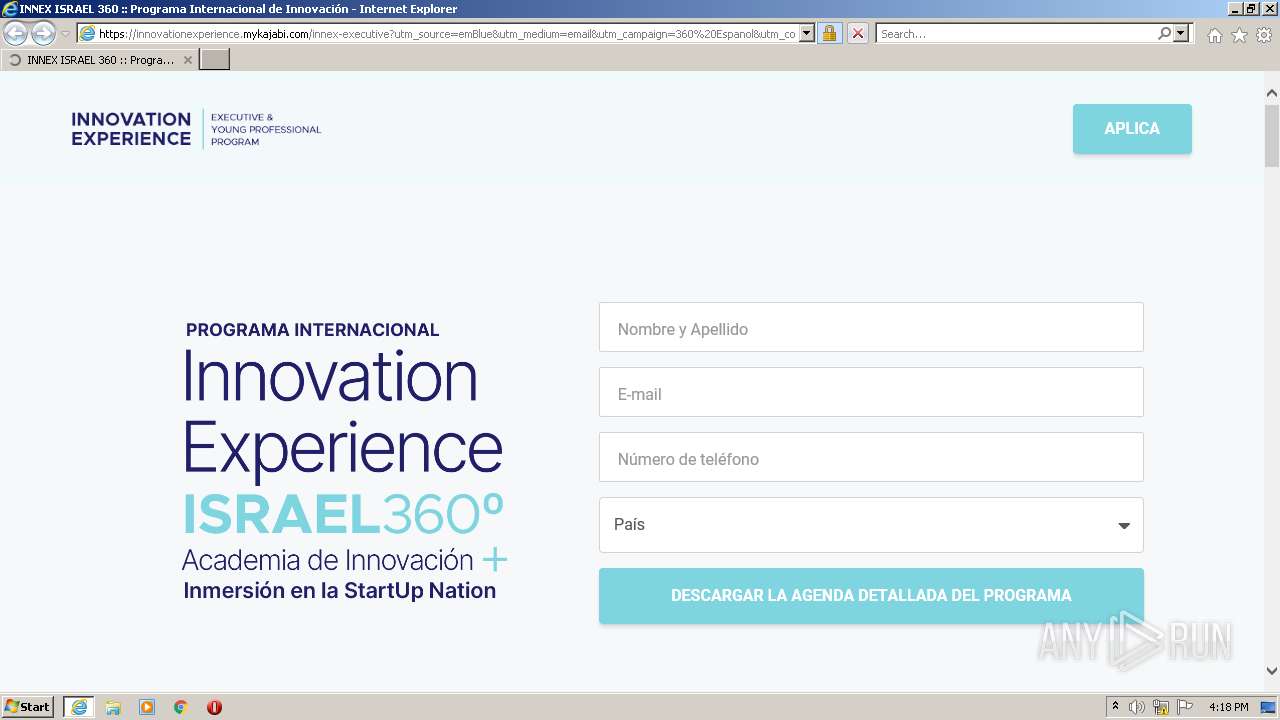
| URL: | https://eur01.safelinks.protection.outlook.com/?url=https%3A%2F%2Furldefense.proofpoint.com%2Fv2%2Furl%3Fu%3Dhttps-3A__nts.embluemail.com_p_cl-3Fdata-3Dlyf4B2IdvFFTKF-252BGyiamaicm7u7nXZxr3cdu2qMiGNWZiJvXdVRz3dUCJn5lTWKbuDvAuRpgIiXEmRTCS4ZeUTHHLcN9Opaco252x-252BIhJNI-253D-21-2D-21-2Ci8apa8-21-2D-21https-253A-252F-252Finnovationexperience.mykajabi.com-252Finnex-2Dexecutive-253Futm-5Fsource-3DemBlue-2526utm-5Fmedium-3Demail-2526utm-5Fcampaign-3D360-2BEspanol-2526utm-5Fcontent-3Drecruiting-2BLATAM-2BNEW-2D-2DAtt.-253A-2BLucas-2B-2D-2BInvitaci-25C3-25B3n-2Ba-2BIsrael-2B360-25C2-25B0-2B-257C-2BL-25C3-25ADderes-2Bde-2BAlto-2BImpacto-2526utm-5Fterm-3DLATAM-2B11.8-2D-2D3-2D-2Dnone-2D-2D0-2D10-2D-2DENVIO-2BSIMPLE%26d%3DDwMFaQ%26c%3DCVCjue1xFAdWlcQqpM6mY11X1YkBLRLie8BLA-Yhu3s%26r%3DCKnsBKPvDQxi14nP5uXh3oF8Own7pjUVJh91LgSMfvk%26m%3D8ZjlM6bxGRycOjT_awLzEmJAXyxEHlIVPoZhhsP2dyzFjJCCzAOvGaMDUY4mghOq%26s%3D4GHprkHJ8PfHsPTeAn71izro0J0W-QEG7joBzkJcNHs%26e%3D&data=05%7C01%7Clucas.chanaha%40prosegur.com%7Cdd26321c47b24c654f0208da7badec24%7C68485601fbbc47c6b1563e1a7e0a4434%7C0%7C0%7C637958284168080712%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C3000%7C%7C%7C&sdata=PVqrS0bRg9yxzPFMa0%2BHk7itNgFXPgdcYiu54oRkgIY%3D&reserved=0 |
| Full analysis: | https://app.any.run/tasks/eeb300cf-821f-42a5-8b98-aaa37ba28939 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 15:17:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AAEB080100E8A6A9745D6C22AE6ACC6A |
| SHA1: | 51A3377229CFDFA85FA3109B33F1920A10662F40 |
| SHA256: | DF48E7B1FAEE380D5C5CBDED84BF323663A02EC1FAAF2B7926FD4D0180E8923F |
| SSDEEP: | 24:2U9q4tiviurowi/SaXgrPp4BOUHiBRpk00vGHb6bhrQ5M4fKV1N5Q2xP7We:1q4Evi3dhQpIHilV0Ub+hcv8x6e |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3792)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 4008)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 4008)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 4008)
INFO
Checks supported languages
- iexplore.exe (PID: 2644)
- iexplore.exe (PID: 3792)
Reads the computer name
- iexplore.exe (PID: 2644)
- iexplore.exe (PID: 3792)
Changes internet zones settings
- iexplore.exe (PID: 2644)
Application launched itself
- iexplore.exe (PID: 2644)
Reads settings of System Certificates
- iexplore.exe (PID: 3792)
- iexplore.exe (PID: 2644)
Reads internet explorer settings
- iexplore.exe (PID: 3792)
Checks Windows Trust Settings
- iexplore.exe (PID: 2644)
- iexplore.exe (PID: 3792)
Reads CPU info
- iexplore.exe (PID: 3792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2644 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://eur01.safelinks.protection.outlook.com/?url=https%3A%2F%2Furldefense.proofpoint.com%2Fv2%2Furl%3Fu%3Dhttps-3A__nts.embluemail.com_p_cl-3Fdata-3Dlyf4B2IdvFFTKF-252BGyiamaicm7u7nXZxr3cdu2qMiGNWZiJvXdVRz3dUCJn5lTWKbuDvAuRpgIiXEmRTCS4ZeUTHHLcN9Opaco252x-252BIhJNI-253D-21-2D-21-2Ci8apa8-21-2D-21https-253A-252F-252Finnovationexperience.mykajabi.com-252Finnex-2Dexecutive-253Futm-5Fsource-3DemBlue-2526utm-5Fmedium-3Demail-2526utm-5Fcampaign-3D360-2BEspanol-2526utm-5Fcontent-3Drecruiting-2BLATAM-2BNEW-2D-2DAtt.-253A-2BLucas-2B-2D-2BInvitaci-25C3-25B3n-2Ba-2BIsrael-2B360-25C2-25B0-2B-257C-2BL-25C3-25ADderes-2Bde-2BAlto-2BImpacto-2526utm-5Fterm-3DLATAM-2B11.8-2D-2D3-2D-2Dnone-2D-2D0-2D10-2D-2DENVIO-2BSIMPLE%26d%3DDwMFaQ%26c%3DCVCjue1xFAdWlcQqpM6mY11X1YkBLRLie8BLA-Yhu3s%26r%3DCKnsBKPvDQxi14nP5uXh3oF8Own7pjUVJh91LgSMfvk%26m%3D8ZjlM6bxGRycOjT_awLzEmJAXyxEHlIVPoZhhsP2dyzFjJCCzAOvGaMDUY4mghOq%26s%3D4GHprkHJ8PfHsPTeAn71izro0J0W-QEG7joBzkJcNHs%26e%3D&data=05%7C01%7Clucas.chanaha%40prosegur.com%7Cdd26321c47b24c654f0208da7badec24%7C68485601fbbc47c6b1563e1a7e0a4434%7C0%7C0%7C637958284168080712%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C3000%7C%7C%7C&sdata=PVqrS0bRg9yxzPFMa0%2BHk7itNgFXPgdcYiu54oRkgIY%3D&reserved=0" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3792 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2644 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4008 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
Total events
22 278
Read events
22 077
Write events
201
Delete events
0
Modification events
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30977630 | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30977630 | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
40
Text files
80
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2644 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2644 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\2F23D0F5E4D72862517E1CB26A329742_F6FACC49395CFA949BCE851E73323C49 | der | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | binary | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\2F23D0F5E4D72862517E1CB26A329742_F6FACC49395CFA949BCE851E73323C49 | binary | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\AEB3247079FFA7BF2B5622D101414A7E | binary | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 2644 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
101
DNS requests
45
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2644 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAGewca9P1l7sgwzOOVR2Hc%3D | US | der | 471 b | whitelisted |
3792 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | der | 2.18 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 151.101.2.133:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHophRq39F1meVBmQbb%2F1x0%3D | US | der | 1.40 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 2.18 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://crl.sectigo.com/SectigoRSAOrganizationValidationSecureServerCA.crl | US | binary | 661 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CEDHS6KbsT5fF2JbjKx8aOD8%3D | US | der | 277 b | whitelisted |
3792 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3792 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 1.42 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 52.222.250.174:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3792 | iexplore.exe | 104.47.2.28:443 | eur01.safelinks.protection.outlook.com | Microsoft Corporation | IE | whitelisted |
3792 | iexplore.exe | 95.140.236.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | GB | malicious |
3792 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2644 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2644 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3792 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | — | US | suspicious |
3792 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
2644 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 104.18.32.68:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
3792 | iexplore.exe | 108.138.2.10:80 | o.ss2.us | BellSouth.net Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
eur01.safelinks.protection.outlook.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
urldefense.proofpoint.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |