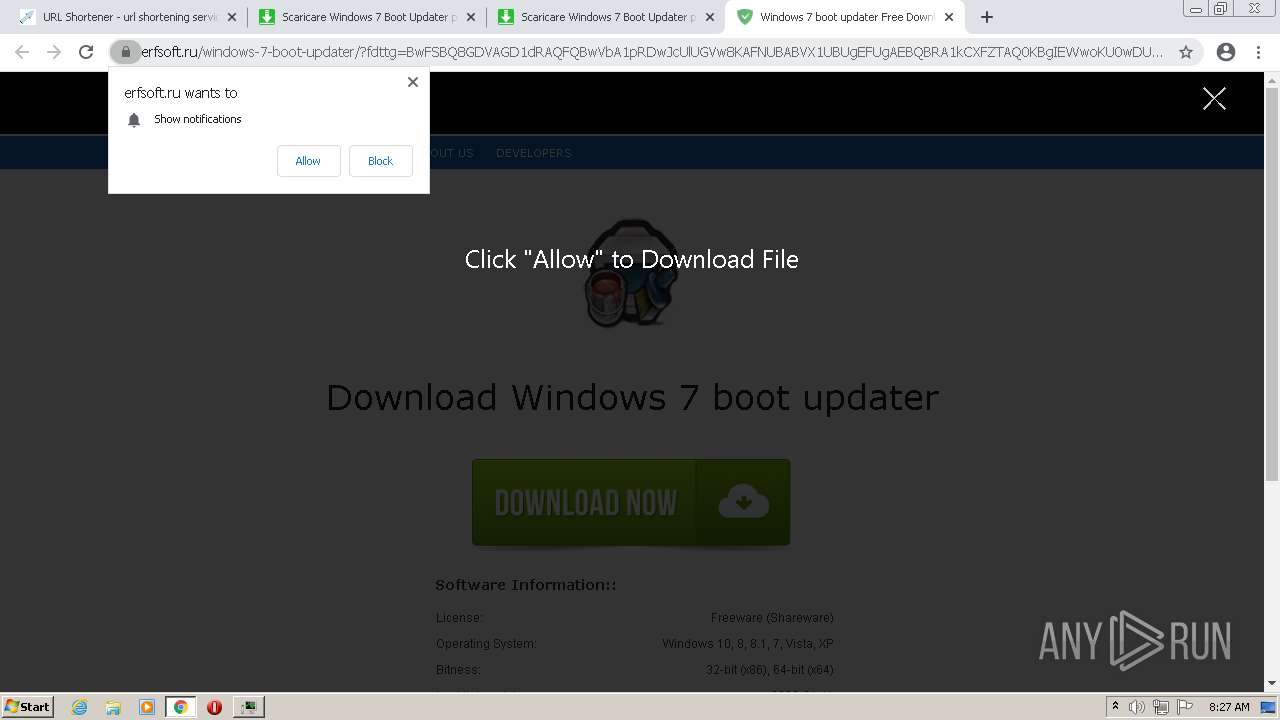
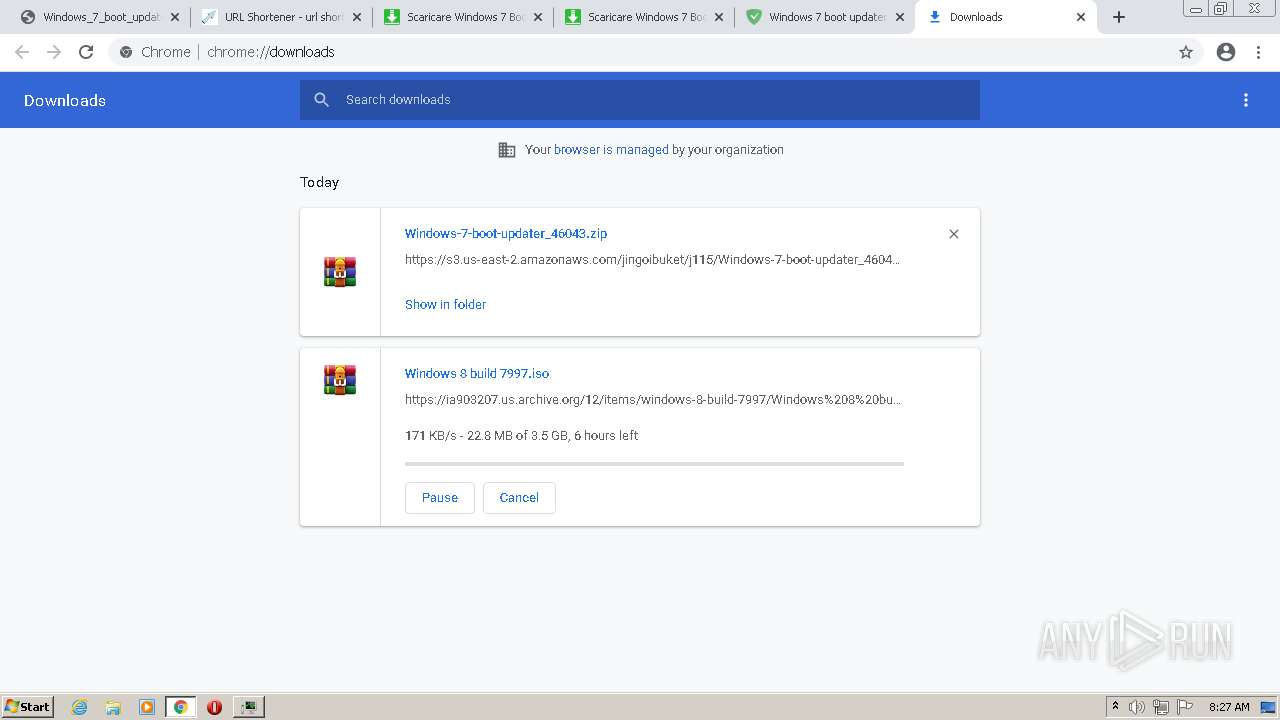
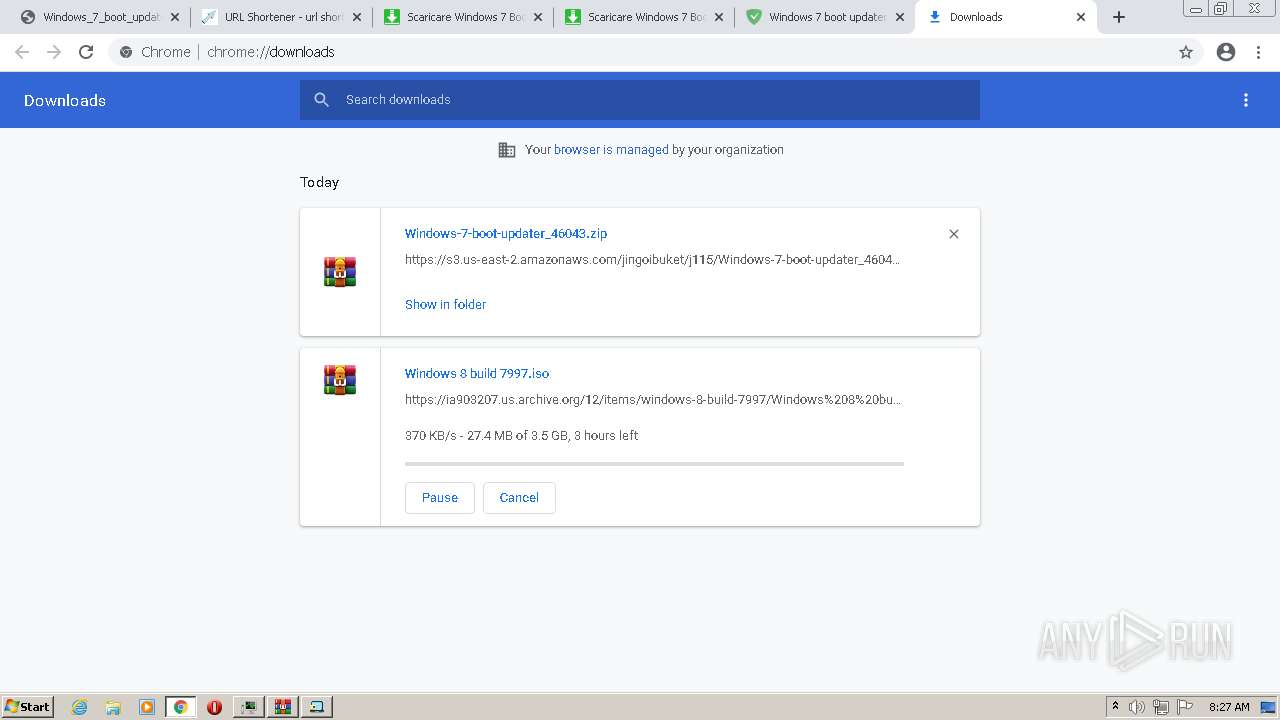
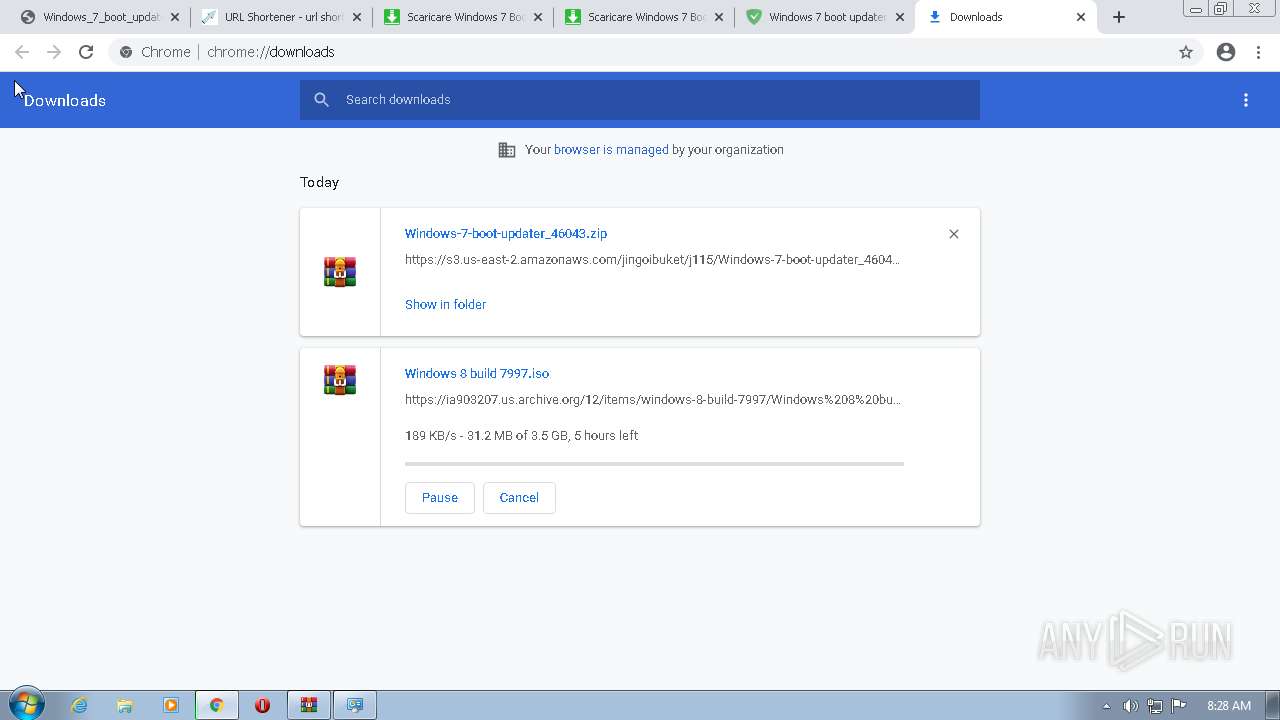
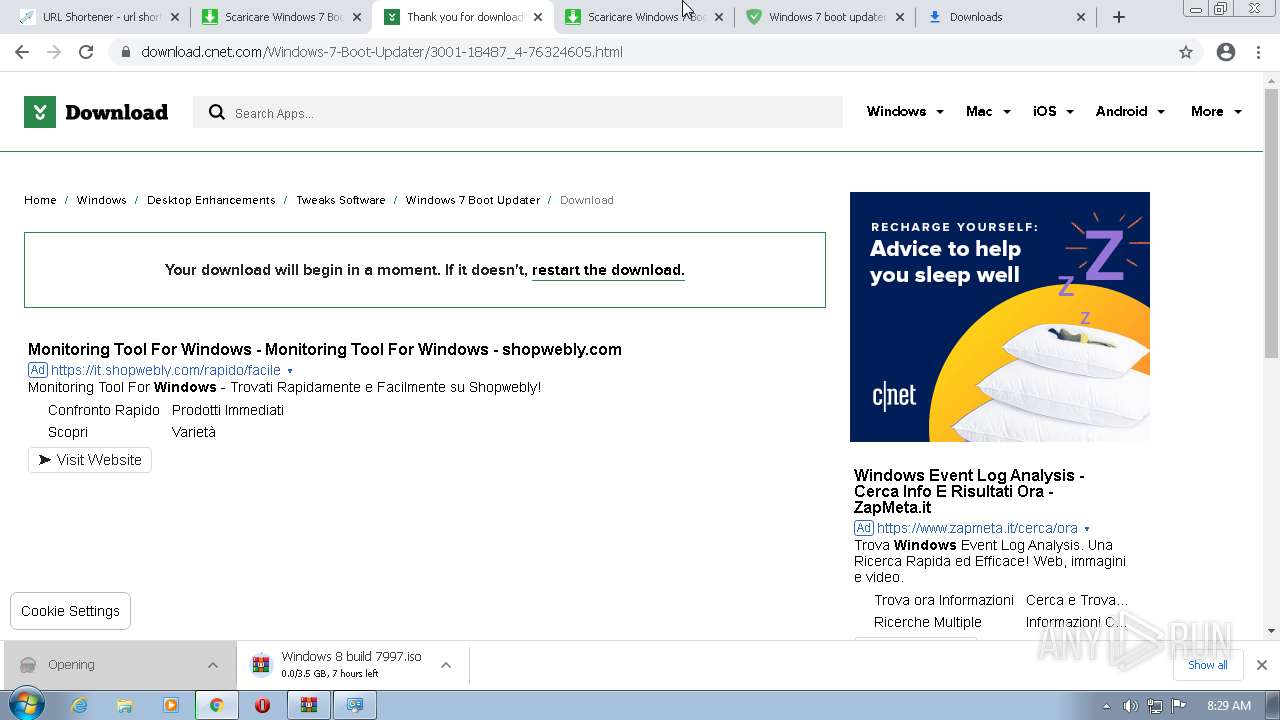
| URL: | https://archive.org/details/windows-8-build-7997 |
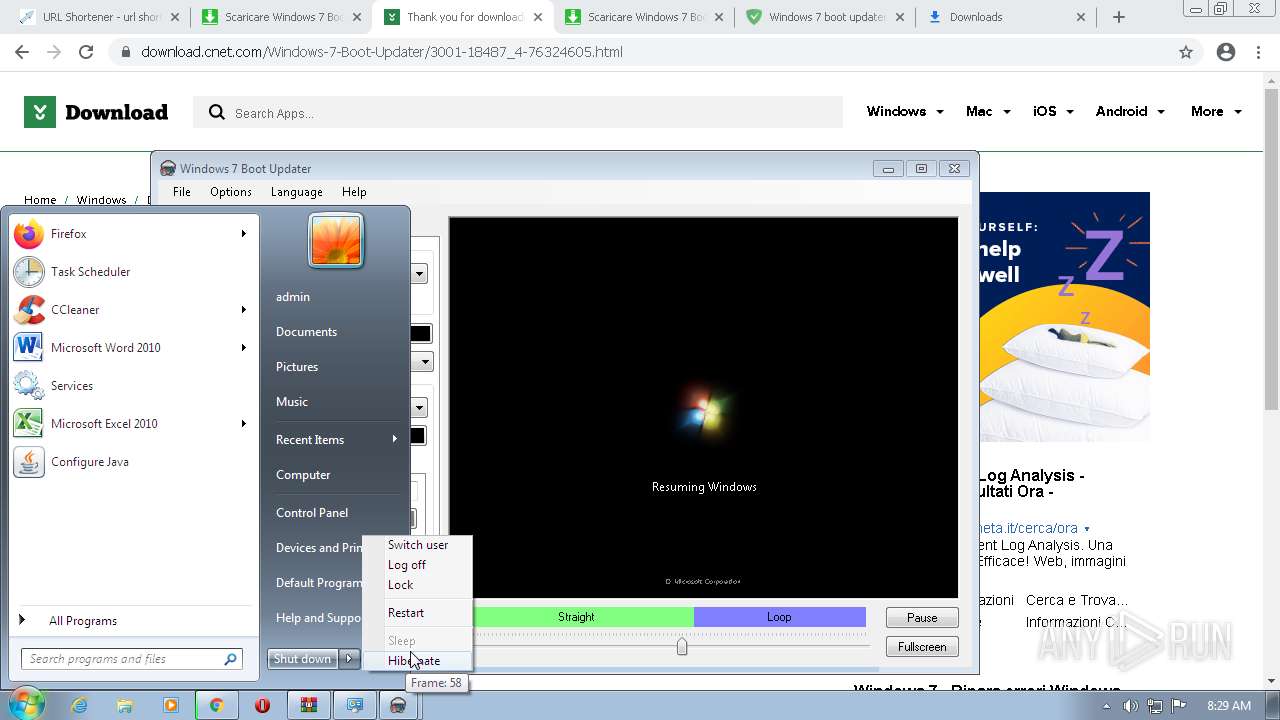
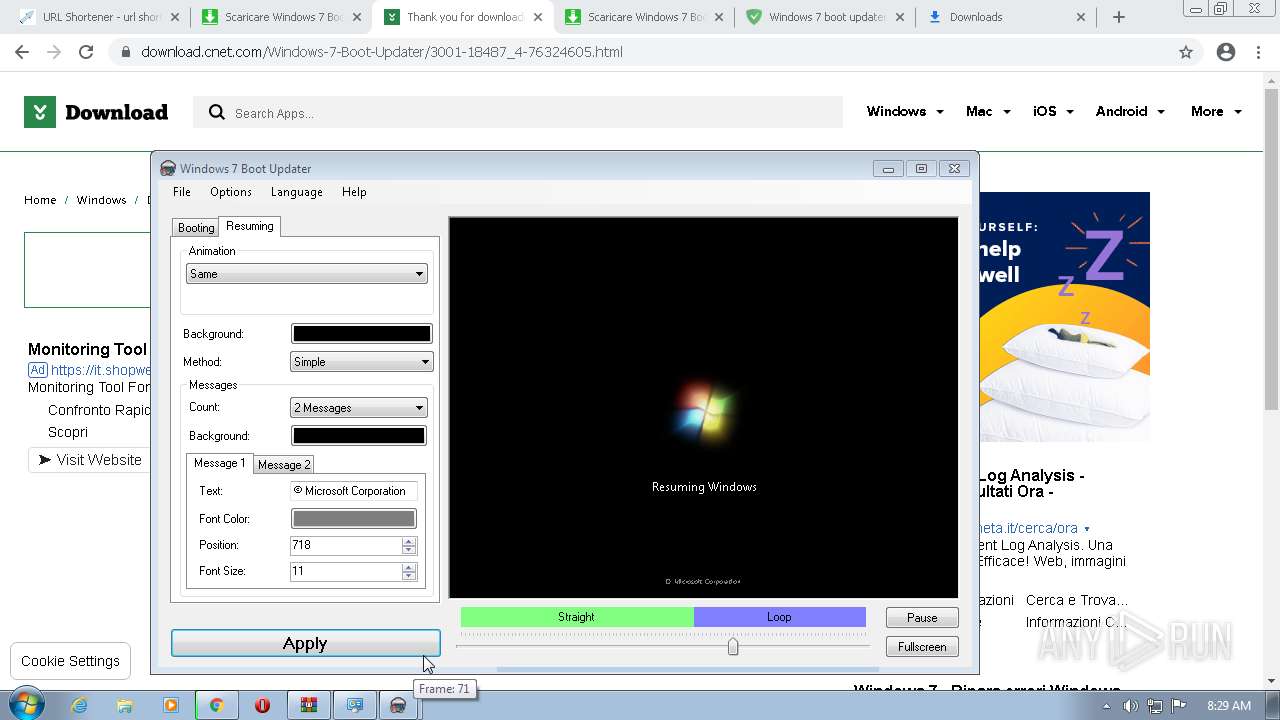
| Full analysis: | https://app.any.run/tasks/40d27f21-7f46-46e8-8527-0802b0a06a93 |
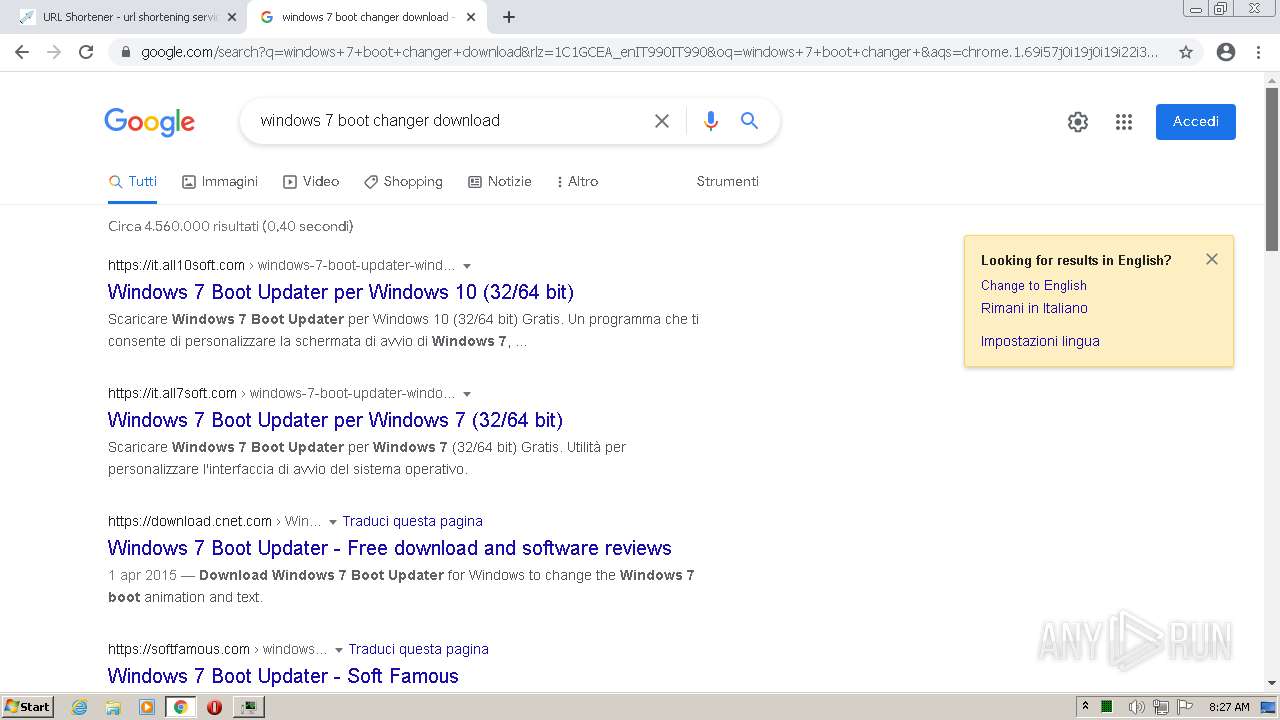
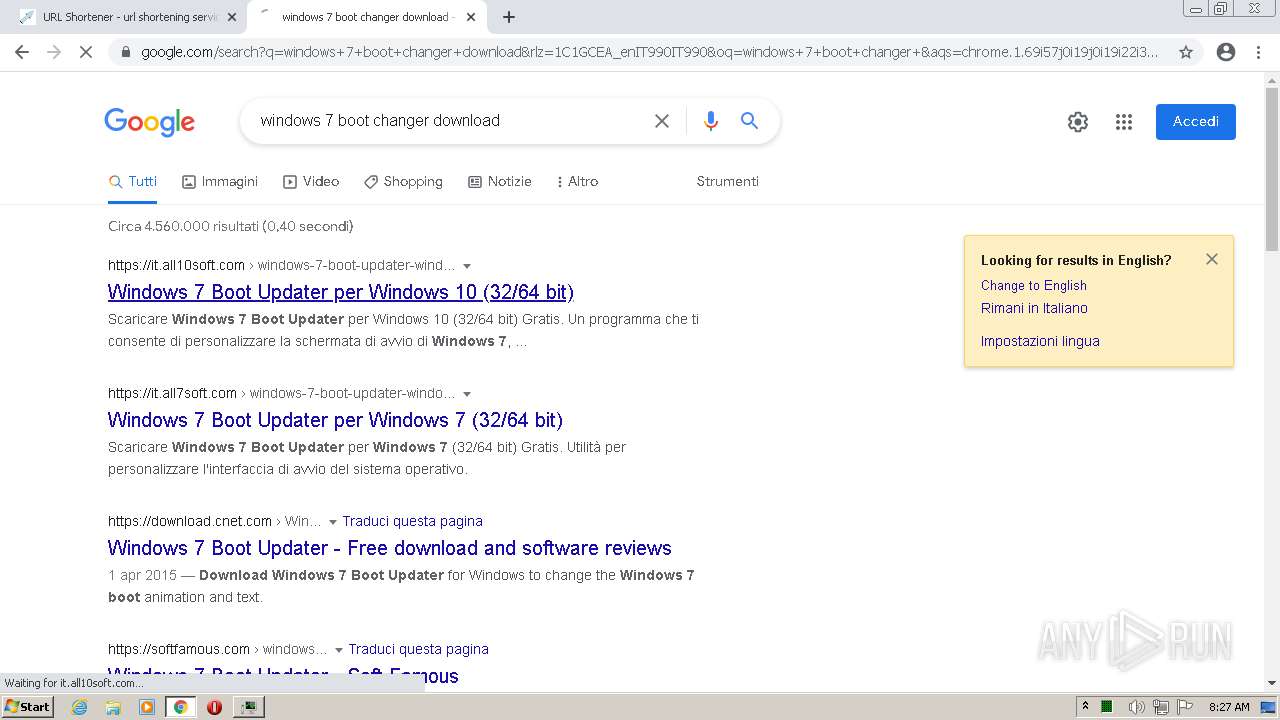
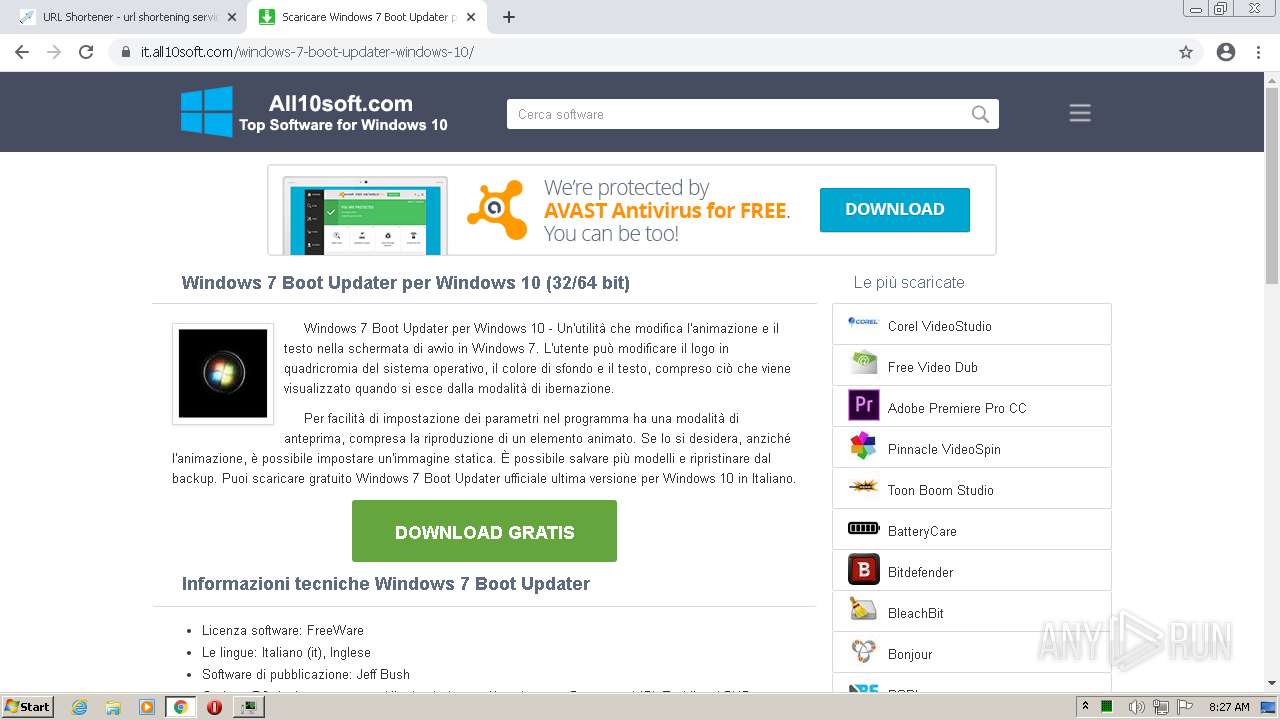
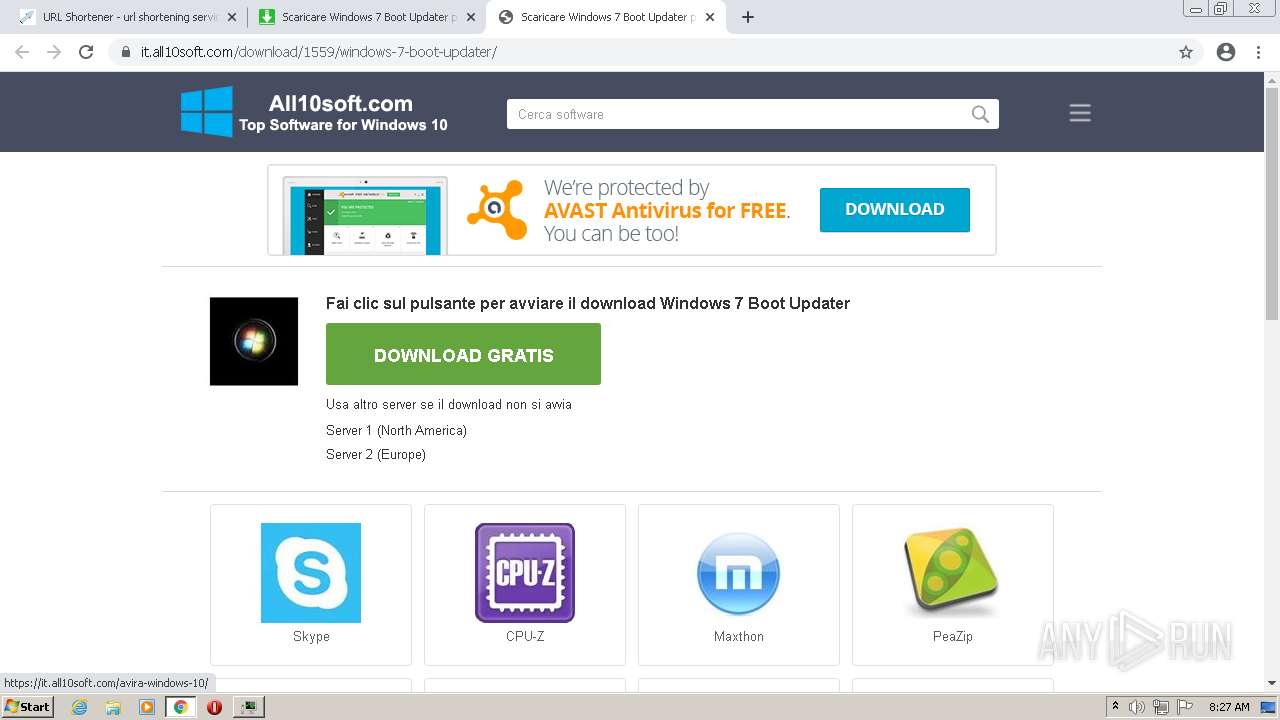
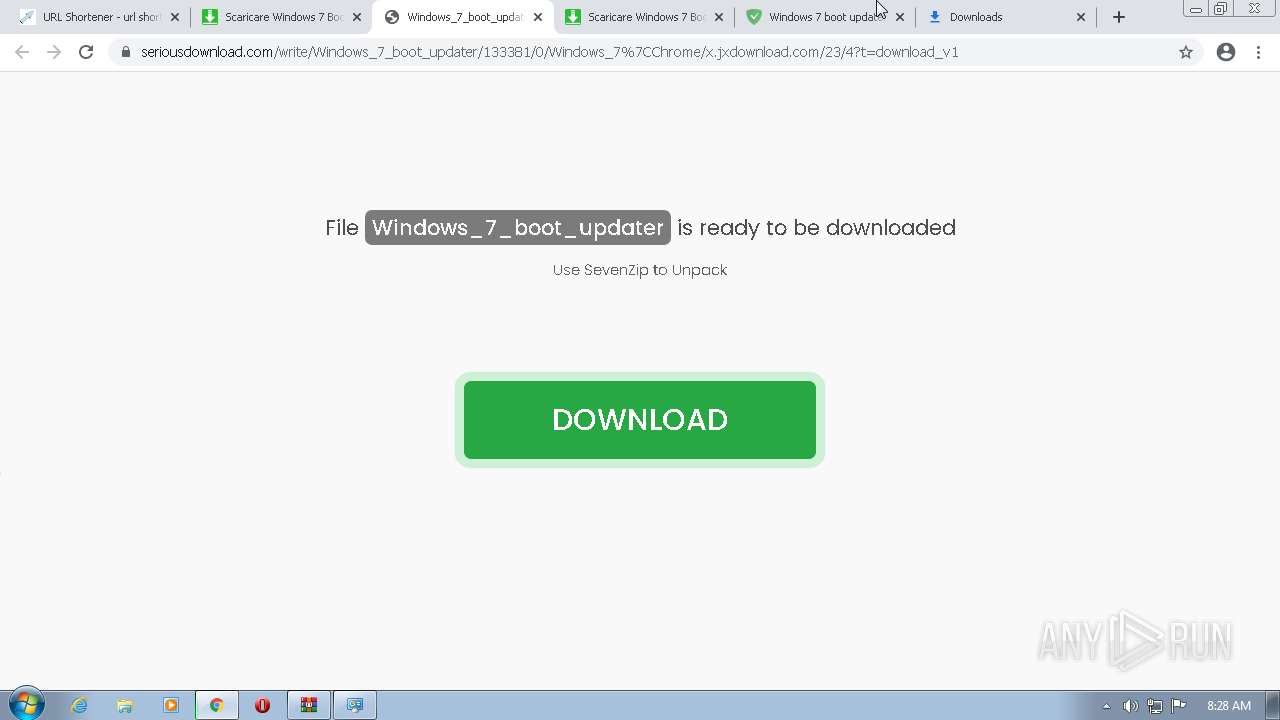
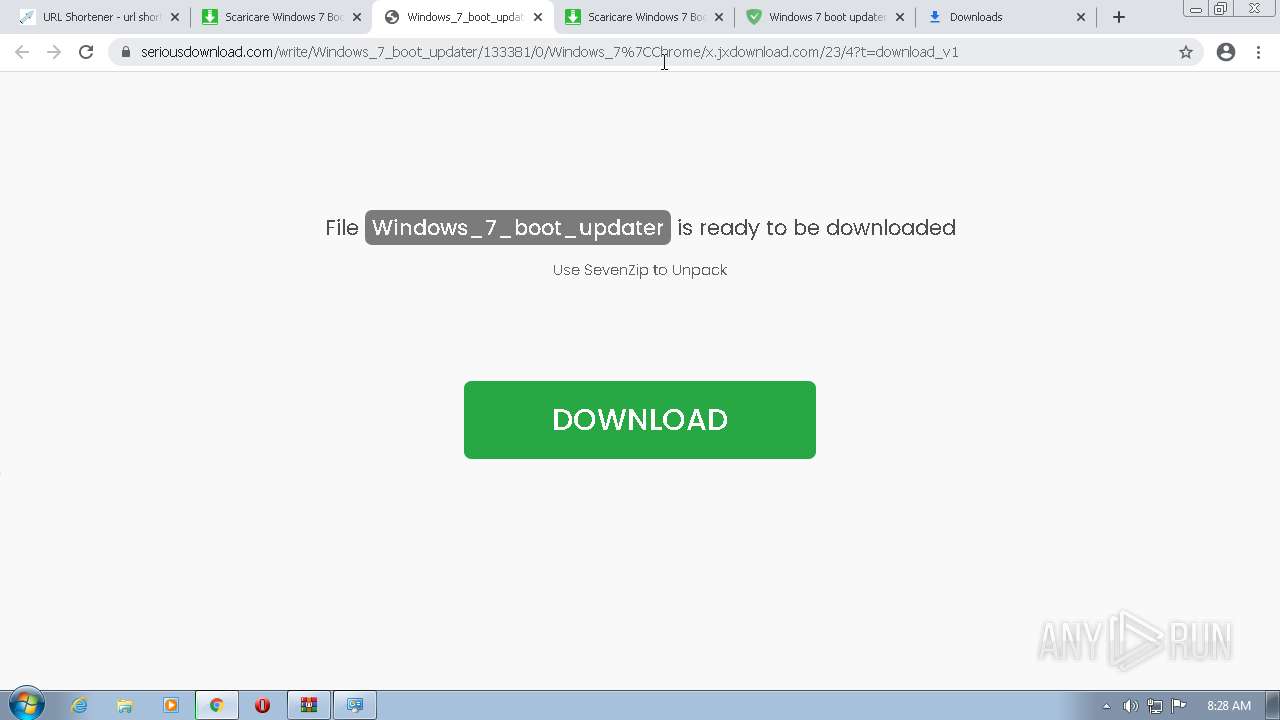
| Verdict: | Malicious activity |
| Analysis date: | January 30, 2022, 08:25:11 |
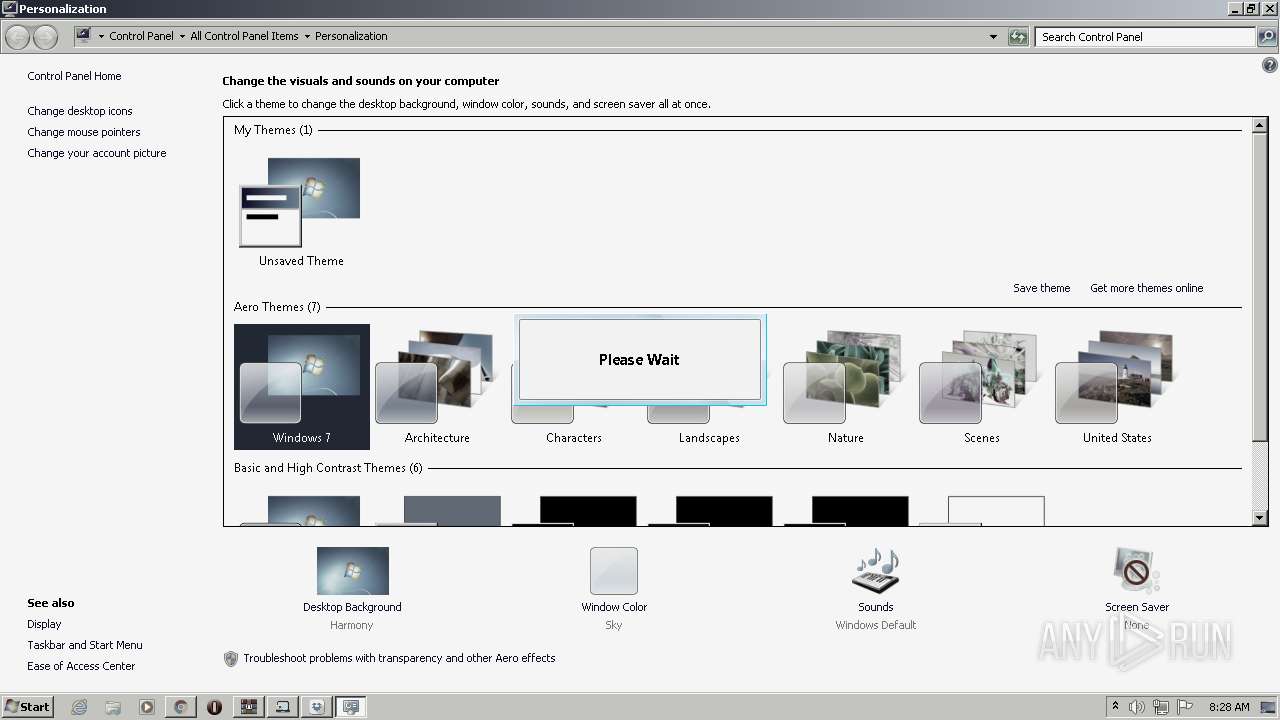
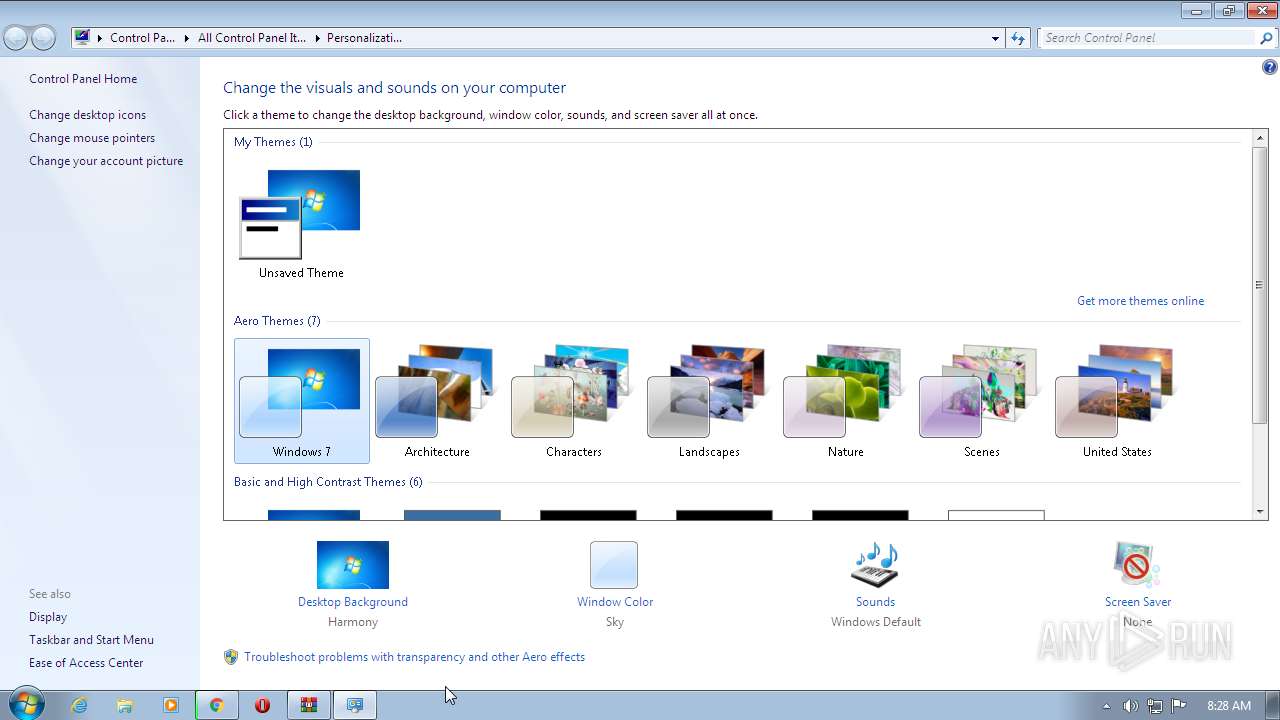
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 193F9379ADC77240D07264318DAD6BA8 |
| SHA1: | CF14A349966A2200C46EFC19F9E560CEF1753295 |
| SHA256: | DF65CA68CE6FC3F7912E6771D54117488AEA1A84D6B522E1A0FFFA6FD86CA7F5 |
| SSDEEP: | 3:N8MFXJwJNSML8Zncj:2MFXeNSB9cj |
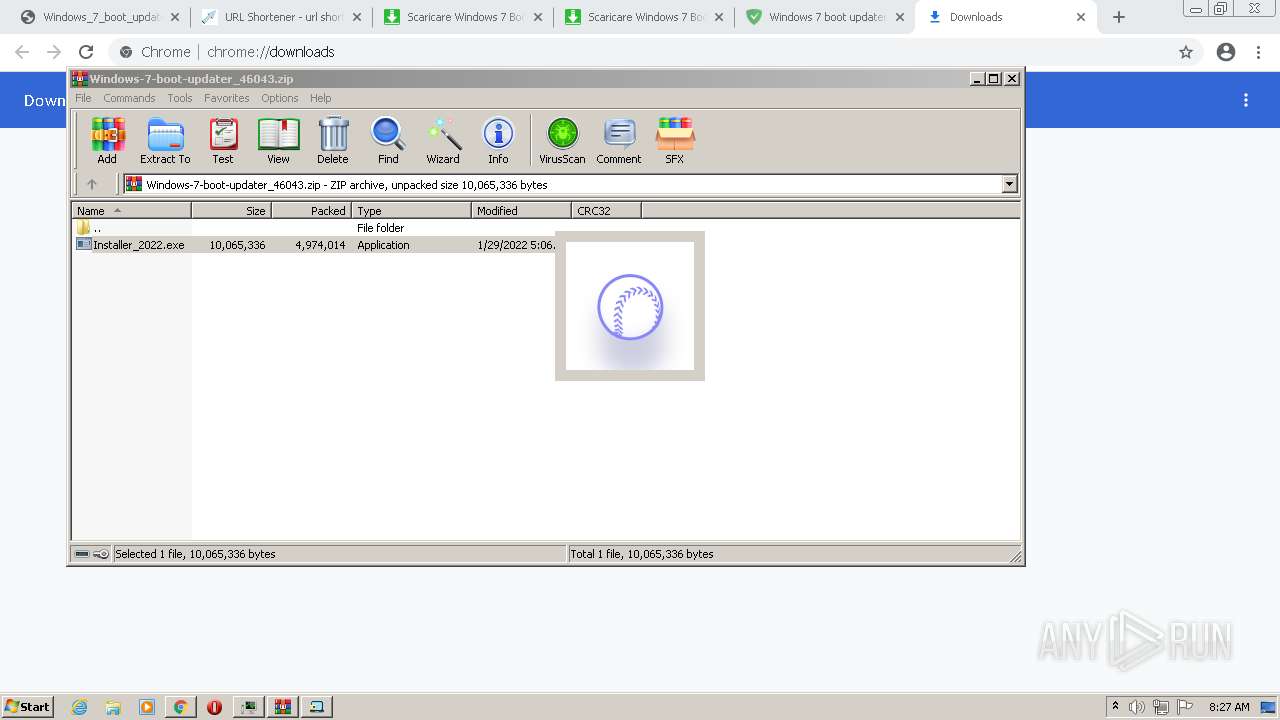
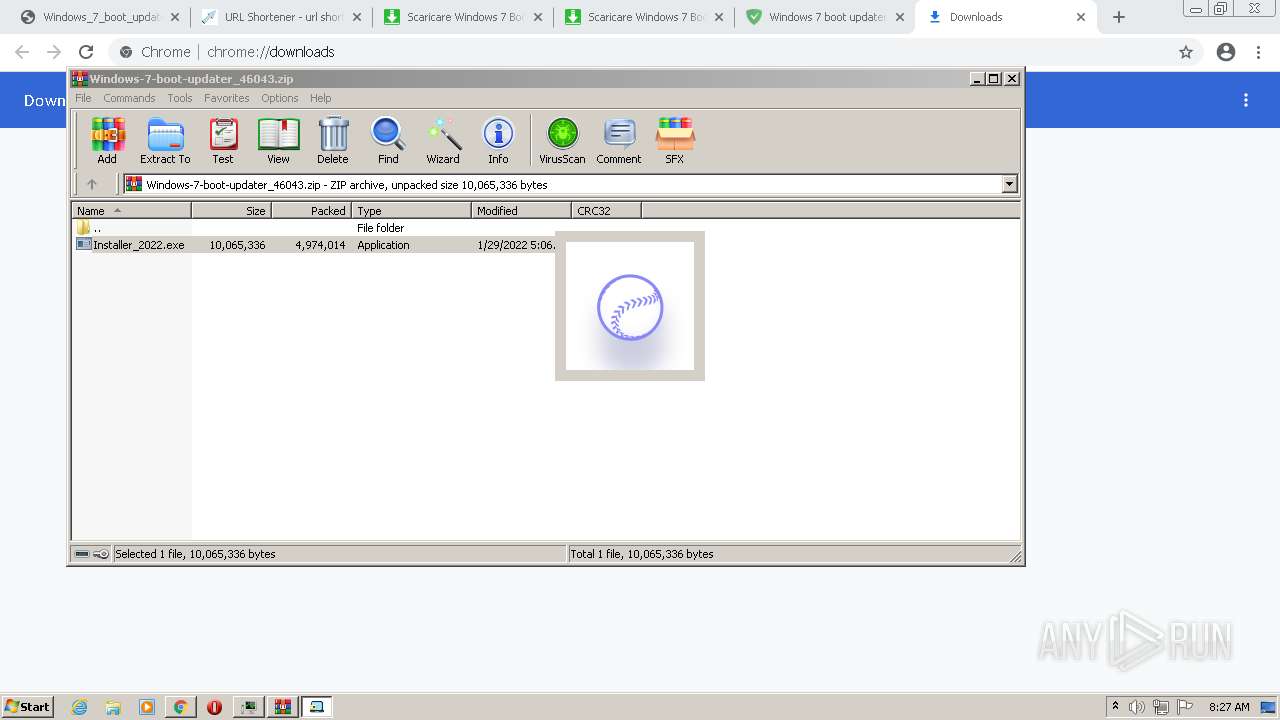
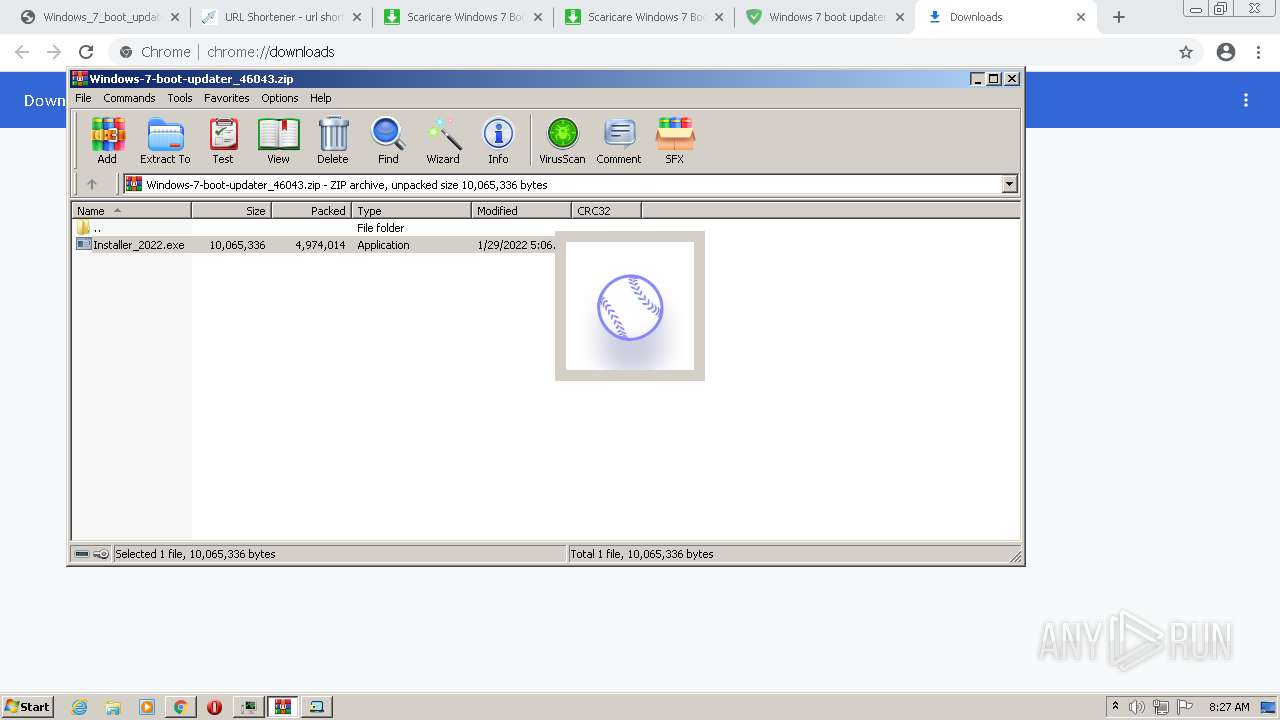
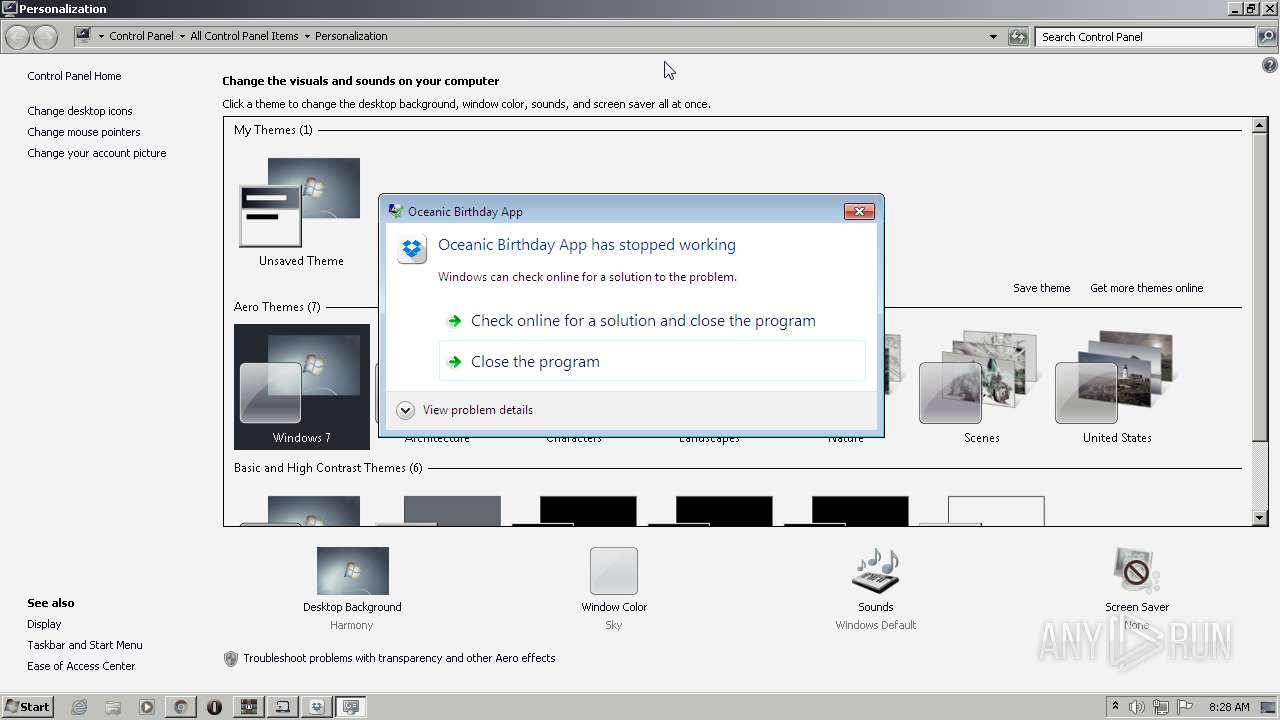
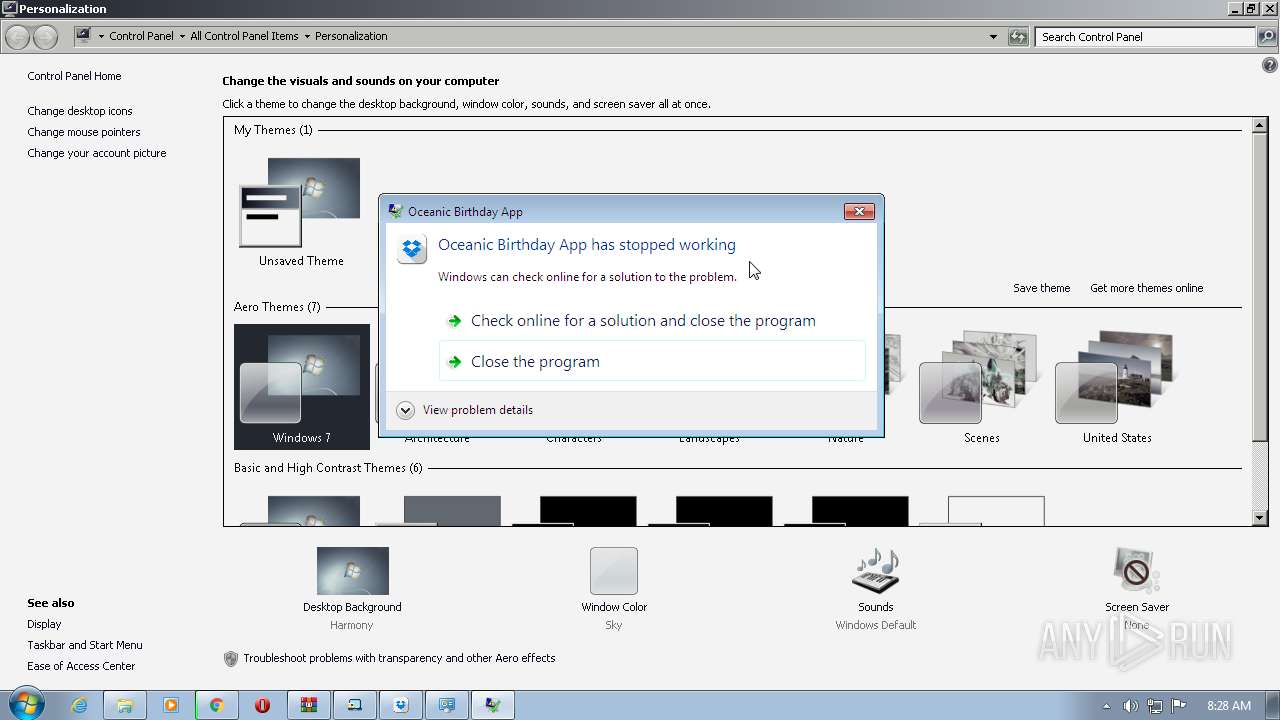
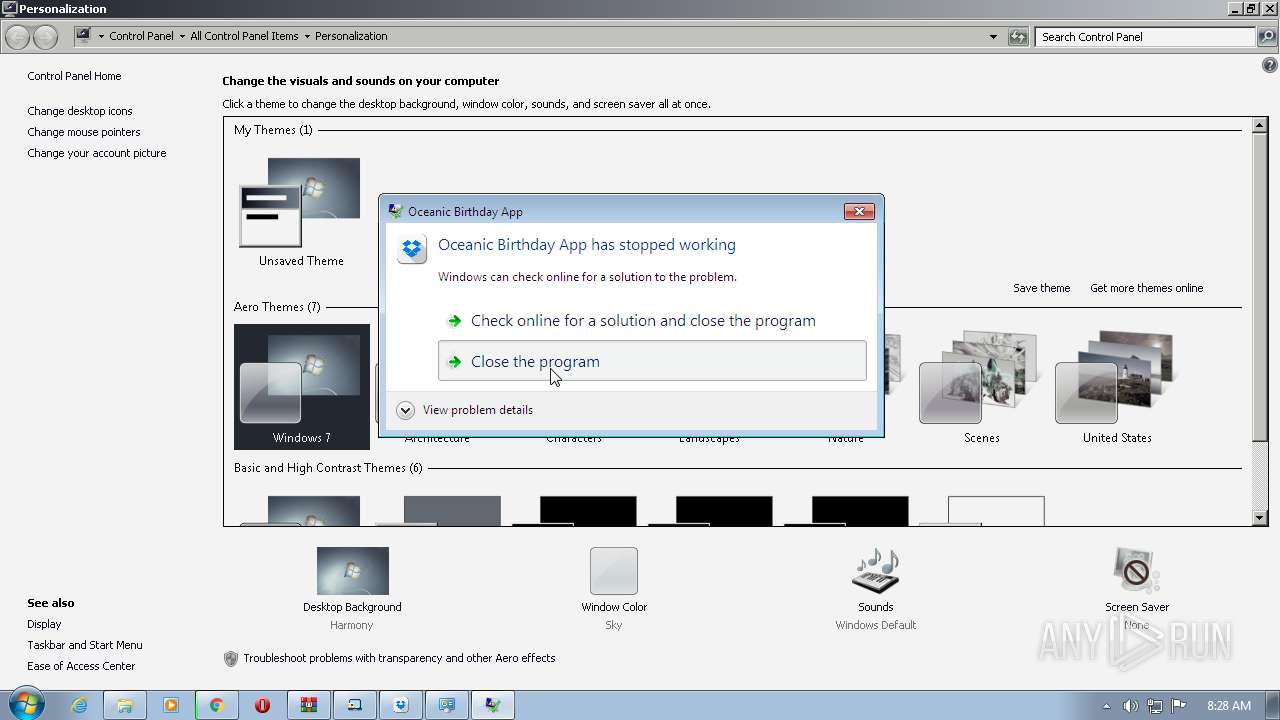
MALICIOUS
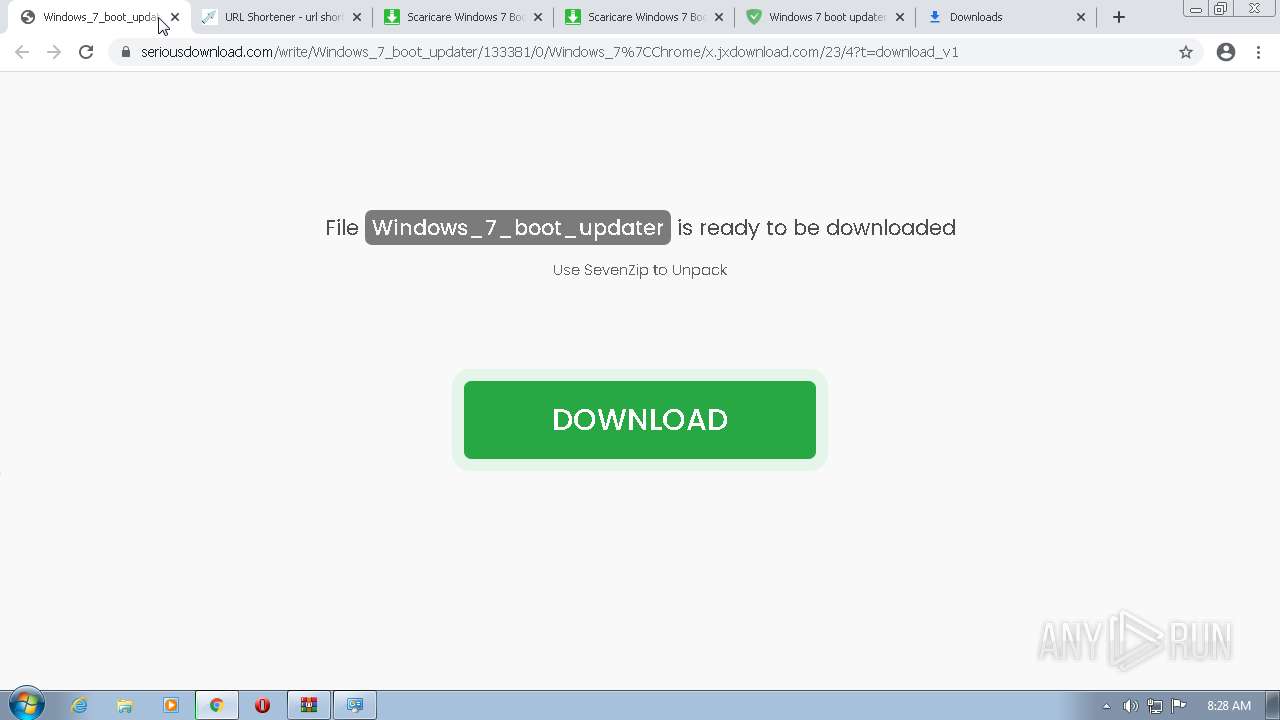
Application was dropped or rewritten from another process
- Installer_2022.exe (PID: 2864)
- Installer_2022.exe (PID: 3016)
- InnocentxUtil.exe (PID: 904)
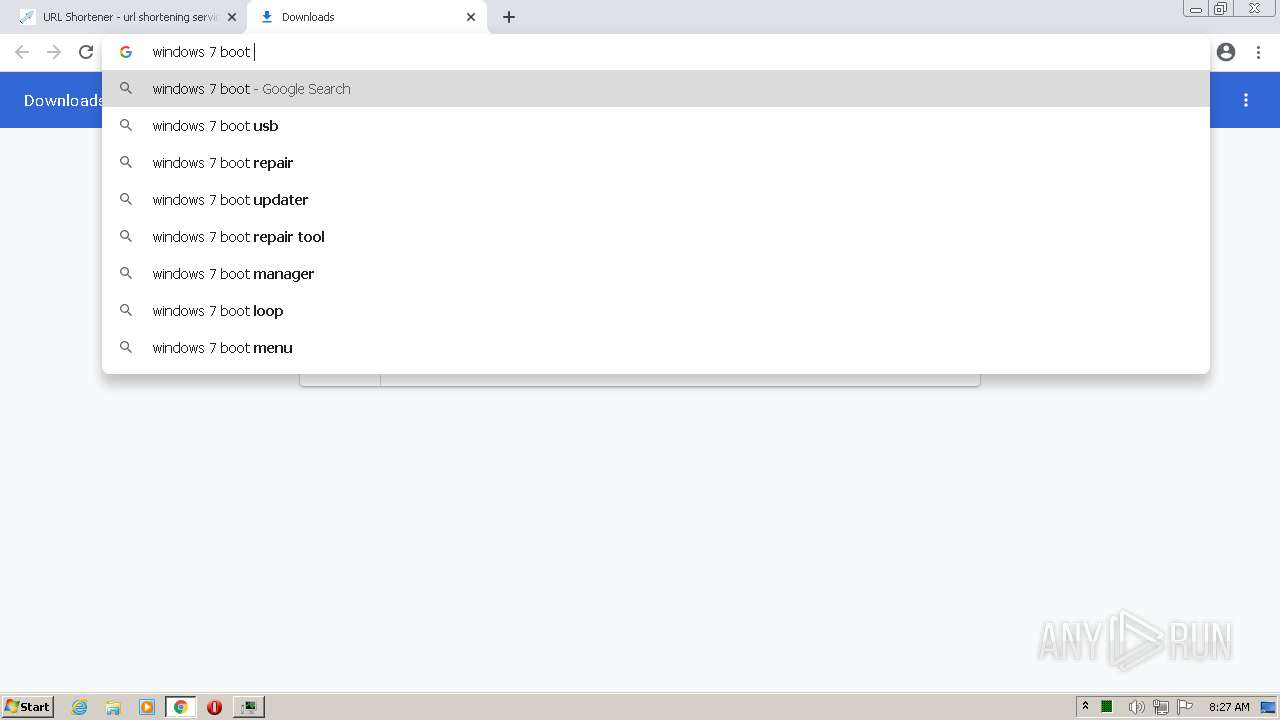
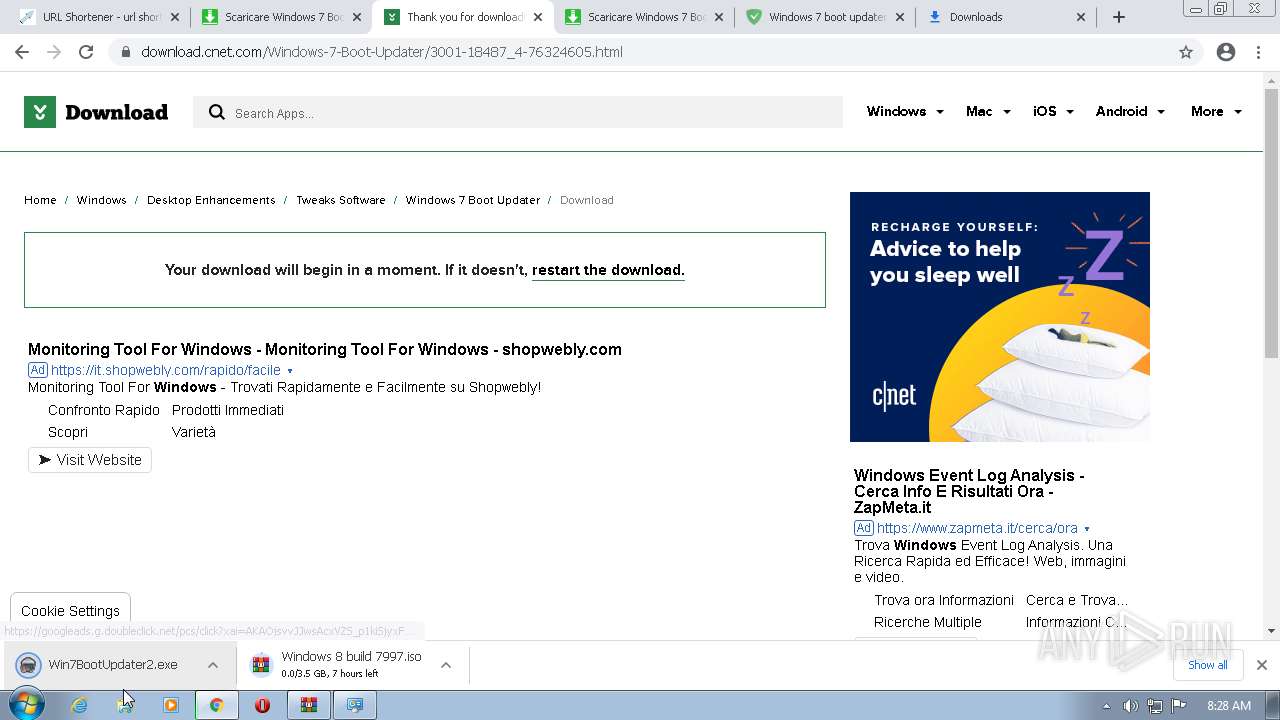
