| download: | release-iceland-s-banned-christmas-advert-on-tv-nopalmoilchristmas |
| Full analysis: | https://app.any.run/tasks/b3417153-61f8-4815-83ff-d1d9458bc200 |
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2018, 12:46:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | 95C377E88D02E4E40941E9DDDB02942C |
| SHA1: | 4EE91B9685738217853FDA2AEA9543E36ACFBD0E |
| SHA256: | DF5E0DA7B7425A9D112AA947A77C006D5579E3F0A84CD9606D2F4CEBDCA701D9 |
| SSDEEP: | 3072:rQ8aNVnMht38P08qt5hvCVvfFohPt4M6nm8P08qt4uELp/NuuT:s8Xuv58w |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
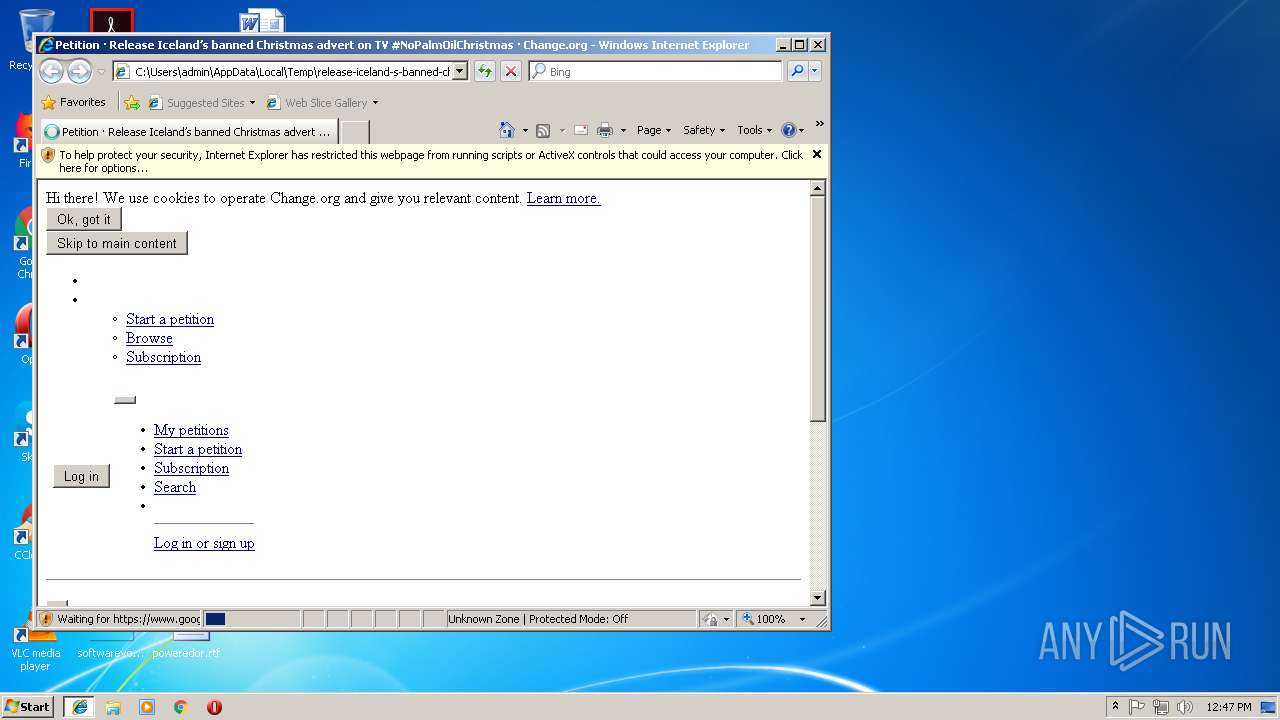
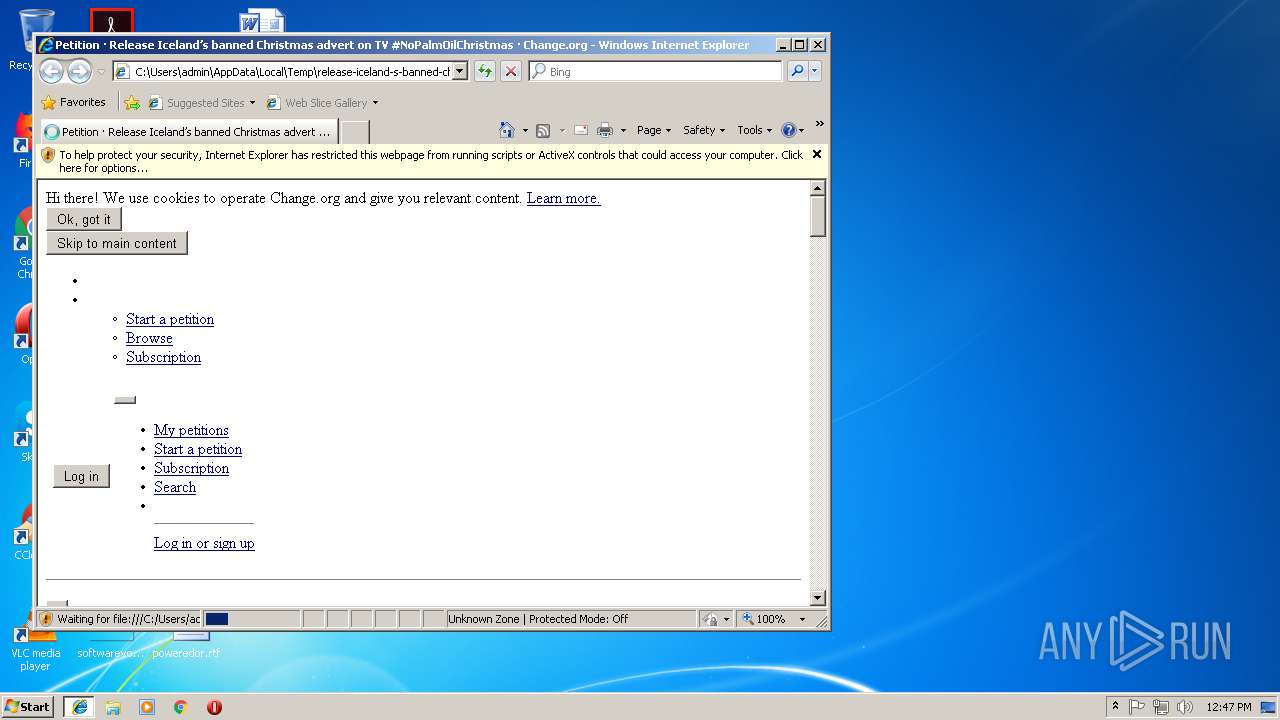
Changes internet zones settings
- iexplore.exe (PID: 920)
Reads internet explorer settings
- iexplore.exe (PID: 1548)
Changes settings of System certificates
- iexplore.exe (PID: 1548)
Creates files in the user directory
- iexplore.exe (PID: 1548)
Reads settings of System Certificates
- iexplore.exe (PID: 1548)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1548)
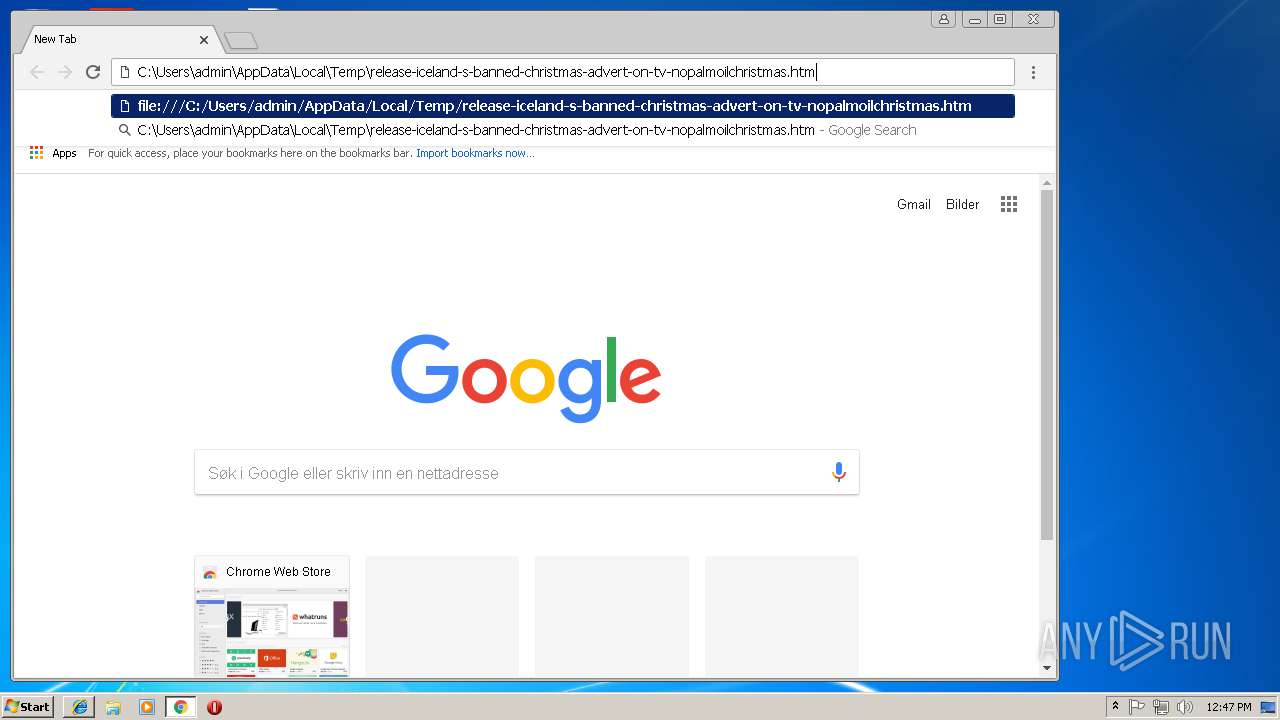
Application launched itself
- chrome.exe (PID: 676)
Reads Internet Cache Settings
- chrome.exe (PID: 676)
- iexplore.exe (PID: 1548)
Reads Microsoft Office registry keys
- chrome.exe (PID: 676)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
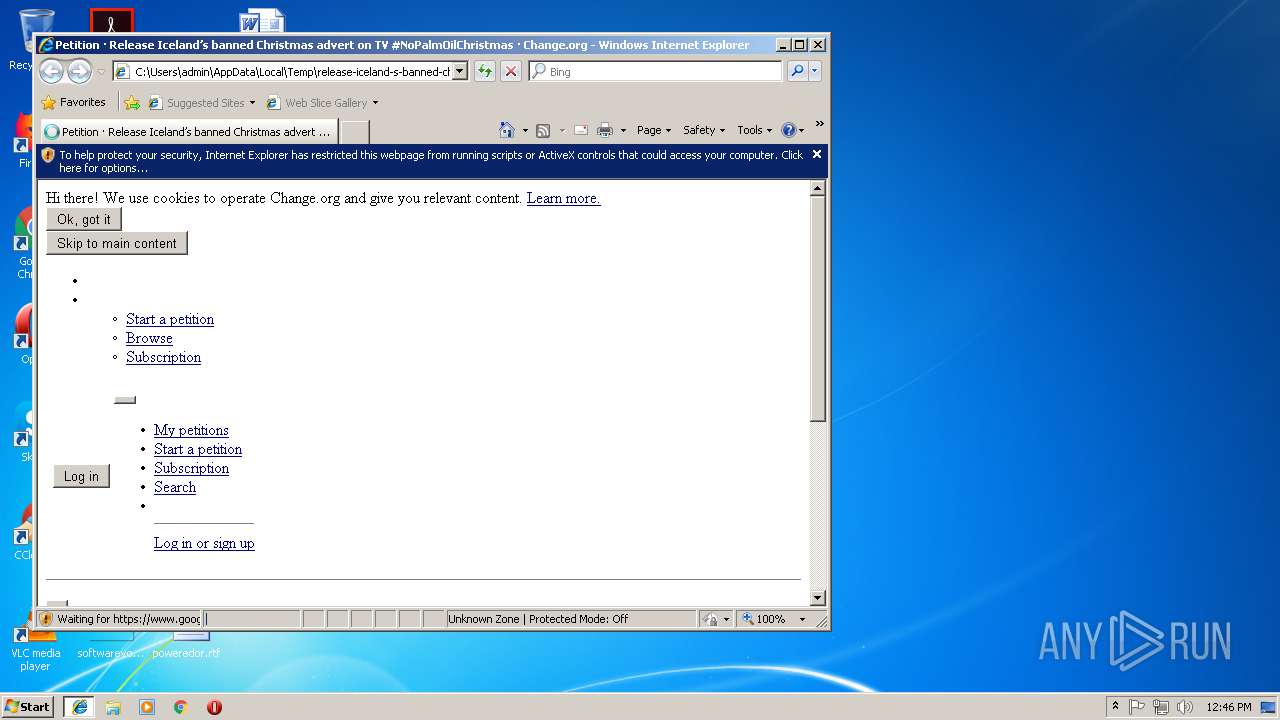
| ContentLanguage: | en-GB |
|---|---|
| viewport: | width=device-width, initial-scale=1 |
| twitterSite: | @change |
| twitterCreator: | @change |
| twitterCard: | summary_large_image |
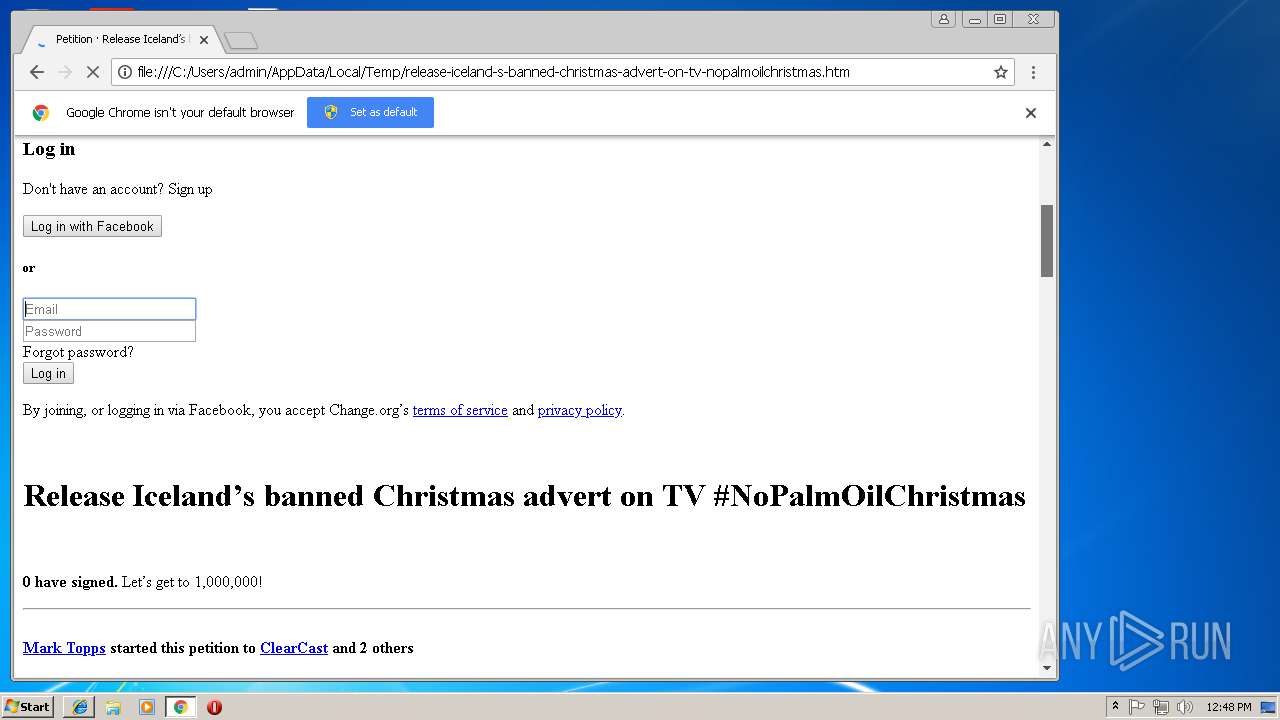
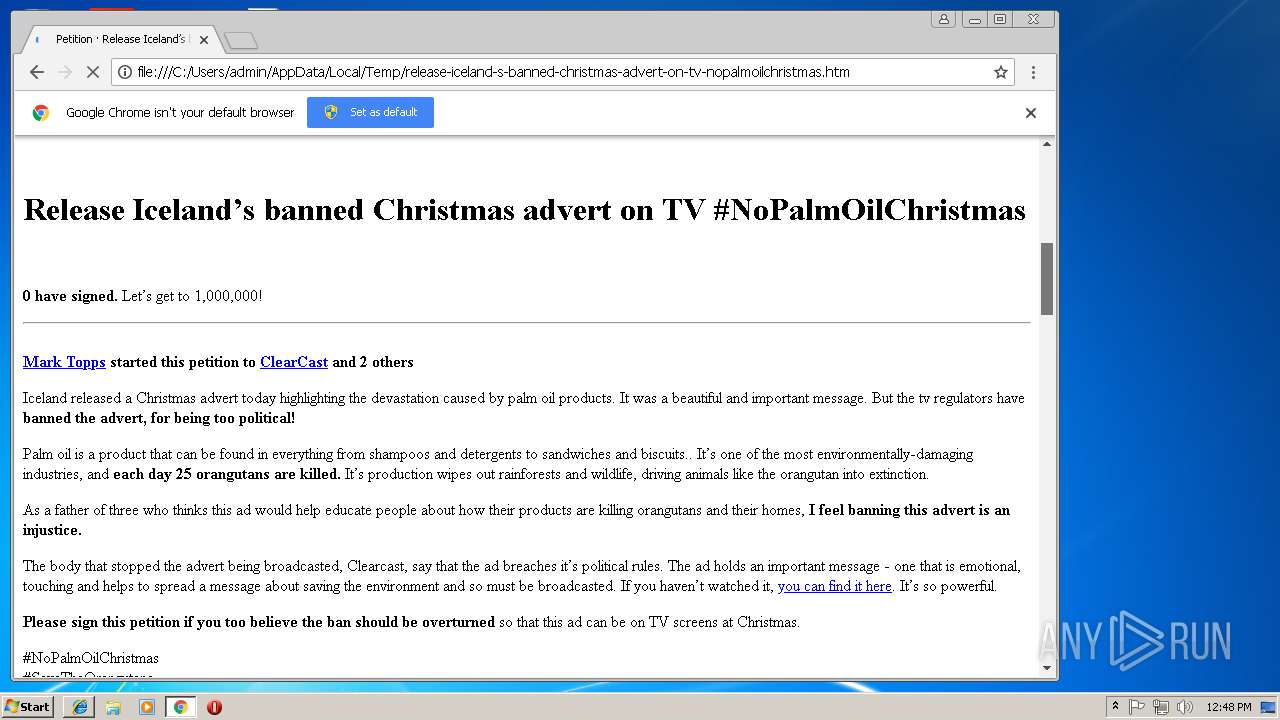
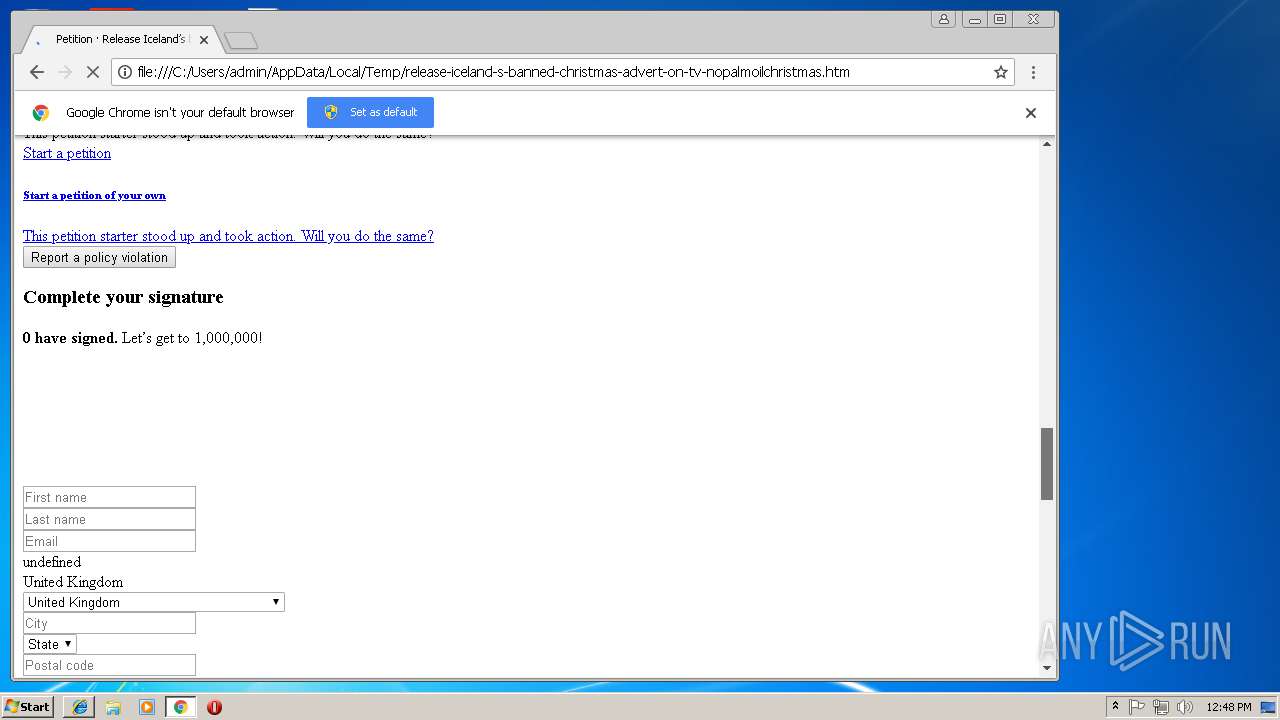
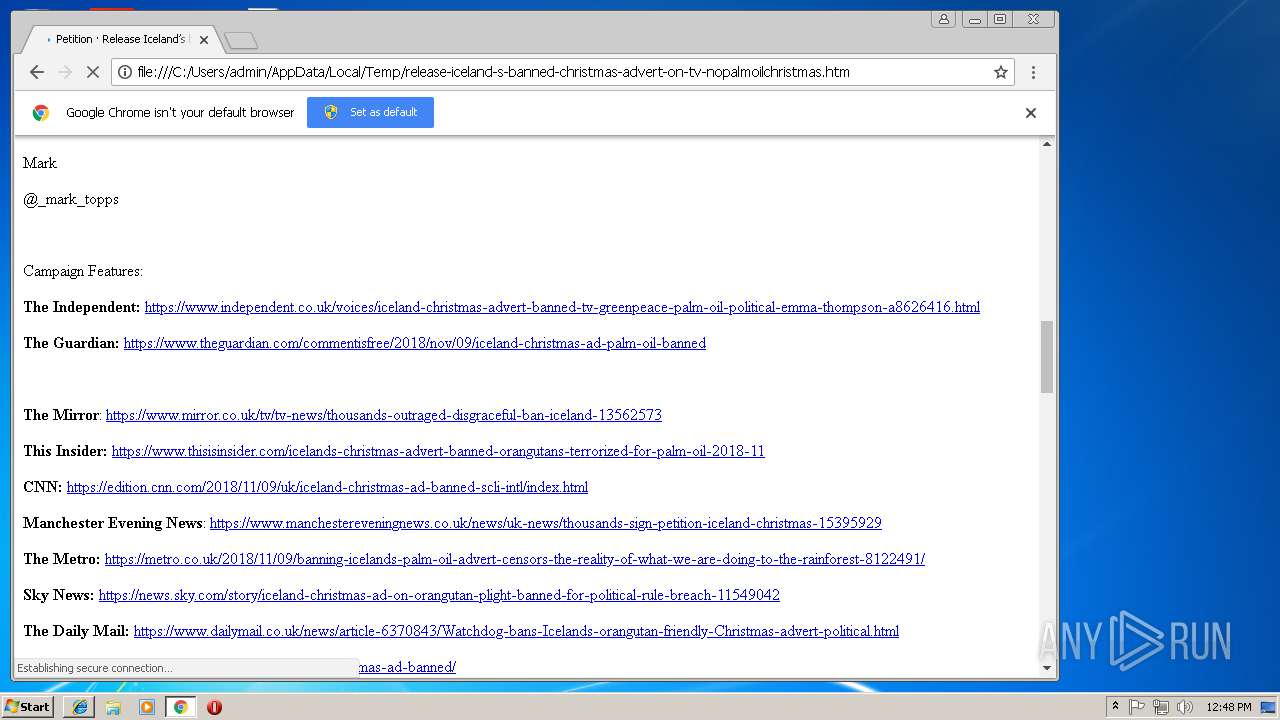
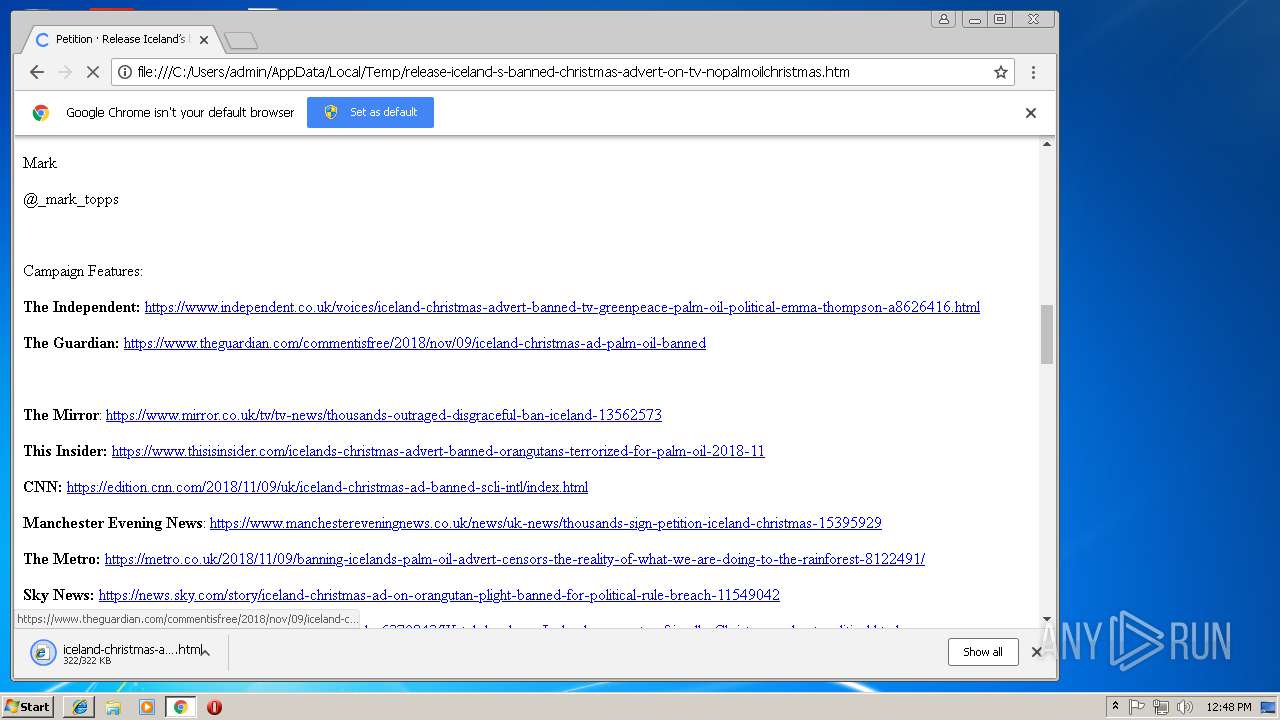
| Title: | Petition · Release Iceland’s banned Christmas advert on TV #NoPalmOilChristmas · Change.org |
Total processes
48
Monitored processes
14
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\release-iceland-s-banned-christmas-advert-on-tv-nopalmoilchristmas.htm | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=872,10866531391684517126,1447579898441791019,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=E50308E60031B2A12177C54739422393 --mojo-platform-channel-handle=2156 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:920 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,10866531391684517126,1447579898441791019,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=61CF276AA986EF113F055288771B09EC --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=61CF276AA986EF113F055288771B09EC --renderer-client-id=7 --mojo-platform-channel-handle=1640 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,10866531391684517126,1447579898441791019,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=0E3E2F9BB68C814877DD532942B311BE --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0E3E2F9BB68C814877DD532942B311BE --renderer-client-id=6 --mojo-platform-channel-handle=3564 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=872,10866531391684517126,1447579898441791019,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2125D6EE08C18DD49FDFA28BCB9B2D20 --mojo-platform-channel-handle=520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,10866531391684517126,1447579898441791019,131072 --enable-features=PasswordImport --service-pipe-token=02C58B9E15057C439F645776D705A5DB --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=02C58B9E15057C439F645776D705A5DB --renderer-client-id=5 --mojo-platform-channel-handle=1760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=872,10866531391684517126,1447579898441791019,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=F4E23A2ECA105C0F8DF297FAF31F5D2E --mojo-platform-channel-handle=2616 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,10866531391684517126,1447579898441791019,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=86CE103B78486F7B3AE872C0F0733A09 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=86CE103B78486F7B3AE872C0F0733A09 --renderer-client-id=10 --mojo-platform-channel-handle=4244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
949
Read events
815
Write events
128
Delete events
6
Modification events
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {52828A75-E80B-11E8-BFAB-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070B0003000E000C002E002500C101 | |||
Executable files
0
Suspicious files
88
Text files
83
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\79ea57ad-3cef-4f36-91af-25e23f4a9833.tmp | — | |
MD5:— | SHA256:— | |||
| 676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@doubleclick[1].txt | text | |
MD5:— | SHA256:— | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\SystemCertificates\My\Certificates\E02357FC7708441D4B0BE5F371F4B28961870F70 | binary | |
MD5:— | SHA256:— | |||
| 676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF5e7892.TMP | text | |
MD5:— | SHA256:— | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018111420181115\index.dat | dat | |
MD5:— | SHA256:— | |||
| 676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\51238791-240c-464c-a6ab-d7e83d806413.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
126
DNS requests
91
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
676 | chrome.exe | GET | 200 | 52.18.169.38:80 | http://bcp.crwdcntrl.net/5/c=12699/rand=330407235/pv=y/int=%23OpR%2384740%23%20%3A%20Site%20Section%20%3A%20C/int=%23OpR%2384742%23%20%3A%20Site%20Section%20%3A%20C/rt=ifr | IE | html | 212 b | whitelisted |
676 | chrome.exe | GET | 302 | 172.217.168.34:80 | http://cm.g.doubleclick.net/pixel?google_nid=lotame_dmp&google_cm | US | html | 296 b | whitelisted |
676 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 54.4 Kb | whitelisted |
676 | chrome.exe | GET | 200 | 104.109.73.63:80 | http://ssl.trustwave.com/issuers/STCA.crt | NL | der | 956 b | whitelisted |
920 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
676 | chrome.exe | GET | 200 | 52.18.169.38:80 | http://bcp.crwdcntrl.net/gmap/?tp=GDMP&google_gid=CAESEP_zhcz_TFlbUGyW0CJl71U&google_cver=1 | IE | image | 49 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1548 | iexplore.exe | 216.58.215.228:443 | www.google.com | Google Inc. | US | whitelisted |
1548 | iexplore.exe | 172.217.168.3:443 | www.google.no | Google Inc. | US | whitelisted |
676 | chrome.exe | 172.217.168.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 216.58.215.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 216.58.215.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 104.16.4.13:443 | assets-fe.change.org | Cloudflare Inc | US | shared |
676 | chrome.exe | 104.109.56.73:443 | cdn.optimizely.com | Akamai International B.V. | NL | whitelisted |
4 | System | 104.16.4.13:445 | assets-fe.change.org | Cloudflare Inc | US | shared |
920 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4 | System | 104.16.5.13:445 | assets-fe.change.org | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
assets-fe.change.org |
| whitelisted |
www.bing.com |
| whitelisted |
dns.msftncsi.com |
| shared |
cdn.optimizely.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
assets.change.org |
| whitelisted |
www.googleadservices.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
www.google.com |
| malicious |