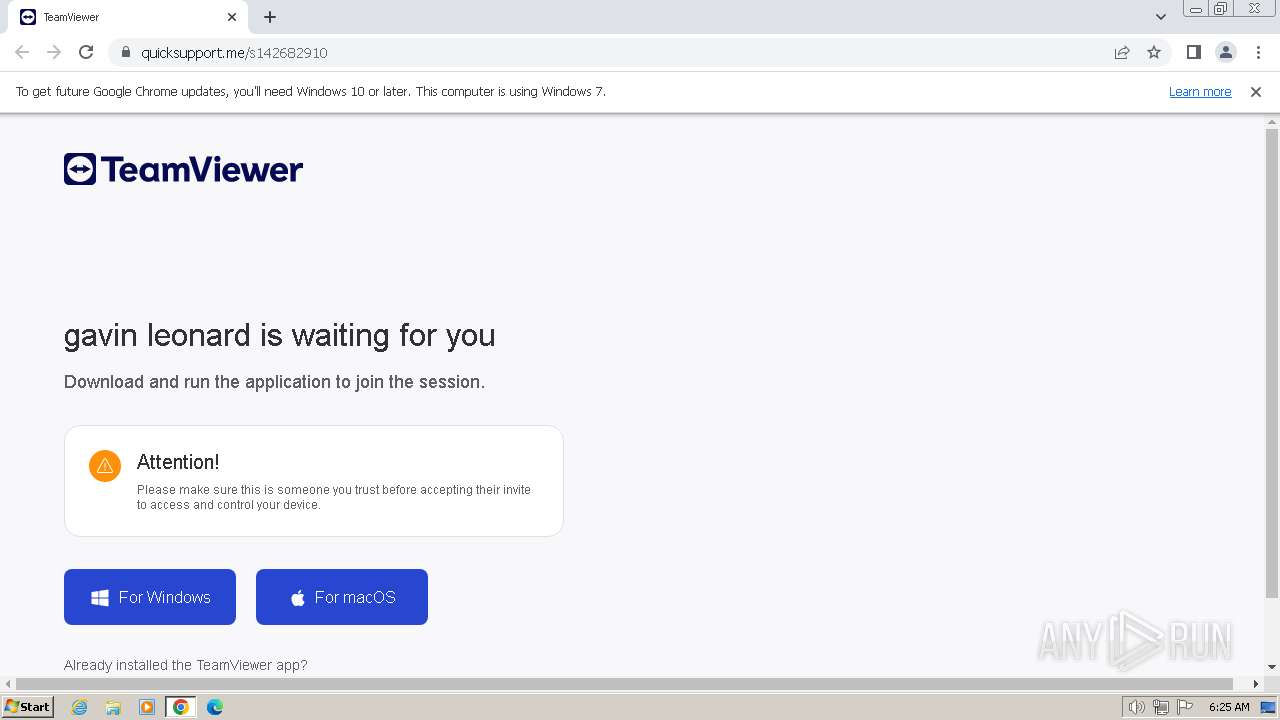
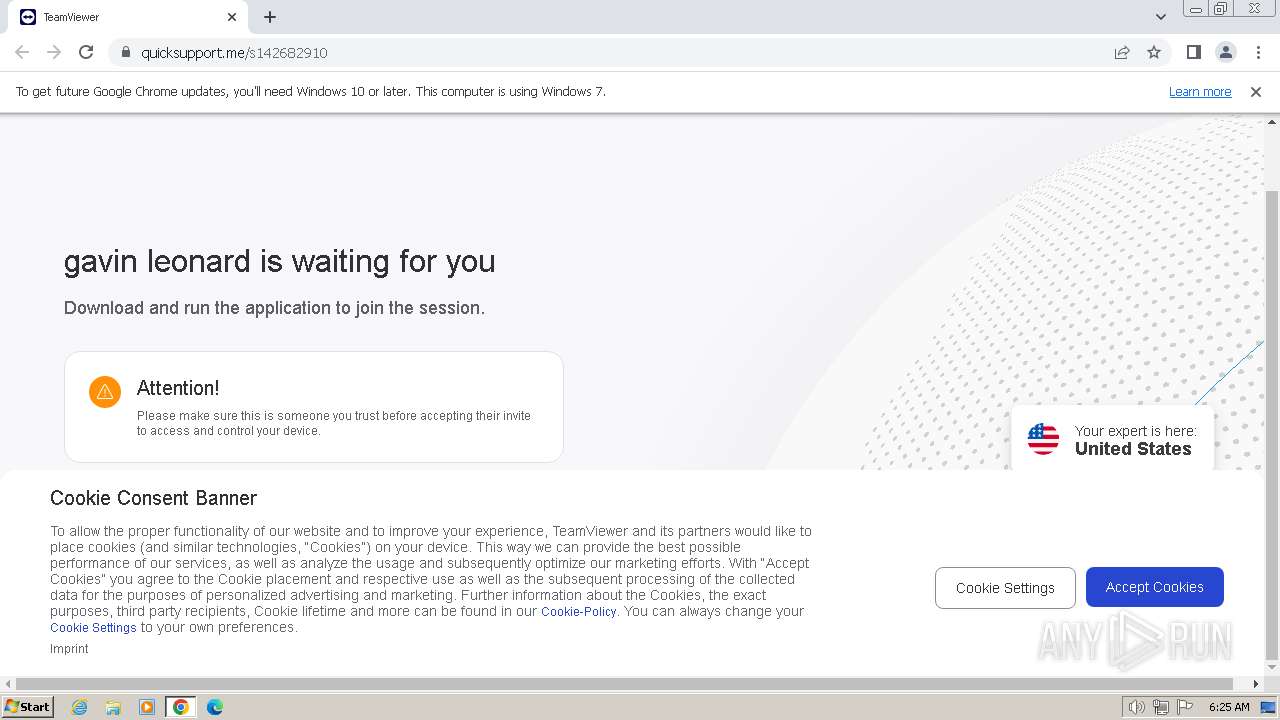
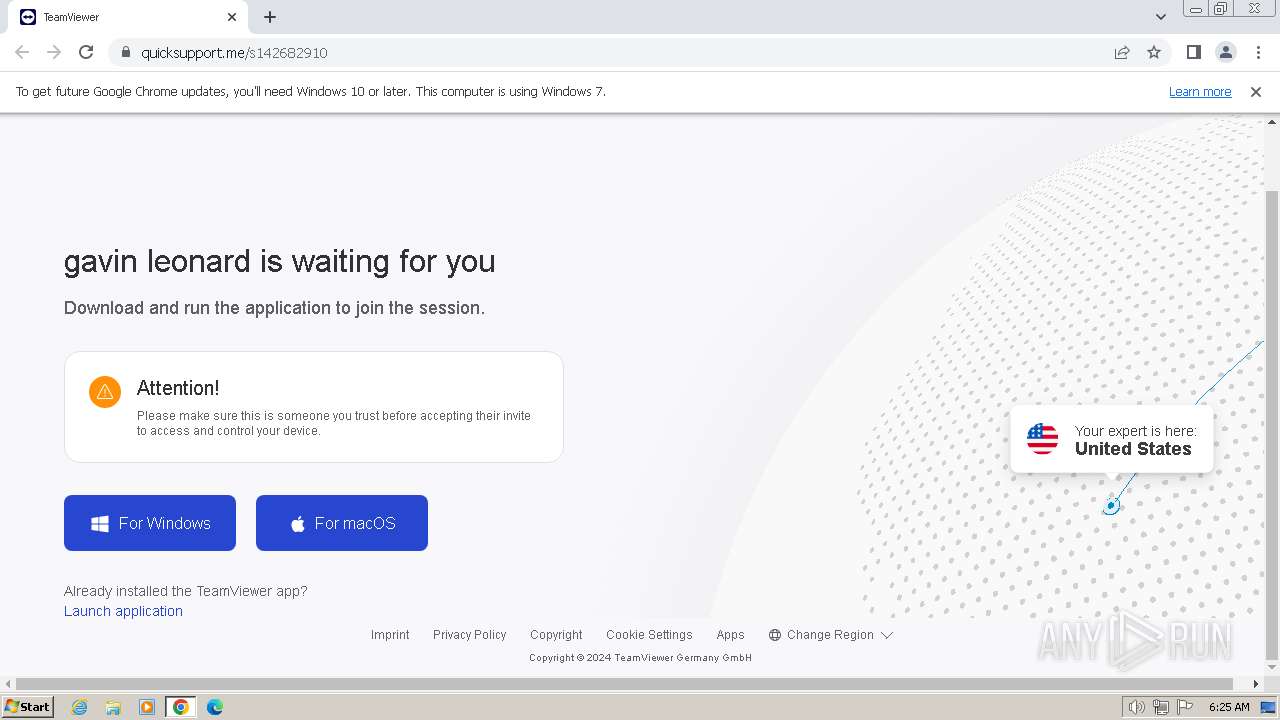
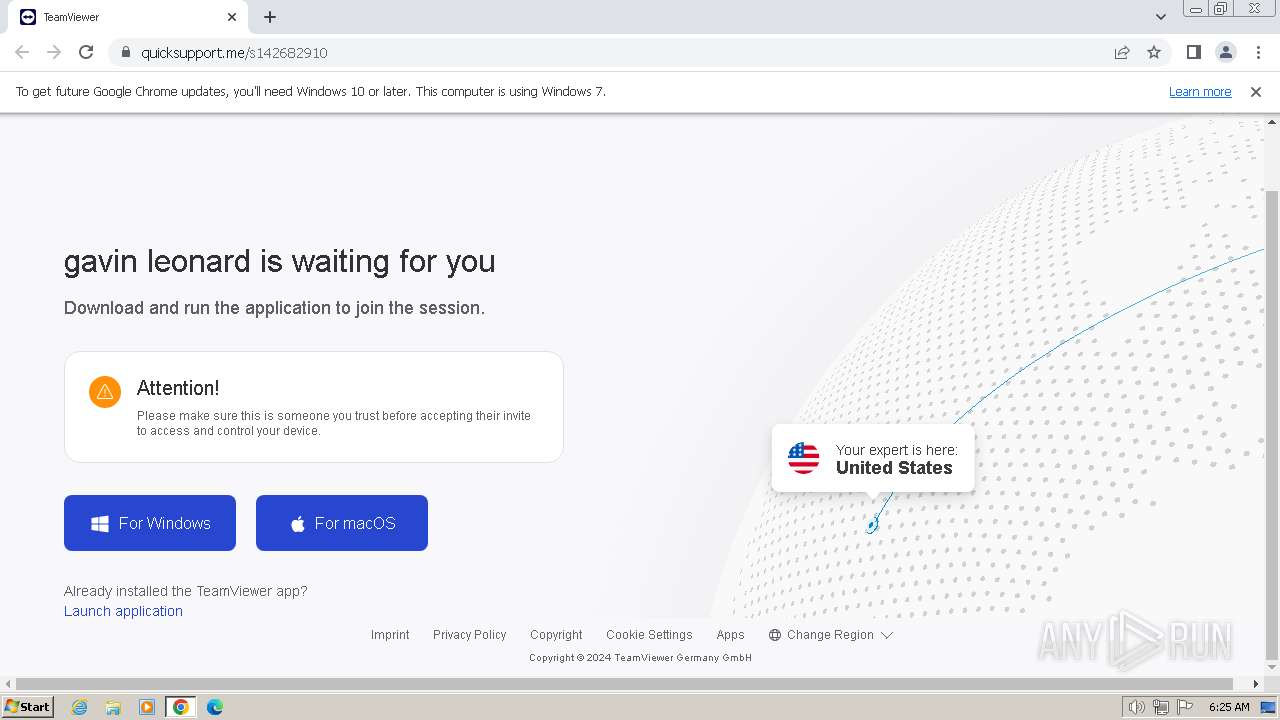
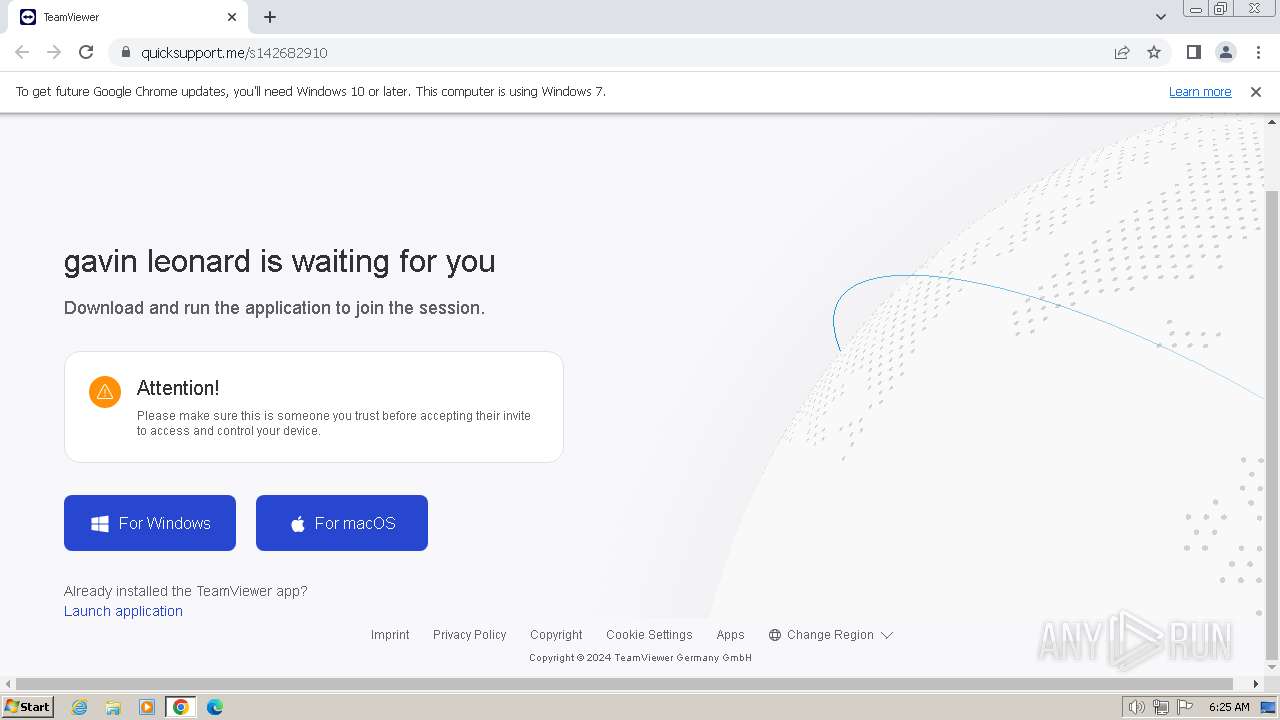
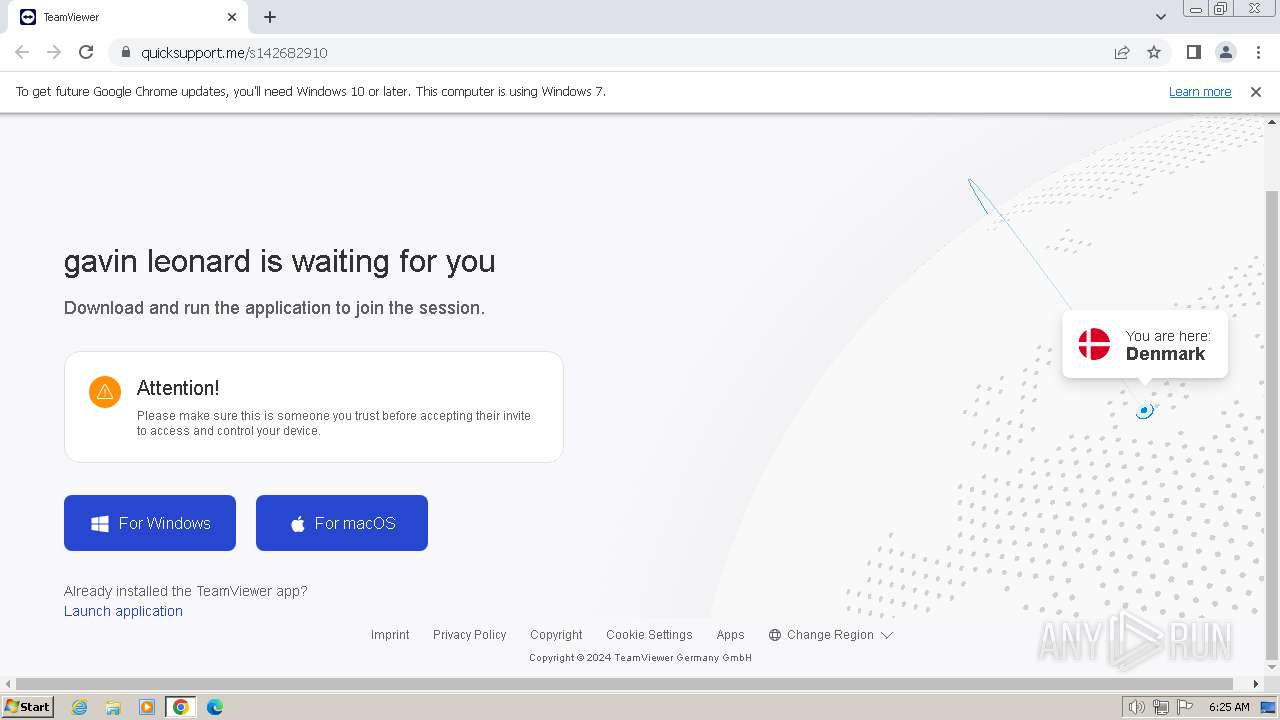
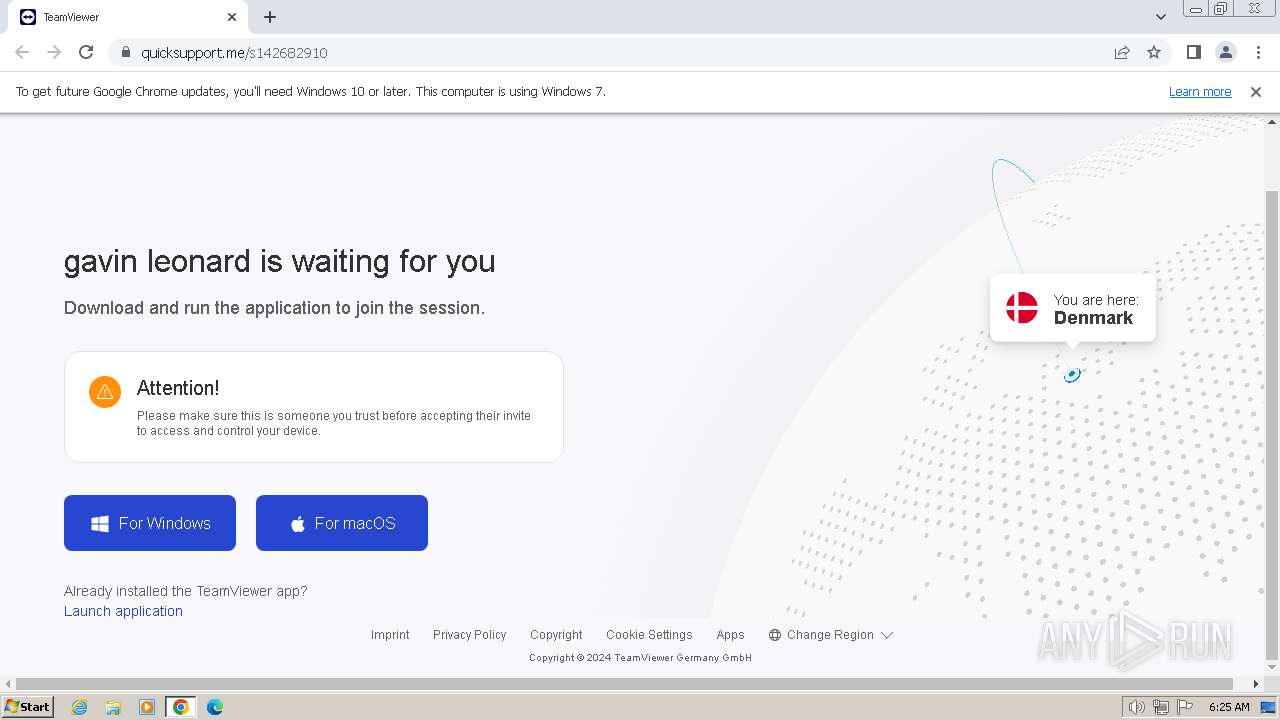
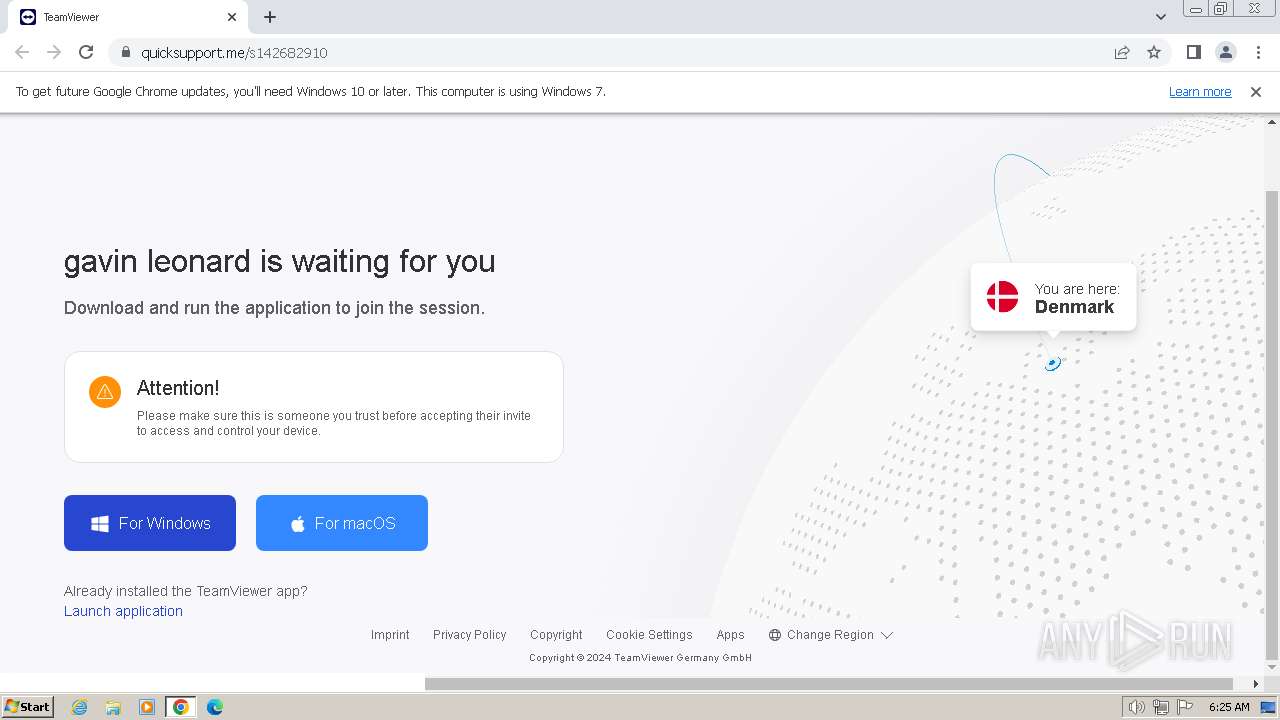
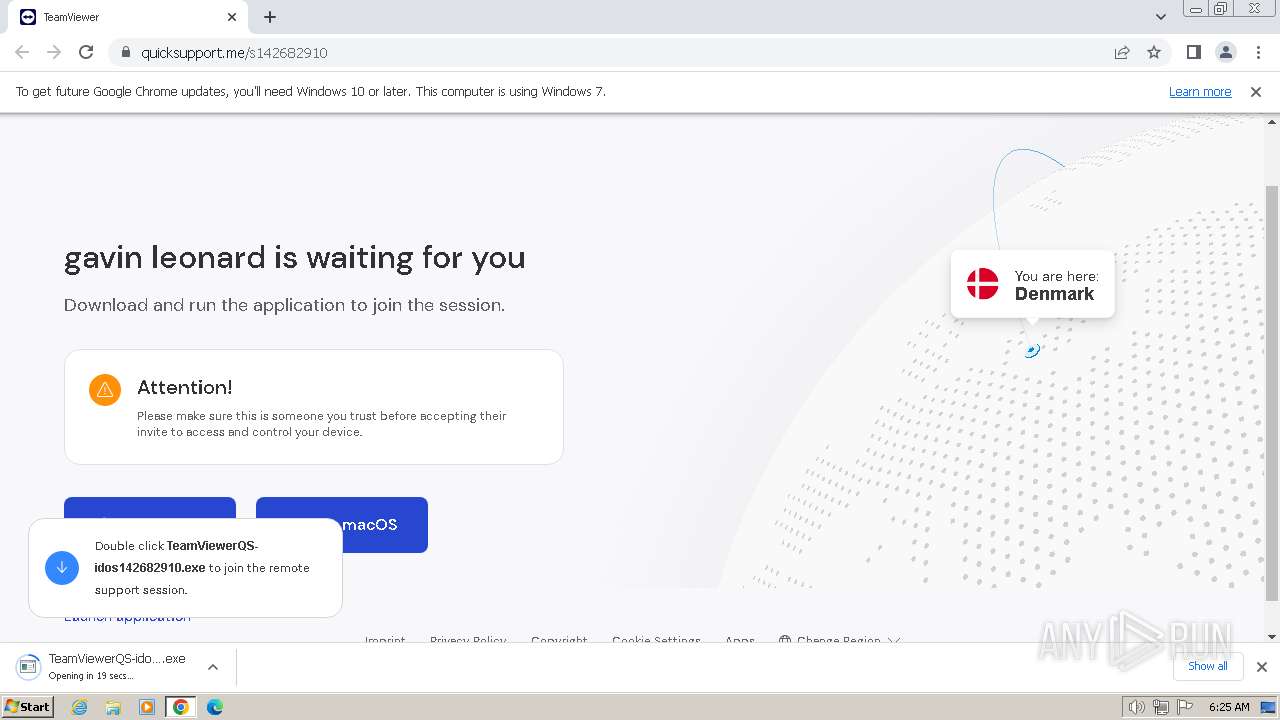
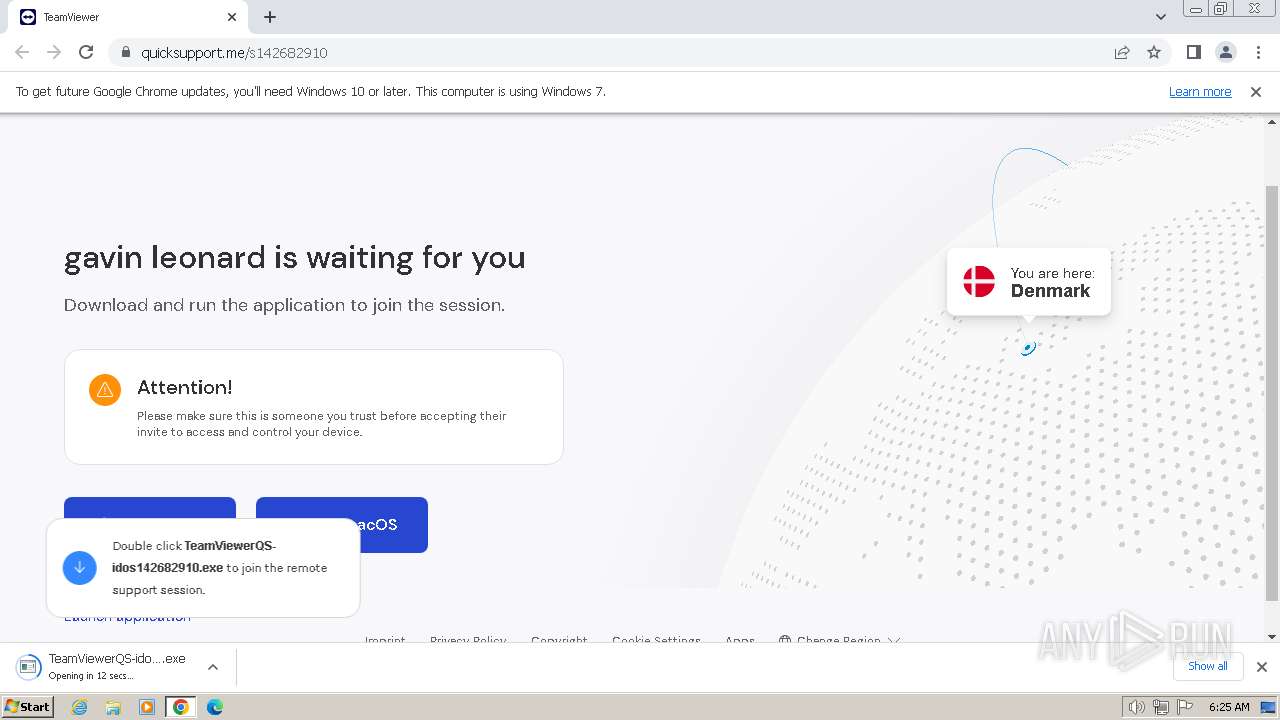
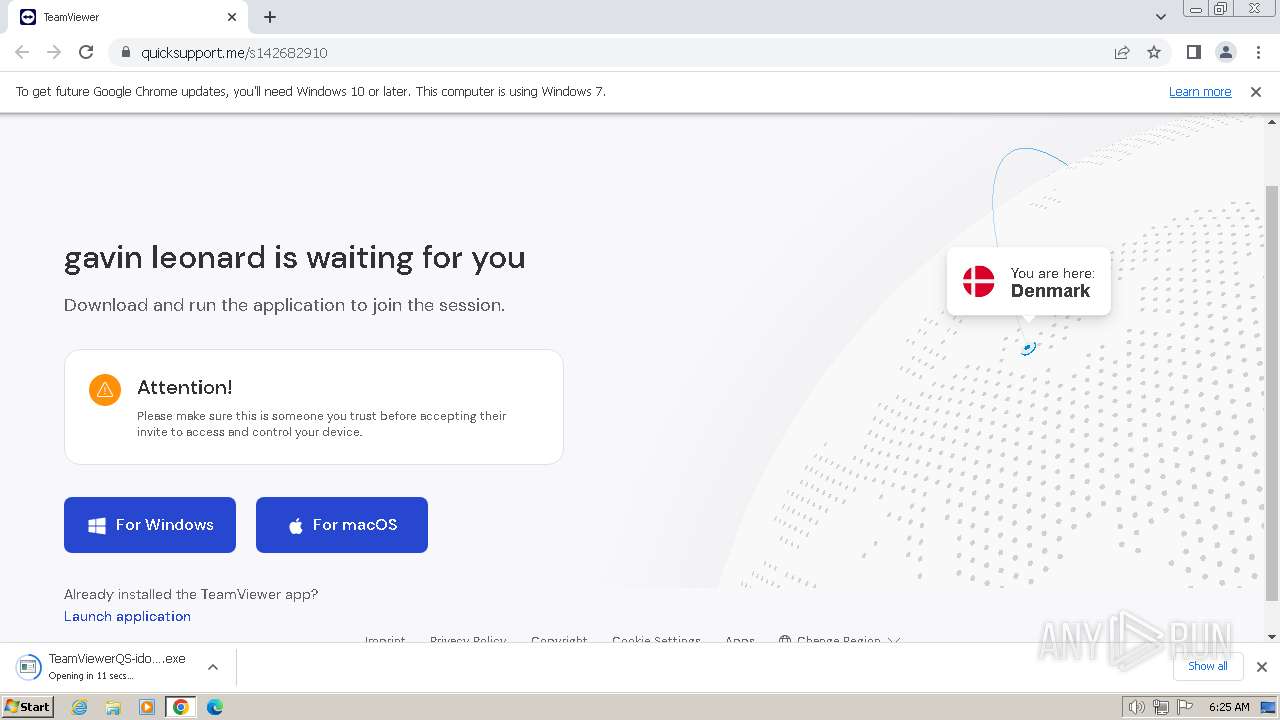
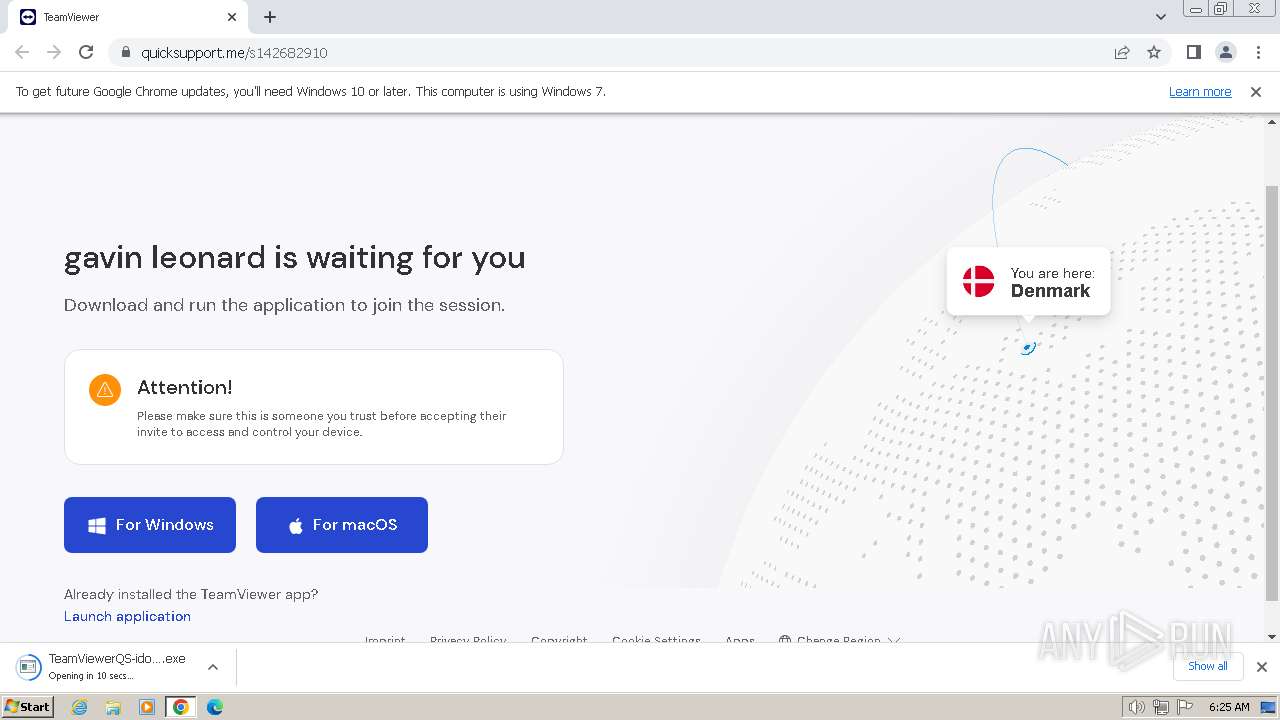
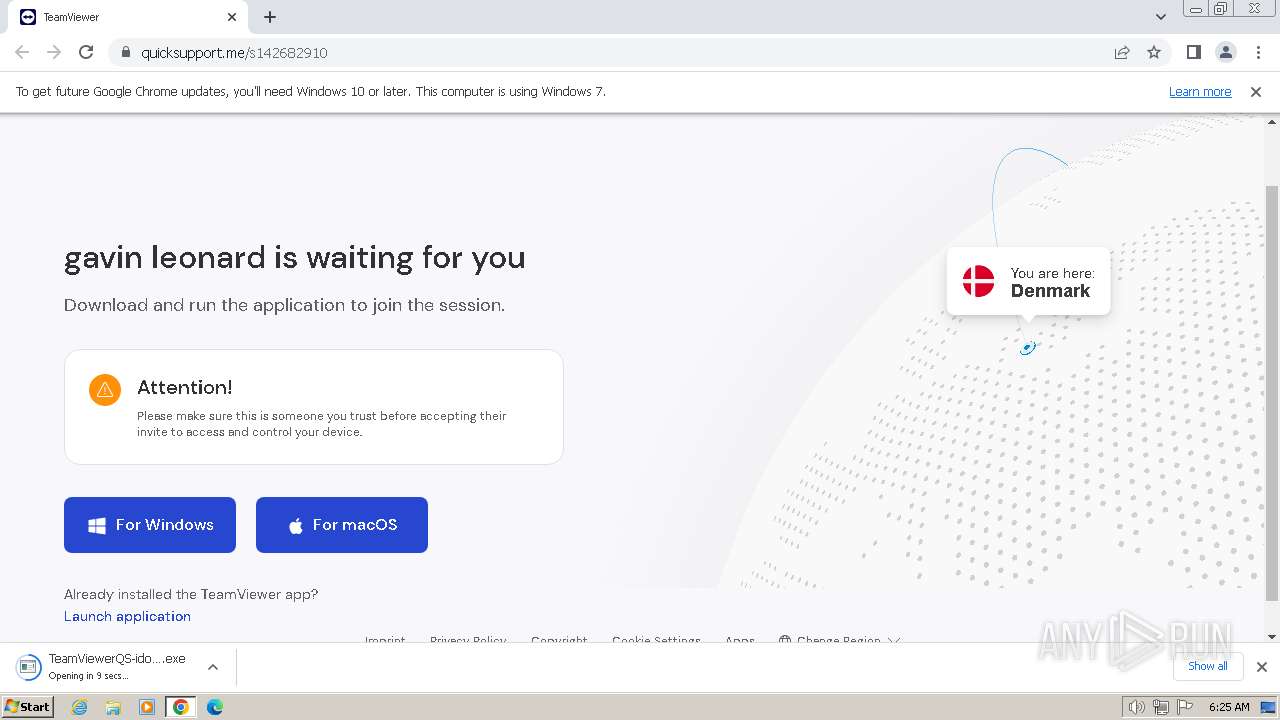
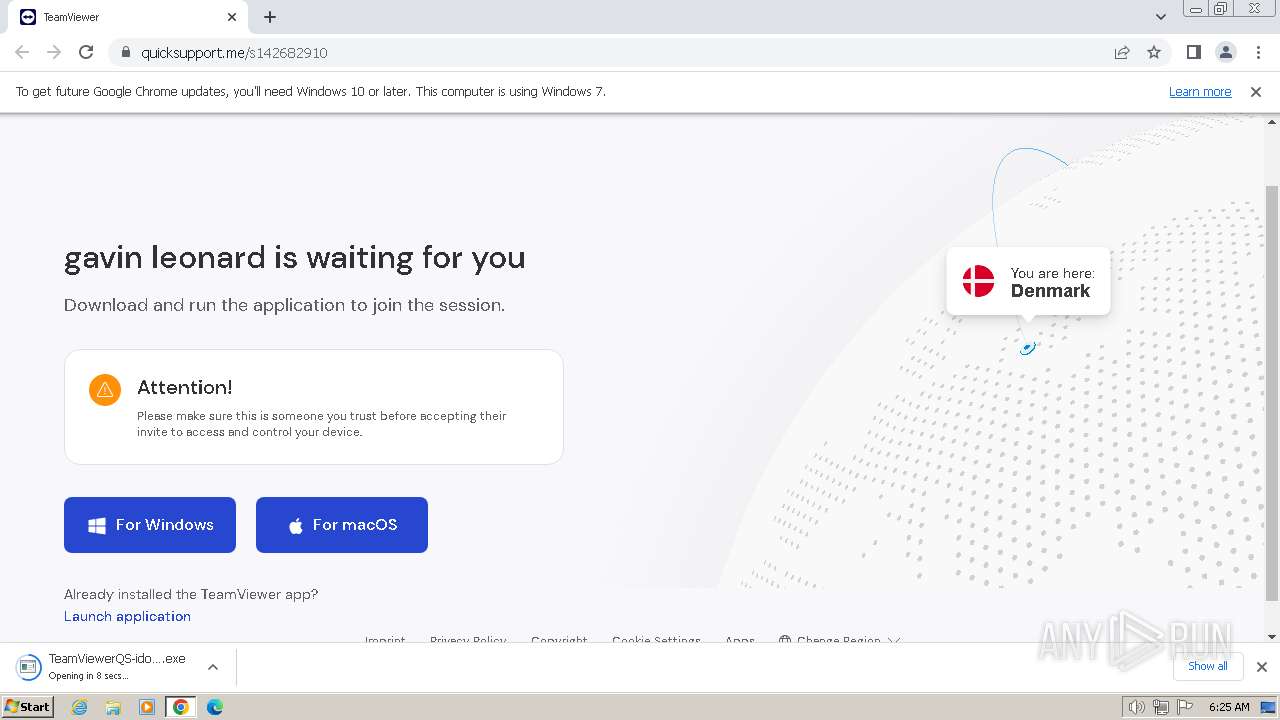
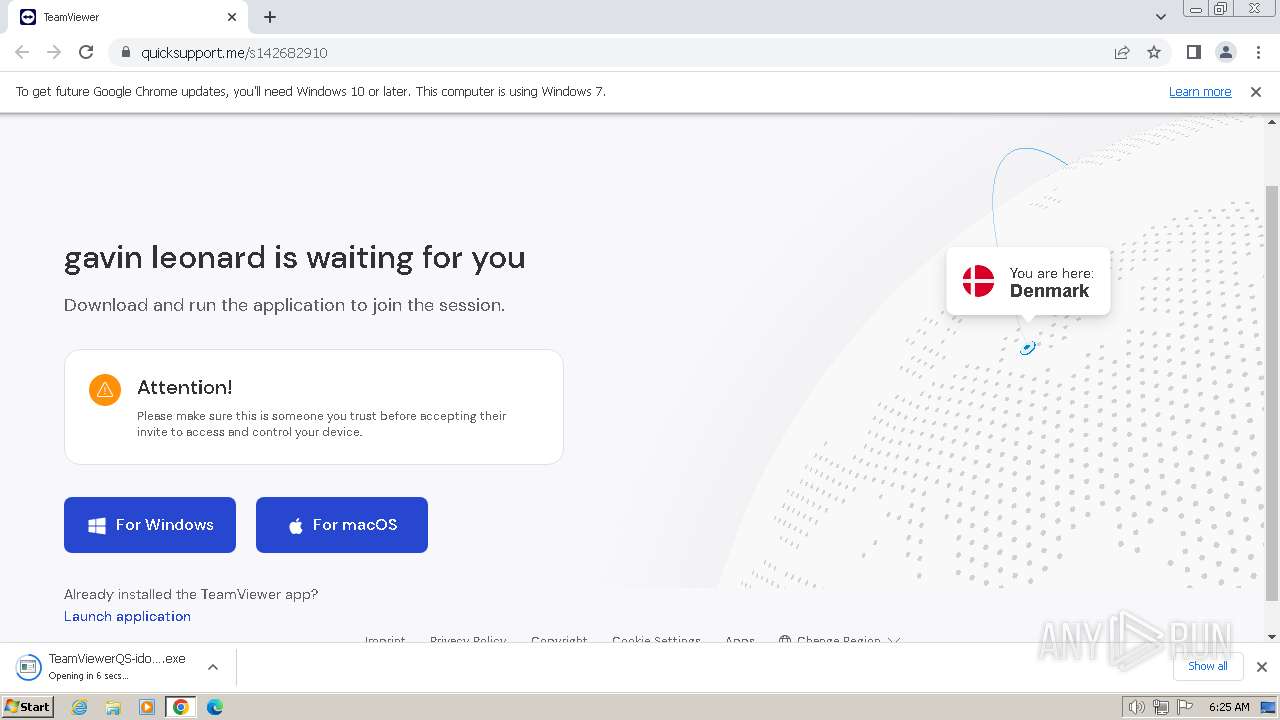
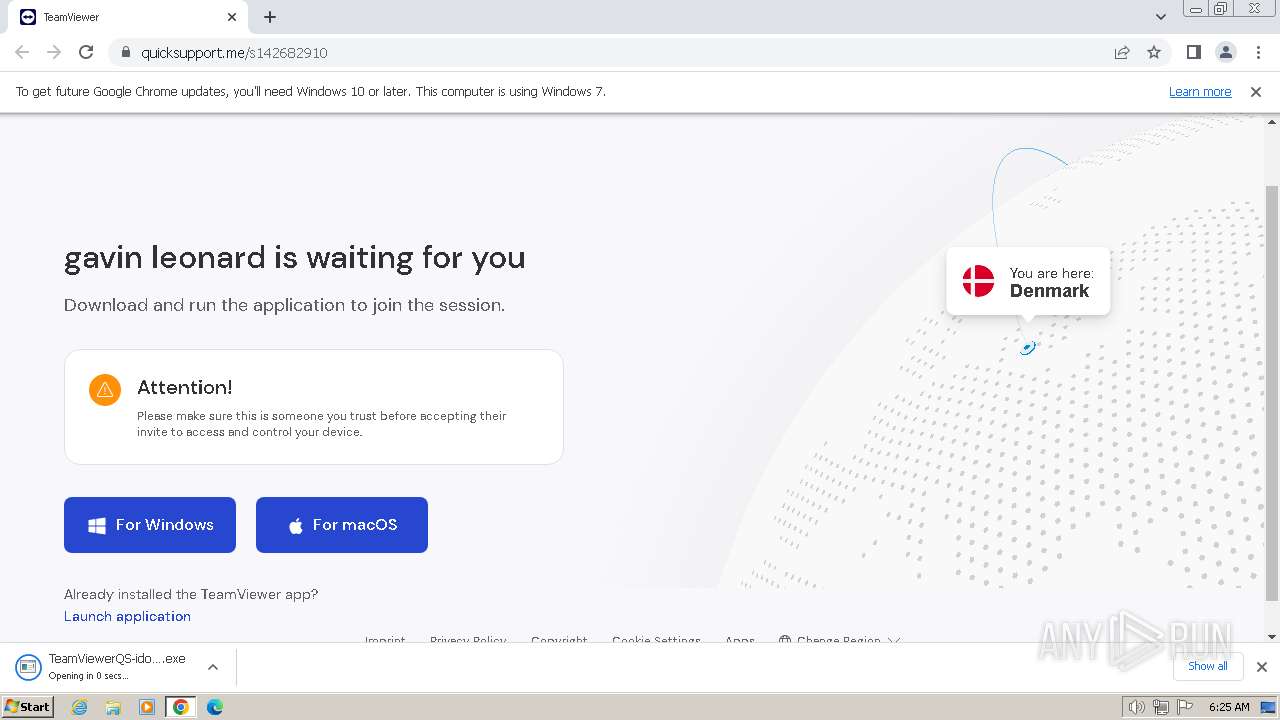
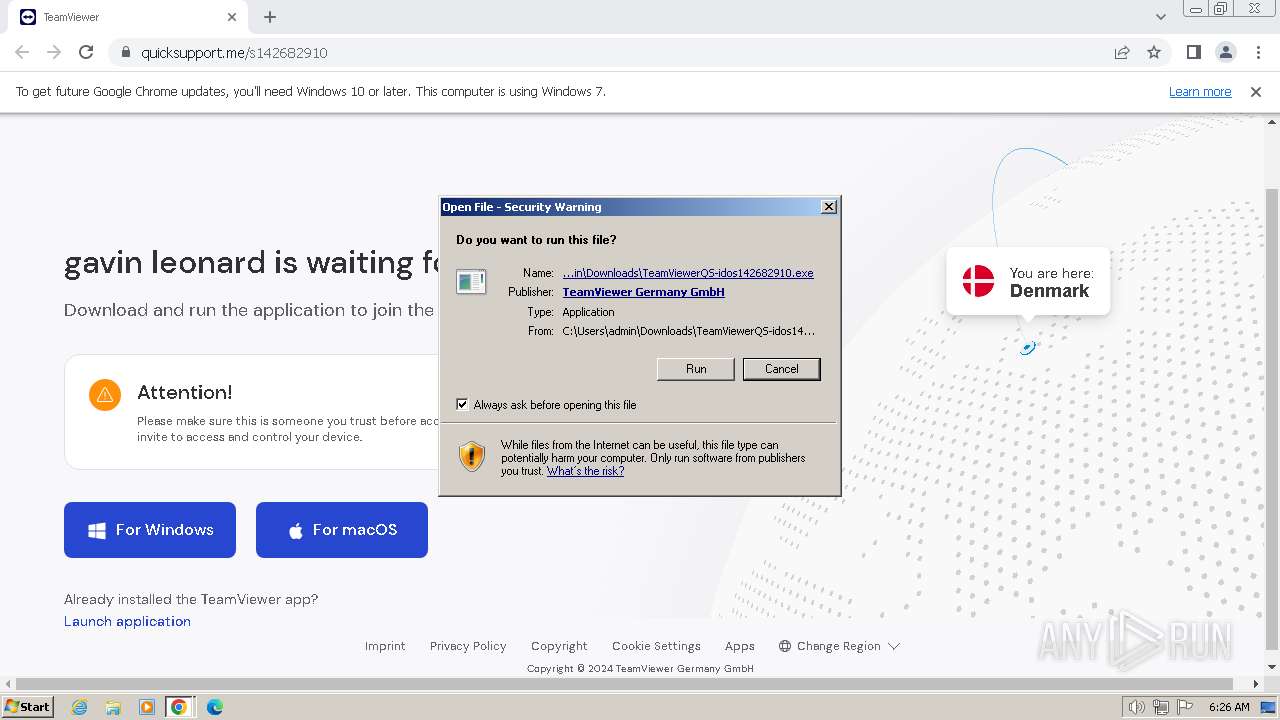
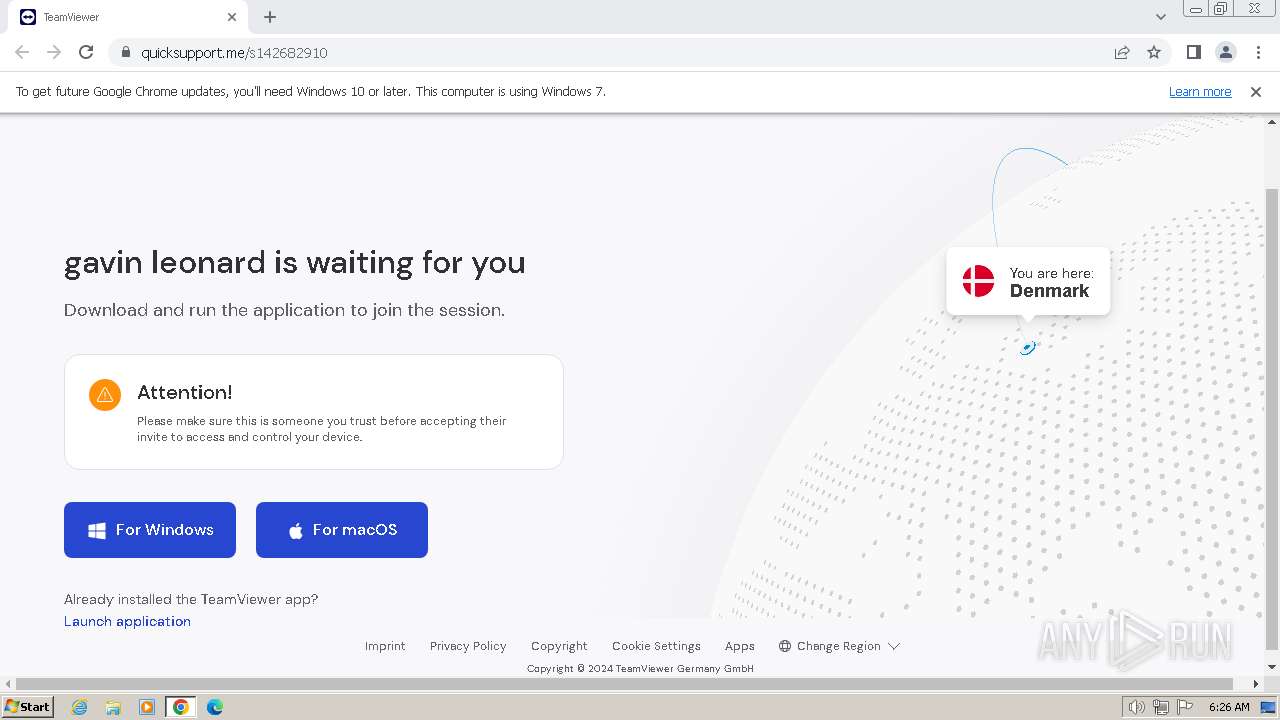
| URL: | https://quicksupport.me/s142682910 |
| Full analysis: | https://app.any.run/tasks/af9a5446-2be8-4f8b-86e3-e3105c4cc66a |
| Verdict: | Malicious activity |
| Analysis date: | March 17, 2024, 06:25:11 |
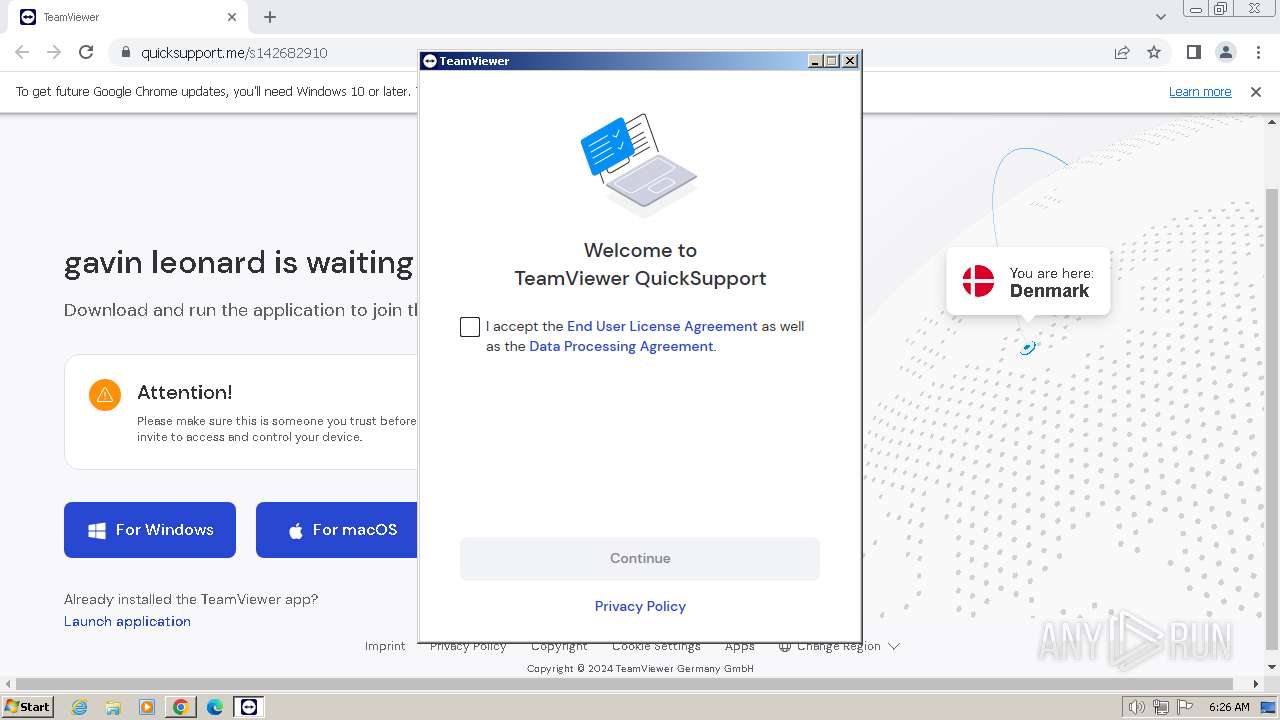
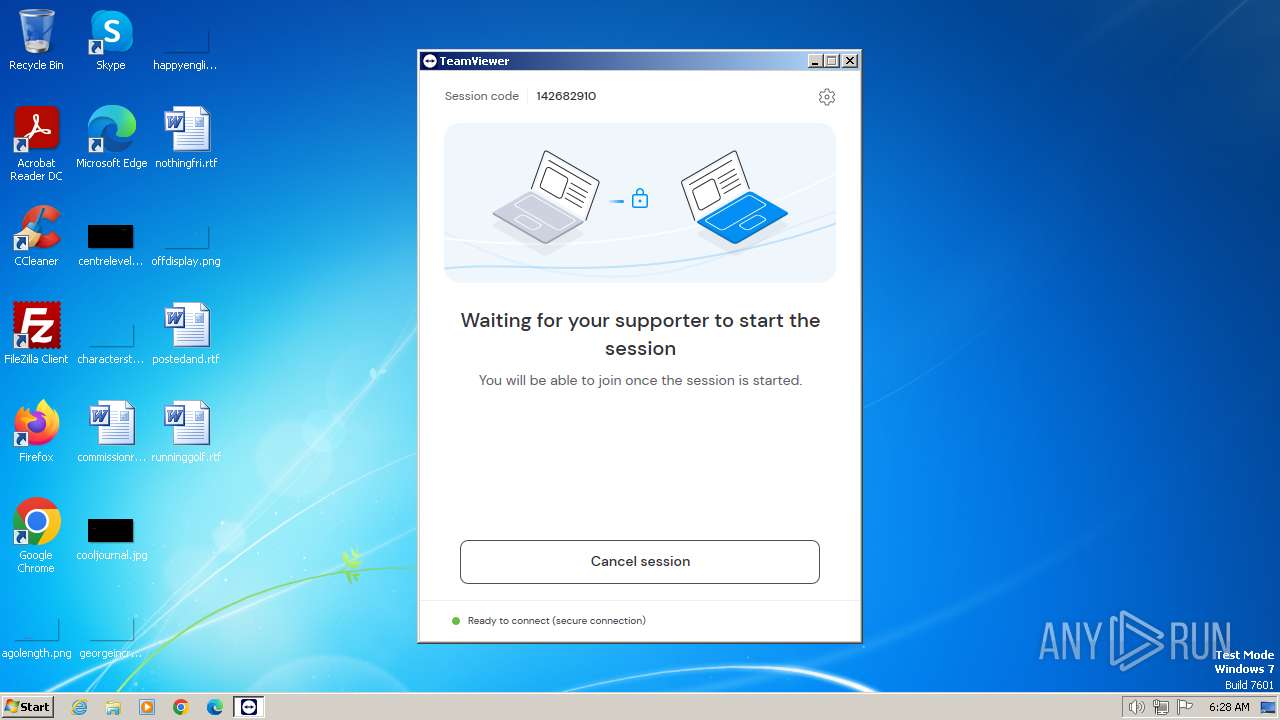
