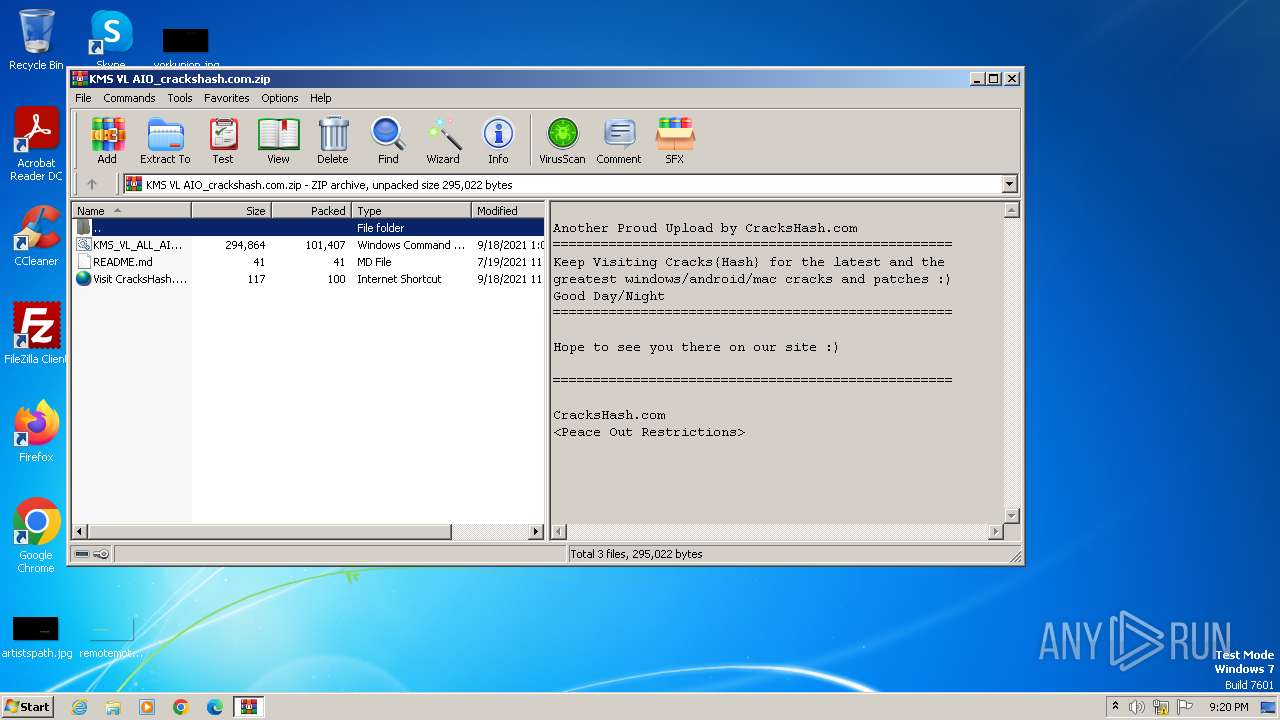
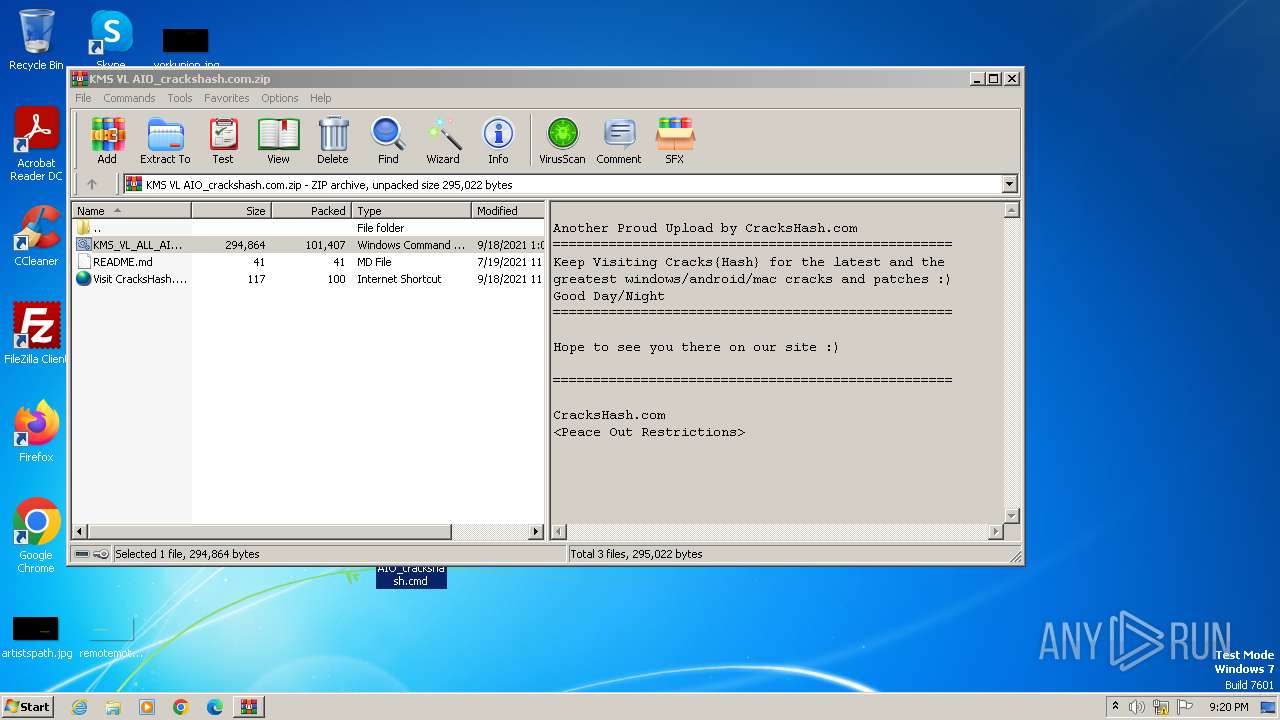
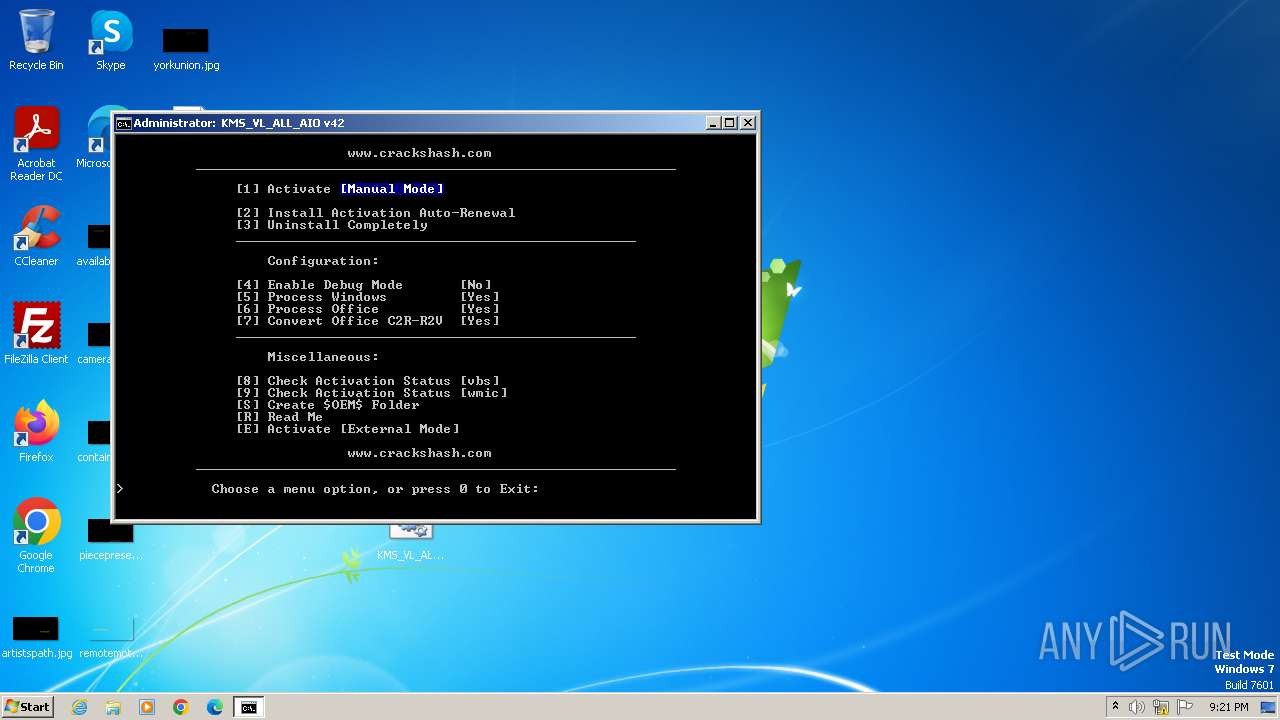
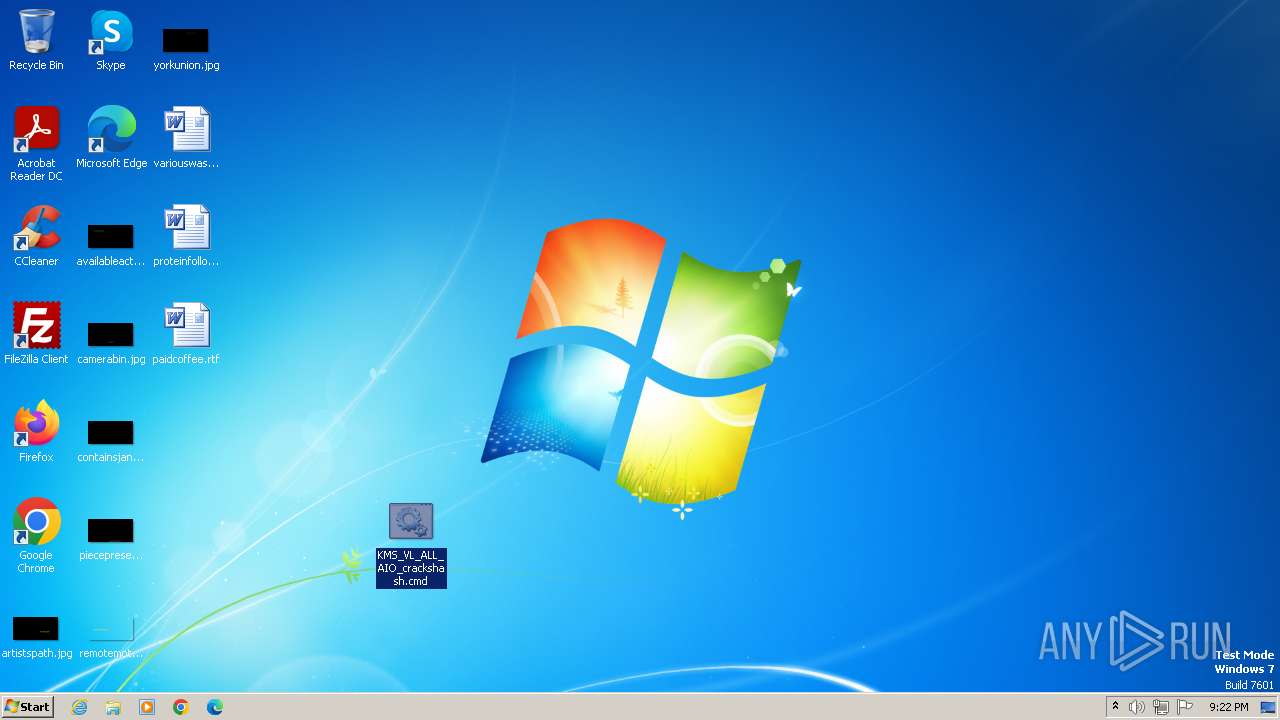
| File name: | KMS VL AIO_crackshash.com.zip |
| Full analysis: | https://app.any.run/tasks/69f0764c-67ae-46e9-b873-4992cb9b60cd |
| Verdict: | Malicious activity |
| Analysis date: | December 04, 2023, 21:20:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | F6262C57883DEE2CEEC3B35DAD35BE10 |
| SHA1: | 8002C075EE443560E7D07DB8D52E5BD961675C21 |
| SHA256: | DF606555E3DC7ADA4ABB747AA413D29CAC4048F5DB778EEE92BE5E81BDB6F4C5 |
| SSDEEP: | 3072:QhWYsvjoFMRLgyGxPLgRKF3er4C4fIXGA:QhWYcoMRLsxL3eZNGA |
MALICIOUS
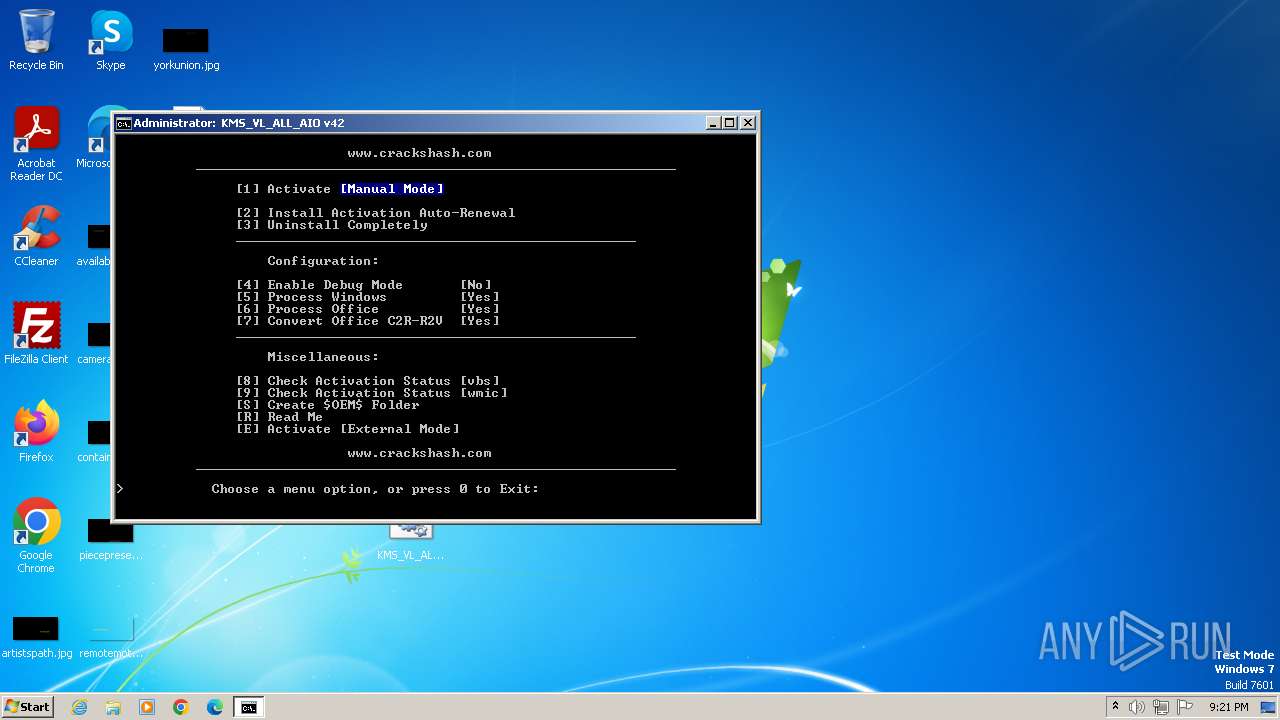
Starts Visual C# compiler
- powershell.exe (PID: 1344)
Creates a writable file in the system directory
- powershell.exe (PID: 1344)
Drops the executable file immediately after the start
- powershell.exe (PID: 1344)
- csc.exe (PID: 3144)
Starts NET.EXE for service management
- cmd.exe (PID: 3940)
- net.exe (PID: 1900)
- net.exe (PID: 788)
- net.exe (PID: 3980)
SUSPICIOUS
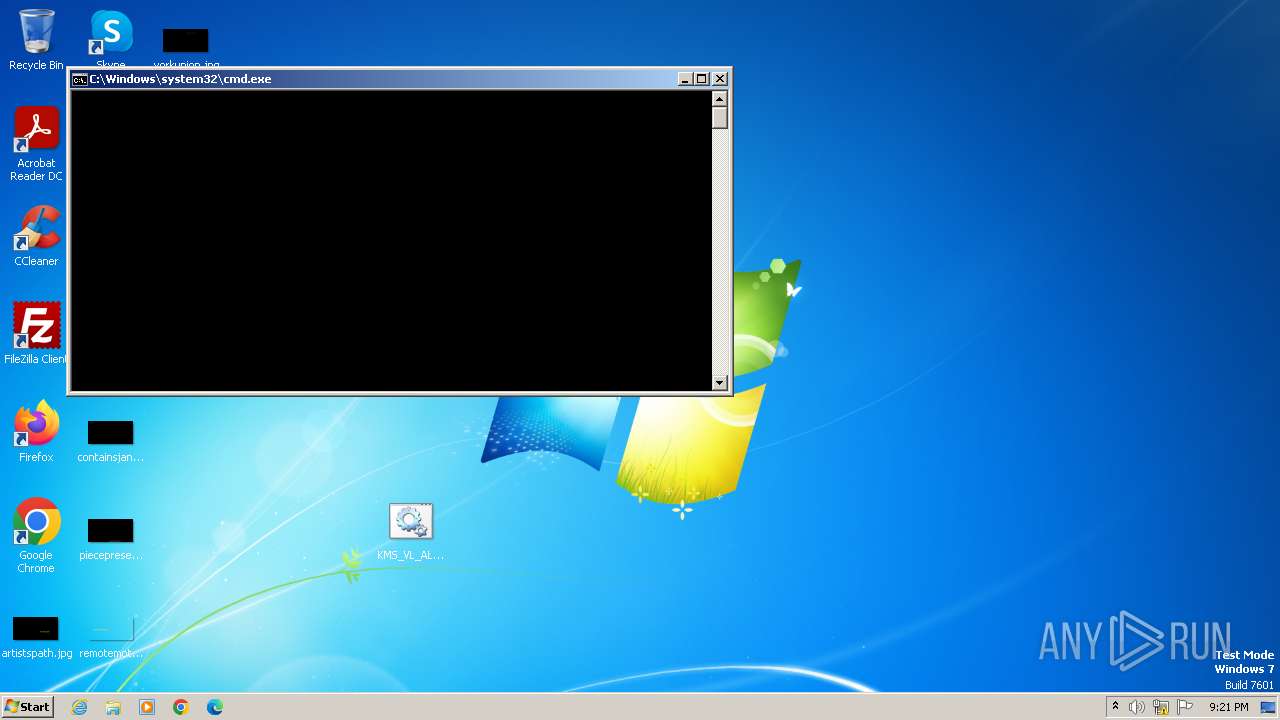
Starts CMD.EXE for commands execution
- cscript.exe (PID: 280)
- cmd.exe (PID: 3940)
Runs shell command (SCRIPT)
- cscript.exe (PID: 280)
Uses RUNDLL32.EXE to load library
- cscript.exe (PID: 280)
Reads the Internet Settings
- cmd.exe (PID: 3940)
- cscript.exe (PID: 280)
- WMIC.exe (PID: 2500)
- WMIC.exe (PID: 120)
- WMIC.exe (PID: 2392)
- WMIC.exe (PID: 3832)
- WMIC.exe (PID: 2052)
- WMIC.exe (PID: 2348)
- WMIC.exe (PID: 3584)
- WMIC.exe (PID: 2924)
- WMIC.exe (PID: 2784)
- WMIC.exe (PID: 4068)
- WMIC.exe (PID: 3192)
Executing commands from ".cmd" file
- cscript.exe (PID: 280)
Application launched itself
- cmd.exe (PID: 3940)
Starts SC.EXE for service management
- cmd.exe (PID: 3940)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3940)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 3940)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 3940)
Powershell version downgrade attack
- powershell.exe (PID: 3720)
- powershell.exe (PID: 1344)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 3940)
Uses .NET C# to load dll
- powershell.exe (PID: 1344)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3940)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3940)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 296)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 2652)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 3216)
INFO
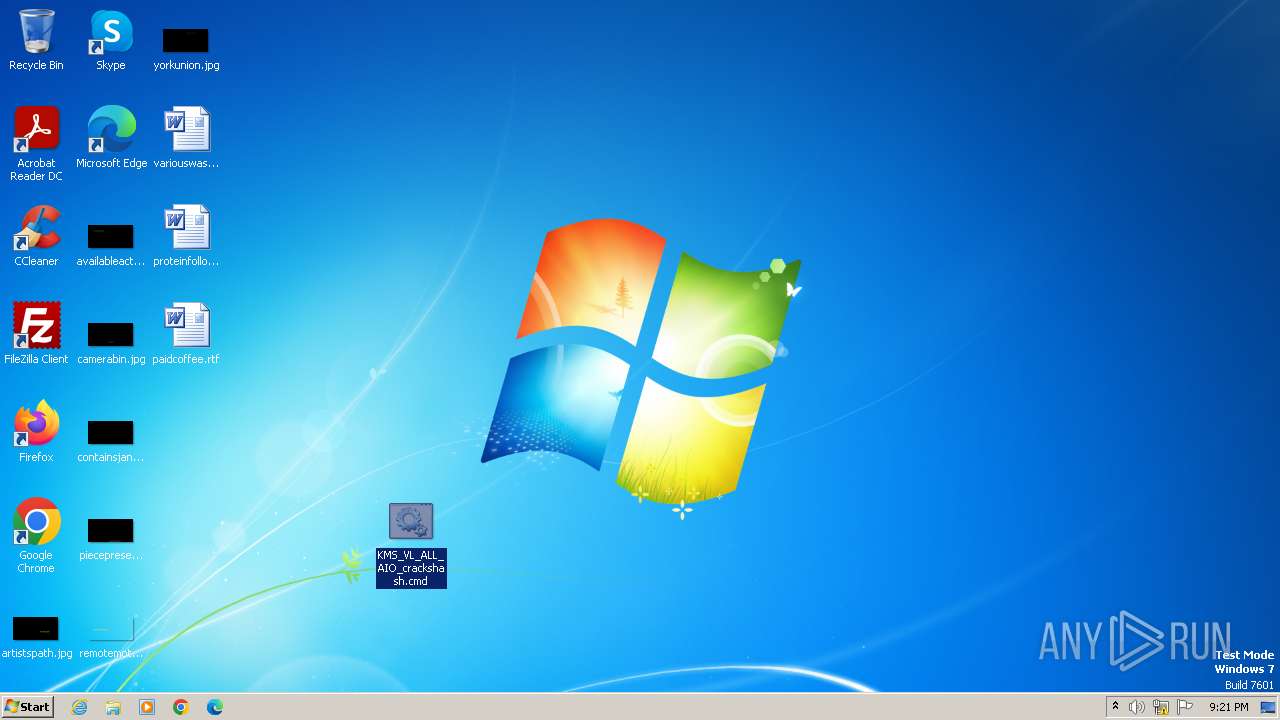
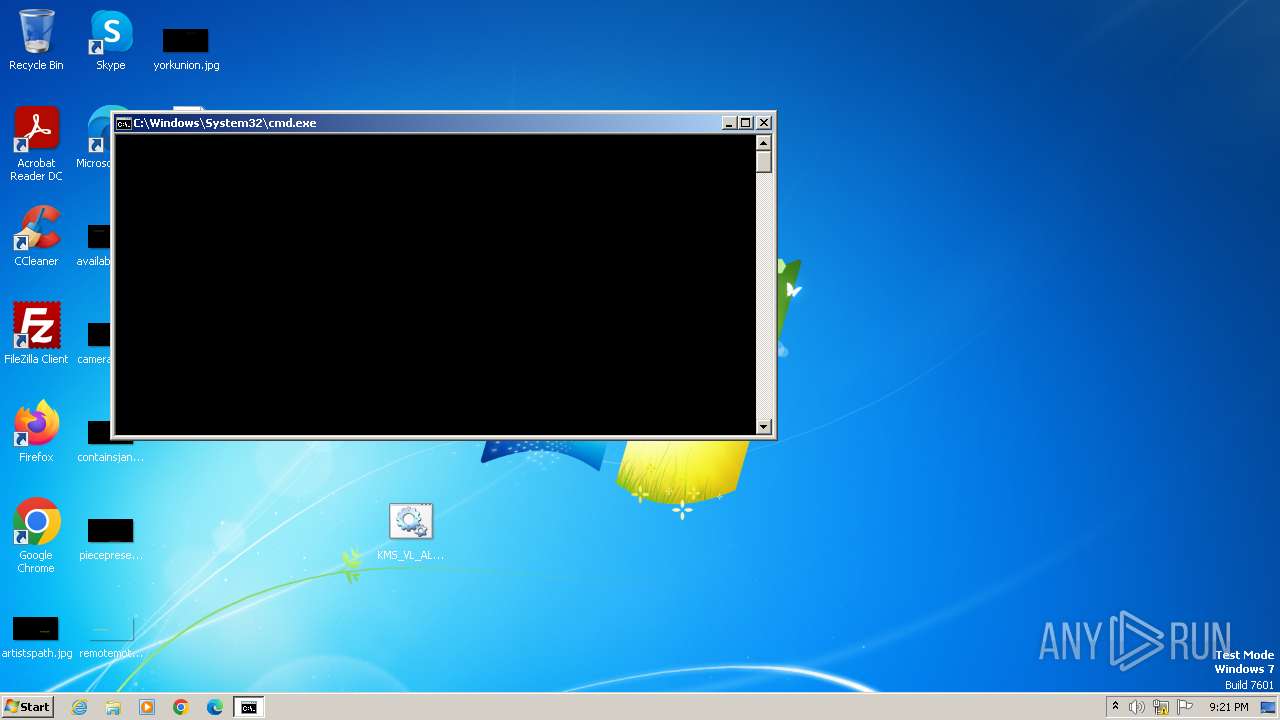
Manual execution by a user
- cmd.exe (PID: 1640)
- msedge.exe (PID: 3492)
- wmpnscfg.exe (PID: 860)
Reads security settings of Internet Explorer
- cscript.exe (PID: 280)
Application launched itself
- msedge.exe (PID: 2764)
- msedge.exe (PID: 3492)
Checks operating system version
- cmd.exe (PID: 3940)
Checks supported languages
- mode.com (PID: 3296)
- wmpnscfg.exe (PID: 860)
- csc.exe (PID: 3144)
- cvtres.exe (PID: 2540)
- mode.com (PID: 2728)
Reads the computer name
- wmpnscfg.exe (PID: 860)
Create files in a temporary directory
- cvtres.exe (PID: 2540)
- csc.exe (PID: 3144)
Reads the machine GUID from the registry
- csc.exe (PID: 3144)
- cvtres.exe (PID: 2540)
Reads Microsoft Office registry keys
- reg.exe (PID: 4044)
- reg.exe (PID: 3108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2021:07:19 15:00:54 |
| ZipCRC: | 0xdb5930a7 |
| ZipCompressedSize: | 41 |
| ZipUncompressedSize: | 41 |
| ZipFileName: | README.md |
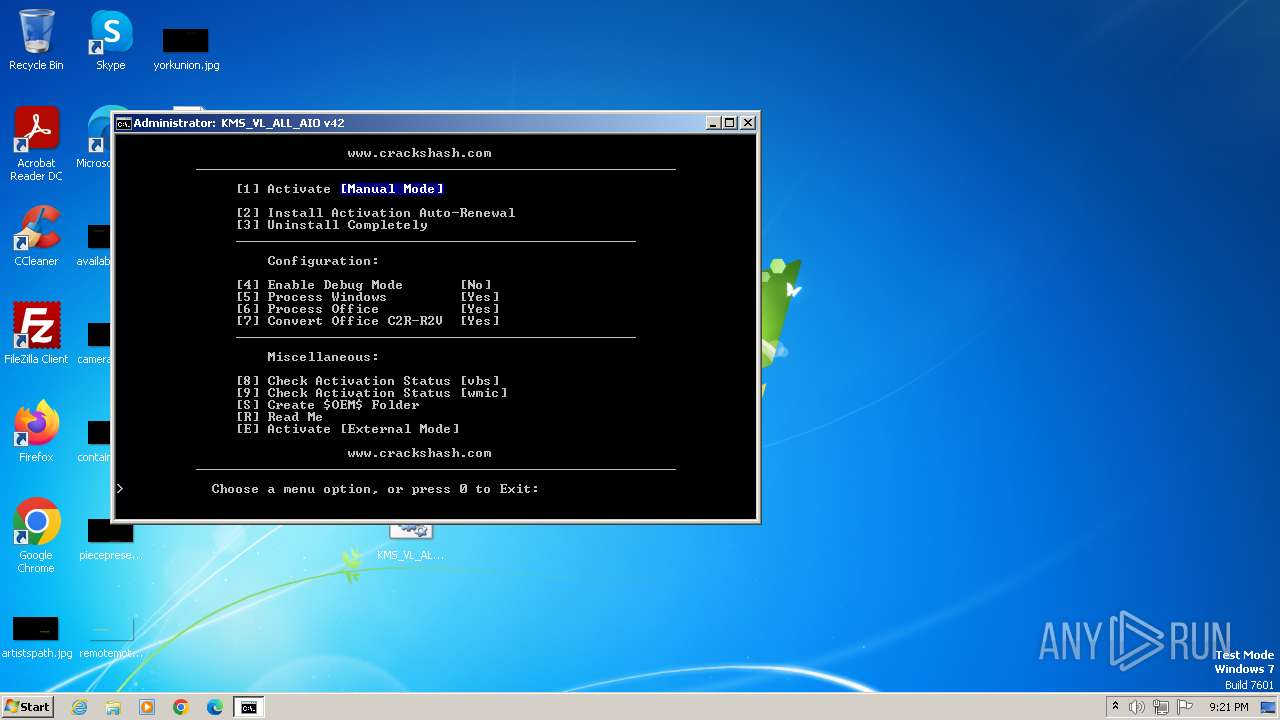
Total processes
217
Monitored processes
171
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | wmic path SoftwareLicensingProduct where (PartialProductKey is not NULL) get ID /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 124 | reg delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe" /v VerifierFlags /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 240 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6a54f598,0x6a54f5a8,0x6a54f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 240 | reg query HKLM\SOFTWARE\Wow6432Node\Microsoft\Office\16.0\Common\InstallRoot /v Path | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 280 | cscript //NoLogo "C:\Users\admin\Desktop\KMS_VL_ALL_AIO_crackshash.cmd?.wsf" //job:ELAV /File:"C:\Users\admin\Desktop\KMS_VL_ALL_AIO_crackshash.cmd" -elevated | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 280 | reg delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe" /v GlobalFlag /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 296 | C:\Windows\system32\cmd.exe /c "wmic path SoftwareLicensingService get Version /VALUE" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 564 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\KMS VL AIO_crackshash.com.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 752 | reg delete "HKLM\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform\0ff1ce15-a989-479d-af46-f275c6370663" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 788 | net stop sppsvc /y | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 108
Read events
7 929
Write events
172
Delete events
7
Modification events
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
2
Suspicious files
77
Text files
48
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4000 | msedge.exe | — | ||
MD5:— | SHA256:— | |||
| 3492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF20a879.TMP | — | |
MD5:— | SHA256:— | |||
| 3492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF20a898.TMP | — | |
MD5:— | SHA256:— | |||
| 3492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF20a8a8.TMP | — | |
MD5:— | SHA256:— | |||
| 3940 | cmd.exe | C:\Windows\Temp\' | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:A9B940DA81B2E13D048EBB32E79FA414 | SHA256:9061129705411EA6CFDD34177BF841CC85EB857BA909D3C4AA69BE8A5C59A8B0 | |||
| 3492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF20a8d7.TMP | — | |
MD5:— | SHA256:— | |||
| 3492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