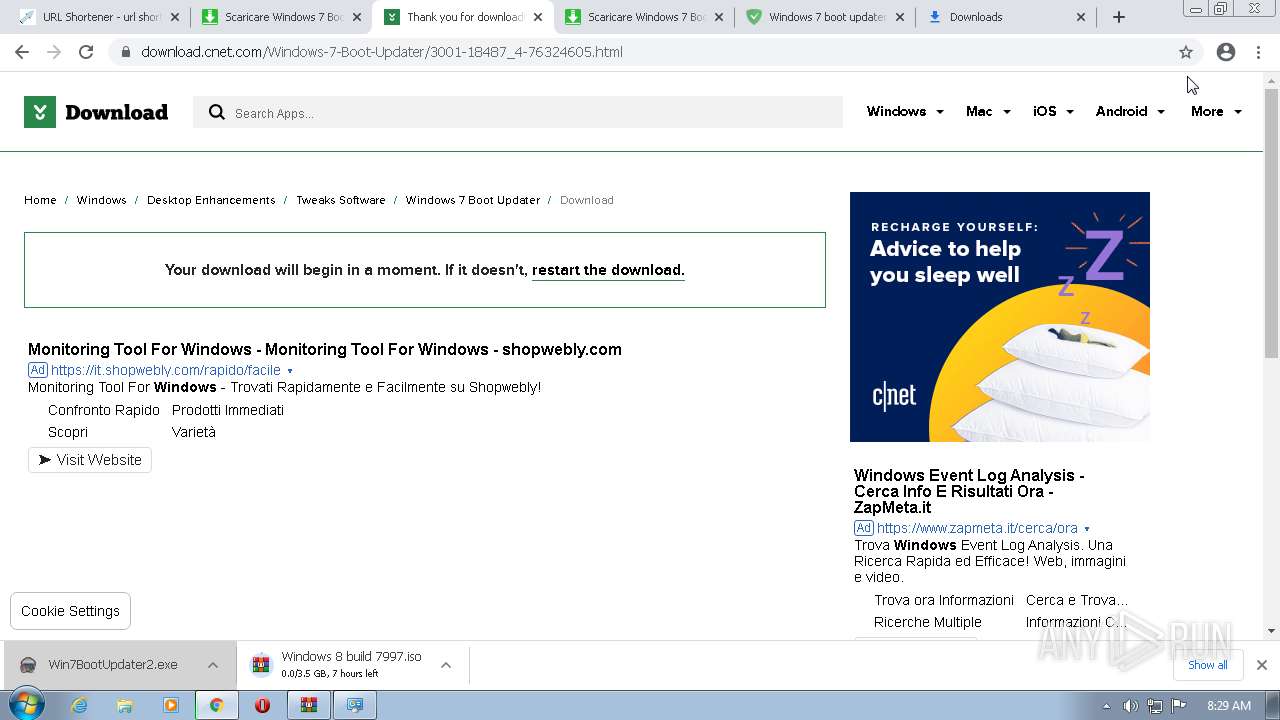
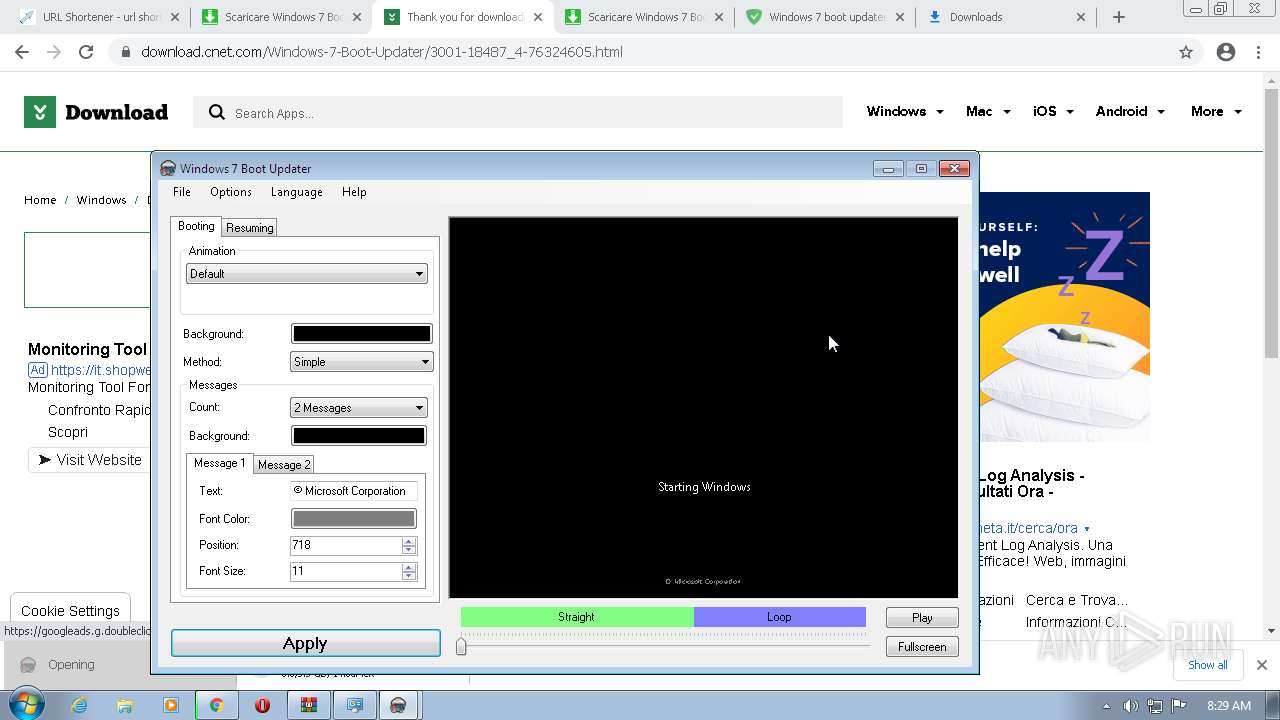
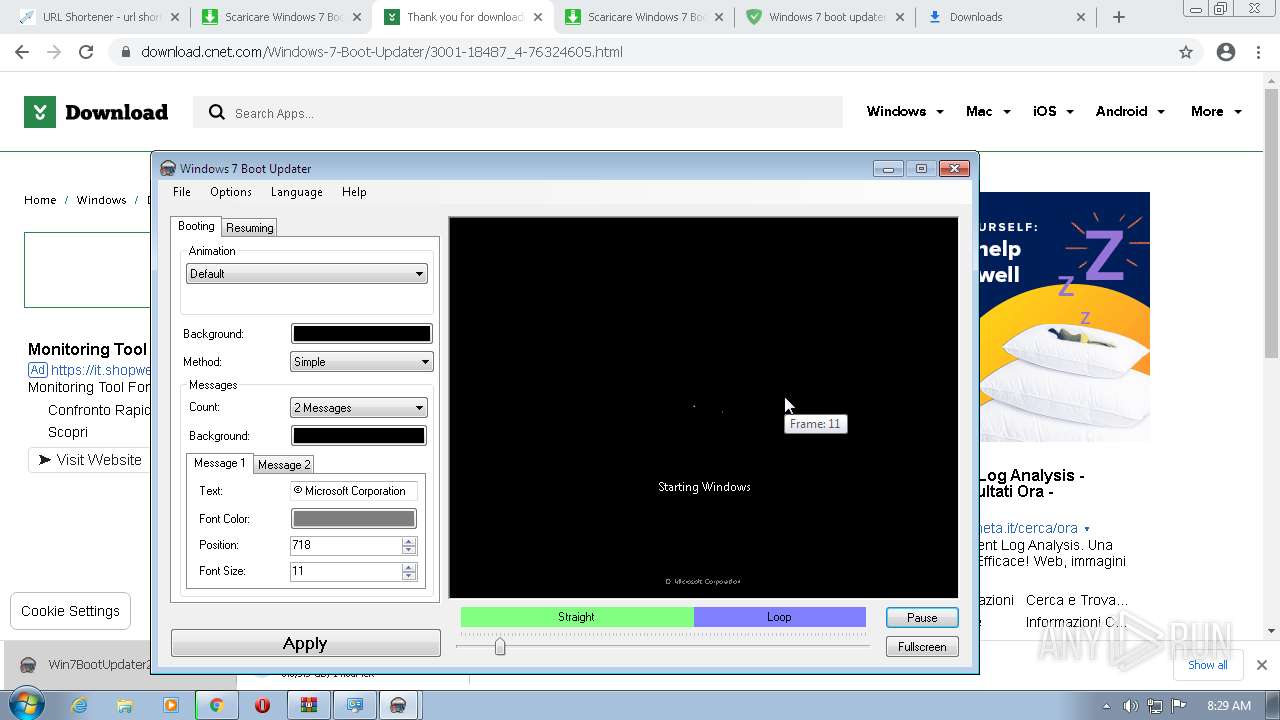
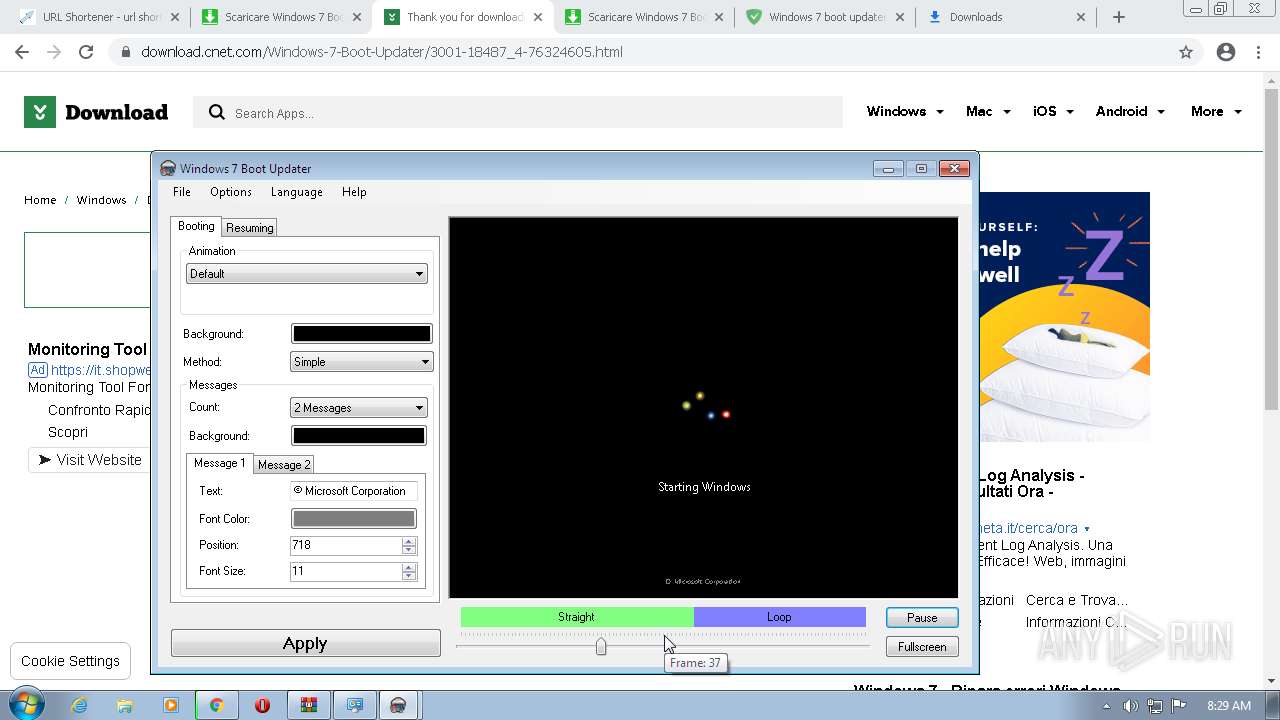
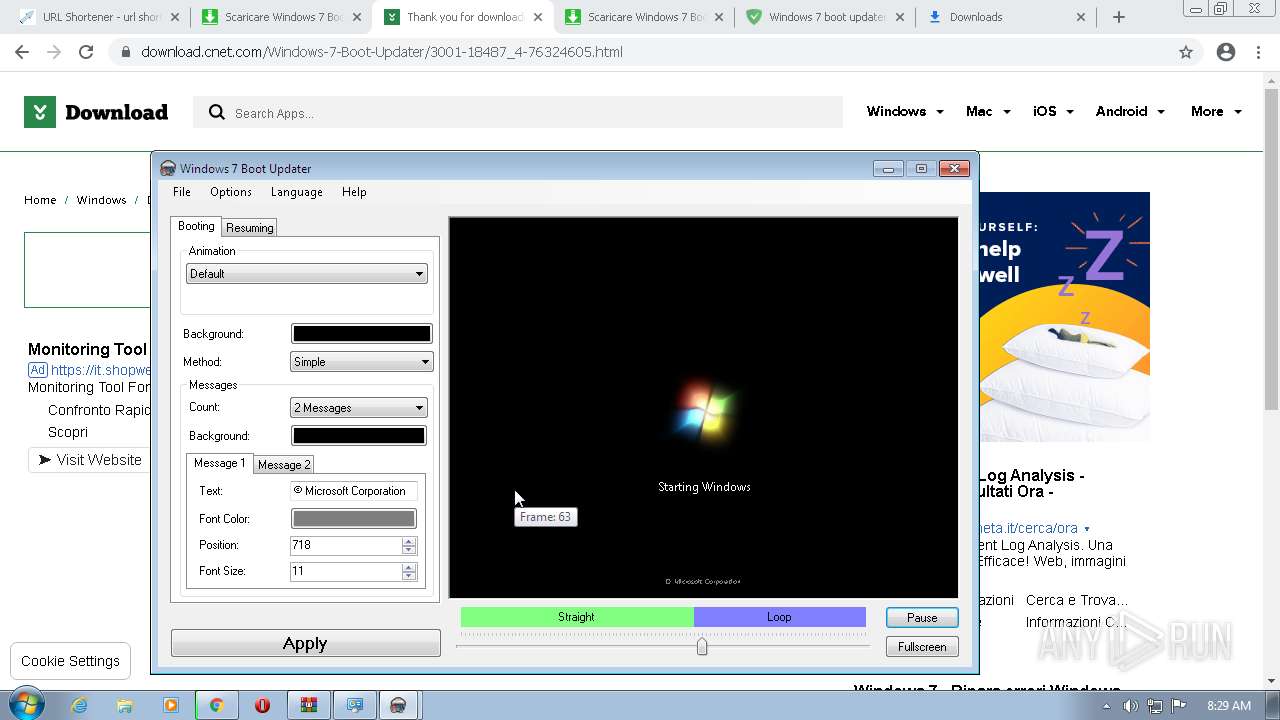
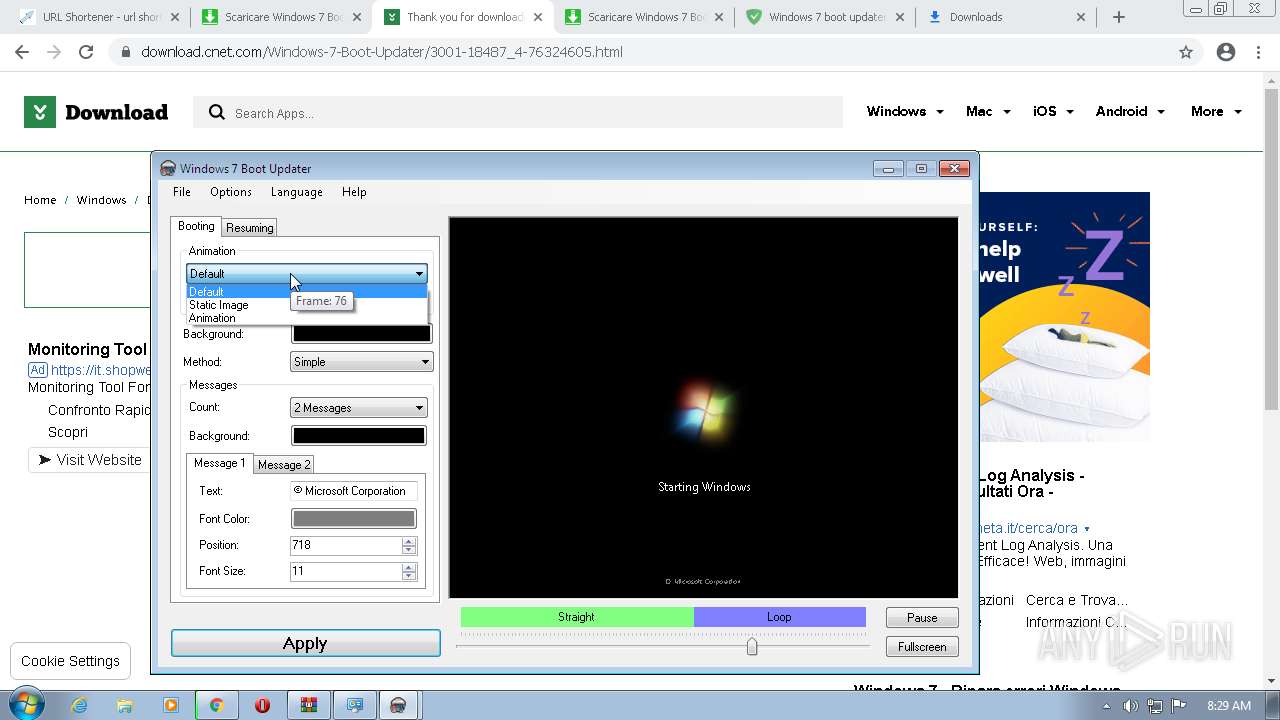
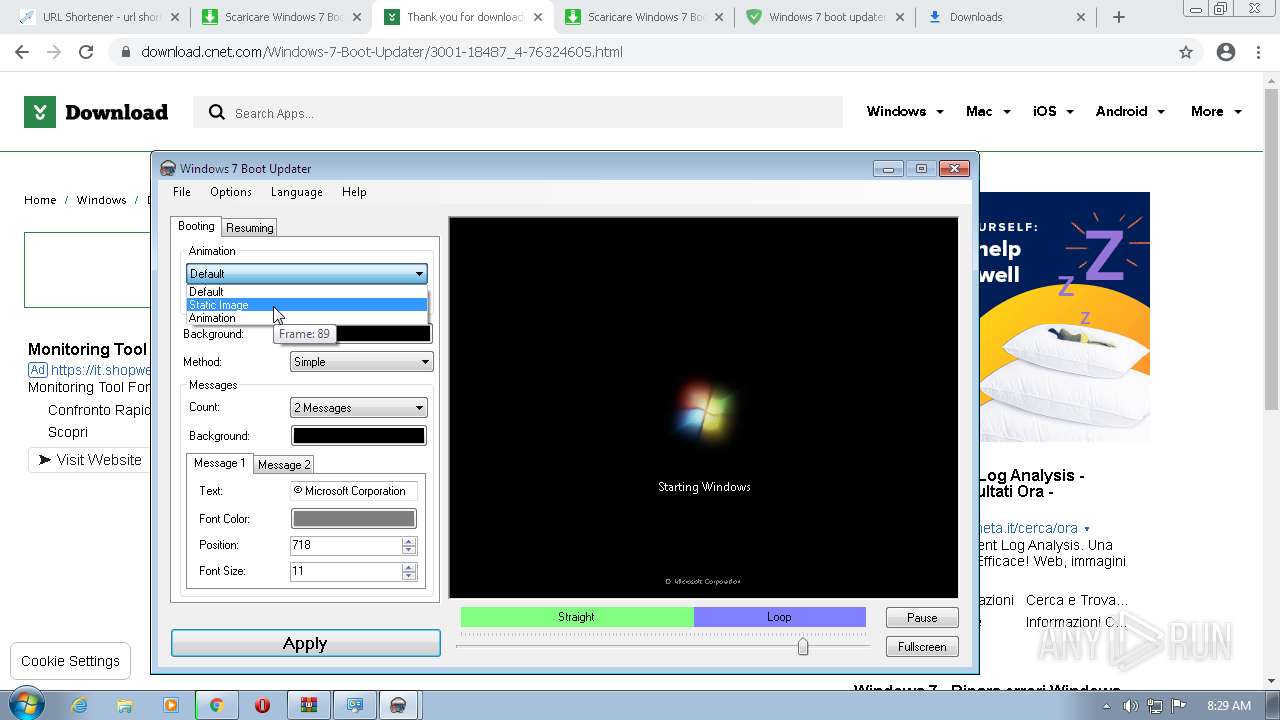
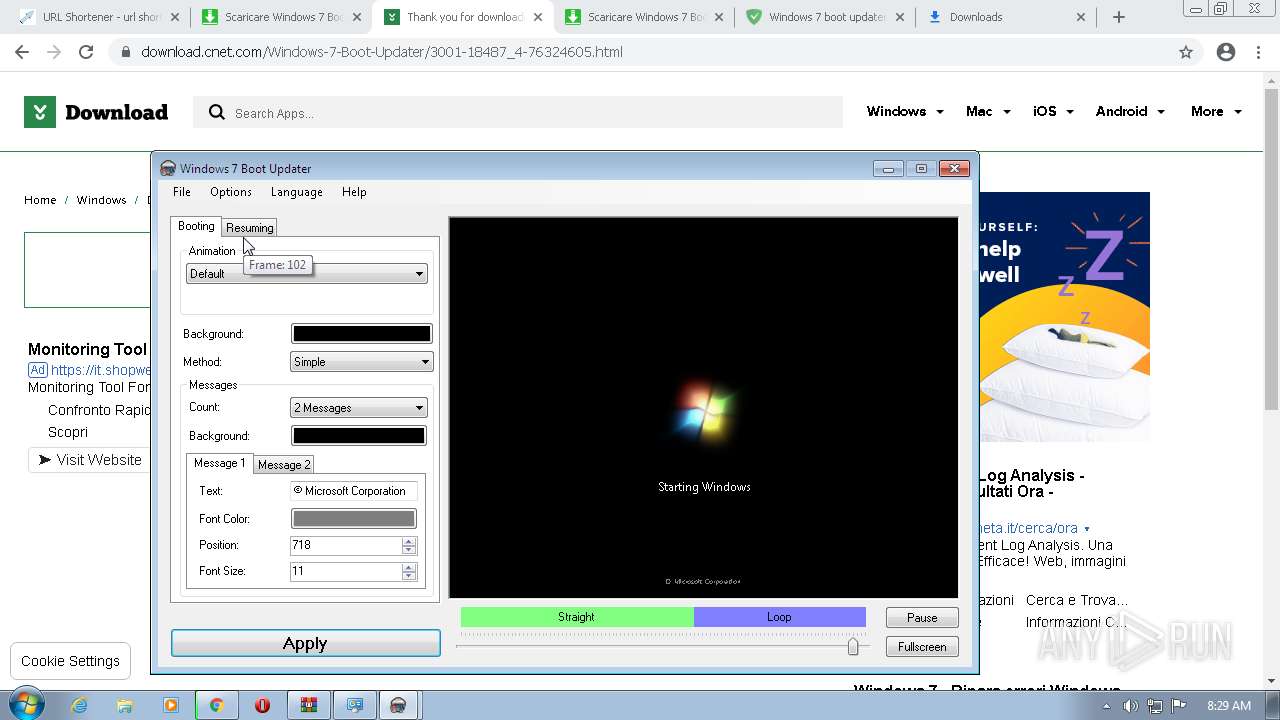
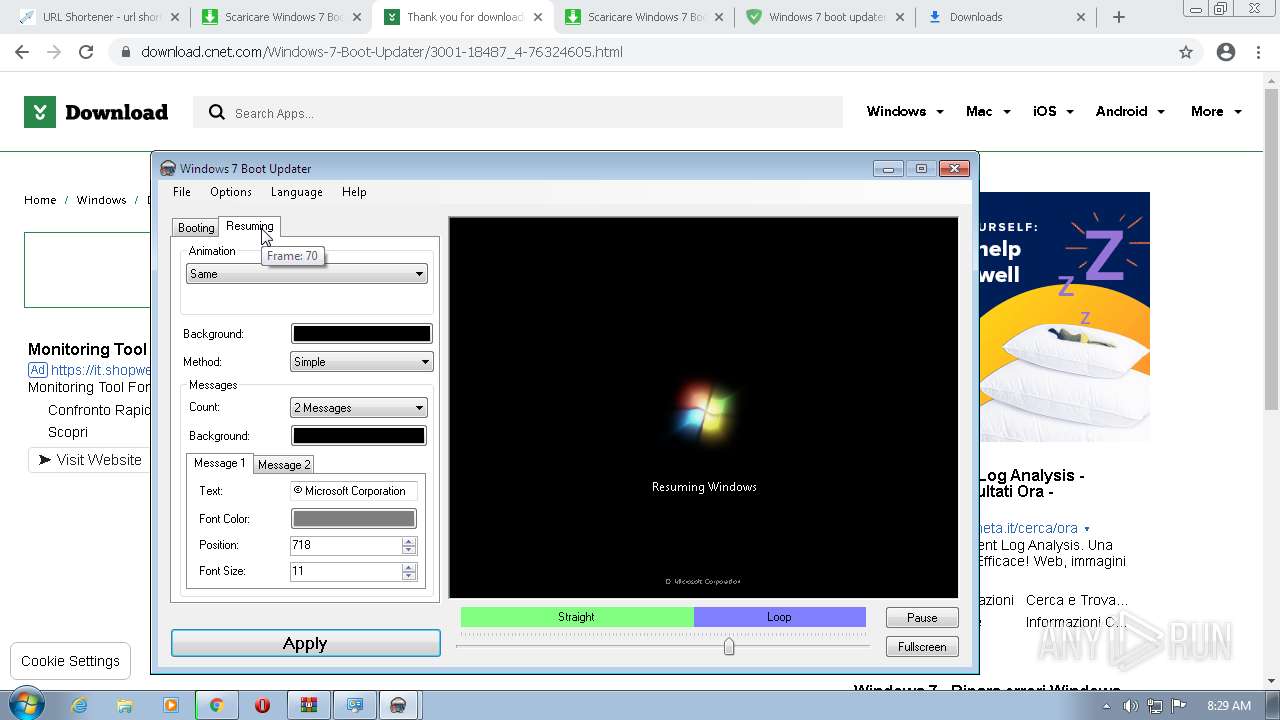
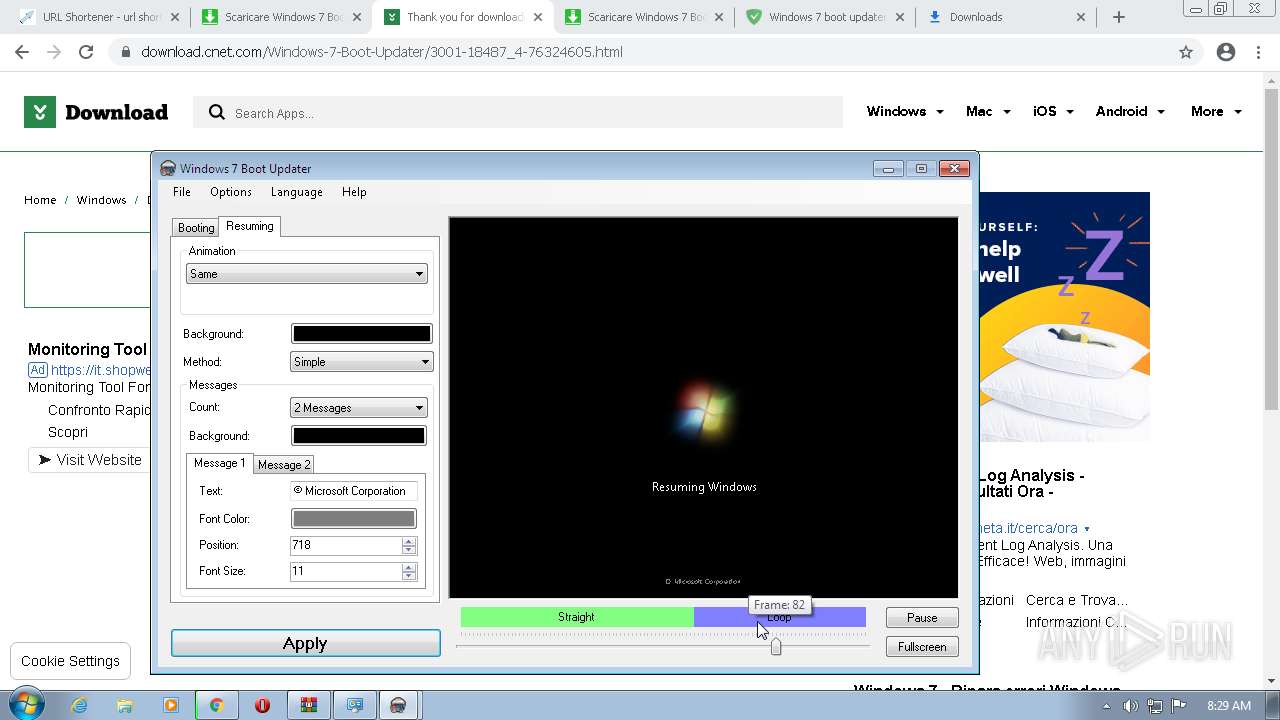
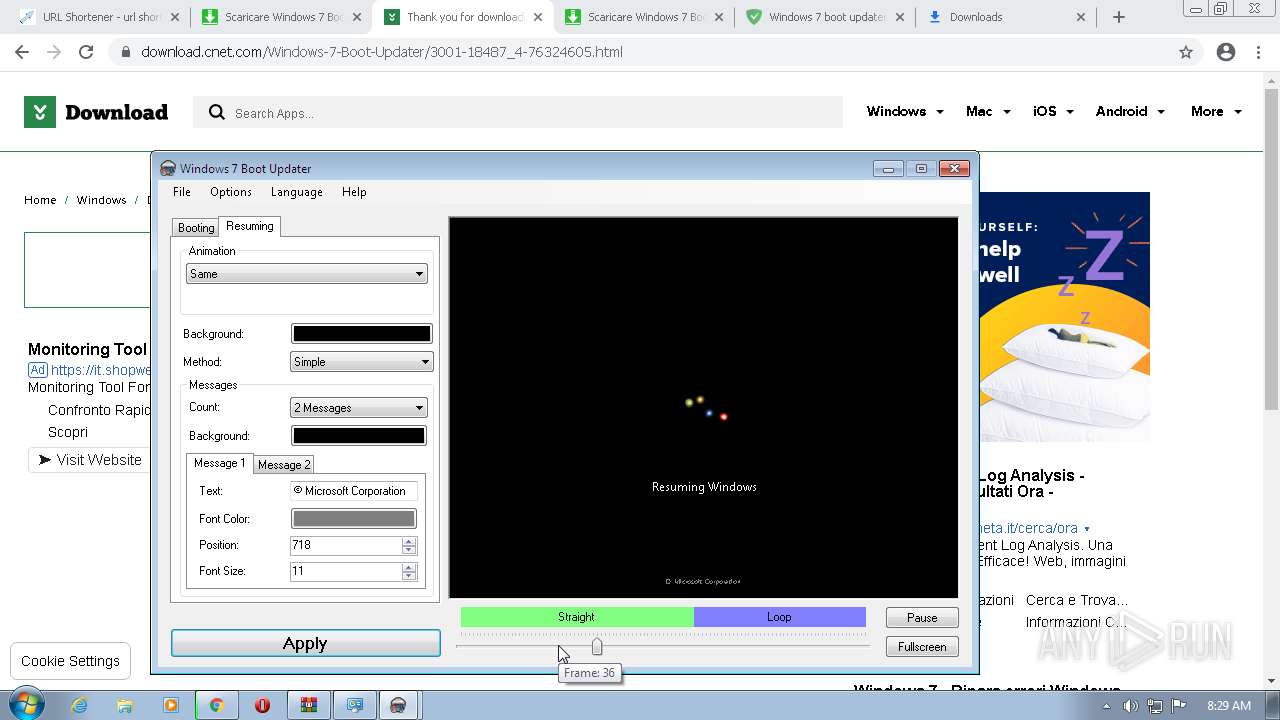
- Win7BootUpdater2.exe (PID: 1212)
- Win7BootUpdater2.exe (PID: 2228)
- Win7BootUpdater2.exe (PID: 3204)
- Win7BootUpdater2.exe (PID: 3908)
Loads dropped or rewritten executable
- Installer_2022.exe (PID: 3016)
Drops executable file immediately after starts
- chrome.exe (PID: 1820)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3060)
- Installer_2022.exe (PID: 2864)
- Installer_2022.exe (PID: 3016)
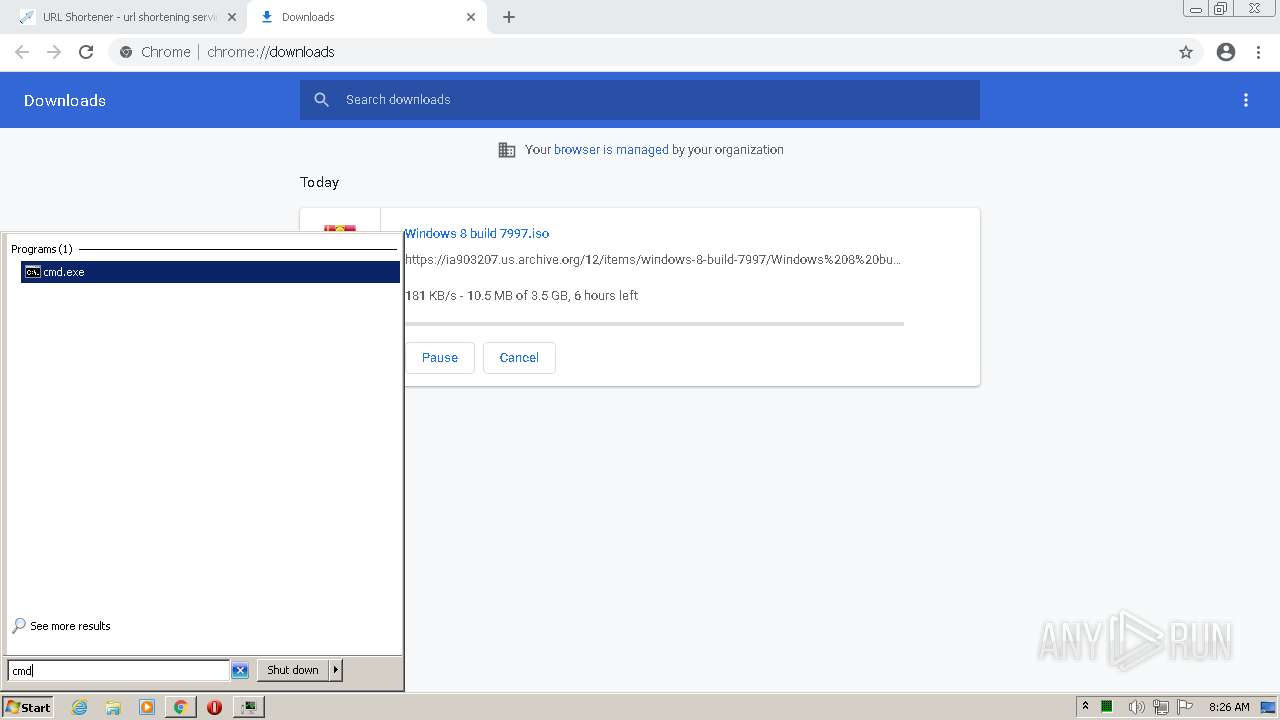
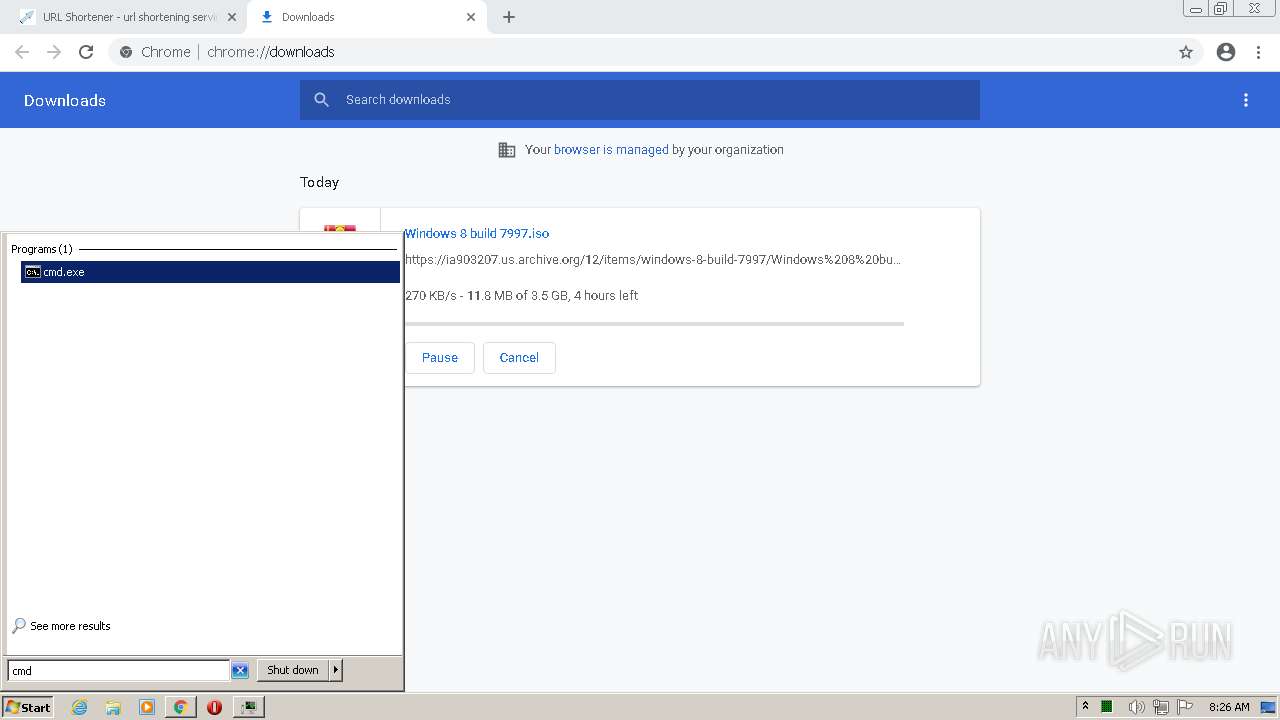
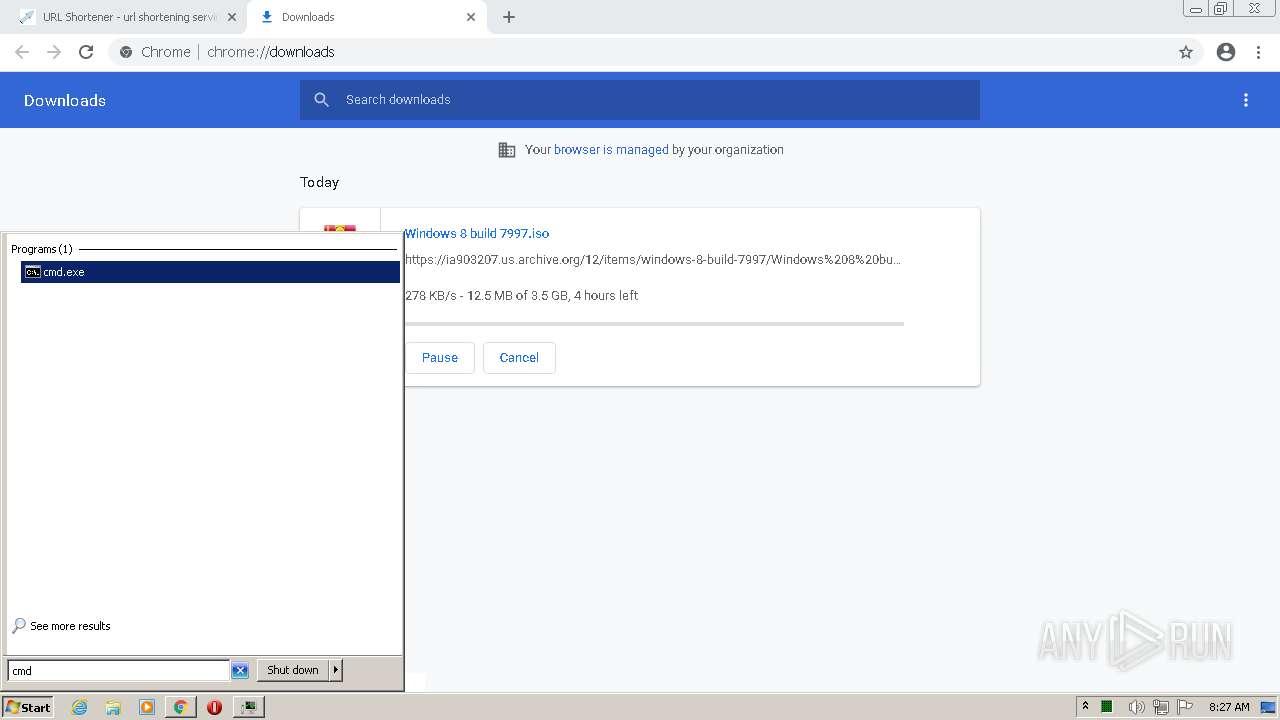
- cmd.exe (PID: 520)
- cmd.exe (PID: 1076)
- cmd.exe (PID: 3428)
- cmd.exe (PID: 912)
- cmd.exe (PID: 1232)
- cmd.exe (PID: 2556)
- InnocentxUtil.exe (PID: 904)
- Win7BootUpdater2.exe (PID: 3908)
- Win7BootUpdater2.exe (PID: 2228)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3060)
- Installer_2022.exe (PID: 3016)
- chrome.exe (PID: 1820)
- chrome.exe (PID: 3652)
Reads the computer name
- Installer_2022.exe (PID: 2864)
- Installer_2022.exe (PID: 3016)
- WinRAR.exe (PID: 3060)
- InnocentxUtil.exe (PID: 904)
- Win7BootUpdater2.exe (PID: 3908)
- Win7BootUpdater2.exe (PID: 2228)
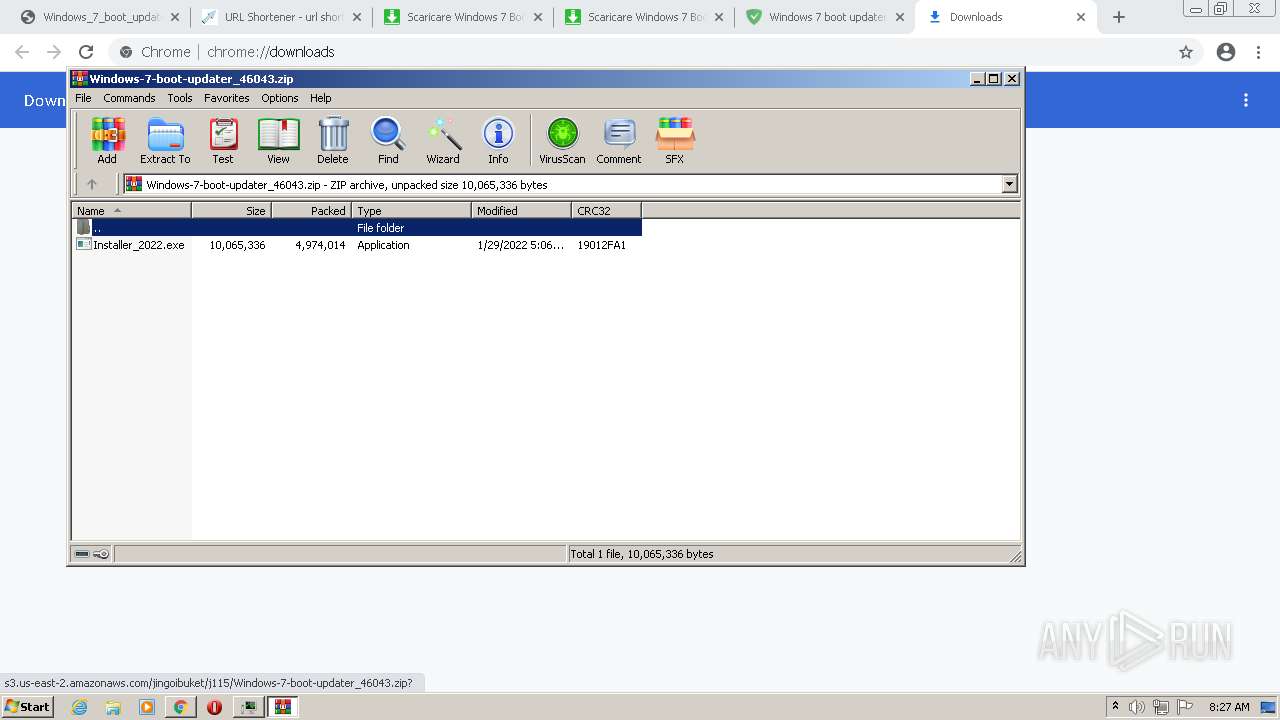
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3060)
- Installer_2022.exe (PID: 3016)
Application launched itself
- Installer_2022.exe (PID: 2864)
- cmd.exe (PID: 520)
- cmd.exe (PID: 1076)
- cmd.exe (PID: 3428)
- cmd.exe (PID: 912)
- cmd.exe (PID: 1232)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 1820)
Creates a directory in Program Files
- Installer_2022.exe (PID: 3016)
Creates files in the program directory
- Installer_2022.exe (PID: 3016)
Starts CMD.EXE for commands execution
- Installer_2022.exe (PID: 3016)
- cmd.exe (PID: 520)
- cmd.exe (PID: 1076)
- cmd.exe (PID: 3428)
- cmd.exe (PID: 1232)
- cmd.exe (PID: 912)
Reads Environment values
- InnocentxUtil.exe (PID: 904)
- Win7BootUpdater2.exe (PID: 3908)
- Win7BootUpdater2.exe (PID: 2228)
Searches for installed software
- InnocentxUtil.exe (PID: 904)
INFO
Application launched itself
- chrome.exe (PID: 3652)
Checks supported languages
- chrome.exe (PID: 3864)
- chrome.exe (PID: 128)
- chrome.exe (PID: 2588)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 2272)
- chrome.exe (PID: 1508)
- chrome.exe (PID: 2508)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 432)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 3456)
- chrome.exe (PID: 1536)
- chrome.exe (PID: 2948)
- chrome.exe (PID: 2764)
- chrome.exe (PID: 3824)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 2684)
- chrome.exe (PID: 2220)
- chrome.exe (PID: 3364)
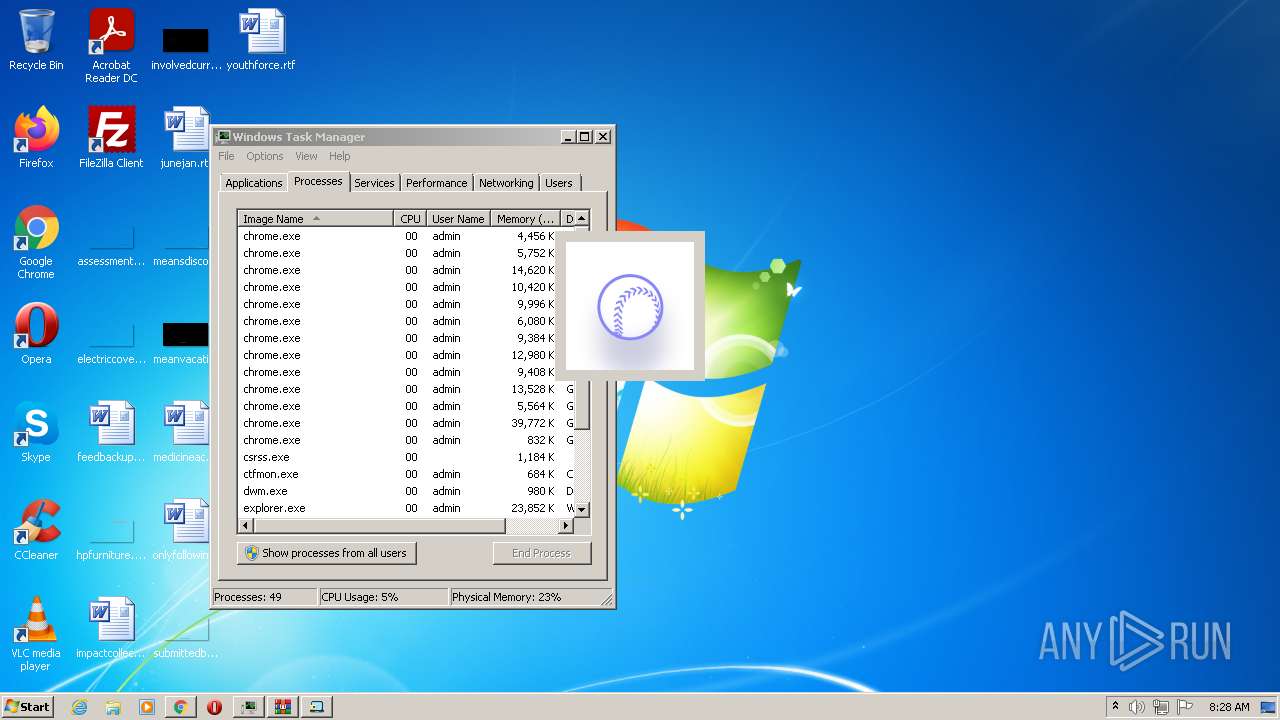
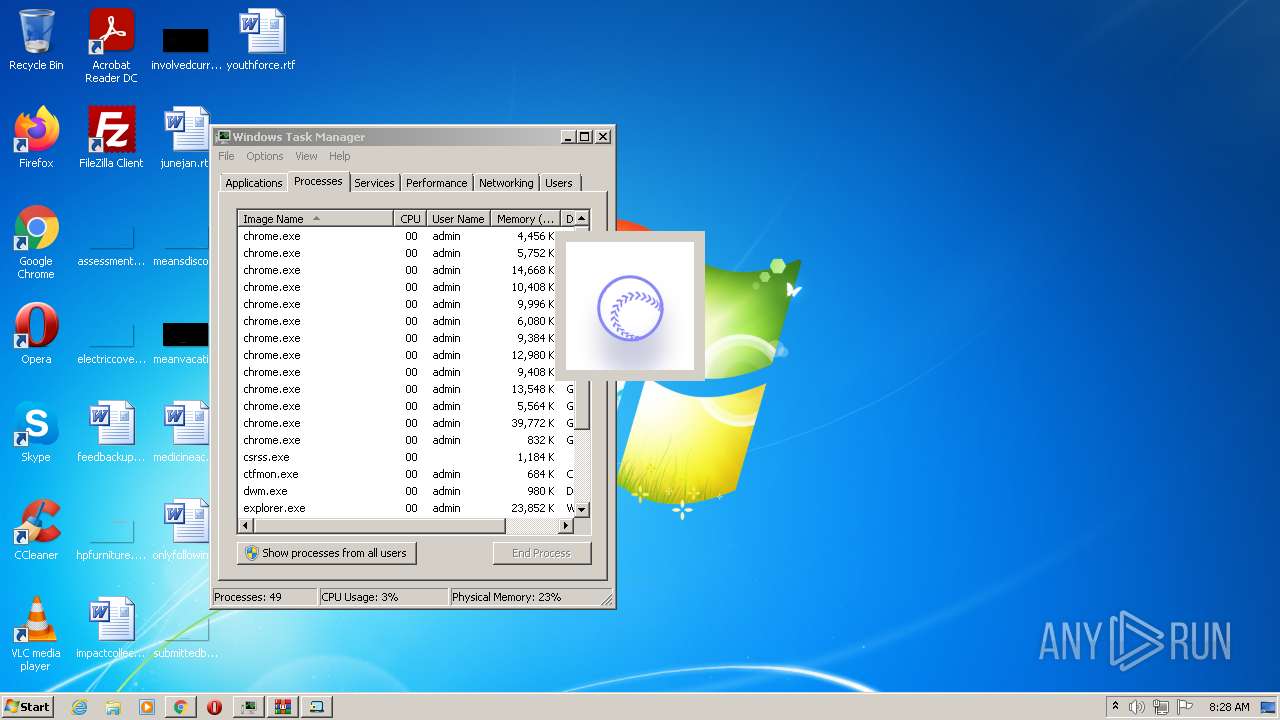
- taskmgr.exe (PID: 3996)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 3648)
- wininit.exe (PID: 128)
- chrome.exe (PID: 2296)
- chrome.exe (PID: 3524)