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E2AF5CA3207E65A02794F2FF3960D57A |
| SHA1: | 8242C32468F319E93CE3415E9B0F0FFA14C5028C |
| SHA256: | DF50A7510064BC73D4994850C4E9F4AF441EDC9D7680EB8B70D1B5A050FAAC08 |
| SSDEEP: | 3:N8IZX/QLIAK5dXP:2ICLIA6XP |
MALICIOUS
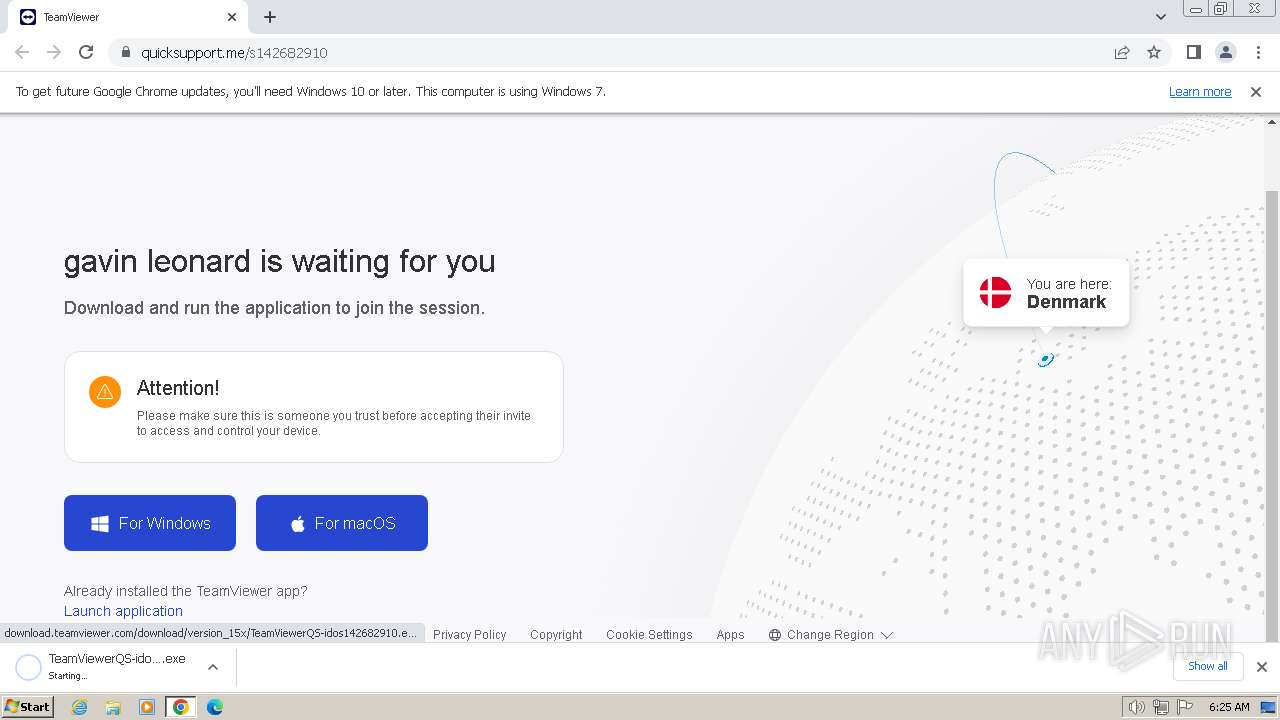
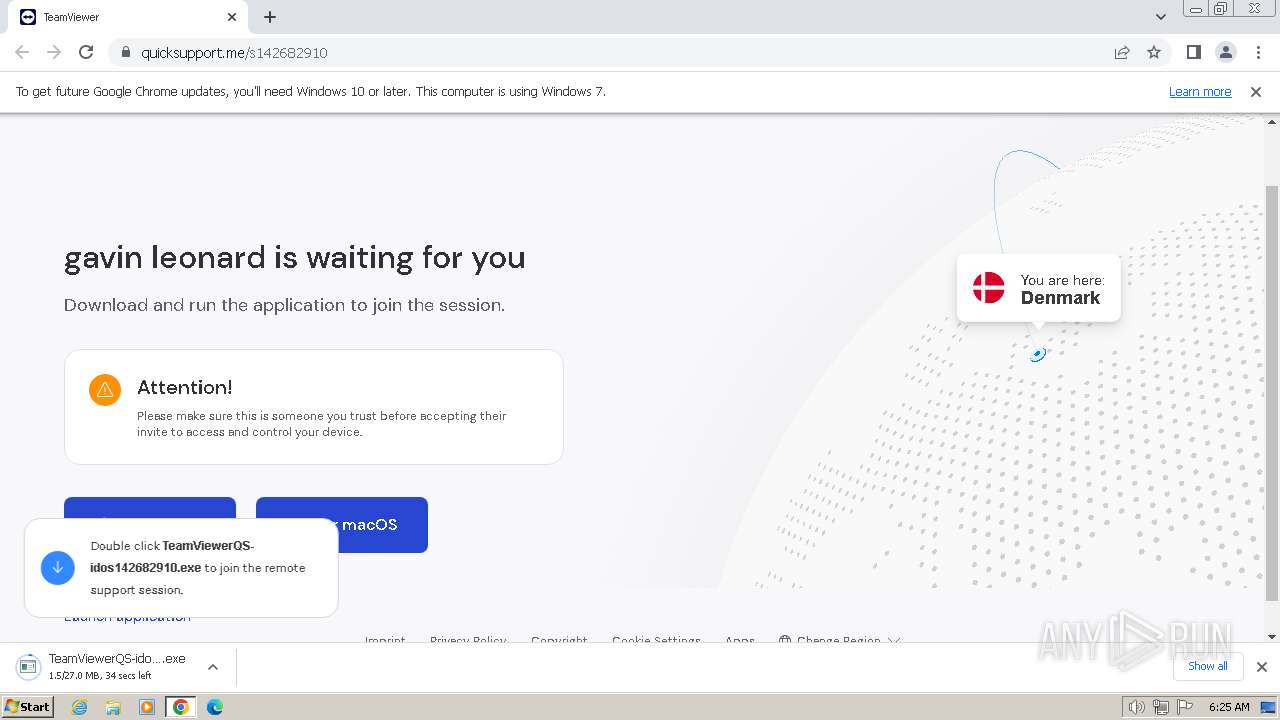
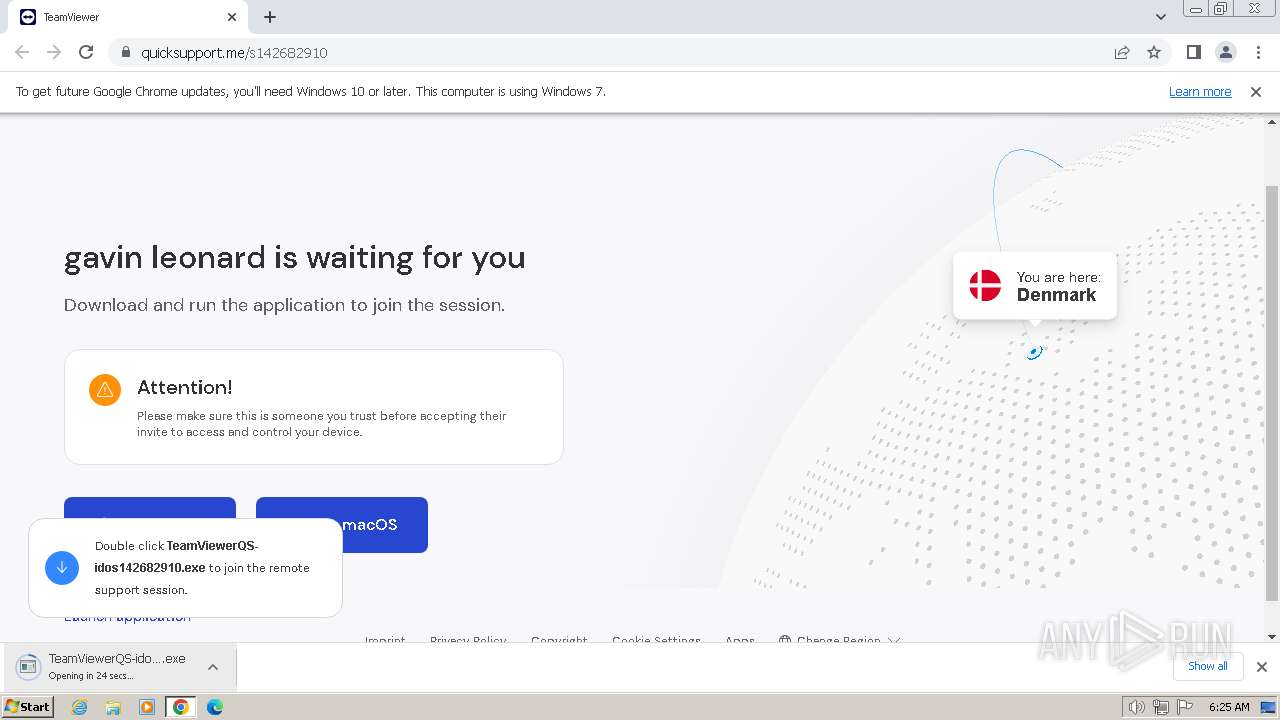
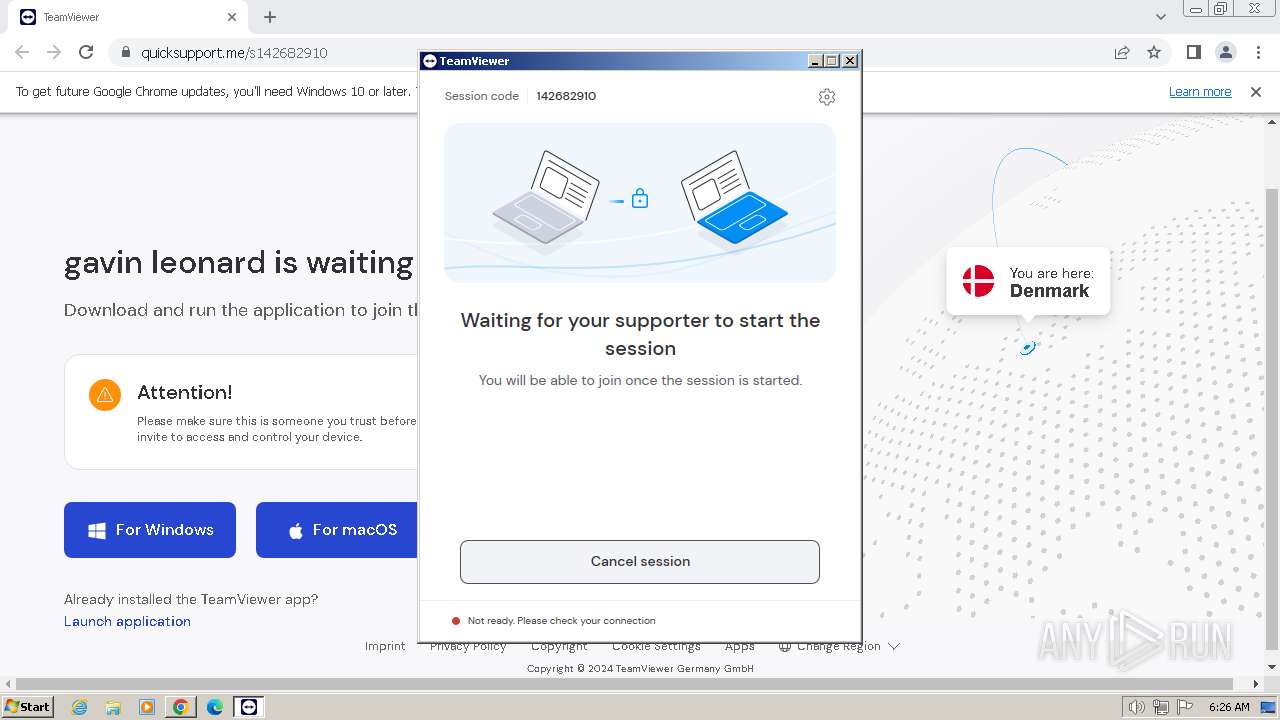
Drops the executable file immediately after the start
- TeamViewerQS-idos142682910.exe (PID: 1652)
Steals credentials from Web Browsers
- TeamViewer.exe (PID: 3136)
Actions looks like stealing of personal data
- TeamViewer.exe (PID: 3136)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- TeamViewerQS-idos142682910.exe (PID: 1652)
Reads the Internet Settings
- TeamViewerQS-idos142682910.exe (PID: 1652)
- TeamViewer.exe (PID: 3564)
- TeamViewer.exe (PID: 3136)
Reads security settings of Internet Explorer
- TeamViewer.exe (PID: 3564)
- TeamViewerQS-idos142682910.exe (PID: 1652)
- TeamViewer.exe (PID: 3136)
Checks Windows Trust Settings
- TeamViewer.exe (PID: 3564)
- TeamViewer.exe (PID: 3136)
- tv_w32.exe (PID: 3560)
- TeamViewer_Desktop.exe (PID: 3428)
Executable content was dropped or overwritten
- TeamViewerQS-idos142682910.exe (PID: 1652)
Drops 7-zip archiver for unpacking
- TeamViewerQS-idos142682910.exe (PID: 1652)
The process creates files with name similar to system file names
- TeamViewerQS-idos142682910.exe (PID: 1652)
Reads settings of System Certificates
- TeamViewer.exe (PID: 3136)
- TeamViewer.exe (PID: 3564)
Reads Microsoft Outlook installation path
- TeamViewer.exe (PID: 3136)
Creates file in the systems drive root
- TeamViewer.exe (PID: 3136)
Application launched itself
- TeamViewer.exe (PID: 3564)
Connects to unusual port
- TeamViewer.exe (PID: 3136)
INFO
The process uses the downloaded file
- chrome.exe (PID: 1216)
- chrome.exe (PID: 3936)
Application launched itself
- chrome.exe (PID: 3936)
Executable content was dropped or overwritten
- chrome.exe (PID: 3936)
Create files in a temporary directory
- TeamViewerQS-idos142682910.exe (PID: 1652)
- TeamViewer.exe (PID: 3136)
- TeamViewer_Desktop.exe (PID: 3428)
Reads the computer name
- TeamViewerQS-idos142682910.exe (PID: 1652)
- TeamViewer.exe (PID: 3564)
- TeamViewer.exe (PID: 3136)
- TeamViewer_Desktop.exe (PID: 3428)
- tv_w32.exe (PID: 3560)
Checks supported languages
- TeamViewerQS-idos142682910.exe (PID: 1652)
- TeamViewer.exe (PID: 3564)
- TeamViewer.exe (PID: 3136)
- tv_w32.exe (PID: 3560)
- TeamViewer_Desktop.exe (PID: 3428)
Reads the machine GUID from the registry
- TeamViewer.exe (PID: 3564)
- TeamViewer.exe (PID: 3136)
- tv_w32.exe (PID: 3560)
- TeamViewer_Desktop.exe (PID: 3428)
Drops the executable file immediately after the start
- chrome.exe (PID: 3936)
Reads the software policy settings
- TeamViewer.exe (PID: 3564)
- TeamViewer.exe (PID: 3136)
- tv_w32.exe (PID: 3560)
- TeamViewer_Desktop.exe (PID: 3428)
Creates files or folders in the user directory
- TeamViewer.exe (PID: 3136)
Reads the time zone
- TeamViewer.exe (PID: 3136)
Process checks computer location settings
- TeamViewer.exe (PID: 3136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
27
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3500 --field-trial-handle=876,i,10123456420668295677,18249836111230789942,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1276 --field-trial-handle=876,i,10123456420668295677,18249836111230789942,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=3336 --field-trial-handle=876,i,10123456420668295677,18249836111230789942,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3704 --field-trial-handle=876,i,10123456420668295677,18249836111230789942,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1652 | "C:\Users\admin\Downloads\TeamViewerQS-idos142682910.exe" | C:\Users\admin\Downloads\TeamViewerQS-idos142682910.exe | chrome.exe | ||||||||||||
User: admin Company: TeamViewer Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bcd8b38,0x6bcd8b48,0x6bcd8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1520 --field-trial-handle=876,i,10123456420668295677,18249836111230789942,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2000 --field-trial-handle=876,i,10123456420668295677,18249836111230789942,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3276 --field-trial-handle=876,i,10123456420668295677,18249836111230789942,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1376 --field-trial-handle=876,i,10123456420668295677,18249836111230789942,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
59 584
Read events
59 389
Write events
185
Delete events
10
Modification events
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
51
Suspicious files
37
Text files
73
Unknown types
256
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF18219c.TMP | — | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:65239F35CB63C76EA1F59EF64F7AAFF4 | SHA256:252EF82CC03FDE4BEF13CF81CD1AC5CE45854212D1A7359035E7A5D6BEDBE229 | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:E53573A93829681410D5E7DBB1B61C78 | SHA256:A82D28F2C1E22A2AE0ABC5F5AF0CC8EE7AD913BAB3A0BF84CE6D8D23F67E06A3 | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF182805.TMP | — | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF182296.TMP | text | |
MD5:C383FD120B14BB0E98E99C1BCC9B43F6 | SHA256:56A3A5EACBD28BEE1CF8C1D0052321A5C27EE858BEF7B2FA1DE20806A0823CC1 | |||
| 3936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:4E2B7997F4C3647F8D1ADA88339BBBA5 | SHA256:C33226C460208AA10537A23CB5128FD887DCBAA335C7DC8BFFBE08A607CCFDF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
26
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 3.07 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | US | binary | 3.07 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | US | binary | 7.06 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | US | binary | 17.1 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | US | binary | 43.5 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | US | binary | 34.8 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | US | binary | 12.4 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 254 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 333 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1496 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
3936 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1496 | chrome.exe | 20.50.2.71:443 | quicksupport.me | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
1496 | chrome.exe | 142.250.185.132:443 | www.google.com | GOOGLE | US | whitelisted |
1496 | chrome.exe | 104.16.62.16:443 | download.teamviewer.com | CLOUDFLARENET | — | shared |
3936 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
1496 | chrome.exe | 142.250.181.234:443 | www.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
quicksupport.me |
| unknown |
www.google.com |
| whitelisted |
download.teamviewer.com |
| shared |
dl.teamviewer.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
router4.teamviewer.com |
| unknown |
clients1.google.com |
| whitelisted |