29
DNS requests
32
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3380 | msedge.exe | 20.105.95.163:443 | nav-edge.smartscreen.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3492 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3380 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
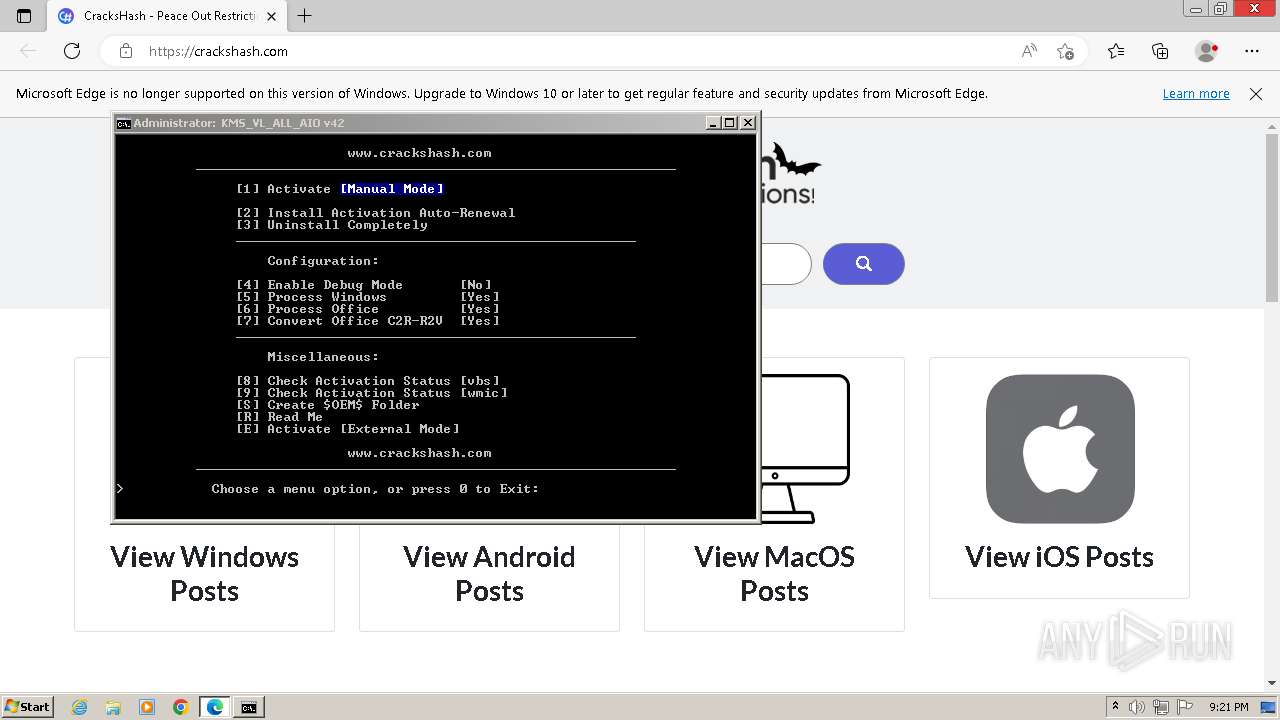
3380 | msedge.exe | 104.21.0.236:443 | www.crackshash.com | CLOUDFLARENET | — | unknown |
3380 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3380 | msedge.exe | 51.104.176.40:443 | data-edge.smartscreen.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
www.crackshash.com |
| unknown |
nav-edge.smartscreen.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
crackshash.com |
| malicious |
data-edge.smartscreen.microsoft.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|