- chrome.exe (PID: 3968)
- chrome.exe (PID: 3732)
- chrome.exe (PID: 3040)
- chrome.exe (PID: 3344)
- chrome.exe (PID: 148)
- chrome.exe (PID: 3936)
- chrome.exe (PID: 3648)
- chrome.exe (PID: 2212)
- chrome.exe (PID: 3100)
- chrome.exe (PID: 2576)
- chrome.exe (PID: 1984)
- chrome.exe (PID: 3192)
- chrome.exe (PID: 2680)
- chrome.exe (PID: 956)
- chrome.exe (PID: 868)
- chrome.exe (PID: 2676)
- chrome.exe (PID: 3980)
- chrome.exe (PID: 2684)
- chrome.exe (PID: 2264)
- chrome.exe (PID: 948)
- chrome.exe (PID: 2972)
- chrome.exe (PID: 3524)
- chrome.exe (PID: 1236)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 360)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 1884)
- chrome.exe (PID: 1820)
- chrome.exe (PID: 752)
- chrome.exe (PID: 524)
- chrome.exe (PID: 3340)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 3796)
- chrome.exe (PID: 148)
- chrome.exe (PID: 3340)
- chrome.exe (PID: 2464)
- chrome.exe (PID: 1872)
- chrome.exe (PID: 1212)
- chrome.exe (PID: 1508)
- chrome.exe (PID: 2232)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 3012)
- chrome.exe (PID: 2680)
Reads the computer name
- chrome.exe (PID: 2272)
- chrome.exe (PID: 128)
- chrome.exe (PID: 432)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 2508)
- chrome.exe (PID: 2220)
- chrome.exe (PID: 2948)
- chrome.exe (PID: 2684)
- chrome.exe (PID: 3824)
- taskmgr.exe (PID: 3996)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 2232)
- chrome.exe (PID: 2216)
Reads the hosts file
- chrome.exe (PID: 3652)
- chrome.exe (PID: 2272)
Reads settings of System Certificates
- chrome.exe (PID: 2272)
- InnocentxUtil.exe (PID: 904)
Reads the date of Windows installation
- chrome.exe (PID: 2220)
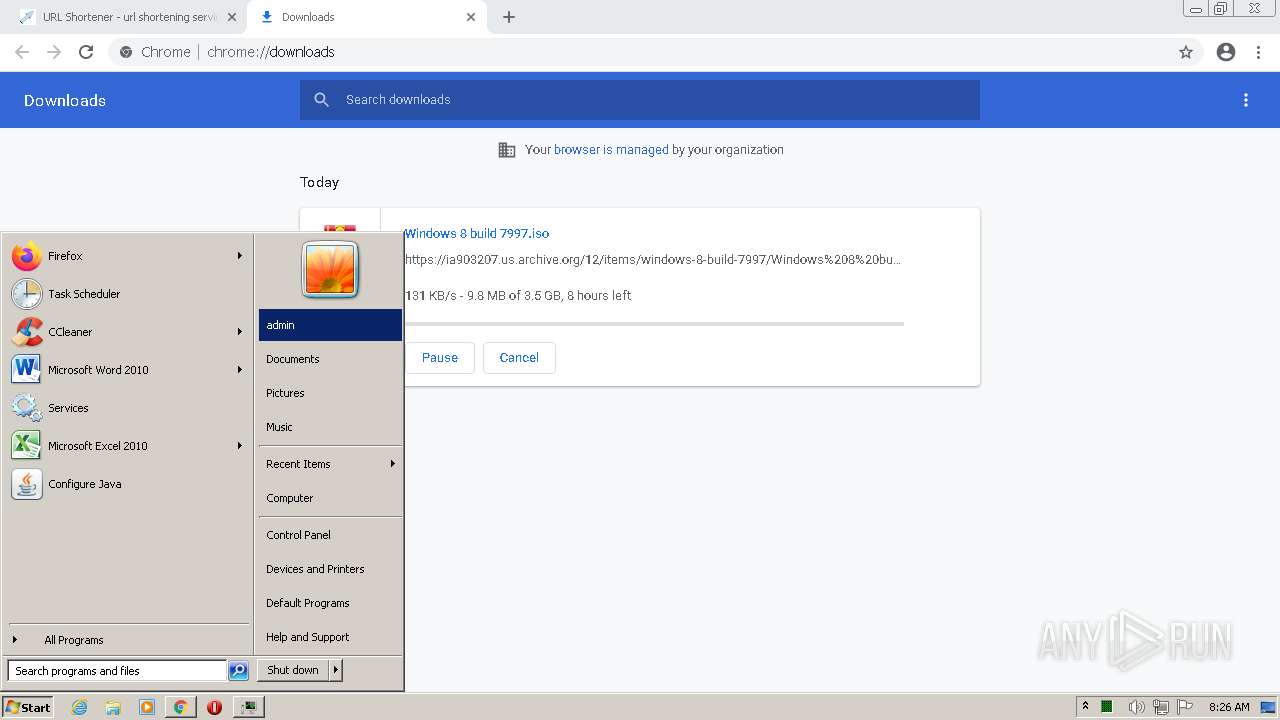
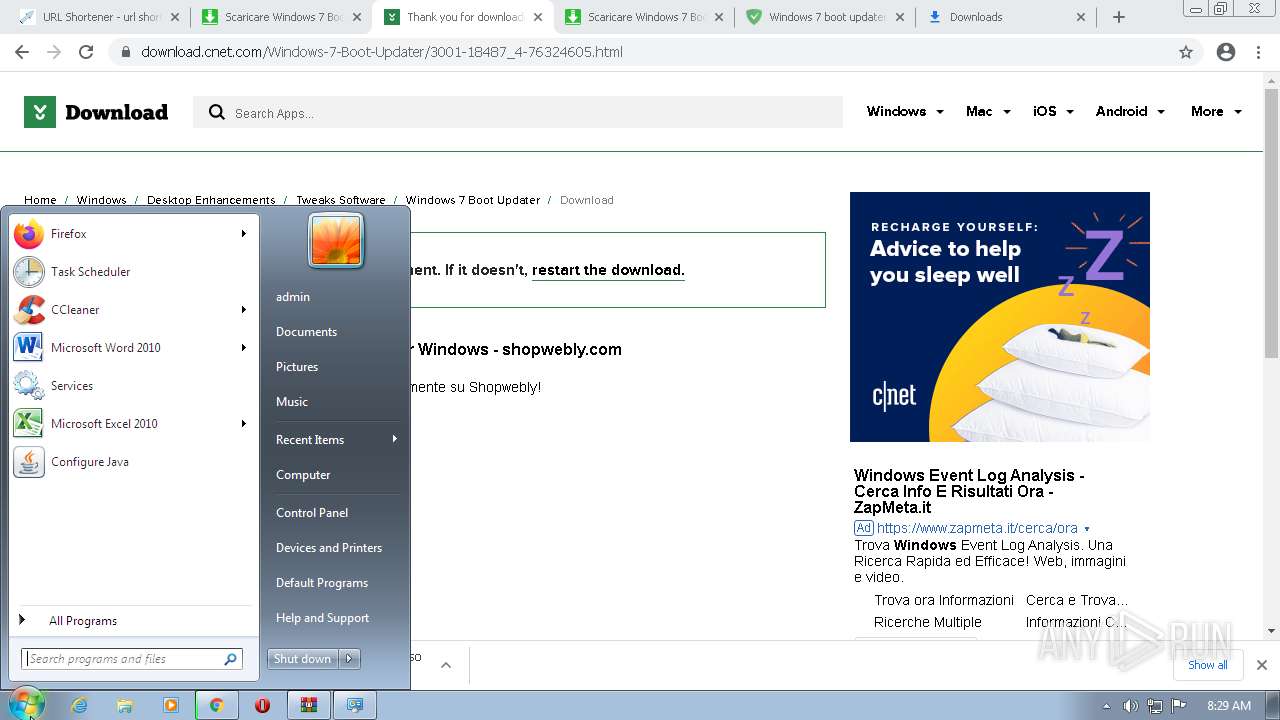
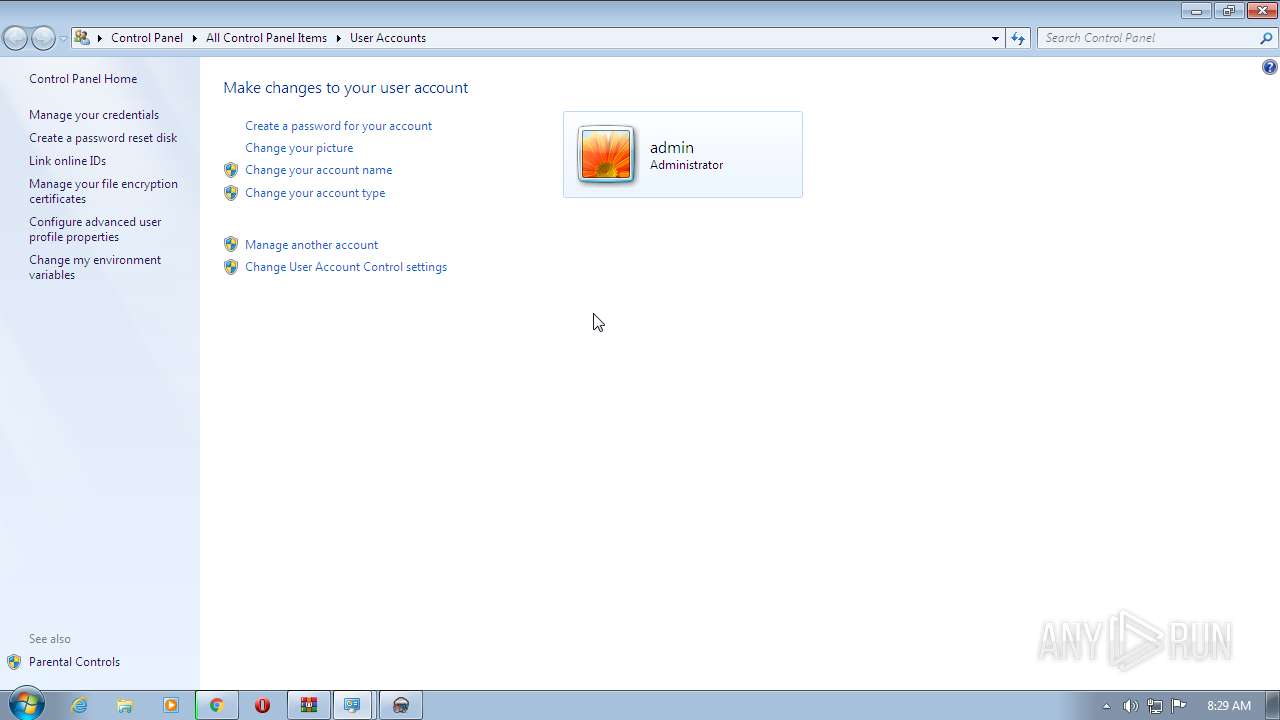
Manual execution by user
- wininit.exe (PID: 128)
- taskmgr.exe (PID: 3996)
Checks Windows Trust Settings
- InnocentxUtil.exe (PID: 904)
- chrome.exe (PID: 3652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
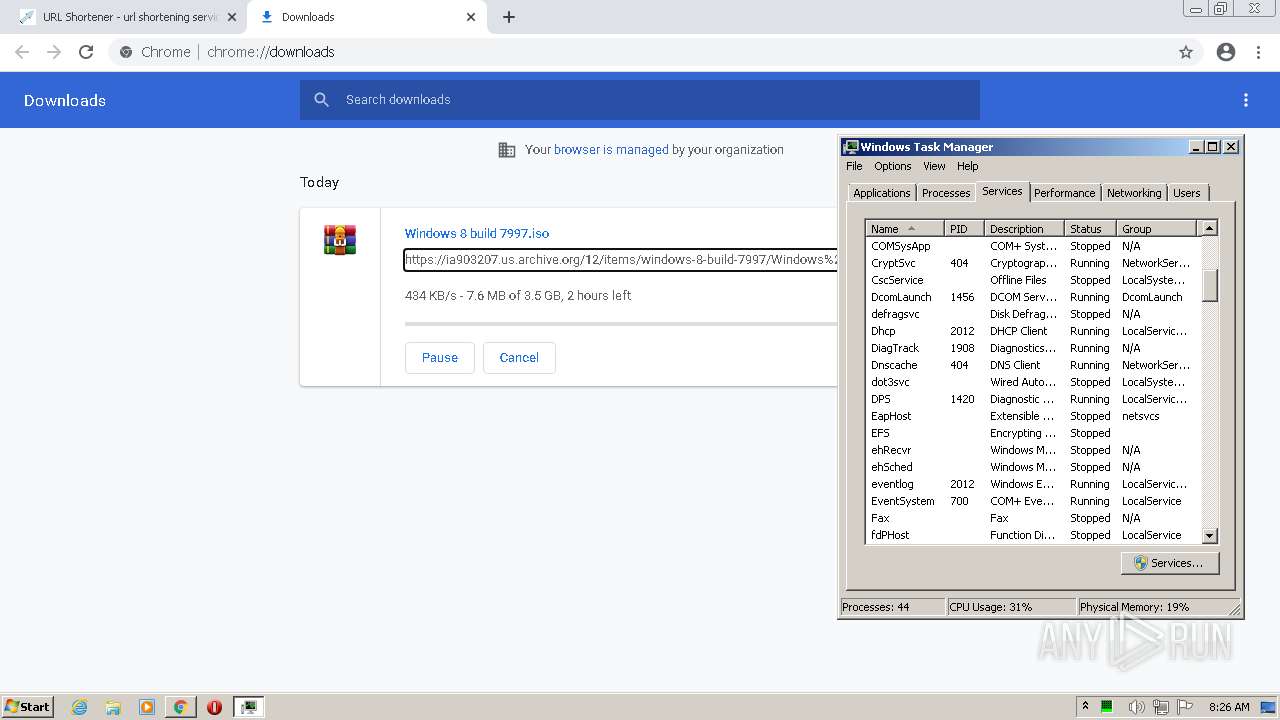
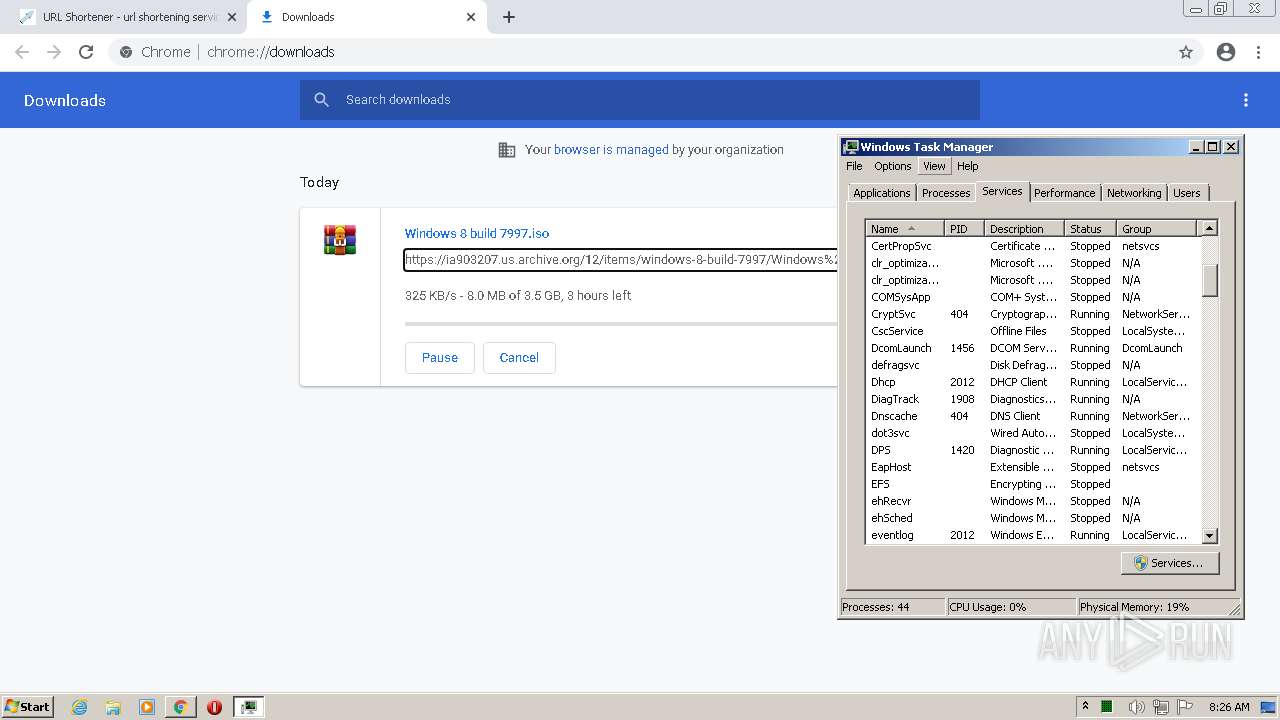
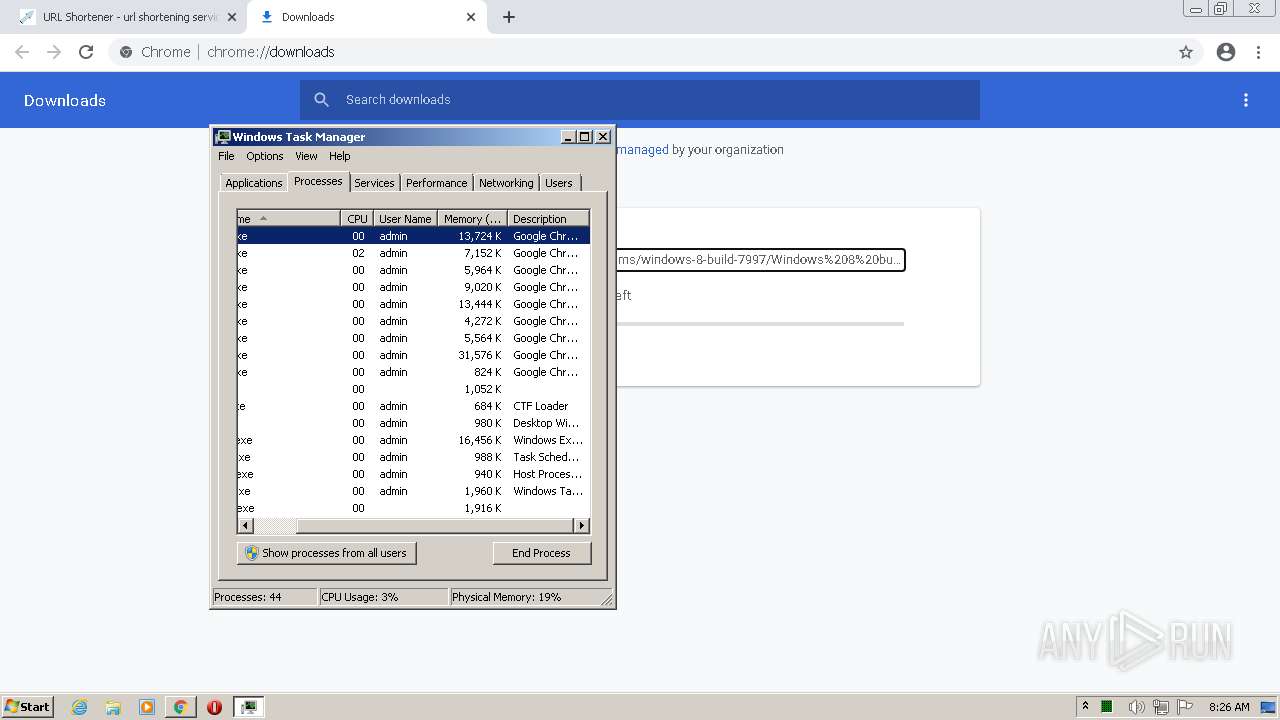
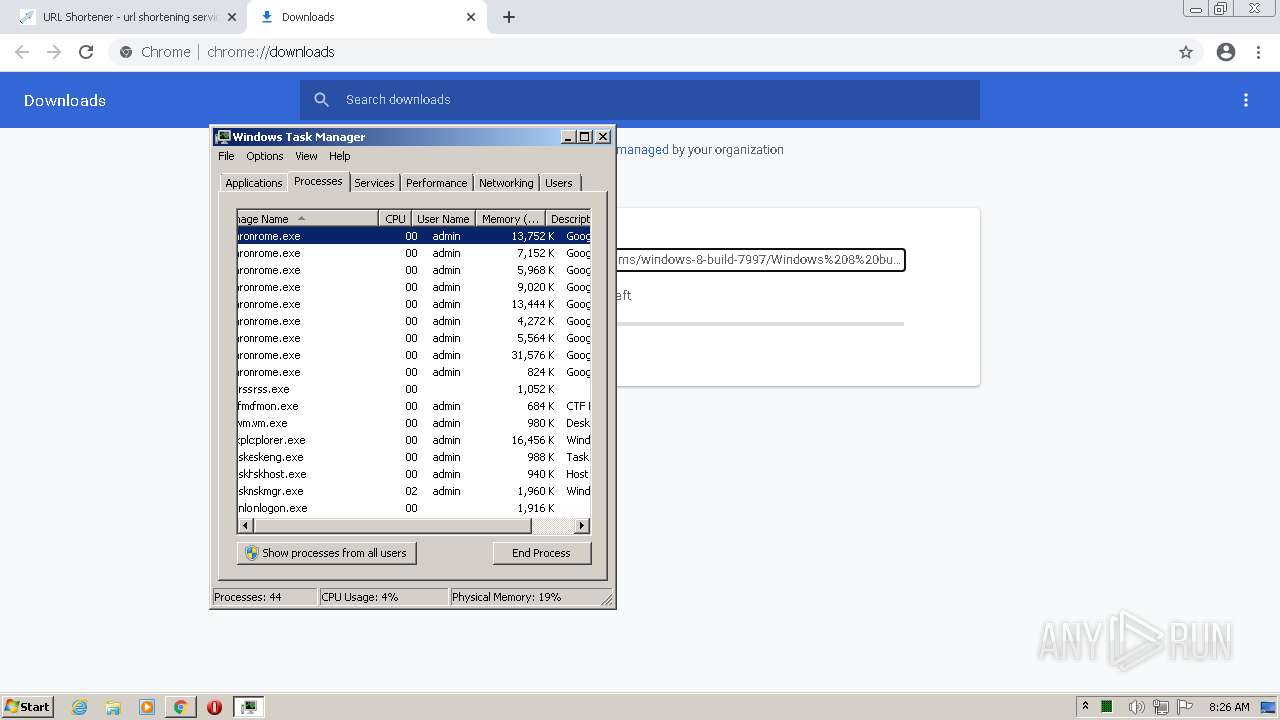
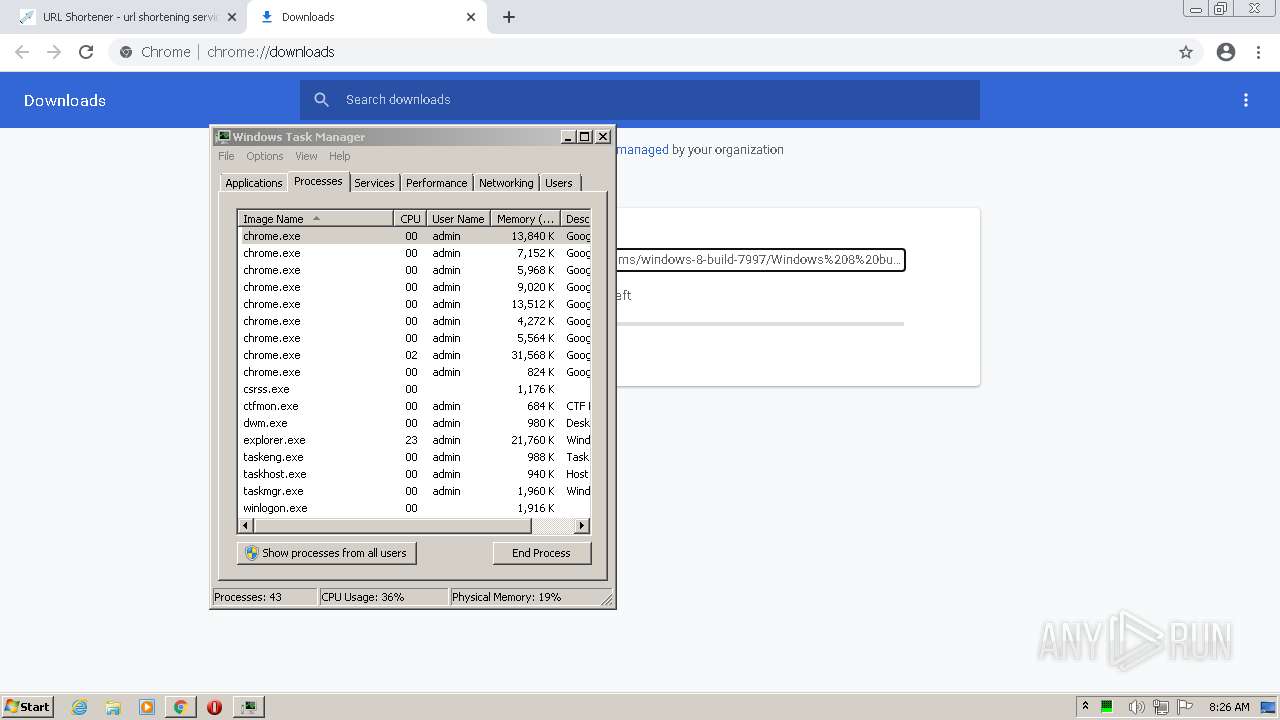
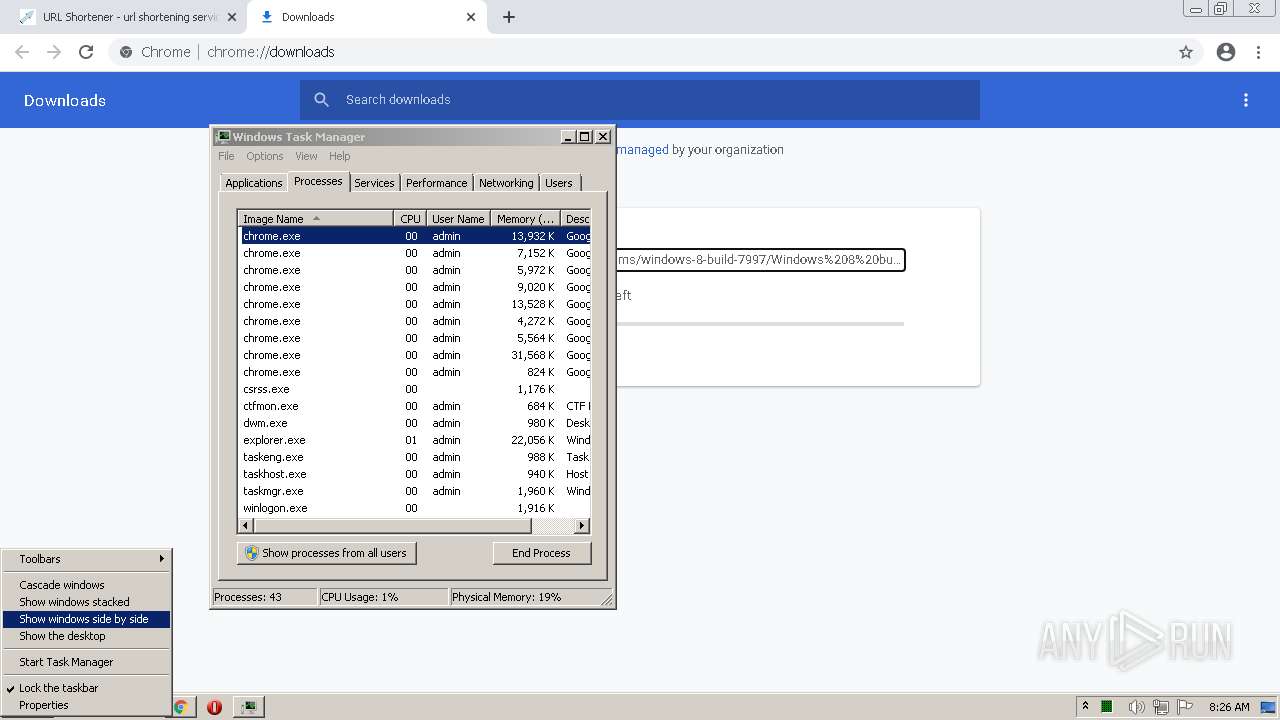
Total processes
147
Monitored processes
88
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,5453799367342131314,6893323941483002362,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1052 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 128 | "C:\Windows\system32\wininit.exe" | C:\Windows\system32\wininit.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Start-Up Application Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1020,5453799367342131314,6893323941483002362,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3528 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,5453799367342131314,6893323941483002362,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=63 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4756 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1020,5453799367342131314,6893323941483002362,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4352 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1020,5453799367342131314,6893323941483002362,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3176 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 520 | C:\Windows\system32\cmd.exe /d /c cmd /d /c cmd /d /c cmd /d /c cmd /d /c cmd /d /c start "" "C:\Program Files\InnocentKNOWLEDGEnyfUtil\InnocentxUtil.exe" 04928466973019 EJelGrM4UZ0/vN9qcSrOgGjFmjfVOIzwcugNykCYGhNIpQvIG52q1Rd11jRk7eg8GDuKaLY/eh7l2Wjb8Q6V1WmroP/pX+aOiHyq6Ox+T1EwZt0/BptPrfkt1MDODGGwR3dnKOOeCl56K4RvHAFgmvE1swe1l/8I/2KtmWLMMAUWdSa9HXmxMhq7UPAr39AYtTRuejSqW68v/1htNnUMvDGNlTyDHPRi/YyPSsDt5iE= | C:\Windows\system32\cmd.exe | — | Installer_2022.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1020,5453799367342131314,6893323941483002362,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4452 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1020,5453799367342131314,6893323941483002362,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4480 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1020,5453799367342131314,6893323941483002362,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3788 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
36 715
Read events
36 398
Write events
310
Delete events
7
Modification events
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
7
Suspicious files
98
Text files
217
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61F64B6B-E44.pma | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dcc71aed-3a2d-4db6-a62e-f473710570d6.tmp | text | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF12c7ad.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF12c78e.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\02ab0f47-3966-491a-ae5f-19ee353945c9.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
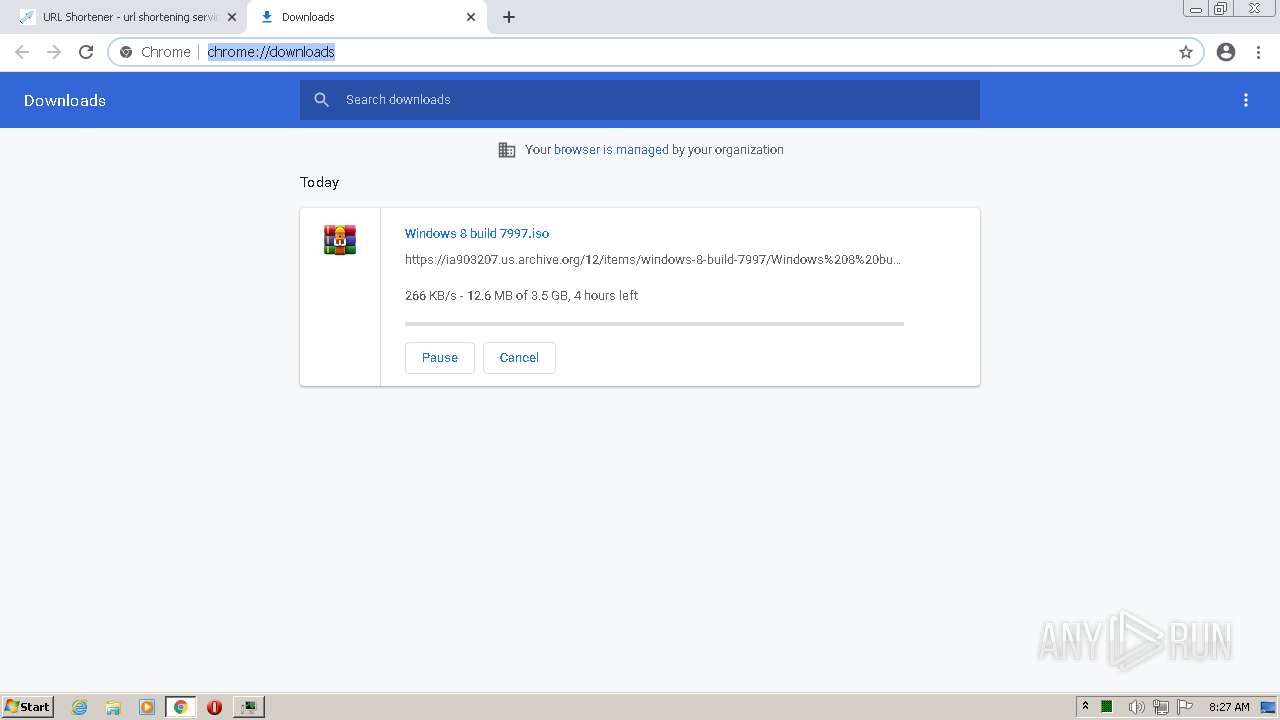
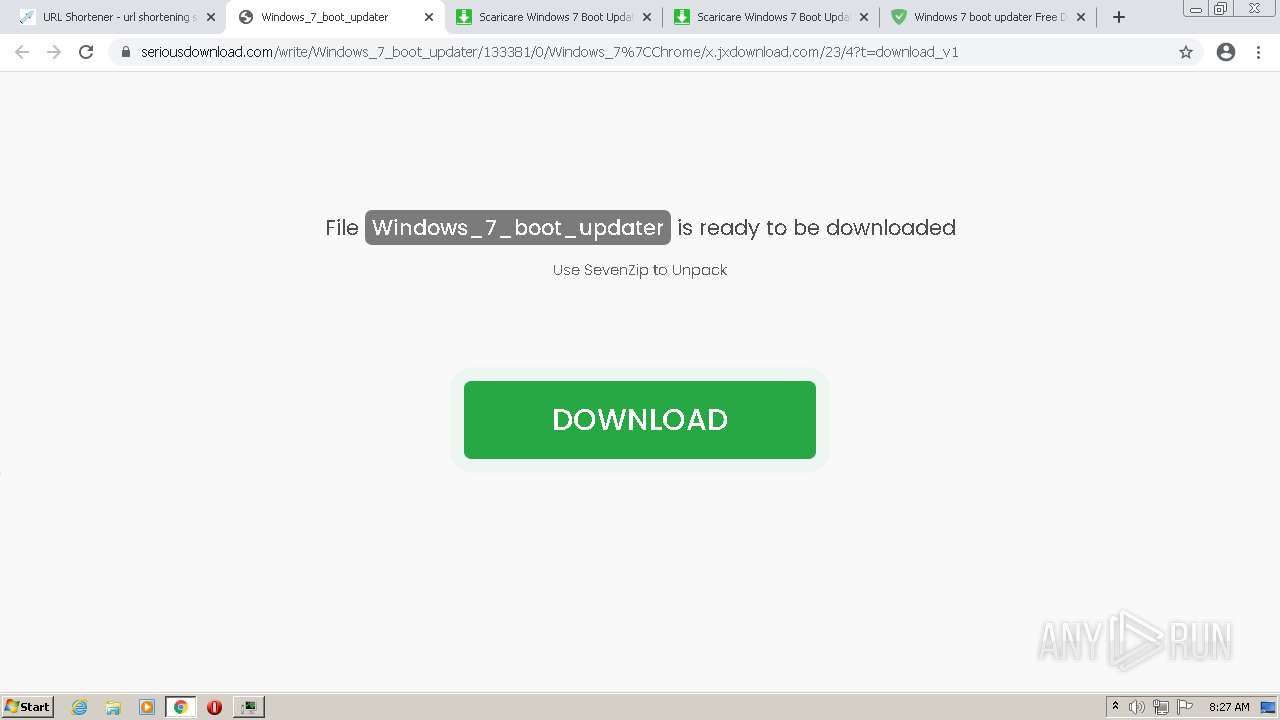
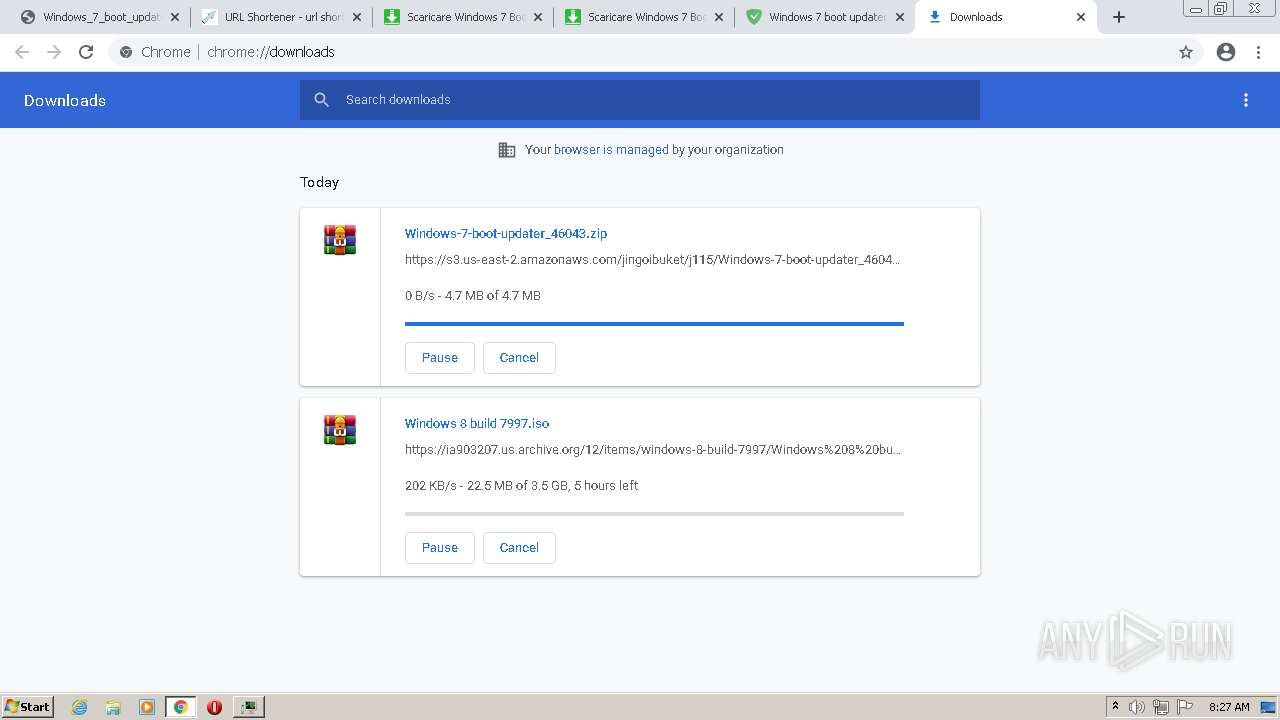
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
211
DNS requests
139
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
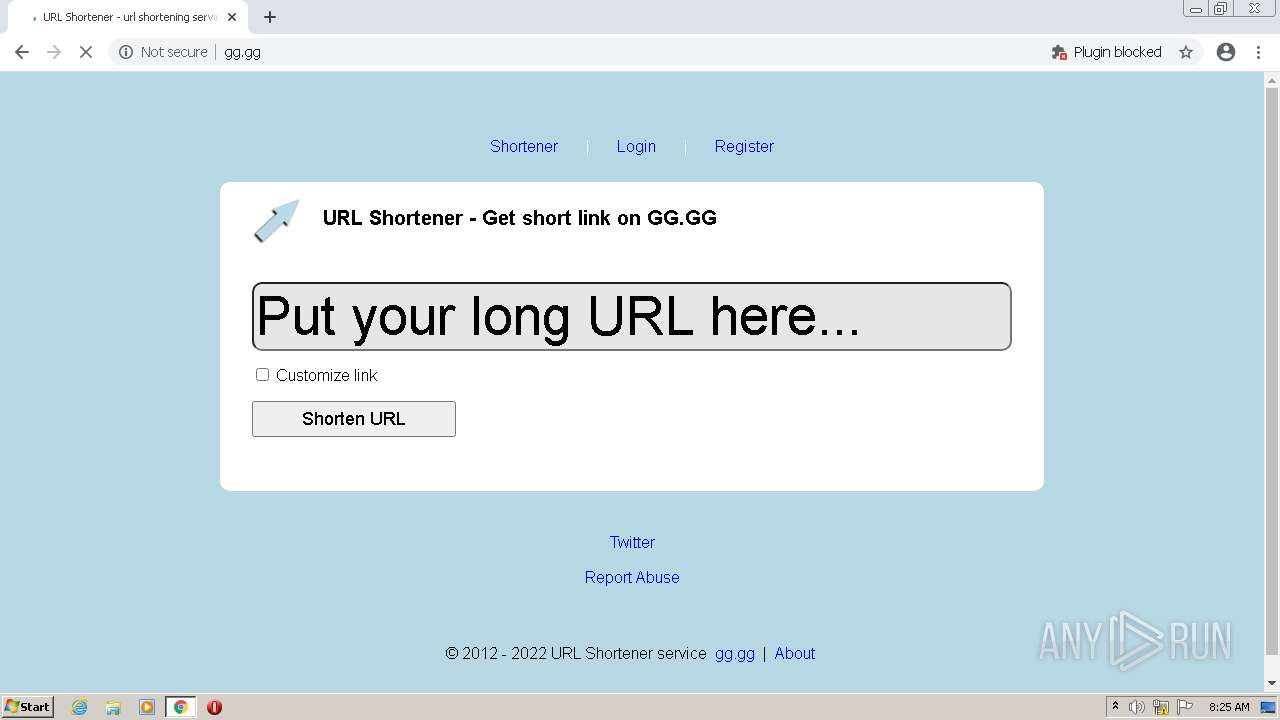
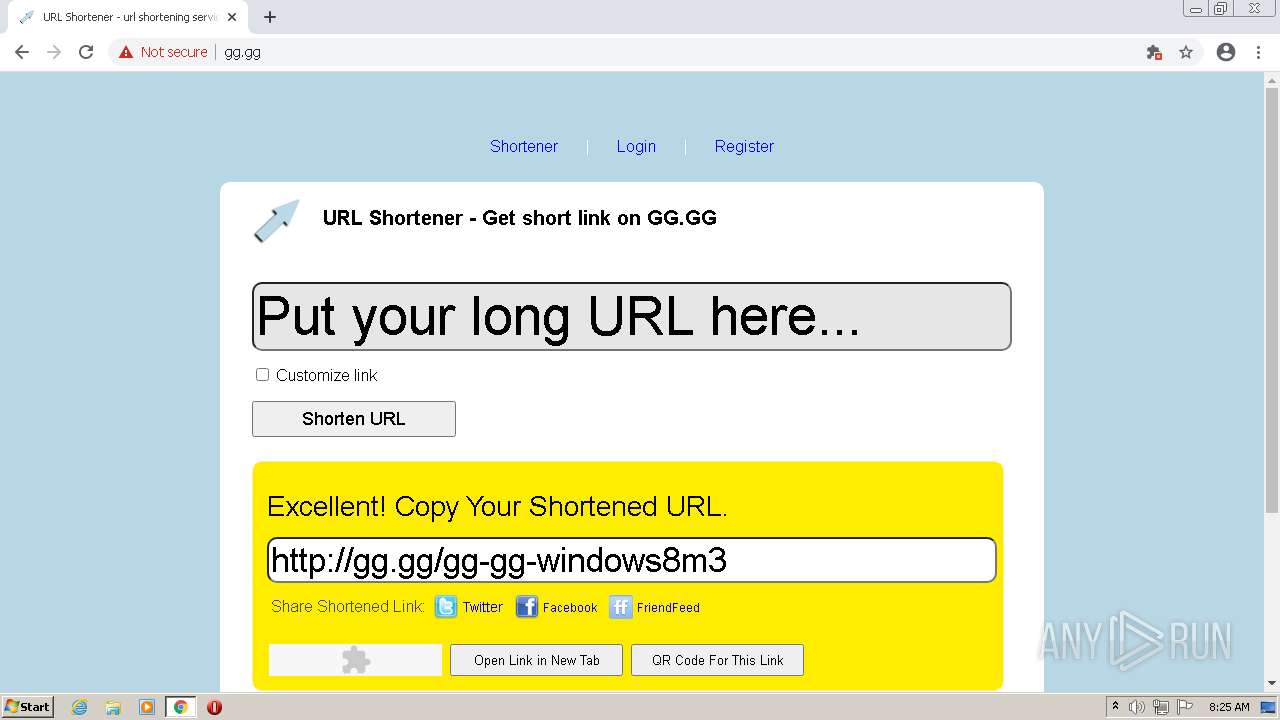
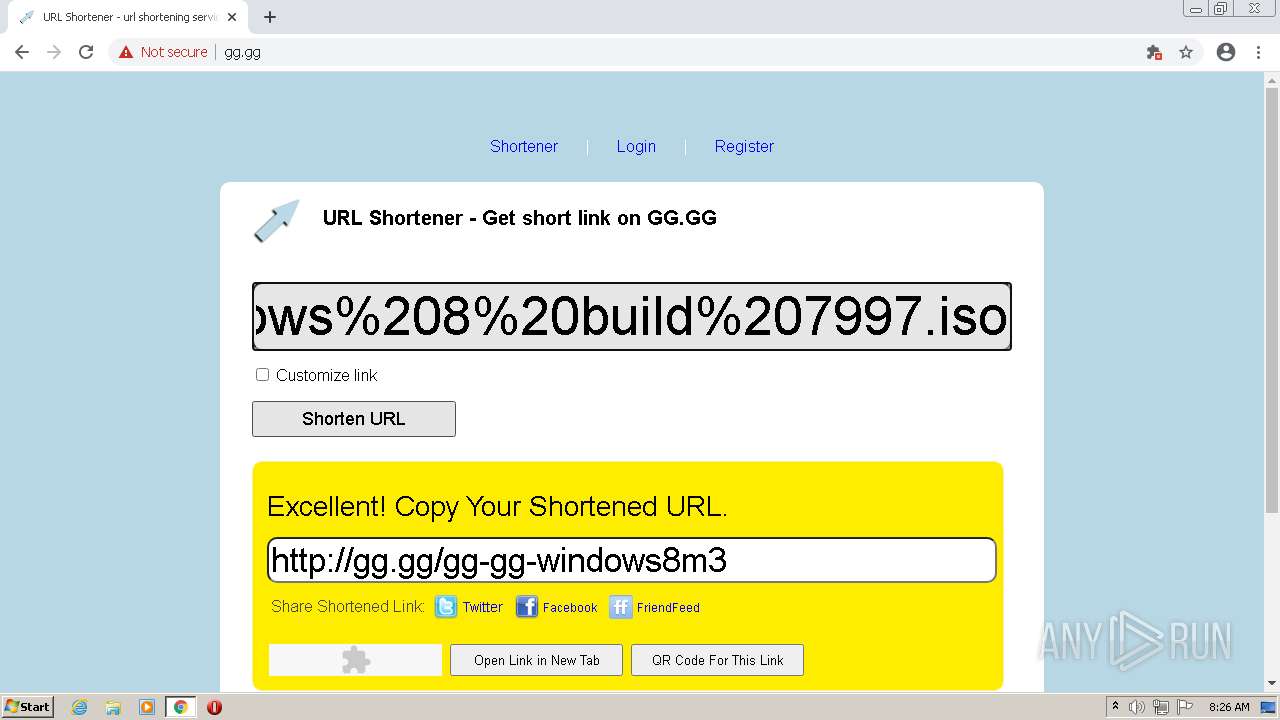
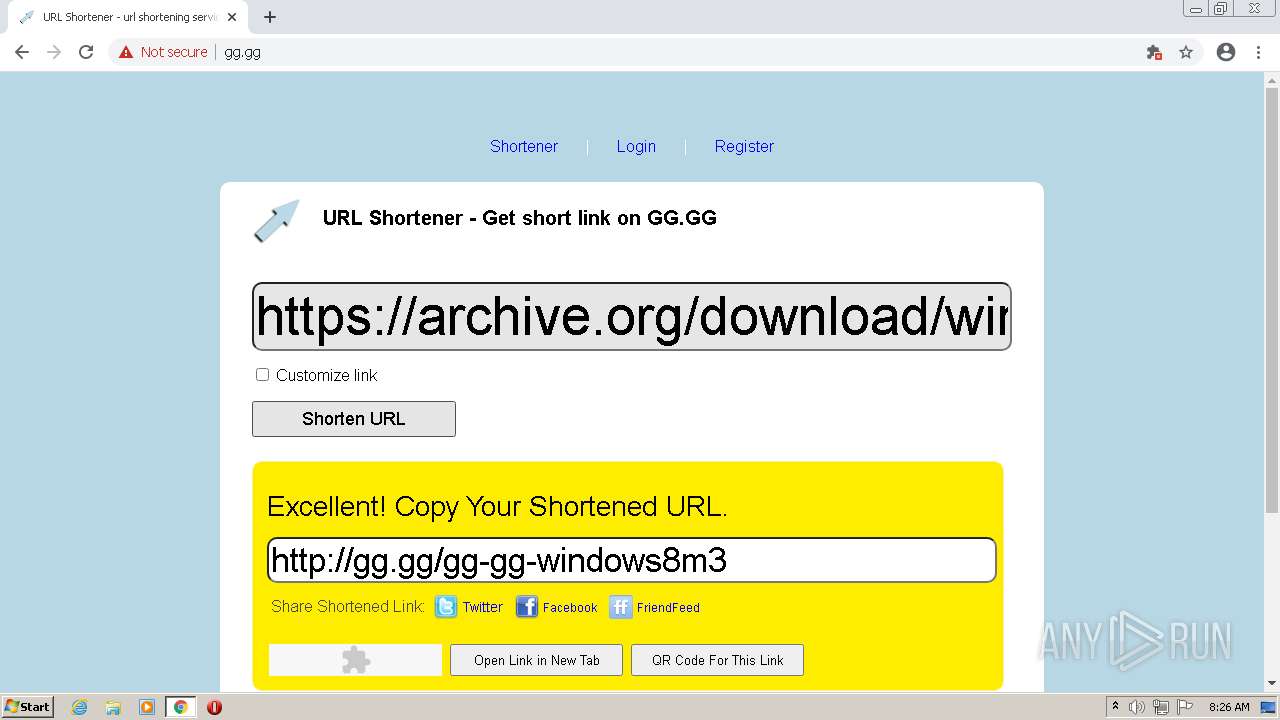
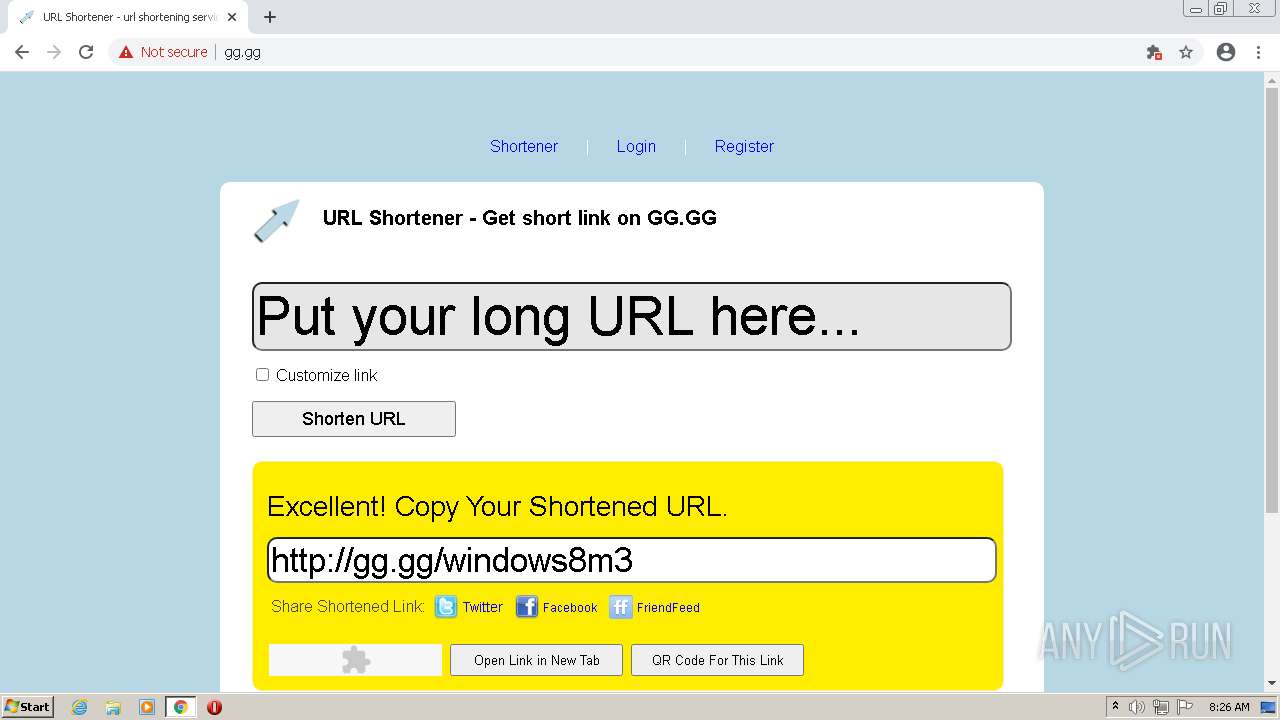
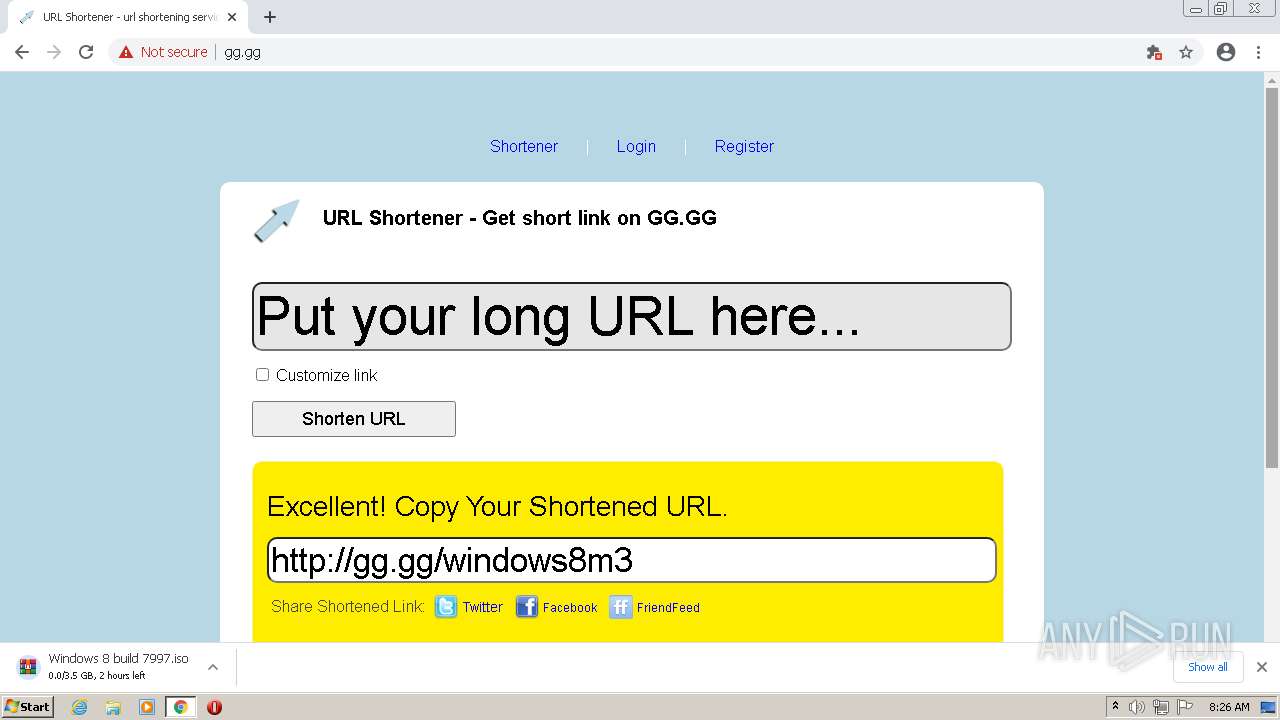
2272 | chrome.exe | GET | 200 | 185.15.209.141:80 | http://gg.gg/ | NL | html | 5.51 Kb | shared |
2272 | chrome.exe | GET | 200 | 185.15.209.141:80 | http://gg.gg/js/logic.js?v2 | NL | text | 5.93 Kb | shared |
2272 | chrome.exe | GET | 200 | 185.15.209.141:80 | http://gg.gg/js/jquery-1.7.2.min.js | NL | html | 92.6 Kb | shared |
2272 | chrome.exe | GET | 200 | 185.15.209.141:80 | http://gg.gg/images/tumblr.png | NL | image | 806 b | shared |
2272 | chrome.exe | GET | 200 | 185.15.209.141:80 | http://gg.gg/js/jquery-ui-1.8.21.custom.min.js | NL | text | 202 Kb | shared |
2272 | chrome.exe | GET | 200 | 185.15.209.141:80 | http://gg.gg/images/friendfeed.png | NL | image | 878 b | shared |
2272 | chrome.exe | GET | 200 | 104.20.229.67:80 | http://www.statcounter.com/counter/counter.js | US | text | 14.7 Kb | whitelisted |
2272 | chrome.exe | GET | 200 | 185.15.209.141:80 | http://gg.gg/images/facebook.png | NL | image | 1.12 Kb | shared |
2272 | chrome.exe | GET | 200 | 185.15.209.141:80 | http://gg.gg/js/jquery.corners.min.js | NL | text | 9.83 Kb | shared |
2272 | chrome.exe | GET | 200 | 185.15.209.141:80 | http://gg.gg/images/logo.png | NL | image | 7.93 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2272 | chrome.exe | 142.250.186.74:443 | — | Google Inc. | US | whitelisted |
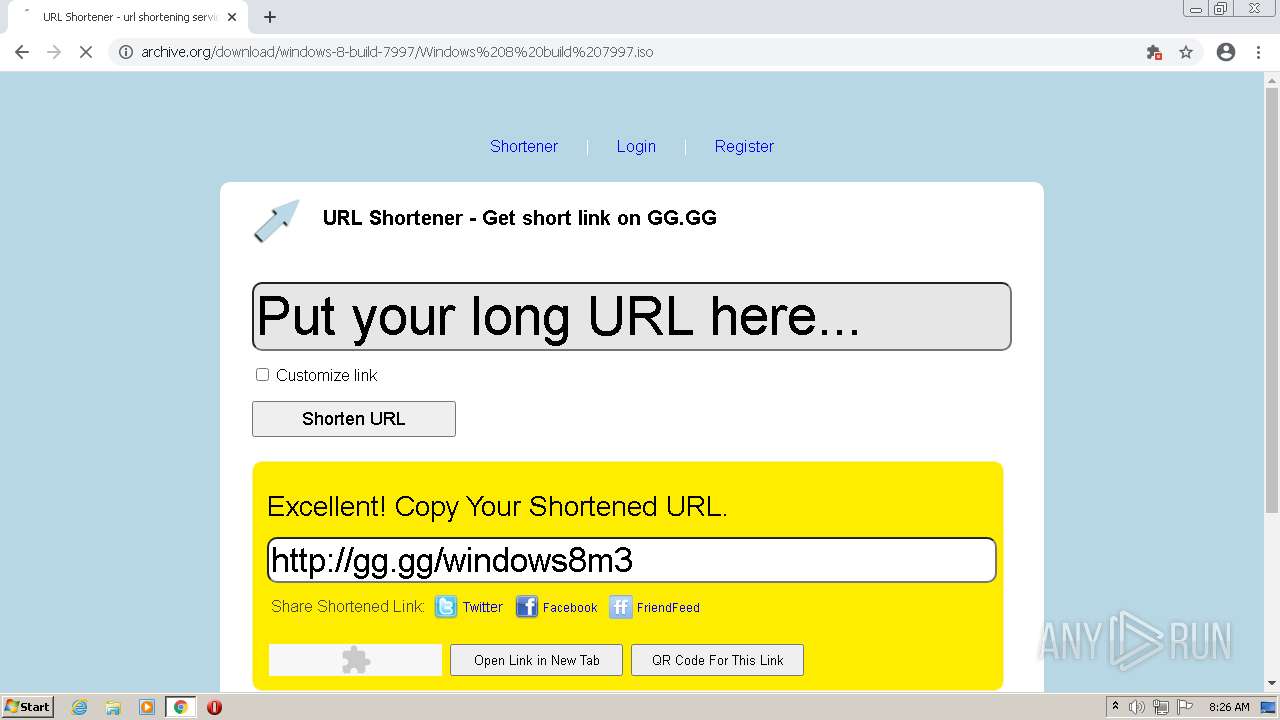
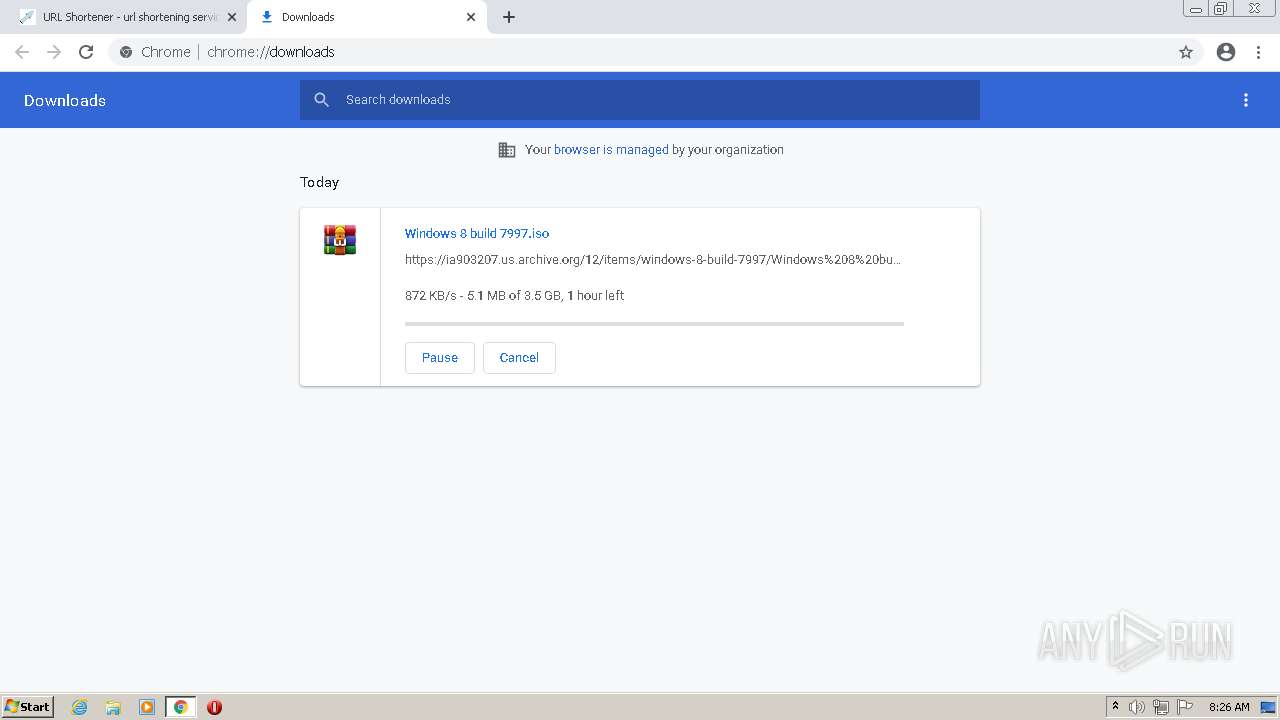
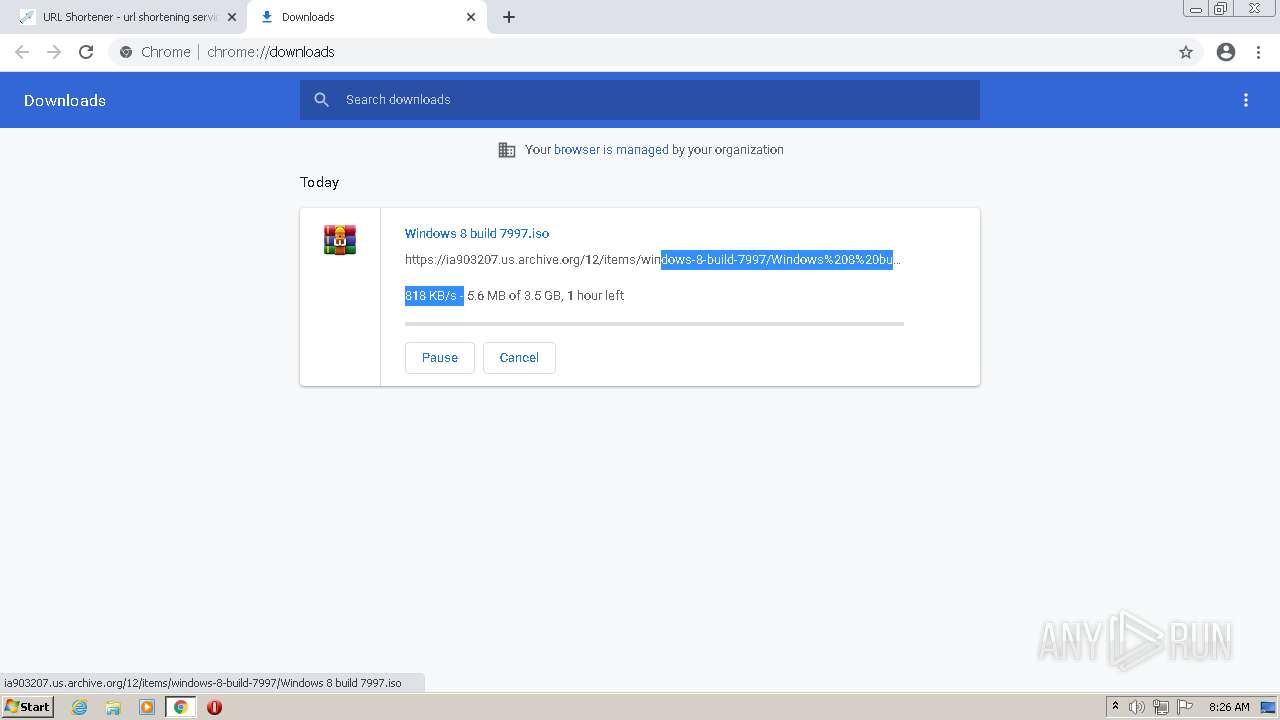
2272 | chrome.exe | 207.241.224.2:443 | archive.org | Internet Archive | US | malicious |
2272 | chrome.exe | 172.217.16.142:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
2272 | chrome.exe | 185.15.209.141:80 | gg.gg | Innovation IT Solutions LTD | NL | suspicious |
2272 | chrome.exe | 104.20.229.67:80 | www.statcounter.com | Cloudflare Inc | US | unknown |
2272 | chrome.exe | 172.217.18.99:443 | update.googleapis.com | Google Inc. | US | whitelisted |
2272 | chrome.exe | 172.217.18.110:443 | apis.google.com | Google Inc. | US | whitelisted |
2272 | chrome.exe | 104.20.228.67:443 | www.statcounter.com | Cloudflare Inc | US | unknown |
2272 | chrome.exe | 207.241.225.102:443 | analytics.archive.org | Internet Archive | US | suspicious |
2272 | chrome.exe | 142.250.186.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
archive.org |
| whitelisted |
polyfill.archive.org |
| suspicious |
analytics.archive.org |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
ia803207.us.archive.org |
| unknown |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
encrypted-tbn0.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY GG Url Shortener Observed in DNS Query |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |